66994b752f86cd4f3e5e91fe08a7b903.ppt
- Количество слайдов: 37
 Cryptography and Network Security Overview & Chapter 1 Fifth Edition by William Stallings Lecture slides by Lawrie Brown Editied by R. Newman
Cryptography and Network Security Overview & Chapter 1 Fifth Edition by William Stallings Lecture slides by Lawrie Brown Editied by R. Newman
 Chapter 0 – Reader’s Guide The art of war teaches us to rely not on the likelihood of the enemy's not coming, but on our own readiness to receive him; not on the chance of his not attacking, but rather on the fact that we have made our position unquestionable. —The Art of War, Sun Tzu
Chapter 0 – Reader’s Guide The art of war teaches us to rely not on the likelihood of the enemy's not coming, but on our own readiness to receive him; not on the chance of his not attacking, but rather on the fact that we have made our position unquestionable. —The Art of War, Sun Tzu
 Roadmap Ø Cryptographic algorithms l l l symmetric ciphers asymmetric encryption hash functions Ø Mutual Trust Ø Network Security Ø Computer Security
Roadmap Ø Cryptographic algorithms l l l symmetric ciphers asymmetric encryption hash functions Ø Mutual Trust Ø Network Security Ø Computer Security
 Standards Organizations Ø National Institute of Standards & Technology (NIST) Ø Internet Society (ISOC) Ø International Telecommunication Union Telecommunication Standardization Sector (ITU-T) Ø International Organization for Standardization (ISO) Ø RSA Labs (de facto)
Standards Organizations Ø National Institute of Standards & Technology (NIST) Ø Internet Society (ISOC) Ø International Telecommunication Union Telecommunication Standardization Sector (ITU-T) Ø International Organization for Standardization (ISO) Ø RSA Labs (de facto)
 Chapter 1 – Introduction Ø The combination of space, time, and strength that must be considered as the basic elements of this theory of defense makes this a fairly complicated matter. Consequently, it is not easy to find a fixed point of departure. . — On War, Carl Von Clausewitz
Chapter 1 – Introduction Ø The combination of space, time, and strength that must be considered as the basic elements of this theory of defense makes this a fairly complicated matter. Consequently, it is not easy to find a fixed point of departure. . — On War, Carl Von Clausewitz
 Computer Security Ø the protection afforded to an automated information system in order to attain the applicable objectives of preserving the integrity, availability and confidentiality of information system resources (includes hardware, software, firmware, information/data, and telecommunications)
Computer Security Ø the protection afforded to an automated information system in order to attain the applicable objectives of preserving the integrity, availability and confidentiality of information system resources (includes hardware, software, firmware, information/data, and telecommunications)
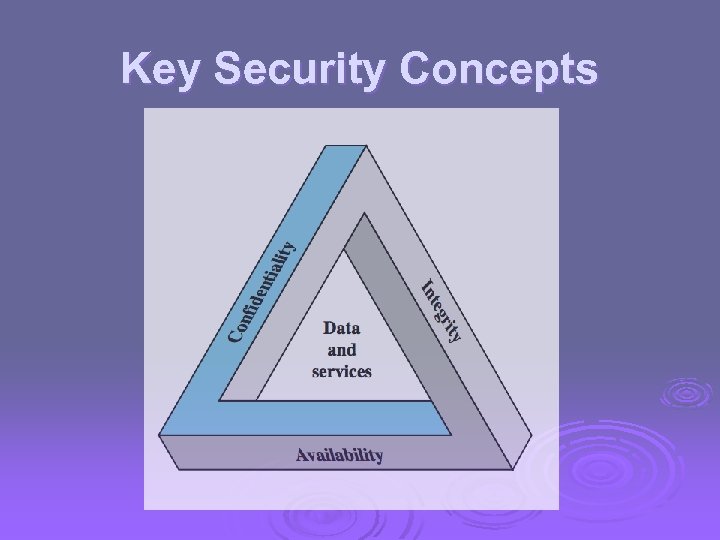 Key Security Concepts
Key Security Concepts
 Levels of Impact Ø can define 3 levels of impact from a security breach l l l Low Moderate High
Levels of Impact Ø can define 3 levels of impact from a security breach l l l Low Moderate High
 Low Impact The loss could be expected to have a limited adverse effect on organizational operations, organizational assets, or individuals. Ø A limited adverse effect means that, for example, the loss of confidentiality, integrity, or availability might l (i) cause a degradation in mission capability to an extent and duration that the organization is able to perform its primary functions, but the effectiveness of the functions is noticeably reduced; l (ii) result in minor damage to organizational assets; l (iii) result in minor financial loss; or l (iv) result in minor harm to individuals. l Example: Block access points, dropping 50% of packets Ø
