dca479fce17aac4bfa6aee9479975230.ppt
- Количество слайдов: 7
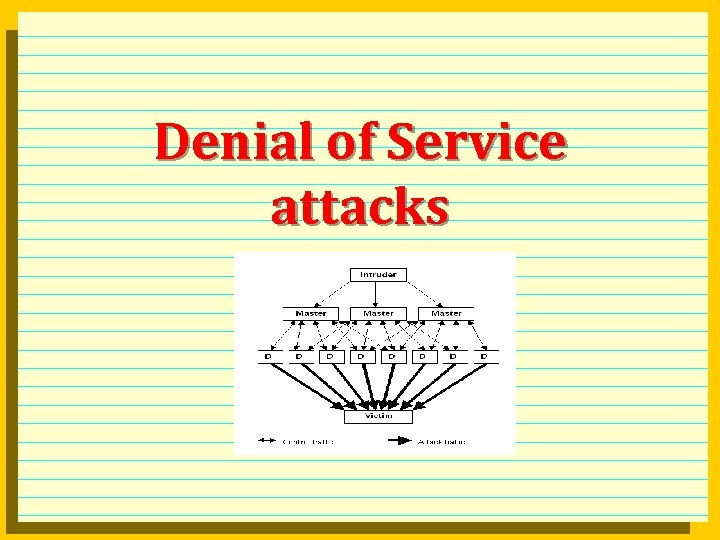 Denial of Service attacks
Denial of Service attacks
 Types of Do. S attacks l Bandwidth consumption l l l attackers have more bandwidth than victim, e. g T 3 (45 Mpbs) attacks T 1 (1. 544 Mbps). attackers amplify their bandwidth engaging other computers to attack victim with higher bandwidth, e. g. 100 56 Kbps attack a T 1 Resource starvation: consumes system resources like CPU, memory, disk space on the victim machine. l Program flaws: exploit inability of programs to handle exceptions (vulnerabilities). l Routing and DNS attacks: manipulate routing tables l l l routing protocols RIP v 1 and BGP v 4 have no, or weak authentication change routing tables to route to attacker’s net or black hole. attack to DNS servers, again route to attackers or black hole.
Types of Do. S attacks l Bandwidth consumption l l l attackers have more bandwidth than victim, e. g T 3 (45 Mpbs) attacks T 1 (1. 544 Mbps). attackers amplify their bandwidth engaging other computers to attack victim with higher bandwidth, e. g. 100 56 Kbps attack a T 1 Resource starvation: consumes system resources like CPU, memory, disk space on the victim machine. l Program flaws: exploit inability of programs to handle exceptions (vulnerabilities). l Routing and DNS attacks: manipulate routing tables l l l routing protocols RIP v 1 and BGP v 4 have no, or weak authentication change routing tables to route to attacker’s net or black hole. attack to DNS servers, again route to attackers or black hole.
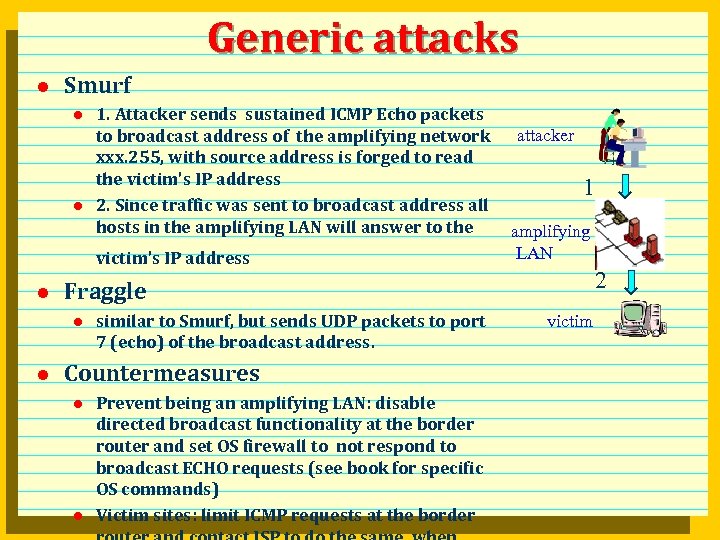 Generic attacks l Smurf l l 1. Attacker sends sustained ICMP Echo packets to broadcast address of the amplifying network xxx. 255, with source address is forged to read the victim’s IP address 2. Since traffic was sent to broadcast address all hosts in the amplifying LAN will answer to the victim’s IP address l 1 amplifying LAN 2 Fraggle l l attacker similar to Smurf, but sends UDP packets to port 7 (echo) of the broadcast address. Countermeasures l l Prevent being an amplifying LAN: disable directed broadcast functionality at the border router and set OS firewall to not respond to broadcast ECHO requests (see book for specific OS commands) Victim sites: limit ICMP requests at the border victim
