758efdd95ec9d46d034dd2a046bca4f2.ppt
- Количество слайдов: 50
 COSIC: the first 35 years of cryptology research in Leuven http: //www. esat. kuleuven. be/cosic 1
COSIC: the first 35 years of cryptology research in Leuven http: //www. esat. kuleuven. be/cosic 1
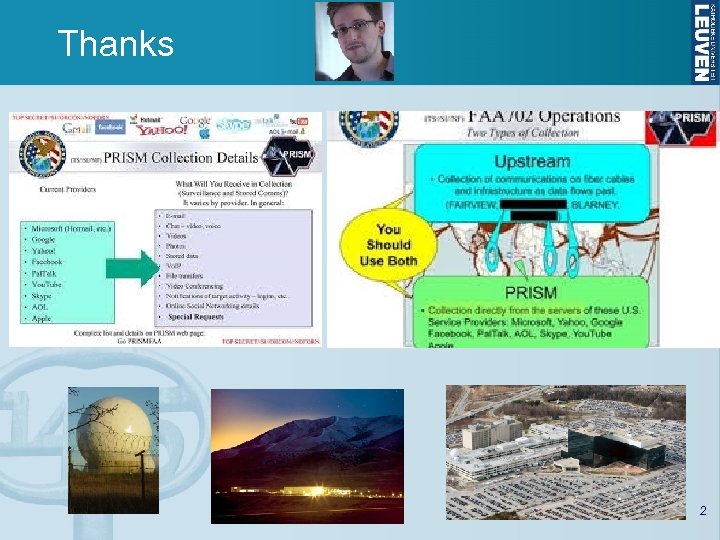 Thanks 2
Thanks 2
 Outline • Crypto 101 • COSIC: a brief overview • COSIC: some success stories Life can only be understood backwards; but it must be lived forwards. Soren Kierkegaard 3
Outline • Crypto 101 • COSIC: a brief overview • COSIC: some success stories Life can only be understood backwards; but it must be lived forwards. Soren Kierkegaard 3
 COMSEC 4
COMSEC 4
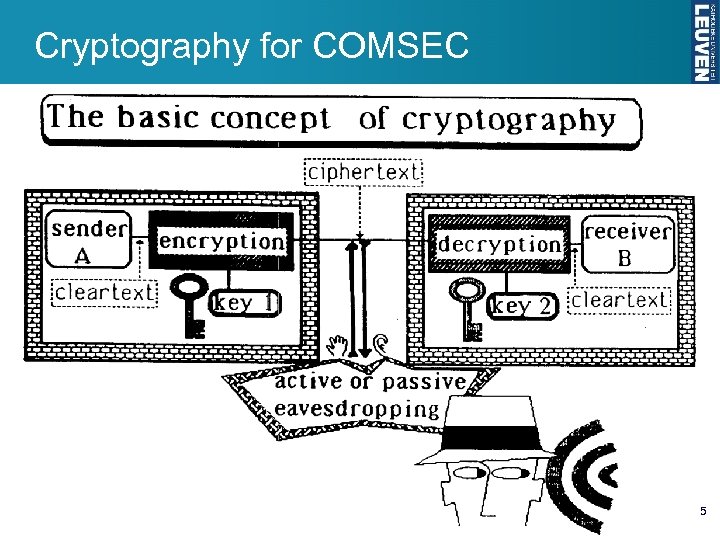 Cryptography for COMSEC 5
Cryptography for COMSEC 5
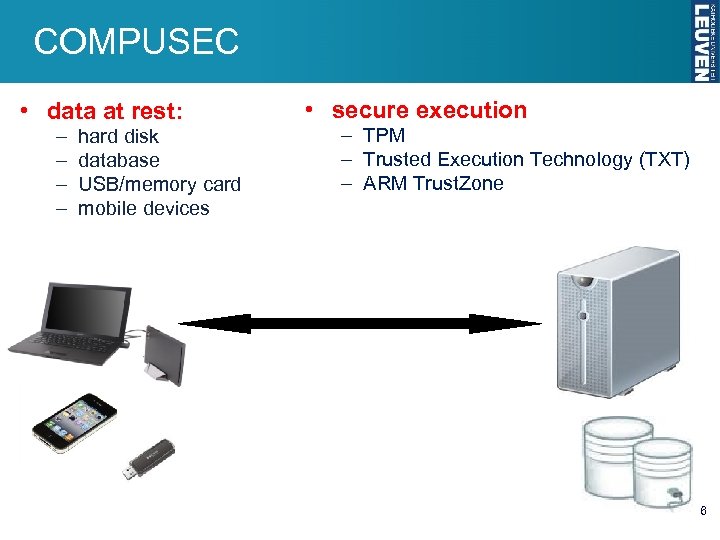 COMPUSEC • data at rest: – – hard disk database USB/memory card mobile devices • secure execution – TPM – Trusted Execution Technology (TXT) – ARM Trust. Zone 6
COMPUSEC • data at rest: – – hard disk database USB/memory card mobile devices • secure execution – TPM – Trusted Execution Technology (TXT) – ARM Trust. Zone 6
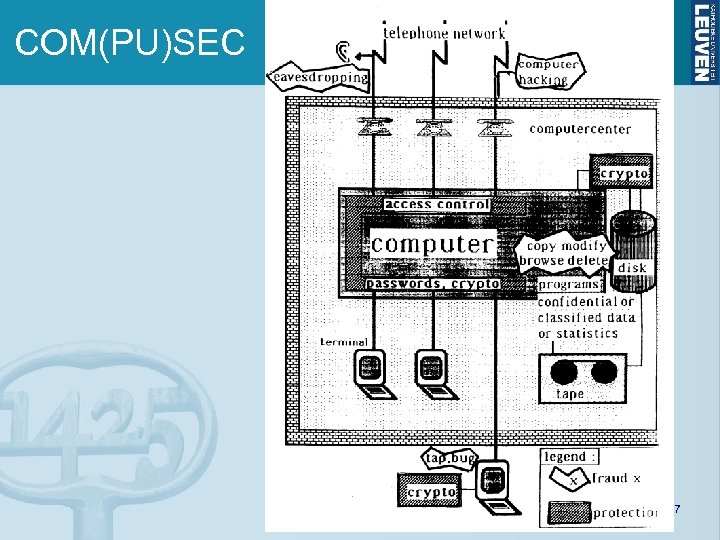 COM(PU)SEC 7
COM(PU)SEC 7
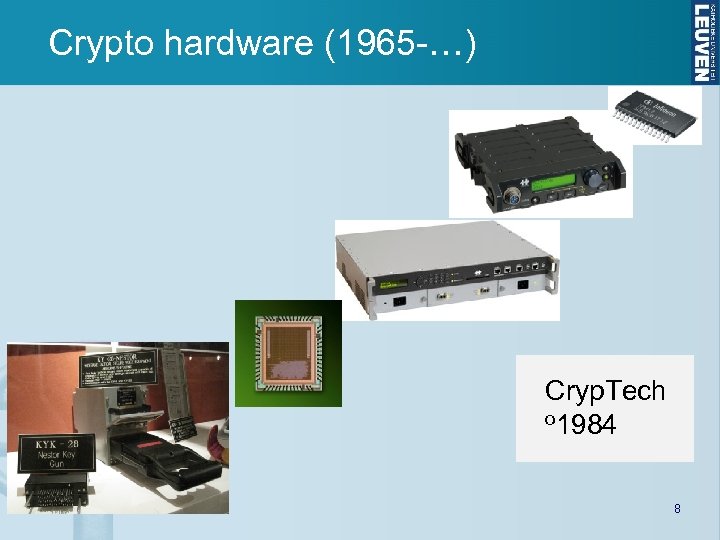 Crypto hardware (1965 -…) Cryp. Tech o 1984 8
Crypto hardware (1965 -…) Cryp. Tech o 1984 8
 Crypto software (1990 -…) Utimaco o 1992 9
Crypto software (1990 -…) Utimaco o 1992 9
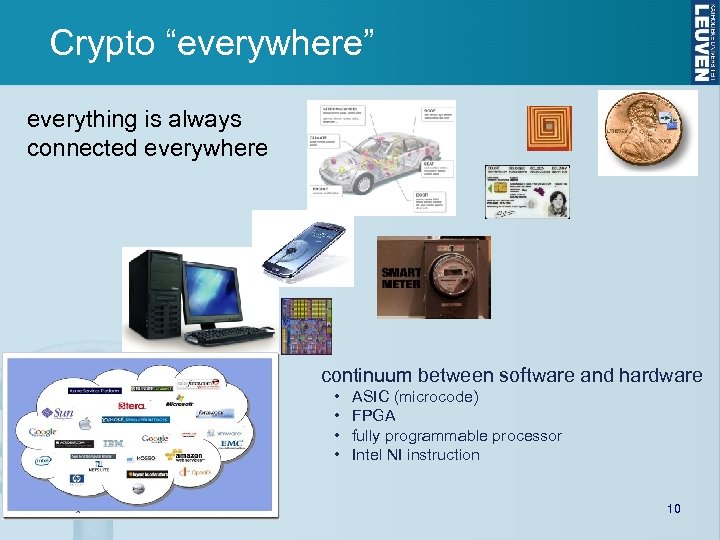 Crypto “everywhere” everything is always connected everywhere continuum between software and hardware • • ASIC (microcode) FPGA fully programmable processor Intel NI instruction 10
Crypto “everywhere” everything is always connected everywhere continuum between software and hardware • • ASIC (microcode) FPGA fully programmable processor Intel NI instruction 10
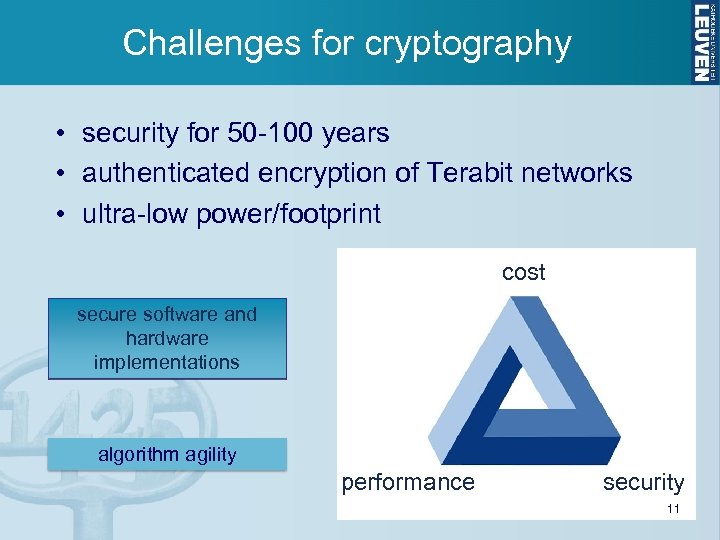 Challenges for cryptography • security for 50 -100 years • authenticated encryption of Terabit networks • ultra-low power/footprint cost secure software and hardware implementations algorithm agility performance security 11
Challenges for cryptography • security for 50 -100 years • authenticated encryption of Terabit networks • ultra-low power/footprint cost secure software and hardware implementations algorithm agility performance security 11
