1164ae332bdc437189f8a9c5e4103785.ppt
- Количество слайдов: 41
 COS 125 DAY 4
COS 125 DAY 4
 Agenda l l l Questions from last Class? ? Using blackboard’s assignment section Today’s topics l l l Assignment #1 Due Assignment #2 Posted l l Communicating on the Internet Due Feb 15 Quiz #1 on Feb 12 l l l Chap 1 -26 20 M/C, 4 short essays, One extra credit Question 60 Min, open book, open notes
Agenda l l l Questions from last Class? ? Using blackboard’s assignment section Today’s topics l l l Assignment #1 Due Assignment #2 Posted l l Communicating on the Internet Due Feb 15 Quiz #1 on Feb 12 l l l Chap 1 -26 20 M/C, 4 short essays, One extra credit Question 60 Min, open book, open notes
 Communicating on the Internet l How email works l How email Spam works l How Newsgroup work l How Internet Chat and Instant Messaging Work l How Internet Phone calls work l How Blogging and RSS works
Communicating on the Internet l How email works l How email Spam works l How Newsgroup work l How Internet Chat and Instant Messaging Work l How Internet Phone calls work l How Blogging and RSS works
 email Animation from www. learnthenet. com
email Animation from www. learnthenet. com
 How email works l l Most heavily used feature on the Internet Advantages l l Asynchronous Ubiquitous Can be made Secure (almost too secure) Disadvantage l l l Impersonal Ubiquitous Insecure (non-confidentiality) Virus, Macros, Trojans Horses Lack of a centralized directory
How email works l l Most heavily used feature on the Internet Advantages l l Asynchronous Ubiquitous Can be made Secure (almost too secure) Disadvantage l l l Impersonal Ubiquitous Insecure (non-confidentiality) Virus, Macros, Trojans Horses Lack of a centralized directory
 How email works l To send email You need an email account l someone@somewhere. com l l With an email you can send Plain text l Formatted text (RTF) l HTML l Attachments l Email Demo from www. learnthenet. com l