Generic attacks l Smurf l l 1. Attacker sends sustained ICMP Echo packets to broadcast address of the amplifying network xxx. 255, with source address is forged to read the victim’s IP address 2. Since traffic was sent to broadcast address all hosts in the amplifying LAN will answer to the victim’s IP address l 1 amplifying LAN 2 Fraggle l l attacker similar to Smurf, but sends UDP packets to port 7 (echo) of the broadcast address. Countermeasures l l Prevent being an amplifying LAN: disable directed broadcast functionality at the border router and set OS firewall to not respond to broadcast ECHO requests (see book for specific OS commands) Victim sites: limit ICMP requests at the border victim
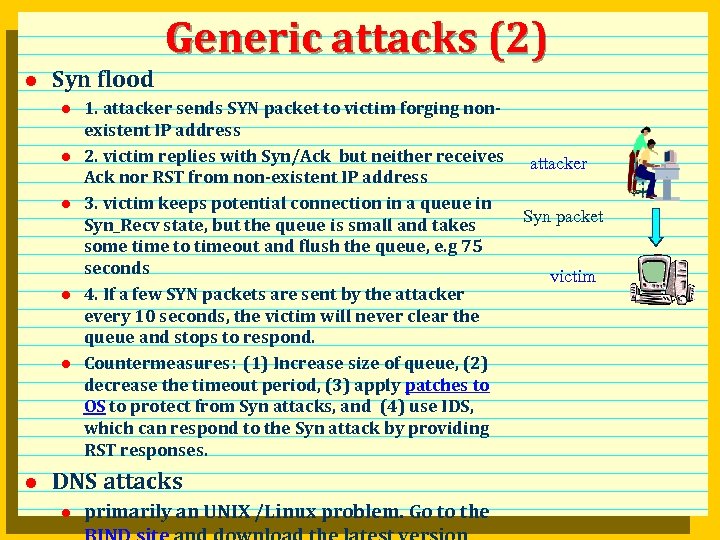 Generic attacks (2) l Syn flood l l l 1. attacker sends SYN packet to victim forging nonexistent IP address 2. victim replies with Syn/Ack but neither receives Ack nor RST from non-existent IP address 3. victim keeps potential connection in a queue in Syn_Recv state, but the queue is small and takes some time to timeout and flush the queue, e. g 75 seconds 4. If a few SYN packets are sent by the attacker every 10 seconds, the victim will never clear the queue and stops to respond. Countermeasures: (1) Increase size of queue, (2) decrease the timeout period, (3) apply patches to OS to protect from Syn attacks, and (4) use IDS, which can respond to the Syn attack by providing RST responses. DNS attacks l primarily an UNIX /Linux problem. Go to the attacker Syn packet victim
Generic attacks (2) l Syn flood l l l 1. attacker sends SYN packet to victim forging nonexistent IP address 2. victim replies with Syn/Ack but neither receives Ack nor RST from non-existent IP address 3. victim keeps potential connection in a queue in Syn_Recv state, but the queue is small and takes some time to timeout and flush the queue, e. g 75 seconds 4. If a few SYN packets are sent by the attacker every 10 seconds, the victim will never clear the queue and stops to respond. Countermeasures: (1) Increase size of queue, (2) decrease the timeout period, (3) apply patches to OS to protect from Syn attacks, and (4) use IDS, which can respond to the Syn attack by providing RST responses. DNS attacks l primarily an UNIX /Linux problem. Go to the attacker Syn packet victim
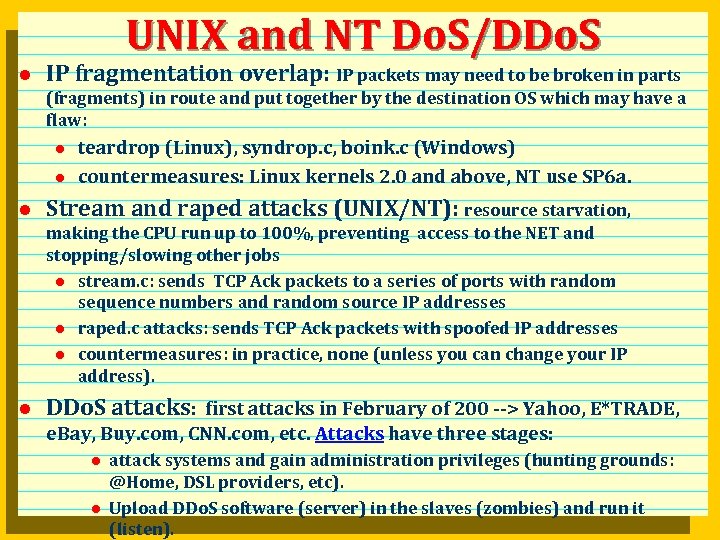 UNIX and NT Do. S/DDo. S l IP fragmentation overlap: IP packets may need to be broken in parts (fragments) in route and put together by the destination OS which may have a flaw: l l l teardrop (Linux), syndrop. c, boink. c (Windows) countermeasures: Linux kernels 2. 