Low Impact The loss could be expected to have a limited adverse effect on organizational operations, organizational assets, or individuals. Ø A limited adverse effect means that, for example, the loss of confidentiality, integrity, or availability might l (i) cause a degradation in mission capability to an extent and duration that the organization is able to perform its primary functions, but the effectiveness of the functions is noticeably reduced; l (ii) result in minor damage to organizational assets; l (iii) result in minor financial loss; or l (iv) result in minor harm to individuals. l Example: Block access points, dropping 50% of packets Ø
 Moderate Impact The loss could be expected to have a serious adverse effect on organizational operations, organizational assets, or individuals. Ø A serious adverse effect means that, for example, the loss might l (i) cause a significant degradation in mission capability to an extent and duration that the organization is able to perform its primary functions, but the effectiveness of the functions is significantly reduced; l (ii) result in significant damage to organizational assets; l (iii) result in significant financial loss; or l (iv) result in significant harm to individuals that does not involve loss of life or serious, life-threatening injuries. l Example: hacking a neft transfer, military information. Ø
Moderate Impact The loss could be expected to have a serious adverse effect on organizational operations, organizational assets, or individuals. Ø A serious adverse effect means that, for example, the loss might l (i) cause a significant degradation in mission capability to an extent and duration that the organization is able to perform its primary functions, but the effectiveness of the functions is significantly reduced; l (ii) result in significant damage to organizational assets; l (iii) result in significant financial loss; or l (iv) result in significant harm to individuals that does not involve loss of life or serious, life-threatening injuries. l Example: hacking a neft transfer, military information. Ø
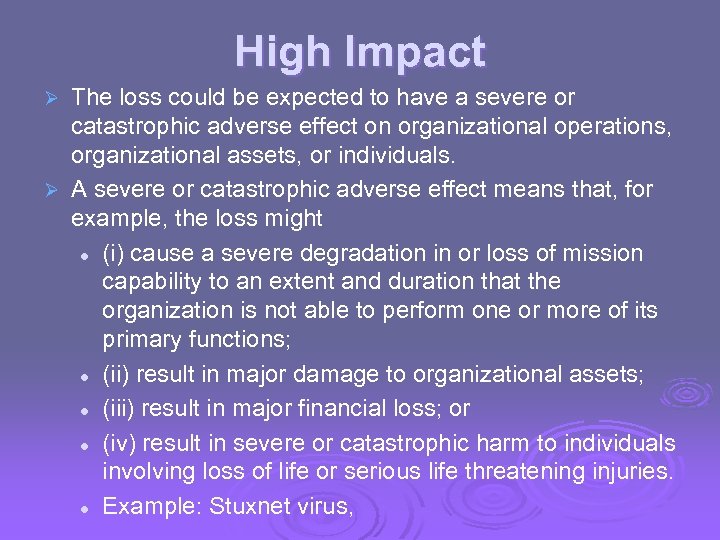 High Impact The loss could be expected to have a severe or catastrophic adverse effect on organizational operations, organizational assets, or individuals. Ø A severe or catastrophic adverse effect means that, for example, the loss might l (i) cause a severe degradation in or loss of mission capability to an extent and duration that the organization is not able to perform one or more of its primary functions; l (ii) result in major damage to organizational assets; l (iii) result in major financial loss; or l (iv) result in severe or catastrophic harm to individuals involving loss of life or serious life threatening injuries. l Example: Stuxnet virus, Ø
High Impact The loss could be expected to have a severe or catastrophic adverse effect on organizational operations, organizational assets, or individuals. Ø A severe or catastrophic adverse effect means that, for example, the loss might l (i) cause a severe degradation in or loss of mission capability to an extent and duration that the organization is not able to perform one or more of its primary functions; l (ii) result in major damage to organizational assets; l (iii) result in major financial loss; or l (iv) result in severe or catastrophic harm to individuals involving loss of life or serious life threatening injuries. l Example: Stuxnet virus, Ø