 Challenges for cryptography 12
Challenges for cryptography 12
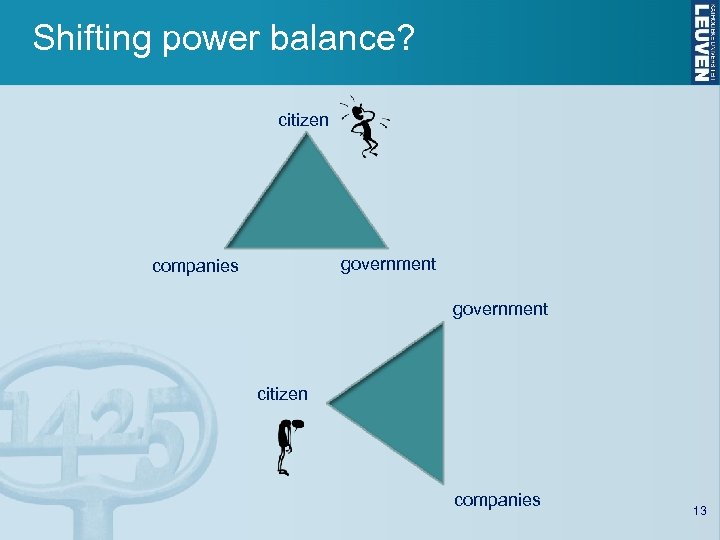 Shifting power balance? citizen government companies government citizen companies 13
Shifting power balance? citizen government companies government citizen companies 13
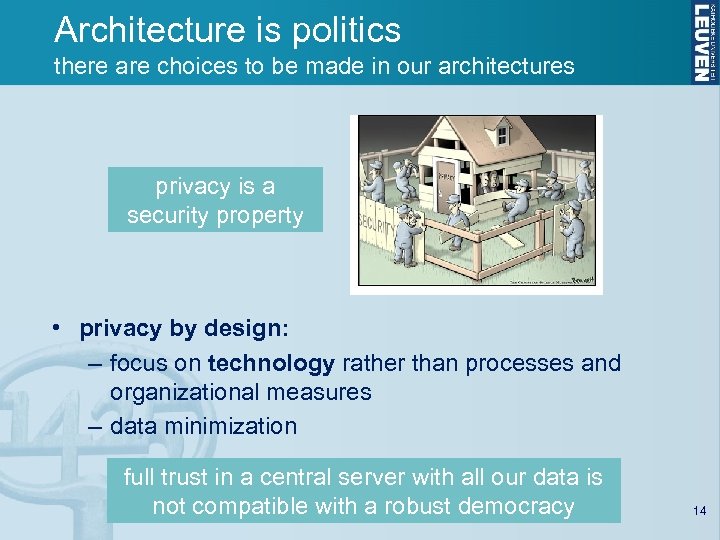 Architecture is politics there are choices to be made in our architectures privacy is a security property • privacy by design: – focus on technology rather than processes and organizational measures – data minimization full trust in a central server with all our data is not compatible with a robust democracy 14
Architecture is politics there are choices to be made in our architectures privacy is a security property • privacy by design: – focus on technology rather than processes and organizational measures – data minimization full trust in a central server with all our data is not compatible with a robust democracy 14
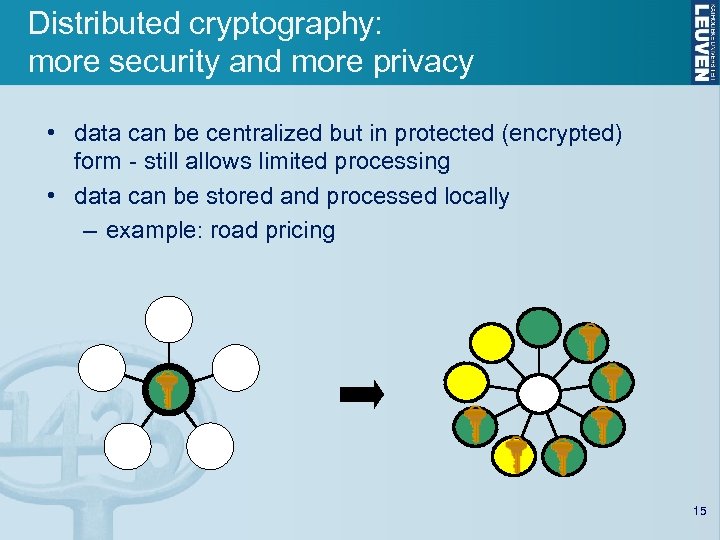 Distributed cryptography: more security and more privacy • data can be centralized but in protected (encrypted) form - still allows limited processing • data can be stored and processed locally – example: road pricing 15
Distributed cryptography: more security and more privacy • data can be centralized but in protected (encrypted) form - still allows limited processing • data can be stored and processed locally – example: road pricing 15
 Outline • Crypto 101 • COSIC: a brief overview • COSIC: some success stories 16
Outline • Crypto 101 • COSIC: a brief overview • COSIC: some success stories 16
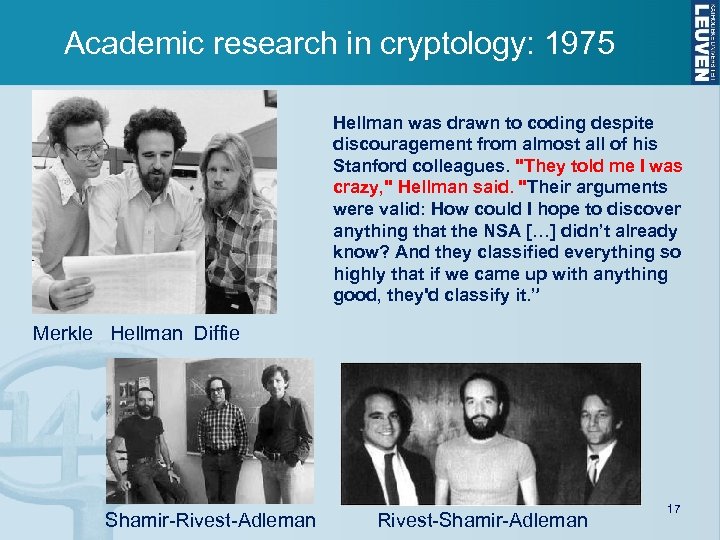 Academic research in cryptology: 1975 Hellman was drawn to coding despite discouragement from almost all of his Stanford colleagues. "They told me I was crazy, " Hellman said. "Their arguments were valid: How could I hope to discover anything that the NSA […] didn’t already know? And they classified everything so highly that if we came up with anything good, they'd classify it. ” Merkle Hellman Diffie Shamir-Rivest-Adleman Rivest-Shamir-Adleman 17