How email works l To send email You need an email account l someone@somewhere. com l l With an email you can send Plain text l Formatted text (RTF) l HTML l Attachments l Email Demo from www. learnthenet. com l
 Outlook email client
Outlook email client
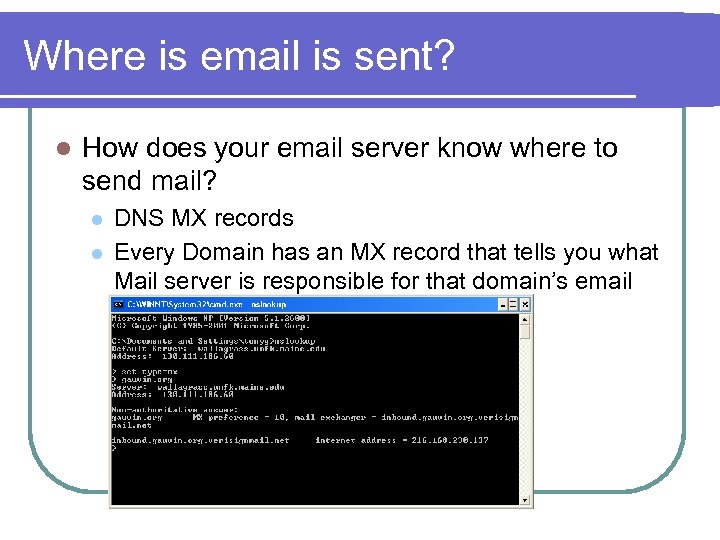 Where is email is sent? l How does your email server know where to send mail? l l DNS MX records Every Domain has an MX record that tells you what Mail server is responsible for that domain’s email
Where is email is sent? l How does your email server know where to send mail? l l DNS MX records Every Domain has an MX record that tells you what Mail server is responsible for that domain’s email
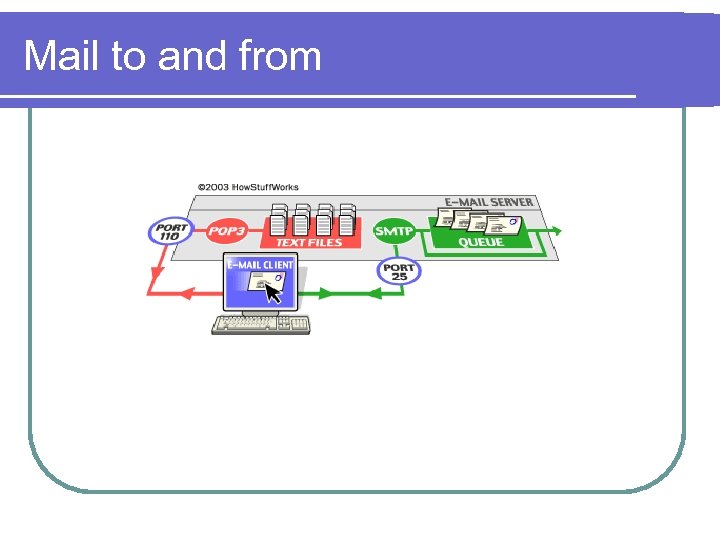 Mail to and from
Mail to and from
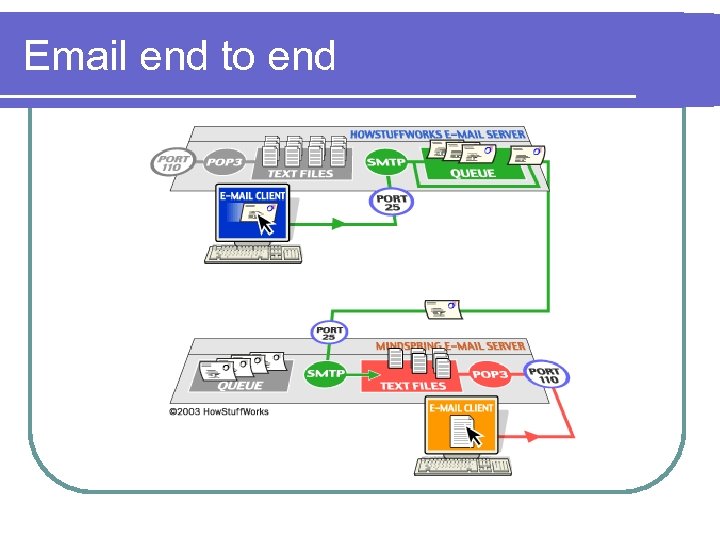 Email end to end
Email end to end
 Mailing Lists A group of people that has similar interests l Each person joins the “group” which has an email address assigned group 1@lists. com l When you send and email to group 1@lists. com everyone that joins the group gets the email l Two types of Mailing lists l l Moderated Unmoderated Mailing List Demo from www. learnthenet. com
Mailing Lists A group of people that has similar interests l Each person joins the “group” which has an email address assigned group 1@lists. com l When you send and email to group 1@lists. com everyone that joins the group gets the email l Two types of Mailing lists l l Moderated Unmoderated Mailing List Demo from www. learnthenet. com
 Making email secure l Encryption Scramble and then descramble the message using a secret code l Most encryption uses two “keys” l One to scramble l The other to unscramble l Some only use one l Encryption demo from Persits. com l Encryption Demo from learnthenet. com l
Making email secure l Encryption Scramble and then descramble the message using a secret code l Most encryption uses two “keys” l One to scramble l The other to unscramble l Some only use one l Encryption demo from Persits. com l Encryption Demo from learnthenet. com l
