453b6e031c2f5d29b696cae5af37111c.ppt
- Количество слайдов: 19
 CS 378 Routing Security Vitaly Shmatikov slide 1
CS 378 Routing Security Vitaly Shmatikov slide 1
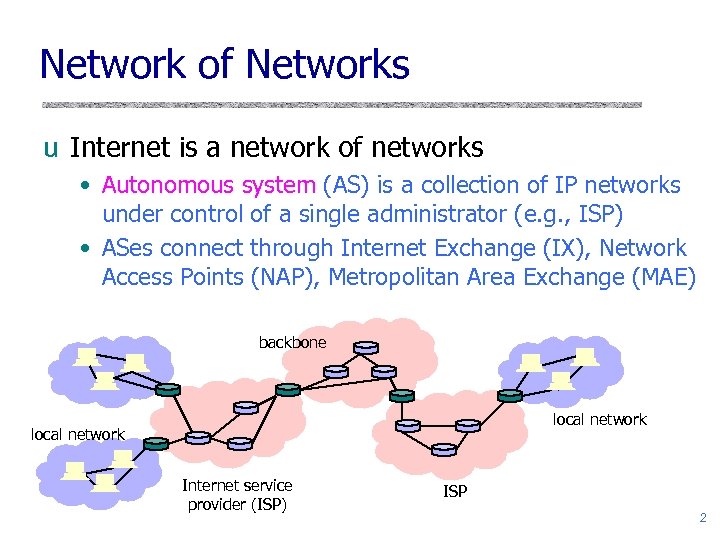 Network of Networks u Internet is a network of networks • Autonomous system (AS) is a collection of IP networks under control of a single administrator (e. g. , ISP) • ASes connect through Internet Exchange (IX), Network Access Points (NAP), Metropolitan Area Exchange (MAE) backbone local network Internet service provider (ISP) ISP 2
Network of Networks u Internet is a network of networks • Autonomous system (AS) is a collection of IP networks under control of a single administrator (e. g. , ISP) • ASes connect through Internet Exchange (IX), Network Access Points (NAP), Metropolitan Area Exchange (MAE) backbone local network Internet service provider (ISP) ISP 2
 Routing Through the Network u IP address is a 32 -bit host identifier (IPv 4) • 128 -bit identifier in IPv 6 u Routing protocols propagate information about routes to hosts and networks • Host is identified by IP address, network by IP prefix u Many types of routing protocols • Distance vector, link-state, path vector u BGP (Border Gateway Protocol) is one of the core routing protocols on the Internet • Inter-domain routing between different ASes 3
Routing Through the Network u IP address is a 32 -bit host identifier (IPv 4) • 128 -bit identifier in IPv 6 u Routing protocols propagate information about routes to hosts and networks • Host is identified by IP address, network by IP prefix u Many types of routing protocols • Distance vector, link-state, path vector u BGP (Border Gateway Protocol) is one of the core routing protocols on the Internet • Inter-domain routing between different ASes 3
 Distance-Vector Routing u Each node keeps vector with distances to all nodes u Periodically sends distance vector to all neighbors u Neighbors send their distance vectors, too; node updates its vector based on received information • Bellman-Ford algorithm: for each destination, router picks the neighbor advertising the cheapest route, adds his entry into its own routing table and re-advertises • Used in RIP (routing information protocol) u Split-horizon update • Do not advertise a route on an interface from which you learned the route in the first place! 4