Academic research in cryptology: 1975 Hellman was drawn to coding despite discouragement from almost all of his Stanford colleagues. "They told me I was crazy, " Hellman said. "Their arguments were valid: How could I hope to discover anything that the NSA […] didn’t already know? And they classified everything so highly that if we came up with anything good, they'd classify it. ” Merkle Hellman Diffie Shamir-Rivest-Adleman Rivest-Shamir-Adleman 17
 COSIC (o 1978) 18
COSIC (o 1978) 18
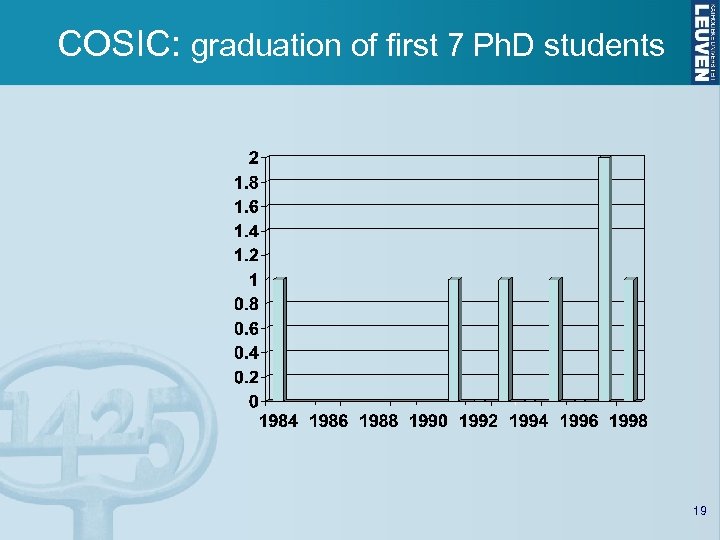 COSIC: graduation of first 7 Ph. D students 19
COSIC: graduation of first 7 Ph. D students 19
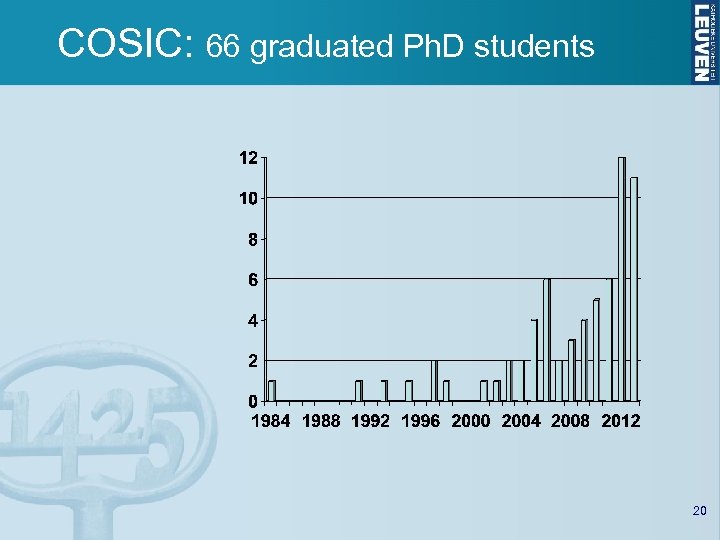 COSIC: 66 graduated Ph. D students 20
COSIC: 66 graduated Ph. D students 20
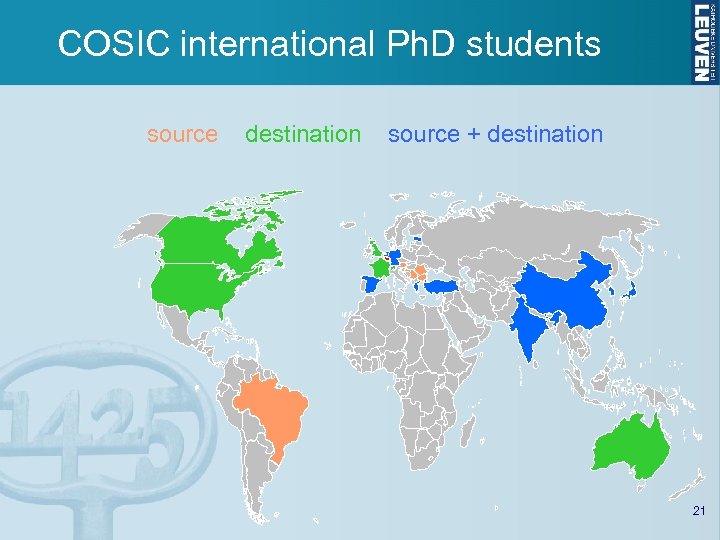 COSIC international Ph. D students source destination source + destination 21
COSIC international Ph. D students source destination source + destination 21
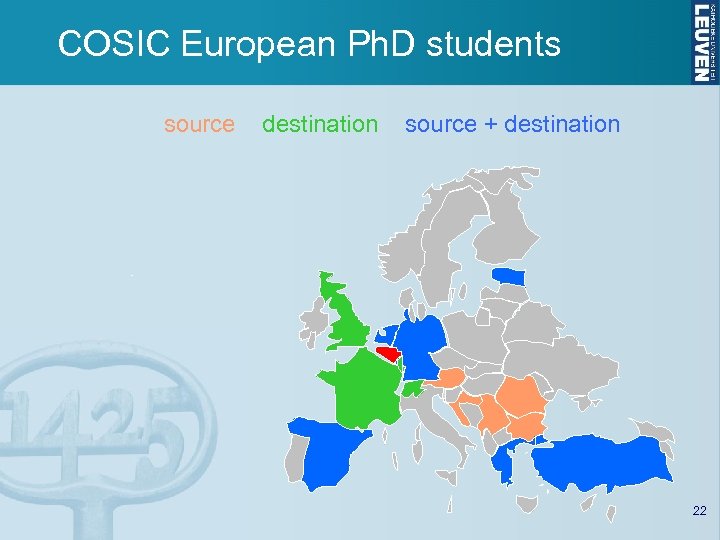 COSIC European Ph. D students source destination source + destination 22
COSIC European Ph. D students source destination source + destination 22
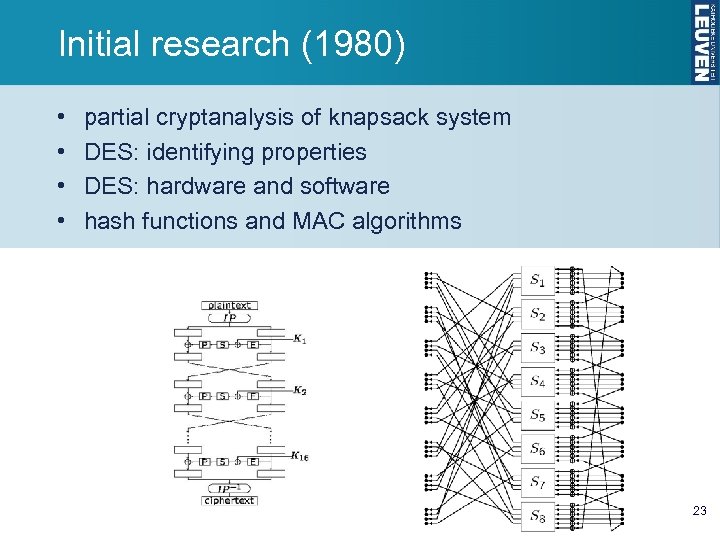 Initial research (1980) • • partial cryptanalysis of knapsack system DES: identifying properties DES: hardware and software hash functions and MAC algorithms 23
Initial research (1980) • • partial cryptanalysis of knapsack system DES: identifying properties DES: hardware and software hash functions and MAC algorithms 23
 Eurocrypt’ 89 - Houthalen FSE’ 94, CMS’ 99, Eurocrypt’ 00, FSE’ 02, FSE ’ 08, ESORICS’ 10, CHES’ 12 24
Eurocrypt’ 89 - Houthalen FSE’ 94, CMS’ 99, Eurocrypt’ 00, FSE’ 02, FSE ’ 08, ESORICS’ 10, CHES’ 12 24
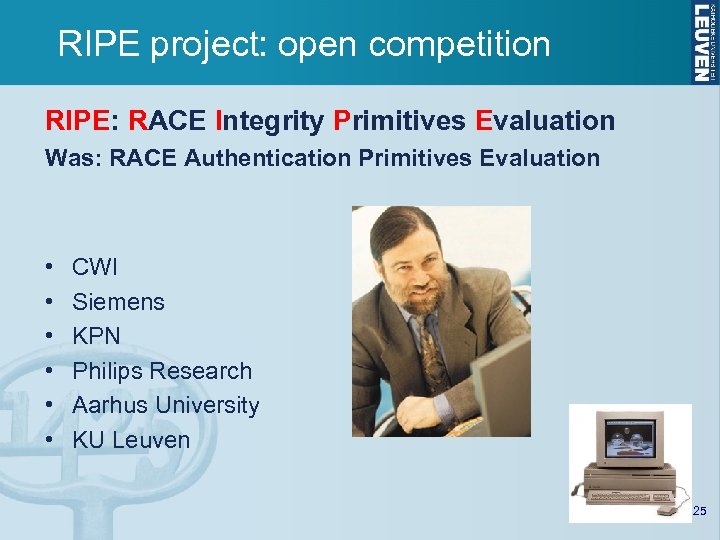 RIPE project: open competition RIPE: RACE Integrity Primitives Evaluation Was: RACE Authentication Primitives Evaluation • • • CWI Siemens KPN Philips Research Aarhus University KU Leuven 25
RIPE project: open competition RIPE: RACE Integrity Primitives Evaluation Was: RACE Authentication Primitives Evaluation • • • CWI Siemens KPN Philips Research Aarhus University KU Leuven 25
 Outline • Crypto 101 • COSIC: a brief overview • COSIC: some success stories 26
Outline • Crypto 101 • COSIC: a brief overview • COSIC: some success stories 26
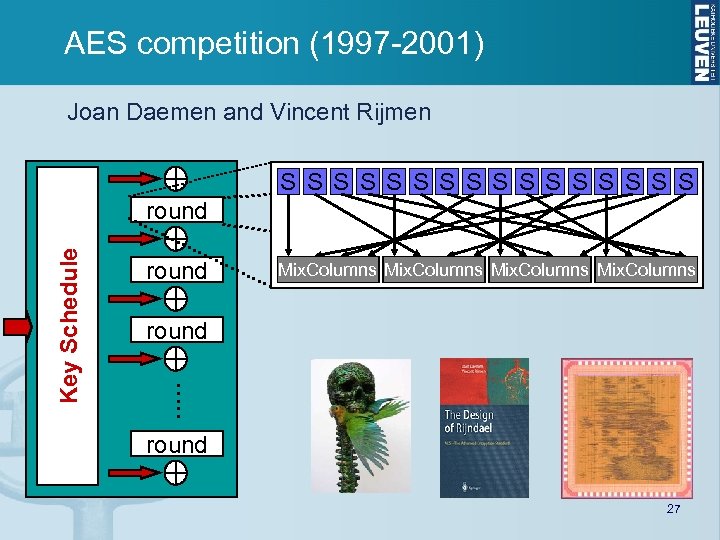 AES competition (1997 -2001) Joan Daemen and Vincent Rijmen S S S S Key Schedule round Mix. Columns S S S S round . . . round 27
