 Course Administration
Course Administration
 Outline of Today’s lecture
Outline of Today’s lecture
 Cryptographic Hash Functions
Cryptographic Hash Functions
 Some Applications of Hash Functions
Some Applications of Hash Functions
 Hash Output Length
Hash Output Length
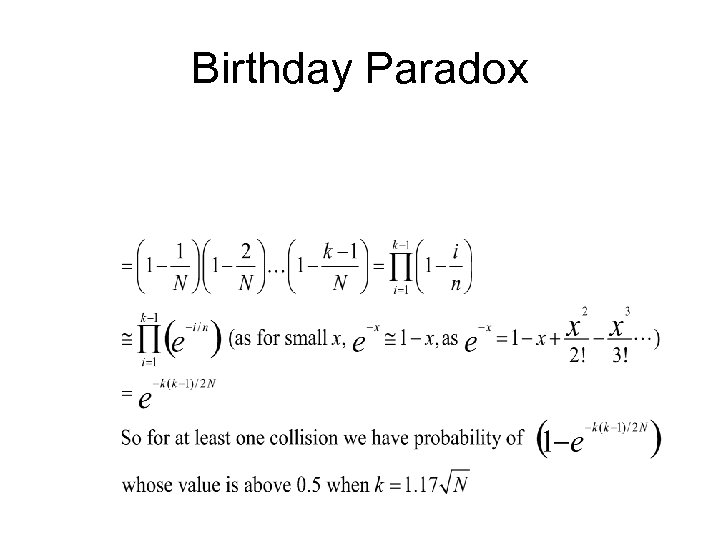 Birthday Paradox
Birthday Paradox
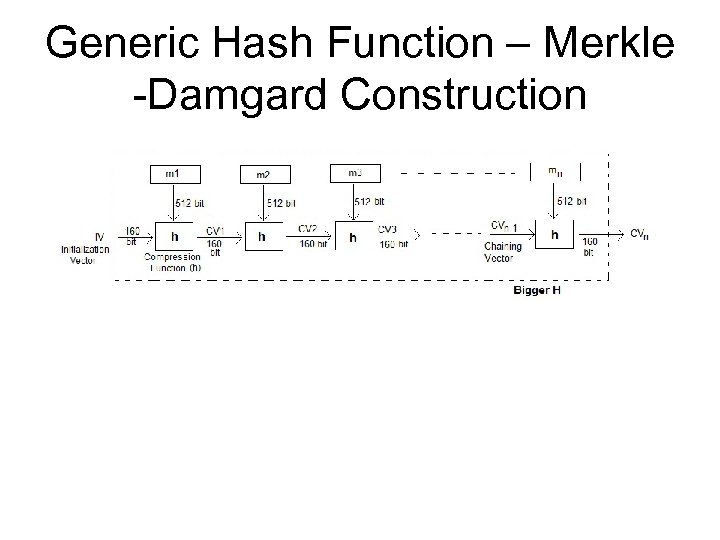 Generic Hash Function – Merkle -Damgard Construction
Generic Hash Function – Merkle -Damgard Construction
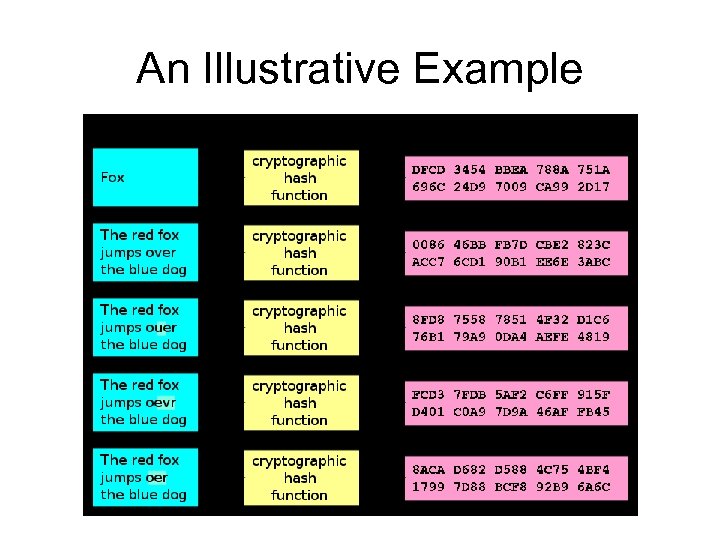 An Illustrative Example
An Illustrative Example
 Practical Examples
Practical Examples
 Further Reading
Further Reading
 Message Authentication Codes
Message Authentication Codes
 MAC – Functions
MAC – Functions
 Security Notion for MAC
Security Notion for MAC
