d38bf3eb2269be7ea2fb689ca12c9ef1.ppt
- Количество слайдов: 161
 CSE 331: Introduction to Networks and Security Slide Set 6 Fall 2001 Instructor: Carl A. Gunter CIS 551 Columbia University
CSE 331: Introduction to Networks and Security Slide Set 6 Fall 2001 Instructor: Carl A. Gunter CIS 551 Columbia University
 Introduction to Security l Goals Ø Ø Ø l l Availability Integrity Confidentiality Ø Ø Ø Targets Ø Ø Ø Hardware Software Data Controls Ø l Physical security Limited interface Identification and authorization Encryption Analysis of costs and benefits
Introduction to Security l Goals Ø Ø Ø l l Availability Integrity Confidentiality Ø Ø Ø Targets Ø Ø Ø Hardware Software Data Controls Ø l Physical security Limited interface Identification and authorization Encryption Analysis of costs and benefits
 Progress and Risk l Security-critical considerations Ø Credit card purchases on the web Ø Voting on the web Ø Banking on the web Ø Mobile agents and active networks l Safety and security considerations Ø Military systems, eg. Star Wars Ø Actuators on public networks
Progress and Risk l Security-critical considerations Ø Credit card purchases on the web Ø Voting on the web Ø Banking on the web Ø Mobile agents and active networks l Safety and security considerations Ø Military systems, eg. Star Wars Ø Actuators on public networks
 Security Requirements Banking l Government l Public Telecommunications Carriers l Corporate / Private Networks l Electronic Commerce l
Security Requirements Banking l Government l Public Telecommunications Carriers l Corporate / Private Networks l Electronic Commerce l
 Banking l Electronic Funds Transfer (EFT) Ø Prosecution of fraud problematic Ø Financial system overall at risk l Automated Teller Machine (ATM)
Banking l Electronic Funds Transfer (EFT) Ø Prosecution of fraud problematic Ø Financial system overall at risk l Automated Teller Machine (ATM)
 Automatic Teller Machines l Goals Ø Availability: Provide automated teller operations 24 x 7 in convenient locations Ø Integrity: Authorized users only, transactional guarantees Ø Confidentiality: Private communication with branches or center Vulnerabilities and controls l Risk analysis and liabilities l
Automatic Teller Machines l Goals Ø Availability: Provide automated teller operations 24 x 7 in convenient locations Ø Integrity: Authorized users only, transactional guarantees Ø Confidentiality: Private communication with branches or center Vulnerabilities and controls l Risk analysis and liabilities l
 Government National security of course, but also l “Unclassified but sensitive information” must not be disclosed l Ø Example: l social security web page Electronic signatures approved for government contractors
Government National security of course, but also l “Unclassified but sensitive information” must not be disclosed l Ø Example: l social security web page Electronic signatures approved for government contractors
 Public Telecom Carriers l Operations, Administration, Maintenance, and Provisioning (OAM&P) Ø Customer network management complexities Ø Theft by hackers Ø Unauthorized eavesdropping Availability is a key concern l Significant insider risks l
Public Telecom Carriers l Operations, Administration, Maintenance, and Provisioning (OAM&P) Ø Customer network management complexities Ø Theft by hackers Ø Unauthorized eavesdropping Availability is a key concern l Significant insider risks l
 Corporate Private Networks Completely private networks are becoming a thing of the past because of telecommuting. l Protection of proprietary information of course, but also concerns like privacy in the health care industry. l Foreign government threat? l
Corporate Private Networks Completely private networks are becoming a thing of the past because of telecommuting. l Protection of proprietary information of course, but also concerns like privacy in the health care industry. l Foreign government threat? l
 Electronic Commerce Electronic Data Interchange (EDI) l Electronic contracts need to be binding l ABA Resolution: “recognize that information in l electronic form, where appropriate, may be considered to satisfy legal requirements regarding a writing or signature to the same extent as information on paper or in other conventional forms, when appropriate security techniques, practices, and procedures have been adopted. ”
Electronic Commerce Electronic Data Interchange (EDI) l Electronic contracts need to be binding l ABA Resolution: “recognize that information in l electronic form, where appropriate, may be considered to satisfy legal requirements regarding a writing or signature to the same extent as information on paper or in other conventional forms, when appropriate security techniques, practices, and procedures have been adopted. ”
 Three Scenarios Vera buys a lathe. l Inter-corporate trading. l Nola’s electronic market. l
Three Scenarios Vera buys a lathe. l Inter-corporate trading. l Nola’s electronic market. l
 Vera Buys a Lathe Vera, owner of Vera’s Manufacturing, shops for a lathe on the internet using WWW. l She finds the desired product from Danielle’s Machine Makers and makes the order using a web form provided by Danielle’s. l Danielle’s confirms that the order really comes from Vera’s manufacturing. l
Vera Buys a Lathe Vera, owner of Vera’s Manufacturing, shops for a lathe on the internet using WWW. l She finds the desired product from Danielle’s Machine Makers and makes the order using a web form provided by Danielle’s. l Danielle’s confirms that the order really comes from Vera’s manufacturing. l
 Vera Pays for the Lathe l l She sends her credit card number, suitably encrypted. She sends an EDI payment order remittance advice transaction set instructing Vera’s bank to credit Danielle’s bank account. She uses an online payment mechanism like a credit-card based payment protocol or electronic check. The lathe is delivered through the usual distribution channels.
Vera Pays for the Lathe l l She sends her credit card number, suitably encrypted. She sends an EDI payment order remittance advice transaction set instructing Vera’s bank to credit Danielle’s bank account. She uses an online payment mechanism like a credit-card based payment protocol or electronic check. The lathe is delivered through the usual distribution channels.
 Inter-Corporate Trading Danielle’s Machine Makers is a mediumsized company in Canada with longestablished requirements for highgrade steel which it buys from Steelcorp. l Steelcorp aims to reduce costs of customer transactions by using secure messaging with its regular customers. l Origin and confidentiality of all correspondence must be ensured. l
Inter-Corporate Trading Danielle’s Machine Makers is a mediumsized company in Canada with longestablished requirements for highgrade steel which it buys from Steelcorp. l Steelcorp aims to reduce costs of customer transactions by using secure messaging with its regular customers. l Origin and confidentiality of all correspondence must be ensured. l
 Nola’s Electronic Market Nola is an entrepreneurial small businessperson who works from her home basement. l She buys items from suppliers willing to do business wholly electronically and sells them through a WWW storefront. l Effective marketing of the web page and very low overhead provide Nola’s competitive edge. l
Nola’s Electronic Market Nola is an entrepreneurial small businessperson who works from her home basement. l She buys items from suppliers willing to do business wholly electronically and sells them through a WWW storefront. l Effective marketing of the web page and very low overhead provide Nola’s competitive edge. l
 Legal Support Mostly by analogy with other commerce rules, but there are challenges. l How to satisfy traditional legal requirements for reduction of agreements to signed writings. l How to apply rules of evidence. l Interpreting, adapting, and complying with existing legal standards for electronic transactions.
Legal Support Mostly by analogy with other commerce rules, but there are challenges. l How to satisfy traditional legal requirements for reduction of agreements to signed writings. l How to apply rules of evidence. l Interpreting, adapting, and complying with existing legal standards for electronic transactions.
 Goals of Security DATA Confidentiality DATA Integrity Availability
Goals of Security DATA Confidentiality DATA Integrity Availability
 Safety and Security Many things in common and some major differences. l Some similarities aid understanding of both. l System vs. Environment. l Accident, breach. l Hazard, vulnerability. l
Safety and Security Many things in common and some major differences. l Some similarities aid understanding of both. l System vs. Environment. l Accident, breach. l Hazard, vulnerability. l
 System vs. Environment (Safety) Environment System
System vs. Environment (Safety) Environment System
 System vs. Environment (Security) Environment System
System vs. Environment (Security) Environment System
 Accident and Security Breach l Accident Ø Loss of life Ø Injury Ø Damage to property l Security Breach Ø Secret is revealed Ø Service is disabled Ø Data is altered Ø Messages are fabricated
Accident and Security Breach l Accident Ø Loss of life Ø Injury Ø Damage to property l Security Breach Ø Secret is revealed Ø Service is disabled Ø Data is altered Ø Messages are fabricated
 Accident Definition An accident is an undesired and unplanned (but not necessarily unexpected) event that results in (at least) a specified level of harm. l Define breach similarly. l A security threat is a possible form of breach l
Accident Definition An accident is an undesired and unplanned (but not necessarily unexpected) event that results in (at least) a specified level of harm. l Define breach similarly. l A security threat is a possible form of breach l
 Hazards and Vulnerabilities l Hazard Ø No fire alarms Ø No fire extinguishers Ø Rags close to furnace l Vulnerability Ø Password too short Ø Secret sent in plaintext over public network Ø Files not write protected
Hazards and Vulnerabilities l Hazard Ø No fire alarms Ø No fire extinguishers Ø Rags close to furnace l Vulnerability Ø Password too short Ø Secret sent in plaintext over public network Ø Files not write protected
 Hazard Definition A hazard is a state or set of conditions of a system that, together with other conditions in the environment of the system, will lead inevitably to an accident. l Define security vulnerability similarly. l
Hazard Definition A hazard is a state or set of conditions of a system that, together with other conditions in the environment of the system, will lead inevitably to an accident. l Define security vulnerability similarly. l
 Other Terms Asset: object of value. l Exposure: threat to an asset. l Attack: effort by an agent to exploit a vulnerability and create a breach. l
Other Terms Asset: object of value. l Exposure: threat to an asset. l Attack: effort by an agent to exploit a vulnerability and create a breach. l
 Major Threats Interruption l Interception l Modification l Fabrication l
Major Threats Interruption l Interception l Modification l Fabrication l
 Major Assets Hardware l Software l Data l
Major Assets Hardware l Software l Data l
 Threats to Hardware Interruption: crash, performance degradation l Interception: theft l Modification: tapping l Fabrication: spoofed devices l
Threats to Hardware Interruption: crash, performance degradation l Interception: theft l Modification: tapping l Fabrication: spoofed devices l
 Threats to Software Code l l l Interruption: deletion, reset protection Interception: theft Modification Ø Ø Ø l Trojan horse Logic bomb Virus Back door Information leak Fabrication: spoofing software distribution on the web
Threats to Software Code l l l Interruption: deletion, reset protection Interception: theft Modification Ø Ø Ø l Trojan horse Logic bomb Virus Back door Information leak Fabrication: spoofing software distribution on the web
 Threats to Software Processes Interruption: bad inputs l Interception: attacks on agents l Modification: of exploited data l Fabrication: service spoofing (man-inthe-middle) l
Threats to Software Processes Interruption: bad inputs l Interception: attacks on agents l Modification: of exploited data l Fabrication: service spoofing (man-inthe-middle) l
 Threats to Data Interruption: deletion, perceived integrity violation l Interception: eavesdropping, snooping memory l Modification: alteration of important information l Fabrication: spoofing web pages l
Threats to Data Interruption: deletion, perceived integrity violation l Interception: eavesdropping, snooping memory l Modification: alteration of important information l Fabrication: spoofing web pages l
 Principles of Security Easiest Penetration: An intruder must be expected to use any available means of penetration. l Adequate Protection: Computer items must be protected only until they lose their value. They must be protected to a degree consistent with their value. l Effectiveness: Controls must be used to be effective. They must be efficient, easy to use, and appropriate. l
Principles of Security Easiest Penetration: An intruder must be expected to use any available means of penetration. l Adequate Protection: Computer items must be protected only until they lose their value. They must be protected to a degree consistent with their value. l Effectiveness: Controls must be used to be effective. They must be efficient, easy to use, and appropriate. l
 Controls Physical security l Limited interface l Identification and authorization l Encryption l
Controls Physical security l Limited interface l Identification and authorization l Encryption l
 Breakdown of S/W Controls l Program controls Ø as exercised by the programmer Ø as dictated by the programming language or programming environment Operating system controls l Development process controls l
Breakdown of S/W Controls l Program controls Ø as exercised by the programmer Ø as dictated by the programming language or programming environment Operating system controls l Development process controls l
 Basic Encryption Monoalphabetic substitution ciphers l Polyalphabetic substitution ciphers l Transposition ciphers l Other hiding techniques l Stream versus block ciphers l
Basic Encryption Monoalphabetic substitution ciphers l Polyalphabetic substitution ciphers l Transposition ciphers l Other hiding techniques l Stream versus block ciphers l
 Circumstances Sender S Transmission Medium T O Interceptor Receiver R
Circumstances Sender S Transmission Medium T O Interceptor Receiver R
 What Can O Do to a Message? Block it (availability) l Intercept it (confidentiality) l Modify it (integrity) l Fabricate another (integrity) l
What Can O Do to a Message? Block it (availability) l Intercept it (confidentiality) l Modify it (integrity) l Fabricate another (integrity) l
 Terminology Encryption / Decryption l Encode / Decode l Plaintext / Ciphertext l Cryptography: hidden writing. l Cryptanalysis: uncovering what is hidden. l
Terminology Encryption / Decryption l Encode / Decode l Plaintext / Ciphertext l Cryptography: hidden writing. l Cryptanalysis: uncovering what is hidden. l
 Monoalphabetic Substitution Substitute one letter for another l Creates “confusion” l
Monoalphabetic Substitution Substitute one letter for another l Creates “confusion” l
 Keyless Encryption C = E(P) and P = D(C) l P = D(E(P)) l Transmit E(P), receiver applies D. l Select D and E so that l Ø Without knowing D or E it is hard to discover P from E(P). Ø It is feasible to know and apply D and E.