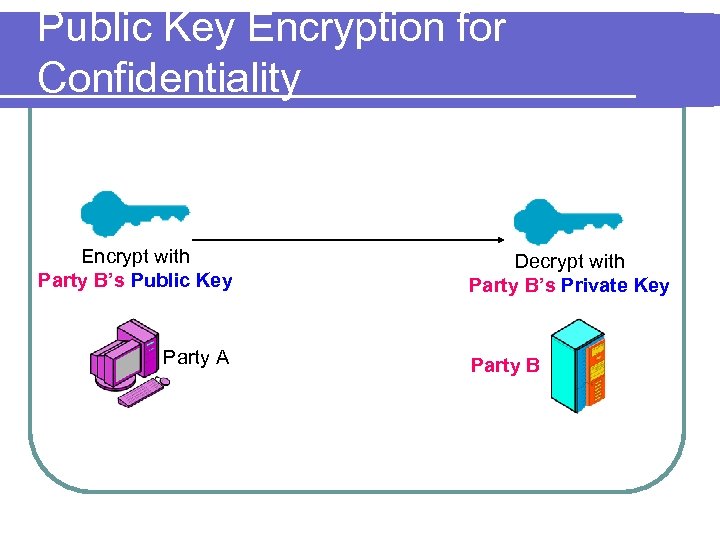 Public Key Encryption for Confidentiality Encrypt with Party B’s Public Key Party A Decrypt with Party B’s Private Key Party B
Public Key Encryption for Confidentiality Encrypt with Party B’s Public Key Party A Decrypt with Party B’s Private Key Party B
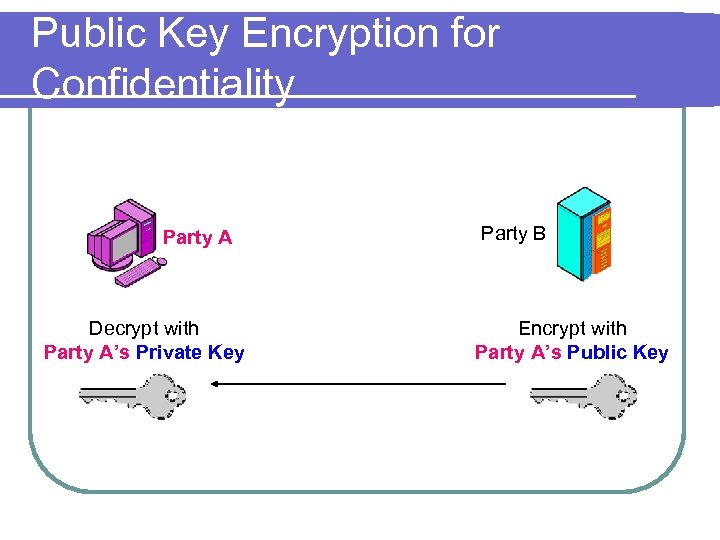 Public Key Encryption for Confidentiality Party A Decrypt with Party A’s Private Key Party B Encrypt with Party A’s Public Key
Public Key Encryption for Confidentiality Party A Decrypt with Party A’s Private Key Party B Encrypt with Party A’s Public Key
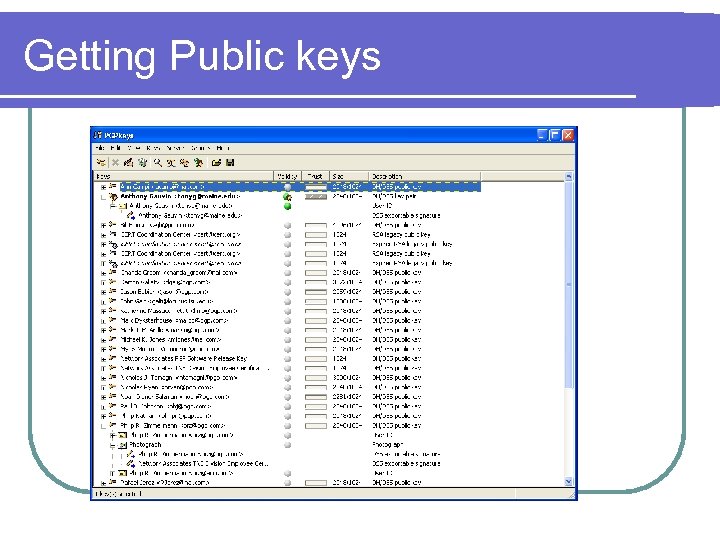 Getting Public keys
Getting Public keys
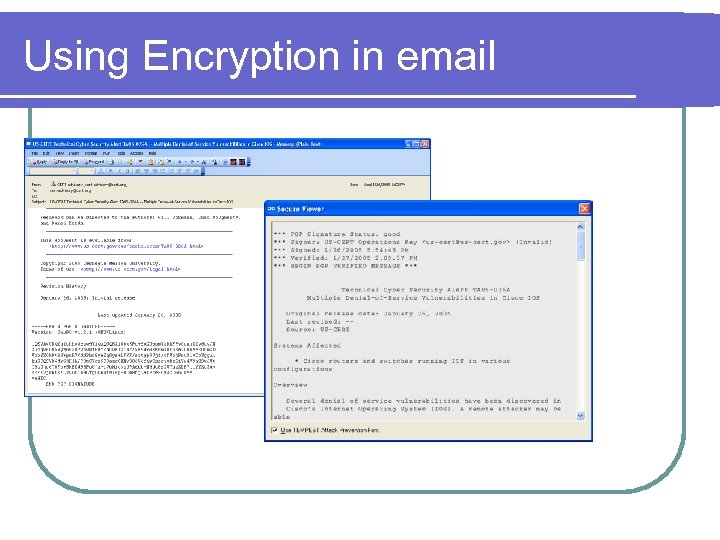 Using Encryption in email
Using Encryption in email
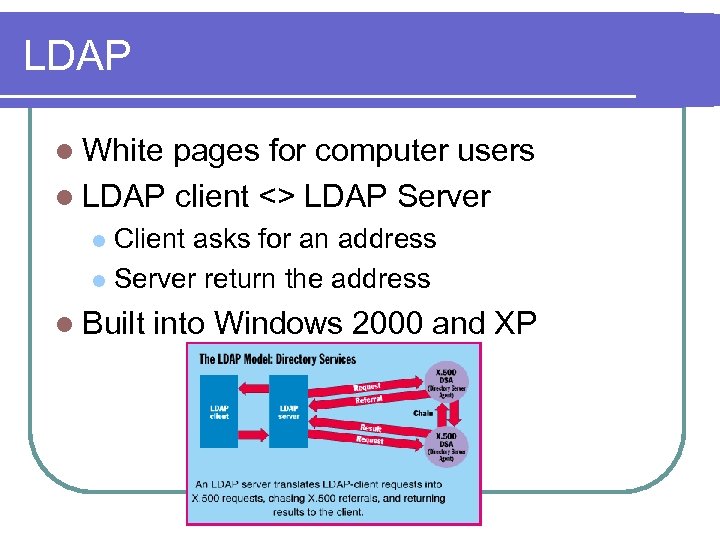 LDAP l White pages for computer users l LDAP client <> LDAP Server Client asks for an address l Server return the address l l Built into Windows 2000 and XP
LDAP l White pages for computer users l LDAP client <> LDAP Server Client asks for an address l Server return the address l l Built into Windows 2000 and XP
 How SPAM works l SPAM is unsolicited Junk email l Why is this done CHEAP mass marketing l Junk postal mail costs at least $0. 20 per mailing l Spam cost around $100 per million emails sent or $0. 0001 per mailing l Origin of the word Spam l l http: //www. odul. com/spam/
How SPAM works l SPAM is unsolicited Junk email l Why is this done CHEAP mass marketing l Junk postal mail costs at least $0. 20 per mailing l Spam cost around $100 per million emails sent or $0. 0001 per mailing l Origin of the word Spam l l http: //www. odul. com/spam/
 Tricks of the SPAMMER trade http: //www. marketing-2000. net/ l Getting email address l l l Directories Newsgroups Buy from other spammers Build a web site to collect them Sending emails l l Manipulate headers to hide sending info Uses some else's email sever l Open SMTP relay’s