Distance-Vector Routing u Each node keeps vector with distances to all nodes u Periodically sends distance vector to all neighbors u Neighbors send their distance vectors, too; node updates its vector based on received information • Bellman-Ford algorithm: for each destination, router picks the neighbor advertising the cheapest route, adds his entry into its own routing table and re-advertises • Used in RIP (routing information protocol) u Split-horizon update • Do not advertise a route on an interface from which you learned the route in the first place! 4
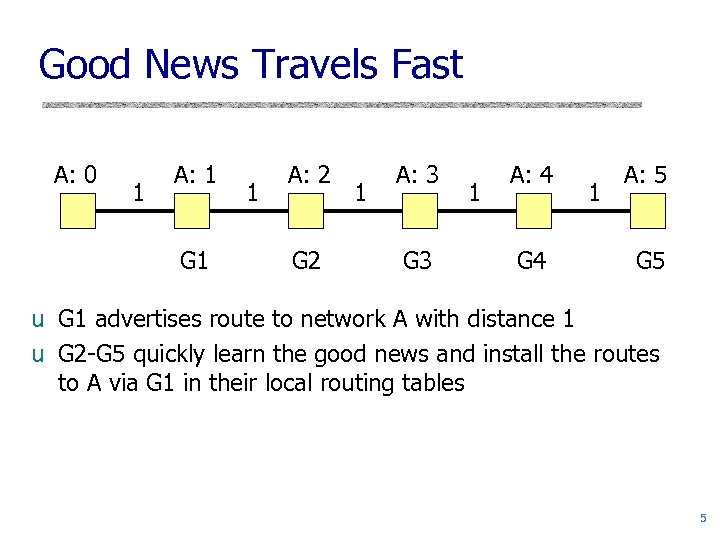 Good News Travels Fast A: 0 1 A: 1 G 1 1 A: 2 G 2 1 A: 3 G 3 1 A: 4 G 4 1 A: 5 G 5 u G 1 advertises route to network A with distance 1 u G 2 -G 5 quickly learn the good news and install the routes to A via G 1 in their local routing tables 5
Good News Travels Fast A: 0 1 A: 1 G 1 1 A: 2 G 2 1 A: 3 G 3 1 A: 4 G 4 1 A: 5 G 5 u G 1 advertises route to network A with distance 1 u G 2 -G 5 quickly learn the good news and install the routes to A via G 1 in their local routing tables 5
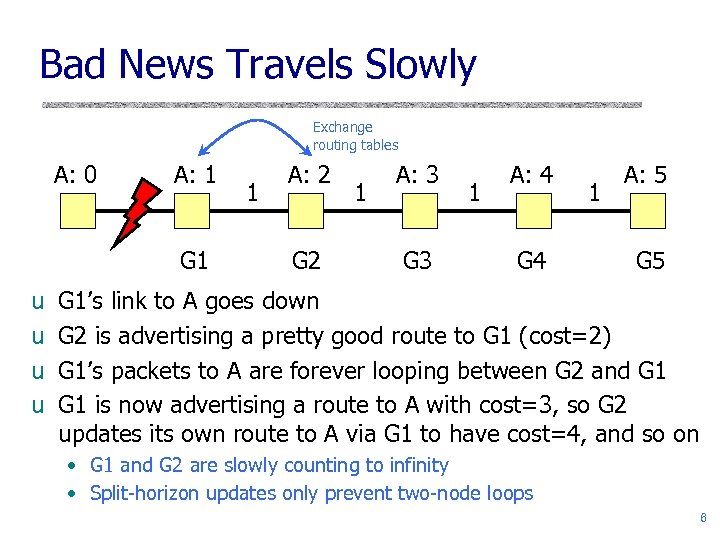 Bad News Travels Slowly Exchange routing tables A: 0 A: 1 G 1 u u 1 A: 2 G 2 1 A: 3 G 3 1 A: 4 G 4 1 A: 5 G 1’s link to A goes down G 2 is advertising a pretty good route to G 1 (cost=2) G 1’s packets to A are forever looping between G 2 and G 1 is now advertising a route to A with cost=3, so G 2 updates its own route to A via G 1 to have cost=4, and so on • G 1 and G 2 are slowly counting to infinity • Split-horizon updates only prevent two-node loops 6
Bad News Travels Slowly Exchange routing tables A: 0 A: 1 G 1 u u 1 A: 2 G 2 1 A: 3 G 3 1 A: 4 G 4 1 A: 5 G 1’s link to A goes down G 2 is advertising a pretty good route to G 1 (cost=2) G 1’s packets to A are forever looping between G 2 and G 1 is now advertising a route to A with cost=3, so G 2 updates its own route to A via G 1 to have cost=4, and so on • G 1 and G 2 are slowly counting to infinity • Split-horizon updates only prevent two-node loops 6