0 and above, NT use SP 6 a. Stream and raped attacks (UNIX/NT): resource starvation, making the CPU run up to 100%, preventing access to the NET and stopping/slowing other jobs l stream. c: sends TCP Ack packets to a series of ports with random sequence numbers and random source IP addresses l raped. c attacks: sends TCP Ack packets with spoofed IP addresses l countermeasures: in practice, none (unless you can change your IP address). l DDo. S attacks: first attacks in February of 200 --> Yahoo, E*TRADE, e. Bay, Buy. com, CNN. com, etc. Attacks have three stages: l l attack systems and gain administration privileges (hunting grounds: @Home, DSL providers, etc). Upload DDo. S software (server) in the slaves (zombies) and run it (listen).
UNIX and NT Do. S/DDo. S l IP fragmentation overlap: IP packets may need to be broken in parts (fragments) in route and put together by the destination OS which may have a flaw: l l l teardrop (Linux), syndrop. c, boink. c (Windows) countermeasures: Linux kernels 2. 0 and above, NT use SP 6 a. Stream and raped attacks (UNIX/NT): resource starvation, making the CPU run up to 100%, preventing access to the NET and stopping/slowing other jobs l stream. c: sends TCP Ack packets to a series of ports with random sequence numbers and random source IP addresses l raped. c attacks: sends TCP Ack packets with spoofed IP addresses l countermeasures: in practice, none (unless you can change your IP address). l DDo. S attacks: first attacks in February of 200 --> Yahoo, E*TRADE, e. Bay, Buy. com, CNN. com, etc. Attacks have three stages: l l attack systems and gain administration privileges (hunting grounds: @Home, DSL providers, etc). Upload DDo. S software (server) in the slaves (zombies) and run it (listen).
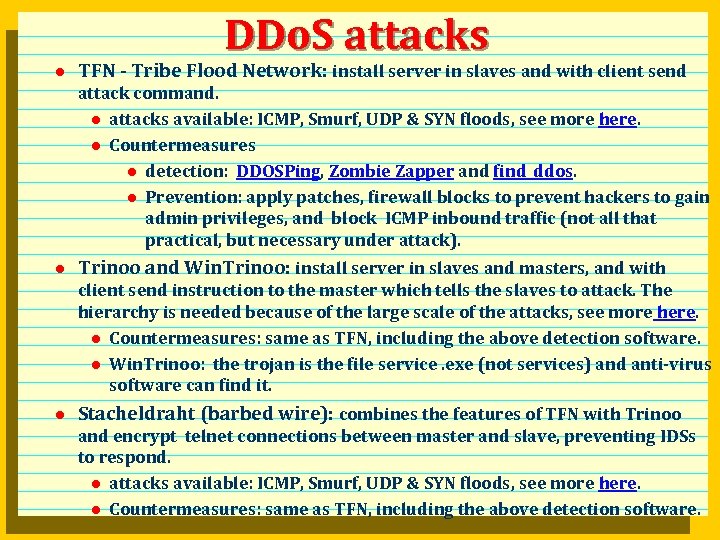 DDo. S attacks l TFN - Tribe Flood Network: install server in slaves and with client send attack command. l attacks available: ICMP, Smurf, UDP & SYN floods, see more here. l Countermeasures l detection: DDOSPing, Zombie Zapper and find_ddos. l Prevention: apply patches, firewall blocks to prevent hackers to gain admin privileges, and block ICMP inbound traffic (not all that practical, but necessary under attack). l Trinoo and Win. Trinoo: install server in slaves and masters, and with client send instruction to the master which tells the slaves to attack. The hierarchy is needed because of the large scale of the attacks, see more here. l Countermeasures: same as TFN, including the above detection software. l Win. Trinoo: the trojan is the file service. exe (not services) and anti-virus software can find it. l Stacheldraht (barbed wire): combines the features of TFN with Trinoo and encrypt telnet connections between master and slave, preventing IDSs to respond. l attacks available: ICMP, Smurf, UDP & SYN floods, see more here. l Countermeasures: same as TFN, including the above detection software.
