9a1d4bd8d4025a21db466afab169b426.ppt
- Количество слайдов: 26
 CSCE 715: Network Systems Security Chin-Tser Huang huangct@cse. sc. edu University of South Carolina 9/12/2006
CSCE 715: Network Systems Security Chin-Tser Huang huangct@cse. sc. edu University of South Carolina 9/12/2006
 AES Cipher – Rijndael n n Process data as 4 groups of 4 bytes (State) Has 9/11/13 rounds in which state undergoes: n n n byte substitution (1 S-box used on every byte) shift rows (permute bytes between groups/columns) mix columns (subs using matrix multiply of groups) add round key (XOR state with key material) Initial XOR key material & incomplete last round All operations can be combined into XOR and table lookups, hence very fast and efficient 9/12/2006 2
AES Cipher – Rijndael n n Process data as 4 groups of 4 bytes (State) Has 9/11/13 rounds in which state undergoes: n n n byte substitution (1 S-box used on every byte) shift rows (permute bytes between groups/columns) mix columns (subs using matrix multiply of groups) add round key (XOR state with key material) Initial XOR key material & incomplete last round All operations can be combined into XOR and table lookups, hence very fast and efficient 9/12/2006 2
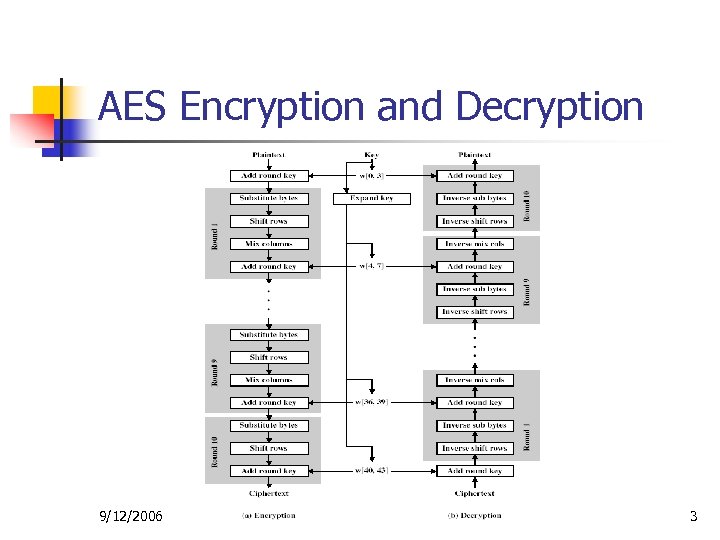 AES Encryption and Decryption 9/12/2006 3
AES Encryption and Decryption 9/12/2006 3
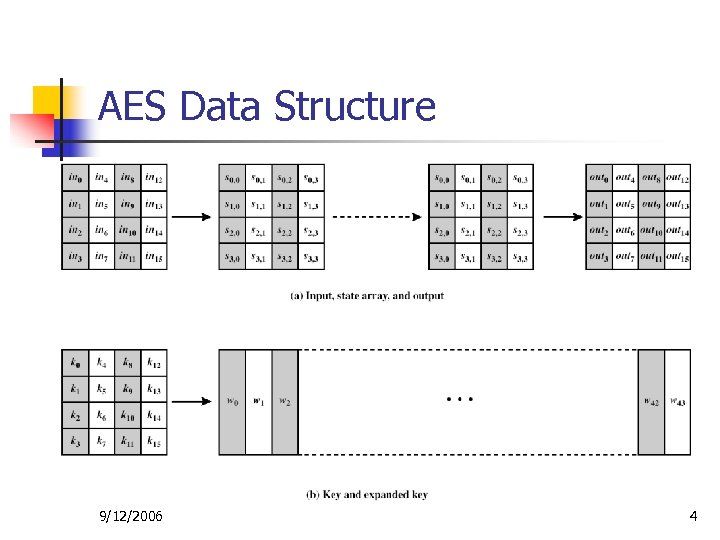 AES Data Structure 9/12/2006 4
AES Data Structure 9/12/2006 4
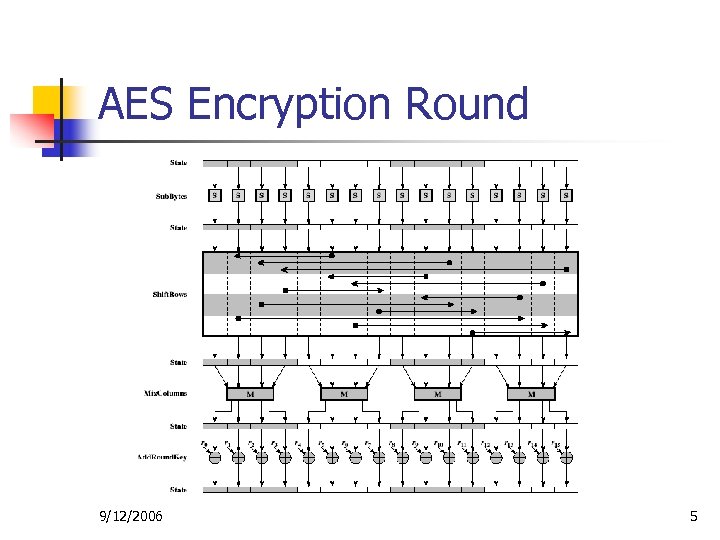 AES Encryption Round 9/12/2006 5
AES Encryption Round 9/12/2006 5
 Byte Substitution n A simple substitution of each byte Uses one table of 16 x 16 bytes containing a permutation of all 256 8 -bit values Each byte of state is replaced by byte in corresponding row (left 4 bits) and column (right 4 bits) n n eg. byte {95} is replaced by row 9 col 5 byte, which is {2 A} S-box is constructed using a defined transformation of the values in GF(28) 9/12/2006 6
Byte Substitution n A simple substitution of each byte Uses one table of 16 x 16 bytes containing a permutation of all 256 8 -bit values Each byte of state is replaced by byte in corresponding row (left 4 bits) and column (right 4 bits) n n eg. byte {95} is replaced by row 9 col 5 byte, which is {2 A} S-box is constructed using a defined transformation of the values in GF(28) 9/12/2006 6