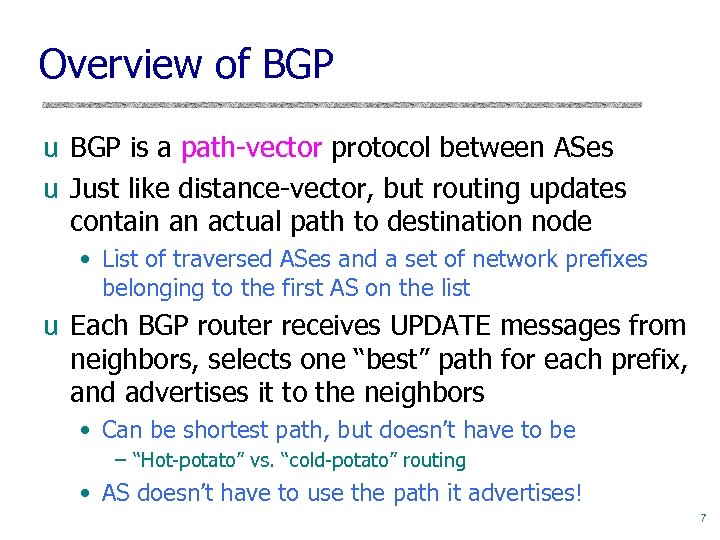 Overview of BGP u BGP is a path-vector protocol between ASes u Just like distance-vector, but routing updates contain an actual path to destination node • List of traversed ASes and a set of network prefixes belonging to the first AS on the list u Each BGP router receives UPDATE messages from neighbors, selects one “best” path for each prefix, and advertises it to the neighbors • Can be shortest path, but doesn’t have to be – “Hot-potato” vs. “cold-potato” routing • AS doesn’t have to use the path it advertises! 7
Overview of BGP u BGP is a path-vector protocol between ASes u Just like distance-vector, but routing updates contain an actual path to destination node • List of traversed ASes and a set of network prefixes belonging to the first AS on the list u Each BGP router receives UPDATE messages from neighbors, selects one “best” path for each prefix, and advertises it to the neighbors • Can be shortest path, but doesn’t have to be – “Hot-potato” vs. “cold-potato” routing • AS doesn’t have to use the path it advertises! 7
![BGP Example 1 [D. Wetherall] 27 265 8 2 7265 7 7 7 265 BGP Example 1 [D. Wetherall] 27 265 8 2 7265 7 7 7 265](https://present5.com/presentation/453b6e031c2f5d29b696cae5af37111c/image-8.jpg) BGP Example 1 [D. Wetherall] 27 265 8 2 7265 7 7 7 265 327 3 265 27 6 4 3265 627 5 5 5 u AS 2 provides transit for AS 7 • Traffic to and from AS 7 travels through AS 2 8
BGP Example 1 [D. Wetherall] 27 265 8 2 7265 7 7 7 265 327 3 265 27 6 4 3265 627 5 5 5 u AS 2 provides transit for AS 7 • Traffic to and from AS 7 travels through AS 2 8
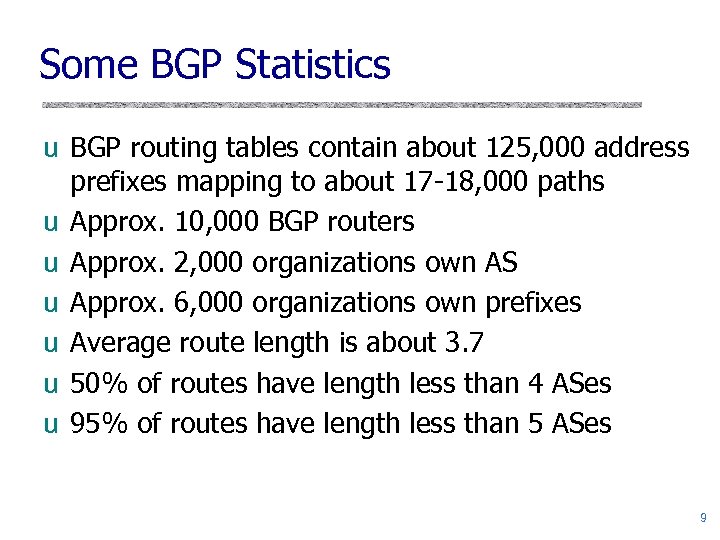 Some BGP Statistics u BGP routing tables contain about 125, 000 address prefixes mapping to about 17 -18, 000 paths u Approx. 10, 000 BGP routers u Approx. 2, 000 organizations own AS u Approx. 6, 000 organizations own prefixes u Average route length is about 3. 7 u 50% of routes have length less than 4 ASes u 95% of routes have length less than 5 ASes 9
Some BGP Statistics u BGP routing tables contain about 125, 000 address prefixes mapping to about 17 -18, 000 paths u Approx. 10, 000 BGP routers u Approx. 2, 000 organizations own AS u Approx. 6, 000 organizations own prefixes u Average route length is about 3. 7 u 50% of routes have length less than 4 ASes u 95% of routes have length less than 5 ASes 9