AES competition (1997 -2001) Joan Daemen and Vincent Rijmen S S S S Key Schedule round Mix. Columns S S S S round . . . round 27
 A stick figure guide to AES http: //www. moserware. com/2009/09/stick-figure-guide-to-advanced. html 28
A stick figure guide to AES http: //www. moserware. com/2009/09/stick-figure-guide-to-advanced. html 28
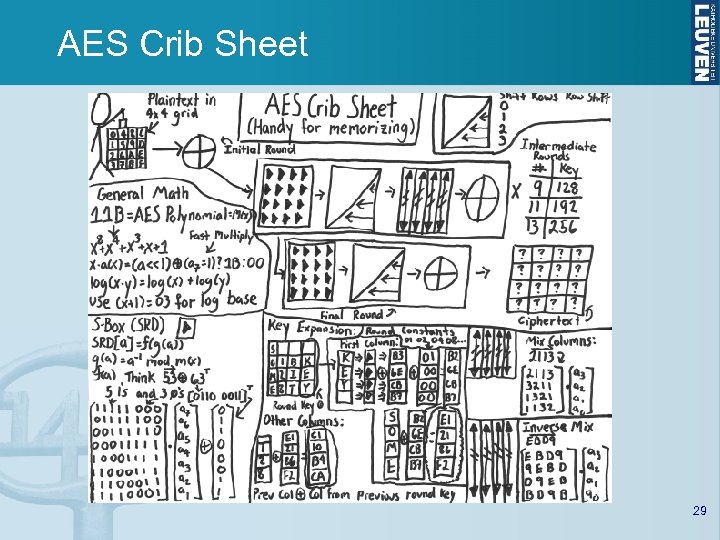 AES Crib Sheet 29
AES Crib Sheet 29
 AES mathematics 30
AES mathematics 30
 Applied Discrete Algebra Sommigen kennen wellicht het Nederlandse lied : “Wat heb ik nou aan algebra, nu ik voor de keuze sta…" Algebra is generous; she often gives more than is asked of her. Jean Le Rond d'Alembert (1717 -1783) 31
Applied Discrete Algebra Sommigen kennen wellicht het Nederlandse lied : “Wat heb ik nou aan algebra, nu ik voor de keuze sta…" Algebra is generous; she often gives more than is asked of her. Jean Le Rond d'Alembert (1717 -1783) 31
 AES Success • FIPS 197 published Nov. 6, 2001, effective May 26 2002 • mandatory for sensitive US govt. information • fast adoption in the market – NIST validation list: 2621 implementations • http: //csrc. nist. gov/groups/STM/cavp/documents/aesval. html – thousands of products: pc, tablet, smartphone, wifi, … – rather slower adoption in financial sector • 2003: AES-128 also for classified information and AES-192/256 for secret and top secret information! • 2010: Intel instruction AES-NI (and AMD follows) Adi Shamir: AES may well be the last block cipher 32
AES Success • FIPS 197 published Nov. 6, 2001, effective May 26 2002 • mandatory for sensitive US govt. information • fast adoption in the market – NIST validation list: 2621 implementations • http: //csrc. nist. gov/groups/STM/cavp/documents/aesval. html – thousands of products: pc, tablet, smartphone, wifi, … – rather slower adoption in financial sector • 2003: AES-128 also for classified information and AES-192/256 for secret and top secret information! • 2010: Intel instruction AES-NI (and AMD follows) Adi Shamir: AES may well be the last block cipher 32
 Cryptanalysis of Keeloq (August 2007) • block cipher with 32 -bit block length and 64 -bit key • market share of 80% as car immobilizer • also to open garage doors August 2007: first practical attack by COSIC, Technion, Hebrew Univ. • 1 hour access to device; 1 day on 100 PCs • may be sufficient to find master key 33
