544629690a31fb8d972458bef930deed.ppt
- Количество слайдов: 18
 CPS 512 Computer Security Private Key Algorithms RSA SSL CPS 290 Page 1
CPS 512 Computer Security Private Key Algorithms RSA SSL CPS 290 Page 1
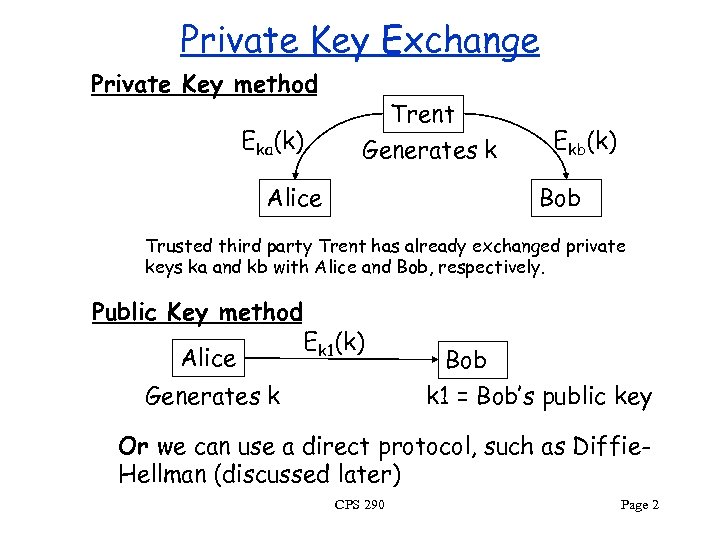 Private Key Exchange Private Key method Eka(k) Trent Generates k Alice Ekb(k) Bob Trusted third party Trent has already exchanged private keys ka and kb with Alice and Bob, respectively. Public Key method Alice Ek 1(k) Generates k Bob k 1 = Bob’s public key Or we can use a direct protocol, such as Diffie. Hellman (discussed later) CPS 290 Page 2
Private Key Exchange Private Key method Eka(k) Trent Generates k Alice Ekb(k) Bob Trusted third party Trent has already exchanged private keys ka and kb with Alice and Bob, respectively. Public Key method Alice Ek 1(k) Generates k Bob k 1 = Bob’s public key Or we can use a direct protocol, such as Diffie. Hellman (discussed later) CPS 290 Page 2
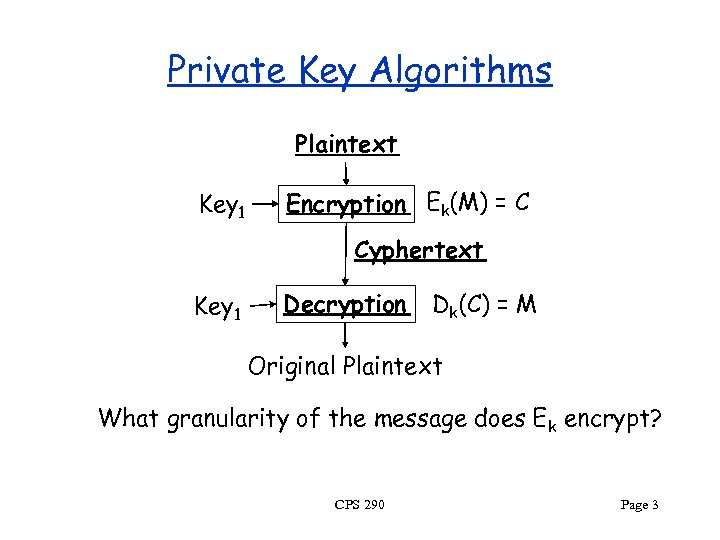 Private Key Algorithms Plaintext Key 1 Encryption Ek(M) = C Cyphertext Key 1 Decryption Dk(C) = M Original Plaintext What granularity of the message does Ek encrypt? CPS 290 Page 3
Private Key Algorithms Plaintext Key 1 Encryption Ek(M) = C Cyphertext Key 1 Decryption Dk(C) = M Original Plaintext What granularity of the message does Ek encrypt? CPS 290 Page 3