 BGP Issues u BGP convergence problems • Protocol allows policy flexibility • Some legal policies prevent convergence • Even shortest-path policy converges slowly u Incentive for dishonesty • ISP pays for some routes, others free u Security problems • Potential for disruptive attacks 10
BGP Issues u BGP convergence problems • Protocol allows policy flexibility • Some legal policies prevent convergence • Even shortest-path policy converges slowly u Incentive for dishonesty • ISP pays for some routes, others free u Security problems • Potential for disruptive attacks 10
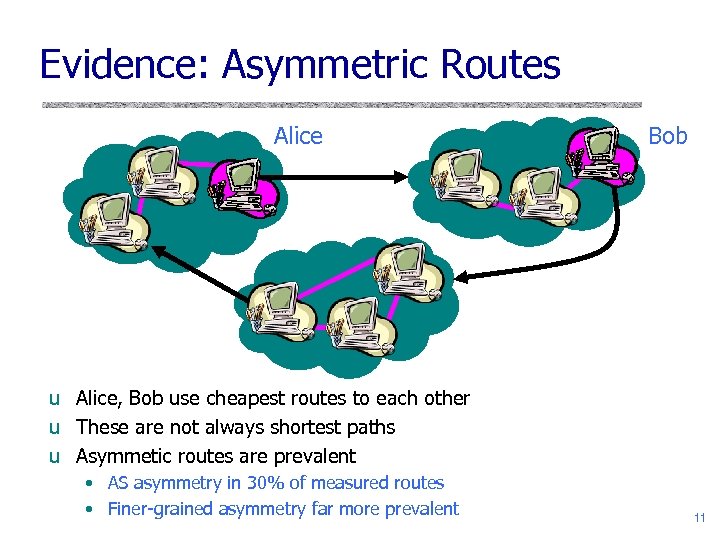 Evidence: Asymmetric Routes Alice Bob u Alice, Bob use cheapest routes to each other u These are not always shortest paths u Asymmetic routes are prevalent • AS asymmetry in 30% of measured routes • Finer-grained asymmetry far more prevalent 11
Evidence: Asymmetric Routes Alice Bob u Alice, Bob use cheapest routes to each other u These are not always shortest paths u Asymmetic routes are prevalent • AS asymmetry in 30% of measured routes • Finer-grained asymmetry far more prevalent 11
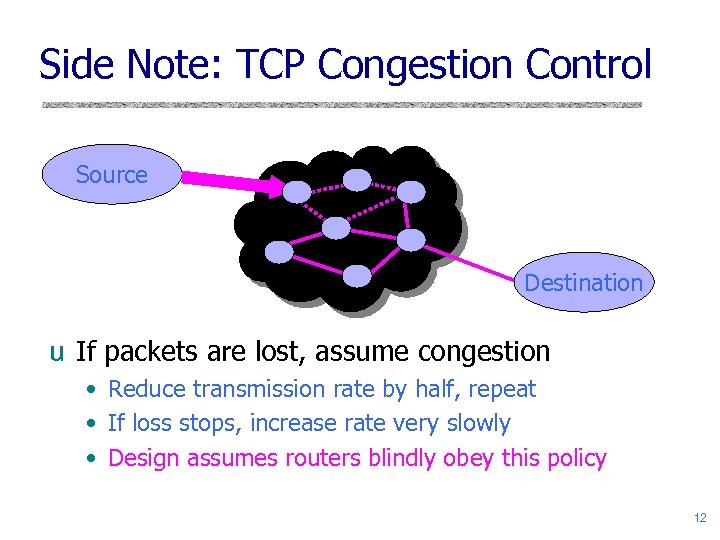 Side Note: TCP Congestion Control Source Destination u If packets are lost, assume congestion • Reduce transmission rate by half, repeat • If loss stops, increase rate very slowly • Design assumes routers blindly obey this policy 12
Side Note: TCP Congestion Control Source Destination u If packets are lost, assume congestion • Reduce transmission rate by half, repeat • If loss stops, increase rate very slowly • Design assumes routers blindly obey this policy 12
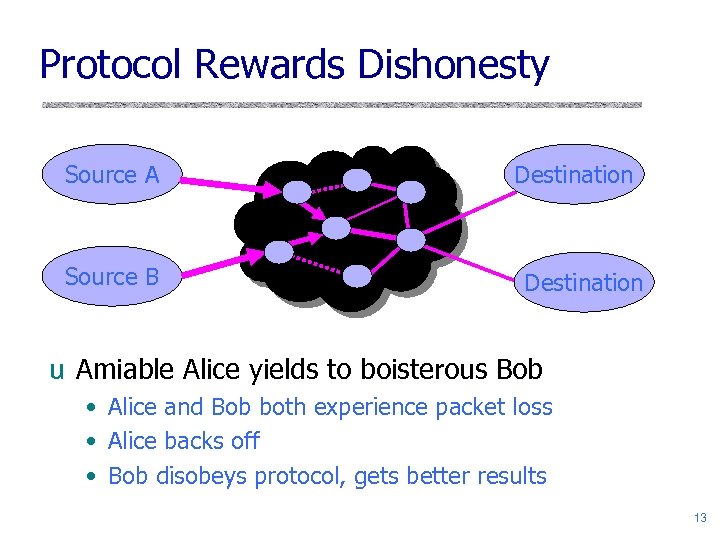 Protocol Rewards Dishonesty Source A Source B Destination u Amiable Alice yields to boisterous Bob • Alice and Bob both experience packet loss • Alice backs off • Bob disobeys protocol, gets better results 13
Protocol Rewards Dishonesty Source A Source B Destination u Amiable Alice yields to boisterous Bob • Alice and Bob both experience packet loss • Alice backs off • Bob disobeys protocol, gets better results 13
