db69fba327de0d367bcfce9bdf66a795.ppt
- Количество слайдов: 17
 Denial of Service attacks on transit networks David Harmelin DANTE Do. S attacks on transit network - David Harmelin ( david. harmelin@dante. org. uk )
Denial of Service attacks on transit networks David Harmelin DANTE Do. S attacks on transit network - David Harmelin ( david. harmelin@dante. org. uk )
 DANTE • advanced network services for the European research community: TEN-155, GÉANT • active in testing and evaluating emerging technologies http: //www. dante. net/tf-ngn • DANCERT (dancert@dante. org. uk) http: //www. dante. net/security Do. S attacks on transit network - David Harmelin ( david. harmelin@dante. org. uk )
DANTE • advanced network services for the European research community: TEN-155, GÉANT • active in testing and evaluating emerging technologies http: //www. dante. net/tf-ngn • DANCERT (dancert@dante. org. uk) http: //www. dante. net/security Do. S attacks on transit network - David Harmelin ( david. harmelin@dante. org. uk )
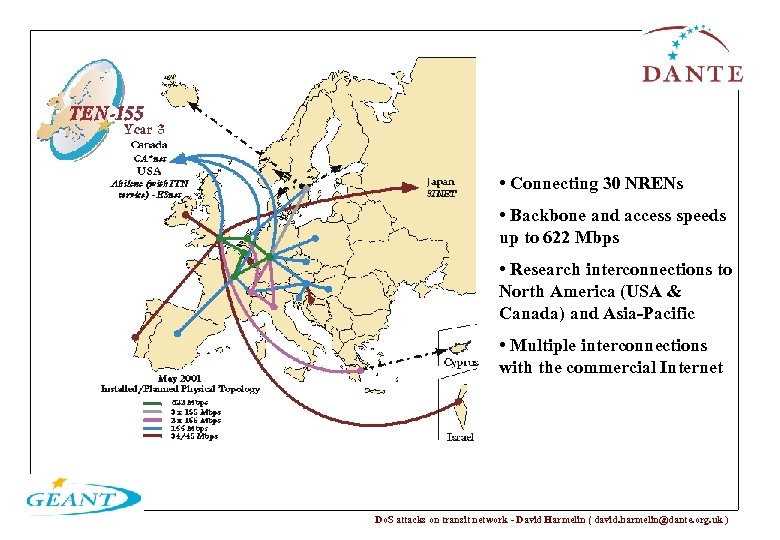 • Connecting 30 NRENs • Backbone and access speeds up to 622 Mbps • Research interconnections to North America (USA & Canada) and Asia-Pacific • Multiple interconnections with the commercial Internet Do. S attacks on transit network - David Harmelin ( david. harmelin@dante. org. uk )
• Connecting 30 NRENs • Backbone and access speeds up to 622 Mbps • Research interconnections to North America (USA & Canada) and Asia-Pacific • Multiple interconnections with the commercial Internet Do. S attacks on transit network - David Harmelin ( david. harmelin@dante. org. uk )
 Definition of a Do. S attack: an attack on a network or computer, the attack primary aim of which is to disrupt access to a given service. In this presentation, only Do. S attacks involving flooding of networks are considered (networked flood-based Do. S attacks). Do. S attacks on transit network - David Harmelin ( david. harmelin@dante. org. uk )
