8f7a7faef466b74998e3f29145145dca.ppt
- Количество слайдов: 36
Database Security Floris Geerts 1
Course organization • One introductory lecture (this one) • Then, a range of db security topics presented by you • You will be graded on the quality of presentation, technical depth, critical assessment of the topic and ability to answer questions raised in class • No exam. 2
Course organization • Today, after this lecture: – Send me an email floris. geerts@ua. ac. be – with your name and at most two partners (in case we need to assign multiple persons to the same topic) – A ranked list of the top 10 topics (11 topics) • Then I will assign the topics. • You’ll get time to study and prepare presentations • You send the slides to me, and incorporate comments 3
Topics 1. Access control • • Getting access Access control mechanisms 2. Safety & integrity • Redundancy • Data integrity 3. Intrusion • DB specific • Software specific 4
Topics 4. Cryptography • • • Symmetric Asymmetric Quantum (optional) 4. Privacy & Security • • Statistical DB Privacy preservation 5
Data Security Dorothy Denning, 1982: • Data Security is the science and study of methods of protecting data (. . . ) from unauthorized disclosure and modification • Data Security = Confidentiality + Integrity 6
Data Security • Distinct from systems and network security – Assumes these are already secure • Tools: – Cryptography, information theory, statistics, … • Applications: – Everywhere 7
Topic 1 Access methods: “Getting in” • It is all about passwords and authentication - How are passwords used for authentication in DBMS? - What kind of password control mechanisms do DBMS have? (e. g. , Oracle, …) - What makes a password good or bad? - Techniques to check this - Techniques to generate one - Alternatives to passwords (e. g. , captcha) 8
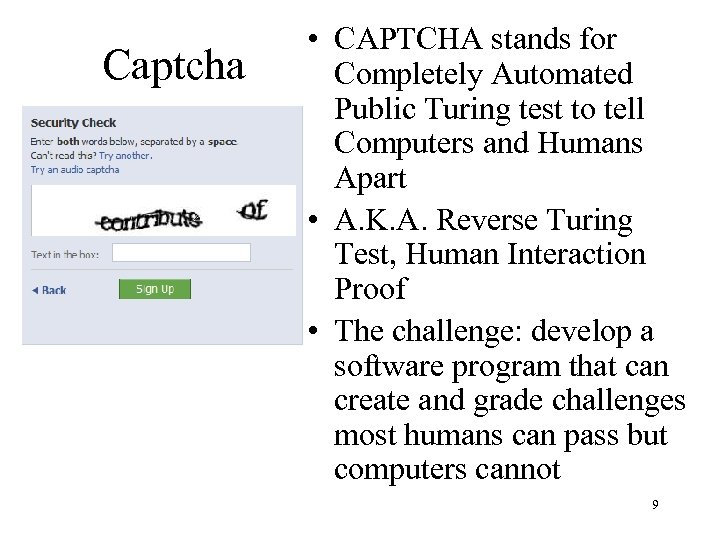
Captcha • CAPTCHA stands for Completely Automated Public Turing test to tell Computers and Humans Apart • A. K. A. Reverse Turing Test, Human Interaction Proof • The challenge: develop a software program that can create and grade challenges most humans can pass but computers cannot 9
Topic 2: Access methods: control mechanisms • How do DBMS control access to different users? • How do DBMS assure that users can only change/query data to which they have access? • As an example 10
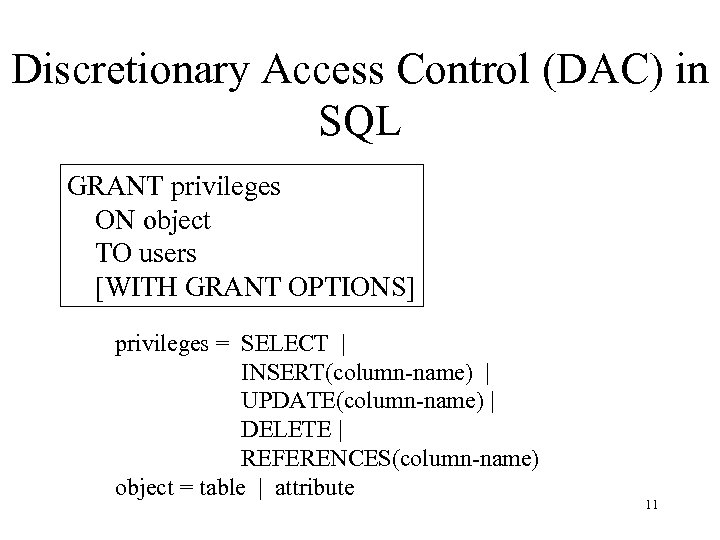