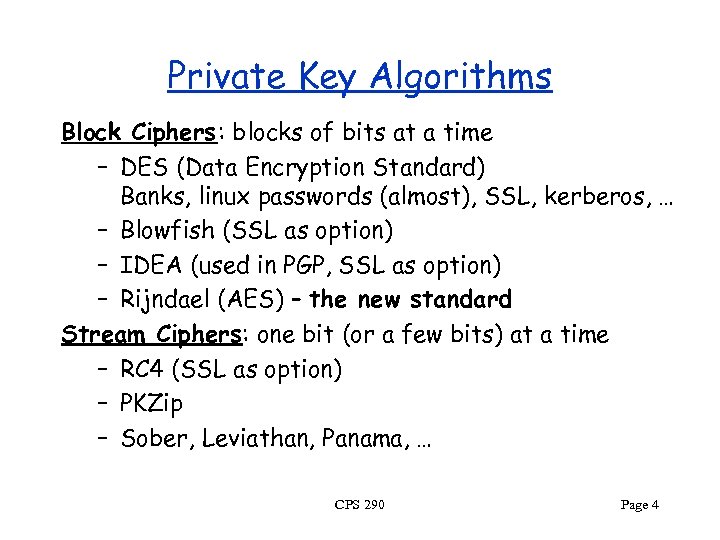 Private Key Algorithms Block Ciphers: blocks of bits at a time – DES (Data Encryption Standard) Banks, linux passwords (almost), SSL, kerberos, … – Blowfish (SSL as option) – IDEA (used in PGP, SSL as option) – Rijndael (AES) – the new standard Stream Ciphers: one bit (or a few bits) at a time – RC 4 (SSL as option) – PKZip – Sober, Leviathan, Panama, … CPS 290 Page 4
Private Key Algorithms Block Ciphers: blocks of bits at a time – DES (Data Encryption Standard) Banks, linux passwords (almost), SSL, kerberos, … – Blowfish (SSL as option) – IDEA (used in PGP, SSL as option) – Rijndael (AES) – the new standard Stream Ciphers: one bit (or a few bits) at a time – RC 4 (SSL as option) – PKZip – Sober, Leviathan, Panama, … CPS 290 Page 4
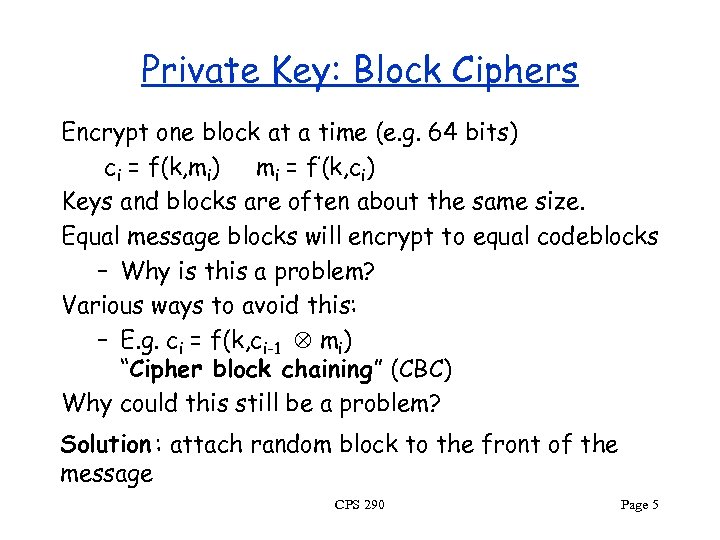 Private Key: Block Ciphers Encrypt one block at a time (e. g. 64 bits) ci = f(k, mi) mi = f’(k, ci) Keys and blocks are often about the same size. Equal message blocks will encrypt to equal codeblocks – Why is this a problem? Various ways to avoid this: – E. g. ci = f(k, ci-1 mi) “Cipher block chaining” (CBC) Why could this still be a problem? Solution : attach random block to the front of the message CPS 290 Page 5