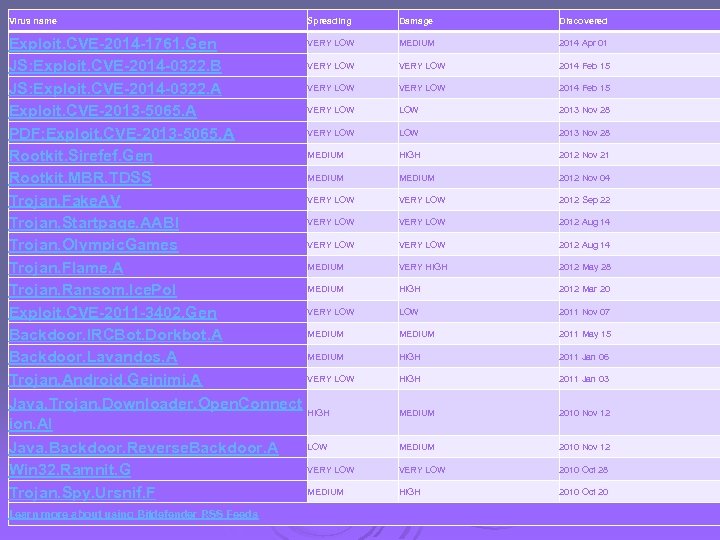 Virus name Spreading VERY LOW Exploit. CVE-2014 -1761. Gen VERY LOW JS: Exploit. CVE-2014 -0322. B VERY LOW JS: Exploit. CVE-2014 -0322. A VERY LOW Exploit. CVE-2013 -5065. A VERY LOW PDF: Exploit. CVE-2013 -5065. A MEDIUM Rootkit. Sirefef. Gen MEDIUM Rootkit. MBR. TDSS VERY LOW Trojan. Fake. AV VERY LOW Trojan. Startpage. AABI VERY LOW Trojan. Olympic. Games MEDIUM Trojan. Flame. A MEDIUM Trojan. Ransom. Ice. Pol VERY LOW Exploit. CVE-2011 -3402. Gen MEDIUM Backdoor. IRCBot. Dorkbot. A MEDIUM Backdoor. Lavandos. A VERY LOW Trojan. Android. Geinimi. A Java. Trojan. Downloader. Open. Connect HIGH ion. AI LOW Java. Backdoor. Reverse. Backdoor. A VERY LOW Win 32. Ramnit. G MEDIUM Trojan. Spy. Ursnif. F Learn more about using Bitdefender RSS Feeds Damage Discovered MEDIUM 2014 Apr 01 VERY LOW 2014 Feb 15 LOW 2013 Nov 28 HIGH 2012 Nov 21 MEDIUM 2012 Nov 04 VERY LOW 2012 Sep 22 VERY LOW 2012 Aug 14 VERY HIGH 2012 May 28 HIGH 2012 Mar 20 LOW 2011 Nov 07 MEDIUM 2011 May 15 HIGH 2011 Jan 06 HIGH 2011 Jan 03 MEDIUM 2010 Nov 12 VERY LOW 2010 Oct 28 HIGH 2010 Oct 20
Virus name Spreading VERY LOW Exploit. CVE-2014 -1761. Gen VERY LOW JS: Exploit. CVE-2014 -0322. B VERY LOW JS: Exploit. CVE-2014 -0322. A VERY LOW Exploit. CVE-2013 -5065. A VERY LOW PDF: Exploit. CVE-2013 -5065. A MEDIUM Rootkit. Sirefef. Gen MEDIUM Rootkit. MBR. TDSS VERY LOW Trojan. Fake. AV VERY LOW Trojan. Startpage. AABI VERY LOW Trojan. Olympic. Games MEDIUM Trojan. Flame. A MEDIUM Trojan. Ransom. Ice. Pol VERY LOW Exploit. CVE-2011 -3402. Gen MEDIUM Backdoor. IRCBot. Dorkbot. A MEDIUM Backdoor. Lavandos. A VERY LOW Trojan. Android. Geinimi. A Java. Trojan. Downloader. Open. Connect HIGH ion. AI LOW Java. Backdoor. Reverse. Backdoor. A VERY LOW Win 32. Ramnit. G MEDIUM Trojan. Spy. Ursnif. F Learn more about using Bitdefender RSS Feeds Damage Discovered MEDIUM 2014 Apr 01 VERY LOW 2014 Feb 15 LOW 2013 Nov 28 HIGH 2012 Nov 21 MEDIUM 2012 Nov 04 VERY LOW 2012 Sep 22 VERY LOW 2012 Aug 14 VERY HIGH 2012 May 28 HIGH 2012 Mar 20 LOW 2011 Nov 07 MEDIUM 2011 May 15 HIGH 2011 Jan 06 HIGH 2011 Jan 03 MEDIUM 2010 Nov 12 VERY LOW 2010 Oct 28 HIGH 2010 Oct 20
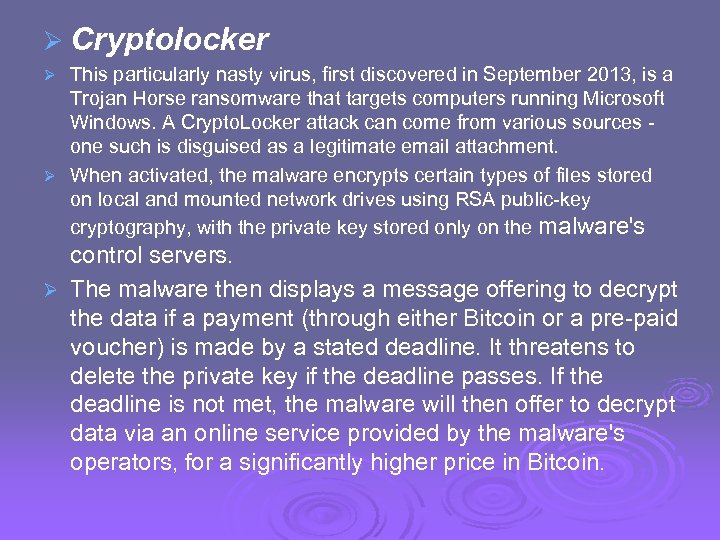 Ø Cryptolocker This particularly nasty virus, first discovered in September 2013, is a Trojan Horse ransomware that targets computers running Microsoft Windows. A Crypto. Locker attack can come from various sources - one such is disguised as a legitimate email attachment. Ø When activated, the malware encrypts certain types of files stored on local and mounted network drives using RSA public-key cryptography, with the private key stored only on the malware's Ø control servers. Ø The malware then displays a message offering to decrypt the data if a payment (through either Bitcoin or a pre-paid voucher) is made by a stated deadline. It threatens to delete the private key if the deadline passes. If the deadline is not met, the malware will then offer to decrypt data via an online service provided by the malware's operators, for a significantly higher price in Bitcoin.
Ø Cryptolocker This particularly nasty virus, first discovered in September 2013, is a Trojan Horse ransomware that targets computers running Microsoft Windows. A Crypto. Locker attack can come from various sources - one such is disguised as a legitimate email attachment. Ø When activated, the malware encrypts certain types of files stored on local and mounted network drives using RSA public-key cryptography, with the private key stored only on the malware's Ø control servers. Ø The malware then displays a message offering to decrypt the data if a payment (through either Bitcoin or a pre-paid voucher) is made by a stated deadline. It threatens to delete the private key if the deadline passes. If the deadline is not met, the malware will then offer to decrypt data via an online service provided by the malware's operators, for a significantly higher price in Bitcoin.