Cryptanalysis of Keeloq (August 2007) • block cipher with 32 -bit block length and 64 -bit key • market share of 80% as car immobilizer • also to open garage doors August 2007: first practical attack by COSIC, Technion, Hebrew Univ. • 1 hour access to device; 1 day on 100 PCs • may be sufficient to find master key 33
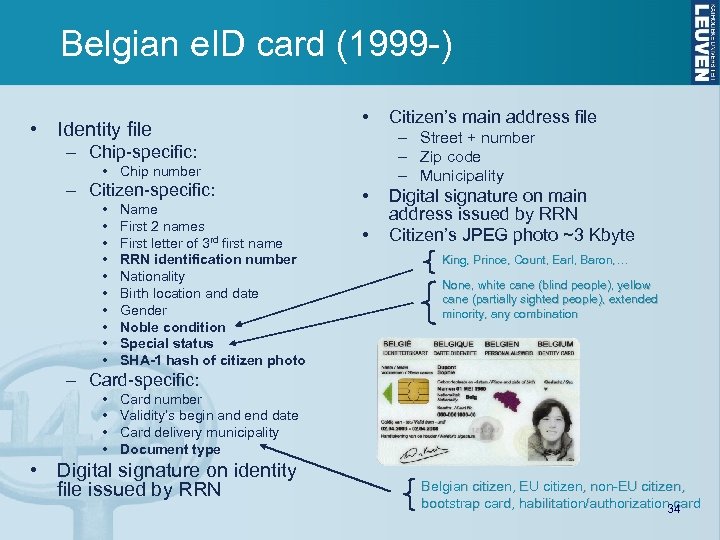 Belgian e. ID card (1999 -) • Identity file • – Street + number – Zip code – Municipality – Chip-specific: • Chip number – Citizen-specific: • • • Name First 2 names First letter of 3 rd first name RRN identification number Nationality Birth location and date Gender Noble condition Special status SHA-1 hash of citizen photo Citizen’s main address file • • Digital signature on main address issued by RRN Citizen’s JPEG photo ~3 Kbyte King, Prince, Count, Earl, Baron, … None, white cane (blind people), yellow cane (partially sighted people), extended minority, any combination – Card-specific: • • Card number Validity’s begin and end date Card delivery municipality Document type • Digital signature on identity file issued by RRN Belgian citizen, EU citizen, non-EU citizen, bootstrap card, habilitation/authorization 34 card
Belgian e. ID card (1999 -) • Identity file • – Street + number – Zip code – Municipality – Chip-specific: • Chip number – Citizen-specific: • • • Name First 2 names First letter of 3 rd first name RRN identification number Nationality Birth location and date Gender Noble condition Special status SHA-1 hash of citizen photo Citizen’s main address file • • Digital signature on main address issued by RRN Citizen’s JPEG photo ~3 Kbyte King, Prince, Count, Earl, Baron, … None, white cane (blind people), yellow cane (partially sighted people), extended minority, any combination – Card-specific: • • Card number Validity’s begin and end date Card delivery municipality Document type • Digital signature on identity file issued by RRN Belgian citizen, EU citizen, non-EU citizen, bootstrap card, habilitation/authorization 34 card
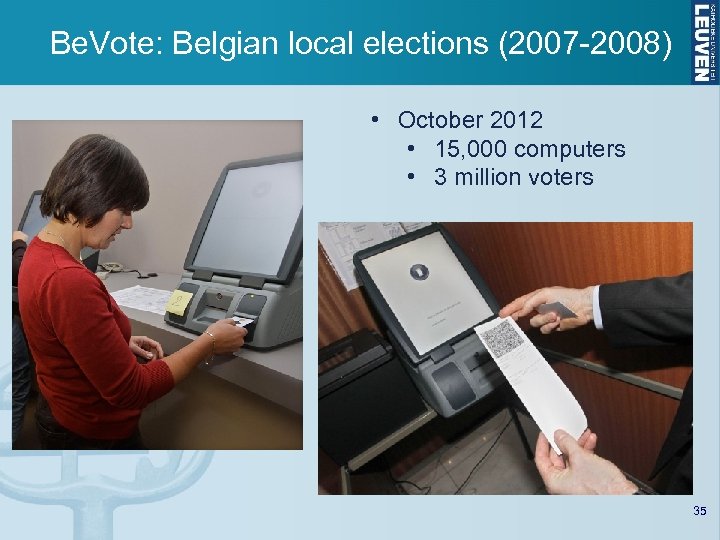 Be. Vote: Belgian local elections (2007 -2008) • October 2012 • 15, 000 computers • 3 million voters 35