Keyless Encryption C = E(P) and P = D(C) l P = D(E(P)) l Transmit E(P), receiver applies D. l Select D and E so that l Ø Without knowing D or E it is hard to discover P from E(P). Ø It is feasible to know and apply D and E.
 Caesar Cipher (Original) E(p) = p + 3 (mod 26) l D(p) = p - 3 (mod 26) l T R E A T Y w u h d w b l I M P O S S I B L E l p s r v v l e o h Easy to recall and calculate D and E. Create a table: A B C D E F G H I J K L M N O P Q R S T U V W X Y Z d e f g h I j k l m n o p q r s t u v w x y z a b c
Caesar Cipher (Original) E(p) = p + 3 (mod 26) l D(p) = p - 3 (mod 26) l T R E A T Y w u h d w b l I M P O S S I B L E l p s r v v l e o h Easy to recall and calculate D and E. Create a table: A B C D E F G H I J K L M N O P Q R S T U V W X Y Z d e f g h I j k l m n o p q r s t u v w x y z a b c
 Encryption Strategy: Confusion The Caesar cipher confuses the letters of the alphabet, causing the result look like gibberish. l As we applied it in the previous example, a space is interpreted as a space, providing no confusion. l Note: changing one letter of plaintext changes exactly one letter of ciphertext. l
Encryption Strategy: Confusion The Caesar cipher confuses the letters of the alphabet, causing the result look like gibberish. l As we applied it in the previous example, a space is interpreted as a space, providing no confusion. l Note: changing one letter of plaintext changes exactly one letter of ciphertext. l
 Algorithm vs. Key l Moreover: Ø It is hard to keep D and E secret if they are much used, and Ø Cryptanalysis is possible. l To address the first of these problems assume: algorithm is known, but key is not known.
Algorithm vs. Key l Moreover: Ø It is hard to keep D and E secret if they are much used, and Ø Cryptanalysis is possible. l To address the first of these problems assume: algorithm is known, but key is not known.
 Encryption with a Key l Symmetric key ØC = E(K, P) Ø P = D(K, C) Ø P = D(K, E(K, P)) l Asymetric key ØC = E(Kpublic, P) Ø P = D(Kprivate, C) Ø P = D(Kprivate, E(Kpublic, P))
Encryption with a Key l Symmetric key ØC = E(K, P) Ø P = D(K, C) Ø P = D(K, E(K, P)) l Asymetric key ØC = E(Kpublic, P) Ø P = D(Kprivate, C) Ø P = D(Kprivate, E(Kpublic, P))
 Permutation Generalize Caesar cipher to allow other ways to permute the alphabet. l What is now called a Caesar cipher is any choice of an offset: ( ) = (n + ) (mod 26). The number n is the key. l Generalize further: use any permutation as a key. l To encode, apply the key to each letter. l To decode, apply the inverse of the key to each letter. l
Permutation Generalize Caesar cipher to allow other ways to permute the alphabet. l What is now called a Caesar cipher is any choice of an offset: ( ) = (n + ) (mod 26). The number n is the key. l Generalize further: use any permutation as a key. l To encode, apply the key to each letter. l To decode, apply the inverse of the key to each letter. l
 Sample Permutations l Example: a passphrase like “this is a long key” can be a key. A B C D E F G H I J K L M N O P Q R S T U V W X Y Z t h i s a l o n g k e y b c d f j m p q r u v w x z l Example: take every third letter. A B C D E F G H I J K L M N O P Q R S T U V W X Y Z a d g j m p s v y b e h k n q t w z c f i l o r u x l ( ) = (3 * ) (mod 26)
Sample Permutations l Example: a passphrase like “this is a long key” can be a key. A B C D E F G H I J K L M N O P Q R S T U V W X Y Z t h i s a l o n g k e y b c d f j m p q r u v w x z l Example: take every third letter. A B C D E F G H I J K L M N O P Q R S T U V W X Y Z a d g j m p s v y b e h k n q t w z c f i l o r u x l ( ) = (3 * ) (mod 26)
 Cryptanalysis of Monoalphabetic Ciphers There are 26! permutation keys, so it is not feasible to try all possible keys. l Mapping a space to itself is a big clue: try to guess short words. l Look for common English repeated letters like a “ss” or “oo” l wklv phvvdjh lv qrw wrr kdug wr euhdn T--- ------- -- -OT TOO ---- TO ----- l Exploit frequency information
Cryptanalysis of Monoalphabetic Ciphers There are 26! permutation keys, so it is not feasible to try all possible keys. l Mapping a space to itself is a big clue: try to guess short words. l Look for common English repeated letters like a “ss” or “oo” l wklv phvvdjh lv qrw wrr kdug wr euhdn T--- ------- -- -OT TOO ---- TO ----- l Exploit frequency information

 Sample Ciphertext hqfubswlrq lv d phdqv rl dwwdlqlqj vhfxuh frpsxwdwlrq ryhu lqvhfxuh fkdqqhov eb xvlqj hqfubswlrq zh glvjxlvh wkh phvvdjh vr wkdw hyhq li wkh wudqvplvvlrq lv glyhuwhg wkh phvvdjh zloo qrw eh uhyhdohg
Sample Ciphertext hqfubswlrq lv d phdqv rl dwwdlqlqj vhfxuh frpsxwdwlrq ryhu lqvhfxuh fkdqqhov eb xvlqj hqfubswlrq zh glvjxlvh wkh phvvdjh vr wkdw hyhq li wkh wudqvplvvlrq lv glyhuwhg wkh phvvdjh zloo qrw eh uhyhdohg
 Note similarity of e and h.
Note similarity of e and h.
 Caesar Cipher Example hqfubswlrq lv d phdqv rl dwwdlqlqj vhfxuh frpsxwdwlrq ryhu lqvhfxuh fkdqqhov eb xvlqj hqfubswlrq zh glvjxlvh wkh phvvdjh vr wkdw hyhq li wkh wudqvplvvlrq lv glyhuwhg wkh phvvdjh zloo qrw eh uhyhdohg ENCRYPTION IS A MEANS OF ATTAINING SECURE COMMUNICATION OVER INSECURE CHANNELS BY USING ENCRYPTION WE DISGUISE THE MESSAGE SO THAT EVEN IF THE TRANSMISSION IS DIVERTED THE MESSAGE WILL NOT BE REVEALED
Caesar Cipher Example hqfubswlrq lv d phdqv rl dwwdlqlqj vhfxuh frpsxwdwlrq ryhu lqvhfxuh fkdqqhov eb xvlqj hqfubswlrq zh glvjxlvh wkh phvvdjh vr wkdw hyhq li wkh wudqvplvvlrq lv glyhuwhg wkh phvvdjh zloo qrw eh uhyhdohg ENCRYPTION IS A MEANS OF ATTAINING SECURE COMMUNICATION OVER INSECURE CHANNELS BY USING ENCRYPTION WE DISGUISE THE MESSAGE SO THAT EVEN IF THE TRANSMISSION IS DIVERTED THE MESSAGE WILL NOT BE REVEALED
 Polyalphabetic Cipher To beat frequency analysis we need to break the connection between frequently occurring ciphertext letters and frequently occurring plaintext letters. l This could be done by varying the translation of letters. l Consider using one translation for letters in even positions and a different one for letters in odd positions. l
Polyalphabetic Cipher To beat frequency analysis we need to break the connection between frequently occurring ciphertext letters and frequently occurring plaintext letters. l This could be done by varying the translation of letters. l Consider using one translation for letters in even positions and a different one for letters in odd positions. l
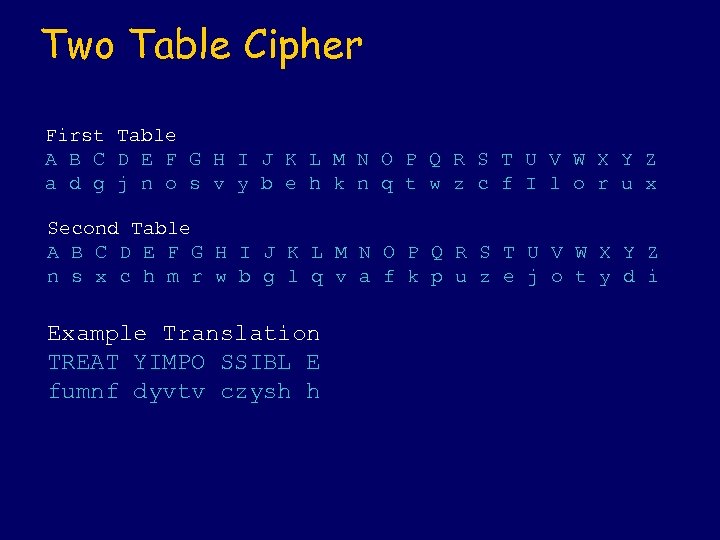 Two Table Cipher First Table A B C D E F G H I J K L M N O P Q R S T U V W X Y Z a d g j n o s v y b e h k n q t w z c f I l o r u x Second Table A B C D E F G H I J K L M N O P Q R S T U V W X Y Z n s x c h m r w b g l q v a f k p u z e j o t y d i Example Translation TREAT YIMPO SSIBL E fumnf dyvtv czysh h
Two Table Cipher First Table A B C D E F G H I J K L M N O P Q R S T U V W X Y Z a d g j n o s v y b e h k n q t w z c f I l o r u x Second Table A B C D E F G H I J K L M N O P Q R S T U V W X Y Z n s x c h m r w b g l q v a f k p u z e j o t y d i Example Translation TREAT YIMPO SSIBL E fumnf dyvtv czysh h


 Vigenere Tableaux The distribution can be further flattened by picking complementary permutations. l Another approach: use more tables. l A Vigenere Tableaux is a collection of 26 permutations. l
Vigenere Tableaux The distribution can be further flattened by picking complementary permutations. l Another approach: use more tables. l A Vigenere Tableaux is a collection of 26 permutations. l

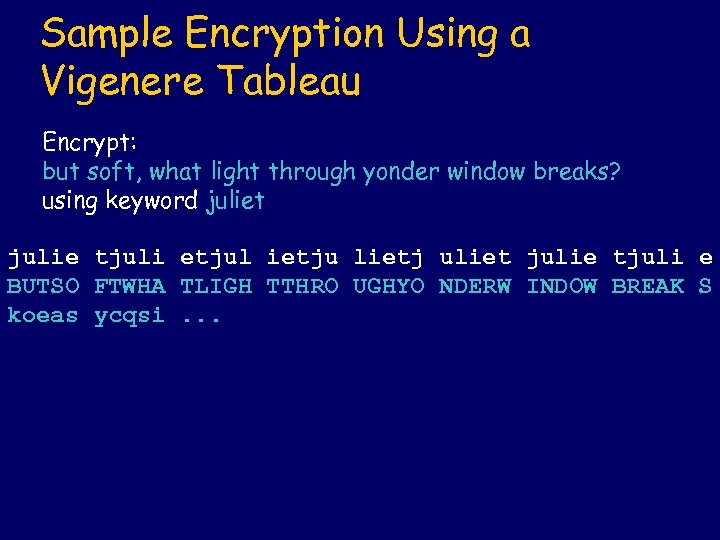 Sample Encryption Using a Vigenere Tableau Encrypt: but soft, what light through yonder window breaks? using keyword juliet julie tjuli etjul ietju lietj uliet julie tjuli e BUTSO FTWHA TLIGH TTHRO UGHYO NDERW INDOW BREAK S koeas ycqsi. . .
Sample Encryption Using a Vigenere Tableau Encrypt: but soft, what light through yonder window breaks? using keyword juliet julie tjuli etjul ietju lietj uliet julie tjuli e BUTSO FTWHA TLIGH TTHRO UGHYO NDERW INDOW BREAK S koeas ycqsi. . .