 BGP Threats: Misconfiguration u Misconfiguration: AS advertises good routes to addresses it does not known how to reach • Result: packets go into a network “black hole” u April 25, 1997: “The day the Internet died” • AS 7007 (Florida Internet Exchange) de-aggregated the full BGP table and re-advertised all prefixes as if it originated paths to them • In effect, AS 7007 was advertising that it has the best route to every host on the Internet • Huge network instability as incorrect routing data propagated and routers crashed under traffic 14
BGP Threats: Misconfiguration u Misconfiguration: AS advertises good routes to addresses it does not known how to reach • Result: packets go into a network “black hole” u April 25, 1997: “The day the Internet died” • AS 7007 (Florida Internet Exchange) de-aggregated the full BGP table and re-advertised all prefixes as if it originated paths to them • In effect, AS 7007 was advertising that it has the best route to every host on the Internet • Huge network instability as incorrect routing data propagated and routers crashed under traffic 14
 BGP Threats: Security u BGP update messages contain no authentication or integrity protection u Attacker may falsify the advertised routes • Modify the IP prefixes associated with the route – Can blackhole traffic to certain IP prefixes • Change the AS path – Either attract traffic to attacker’s AS, or divert traffic away – Interesting economic incentive: an ISP wants to dump its traffic on other ISPs without routing their traffic in exchange • Re-advertise/propagate AS path without permission – For example, multi-homed customer may end up advertising transit capability between two large ISPs 15
BGP Threats: Security u BGP update messages contain no authentication or integrity protection u Attacker may falsify the advertised routes • Modify the IP prefixes associated with the route – Can blackhole traffic to certain IP prefixes • Change the AS path – Either attract traffic to attacker’s AS, or divert traffic away – Interesting economic incentive: an ISP wants to dump its traffic on other ISPs without routing their traffic in exchange • Re-advertise/propagate AS path without permission – For example, multi-homed customer may end up advertising transit capability between two large ISPs 15