Be. Vote: Belgian local elections (2007 -2008) • October 2012 • 15, 000 computers • 3 million voters 35
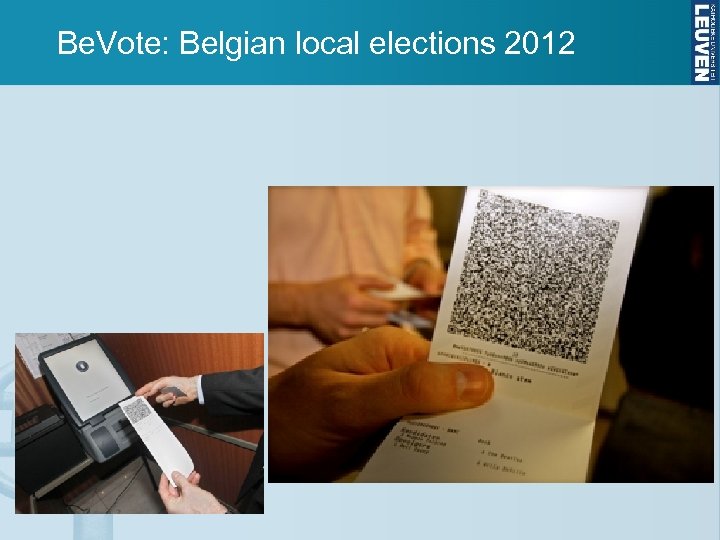 Be. Vote: Belgian local elections 2012 36
Be. Vote: Belgian local elections 2012 36
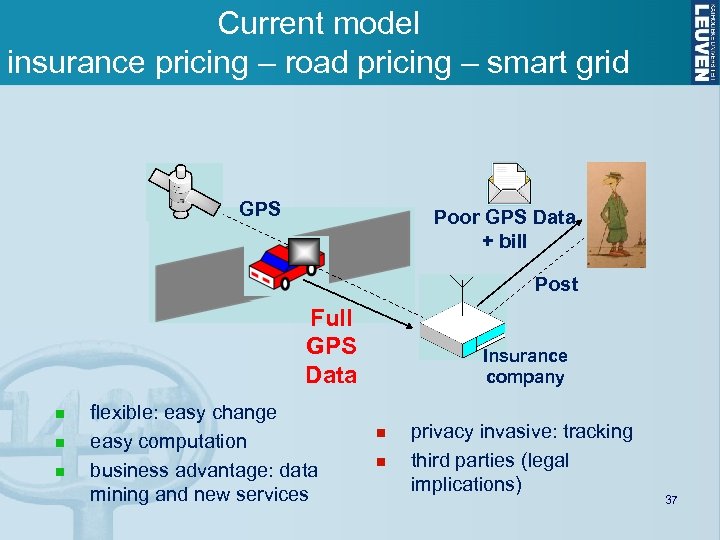 Current model insurance pricing – road pricing – smart grid GPS Poor GPS Data + bill Post Full GPS Data n n n flexible: easy change easy computation business advantage: data mining and new services Insurance company n n privacy invasive: tracking third parties (legal implications) 37
Current model insurance pricing – road pricing – smart grid GPS Poor GPS Data + bill Post Full GPS Data n n n flexible: easy change easy computation business advantage: data mining and new services Insurance company n n privacy invasive: tracking third parties (legal implications) 37
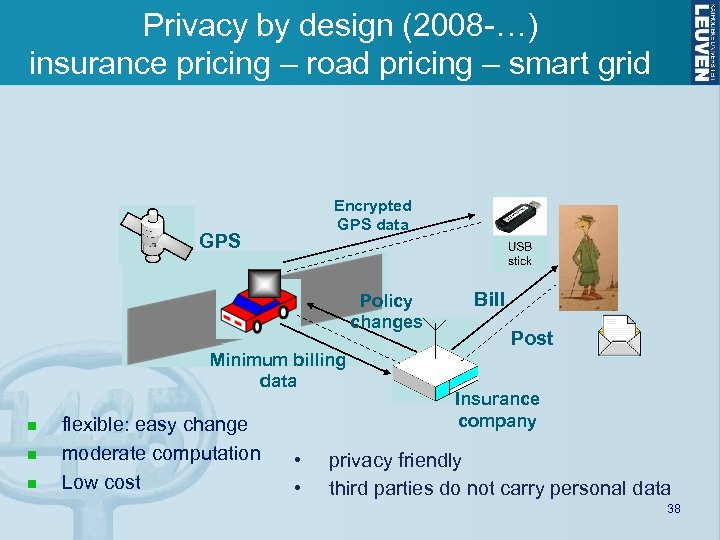 Privacy by design (2008 -…) insurance pricing – road pricing – smart grid Encrypted GPS data GPS Policy changes Minimum billing data n n n flexible: easy change moderate computation Low cost • • Bill Post Insurance company privacy friendly third parties do not carry personal data 38
Privacy by design (2008 -…) insurance pricing – road pricing – smart grid Encrypted GPS data GPS Policy changes Minimum billing data n n n flexible: easy change moderate computation Low cost • • Bill Post Insurance company privacy friendly third parties do not carry personal data 38
 Device fingerprinting much more prevalent than believed (2013) • control of cookies • Do-Not-Track Extension • but browser is unique: version, screen size, fonts • • • 1. 5% of the 10, 000 top websites track based on Flash 404 out of the top 1 million sites track based on fonts Do-Not-Track Extension is ignored TOR users can be tracked 12 new tracking providers identified G. Acar, M. Juarez, C. Diaz, S. Guerses, B. Preneel, N. Nikiforakis, F. Piessens, FPDetective: Dusting the Web for Fingerprinters, ACM CCS 2012 39