Discretionary Access Control (DAC) in SQL GRANT privileges ON object TO users [WITH GRANT OPTIONS] privileges = SELECT | INSERT(column-name) | UPDATE(column-name) | DELETE | REFERENCES(column-name) object = table | attribute 11
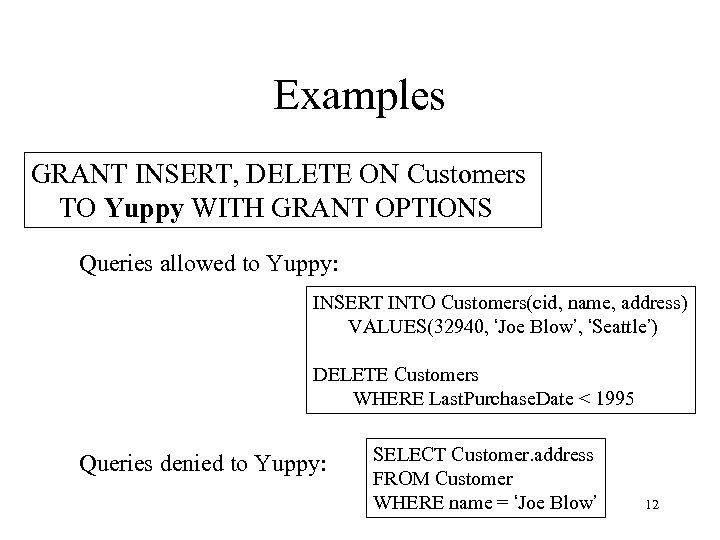
Examples GRANT INSERT, DELETE ON Customers TO Yuppy WITH GRANT OPTIONS Queries allowed to Yuppy: INSERT INTO Customers(cid, name, address) VALUES(32940, ‘Joe Blow’, ‘Seattle’) DELETE Customers WHERE Last. Purchase. Date < 1995 Queries denied to Yuppy: SELECT Customer. address FROM Customer WHERE name = ‘Joe Blow’ 12
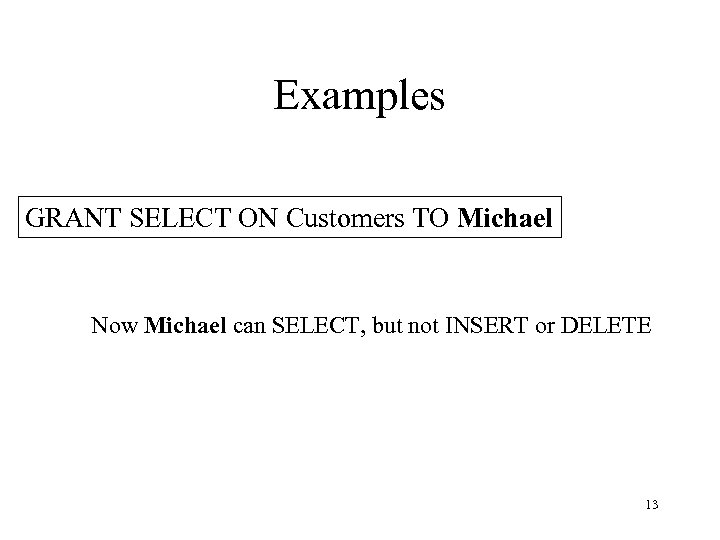
Examples GRANT SELECT ON Customers TO Michael Now Michael can SELECT, but not INSERT or DELETE 13
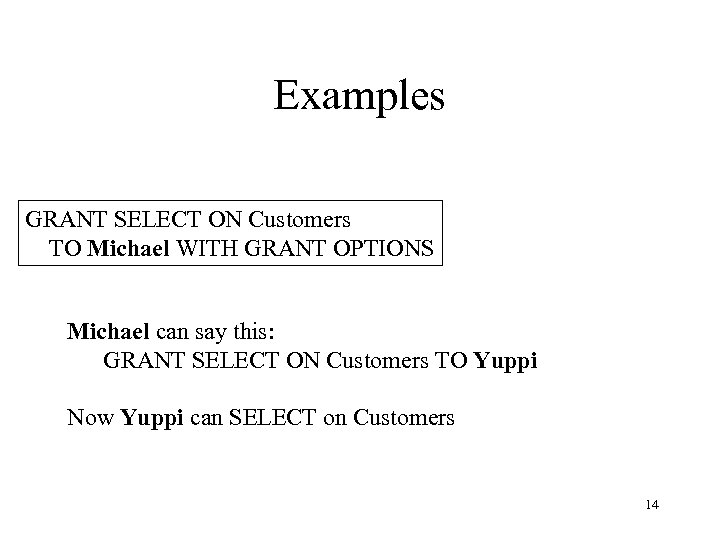
Examples GRANT SELECT ON Customers TO Michael WITH GRANT OPTIONS Michael can say this: GRANT SELECT ON Customers TO Yuppi Now Yuppi can SELECT on Customers 14
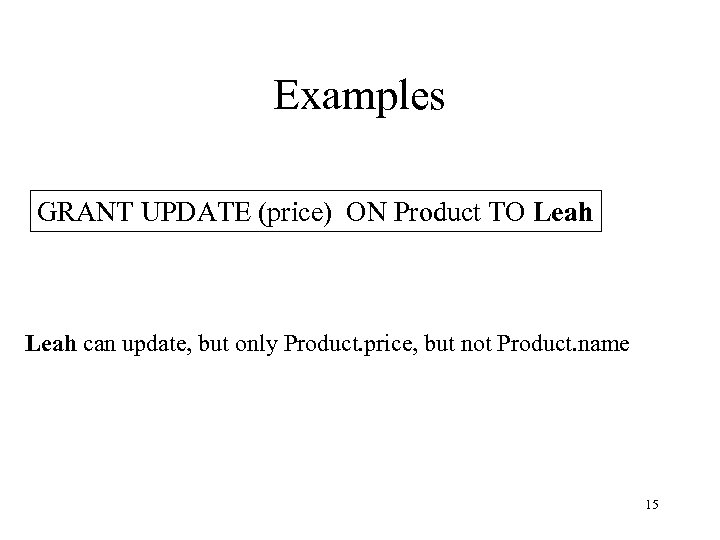
Examples GRANT UPDATE (price) ON Product TO Leah can update, but only Product. price, but not Product. name 15
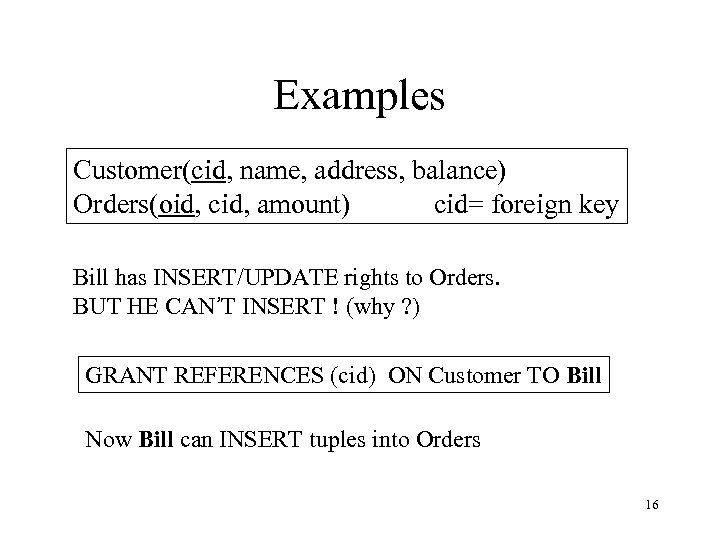
Examples Customer(cid, name, address, balance) Orders(oid, cid, amount) cid= foreign key Bill has INSERT/UPDATE rights to Orders. BUT HE CAN’T INSERT ! (why ? ) GRANT REFERENCES (cid) ON Customer TO Bill Now Bill can INSERT tuples into Orders 16