 Shift Rows n Circular byte shift in each row n n n 1 st row is unchanged 2 nd row does 1 byte circular shift to left 3 rd row does 2 byte circular shift to left 4 th row does 3 byte circular shift to left Decryption does shifts to right Since state is processed by columns, this step permutes bytes between the columns 9/12/2006 7
Shift Rows n Circular byte shift in each row n n n 1 st row is unchanged 2 nd row does 1 byte circular shift to left 3 rd row does 2 byte circular shift to left 4 th row does 3 byte circular shift to left Decryption does shifts to right Since state is processed by columns, this step permutes bytes between the columns 9/12/2006 7
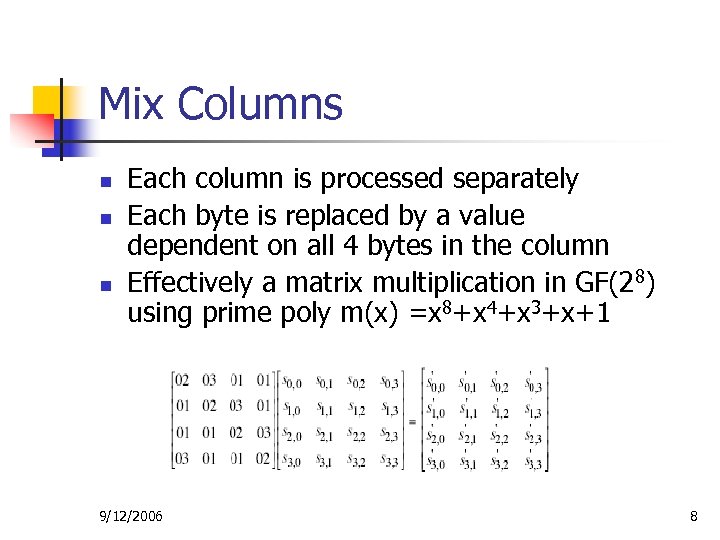 Mix Columns n n n Each column is processed separately Each byte is replaced by a value dependent on all 4 bytes in the column Effectively a matrix multiplication in GF(28) using prime poly m(x) =x 8+x 4+x 3+x+1 9/12/2006 8
Mix Columns n n n Each column is processed separately Each byte is replaced by a value dependent on all 4 bytes in the column Effectively a matrix multiplication in GF(28) using prime poly m(x) =x 8+x 4+x 3+x+1 9/12/2006 8
 Add Round Key n n XOR state with 128 bits of the round key Again processed by column (though effectively a series of byte operations) Inverse for decryption is identical since XOR is own inverse, just with correct round key Designed to be as simple as possible 9/12/2006 9
Add Round Key n n XOR state with 128 bits of the round key Again processed by column (though effectively a series of byte operations) Inverse for decryption is identical since XOR is own inverse, just with correct round key Designed to be as simple as possible 9/12/2006 9
 AES Key Expansion n Take 128 -bit (16 -byte) key and expand into array of 44/52/60 32 -bit words Start by copying key into first 4 words Then loop creating words that depend on values in previous and 4 places back n n n in 3 of 4 cases just XOR these together every 4 th has S-box + rotate + XOR constant of previous before XOR together Designed to resist known attacks 9/12/2006 10