 One-Time Pad Using a Vigenere tableau with more keys than letters in the message would defeat the techniques we have discussed. l Indeed, this is an unbreakable code. l It’s disadvantage is the long keys required. l
One-Time Pad Using a Vigenere tableau with more keys than letters in the message would defeat the techniques we have discussed. l Indeed, this is an unbreakable code. l It’s disadvantage is the long keys required. l
 History of the One Time Pad l l l G. Vernam patented an idea for telegraph encryption in 1919. This was based on punched tape from a teletype. 32 alphabets were used in no regular pattern. W. Kunze, R. Schauffler, and E. Langlotz developed an approach to German diplomatic correspondence circa 1921 -1923 from which the name “one time pad” derives. Pads of 50 numbered sheets were used, with 48 five-digit groups on each. No sheets were used twice; they were destroyed after use.
History of the One Time Pad l l l G. Vernam patented an idea for telegraph encryption in 1919. This was based on punched tape from a teletype. 32 alphabets were used in no regular pattern. W. Kunze, R. Schauffler, and E. Langlotz developed an approach to German diplomatic correspondence circa 1921 -1923 from which the name “one time pad” derives. Pads of 50 numbered sheets were used, with 48 five-digit groups on each. No sheets were used twice; they were destroyed after use.
 Binary Vernam Cipher
Binary Vernam Cipher
 Long Random Sequences Middle digits from numbers in a phone book l Book of prose? Danger: frequency analysis possible! l
Long Random Sequences Middle digits from numbers in a phone book l Book of prose? Danger: frequency analysis possible! l
 Pseudo-random number generators l Linear congruential random number generator Ø Seed r(0), constants a, b, n Ø r(i+1) = (a * r(i) + b) mod n l Probable Word Attack Ø Solve a family of equations
Pseudo-random number generators l Linear congruential random number generator Ø Seed r(0), constants a, b, n Ø r(i+1) = (a * r(i) + b) mod n l Probable Word Attack Ø Solve a family of equations
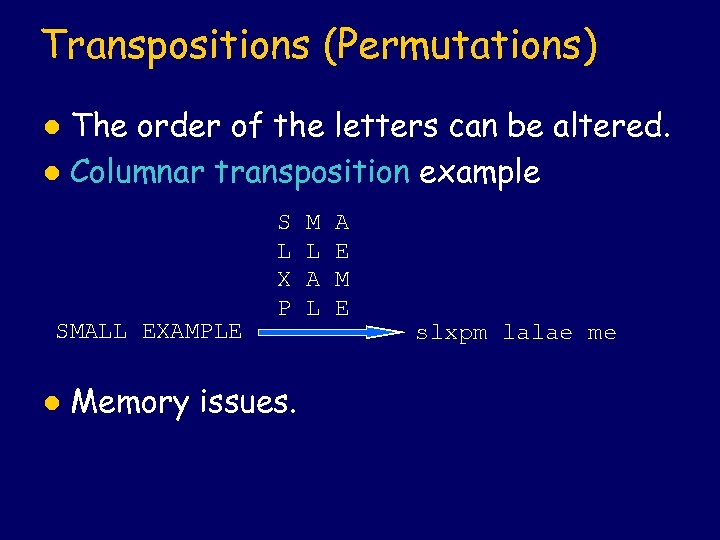 Transpositions (Permutations) The order of the letters can be altered. l Columnar transposition example l SMALL EXAMPLE l S L X P Memory issues. M L A E M E slxpm lalae me
Transpositions (Permutations) The order of the letters can be altered. l Columnar transposition example l SMALL EXAMPLE l S L X P Memory issues. M L A E M E slxpm lalae me
 Larger Example THIS IS A MESSAGE TO SHOW A COLUMNAR TRANSPOSITION WORKS This is encoded using 5 columns and 10 rows. T S S O H O A N I W H A A S O L R S T O I M G H W U T P I R S E E O A M R O O K I S T W C N A S N S
Larger Example THIS IS A MESSAGE TO SHOW A COLUMNAR TRANSPOSITION WORKS This is encoded using 5 columns and 10 rows. T S S O H O A N I W H A A S O L R S T O I M G H W U T P I R S E E O A M R O O K I S T W C N A S N S
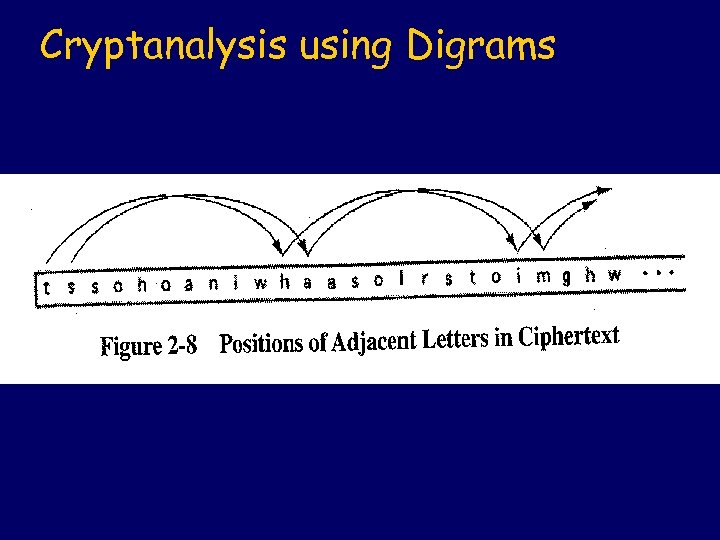 Cryptanalysis using Digrams
Cryptanalysis using Digrams


 How Many Columns?
How Many Columns?

 Other Encryption Ideas Open code. l Stegonagraphy. l Fractionated Morse Code. l Foreign languages. l Ø 1918 eight Choctaws in Company D, 141 st Infantry. Ø 50, 000 Navaho speakers in WWII. Ø Only 18 non-Navahos could speak it.
Other Encryption Ideas Open code. l Stegonagraphy. l Fractionated Morse Code. l Foreign languages. l Ø 1918 eight Choctaws in Company D, 141 st Infantry. Ø 50, 000 Navaho speakers in WWII. Ø Only 18 non-Navahos could speak it.
 Stream and Block Ciphers l Stream ciphers convert one symbol of plaintext immediately into a symbol of ciphertext. Ø Polyalphabetic substitution cipher, and Ø Fractionated Morse, but Ø Not columnar transposition.
Stream and Block Ciphers l Stream ciphers convert one symbol of plaintext immediately into a symbol of ciphertext. Ø Polyalphabetic substitution cipher, and Ø Fractionated Morse, but Ø Not columnar transposition.
 Advantages and Disadvantages l Advantages Ø Speed Ø Low l error propogation Disadvantages Ø Low diffusion Ø Susceptibility to attacks on integrity
Advantages and Disadvantages l Advantages Ø Speed Ø Low l error propogation Disadvantages Ø Low diffusion Ø Susceptibility to attacks on integrity
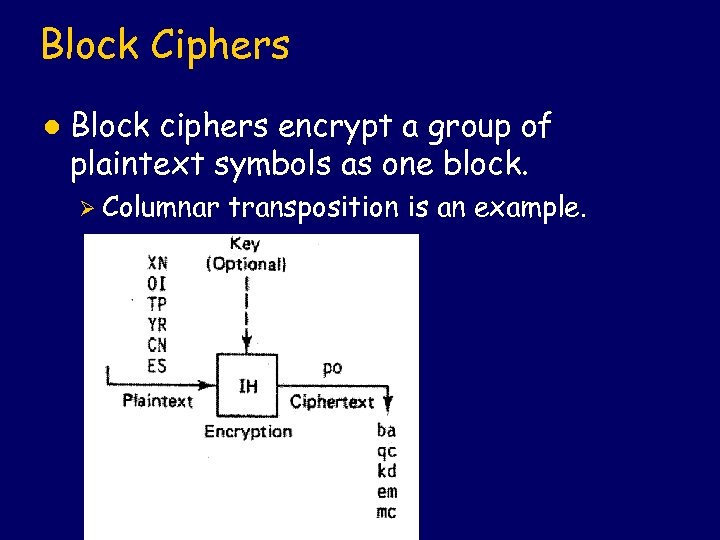 Block Ciphers l Block ciphers encrypt a group of plaintext symbols as one block. Ø Columnar transposition is an example.
Block Ciphers l Block ciphers encrypt a group of plaintext symbols as one block. Ø Columnar transposition is an example.
 Advantages and Disadvantages l Advantages Ø Diffusion Ø Immunity l to insertions Disadvantages Ø Slowness Ø Error propogation
Advantages and Disadvantages l Advantages Ø Diffusion Ø Immunity l to insertions Disadvantages Ø Slowness Ø Error propogation
 Confusion and Diffusion Confusion: difficulty in determining how a change in the plaintext will affect the ciphertext. l Diffusion: spreading of the effect of a change in the plaintext to many parts of the ciphertext. l
Confusion and Diffusion Confusion: difficulty in determining how a change in the plaintext will affect the ciphertext. l Diffusion: spreading of the effect of a change in the plaintext to many parts of the ciphertext. l
 Attacks on Encryption Ciphertext only l Known (or probable) plaintext l Chosen plaintext l Ø Chosen l sample of encrypted plaintext Adaptive chosen plaintext Ø Ability to gain new chosen samples of encrypted plaintext based on existing samples l Chosen or adaptive chosen ciphertext Ø Temporary access to decryption
Attacks on Encryption Ciphertext only l Known (or probable) plaintext l Chosen plaintext l Ø Chosen l sample of encrypted plaintext Adaptive chosen plaintext Ø Ability to gain new chosen samples of encrypted plaintext based on existing samples l Chosen or adaptive chosen ciphertext Ø Temporary access to decryption
 Encryption with a Key (Revision) l Symmetric key ØC = E(K, P) Ø P = D(K, C) Ø P = D(K, E(K, P)) l Asymetric key ØC = E(Kpublic, P) Ø P = D(Kprivate, C) Ø P = D(Kprivate, E(Kpublic, P))
Encryption with a Key (Revision) l Symmetric key ØC = E(K, P) Ø P = D(K, C) Ø P = D(K, E(K, P)) l Asymetric key ØC = E(Kpublic, P) Ø P = D(Kprivate, C) Ø P = D(Kprivate, E(Kpublic, P))
 Definitions Trusted Third Party (TTP) l Unconditionally trusted TTP must be trusted completely l Functionally trusted TTP must be trusted for availability and integrity. l
Definitions Trusted Third Party (TTP) l Unconditionally trusted TTP must be trusted completely l Functionally trusted TTP must be trusted for availability and integrity. l


 Advantages of Symmetric Efficient encryption l Relatively short keys l Useful as primitives for various functions (pseudorandom number generators, hash functions, etc. ) l Good composition properties l Extensive history l
Advantages of Symmetric Efficient encryption l Relatively short keys l Useful as primitives for various functions (pseudorandom number generators, hash functions, etc. ) l Good composition properties l Extensive history l
 Disadvantages of Symmetric Key must remain secret at both ends. l Many key pairs must be managed in a large network. May require unconditionally trusted TTP. l Keys must be changed frequently. l Large keys or TTP required for public verification function of digital signatures. l
Disadvantages of Symmetric Key must remain secret at both ends. l Many key pairs must be managed in a large network. May require unconditionally trusted TTP. l Keys must be changed frequently. l Large keys or TTP required for public verification function of digital signatures. l
 Advantages of Asymmetric Only the private key must be kept secret. l Key management requires only a functionally trusted TTP. l Long-lived keys. l Efficient digital signatures with relatively small keys for public verification function. l
Advantages of Asymmetric Only the private key must be kept secret. l Key management requires only a functionally trusted TTP. l Long-lived keys. l Efficient digital signatures with relatively small keys for public verification function. l
 Disadvantage of Asymmetric Lower throughput for encryption. l Large key sizes. l Security based on presumed complexity of a small collection of numbertheoretic problems. l Limited history. l
Disadvantage of Asymmetric Lower throughput for encryption. l Large key sizes. l Security based on presumed complexity of a small collection of numbertheoretic problems. l Limited history. l
 Roundup Comparison Asymmetric (public) key cryptography facilitates efficient digital signatures and key management. l Symmetric (shared secret) key cryptography provides efficient encryption. l
Roundup Comparison Asymmetric (public) key cryptography facilitates efficient digital signatures and key management. l Symmetric (shared secret) key cryptography provides efficient encryption. l
 Complementary Use l Use public keys to help establish symmetric key for encrypted session.
