c13c5f8ef8611773ecdc74c23733da66.ppt
- Количество слайдов: 33
CSCE 824 Secure (and Distributed) Database Management Systems Farkas CSCE 824 1
Course Aim n Advanced understanding of DBMS concepts – From relation to un- and semistructured data models – New type of applications – Security needs Farkas CSCE 824 2
Reference Materials n Recommended: – T. Ozsu and P. Valduriez, Principles of Distributed Database Systems, Springer; 3 rd Edition. edition (March 2, 2011), ISBN-10: 1441988335 – M. Gertz, S. Jajodia, Handbook of database security: applications and trend, Springer 2008 – Online materials Farkas CSCE 824 3
Conference Proceedings and Journals n n n Farkas Proceedings of Secure Data Management Workshop, links: 2012 http: //www. hitech-projects. com/sdmworkshop/sdm 12. html , 2011 http: //www. hitechprojects. com/sdm-workshop/sdm 11. html Proceedings of IFIP WG 11. 3 Data and Application Security and Privacy, links: 2012 http: //conferences. telecom-bretagne. eu/dbsec 2012/ , 2011 http: //www. egr. vcu. edu/dbsec 2011/ Proceedings of International Conference of Very Large Databases (VLDB), links: 2012 http: //www. vldb 2012. org/ , 2011 http: //www. vldb. org/2011/ CSCE 824 4
Journals and Books IEEE Transactions on Knowledge and Data Engineering (TKDE) n ACM Transactions on Information and System Security (TISSEC) n M. Gertz, S. Jajodia, Handbook of database security: applications and trend, Springer 2008 n Farkas CSCE 824 5
Challenge n n n Farkas Research project: there will be one group research project. Students must present the related work and their results to the class in the last lectures of the semester. Homework assignments. There will be several homework exercises and reading for the lectures. Tests: there will be two tests covering the course materials. Both tests are open book, in-class tests. CSCE 824 6