AES Key Expansion n Take 128 -bit (16 -byte) key and expand into array of 44/52/60 32 -bit words Start by copying key into first 4 words Then loop creating words that depend on values in previous and 4 places back n n n in 3 of 4 cases just XOR these together every 4 th has S-box + rotate + XOR constant of previous before XOR together Designed to resist known attacks 9/12/2006 10
 AES Decryption n n AES decryption is not identical to encryption because steps are done in reverse But can define an equivalent inverse cipher with steps as for encryption n but using inverses of each step with a different key schedule Works since result is unchanged when n n swap byte substitution & shift rows swap mix columns and add (tweaked) round key 9/12/2006 11
AES Decryption n n AES decryption is not identical to encryption because steps are done in reverse But can define an equivalent inverse cipher with steps as for encryption n but using inverses of each step with a different key schedule Works since result is unchanged when n n swap byte substitution & shift rows swap mix columns and add (tweaked) round key 9/12/2006 11
 Implementation Aspects n Can efficiently implement on 8 -bit CPU n n byte substitution works on bytes using a table of 256 entries shift rows is simple byte shifting add round key works on byte XORs mix columns requires matrix multiply in GF(28) which works on byte values, can be simplified to use a table lookup 9/12/2006 12
Implementation Aspects n Can efficiently implement on 8 -bit CPU n n byte substitution works on bytes using a table of 256 entries shift rows is simple byte shifting add round key works on byte XORs mix columns requires matrix multiply in GF(28) which works on byte values, can be simplified to use a table lookup 9/12/2006 12
 Implementation Aspects n Can efficiently implement on 32 -bit CPU n n n redefine steps to use 32 -bit words can precompute 4 tables of 256 -words then each column in each round can be computed using 4 table lookups + 4 XORs at a cost of 16 Kb to store tables Designers believe this very efficient implementation was a key factor in its selection as the AES cipher 9/12/2006 13