Complementary Use l Use public keys to help establish symmetric key for encrypted session.
 Modern Cryptography Diffie Hellman l RSA l Hash algorithms l DES l Clipper key escrow l Modes of operation l Digital signatures l
Modern Cryptography Diffie Hellman l RSA l Hash algorithms l DES l Clipper key escrow l Modes of operation l Digital signatures l
 Public Key Cryptography Some number theory. l Diffie-Hellman key exchange. l Some more number theory. l RSA public keys. l
Public Key Cryptography Some number theory. l Diffie-Hellman key exchange. l Some more number theory. l RSA public keys. l
 Establishing a Shared Secret Suppose Alice has an authenticated channel for communicating with Bob. l Alice and Bob wish to use this channel to established a shared secret. l However, Eve is able to learn everything sent over the channel. l If Alice and Bob have no other channel to use, can they establish a shared secret that Eve does not know? l
Establishing a Shared Secret Suppose Alice has an authenticated channel for communicating with Bob. l Alice and Bob wish to use this channel to established a shared secret. l However, Eve is able to learn everything sent over the channel. l If Alice and Bob have no other channel to use, can they establish a shared secret that Eve does not know? l
 General Strategy Alice and Bob exchange information, each keeping a secret to themselves. l The secrets that they keep allow them to compute a shared secret. l Since Eve lacks either of these secrets she is unable to compute the shared secret. l
General Strategy Alice and Bob exchange information, each keeping a secret to themselves. l The secrets that they keep allow them to compute a shared secret. l Since Eve lacks either of these secrets she is unable to compute the shared secret. l
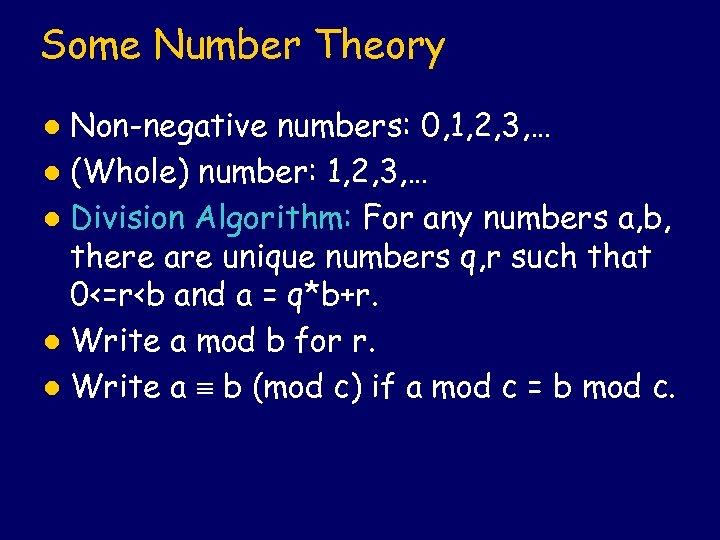 Some Number Theory Non-negative numbers: 0, 1, 2, 3, … l (Whole) number: 1, 2, 3, … l Division Algorithm: For any numbers a, b, there are unique numbers q, r such that 0<=r
Some Number Theory Non-negative numbers: 0, 1, 2, 3, … l (Whole) number: 1, 2, 3, … l Division Algorithm: For any numbers a, b, there are unique numbers q, r such that 0<=r
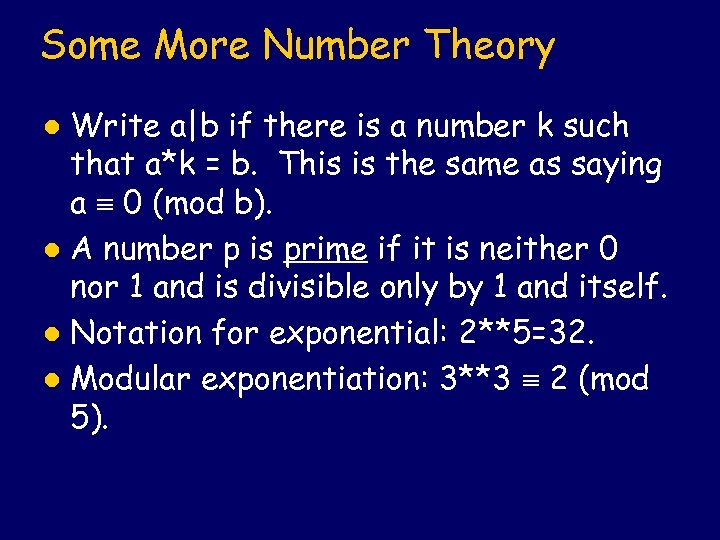 Some More Number Theory Write a|b if there is a number k such that a*k = b. This is the same as saying a 0 (mod b). l A number p is prime if it is neither 0 nor 1 and is divisible only by 1 and itself. l Notation for exponential: 2**5=32. l Modular exponentiation: 3**3 2 (mod 5). l
Some More Number Theory Write a|b if there is a number k such that a*k = b. This is the same as saying a 0 (mod b). l A number p is prime if it is neither 0 nor 1 and is divisible only by 1 and itself. l Notation for exponential: 2**5=32. l Modular exponentiation: 3**3 2 (mod 5). l
 Primitive Roots A primitive root of a prime p is a number such that { **1 mod p, …, **(p-1) mod p} = {1, …, p-1}. l Example: 2 is not a primitive root of 7, but 3 is a primitive root of 7. l
Primitive Roots A primitive root of a prime p is a number such that { **1 mod p, …, **(p-1) mod p} = {1, …, p-1}. l Example: 2 is not a primitive root of 7, but 3 is a primitive root of 7. l
 Diffie-Hellman Key Exchange Alice and Bob agree on a shared basis. l Alice selects a private key XA < q and calculates a public key YA from it using q and . l Bob does the same to get XB and YB. l Alice and Bob exchange their public keys (which are now known to Eve), but keep their private keys. l
Diffie-Hellman Key Exchange Alice and Bob agree on a shared basis. l Alice selects a private key XA < q and calculates a public key YA from it using q and . l Bob does the same to get XB and YB. l Alice and Bob exchange their public keys (which are now known to Eve), but keep their private keys. l
 Diffie-Hellman, continued Alice knows XA, YA, and YB. l Bob knows XB, YB, and YA. l Eve knows YA and YB. l Alice combines XA with YB to get S, the shared secret. l Bob combines XB with YA to get S, the (same) shared secret. l Eve tries to get S from YA and YB, but gives up in disgust. l
Diffie-Hellman, continued Alice knows XA, YA, and YB. l Bob knows XB, YB, and YA. l Eve knows YA and YB. l Alice combines XA with YB to get S, the shared secret. l Bob combines XB with YA to get S, the (same) shared secret. l Eve tries to get S from YA and YB, but gives up in disgust. l
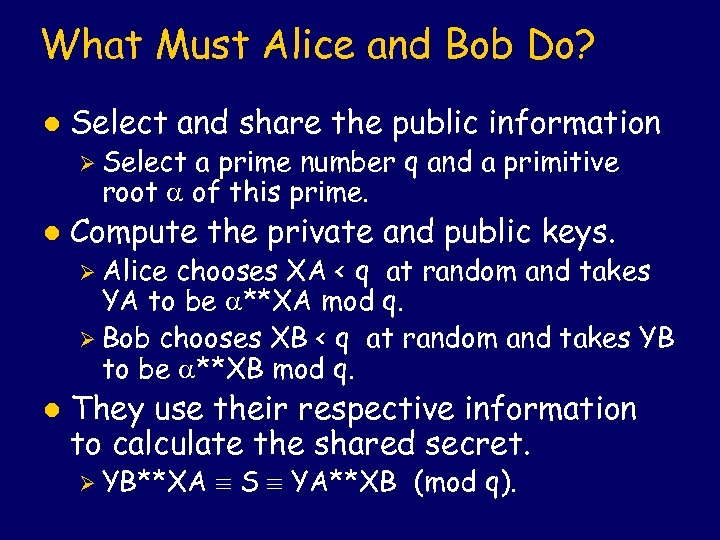 What Must Alice and Bob Do? l Select and share the public information Ø Select a prime number q and a primitive root of this prime. l Compute the private and public keys. Ø Alice chooses XA < q at random and takes YA to be **XA mod q. Ø Bob chooses XB < q at random and takes YB to be **XB mod q. l They use their respective information to calculate the shared secret. Ø YB**XA S YA**XB (mod q).
What Must Alice and Bob Do? l Select and share the public information Ø Select a prime number q and a primitive root of this prime. l Compute the private and public keys. Ø Alice chooses XA < q at random and takes YA to be **XA mod q. Ø Bob chooses XB < q at random and takes YB to be **XB mod q. l They use their respective information to calculate the shared secret. Ø YB**XA S YA**XB (mod q).
 Realization of the Approach What must not be possible: use the public information and public keys to compute the shared secret. l Strategy: calculations by Alice and Bob involve modular exponentiation. The obvious calculation by Eve involves discrete logarithms. l
Realization of the Approach What must not be possible: use the public information and public keys to compute the shared secret. l Strategy: calculations by Alice and Bob involve modular exponentiation. The obvious calculation by Eve involves discrete logarithms. l
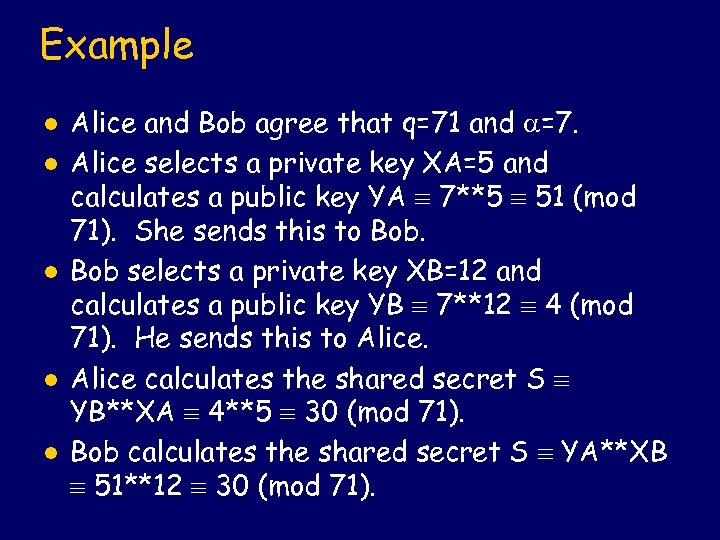 Example l l l Alice and Bob agree that q=71 and =7. Alice selects a private key XA=5 and calculates a public key YA 7**5 51 (mod 71). She sends this to Bob selects a private key XB=12 and calculates a public key YB 7**12 4 (mod 71). He sends this to Alice calculates the shared secret S YB**XA 4**5 30 (mod 71). Bob calculates the shared secret S YA**XB 51**12 30 (mod 71).
Example l l l Alice and Bob agree that q=71 and =7. Alice selects a private key XA=5 and calculates a public key YA 7**5 51 (mod 71). She sends this to Bob selects a private key XB=12 and calculates a public key YB 7**12 4 (mod 71). He sends this to Alice calculates the shared secret S YB**XA 4**5 30 (mod 71). Bob calculates the shared secret S YA**XB 51**12 30 (mod 71).
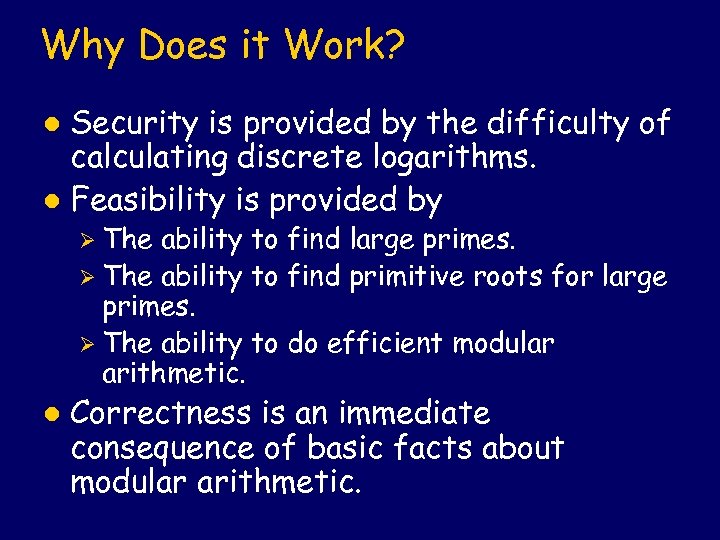 Why Does it Work? Security is provided by the difficulty of calculating discrete logarithms. l Feasibility is provided by l Ø The ability to find large primes. Ø The ability to find primitive roots for large primes. Ø The ability to do efficient modular arithmetic. l Correctness is an immediate consequence of basic facts about modular arithmetic.