Definition of a Do. S attack: an attack on a network or computer, the attack primary aim of which is to disrupt access to a given service. In this presentation, only Do. S attacks involving flooding of networks are considered (networked flood-based Do. S attacks). Do. S attacks on transit network - David Harmelin ( david. harmelin@dante. org. uk )
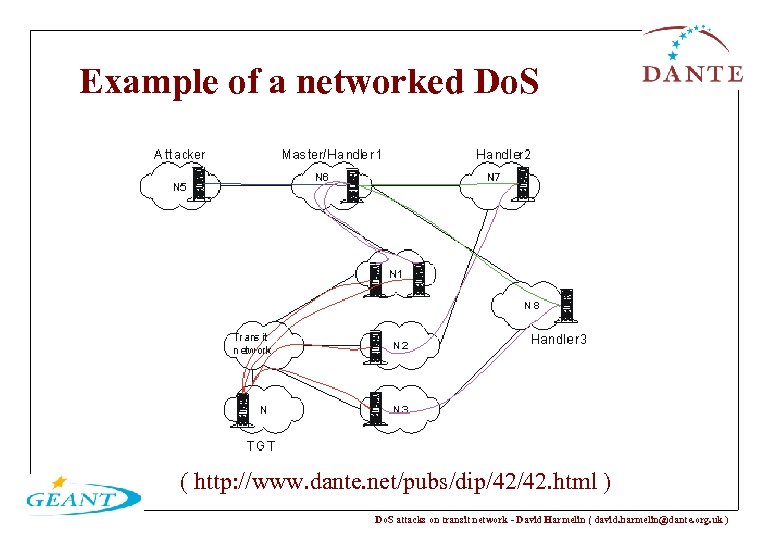 Example of a networked Do. S ( http: //www. dante. net/pubs/dip/42/42. html ) Do. S attacks on transit network - David Harmelin ( david. harmelin@dante. org. uk )
Example of a networked Do. S ( http: //www. dante. net/pubs/dip/42/42. html ) Do. S attacks on transit network - David Harmelin ( david. harmelin@dante. org. uk )
 Why care about Do. S attacks? • Do. S attacks add to the overall costs : – when unnoticed – one target, many outages – elements not targeted may still be victims • all users (using the starved resource) suffer. • No quick fix in sight! Need for better co-operation between ISPs. Do. S attacks on transit network - David Harmelin ( david. harmelin@dante. org. uk )
Why care about Do. S attacks? • Do. S attacks add to the overall costs : – when unnoticed – one target, many outages – elements not targeted may still be victims • all users (using the starved resource) suffer. • No quick fix in sight! Need for better co-operation between ISPs. Do. S attacks on transit network - David Harmelin ( david. harmelin@dante. org. uk )
 Are you affected by Do. S attacks? • Everybody running/using IP networks or services is. • Do. S attacks are rarely reported in the media. • Most organisations do notice when affected. • Management may not be notified. Do. S attacks on transit network - David Harmelin ( david. harmelin@dante. org. uk )
Are you affected by Do. S attacks? • Everybody running/using IP networks or services is. • Do. S attacks are rarely reported in the media. • Most organisations do notice when affected. • Management may not be notified. Do. S attacks on transit network - David Harmelin ( david. harmelin@dante. org. uk )
 DANTE and Do. S attacks • 1999: Do. S attacks noticed regularly on TEN-155. • Beginning 2000: Do. S attacks against major companies in the news. • 2000: first tool based on peer-peer matrix analysis. Failed. • End 2000: second tool, based on sampled flow data. DANCERT relies on it to reduce the amount of Do. S attacks on transit network - David Harmelin ( david. harmelin@dante. org. uk )