Private Key: Block Ciphers Encrypt one block at a time (e. g. 64 bits) ci = f(k, mi) mi = f’(k, ci) Keys and blocks are often about the same size. Equal message blocks will encrypt to equal codeblocks – Why is this a problem? Various ways to avoid this: – E. g. ci = f(k, ci-1 mi) “Cipher block chaining” (CBC) Why could this still be a problem? Solution : attach random block to the front of the message CPS 290 Page 5
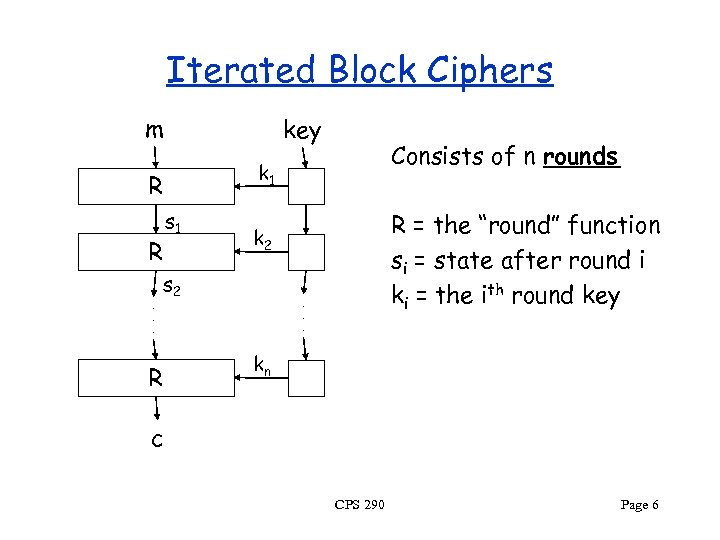 Iterated Block Ciphers m key R R. . . s 1 R = the “round” function si = state after round i ki = the ith round key k 2 s 2 R Consists of n rounds k 1 . . . kn c CPS 290 Page 6
Iterated Block Ciphers m key R R. . . s 1 R = the “round” function si = state after round i ki = the ith round key k 2 s 2 R Consists of n rounds k 1 . . . kn c CPS 290 Page 6
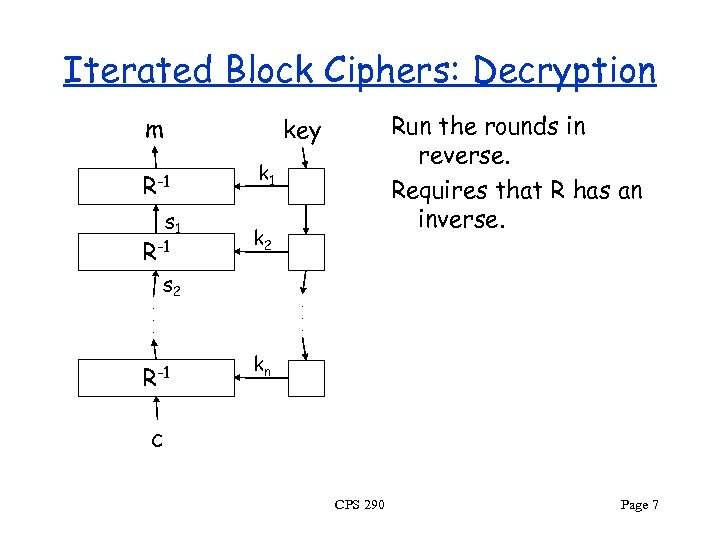 Iterated Block Ciphers: Decryption m R-1 s 1 R-1. . . Run the rounds in reverse. Requires that R has an inverse. key k 1 k 2 s 2 R-1 . . . kn c CPS 290 Page 7
Iterated Block Ciphers: Decryption m R-1 s 1 R-1. . . Run the rounds in reverse. Requires that R has an inverse. key k 1 k 2 s 2 R-1 . . . kn c CPS 290 Page 7
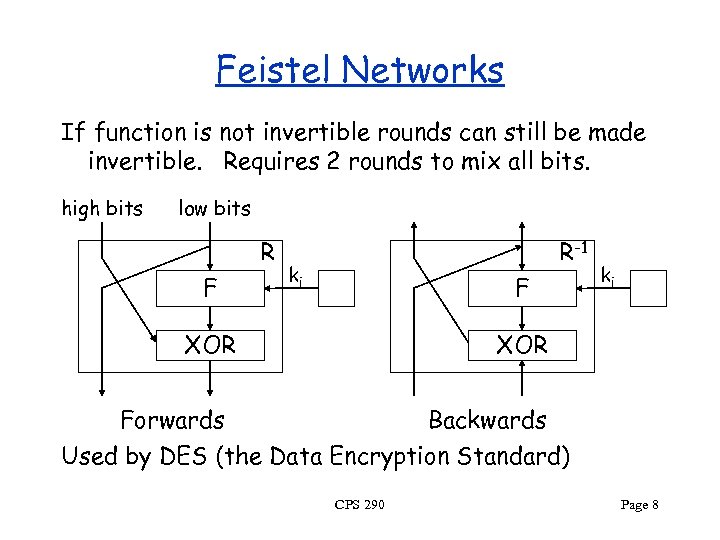 Feistel Networks If function is not invertible rounds can still be made invertible. Requires 2 rounds to mix all bits. high bits low bits R F R-1 ki F XOR ki XOR Forwards Backwards Used by DES (the Data Encryption Standard) CPS 290 Page 8