Why Does it Work? Security is provided by the difficulty of calculating discrete logarithms. l Feasibility is provided by l Ø The ability to find large primes. Ø The ability to find primitive roots for large primes. Ø The ability to do efficient modular arithmetic. l Correctness is an immediate consequence of basic facts about modular arithmetic.
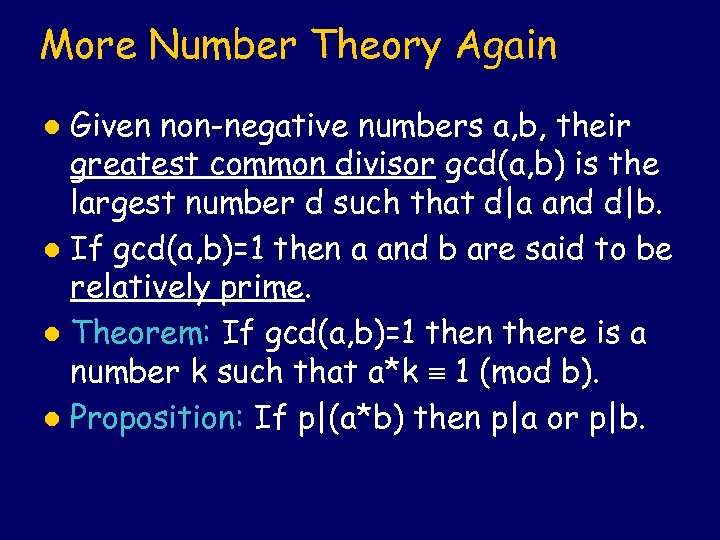 More Number Theory Again Given non-negative numbers a, b, their greatest common divisor gcd(a, b) is the largest number d such that d|a and d|b. l If gcd(a, b)=1 then a and b are said to be relatively prime. l Theorem: If gcd(a, b)=1 then there is a number k such that a*k 1 (mod b). l Proposition: If p|(a*b) then p|a or p|b. l
More Number Theory Again Given non-negative numbers a, b, their greatest common divisor gcd(a, b) is the largest number d such that d|a and d|b. l If gcd(a, b)=1 then a and b are said to be relatively prime. l Theorem: If gcd(a, b)=1 then there is a number k such that a*k 1 (mod b). l Proposition: If p|(a*b) then p|a or p|b. l
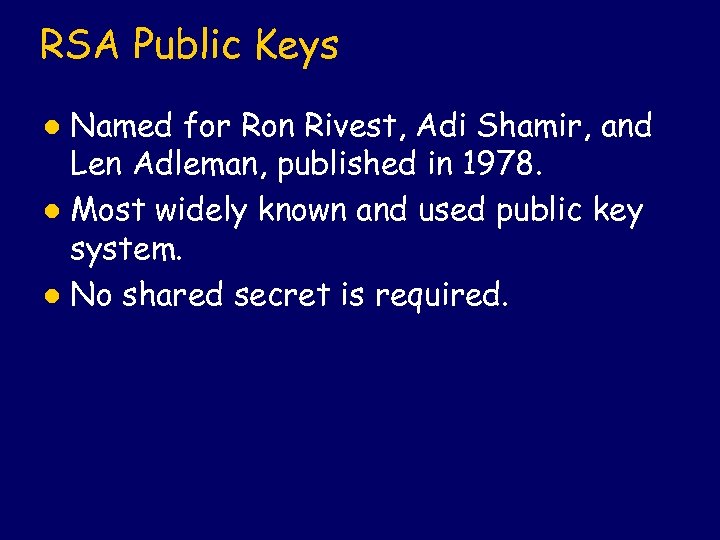 RSA Public Keys Named for Ron Rivest, Adi Shamir, and Len Adleman, published in 1978. l Most widely known and used public key system. l No shared secret is required. l
RSA Public Keys Named for Ron Rivest, Adi Shamir, and Len Adleman, published in 1978. l Most widely known and used public key system. l No shared secret is required. l
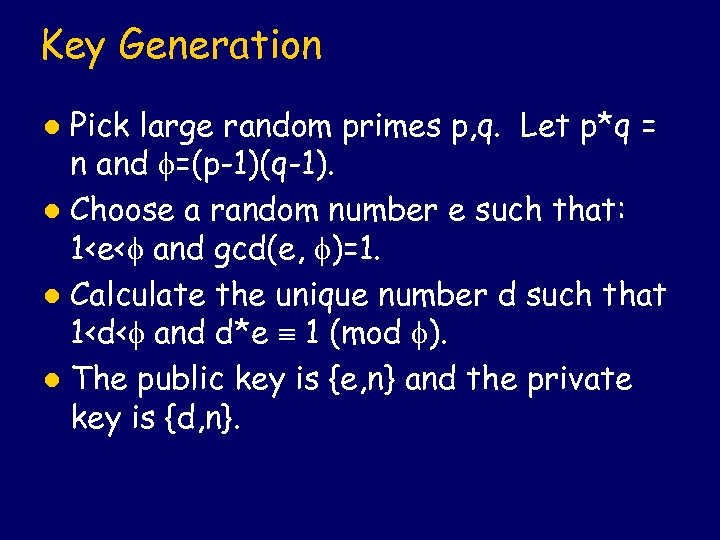 Key Generation Pick large random primes p, q. Let p*q = n and =(p-1)(q-1). l Choose a random number e such that: 1
Key Generation Pick large random primes p, q. Let p*q = n and =(p-1)(q-1). l Choose a random number e such that: 1
 Encryption and Decryption Encryption: Suppose we are given a message m represented as a number such that 1<=m
Encryption and Decryption Encryption: Suppose we are given a message m represented as a number such that 1<=m
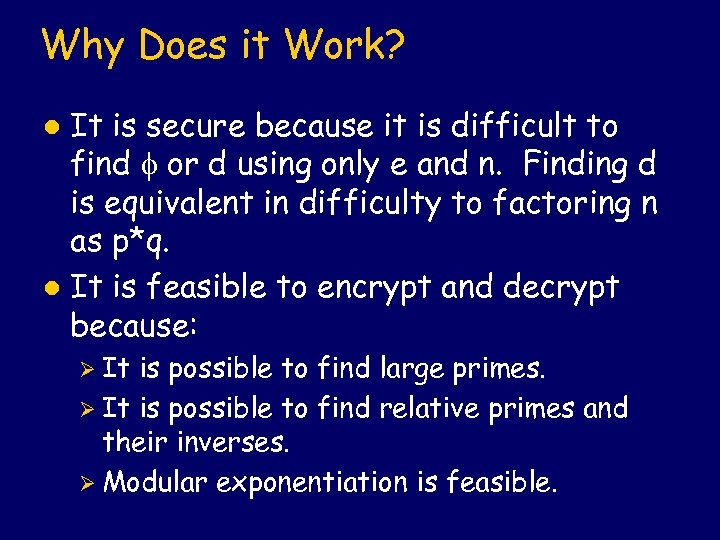 Why Does it Work? It is secure because it is difficult to find or d using only e and n. Finding d is equivalent in difficulty to factoring n as p*q. l It is feasible to encrypt and decrypt because: l Ø It is possible to find large primes. Ø It is possible to find relative primes and their inverses. Ø Modular exponentiation is feasible.
Why Does it Work? It is secure because it is difficult to find or d using only e and n. Finding d is equivalent in difficulty to factoring n as p*q. l It is feasible to encrypt and decrypt because: l Ø It is possible to find large primes. Ø It is possible to find relative primes and their inverses. Ø Modular exponentiation is feasible.
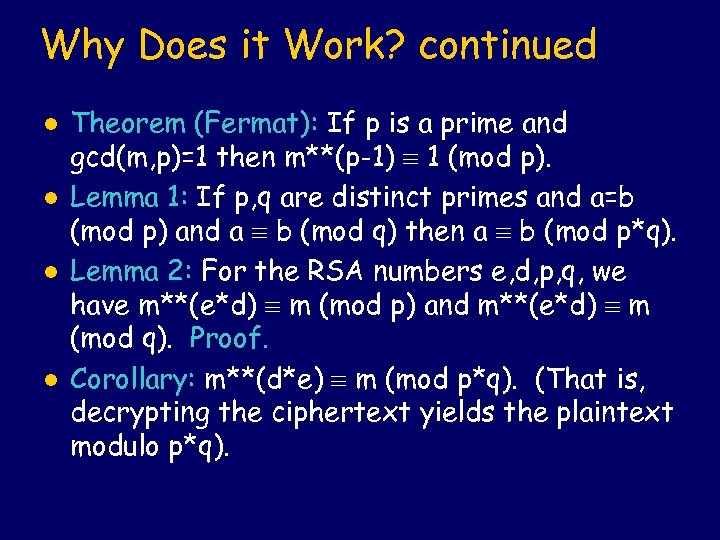 Why Does it Work? continued l l Theorem (Fermat): If p is a prime and gcd(m, p)=1 then m**(p-1) 1 (mod p). Lemma 1: If p, q are distinct primes and a=b (mod p) and a b (mod q) then a b (mod p*q). Lemma 2: For the RSA numbers e, d, p, q, we have m**(e*d) m (mod p) and m**(e*d) m (mod q). Proof. Corollary: m**(d*e) m (mod p*q). (That is, decrypting the ciphertext yields the plaintext modulo p*q).
Why Does it Work? continued l l Theorem (Fermat): If p is a prime and gcd(m, p)=1 then m**(p-1) 1 (mod p). Lemma 1: If p, q are distinct primes and a=b (mod p) and a b (mod q) then a b (mod p*q). Lemma 2: For the RSA numbers e, d, p, q, we have m**(e*d) m (mod p) and m**(e*d) m (mod q). Proof. Corollary: m**(d*e) m (mod p*q). (That is, decrypting the ciphertext yields the plaintext modulo p*q).
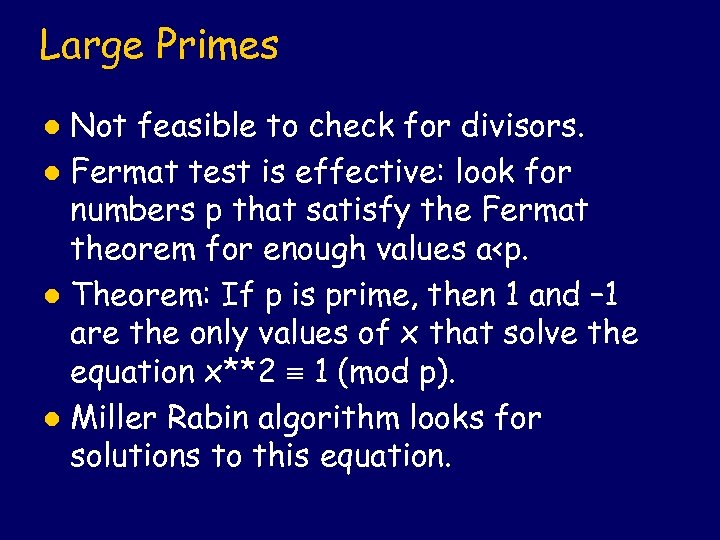 Large Primes Not feasible to check for divisors. l Fermat test is effective: look for numbers p that satisfy the Fermat theorem for enough values a
Large Primes Not feasible to check for divisors. l Fermat test is effective: look for numbers p that satisfy the Fermat theorem for enough values a
 Euclid’s Algorithm l l Finding relative primes cannot be done by enumerating all divisors. Euclid’s Algorithm: If a, b are non-negative numbers and b>0, then gcd(a, b)=gcd(b, a mod b). Since a mod b is less than a, this terminates if repeatedly applied. It also terminates quickly. Extended Euclid Algorithm keeps some additional information so that if the result is 1, then the additional information includes the inverse of a.
Euclid’s Algorithm l l Finding relative primes cannot be done by enumerating all divisors. Euclid’s Algorithm: If a, b are non-negative numbers and b>0, then gcd(a, b)=gcd(b, a mod b). Since a mod b is less than a, this terminates if repeatedly applied. It also terminates quickly. Extended Euclid Algorithm keeps some additional information so that if the result is 1, then the additional information includes the inverse of a.