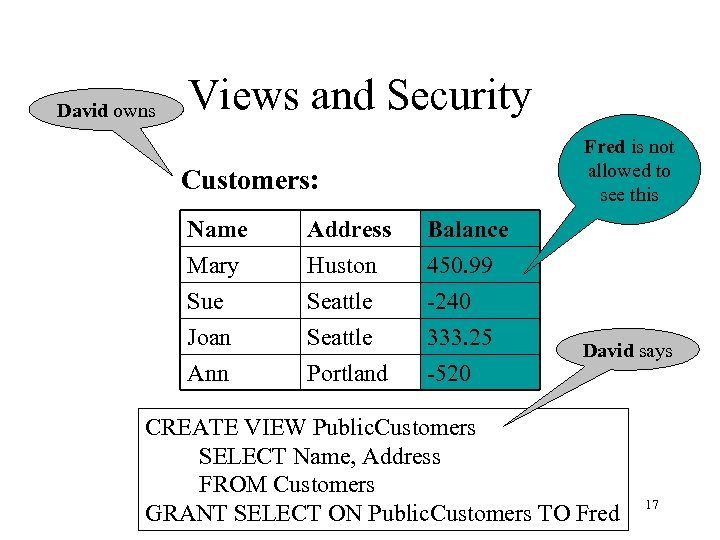
David owns Views and Security Fred is not allowed to see this Customers: Name Mary Sue Joan Address Huston Seattle Balance 450. 99 -240 333. 25 Ann Portland -520 David says CREATE VIEW Public. Customers SELECT Name, Address FROM Customers GRANT SELECT ON Public. Customers TO Fred 17
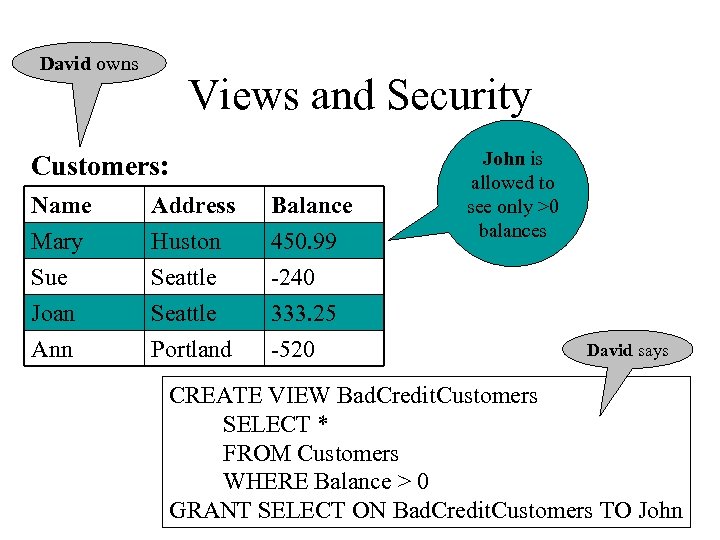
David owns Views and Security Customers: Name Mary Sue Joan Address Huston Seattle Balance 450. 99 -240 333. 25 Ann Portland -520 John is allowed to see only >0 balances David says CREATE VIEW Bad. Credit. Customers SELECT * FROM Customers WHERE Balance > 0 18 GRANT SELECT ON Bad. Credit. Customers TO John
![Revocation REVOKE [GRANT OPTION FOR] privileges ON object FROM users { RESTRICT | CASCADE Revocation REVOKE [GRANT OPTION FOR] privileges ON object FROM users { RESTRICT | CASCADE](https://present5.com/presentation/8f7a7faef466b74998e3f29145145dca/image-19.jpg)
Revocation REVOKE [GRANT OPTION FOR] privileges ON object FROM users { RESTRICT | CASCADE } Administrator says: REVOKE SELECT ON Customers FROM David CASCADE John loses SELECT privileges on Bad. Credit. Customers 19