Feistel Networks If function is not invertible rounds can still be made invertible. Requires 2 rounds to mix all bits. high bits low bits R F R-1 ki F XOR ki XOR Forwards Backwards Used by DES (the Data Encryption Standard) CPS 290 Page 8
 Product Ciphers Each round has two components: – Substitution on smaller blocks Decorrelate input and output: “confusion” – Permutation across the smaller blocks Mix the bits: “diffusion” Substitution-Permutation Product Cipher Avalanche Effect: 1 bit of input should affect all output bits, ideally evenly, and for all settings of other in bits CPS 290 Page 9
Product Ciphers Each round has two components: – Substitution on smaller blocks Decorrelate input and output: “confusion” – Permutation across the smaller blocks Mix the bits: “diffusion” Substitution-Permutation Product Cipher Avalanche Effect: 1 bit of input should affect all output bits, ideally evenly, and for all settings of other in bits CPS 290 Page 9
 Rijndael Selected by AES (Advanced Encryption Standard, part of NIST) as the new private-key encryption standard. Based on an open “competition”. – Competition started Sept. 1997. – Narrowed to 5 Sept. 1999 • MARS by IBM, RC 6 by RSA, Twofish by Counterplane, Serpent, and Rijndael – Rijndael selected Oct. 2000. – Official Oct. 2001? (AES page on Rijndael) Designed by Rijmen and Daemen (Dutch) CPS 290 Page 10