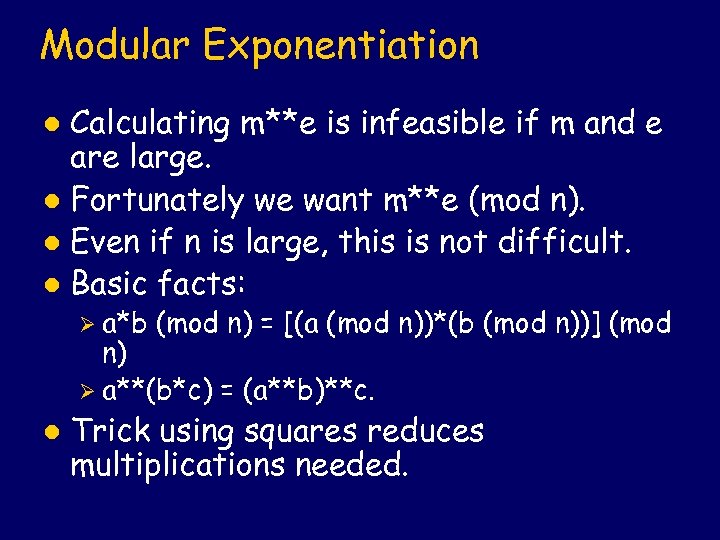 Modular Exponentiation Calculating m**e is infeasible if m and e are large. l Fortunately we want m**e (mod n). l Even if n is large, this is not difficult. l Basic facts: l Ø a*b (mod n) = [(a (mod n))*(b (mod n))] (mod n) Ø a**(b*c) = (a**b)**c. l Trick using squares reduces multiplications needed.
Modular Exponentiation Calculating m**e is infeasible if m and e are large. l Fortunately we want m**e (mod n). l Even if n is large, this is not difficult. l Basic facts: l Ø a*b (mod n) = [(a (mod n))*(b (mod n))] (mod n) Ø a**(b*c) = (a**b)**c. l Trick using squares reduces multiplications needed.
 Hash Algorithms Reduce a message of variable size to a small digest of fixed size. l The probability that a randomly chosen message maps to an n-bit hash should ideally be 2**-n. l Example: The NIST Secure Hash Algorithm takes a message of less than 2**64 bits and produces a digest of 160 bits. l
Hash Algorithms Reduce a message of variable size to a small digest of fixed size. l The probability that a randomly chosen message maps to an n-bit hash should ideally be 2**-n. l Example: The NIST Secure Hash Algorithm takes a message of less than 2**64 bits and produces a digest of 160 bits. l
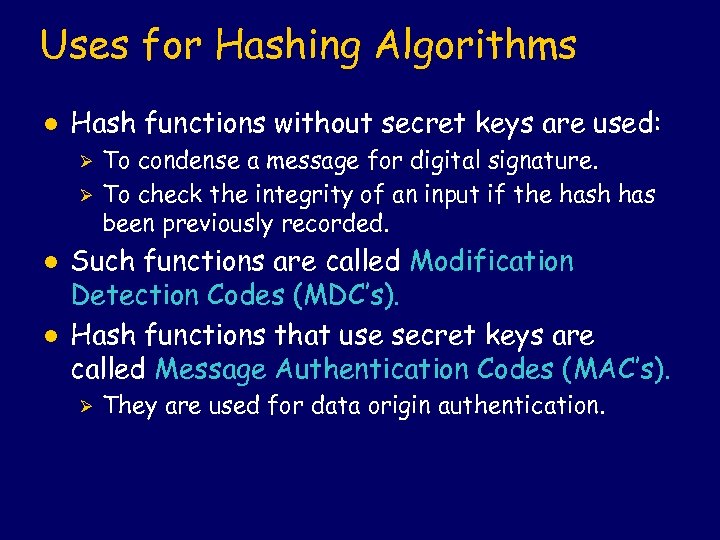 Uses for Hashing Algorithms l Hash functions without secret keys are used: Ø Ø l l To condense a message for digital signature. To check the integrity of an input if the hash has been previously recorded. Such functions are called Modification Detection Codes (MDC’s). Hash functions that use secret keys are called Message Authentication Codes (MAC’s). Ø They are used for data origin authentication.
Uses for Hashing Algorithms l Hash functions without secret keys are used: Ø Ø l l To condense a message for digital signature. To check the integrity of an input if the hash has been previously recorded. Such functions are called Modification Detection Codes (MDC’s). Hash functions that use secret keys are called Message Authentication Codes (MAC’s). Ø They are used for data origin authentication.
 Properties of MDC’s l Hash functions h for cryptographic use as MDC’s fall in one or both of the following classes. Ø Collision Resistant Hash Function (CRHF): It should be computationally infeasible to find two distinct inputs that hash to a common value ( i. e. . h(x) = h(y) ). Ø One Way Hash Function (OWHF): Given a specific hash value y, it should be computationally infeasible to find an input x such that h(x)=y.
Properties of MDC’s l Hash functions h for cryptographic use as MDC’s fall in one or both of the following classes. Ø Collision Resistant Hash Function (CRHF): It should be computationally infeasible to find two distinct inputs that hash to a common value ( i. e. . h(x) = h(y) ). Ø One Way Hash Function (OWHF): Given a specific hash value y, it should be computationally infeasible to find an input x such that h(x)=y.
 Secure Hash Algorithm Pad message so it can be divided into 512 -bit blocks, including a 64 bit value giving the length of the original message. l Process each block as 16 32 -bit words called W(t) for t from 0 to 15. l Expand from these 16 words to 80 words by defining as follows for each t from 16 to 79: l Ø W(t) : = W(t-3) W(t-8) W(t-14) W(t-16)
Secure Hash Algorithm Pad message so it can be divided into 512 -bit blocks, including a 64 bit value giving the length of the original message. l Process each block as 16 32 -bit words called W(t) for t from 0 to 15. l Expand from these 16 words to 80 words by defining as follows for each t from 16 to 79: l Ø W(t) : = W(t-3) W(t-8) W(t-14) W(t-16)
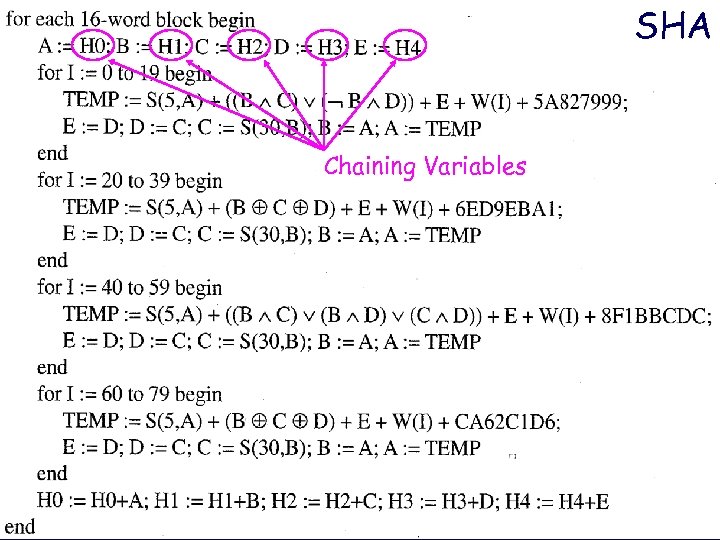 SHA Chaining Variables
SHA Chaining Variables
 NBS Requirements for DES l l l l l Provide a high level of security. Completely specified and easy to understand. Security must not depend on secrecy of the algorithm. Available to all users. Adaptable for diverse applications. Economical to implement in electronic devices. Efficient to use. Able to be validated. Exportable.
NBS Requirements for DES l l l l l Provide a high level of security. Completely specified and easy to understand. Security must not depend on secrecy of the algorithm. Available to all users. Adaptable for diverse applications. Economical to implement in electronic devices. Efficient to use. Able to be validated. Exportable.
 DES History Based on Lucifer algorithm of IBM. l Algorithm developed by IBM for NBS became known as the Digital Encryption Standard. l Assistance provided by NSA. l Official name in the US: Data Encryption Algorithm (DEA). l Official name internationally: Data Encryption Algorithm-1 (DEA-1). l
DES History Based on Lucifer algorithm of IBM. l Algorithm developed by IBM for NBS became known as the Digital Encryption Standard. l Assistance provided by NSA. l Official name in the US: Data Encryption Algorithm (DEA). l Official name internationally: Data Encryption Algorithm-1 (DEA-1). l
 DES Algorithm l Based on product of substitution and permutation ciphers applied in rounds.
DES Algorithm l Based on product of substitution and permutation ciphers applied in rounds.
 DES Characterized Substitution-Permutation (SP) Network l Iterated block cipher: sequential repetition of round function l Feistel cipher: iterated cipher on halved inputs combined at each round in a specific way l
DES Characterized Substitution-Permutation (SP) Network l Iterated block cipher: sequential repetition of round function l Feistel cipher: iterated cipher on halved inputs combined at each round in a specific way l
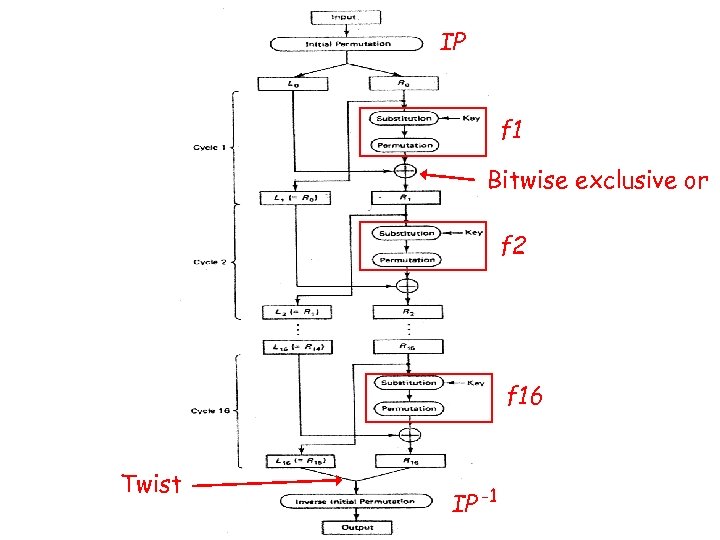 IP f 1 Bitwise exclusive or f 2 f 16 Twist IP -1
IP f 1 Bitwise exclusive or f 2 f 16 Twist IP -1
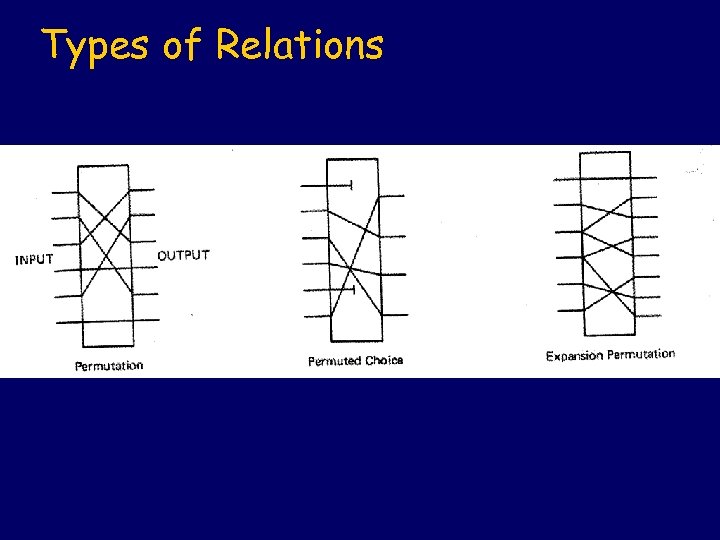 Types of Relations
Types of Relations
 Summary 64 bit keys with each 8 th bit designated as a parity bit, thus 56 significant bits l Rotations and choice permutations on original key are used to create 16 subkeys K(I), each 48 bits l f(I)(R(I-1)) = g(R(I-1), K(I)) l g(R(I-1), K(I)) = P( S(E(R(I-1)) K(I)) ) l E is an expansion permutation, S is a substitution, and P is a permutation l
Summary 64 bit keys with each 8 th bit designated as a parity bit, thus 56 significant bits l Rotations and choice permutations on original key are used to create 16 subkeys K(I), each 48 bits l f(I)(R(I-1)) = g(R(I-1), K(I)) l g(R(I-1), K(I)) = P( S(E(R(I-1)) K(I)) ) l E is an expansion permutation, S is a substitution, and P is a permutation l
 Subkeys Start with the 56 significant bits of the key, divide into two 28 bit halves. l Apply left circular shift to each half using the following table to indicate how much to shift l
Subkeys Start with the 56 significant bits of the key, divide into two 28 bit halves. l Apply left circular shift to each half using the following table to indicate how much to shift l
 Subkeys continued l After the shifts, concatenate the two 28 bit vectors and use the following table to select 48 of these bits
Subkeys continued l After the shifts, concatenate the two 28 bit vectors and use the following table to select 48 of these bits
 Expansion Permutation E l E is applied to 32 bit vector R(I-1) to obtain a 48 bit vector. It is defined by the following table
Expansion Permutation E l E is applied to 32 bit vector R(I-1) to obtain a 48 bit vector. It is defined by the following table
 “S Box” Substitutions S l S is applied to the result of exclusive or combination of the expansion of R(I-1) and the subkey K(I). It is essentially a substitution cipher on 6 bit words, mapping them to 4 bit words, defined by the table on the slide after next.