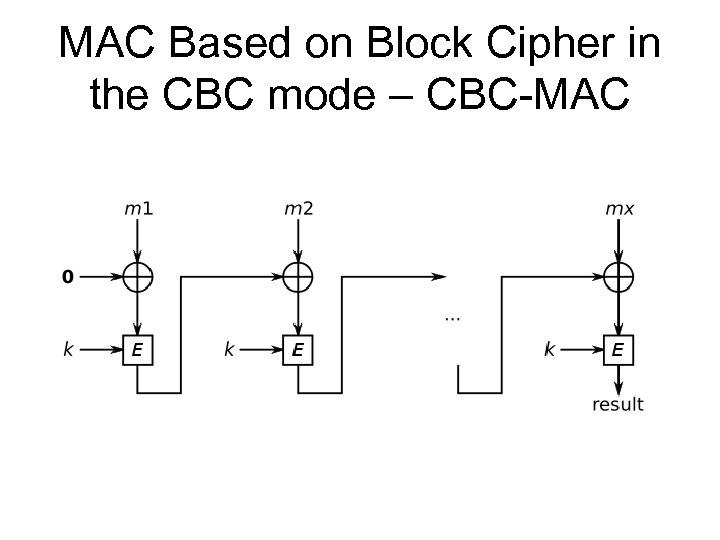 MAC Based on Block Cipher in the CBC mode – CBC-MAC
MAC Based on Block Cipher in the CBC mode – CBC-MAC
 CBC-MAC
CBC-MAC
 HMAC: MAC using Hash Functions
HMAC: MAC using Hash Functions
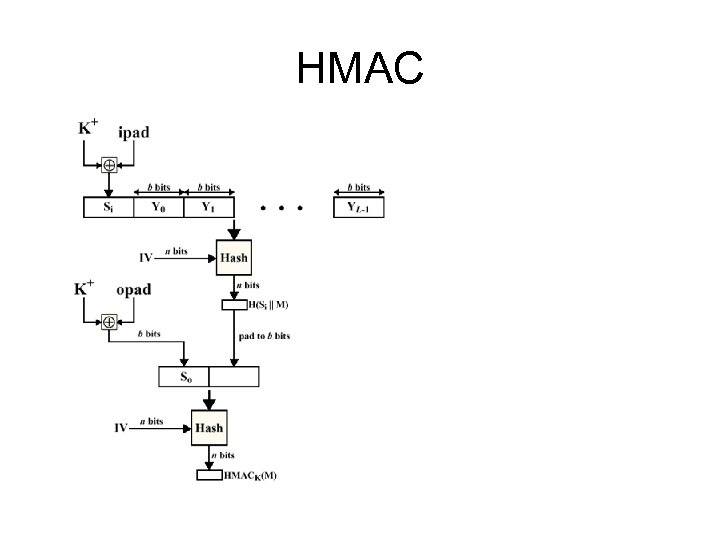 HMAC
HMAC
 Security of HMAC
Security of HMAC
 Further Reading
Further Reading
 Email Security
Email Security
 Email Security Enhancements
Email Security Enhancements
 Pretty Good Privacy (PGP)
Pretty Good Privacy (PGP)
 PGP Operation – Authentication
PGP Operation – Authentication
 PGP Operation – Confidentiality
PGP Operation – Confidentiality
 PGP Operation – Compression
PGP Operation – Compression
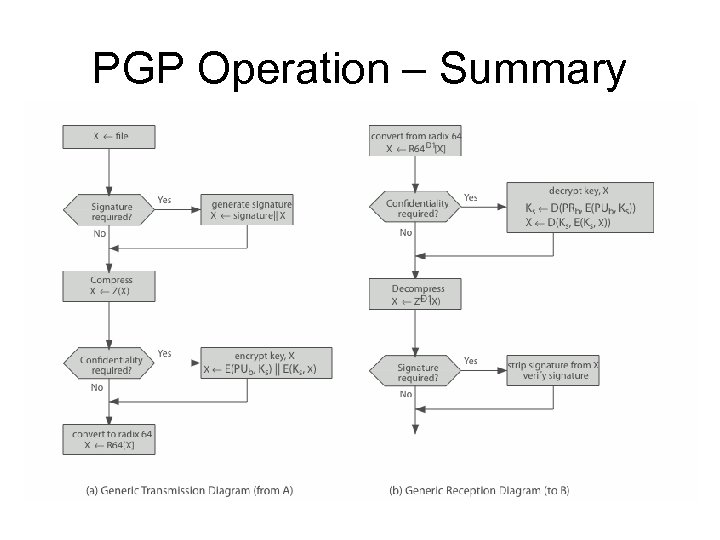 PGP Operation – Summary
PGP Operation – Summary
 PGP Session Keys
PGP Session Keys