Rijndael Selected by AES (Advanced Encryption Standard, part of NIST) as the new private-key encryption standard. Based on an open “competition”. – Competition started Sept. 1997. – Narrowed to 5 Sept. 1999 • MARS by IBM, RC 6 by RSA, Twofish by Counterplane, Serpent, and Rijndael – Rijndael selected Oct. 2000. – Official Oct. 2001? (AES page on Rijndael) Designed by Rijmen and Daemen (Dutch) CPS 290 Page 10
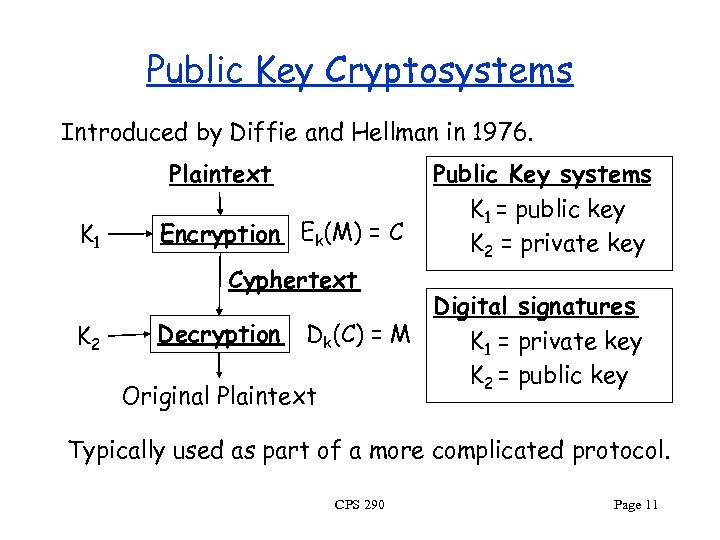 Public Key Cryptosystems Introduced by Diffie and Hellman in 1976. Plaintext K 1 Encryption Ek(M) = C Cyphertext K 2 Public Key systems K 1 = public key K 2 = private key Digital signatures Decryption Dk(C) = M K 1 = private key K 2 = public key Original Plaintext Typically used as part of a more complicated protocol. CPS 290 Page 11
Public Key Cryptosystems Introduced by Diffie and Hellman in 1976. Plaintext K 1 Encryption Ek(M) = C Cyphertext K 2 Public Key systems K 1 = public key K 2 = private key Digital signatures Decryption Dk(C) = M K 1 = private key K 2 = public key Original Plaintext Typically used as part of a more complicated protocol. CPS 290 Page 11
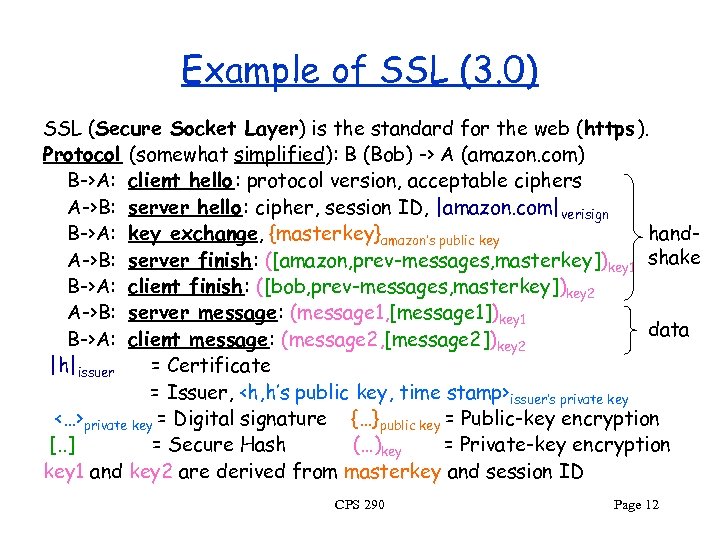 Example of SSL (3. 0) SSL (Secure Socket Layer) is the standard for the web (https ). Protocol (somewhat simplified): B (Bob) -> A (amazon. com) B->A: client hello: protocol version, acceptable ciphers A->B: server hello: cipher, session ID, |amazon. com|verisign