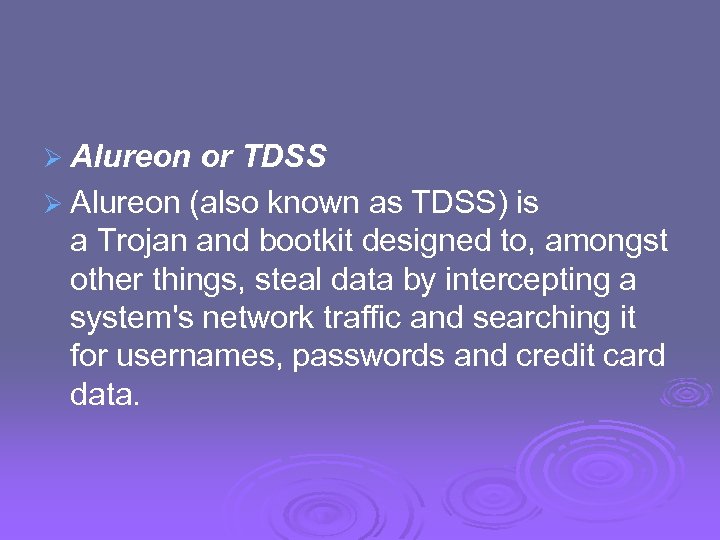 Ø Alureon or TDSS Ø Alureon (also known as TDSS) is a Trojan and bootkit designed to, amongst other things, steal data by intercepting a system's network traffic and searching it for usernames, passwords and credit card data.
Ø Alureon or TDSS Ø Alureon (also known as TDSS) is a Trojan and bootkit designed to, amongst other things, steal data by intercepting a system's network traffic and searching it for usernames, passwords and credit card data.
 Ø Zeus This botnet toolkit creates malware and is mainly used to collect data and steal identities and bank information. Zeus is particularly difficult to deal with is it is not just one botnet - it can create others to steal any data stored on your computer. Ø Trojan: Win 32/fakesvsdef Ø This is a Trojan Horse targeting the Microsoft Windows operating system that was first documented in late 2010. It was originally dispersed as an application called "HDD Defragmenter" hence the name "Fake. Sysdef" or "Fake System Defragmenter. " Ø
Ø Zeus This botnet toolkit creates malware and is mainly used to collect data and steal identities and bank information. Zeus is particularly difficult to deal with is it is not just one botnet - it can create others to steal any data stored on your computer. Ø Trojan: Win 32/fakesvsdef Ø This is a Trojan Horse targeting the Microsoft Windows operating system that was first documented in late 2010. It was originally dispersed as an application called "HDD Defragmenter" hence the name "Fake. Sysdef" or "Fake System Defragmenter. " Ø
 Examples of Security Requirements Ø confidentiality – student grades Ø integrity – patient information Ø availability – authentication service Ø authenticity – admission ticket Ø non-repudiation – stock sell order
Examples of Security Requirements Ø confidentiality – student grades Ø integrity – patient information Ø availability – authentication service Ø authenticity – admission ticket Ø non-repudiation – stock sell order
 Computer Security Challenges 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. not simple – easy to get it wrong must consider potential attacks procedures used counter-intuitive involve algorithms and secret info must decide where to deploy mechanisms battle of wits between attacker / admin not perceived on benefit until fails requires regular monitoring a process, not an event too often an after-thought regarded as impediment to using system “Unusable security is not secure”