“S Box” Substitutions S l S is applied to the result of exclusive or combination of the expansion of R(I-1) and the subkey K(I). It is essentially a substitution cipher on 6 bit words, mapping them to 4 bit words, defined by the table on the slide after next.
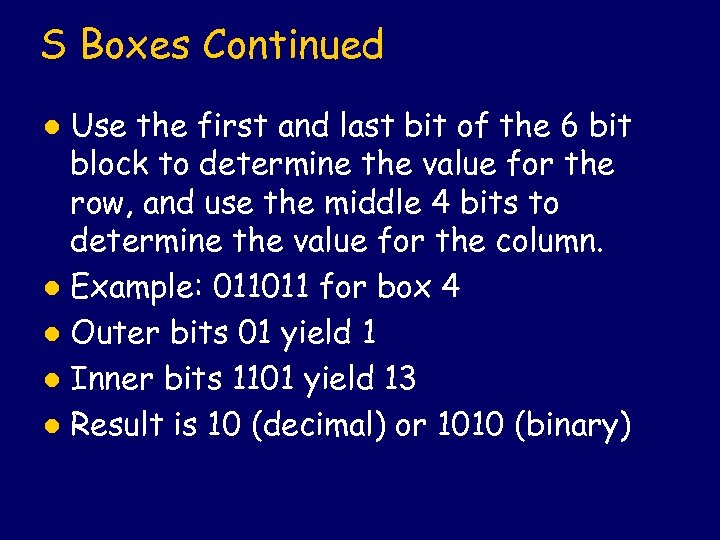 S Boxes Continued Use the first and last bit of the 6 bit block to determine the value for the row, and use the middle 4 bits to determine the value for the column. l Example: 011011 for box 4 l Outer bits 01 yield 1 l Inner bits 1101 yield 13 l Result is 10 (decimal) or 1010 (binary) l
S Boxes Continued Use the first and last bit of the 6 bit block to determine the value for the row, and use the middle 4 bits to determine the value for the column. l Example: 011011 for box 4 l Outer bits 01 yield 1 l Inner bits 1101 yield 13 l Result is 10 (decimal) or 1010 (binary) l

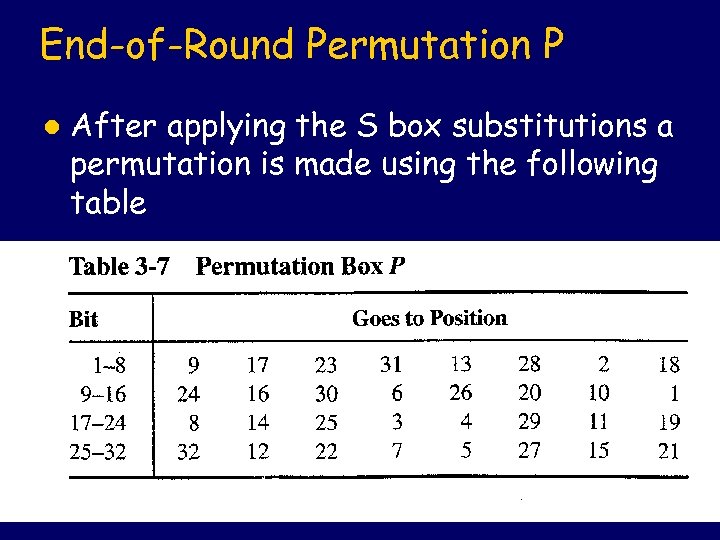 End-of-Round Permutation P l After applying the S box substitutions a permutation is made using the following table
End-of-Round Permutation P l After applying the S box substitutions a permutation is made using the following table
 R(I-1) 32 K(I) E 48 48 48 8 x 6 bits 6 S 1 S 2 S 3 S 4 S 5 S 6 S 7 S 8 Substitutions 4 8 x 4 bits 32 P 32 g(R(I-1), K(I)) = P(S(E(R(I-1)) K(I)))
R(I-1) 32 K(I) E 48 48 48 8 x 6 bits 6 S 1 S 2 S 3 S 4 S 5 S 6 S 7 S 8 Substitutions 4 8 x 4 bits 32 P 32 g(R(I-1), K(I)) = P(S(E(R(I-1)) K(I)))
 Final Permutation IP Inverse
Final Permutation IP Inverse
 DES Properties l l Each bit of the ciphertext depends on all bits of the key and all bits of the plaintext. There is no statistical relationship evident between plaintext and ciphertext. Altering any single plaintext or key bit alters each ciphertext bit with probability 1/2. Altering a ciphertext bit results in an unpredictable change to the recovered plaintext.
DES Properties l l Each bit of the ciphertext depends on all bits of the key and all bits of the plaintext. There is no statistical relationship evident between plaintext and ciphertext. Altering any single plaintext or key bit alters each ciphertext bit with probability 1/2. Altering a ciphertext bit results in an unpredictable change to the recovered plaintext.
 Weak and Semi-Weak Keys l l l A weak key is a key K such that E(K, x)) = x for all x. That is, E(K, -) is an involution. DES has 4 weak keys. A pair of DES keys K and L is semi-weak if E(K, E(L, x)) = x. That is, encryption for K acts like decryption for L. DES has 6 semi-weak key pairs. These arise when the subkeys K(1) to K(16) correspond to L(16) to L(1).
Weak and Semi-Weak Keys l l l A weak key is a key K such that E(K, x)) = x for all x. That is, E(K, -) is an involution. DES has 4 weak keys. A pair of DES keys K and L is semi-weak if E(K, E(L, x)) = x. That is, encryption for K acts like decryption for L. DES has 6 semi-weak key pairs. These arise when the subkeys K(1) to K(16) correspond to L(16) to L(1).
 (Value before initial permutation)
(Value before initial permutation)
 Security and Law Enforcement Wire taps by law enforcement agencies are allowed when approved by court. l Can a wire tap succeed against a triple. DES encoded conversation? l Aims of key escrow: l Ø Provide strong symmetric key security Ø Provide for wire taps on encrypted communications.
Security and Law Enforcement Wire taps by law enforcement agencies are allowed when approved by court. l Can a wire tap succeed against a triple. DES encoded conversation? l Aims of key escrow: l Ø Provide strong symmetric key security Ø Provide for wire taps on encrypted communications.
 Key Escrow
Key Escrow
 NSA Clipper Program Key split into two parts, held by two government agencies. l Law enforcement officials with good cause can obtain a court order and get the two key halves. l Encryption algorithm classified. NSA to provide only hardware embodiments of the algorithm. l
NSA Clipper Program Key split into two parts, held by two government agencies. l Law enforcement officials with good cause can obtain a court order and get the two key halves. l Encryption algorithm classified. NSA to provide only hardware embodiments of the algorithm. l
 Keys and Fields Skipjack algorithm: 80 bit keys encrypting 64 bit blocks in 32 rounds. l D(K, E(K, M)) = M as usual l Law Enforcement Agents’ Field (LEAF): E(f, E(u, k)&n&a)) where l Øf is an 80 -bit key for Clipper chips Ø n is a 30 -bit identifier for the unit Ø a is an escrow authenticator Ø u is an 80 -bit unit-specific key Ø k is an 80 -bit session key
Keys and Fields Skipjack algorithm: 80 bit keys encrypting 64 bit blocks in 32 rounds. l D(K, E(K, M)) = M as usual l Law Enforcement Agents’ Field (LEAF): E(f, E(u, k)&n&a)) where l Øf is an 80 -bit key for Clipper chips Ø n is a 30 -bit identifier for the unit Ø a is an escrow authenticator Ø u is an 80 -bit unit-specific key Ø k is an 80 -bit session key
 Clipper Message Fields
Clipper Message Fields
 Who Knows What l Known to law enforcement agencies: Ø The l Split between two government agencies: Ø The l key f. key u. Indexed by each agency Ø The identifier n.
Who Knows What l Known to law enforcement agencies: Ø The l Split between two government agencies: Ø The l key f. key u. Indexed by each agency Ø The identifier n.
 “Wire Tapping” Protocol Intercept communication l Determine that encoding uses Clipper l Decrypt E(f, E(u, k)&n&a)) to get n l Deliver n and court order to escrow agencies l Get the two halves of u l Use u to decrypt E(u, k) to get k l Use k to decrypt session l
“Wire Tapping” Protocol Intercept communication l Determine that encoding uses Clipper l Decrypt E(f, E(u, k)&n&a)) to get n l Deliver n and court order to escrow agencies l Get the two halves of u l Use u to decrypt E(u, k) to get k l Use k to decrypt session l
 Capstone Clipper chip: implements encryption and appending of LEAF. l Capstone cryptographic device: performs basic algorithm together with key exchange, hashing, and digital signature authentication. l Capstone also known as Tessera. Clipper program also known as Mosaic. l
Capstone Clipper chip: implements encryption and appending of LEAF. l Capstone cryptographic device: performs basic algorithm together with key exchange, hashing, and digital signature authentication. l Capstone also known as Tessera. Clipper program also known as Mosaic. l
 Panel Conclusions about Clipper There is no significant risk that Skipjack will be broken by exhaustive search in the next 30 to 40 years. l There is no significant risk that Skipjack will be broken through a shortcut method of attack. l The strength of Skipjack encryption does not depend on the secrecy of the algorithm. l
Panel Conclusions about Clipper There is no significant risk that Skipjack will be broken by exhaustive search in the next 30 to 40 years. l There is no significant risk that Skipjack will be broken through a shortcut method of attack. l The strength of Skipjack encryption does not depend on the secrecy of the algorithm. l
 Revision on Cryptography l Public (Asymmetric) Key Systems Ø Diffie-Hellman Ø RSA l Hash Functions (Collision Resistant, One Way) Ø SHA-1 l Secret (Symmetric) Key Systems Ø DES
Revision on Cryptography l Public (Asymmetric) Key Systems Ø Diffie-Hellman Ø RSA l Hash Functions (Collision Resistant, One Way) Ø SHA-1 l Secret (Symmetric) Key Systems Ø DES
 Modes of Operation Electronic codebook (ECB) mode. l Chain block chain (CBC) mode. l Cipher feedback (CFB) mode. l Output feedback (OFB) mode. l For details, see 7. 2. 2 in: Handbook of Applied Cryptography, AJ Menezes, PC van Ooschot, and SA Vanstone, 1996. l
Modes of Operation Electronic codebook (ECB) mode. l Chain block chain (CBC) mode. l Cipher feedback (CFB) mode. l Output feedback (OFB) mode. l For details, see 7. 2. 2 in: Handbook of Applied Cryptography, AJ Menezes, PC van Ooschot, and SA Vanstone, 1996. l
 Electronic Codebook (ECB) Encrypt each block individually l Properties l Ø Identical plaintext blocks yield identical ciphertext. Ø Order matters, but each successive block can be enciphered without regard to previous blocks Ø Bit errors affect only the block in which they occur.
Electronic Codebook (ECB) Encrypt each block individually l Properties l Ø Identical plaintext blocks yield identical ciphertext. Ø Order matters, but each successive block can be enciphered without regard to previous blocks Ø Bit errors affect only the block in which they occur.
