25e2077546beb4a8e3af401401336f2a.ppt
- Количество слайдов: 20
 Course Outline • Traditional Static Program Analysis – Theory • Compiler Optimizations; Control Flow Graphs • Data-flow Analysis: Data-flow frameworks – Classic analyses and applications • Software Testing • Dynamic Program Analysis
Course Outline • Traditional Static Program Analysis – Theory • Compiler Optimizations; Control Flow Graphs • Data-flow Analysis: Data-flow frameworks – Classic analyses and applications • Software Testing • Dynamic Program Analysis
 Announcements • Homework 1 – I will be done grading on Thursday • Homework 2 – Due Thursday, March 3 rd • Problems with CS system • My other email: milana 2@rpi. edu
Announcements • Homework 1 – I will be done grading on Thursday • Homework 2 – Due Thursday, March 3 rd • Problems with CS system • My other email: milana 2@rpi. edu
 Outline • Data-flow frameworks – – – Monotone frameworks Distributive frameworks The “Maximal Fixed Point” (MFP) solution The “Meet Over all Paths” (MOP) solution Analysis safety (correctness) and analysis precision • Reading: Compilers: Principles, Techniques and Tools, by Aho, Lam, Sethi and Ullman, Chapter 9. 3
Outline • Data-flow frameworks – – – Monotone frameworks Distributive frameworks The “Maximal Fixed Point” (MFP) solution The “Meet Over all Paths” (MOP) solution Analysis safety (correctness) and analysis precision • Reading: Compilers: Principles, Techniques and Tools, by Aho, Lam, Sethi and Ullman, Chapter 9. 3
 Monotone Dataflow Frameworks • Generic data-flow equations: in(i) = V out(m) m in pred(i) out(i) = fi (in(i)) Parameters: – Property space: in(i), out(i) are elements of a property space • Combination operator V: U for may problems and ∩ for must • problems Initial values set to the 0 (smallest element) of the property space – Transfer functions: fi is associated with node i – If we instantiate these parameters in a certain way, then our analysis is an instance of the monotone dataflow framework
Monotone Dataflow Frameworks • Generic data-flow equations: in(i) = V out(m) m in pred(i) out(i) = fi (in(i)) Parameters: – Property space: in(i), out(i) are elements of a property space • Combination operator V: U for may problems and ∩ for must • problems Initial values set to the 0 (smallest element) of the property space – Transfer functions: fi is associated with node i – If we instantiate these parameters in a certain way, then our analysis is an instance of the monotone dataflow framework
 Monotone Frameworks: Requirements • The property space must be a complete lattice L under partial order ≤ where L satisfies the Ascending Chain Condition – – The combination operator V Initial values set to the 0 of L • The transfer functions: fi: L L Each fi must be monotone If fi is distributive, then our analysis is said to be distributive, a very special instance of the monotone dataflow framework
Monotone Frameworks: Requirements • The property space must be a complete lattice L under partial order ≤ where L satisfies the Ascending Chain Condition – – The combination operator V Initial values set to the 0 of L • The transfer functions: fi: L L Each fi must be monotone If fi is distributive, then our analysis is said to be distributive, a very special instance of the monotone dataflow framework
 The Maximal Fixed Point /* Initialize to initial values */ in(1)=Initial. Value; in(1) = UNDEF for m : = 2 to n do in(m) : = 0; in(m) : = Ø W : = {1, 2, …, n} /* put every node on the worklist */ 1 (MFP) while W ≠ Ø do { remove i from W; out(i) = fi(in(i)); out. RD(i) = in. RD(i)∩pres(i)Ugen(i) for j in successors(i) if out(i) ≤ in(j) then { if out. RD(i) not subset of in. RD (j) in(j) = out(i) V in(j); in. RD(j) = out(i) U in. RD(j) if j not in W do add j to W } } 1. The Least Fixed Point (LFP) actually…
The Maximal Fixed Point /* Initialize to initial values */ in(1)=Initial. Value; in(1) = UNDEF for m : = 2 to n do in(m) : = 0; in(m) : = Ø W : = {1, 2, …, n} /* put every node on the worklist */ 1 (MFP) while W ≠ Ø do { remove i from W; out(i) = fi(in(i)); out. RD(i) = in. RD(i)∩pres(i)Ugen(i) for j in successors(i) if out(i) ≤ in(j) then { if out. RD(i) not subset of in. RD (j) in(j) = out(i) V in(j); in. RD(j) = out(i) U in. RD(j) if j not in W do add j to W } } 1. The Least Fixed Point (LFP) actually…
 Properties of the algorithm • Lemma 1: The algorithm terminates. Sketch of the proof: We have ink(j) ≤ ink+1(j) and since L has ACC, in(j) changes at most O(h) times. Each j is put on W at most O(h) times (h is the height of the lattice L). Complexity: At each iteration, the analysis examines e(j)out edges. Thus, number of basic operations is bounded by h*(e(1)out+…+e(N)out)=O(h*E). We can do better on certain graphs.