Device fingerprinting much more prevalent than believed (2013) • control of cookies • Do-Not-Track Extension • but browser is unique: version, screen size, fonts • • • 1. 5% of the 10, 000 top websites track based on Flash 404 out of the top 1 million sites track based on fonts Do-Not-Track Extension is ignored TOR users can be tracked 12 new tracking providers identified G. Acar, M. Juarez, C. Diaz, S. Guerses, B. Preneel, N. Nikiforakis, F. Piessens, FPDetective: Dusting the Web for Fingerprinters, ACM CCS 2012 39
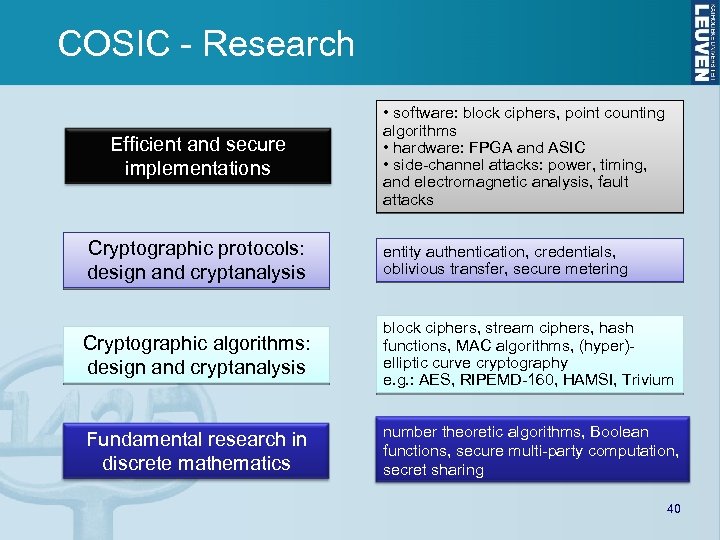 COSIC - Research Efficient and secure implementations • software: block ciphers, point counting algorithms • hardware: FPGA and ASIC • side-channel attacks: power, timing, and electromagnetic analysis, fault attacks Cryptographic protocols: design and cryptanalysis entity authentication, credentials, oblivious transfer, secure metering Cryptographic algorithms: design and cryptanalysis block ciphers, stream ciphers, hash functions, MAC algorithms, (hyper)elliptic curve cryptography e. g. : AES, RIPEMD-160, HAMSI, Trivium Fundamental research in discrete mathematics number theoretic algorithms, Boolean functions, secure multi-party computation, secret sharing 40
COSIC - Research Efficient and secure implementations • software: block ciphers, point counting algorithms • hardware: FPGA and ASIC • side-channel attacks: power, timing, and electromagnetic analysis, fault attacks Cryptographic protocols: design and cryptanalysis entity authentication, credentials, oblivious transfer, secure metering Cryptographic algorithms: design and cryptanalysis block ciphers, stream ciphers, hash functions, MAC algorithms, (hyper)elliptic curve cryptography e. g. : AES, RIPEMD-160, HAMSI, Trivium Fundamental research in discrete mathematics number theoretic algorithms, Boolean functions, secure multi-party computation, secret sharing 40
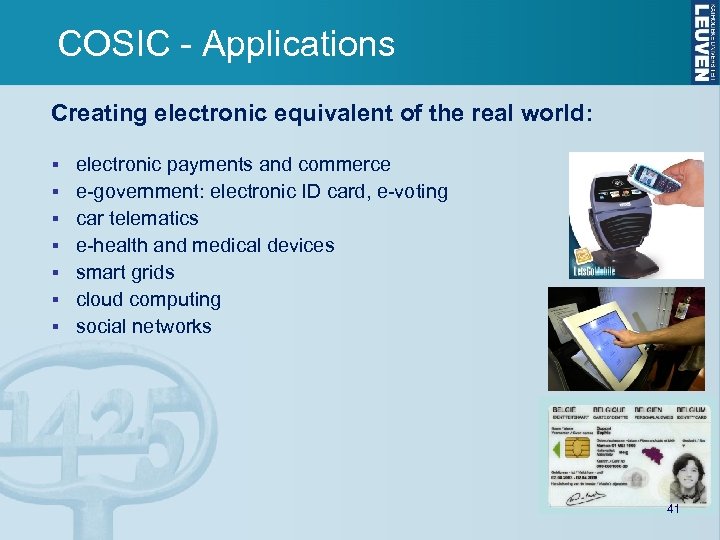 COSIC - Applications Creating electronic equivalent of the real world: electronic payments and commerce e-government: electronic ID card, e-voting car telematics e-health and medical devices smart grids cloud computing social networks 41
COSIC - Applications Creating electronic equivalent of the real world: electronic payments and commerce e-government: electronic ID card, e-voting car telematics e-health and medical devices smart grids cloud computing social networks 41