hand. B->A: key exchange, {masterkey}amazon’s public key A->B: server finish: ([amazon, prev-messages, masterkey])key 1 shake B->A: client finish : ([bob, prev-messages, masterkey])key 2 A->B: server message: (message 1, [message 1])key 1 data B->A: client message: (message 2, [message 2])key 2 |h|issuer = Certificate = Issuer,
Example of SSL (3. 0) SSL (Secure Socket Layer) is the standard for the web (https ). Protocol (somewhat simplified): B (Bob) -> A (amazon. com) B->A: client hello: protocol version, acceptable ciphers A->B: server hello: cipher, session ID, |amazon. com|verisign hand. B->A: key exchange, {masterkey}amazon’s public key A->B: server finish: ([amazon, prev-messages, masterkey])key 1 shake B->A: client finish : ([bob, prev-messages, masterkey])key 2 A->B: server message: (message 1, [message 1])key 1 data B->A: client message: (message 2, [message 2])key 2 |h|issuer = Certificate = Issuer,
 Server Name Issue The client expects the server to send a certificate matching the domain of the requested Web site. But the client doesn’t tell the server which Web site it is requesting -- not a problem if server hosts only one site. For servers hosting multiple secure Web sites, the “solution” is to assign multiple IP addresses to the network interface, one for each certificate. Akamai uses approximately 10 M IP addresses for this purpose. Better solution: “server name” extension in successor to SSL, TLS CPS 290 Page 13