Implementation Aspects n Can efficiently implement on 32 -bit CPU n n n redefine steps to use 32 -bit words can precompute 4 tables of 256 -words then each column in each round can be computed using 4 table lookups + 4 XORs at a cost of 16 Kb to store tables Designers believe this very efficient implementation was a key factor in its selection as the AES cipher 9/12/2006 13
 Points of Vulnerability n n n Adversary can eavesdrop from a machine on the same LAN Adversary can eavesdrop by dialing into communication server Adversary can eavesdrop by gaining physical control of part of external links n n twisted pair, coaxial cable, or optical fiber radio or satellite links 9/12/2006 14
Points of Vulnerability n n n Adversary can eavesdrop from a machine on the same LAN Adversary can eavesdrop by dialing into communication server Adversary can eavesdrop by gaining physical control of part of external links n n twisted pair, coaxial cable, or optical fiber radio or satellite links 9/12/2006 14
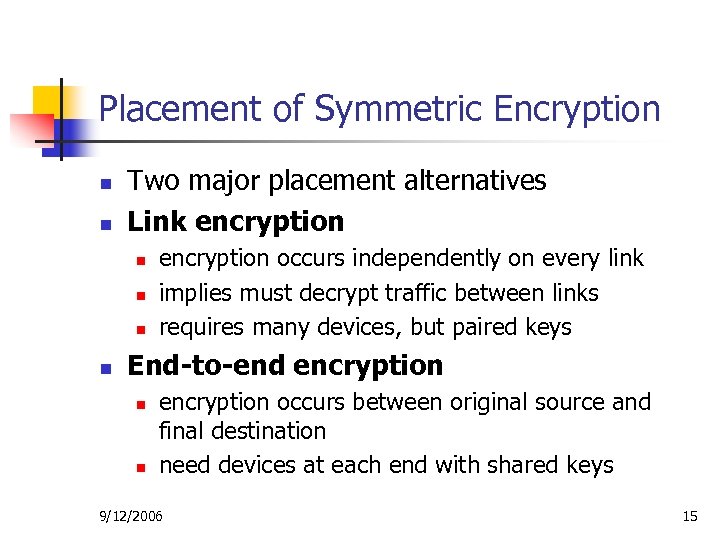 Placement of Symmetric Encryption n n Two major placement alternatives Link encryption n n encryption occurs independently on every link implies must decrypt traffic between links requires many devices, but paired keys End-to-end encryption n n encryption occurs between original source and final destination need devices at each end with shared keys 9/12/2006 15
Placement of Symmetric Encryption n n Two major placement alternatives Link encryption n n encryption occurs independently on every link implies must decrypt traffic between links requires many devices, but paired keys End-to-end encryption n n encryption occurs between original source and final destination need devices at each end with shared keys 9/12/2006 15
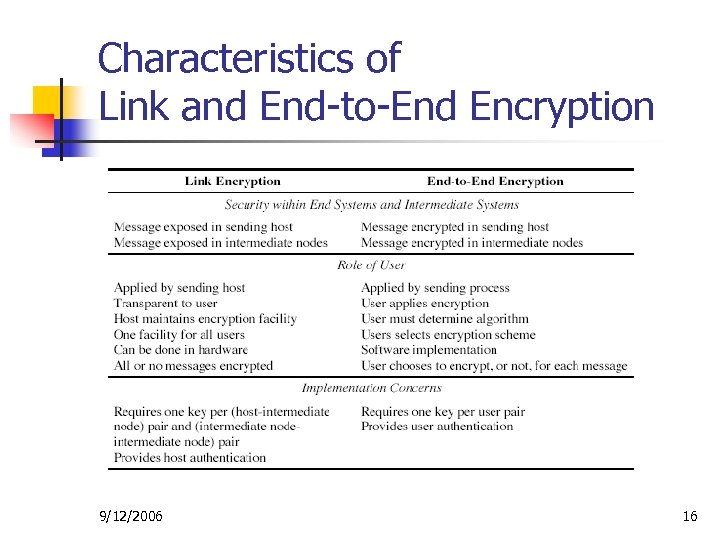 Characteristics of Link and End-to-End Encryption 9/12/2006 16
Characteristics of Link and End-to-End Encryption 9/12/2006 16
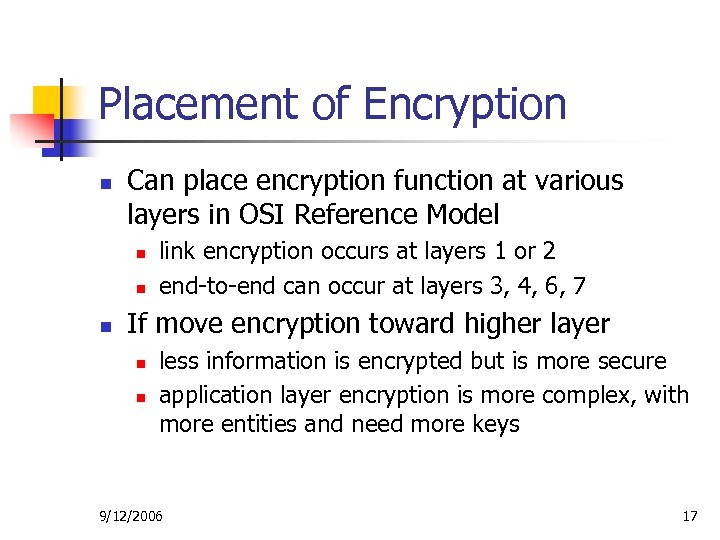 Placement of Encryption n Can place encryption function at various layers in OSI Reference Model n n n link encryption occurs at layers 1 or 2 end-to-end can occur at layers 3, 4, 6, 7 If move encryption toward higher layer n n less information is encrypted but is more secure application layer encryption is more complex, with more entities and need more keys 9/12/2006 17