 Conclusions • • starting from discrete algebra gaining from Moore’s law vertical approach driven by (civilian) applications conflicting interests: diplomacy needed Life can only be understood backwards; but it must be lived forwards. Soren Kierkegaard Ad Multos Annos 42
Conclusions • • starting from discrete algebra gaining from Moore’s law vertical approach driven by (civilian) applications conflicting interests: diplomacy needed Life can only be understood backwards; but it must be lived forwards. Soren Kierkegaard Ad Multos Annos 42
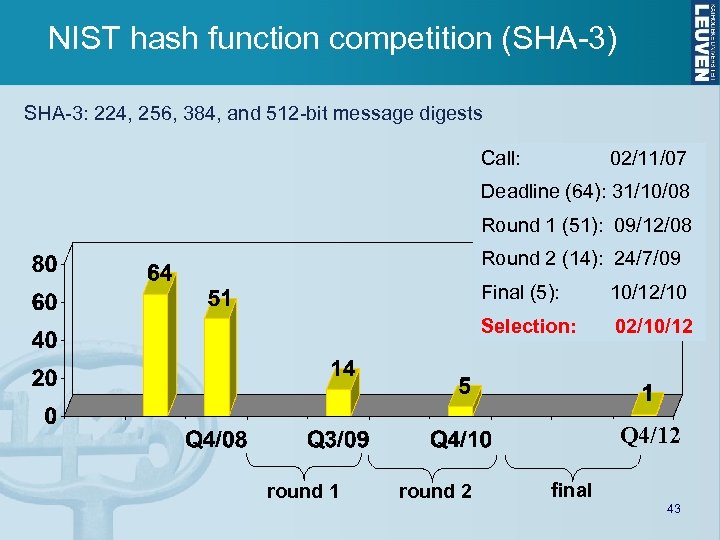 NIST hash function competition (SHA-3) SHA-3: 224, 256, 384, and 512 -bit message digests Call: 02/11/07 Deadline (64): 31/10/08 Round 1 (51): 09/12/08 Round 2 (14): 24/7/09 Final (5): 10/12/10 Selection: 02/10/12 Q 4/12 round 1 round 2 final 43
NIST hash function competition (SHA-3) SHA-3: 224, 256, 384, and 512 -bit message digests Call: 02/11/07 Deadline (64): 31/10/08 Round 1 (51): 09/12/08 Round 2 (14): 24/7/09 Final (5): 10/12/10 Selection: 02/10/12 Q 4/12 round 1 round 2 final 43
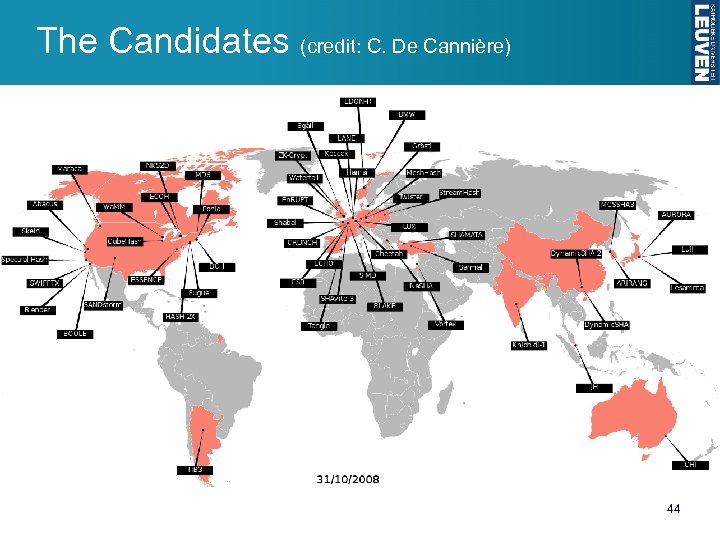 The Candidates (credit: C. De Cannière) 44 44
The Candidates (credit: C. De Cannière) 44 44
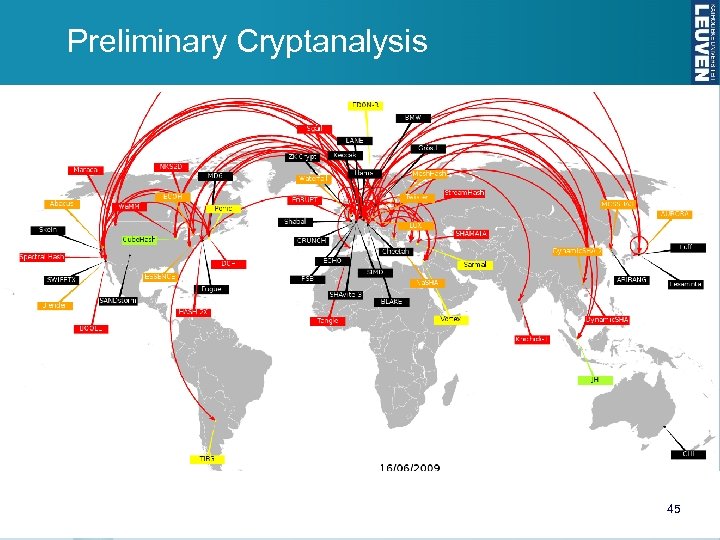 Preliminary Cryptanalysis Slide credit: Christophe De Cannière 45 45
Preliminary Cryptanalysis Slide credit: Christophe De Cannière 45 45
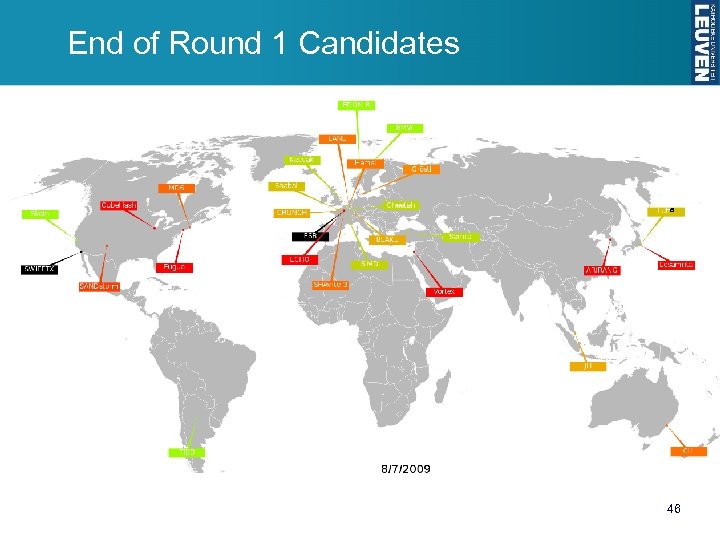 End of Round 1 Candidates a Slide credit: Christophe De Cannière 46 46
End of Round 1 Candidates a Slide credit: Christophe De Cannière 46 46
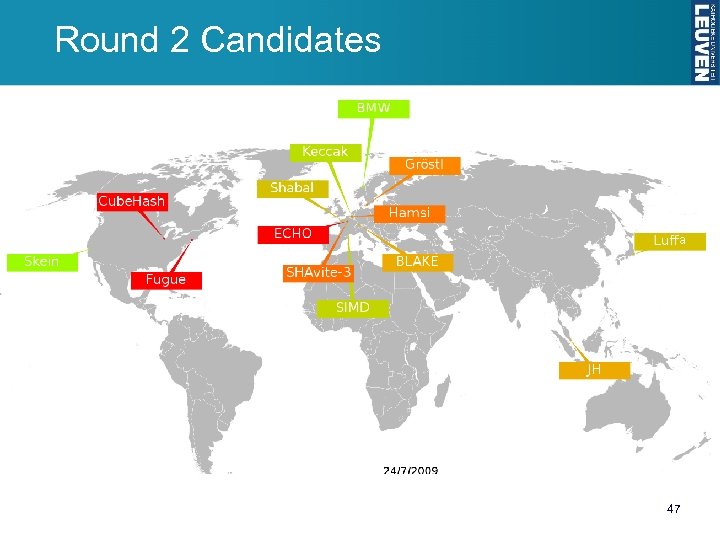 Round 2 Candidates a Slide credit: Christophe De Cannière 47 47
Round 2 Candidates a Slide credit: Christophe De Cannière 47 47
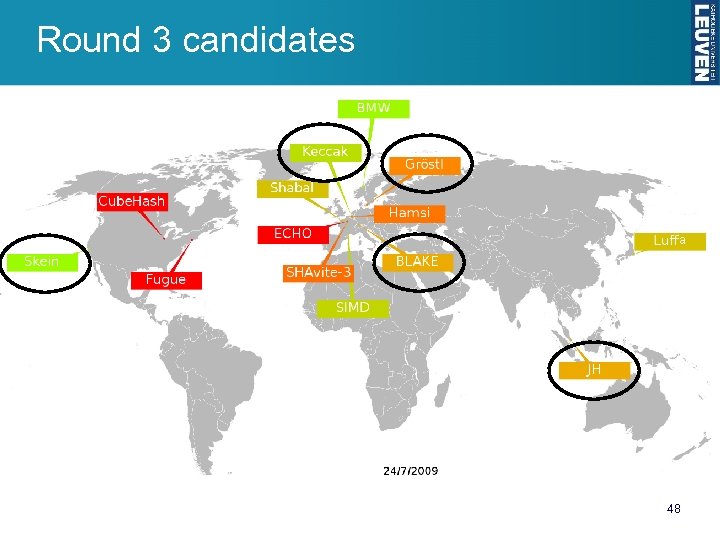 Round 3 candidates a Slide credit: Christophe De Cannière 48 48
Round 3 candidates a Slide credit: Christophe De Cannière 48 48
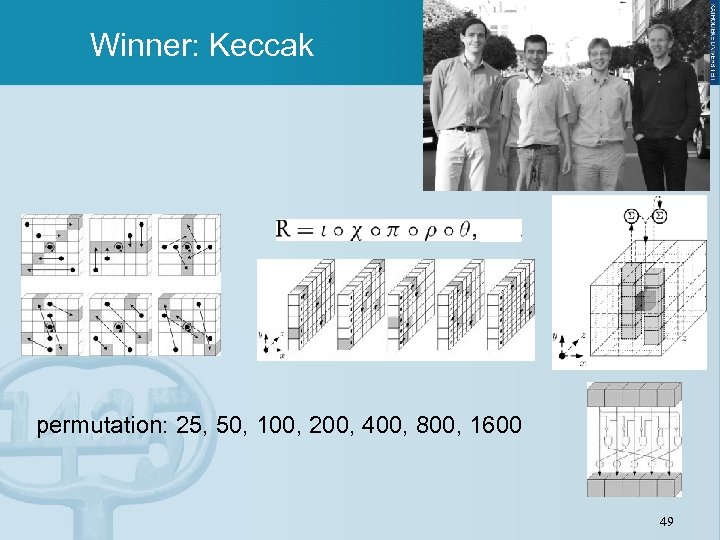 Winner: Keccak permutation: 25, 50, 100, 200, 400, 800, 1600 49
Winner: Keccak permutation: 25, 50, 100, 200, 400, 800, 1600 49
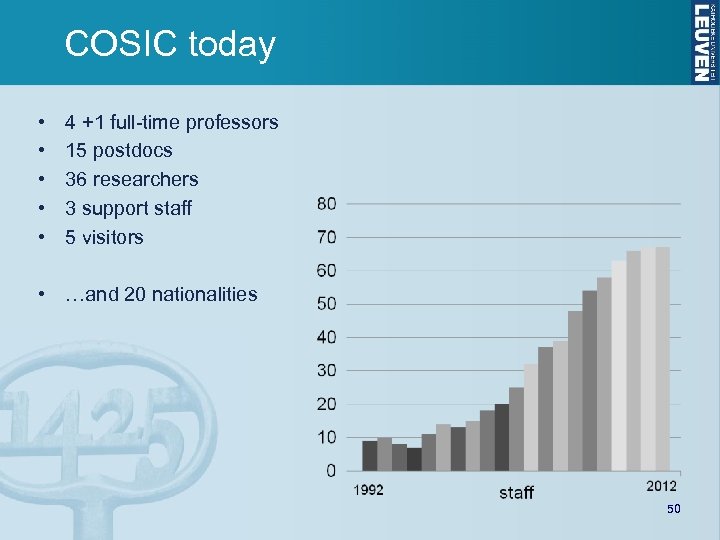 COSIC today • • • 4 +1 full-time professors 15 postdocs 36 researchers 3 support staff 5 visitors • …and 20 nationalities 50
COSIC today • • • 4 +1 full-time professors 15 postdocs 36 researchers 3 support staff 5 visitors • …and 20 nationalities 50