Properties of the algorithm • Lemma 1: The algorithm terminates. Sketch of the proof: We have ink(j) ≤ ink+1(j) and since L has ACC, in(j) changes at most O(h) times. Each j is put on W at most O(h) times (h is the height of the lattice L). Complexity: At each iteration, the analysis examines e(j)out edges. Thus, number of basic operations is bounded by h*(e(1)out+…+e(N)out)=O(h*E). We can do better on certain graphs.
 Properties of the Algorithm • Lemma 2: The algorithm computes the least solution of the dataflow equations. – For every node i MFP computes solution MFP(i) = {in(i), out(i)}, such that every other solution {in’(i), out’(i)} of the dataflow equations is “larger” than the MFP • Lemma 3: The algorithm computes a correct (safe) solution.
Properties of the Algorithm • Lemma 2: The algorithm computes the least solution of the dataflow equations. – For every node i MFP computes solution MFP(i) = {in(i), out(i)}, such that every other solution {in’(i), out’(i)} of the dataflow equations is “larger” than the MFP • Lemma 3: The algorithm computes a correct (safe) solution.
 Example 1. z: =x+y 2. if (z > 500) 3. skip in. AE(1) = Ø out. AE(1) = (in. AE(1)-Ez) {x+y} in. AE(2) = out. AE(1) V out. AE(3) out. AE(2) = in. AE(2) inout(3) = out. AE(2) out. AE(3) = in. AE(3) Solution 1 Ø {x+y} Solution 2 Ø {x+y} Ø Ø {x+y} Ø Ø Equivalent to: in. AE(2) = {x+y} V in. AE(2) and recall that V is ∩ (i. e. , set intersection). That is why we needed to initialize in. AE(2) and the other initial values to the universal set of expressions (0 of the Available Expressions lattice), rather than to the more intuitive empty set.
Example 1. z: =x+y 2. if (z > 500) 3. skip in. AE(1) = Ø out. AE(1) = (in. AE(1)-Ez) {x+y} in. AE(2) = out. AE(1) V out. AE(3) out. AE(2) = in. AE(2) inout(3) = out. AE(2) out. AE(3) = in. AE(3) Solution 1 Ø {x+y} Solution 2 Ø {x+y} Ø Ø {x+y} Ø Ø Equivalent to: in. AE(2) = {x+y} V in. AE(2) and recall that V is ∩ (i. e. , set intersection). That is why we needed to initialize in. AE(2) and the other initial values to the universal set of expressions (0 of the Available Expressions lattice), rather than to the more intuitive empty set.
 Meet Over All Paths (MOP) Solution 1 ρ n 1 n 2 … nk n • Desired dataflow information at n is obtained by traversing ALL PATHS from ρ to n. For every path p=(ρ, n 1, n 2. . . , nk) we compute fnk(…fn 2(fn 1(init(ρ)))) • The MOP at entry of n is V fnk(…fn 2(fn 1(init(ρ)))) p in paths from ρ to n • The MOP is the best summary of dataflow facts possible to compute with this static analysis
Meet Over All Paths (MOP) Solution 1 ρ n 1 n 2 … nk n • Desired dataflow information at n is obtained by traversing ALL PATHS from ρ to n. For every path p=(ρ, n 1, n 2. . . , nk) we compute fnk(…fn 2(fn 1(init(ρ)))) • The MOP at entry of n is V fnk(…fn 2(fn 1(init(ρ)))) p in paths from ρ to n • The MOP is the best summary of dataflow facts possible to compute with this static analysis
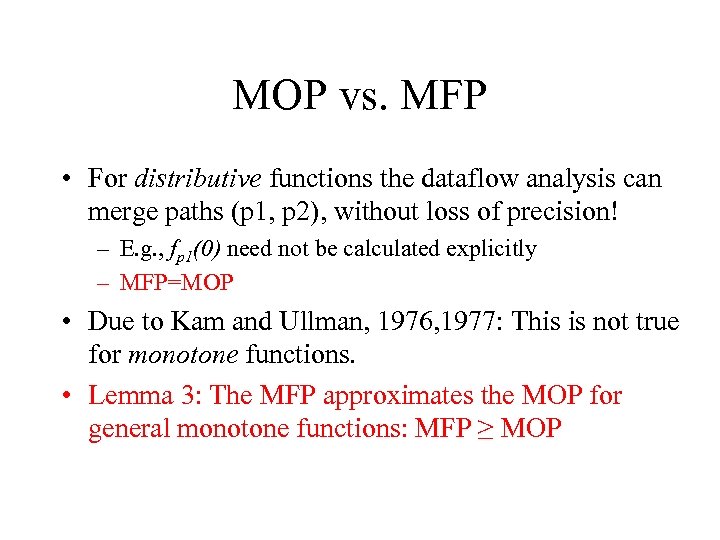 MOP vs. MFP • For distributive functions the dataflow analysis can merge paths (p 1, p 2), without loss of precision! – E. g. , fp 1(0) need not be calculated explicitly – MFP=MOP • Due to Kam and Ullman, 1976, 1977: This is not true for monotone functions. • Lemma 3: The MFP approximates the MOP for general monotone functions: MFP ≥ MOP
MOP vs. MFP • For distributive functions the dataflow analysis can merge paths (p 1, p 2), without loss of precision! – E. g. , fp 1(0) need not be calculated explicitly – MFP=MOP • Due to Kam and Ullman, 1976, 1977: This is not true for monotone functions. • Lemma 3: The MFP approximates the MOP for general monotone functions: MFP ≥ MOP
 Safety of a Dataflow Solution • Safe (also, correct or sound) solution overestimates the best possible dataflow solution, i. e. , x ≥ MOP is an approximate solution • Acceptable solution is better than what we can do with the MFP, i. e. , x ≤ MFP • Between MOP and MFP are interesting solutions Acceptable Safe MOP 0
Safety of a Dataflow Solution • Safe (also, correct or sound) solution overestimates the best possible dataflow solution, i. e. , x ≥ MOP is an approximate solution • Acceptable solution is better than what we can do with the MFP, i. e. , x ≤ MFP • Between MOP and MFP are interesting solutions Acceptable Safe MOP 0