Placement of Encryption n Can place encryption function at various layers in OSI Reference Model n n n link encryption occurs at layers 1 or 2 end-to-end can occur at layers 3, 4, 6, 7 If move encryption toward higher layer n n less information is encrypted but is more secure application layer encryption is more complex, with more entities and need more keys 9/12/2006 17
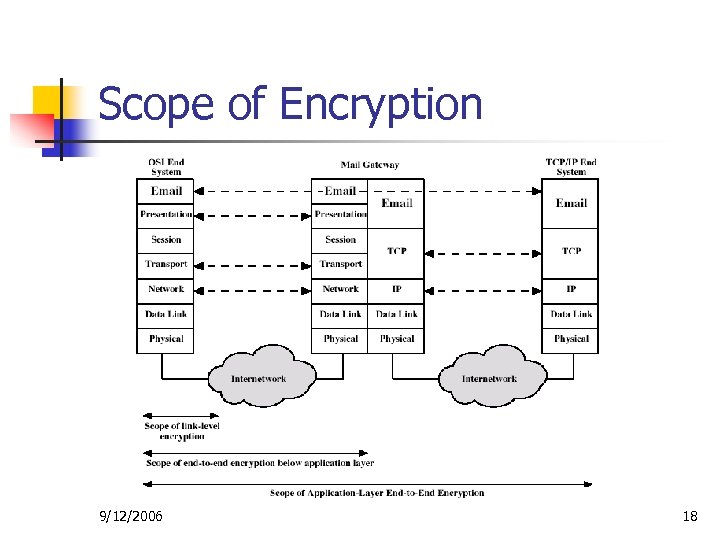 Scope of Encryption 9/12/2006 18
Scope of Encryption 9/12/2006 18
 Traffic Analysis n n n When using end-to-end encryption, must leave headers in clear so network can correctly route information Hence although contents are protected, traffic patterns are not protected Ideally both are desired n n end-to-end protects data contents over entire path and provides authentication link protects traffic flows from monitoring 9/12/2006 19
Traffic Analysis n n n When using end-to-end encryption, must leave headers in clear so network can correctly route information Hence although contents are protected, traffic patterns are not protected Ideally both are desired n n end-to-end protects data contents over entire path and provides authentication link protects traffic flows from monitoring 9/12/2006 19
 Key Distribution n Symmetric schemes require both parties to share a common secret key Need to securely distribute this key If key is compromised during distribution, all communications between two parties are compromised 9/12/2006 20
Key Distribution n Symmetric schemes require both parties to share a common secret key Need to securely distribute this key If key is compromised during distribution, all communications between two parties are compromised 9/12/2006 20
 Key Distribution Schemes n Various key distribution schemes for two parties A can select key and physically deliver to B § third party C can select and deliver key to A and B § if A and B have shared a key previously, can use previous key to encrypt a new key § if A and B have secure communications with third party C, C can relay key between A and B § 9/12/2006 21