Computer Security Challenges 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. not simple – easy to get it wrong must consider potential attacks procedures used counter-intuitive involve algorithms and secret info must decide where to deploy mechanisms battle of wits between attacker / admin not perceived on benefit until fails requires regular monitoring a process, not an event too often an after-thought regarded as impediment to using system “Unusable security is not secure”
 OSI Security Architecture Ø ITU-T X. 800 “Security Architecture for OSI” Ø defines a systematic way of defining and providing security requirements Ø for us it provides a useful, if abstract, overview of concepts we will study
OSI Security Architecture Ø ITU-T X. 800 “Security Architecture for OSI” Ø defines a systematic way of defining and providing security requirements Ø for us it provides a useful, if abstract, overview of concepts we will study
 Aspects of Security Ø consider 3 aspects of information security: l l l l security attack security mechanism (control) security service, note terms threat – a potential for violation of security vulnerability – a way by which loss can happen attack – an assault on system security, a deliberate attempt to evade security services
Aspects of Security Ø consider 3 aspects of information security: l l l l security attack security mechanism (control) security service, note terms threat – a potential for violation of security vulnerability – a way by which loss can happen attack – an assault on system security, a deliberate attempt to evade security services
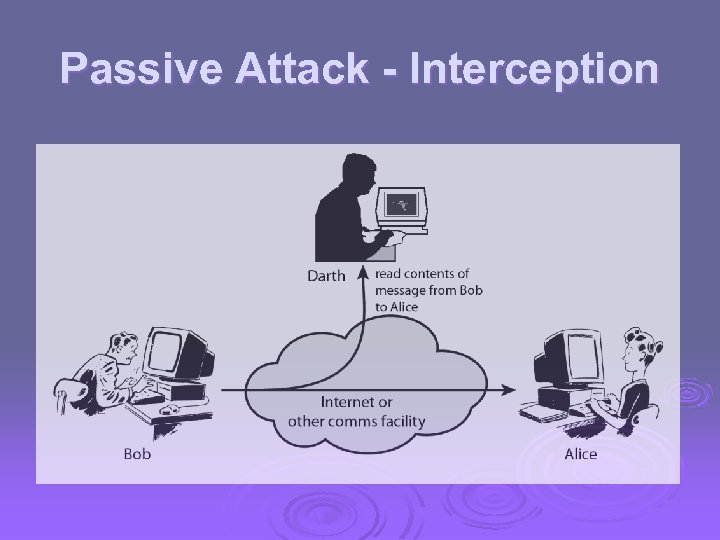 Passive Attack - Interception
Passive Attack - Interception
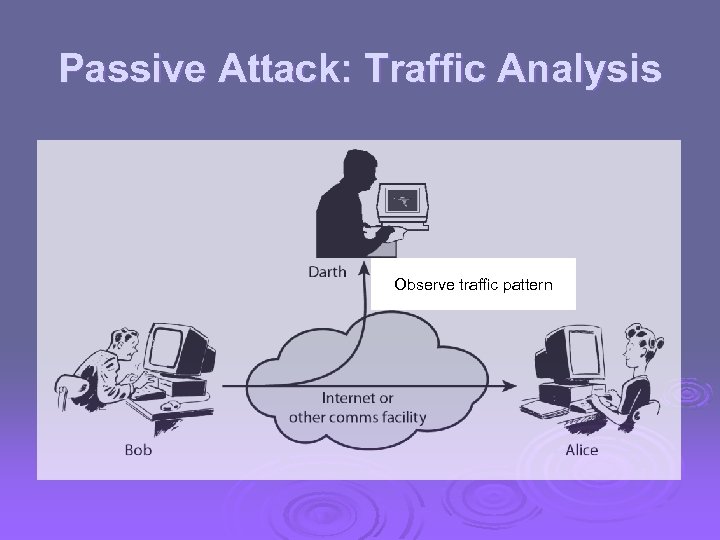 Passive Attack: Traffic Analysis Observe traffic pattern
Passive Attack: Traffic Analysis Observe traffic pattern
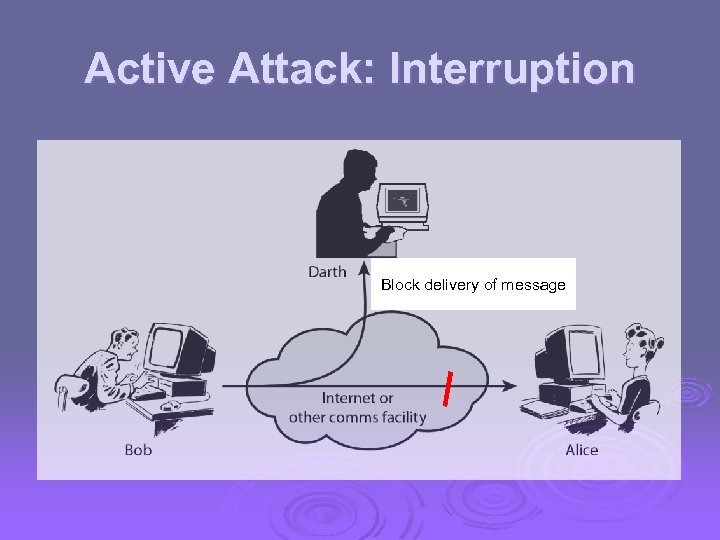 Active Attack: Interruption Block delivery of message
Active Attack: Interruption Block delivery of message
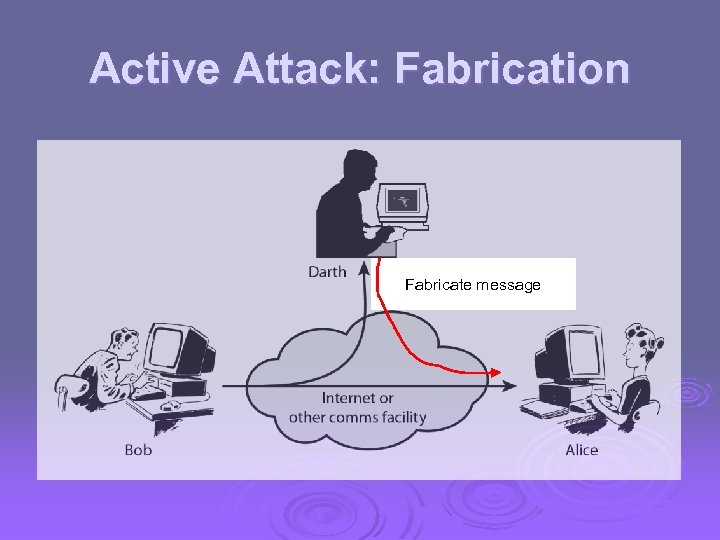 Active Attack: Fabrication Fabricate message
Active Attack: Fabrication Fabricate message
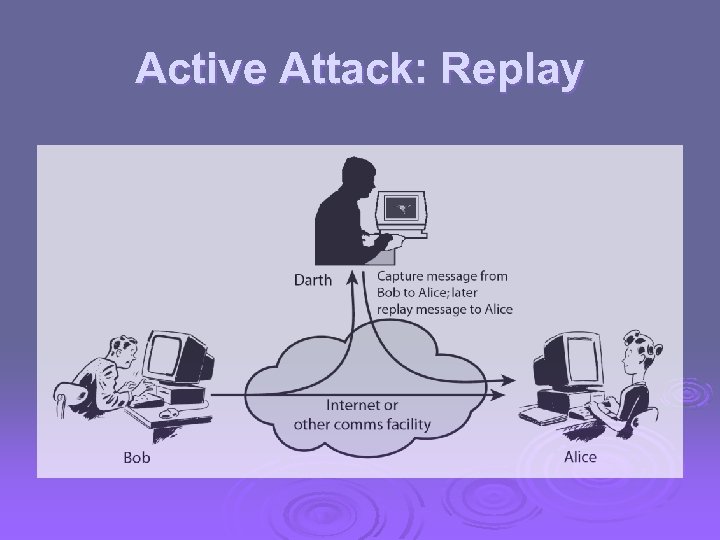 Active Attack: Replay
Active Attack: Replay
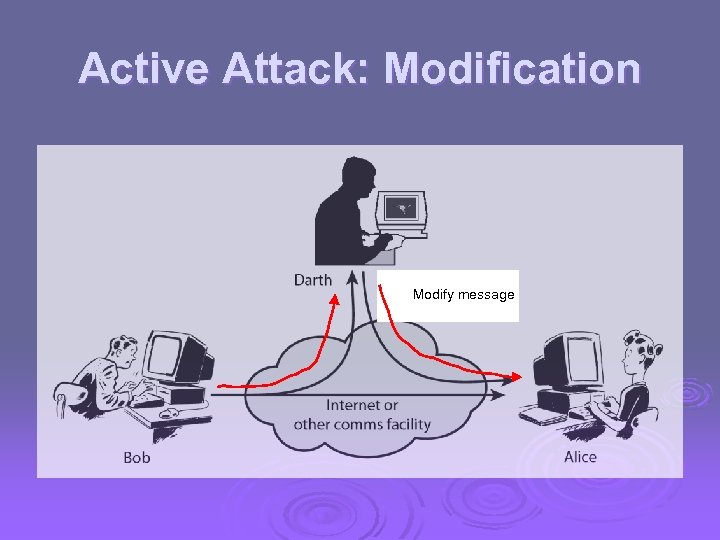 Active Attack: Modification Modify message
Active Attack: Modification Modify message
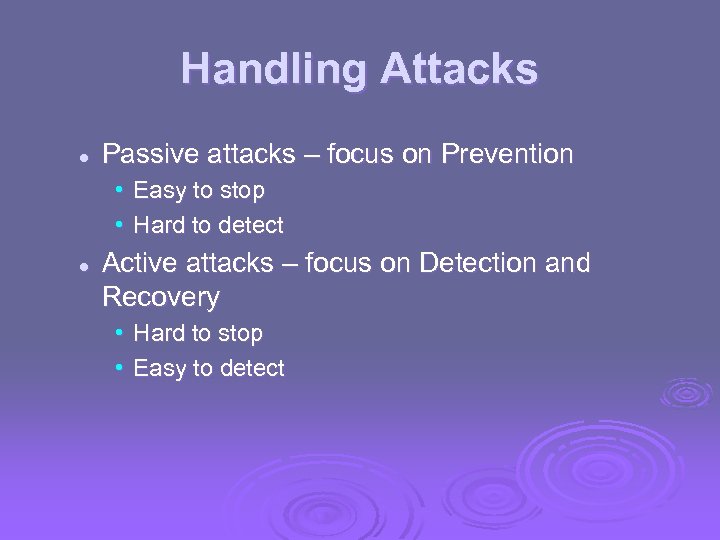 Handling Attacks l Passive attacks – focus on Prevention • Easy to stop • Hard to detect l Active attacks – focus on Detection and Recovery • Hard to stop • Easy to detect
Handling Attacks l Passive attacks – focus on Prevention • Easy to stop • Hard to detect l Active attacks – focus on Detection and Recovery • Hard to stop • Easy to detect