![Revocation Joe: GRANT […. ] TO Art … Art: GRANT […. ] TO Bob Revocation Joe: GRANT […. ] TO Art … Art: GRANT […. ] TO Bob](https://present5.com/presentation/8f7a7faef466b74998e3f29145145dca/image-20.jpg)
Revocation Joe: GRANT […. ] TO Art … Art: GRANT […. ] TO Bob … Bob: GRANT […. ] TO Art … Joe: GRANT […. ] TO Cal … Cal: GRANT […. ] TO Bob … Joe: REVOKE […. ] FROM Art CASCADE Same privilege, same object, GRANT OPTION What happens ? ? 20
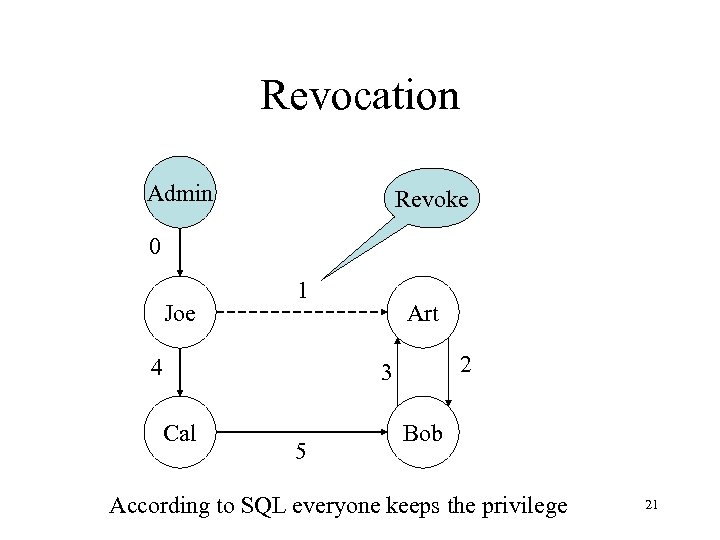
Revocation Admin Revoke 0 Joe 1 4 Art 2 3 Cal 5 Bob According to SQL everyone keeps the privilege 21
Other approaches Discretionary Access Control (DAC) Label-based Access Control (LBAC) Role-based Access Control (RBAC) Mandatory Access Control (MAC) Pro’s and con’s of these control mechanisms? 22
Topic: Safety & Integrity It is about keeping our precious bits safe from harm. • Disk failure which mostly goes together with data loss • System failure which can cause data inconsistency. (For example a Denial-Of-Service attack can result in system failures because of the exhaustion of system resources. 23
Topic 3: Recovery • Mostly solved by redundancy: – having and organizing redundant information so that the data stored can be recovered in case there is a disk failure. – Where and how to store? Secondary storage, RAIDs – How to assure that all the data has a copy somewhere 24