 PGP Public & Private Keys
PGP Public & Private Keys
 PGP Key Rings
PGP Key Rings
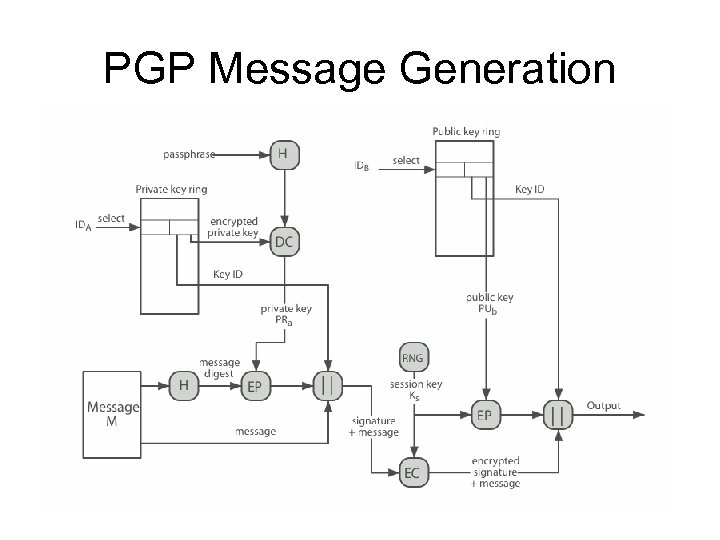 PGP Message Generation
PGP Message Generation
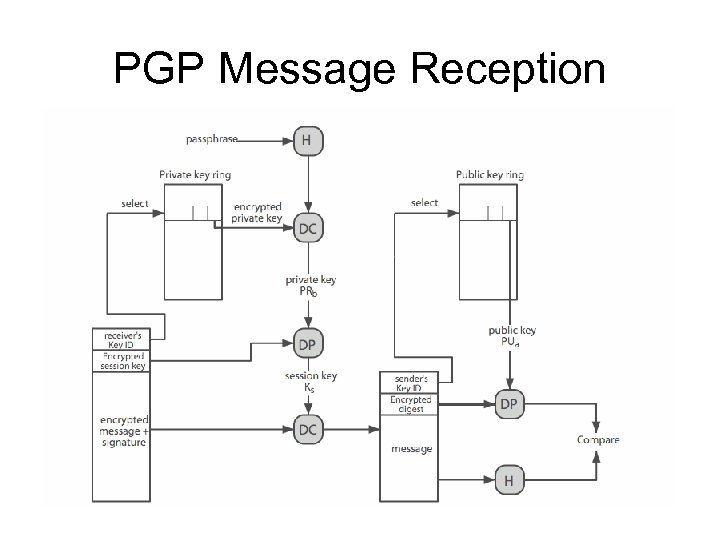 PGP Message Reception
PGP Message Reception
 PGP Key Distribution
PGP Key Distribution
 PGP Key Distribution
PGP Key Distribution
 PGP Key Distribution Issues
PGP Key Distribution Issues
 PGP in Practice
PGP in Practice
 References
References
 Key Distribution
Key Distribution
 “Private Key” Distribution: An Attempt
“Private Key” Distribution: An Attempt
 Some questions
Some questions
 Key Distribution
Key Distribution
 Public Key Distribution
Public Key Distribution
 Naming and Certificates
Naming and Certificates
 Types of Certificates
Types of Certificates
 Public Key Certificate