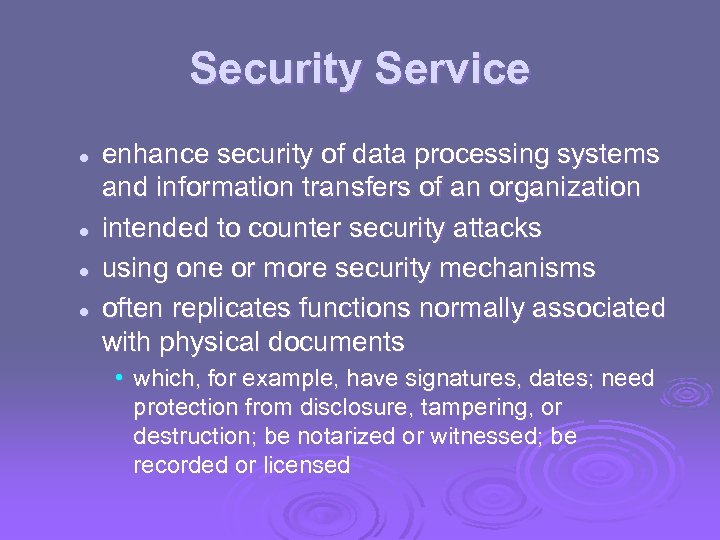 Security Service l l enhance security of data processing systems and information transfers of an organization intended to counter security attacks using one or more security mechanisms often replicates functions normally associated with physical documents • which, for example, have signatures, dates; need protection from disclosure, tampering, or destruction; be notarized or witnessed; be recorded or licensed
Security Service l l enhance security of data processing systems and information transfers of an organization intended to counter security attacks using one or more security mechanisms often replicates functions normally associated with physical documents • which, for example, have signatures, dates; need protection from disclosure, tampering, or destruction; be notarized or witnessed; be recorded or licensed
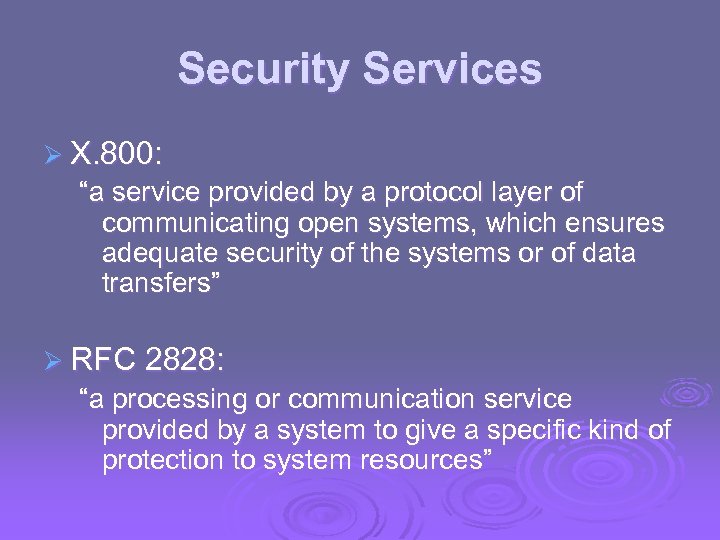 Security Services Ø X. 800: “a service provided by a protocol layer of communicating open systems, which ensures adequate security of the systems or of data transfers” Ø RFC 2828: “a processing or communication service provided by a system to give a specific kind of protection to system resources”
Security Services Ø X. 800: “a service provided by a protocol layer of communicating open systems, which ensures adequate security of the systems or of data transfers” Ø RFC 2828: “a processing or communication service provided by a system to give a specific kind of protection to system resources”
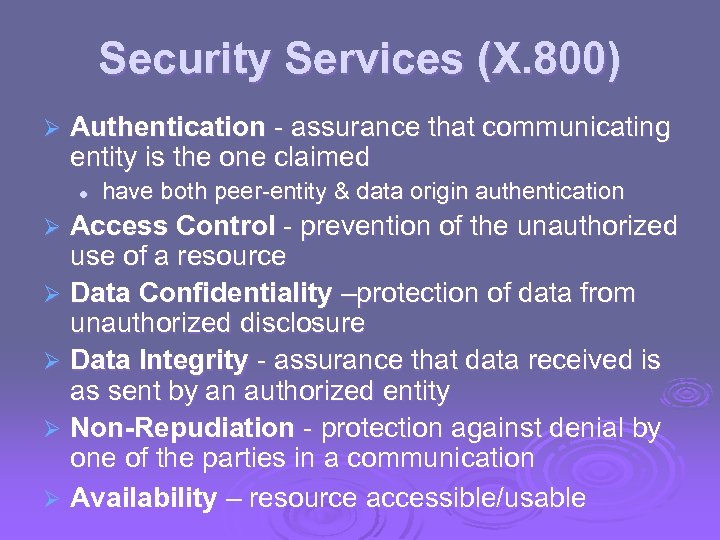 Security Services (X. 800) Ø Authentication - assurance that communicating entity is the one claimed l have both peer-entity & data origin authentication Access Control - prevention of the unauthorized use of a resource Ø Data Confidentiality –protection of data from unauthorized disclosure Ø Data Integrity - assurance that data received is as sent by an authorized entity Ø Non-Repudiation - protection against denial by one of the parties in a communication Ø Availability – resource accessible/usable Ø
Security Services (X. 800) Ø Authentication - assurance that communicating entity is the one claimed l have both peer-entity & data origin authentication Access Control - prevention of the unauthorized use of a resource Ø Data Confidentiality –protection of data from unauthorized disclosure Ø Data Integrity - assurance that data received is as sent by an authorized entity Ø Non-Repudiation - protection against denial by one of the parties in a communication Ø Availability – resource accessible/usable Ø