Topic 4: Integrity • How to assure that all data is consistent – The same data in all copies • How to assure that nothing gets corrupted during transmission – Error correcting codes • How to keep track of changes and possible unauthorized access – Transaction log/data auditing 25
Topic 5: DB intrusion • Intrusion prevention – detecting ongoing attacks in real time in order to prevent damage to the database. • Intrusion detection – Use of database auditing • Example: SQL injection 26
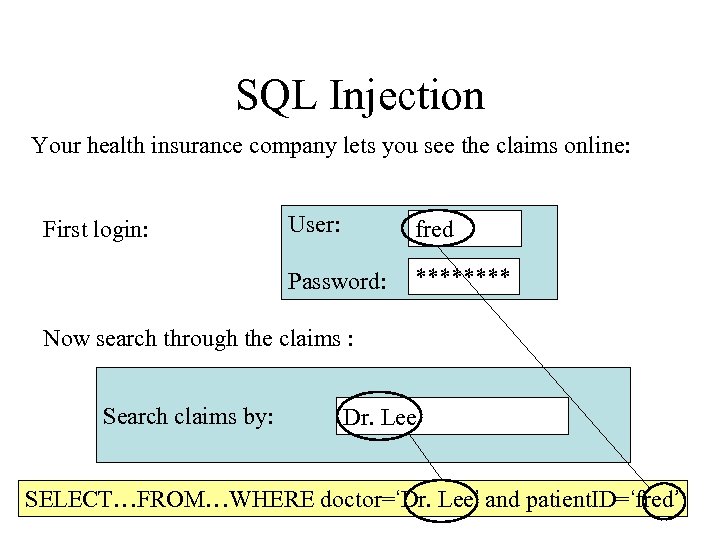
SQL Injection Your health insurance company lets you see the claims online: User: fred Password: First login: **** Now search through the claims : Search claims by: Dr. Lee SELECT…FROM…WHERE doctor=‘Dr. Lee’ and patient. ID=‘fred’ 27
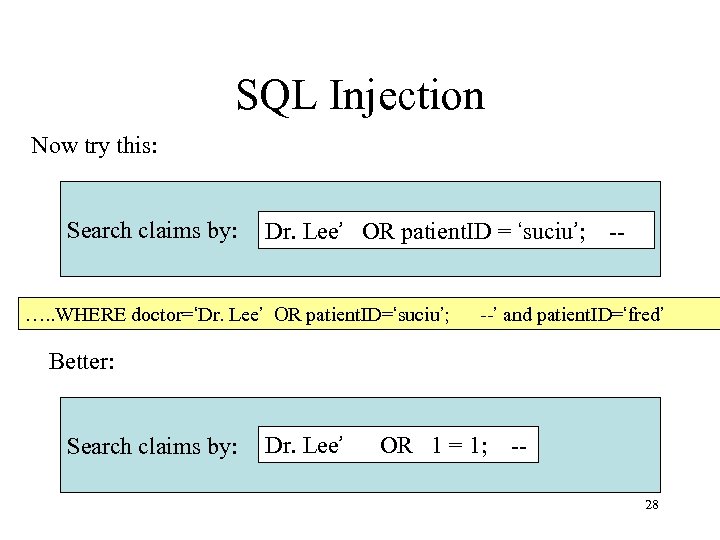
SQL Injection Now try this: Search claims by: Dr. Lee’ OR patient. ID = ‘suciu’; -- …. . WHERE doctor=‘Dr. Lee’ OR patient. ID=‘suciu’; --’ and patient. ID=‘fred’ Better: Search claims by: Dr. Lee’ OR 1 = 1; -28
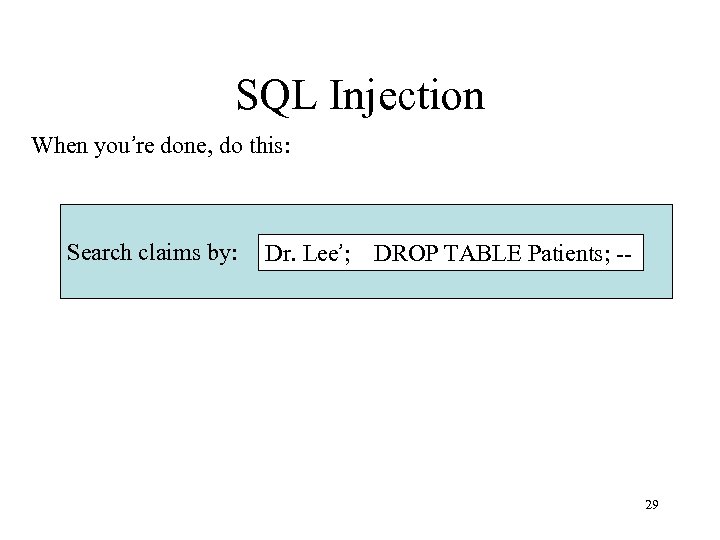
SQL Injection When you’re done, do this: Search claims by: Dr. Lee’; DROP TABLE Patients; -- 29