DANTE and Do. S attacks • 1999: Do. S attacks noticed regularly on TEN-155. • Beginning 2000: Do. S attacks against major companies in the news. • 2000: first tool based on peer-peer matrix analysis. Failed. • End 2000: second tool, based on sampled flow data. DANCERT relies on it to reduce the amount of Do. S attacks on transit network - David Harmelin ( david. harmelin@dante. org. uk )
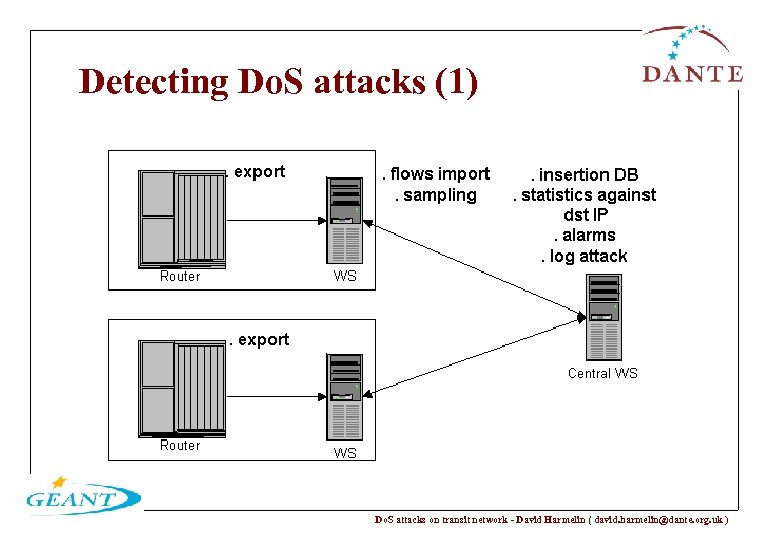 Detecting Do. S attacks (1) Do. S attacks on transit network - David Harmelin ( david. harmelin@dante. org. uk )
Detecting Do. S attacks (1) Do. S attacks on transit network - David Harmelin ( david. harmelin@dante. org. uk )
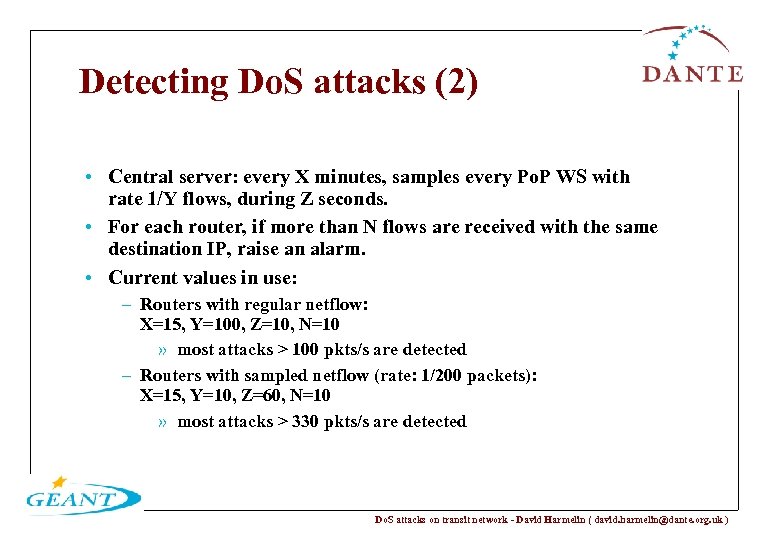 Detecting Do. S attacks (2) • Central server: every X minutes, samples every Po. P WS with rate 1/Y flows, during Z seconds. • For each router, if more than N flows are received with the same destination IP, raise an alarm. • Current values in use: – Routers with regular netflow: X=15, Y=100, Z=10, N=10 » most attacks > 100 pkts/s are detected – Routers with sampled netflow (rate: 1/200 packets): X=15, Y=10, Z=60, N=10 » most attacks > 330 pkts/s are detected Do. S attacks on transit network - David Harmelin ( david. harmelin@dante. org. uk )
Detecting Do. S attacks (2) • Central server: every X minutes, samples every Po. P WS with rate 1/Y flows, during Z seconds. • For each router, if more than N flows are received with the same destination IP, raise an alarm. • Current values in use: – Routers with regular netflow: X=15, Y=100, Z=10, N=10 » most attacks > 100 pkts/s are detected – Routers with sampled netflow (rate: 1/200 packets): X=15, Y=10, Z=60, N=10 » most attacks > 330 pkts/s are detected Do. S attacks on transit network - David Harmelin ( david. harmelin@dante. org. uk )