 ECB Figure
ECB Figure
 Block Replay
Block Replay
 Cipher Block Chaining (CBC) Take an exclusive or of each plaintext block with the previous ciphertext block before encrypting. l Properties l Ø Depends on initialization vector (IV). Ø Ciphertext depends on all previous plaintext blocks. Ø Bit errors in ciphertext propagate to two blocks. (“Self-synchronizing. ”)
Cipher Block Chaining (CBC) Take an exclusive or of each plaintext block with the previous ciphertext block before encrypting. l Properties l Ø Depends on initialization vector (IV). Ø Ciphertext depends on all previous plaintext blocks. Ø Bit errors in ciphertext propagate to two blocks. (“Self-synchronizing. ”)
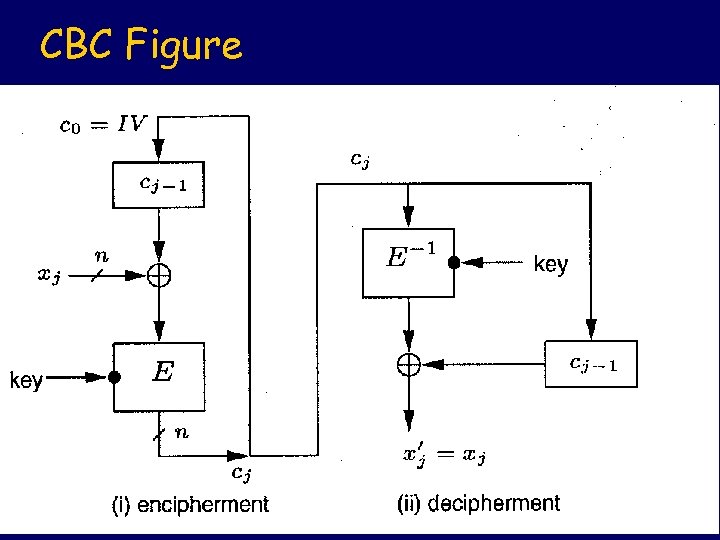 CBC Figure
CBC Figure
 Cipher Feedback (CFB) Encrypt blocks to produce encrypted plaintext of shorter length by using a shift register. l Properties l Ø Depends on initialization vector (IV). Ø Ciphertext depends on all previous plaintext blocks. Ø Self-synchronizing: bit errors in ciphertext propagate to a limited number of blocks.
Cipher Feedback (CFB) Encrypt blocks to produce encrypted plaintext of shorter length by using a shift register. l Properties l Ø Depends on initialization vector (IV). Ø Ciphertext depends on all previous plaintext blocks. Ø Self-synchronizing: bit errors in ciphertext propagate to a limited number of blocks.
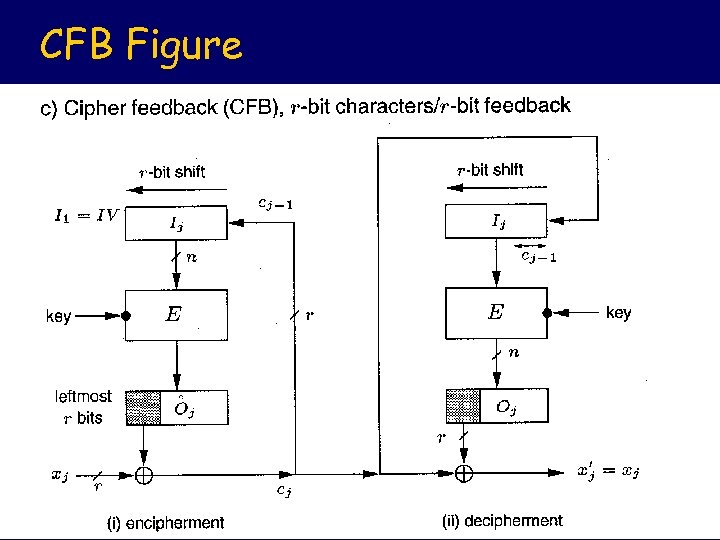 CFB Figure
CFB Figure
 Output Feedback (OFB) Like CFB, but not using the enciphered text in creating the key stream. l Properties l Ø Like CFB, but the key stream is independent of the input plaintext and can therefore be pre-computed.
Output Feedback (OFB) Like CFB, but not using the enciphered text in creating the key stream. l Properties l Ø Like CFB, but the key stream is independent of the input plaintext and can therefore be pre-computed.
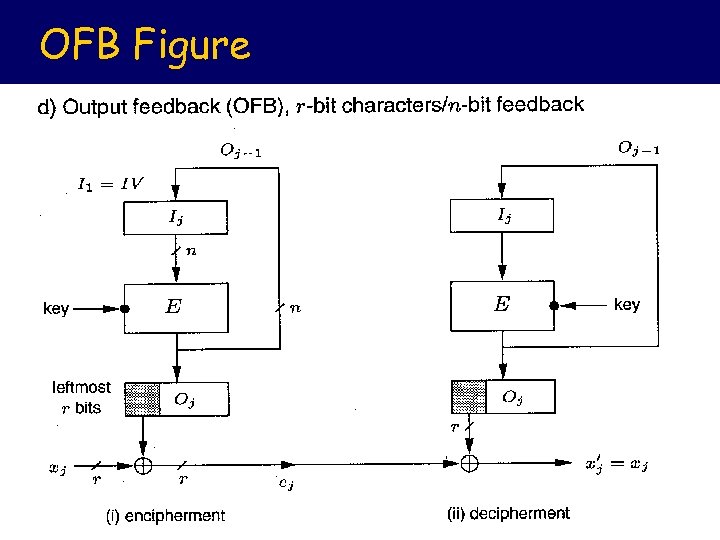 OFB Figure
OFB Figure
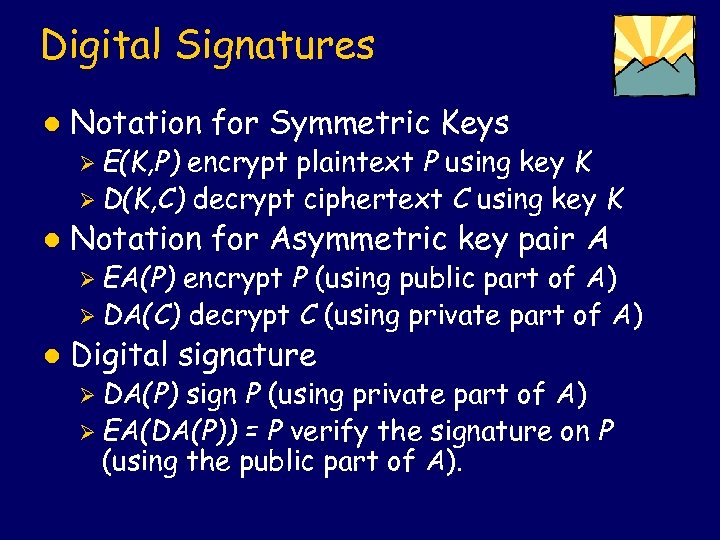 Digital Signatures l Notation for Symmetric Keys Ø E(K, P) encrypt plaintext P using key K Ø D(K, C) decrypt ciphertext C using key K l Notation for Asymmetric key pair A Ø EA(P) encrypt P (using public part of A) Ø DA(C) decrypt C (using private part of A) l Digital signature Ø DA(P) sign P (using private part of A) Ø EA(DA(P)) = P verify the signature on P (using the public part of A).
Digital Signatures l Notation for Symmetric Keys Ø E(K, P) encrypt plaintext P using key K Ø D(K, C) decrypt ciphertext C using key K l Notation for Asymmetric key pair A Ø EA(P) encrypt P (using public part of A) Ø DA(C) decrypt C (using private part of A) l Digital signature Ø DA(P) sign P (using private part of A) Ø EA(DA(P)) = P verify the signature on P (using the public part of A).
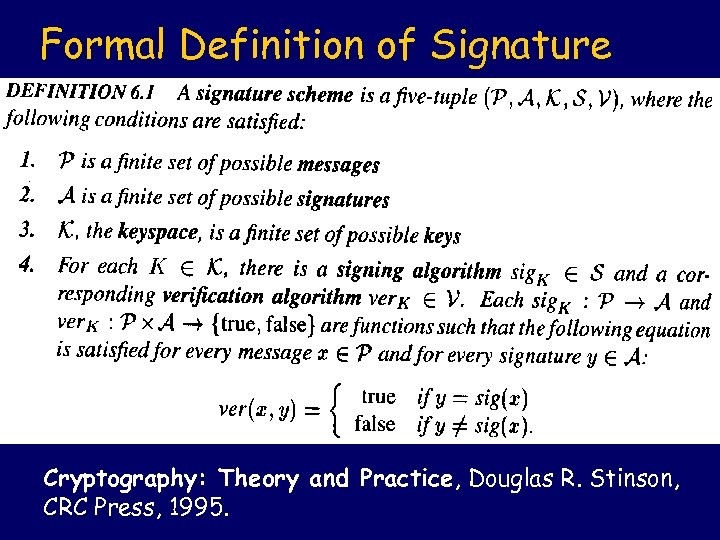 Formal Definition of Signature Cryptography: Theory and Practice, Douglas R. Stinson, CRC Press, 1995.
Formal Definition of Signature Cryptography: Theory and Practice, Douglas R. Stinson, CRC Press, 1995.

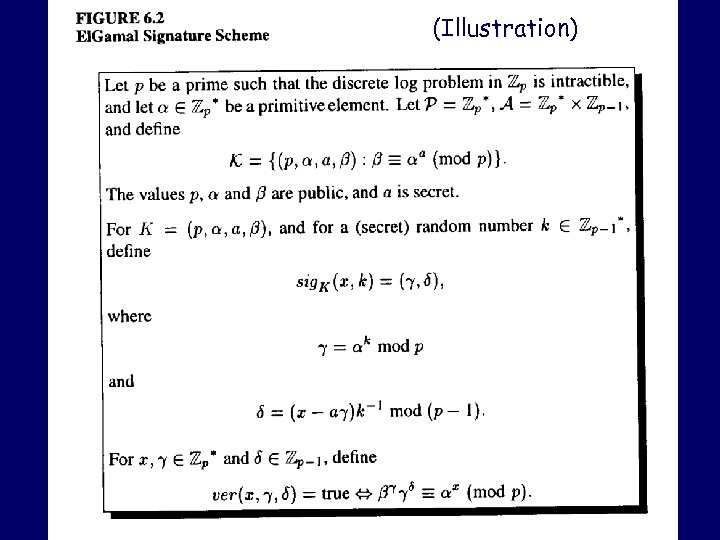 (Illustration)
(Illustration)
 (Illustration)
(Illustration)
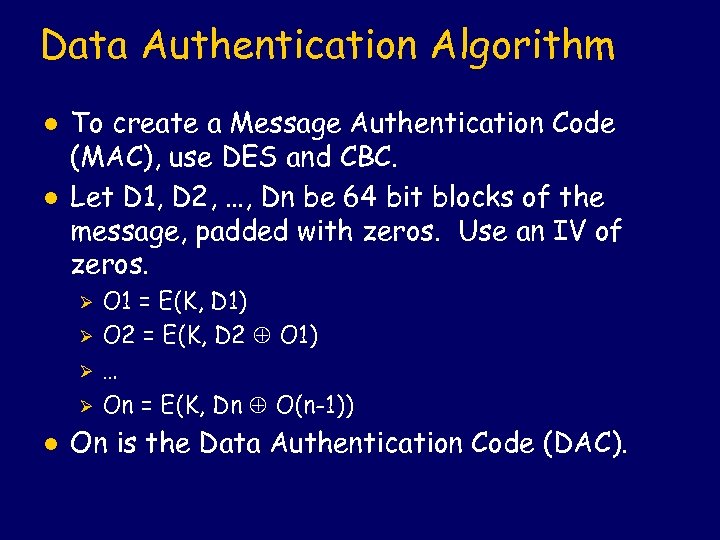 Data Authentication Algorithm l l To create a Message Authentication Code (MAC), use DES and CBC. Let D 1, D 2, …, Dn be 64 bit blocks of the message, padded with zeros. Use an IV of zeros. Ø Ø l O 1 = E(K, D 1) O 2 = E(K, D 2 O 1) … On = E(K, Dn O(n-1)) On is the Data Authentication Code (DAC).
Data Authentication Algorithm l l To create a Message Authentication Code (MAC), use DES and CBC. Let D 1, D 2, …, Dn be 64 bit blocks of the message, padded with zeros. Use an IV of zeros. Ø Ø l O 1 = E(K, D 1) O 2 = E(K, D 2 O 1) … On = E(K, Dn O(n-1)) On is the Data Authentication Code (DAC).
 Internet MAC Modular use of cryptographic hash function for MAC. l Use existing kinds of hash functions. l Avoid significant degradation in performance of hashing. l Well-understood cryptographic analysis. l
Internet MAC Modular use of cryptographic hash function for MAC. l Use existing kinds of hash functions. l Avoid significant degradation in performance of hashing. l Well-understood cryptographic analysis. l
 HMAC Cryptographic hash function H. l Key K, expanded to K+ to match block size for hash. l Pads: opad and ipad. l Message M. l O = K+ opad. l I = K+ ipad. l HMAC(K, M) = H(O || H(I || M)). l
HMAC Cryptographic hash function H. l Key K, expanded to K+ to match block size for hash. l Pads: opad and ipad. l Message M. l O = K+ opad. l I = K+ ipad. l HMAC(K, M) = H(O || H(I || M)). l