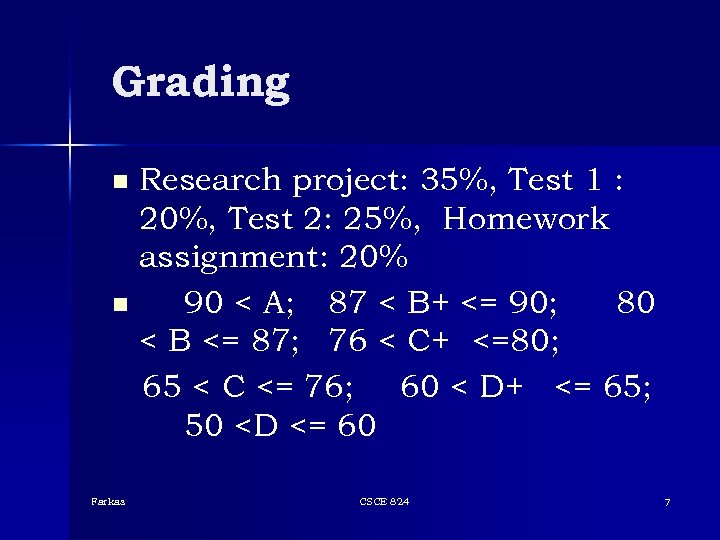
Grading Research project: 35%, Test 1 : 20%, Test 2: 25%, Homework assignment: 20% n 90 < A; 87 < B+ <= 90; 80 < B <= 87; 76 < C+ <=80; 65 < C <= 76; 60 < D+ <= 65; 50 <D <= 60 n Farkas CSCE 824 7
Topics Covered Weeks 1 -5: Distributed and Nontraditional Databases n Weeks 6 -11: Database Security n Weeks 12 -15: Student Presentations n Farkas CSCE 824 8
• Students’ Introduction Name Major Interest in class Farkas CSCE 824 9
Information Assurance Studies CSCE 727 - Farkas 10
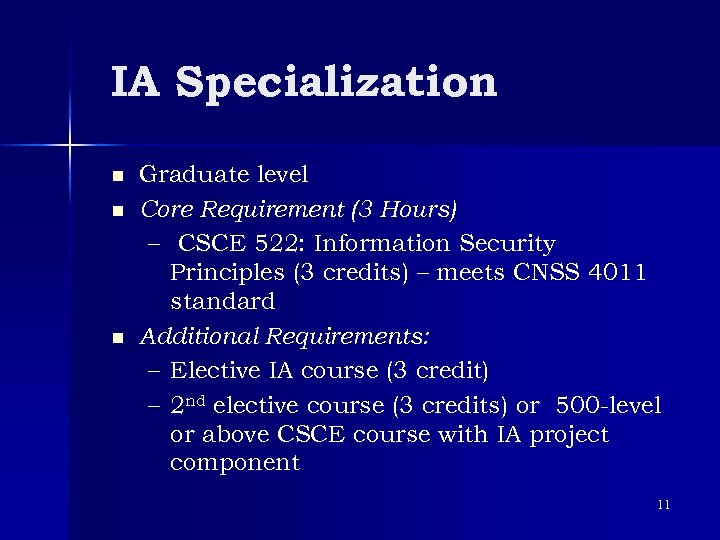
IA Specialization n Graduate level Core Requirement (3 Hours) – CSCE 522: Information Security Principles (3 credits) – meets CNSS 4011 standard Additional Requirements: – Elective IA course (3 credit) – 2 nd elective course (3 credits) or 500 -level or above CSCE course with IA project component 11
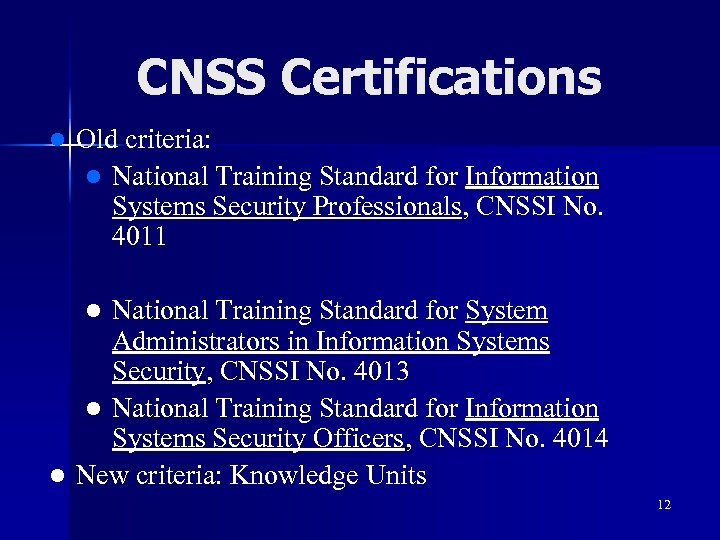
CNSS Certifications l Old criteria: l National Training Standard for Information Systems Security Professionals, CNSSI No. 4011 National Training Standard for System Administrators in Information Systems Security, CNSSI No. 4013 l National Training Standard for Information Systems Security Officers, CNSSI No. 4014 l New criteria: Knowledge Units l 12
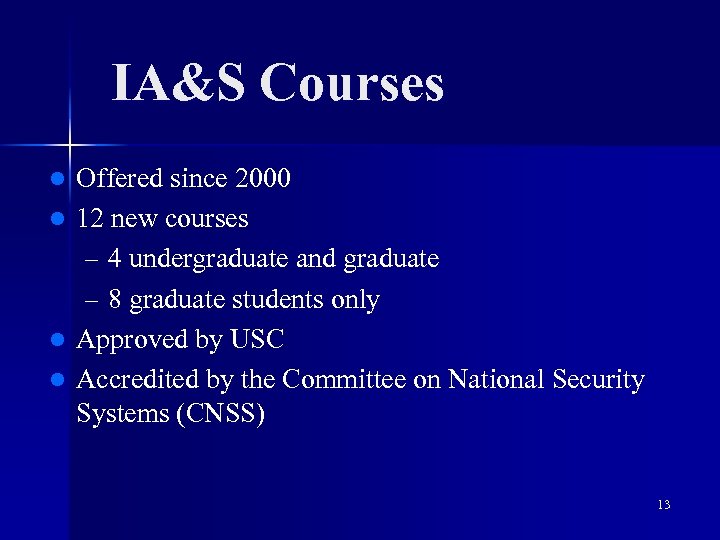
IA&S Courses Offered since 2000 l 12 new courses – 4 undergraduate and graduate – 8 graduate students only l Approved by USC l Accredited by the Committee on National Security Systems (CNSS) l 13

IA&S Certificate Program http: //www. cse. sc. edu/isl/education/iaands (modifications are approved, starting Fall 2016) 14
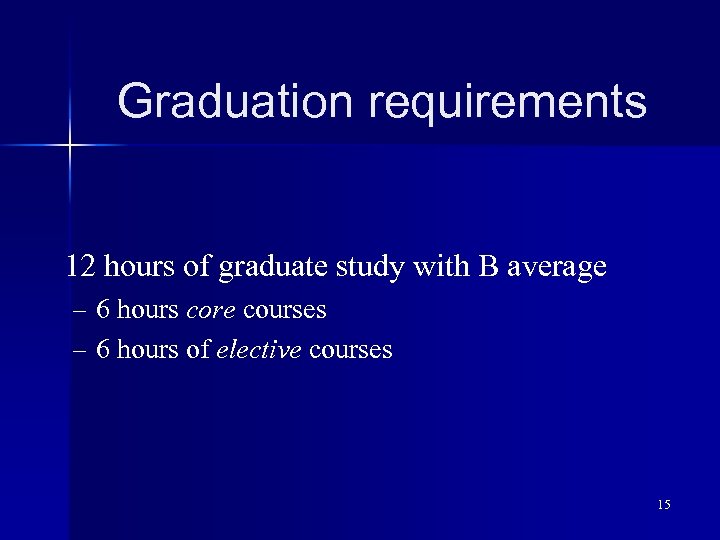
Graduation requirements 12 hours of graduate study with B average – 6 hours core courses – 6 hours of elective courses 15