Server Name Issue The client expects the server to send a certificate matching the domain of the requested Web site. But the client doesn’t tell the server which Web site it is requesting -- not a problem if server hosts only one site. For servers hosting multiple secure Web sites, the “solution” is to assign multiple IP addresses to the network interface, one for each certificate. Akamai uses approximately 10 M IP addresses for this purpose. Better solution: “server name” extension in successor to SSL, TLS CPS 290 Page 13
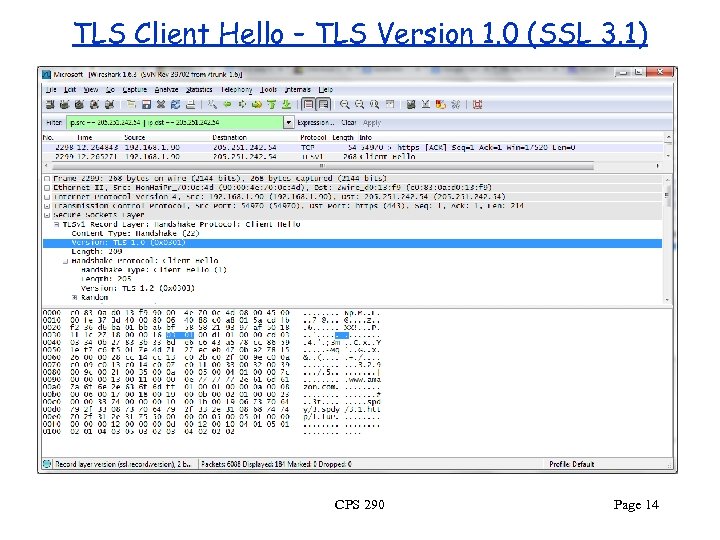 TLS Client Hello – TLS Version 1. 0 (SSL 3. 1) CPS 290 Page 14
TLS Client Hello – TLS Version 1. 0 (SSL 3. 1) CPS 290 Page 14
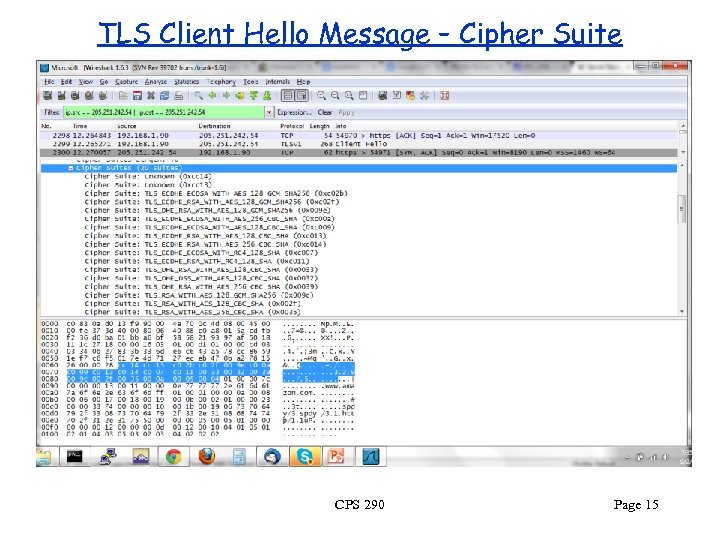 TLS Client Hello Message – Cipher Suite CPS 290 Page 15
TLS Client Hello Message – Cipher Suite CPS 290 Page 15
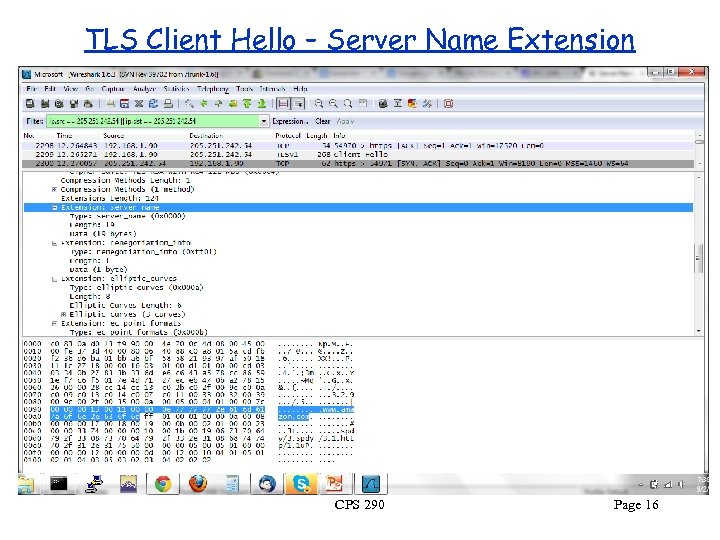 TLS Client Hello – Server Name Extension CPS 290 Page 16
TLS Client Hello – Server Name Extension CPS 290 Page 16
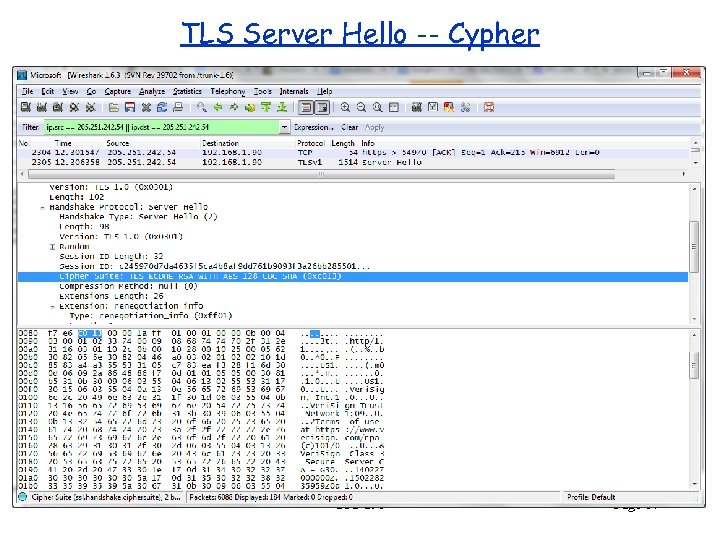 TLS Server Hello -- Cypher CPS 290 Page 17
TLS Server Hello -- Cypher CPS 290 Page 17
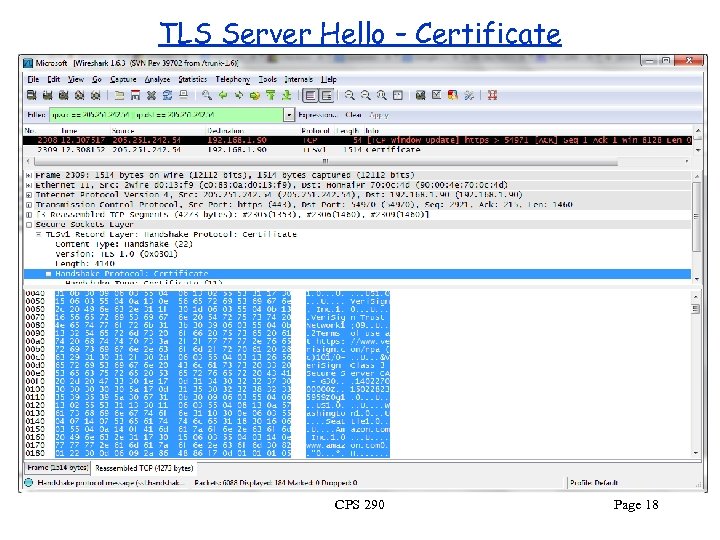 TLS Server Hello – Certificate CPS 290 Page 18
TLS Server Hello – Certificate CPS 290 Page 18