 Protecting BGP u Simple authentication of packet sources and packet integrity is not enough u Before AS advertises a set of IP addresses, the owner of these addresses must authorize it • Goal: verify path origin u Each AS along the path must be authorized by the preceding AS to advertise the prefixes contained in the UPDATE message • Goal: verify propagation of the path vector 16
Protecting BGP u Simple authentication of packet sources and packet integrity is not enough u Before AS advertises a set of IP addresses, the owner of these addresses must authorize it • Goal: verify path origin u Each AS along the path must be authorized by the preceding AS to advertise the prefixes contained in the UPDATE message • Goal: verify propagation of the path vector 16
![S-BGP Protocol [Kent, Lynn, Seo] u Address attestation • Owner of one or more S-BGP Protocol [Kent, Lynn, Seo] u Address attestation • Owner of one or more](https://present5.com/presentation/453b6e031c2f5d29b696cae5af37111c/image-17.jpg) S-BGP Protocol [Kent, Lynn, Seo] u Address attestation • Owner of one or more prefixes certifies that the origin AS is authorized to advertise the prefixes • Need a public-key infrastructure (PKI) – X. 509 certificates prove prefix ownership; owner can then delegate his “prefix advertising rights” to his ISP u Route attestation • Router belonging to an AS certifies (using digital signatures) that the next AS is authorized to propagate this route advertisement to its neighbors • Need a separate public-key infrastructure – Certificates prove that AS owns a particular router 17
S-BGP Protocol [Kent, Lynn, Seo] u Address attestation • Owner of one or more prefixes certifies that the origin AS is authorized to advertise the prefixes • Need a public-key infrastructure (PKI) – X. 509 certificates prove prefix ownership; owner can then delegate his “prefix advertising rights” to his ISP u Route attestation • Router belonging to an AS certifies (using digital signatures) that the next AS is authorized to propagate this route advertisement to its neighbors • Need a separate public-key infrastructure – Certificates prove that AS owns a particular router 17