SQL Injection • The DBMS works perfectly. So why is SQL injection possible so often ? 30
Topic 6: Software intrusion • Leveraging Stack and Buffer overflow in programs • How to prevent/detect such intrusions? 31
Topic 7: Cryptography symmetric Commonly used techniques Same encryption and decryption key DES, AES 32
Topic 8: Cryptography – asymmetric • Different encoding and decoding keys • Public key • RSA 33
Topic 9: Cryptography Quantum • Newest methods based on quantum computing • You need to ask if you want this – it is a bit math heavy. 34
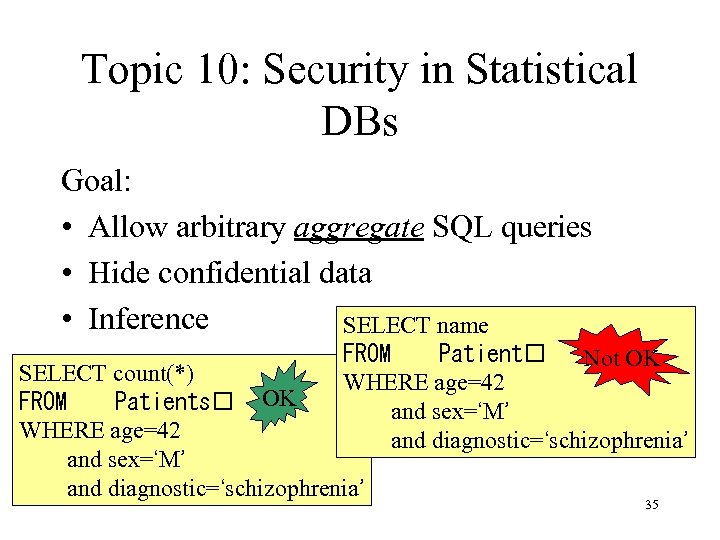
Topic 10: Security in Statistical DBs Goal: • Allow arbitrary aggregate SQL queries • Hide confidential data • Inference SELECT name FROM Patient Not OK WHERE age=42 and sex=‘M’ and diagnostic=‘schizophrenia’ SELECT count(*) FROM Patients OK WHERE age=42 and sex=‘M’ and diagnostic=‘schizophrenia’ 35
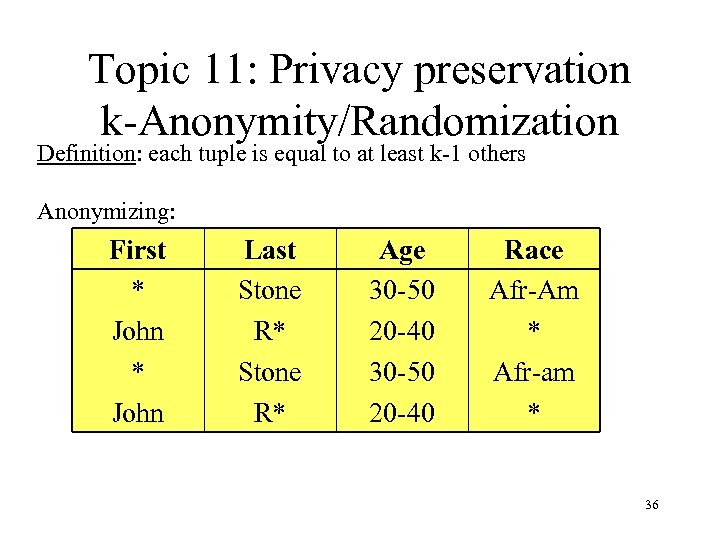
Topic 11: Privacy preservation k-Anonymity/Randomization Definition: each tuple is equal to at least k-1 others Anonymizing: First Harry * John Beatrice * John Last Stone Reyser R* Stone Ramos R* Age 30 -50 34 20 -40 36 30 -50 47 20 -40 22 Race Afr-Am Cauc * Afr-am Hisp * 36
8f7a7faef466b74998e3f29145145dca.ppt