 Results • Running the tool on 4 core routers since 12/2000. • Logging all attacks detected since 03/2001 • Trade-off between – accuracy (confirmed attacks/alarms raised=98%) – detection effectiveness (>100 pkt/s). • Average of 34 different attacks per day logged, up to 5 -6 concurrent (96 polls per day). • 90% “C class” attacks - easily traceable. • 75% of attacks are 40 bytes TCP packets. Do. S attacks on transit network - David Harmelin ( david. harmelin@dante. org. uk )
Results • Running the tool on 4 core routers since 12/2000. • Logging all attacks detected since 03/2001 • Trade-off between – accuracy (confirmed attacks/alarms raised=98%) – detection effectiveness (>100 pkt/s). • Average of 34 different attacks per day logged, up to 5 -6 concurrent (96 polls per day). • 90% “C class” attacks - easily traceable. • 75% of attacks are 40 bytes TCP packets. Do. S attacks on transit network - David Harmelin ( david. harmelin@dante. org. uk )
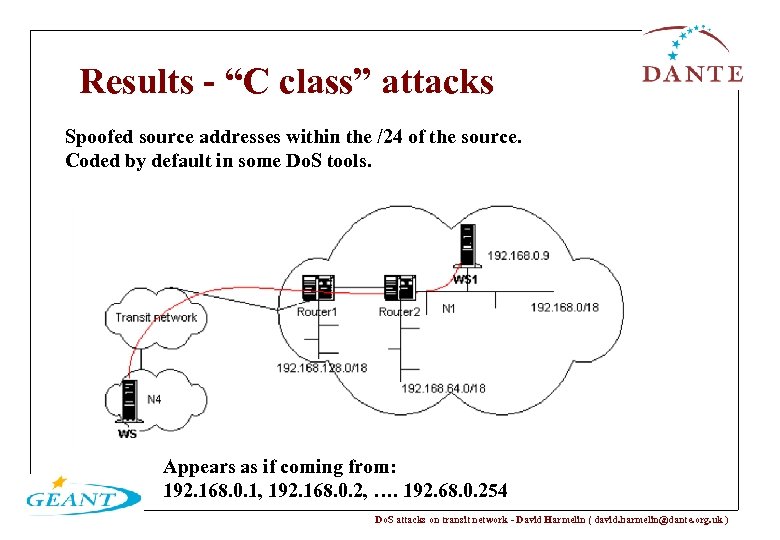 Results - “C class” attacks Spoofed source addresses within the /24 of the source. Coded by default in some Do. S tools. Appears as if coming from: 192. 168. 0. 1, 192. 168. 0. 2, …. 192. 68. 0. 254 Do. S attacks on transit network - David Harmelin ( david. harmelin@dante. org. uk )
Results - “C class” attacks Spoofed source addresses within the /24 of the source. Coded by default in some Do. S tools. Appears as if coming from: 192. 168. 0. 1, 192. 168. 0. 2, …. 192. 68. 0. 254 Do. S attacks on transit network - David Harmelin ( david. harmelin@dante. org. uk )
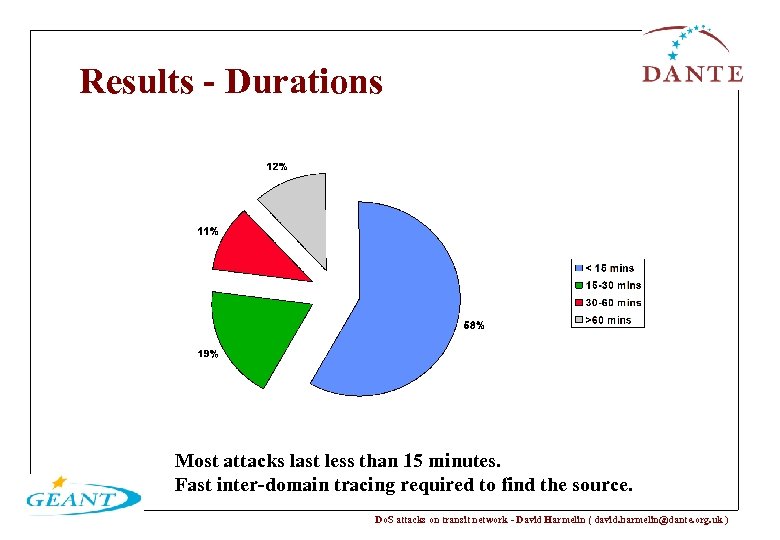 Results - Durations Most attacks last less than 15 minutes. Fast inter-domain tracing required to find the source. Do. S attacks on transit network - David Harmelin ( david. harmelin@dante. org. uk )
Results - Durations Most attacks last less than 15 minutes. Fast inter-domain tracing required to find the source. Do. S attacks on transit network - David Harmelin ( david. harmelin@dante. org. uk )
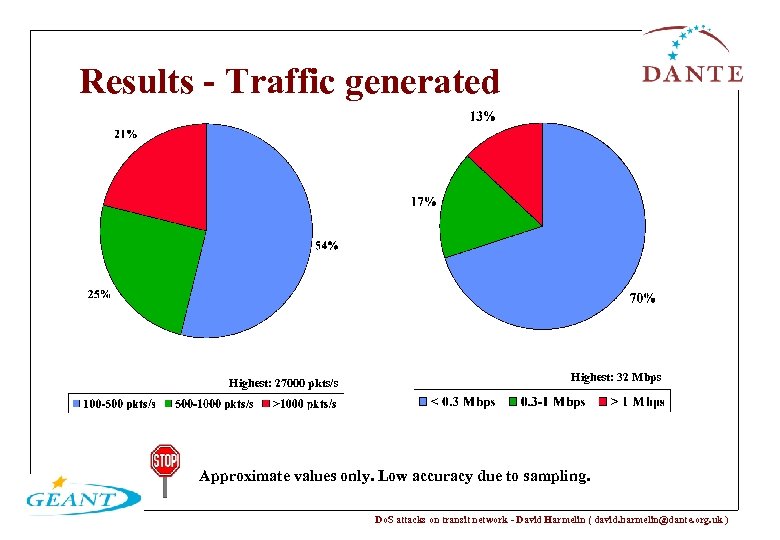 Results - Traffic generated Highest: 27000 pkts/s Highest: 32 Mbps Approximate values only. Low accuracy due to sampling. Do. S attacks on transit network - David Harmelin ( david. harmelin@dante. org. uk )