Public Key Certificate
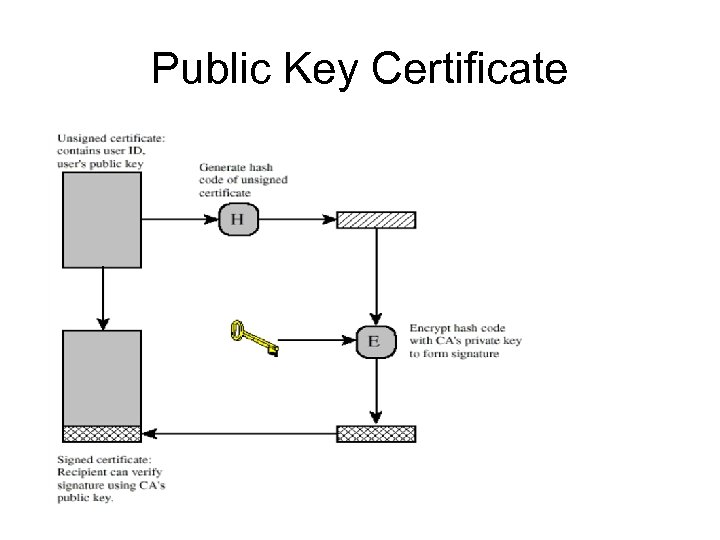 Public Key Certificate
Public Key Certificate
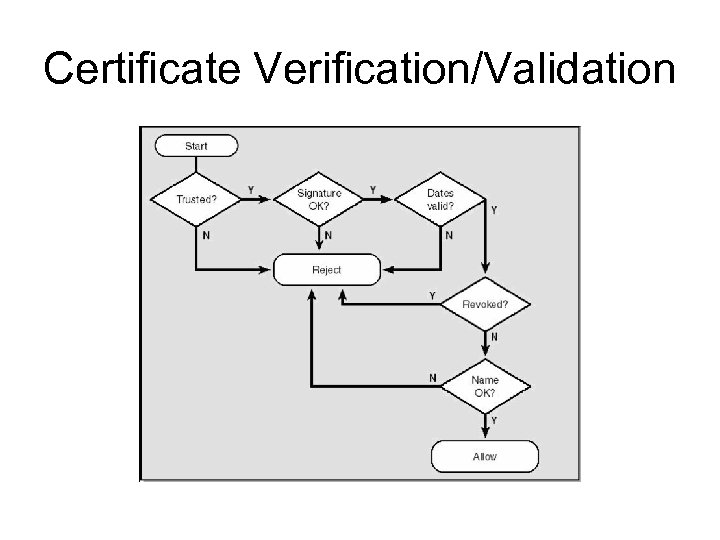 Certificate Verification/Validation
Certificate Verification/Validation
 Certificate Revocation
Certificate Revocation
 X. 509
X. 509
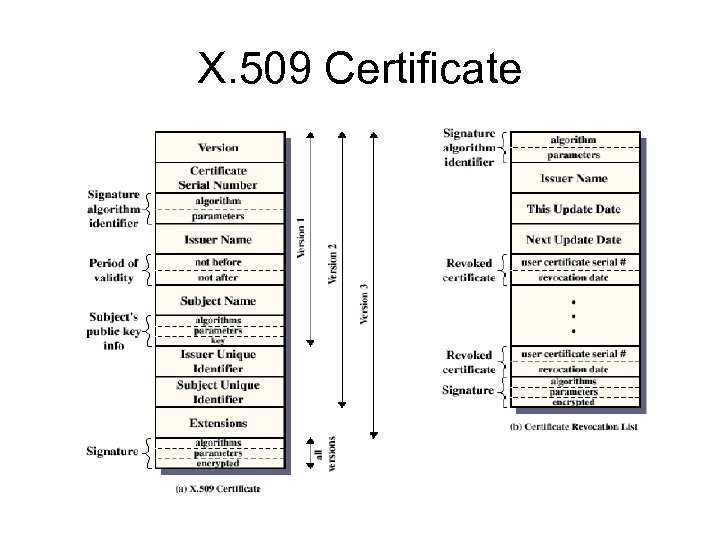 X. 509 Certificate
X. 509 Certificate
 Advantages of CA Over KDC
Advantages of CA Over KDC
 Public-key Infrastructure (PKI)
Public-key Infrastructure (PKI)
 Problems with PKI – Private Key
Problems with PKI – Private Key
 Problems with PKI - Conflicts
Problems with PKI - Conflicts
 Trustworthiness of Issuer
Trustworthiness of Issuer
 Further Reading
Further Reading
 Further Reading
Further Reading
 Some questions
Some questions
 Some Questions
Some Questions