2165497dd84070494eff656abcb16ac9.ppt
- Количество слайдов: 6
Cyber Security & Critical Controls Chris Few Industry Enabling Services CESG February 2011 © Crown Copyright. All rights reserved.
Cyber Essentials • An HMG scheme for testing security controls to defeat common Internet based threats • Covers five control areas: – Internet Gateways; Secure configuration; User access control; Malware protection; Patch management • Includes a two tier assurance framework: – Cyber Essentials: verified self-assessment • Organisation completes self assessment questionnaire • Responses reviewed as reasonable by assessor – Cyber Essentials PLUS: independently tested • Tests whether controls implemented are sufficient to defeat common Internet based attacks February 2011 © Crown Copyright. All rights reserved.
Relevance of Cyber Essentials to LMN • Policing of connections to shared academic networks • Criterion for selecting suppliers accessing academic data • Demonstrating commitment to cyber security • Incorporation into ESISS penetration testing improves clarity of scope of testing February 2011 © Crown Copyright. All rights reserved.
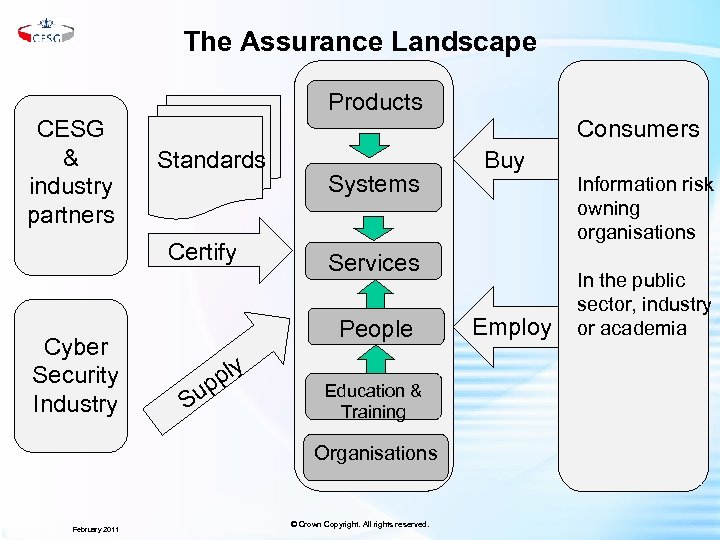
The Assurance Landscape Products CESG & industry partners Consumers Standards Certify Cyber Security Industry Systems Services People Su ply p Education & Training Organisations February 2011 Buy © Crown Copyright. All rights reserved. Employ Information risk owning organisations In the public sector, industry or academia
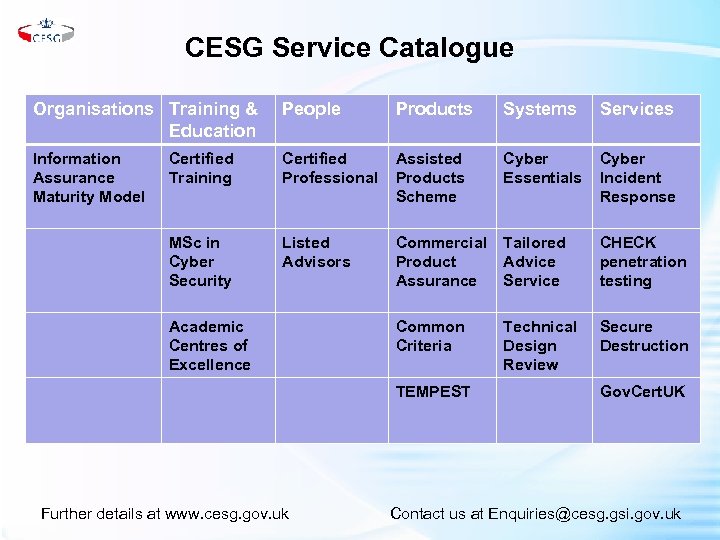
CESG Service Catalogue Organisations Training & Education People Products Systems Services Information Assurance Maturity Model Certified Training Certified Professional Assisted Products Scheme Cyber Essentials Cyber Incident Response MSc in Cyber Security Listed Advisors Commercial Product Assurance Tailored Advice Service CHECK penetration testing Common Criteria Technical Design Review Secure Destruction Academic Centres of Excellence TEMPEST Further details at www. cesg. gov. uk Gov. Cert. UK Contact us at Enquiries@cesg. gsi. gov. uk
Questions for LMN • Which parts of the CESG service catalogue are most relevant to you? • How can CESG develop its portfolio of schemes to meet your needs? • Can CESG facilitate closer relationships between academia and industry on the topic of cyber security? February 2011 © Crown Copyright. All rights reserved.
2165497dd84070494eff656abcb16ac9.ppt