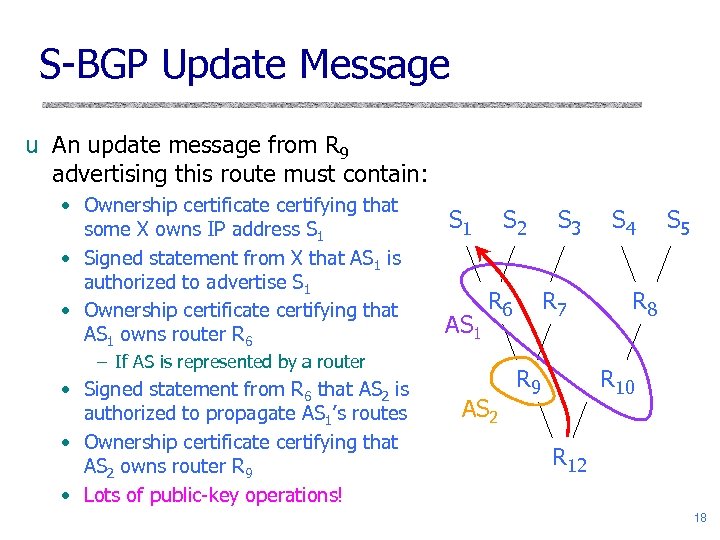 S-BGP Update Message u An update message from R 9 advertising this route must contain: • Ownership certificate certifying that some X owns IP address S 1 • Signed statement from X that AS 1 is authorized to advertise S 1 • Ownership certificate certifying that AS 1 owns router R 6 S 1 AS 1 S 2 R 6 – If AS is represented by a router • Signed statement from R 6 that AS 2 is authorized to propagate AS 1’s routes • Ownership certificate certifying that AS 2 owns router R 9 • Lots of public-key operations! AS 2 S 3 R 7 R 9 S 4 S 5 R 8 R 10 R 12 18
S-BGP Update Message u An update message from R 9 advertising this route must contain: • Ownership certificate certifying that some X owns IP address S 1 • Signed statement from X that AS 1 is authorized to advertise S 1 • Ownership certificate certifying that AS 1 owns router R 6 S 1 AS 1 S 2 R 6 – If AS is represented by a router • Signed statement from R 6 that AS 2 is authorized to propagate AS 1’s routes • Ownership certificate certifying that AS 2 owns router R 9 • Lots of public-key operations! AS 2 S 3 R 7 R 9 S 4 S 5 R 8 R 10 R 12 18
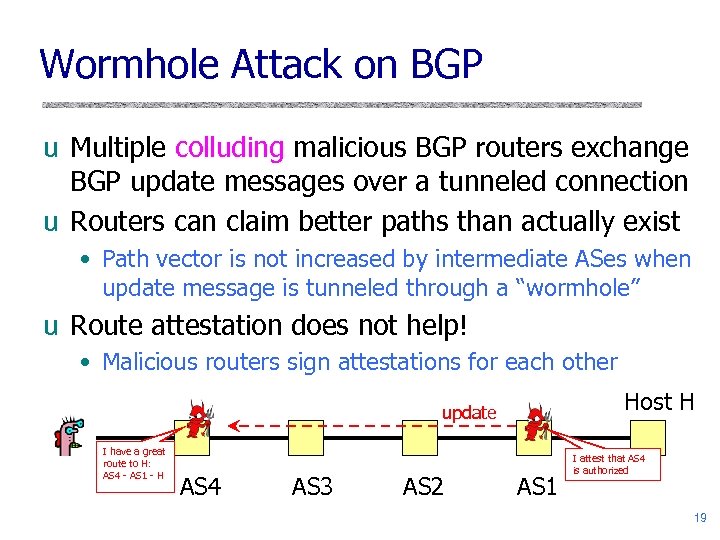 Wormhole Attack on BGP u Multiple colluding malicious BGP routers exchange BGP update messages over a tunneled connection u Routers can claim better paths than actually exist • Path vector is not increased by intermediate ASes when update message is tunneled through a “wormhole” u Route attestation does not help! • Malicious routers sign attestations for each other Host H update I have a great route to H: AS 4 - AS 1 - H AS 4 AS 3 AS 2 AS 1 I attest that AS 4 is authorized 19
Wormhole Attack on BGP u Multiple colluding malicious BGP routers exchange BGP update messages over a tunneled connection u Routers can claim better paths than actually exist • Path vector is not increased by intermediate ASes when update message is tunneled through a “wormhole” u Route attestation does not help! • Malicious routers sign attestations for each other Host H update I have a great route to H: AS 4 - AS 1 - H AS 4 AS 3 AS 2 AS 1 I attest that AS 4 is authorized 19