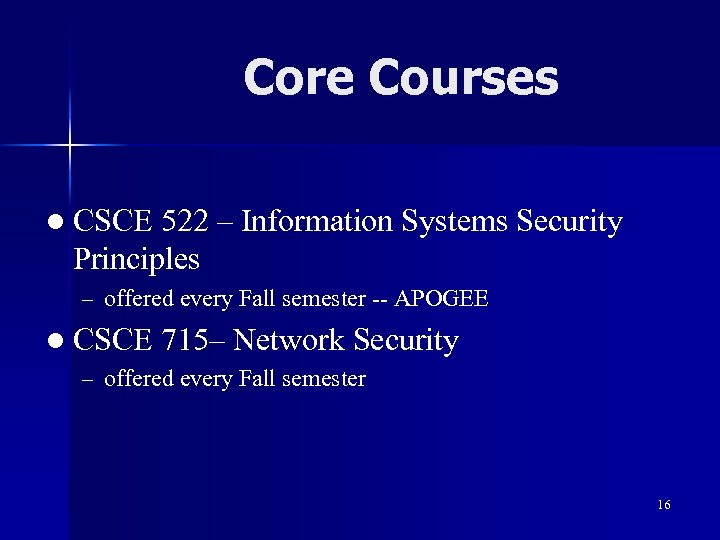
Core Courses l CSCE 522 – Information Systems Security Principles – offered every Fall semester -- APOGEE l CSCE 715– Network Security – offered every Fall semester 16
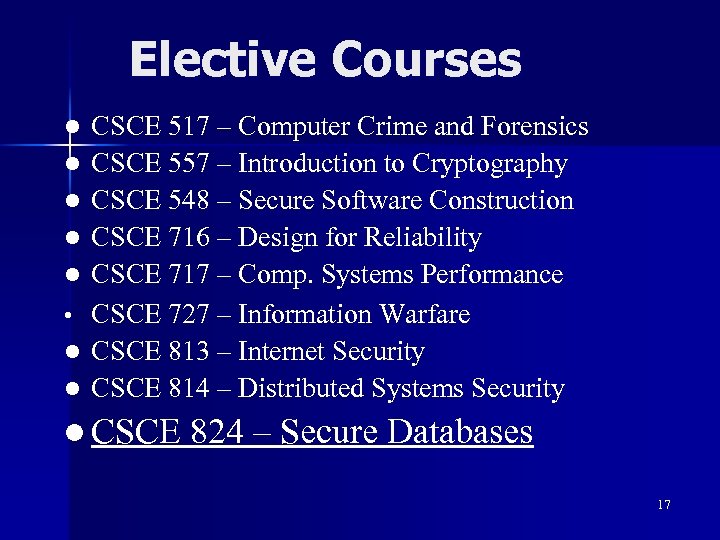
Elective Courses l l l • l l CSCE 517 – Computer Crime and Forensics CSCE 557 – Introduction to Cryptography CSCE 548 – Secure Software Construction CSCE 716 – Design for Reliability CSCE 717 – Comp. Systems Performance CSCE 727 – Information Warfare CSCE 813 – Internet Security CSCE 814 – Distributed Systems Security l CSCE 824 – Secure Databases 17
Center for Information Assurance Engineering (CIAE) http: //www. cse. sc. edu/isl n Information about: n – Research – Education – Publications – People – Useful links 18
Questions? Farkas CSCE 824 19
Database Management System (DBMS) n Collection of – interrelated data and – set of programs to access the data Convenient and efficient processing of data n Database Application Software n Farkas CSCE 824 20
Evolution of Database Systems n n Farkas Early days: customized applications built on top of file systems Drawbacks of using file systems to store data: – Data redundancy and inconsistency – Difficulty in accessing data – Atomicity of updates – Concurrency control – Security – Data isolation — multiple files and formats – Integrity problems CSCE 824 21
Abstraction n View level: different perspectives – Application programs hide irrelevant data n Logical level: data models – Logical representation of data – Different approaches: hierarchical, network, object oriented, semi-structured, etc. – Data independence principle n Farkas Physical level: how data is stored CSCE 824 22
Data Models n A collection of tools for describing – Data – Relationships among data items – Semantics of stored data – Database constraints Farkas CSCE 824 23