 Precision of a Dataflow Solution • Precise solution is one that is close to MOP – A precise solution contains few spurious facts • MOP ≤ X ≤ Y: X is more precise than Y
Precision of a Dataflow Solution • Precise solution is one that is close to MOP – A precise solution contains few spurious facts • MOP ≤ X ≤ Y: X is more precise than Y
 Safe Solutions • In Available Expressions the 1 is the empty set, and the combination operator is set intersection. – It is safe to err by saying that an expression is NOT AVAILABLE when it might be. – We compute a smaller set. Thus, under our definition of ≤, this solution is larger than the MOP. • In Reaching Definitions the 1 is the universal set of definitions, the combination is the union. – It is safe to err by saying that a definition reaches a node when in fact it DOES NOT REACH the node. – We compute a larger set. Thus, under our definition of ≤ (which is natural), the solution is larger than the MOP
Safe Solutions • In Available Expressions the 1 is the empty set, and the combination operator is set intersection. – It is safe to err by saying that an expression is NOT AVAILABLE when it might be. – We compute a smaller set. Thus, under our definition of ≤, this solution is larger than the MOP. • In Reaching Definitions the 1 is the universal set of definitions, the combination is the union. – It is safe to err by saying that a definition reaches a node when in fact it DOES NOT REACH the node. – We compute a larger set. Thus, under our definition of ≤ (which is natural), the solution is larger than the MOP
 Two Views of Reaching Definitions Defs Safe solutions are here; they are larger sets of definitions. MOP/MFP 0 element Join semi-lattice formulation. We used this formulation.
Two Views of Reaching Definitions Defs Safe solutions are here; they are larger sets of definitions. MOP/MFP 0 element Join semi-lattice formulation. We used this formulation.
 Two Views of Reaching Definitions Ø def 1 … Defs 1 element defk. . MOP/MFP Safe solutions are larger sets of definitions than MOP Meet semi-lattice formulation
Two Views of Reaching Definitions Ø def 1 … Defs 1 element defk. . MOP/MFP Safe solutions are larger sets of definitions than MOP Meet semi-lattice formulation
 Kam and Ullman Results • On monotone dataflow frameworks, iterative algorithms converge to the MFP of the dataflow equations (our Lemmas 1 and 2) • MOP ≤ MFP (in our join formulation) (our Lemma 3) • One monotone framework that is not distributive is constant propagation • The MOP is undecidable for an arbitrary instance of a monotone framework.
Kam and Ullman Results • On monotone dataflow frameworks, iterative algorithms converge to the MFP of the dataflow equations (our Lemmas 1 and 2) • MOP ≤ MFP (in our join formulation) (our Lemma 3) • One monotone framework that is not distributive is constant propagation • The MOP is undecidable for an arbitrary instance of a monotone framework.
 Many Applications! • White-box testing: compute coverage – Control-flow-based testing – Data-flow-based testing • Intuitively, test each def-use chain • Regression testing – Analyze changes and select regression tests that actually test changed code
Many Applications! • White-box testing: compute coverage – Control-flow-based testing – Data-flow-based testing • Intuitively, test each def-use chain • Regression testing – Analyze changes and select regression tests that actually test changed code
 Many Applications! • Reverse engineering – UML class diagrams – UML sequence diagrams – Many tools do these; Eclipse plug-ins • Automated refactoring – Analyze program, prove “safety” of the refactoring – Eclipse plug-ins
Many Applications! • Reverse engineering – UML class diagrams – UML sequence diagrams – Many tools do these; Eclipse plug-ins • Automated refactoring – Analyze program, prove “safety” of the refactoring – Eclipse plug-ins
 Many Applications! • Static debugging – Memory errors in C/C++ programs • Memory leaks • Null pointer dereferences • Array-out-of-bound accesses – Concurrency errors in shared-memory apps • Data-races • Atomicity violations • Deadlocks
Many Applications! • Static debugging – Memory errors in C/C++ programs • Memory leaks • Null pointer dereferences • Array-out-of-bound accesses – Concurrency errors in shared-memory apps • Data-races • Atomicity violations • Deadlocks