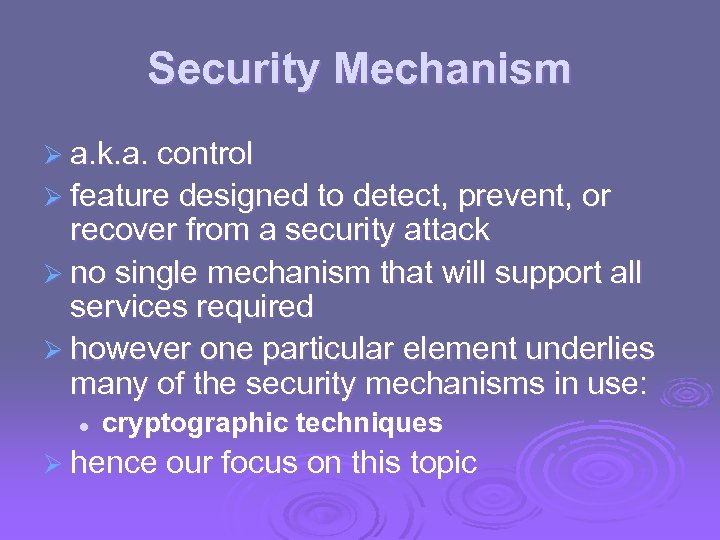 Security Mechanism Ø a. k. a. control Ø feature designed to detect, prevent, or recover from a security attack Ø no single mechanism that will support all services required Ø however one particular element underlies many of the security mechanisms in use: l cryptographic techniques Ø hence our focus on this topic
Security Mechanism Ø a. k. a. control Ø feature designed to detect, prevent, or recover from a security attack Ø no single mechanism that will support all services required Ø however one particular element underlies many of the security mechanisms in use: l cryptographic techniques Ø hence our focus on this topic
 Security Mechanisms (X. 800) Ø specific security mechanisms: l encipherment, digital signatures, access controls, data integrity, authentication exchange, traffic padding, routing control, notarization Ø pervasive security mechanisms: l trusted functionality, security labels, event detection, security audit trails, security recovery
Security Mechanisms (X. 800) Ø specific security mechanisms: l encipherment, digital signatures, access controls, data integrity, authentication exchange, traffic padding, routing control, notarization Ø pervasive security mechanisms: l trusted functionality, security labels, event detection, security audit trails, security recovery
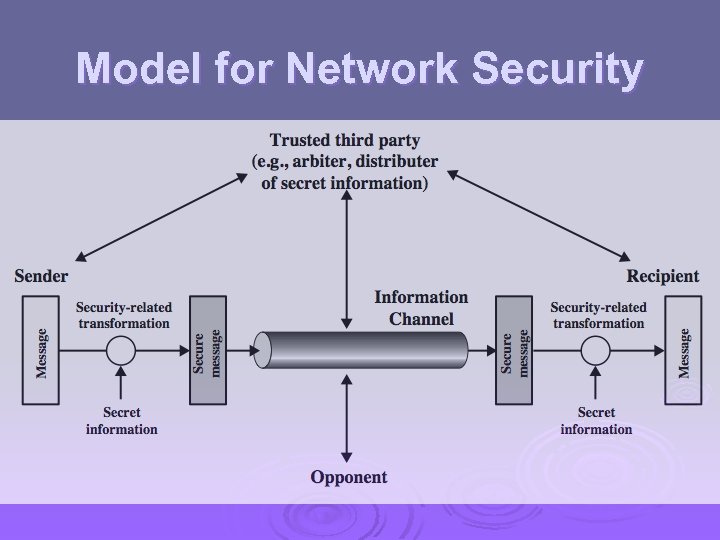 Model for Network Security
Model for Network Security
 In cryptography, a certificate authority or certification authority (CA) is an entity that issues digital certificates. A digital certificate certifies the ownership of a public key by the named subject of the certificate. Ø Mozilla, which is a non-profit organization, distributes several commercial CA certificates with its products. [1] While Mozilla developed their own policy, the CA/Browser Forum developed similar guidelines for CA trust. Ø Aside from commercial CAs, some providers issue digital certificates to the public at no cost; a noteworthy example is CAcert. Ø Symantec (which bought Veri. Sign's SSL interests and owns Thawte and Geotrust) with 35. 7% market share Ø Comodo SSL with 26. 9% Ø Global. Sign with 14. 9% Ø Go Daddy with 13. 0% Ø Ø Digi. Cert with 3. 4%[9]