Key Distribution Schemes n Various key distribution schemes for two parties A can select key and physically deliver to B § third party C can select and deliver key to A and B § if A and B have shared a key previously, can use previous key to encrypt a new key § if A and B have secure communications with third party C, C can relay key between A and B § 9/12/2006 21
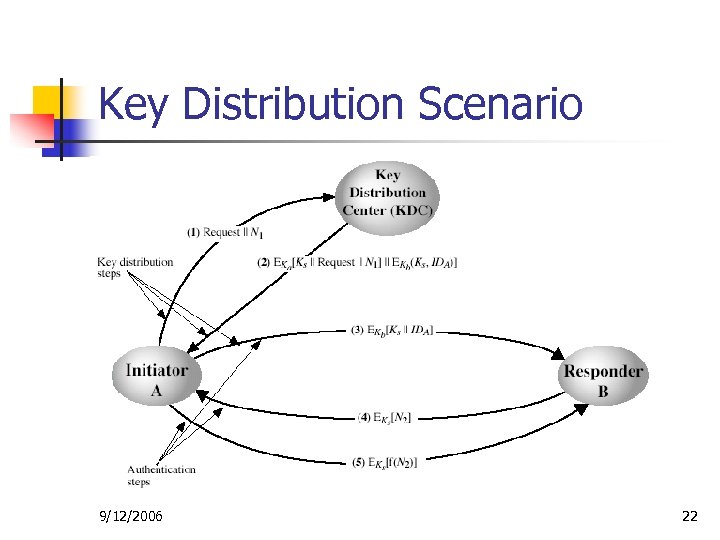 Key Distribution Scenario 9/12/2006 22
Key Distribution Scenario 9/12/2006 22
 Key Distribution Issues n n n Hierarchies of KDC’s are required for large networks, but must trust each other Session key lifetimes should be limited for greater security Use of automatic key distribution on behalf of users, but must trust system Use of decentralized key distribution Controlling purposes keys are used for 9/12/2006 23
Key Distribution Issues n n n Hierarchies of KDC’s are required for large networks, but must trust each other Session key lifetimes should be limited for greater security Use of automatic key distribution on behalf of users, but must trust system Use of decentralized key distribution Controlling purposes keys are used for 9/12/2006 23
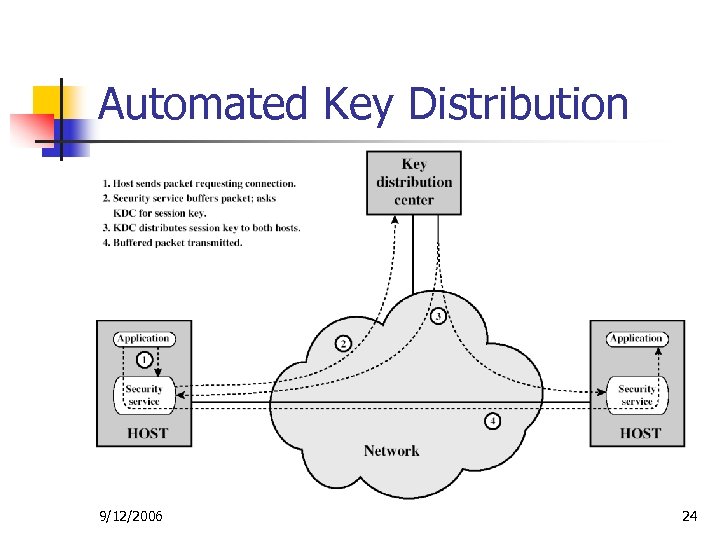 Automated Key Distribution 9/12/2006 24
Automated Key Distribution 9/12/2006 24
 Summary of Symmetric Encryption n n Traditional symmetric cryptography uses one key shared by both sender and receiver If this key is disclosed, communications are compromised Symmetric because parties are equal Provide confidentiality, but does not provide non-repudiation 9/12/2006 25
Summary of Symmetric Encryption n n Traditional symmetric cryptography uses one key shared by both sender and receiver If this key is disclosed, communications are compromised Symmetric because parties are equal Provide confidentiality, but does not provide non-repudiation 9/12/2006 25
 Next Class n n n Asymmetric encryption: RSA Key management with asymmetric encryption Read Chapter 9, 10 9/12/2006 26
Next Class n n n Asymmetric encryption: RSA Key management with asymmetric encryption Read Chapter 9, 10 9/12/2006 26