Results - Traffic generated Highest: 27000 pkts/s Highest: 32 Mbps Approximate values only. Low accuracy due to sampling. Do. S attacks on transit network - David Harmelin ( david. harmelin@dante. org. uk )
 Known limitations of this method • Routers capabilities (netflow required) • Detecting networked flood-based Do. S attacks only. . . • … but not ALL. • Detection helps, but further need for co-operation. Do. S attacks on transit network - David Harmelin ( david. harmelin@dante. org. uk )
Known limitations of this method • Routers capabilities (netflow required) • Detecting networked flood-based Do. S attacks only. . . • … but not ALL. • Detection helps, but further need for co-operation. Do. S attacks on transit network - David Harmelin ( david. harmelin@dante. org. uk )
 Other approaches exist • No detection • Human detection • Monitoring CPU load, and traffic counters. • IETF working on itrace • Passive monitoring • Other flow monitoring approaches Do. S attacks on transit network - David Harmelin ( david. harmelin@dante. org. uk )
Other approaches exist • No detection • Human detection • Monitoring CPU load, and traffic counters. • IETF working on itrace • Passive monitoring • Other flow monitoring approaches Do. S attacks on transit network - David Harmelin ( david. harmelin@dante. org. uk )
 Who should help? How? • IP network operators: – automatic detection and logging of Do. S attacks – co-operation between CERT teams – SLAs • End-sites: – prevention – trace when Do. S traffic sources are reported • DANTE: – http: //www. dante. net/security/dos/ – gives away the in-house software to transit providers. Do. S attacks on transit network - David Harmelin ( david. harmelin@dante. org. uk )
Who should help? How? • IP network operators: – automatic detection and logging of Do. S attacks – co-operation between CERT teams – SLAs • End-sites: – prevention – trace when Do. S traffic sources are reported • DANTE: – http: //www. dante. net/security/dos/ – gives away the in-house software to transit providers. Do. S attacks on transit network - David Harmelin ( david. harmelin@dante. org. uk )