In cryptography, a certificate authority or certification authority (CA) is an entity that issues digital certificates. A digital certificate certifies the ownership of a public key by the named subject of the certificate. Ø Mozilla, which is a non-profit organization, distributes several commercial CA certificates with its products. [1] While Mozilla developed their own policy, the CA/Browser Forum developed similar guidelines for CA trust. Ø Aside from commercial CAs, some providers issue digital certificates to the public at no cost; a noteworthy example is CAcert. Ø Symantec (which bought Veri. Sign's SSL interests and owns Thawte and Geotrust) with 35. 7% market share Ø Comodo SSL with 26. 9% Ø Global. Sign with 14. 9% Ø Go Daddy with 13. 0% Ø Ø Digi. Cert with 3. 4%[9]
 Model for Network Security Ø using this model requires us to: 1. 2. 3. 4. design a suitable algorithm for the security transformation generate the secret information (keys) used by the algorithm develop methods to distribute and share the secret information specify a protocol enabling the principals to use the transformation and secret information for a security service
Model for Network Security Ø using this model requires us to: 1. 2. 3. 4. design a suitable algorithm for the security transformation generate the secret information (keys) used by the algorithm develop methods to distribute and share the secret information specify a protocol enabling the principals to use the transformation and secret information for a security service
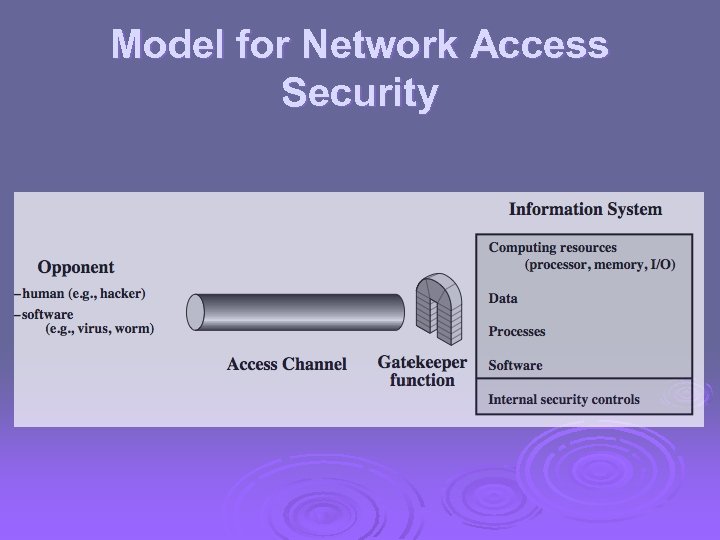 Model for Network Access Security
Model for Network Access Security
 Model for Network Access Security Ø using this model requires us to: select appropriate gatekeeper functions to identify users implement security controls to ensure only authorised users access designated information or resources 1. 2. Ø note that model does not include: 1. 2. 3. monitoring of system for successful penetration monitoring of authorized users for misuse audit logging forensic uses, etc.
Model for Network Access Security Ø using this model requires us to: select appropriate gatekeeper functions to identify users implement security controls to ensure only authorised users access designated information or resources 1. 2. Ø note that model does not include: 1. 2. 3. monitoring of system for successful penetration monitoring of authorized users for misuse audit logging forensic uses, etc.
 Summary Ø topic roadmap & standards organizations Ø security concepts: l confidentiality, integrity, availability Ø X. 800 security architecture Ø security attacks, services, mechanisms Ø models for network (access) security
Summary Ø topic roadmap & standards organizations Ø security concepts: l confidentiality, integrity, availability Ø X. 800 security architecture Ø security attacks, services, mechanisms Ø models for network (access) security