Database Management Systems n Smaller and smaller systems – Past: large and expensive DBMS – Present: DBMS in most personal computers n More and more data stored – BIG DATA – Past: few MB – Present: terabyte (1012 bytes), petabyte (1015 bytes) n n Farkas Functionality: from physical to view level Optimization CSCE 824 24
Data Definition Language (DDL) Defines the database schema and constraints n DDL compiler data dictionary n Metadata – data about data n Farkas CSCE 824 25
Data Manipulation Language (DML) n n Accessing and manipulating the data Query Languages – Procedural – user specifies what data is required and how to get those data – Nonprocedural – user specifies what data is required without specifying how to get those data Farkas CSCE 824 26
Current Demands Efficient data processing of large data sets n Long running transactions n Real-time demand n Usability for specific applications n … n Farkas CSCE 824 27

Data Security
Security Objectives n n n Farkas Confidentiality: prevent/detect/deter improper disclosure of information Integrity: prevent/detect/deter improper modification of information Availability: prevent/detect/deter improper denial of access to services CSCE 824 29
Security Threats Poor design n Insufficient quality control n Accidents n Attacks n Farkas CSCE 824 30
Achieving Security n Policy – What to protect? n Mechanism – How to protect? n Assurance – How good is the protection? Farkas CSCE 824 31
Database Security Policy n Access control models n Inference control n Integrity protection n Privacy problems n Fault tolerance and recovery n Auditing and intrusion detection n TOOLS n Farkas CSCE 824 32
Next Class Relational data model Farkas CSCE 824 33
c13c5f8ef8611773ecdc74c23733da66.ppt