DDo. S attacks l TFN - Tribe Flood Network: install server in slaves and with client send attack command. l attacks available: ICMP, Smurf, UDP & SYN floods, see more here. l Countermeasures l detection: DDOSPing, Zombie Zapper and find_ddos. l Prevention: apply patches, firewall blocks to prevent hackers to gain admin privileges, and block ICMP inbound traffic (not all that practical, but necessary under attack). l Trinoo and Win. Trinoo: install server in slaves and masters, and with client send instruction to the master which tells the slaves to attack. The hierarchy is needed because of the large scale of the attacks, see more here. l Countermeasures: same as TFN, including the above detection software. l Win. Trinoo: the trojan is the file service. exe (not services) and anti-virus software can find it. l Stacheldraht (barbed wire): combines the features of TFN with Trinoo and encrypt telnet connections between master and slave, preventing IDSs to respond. l attacks available: ICMP, Smurf, UDP & SYN floods, see more here. l Countermeasures: same as TFN, including the above detection software.
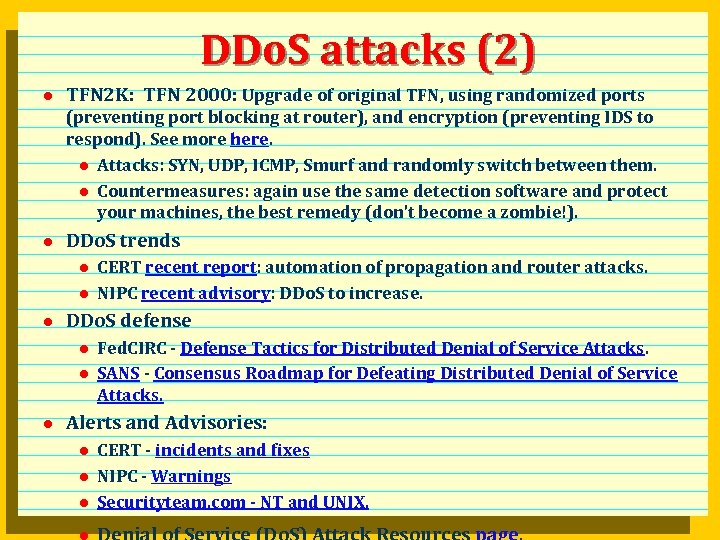 DDo. S attacks (2) l TFN 2 K: TFN 2000: Upgrade of original TFN, using randomized ports (preventing port blocking at router), and encryption (preventing IDS to respond). See more here. l Attacks: SYN, UDP, ICMP, Smurf and randomly switch between them. l Countermeasures: again use the same detection software and protect your machines, the best remedy (don’t become a zombie!). l DDo. S trends l l l DDo. S defense l l l CERT recent report: automation of propagation and router attacks. NIPC recent advisory: DDo. S to increase. Fed. CIRC - Defense Tactics for Distributed Denial of Service Attacks. SANS - Consensus Roadmap for Defeating Distributed Denial of Service Attacks. Alerts and Advisories: l l l CERT - incidents and fixes NIPC - Warnings Securityteam. com - NT and UNIX.
DDo. S attacks (2) l TFN 2 K: TFN 2000: Upgrade of original TFN, using randomized ports (preventing port blocking at router), and encryption (preventing IDS to respond). See more here. l Attacks: SYN, UDP, ICMP, Smurf and randomly switch between them. l Countermeasures: again use the same detection software and protect your machines, the best remedy (don’t become a zombie!). l DDo. S trends l l l DDo. S defense l l l CERT recent report: automation of propagation and router attacks. NIPC recent advisory: DDo. S to increase. Fed. CIRC - Defense Tactics for Distributed Denial of Service Attacks. SANS - Consensus Roadmap for Defeating Distributed Denial of Service Attacks. Alerts and Advisories: l l l CERT - incidents and fixes NIPC - Warnings Securityteam. com - NT and UNIX.