Tricks of the SPAMMER trade http: //www. marketing-2000. net/ l Getting email address l l l Directories Newsgroups Buy from other spammers Build a web site to collect them Sending emails l l Manipulate headers to hide sending info Uses some else's email sever l Open SMTP relay’s
 Stopping Spammers l Laws don’t work l l Special anti-spam software l l Spammer just get “trickier” and by pass software Blocking places that send spam l l Can’t prosecute what you can’t catch Laws are tied to jurisdictions, Spammers aren’t Spam laws Since spammer don’t use their own mail servers you run the risk of blocking legitimate email Best practice –Get more email addresses l Get an email address just for spammers l l me@hotmail. com Protect important emails by using sparingly l l One just for family & friends One just for work or school
Stopping Spammers l Laws don’t work l l Special anti-spam software l l Spammer just get “trickier” and by pass software Blocking places that send spam l l Can’t prosecute what you can’t catch Laws are tied to jurisdictions, Spammers aren’t Spam laws Since spammer don’t use their own mail servers you run the risk of blocking legitimate email Best practice –Get more email addresses l Get an email address just for spammers l l me@hotmail. com Protect important emails by using sparingly l l One just for family & friends One just for work or school
 Newsgroups l USENET is the worlds biggest discussion forum. Collections of newsgroup of many subjects l Best place to see the groups is l l http: //groups. google. com Demo of newsgroups from Learnthenet. com l Just like mailing lists newsgroup can be l Moderated l Unmoderated l
Newsgroups l USENET is the worlds biggest discussion forum. Collections of newsgroup of many subjects l Best place to see the groups is l l http: //groups. google. com Demo of newsgroups from Learnthenet. com l Just like mailing lists newsgroup can be l Moderated l Unmoderated l
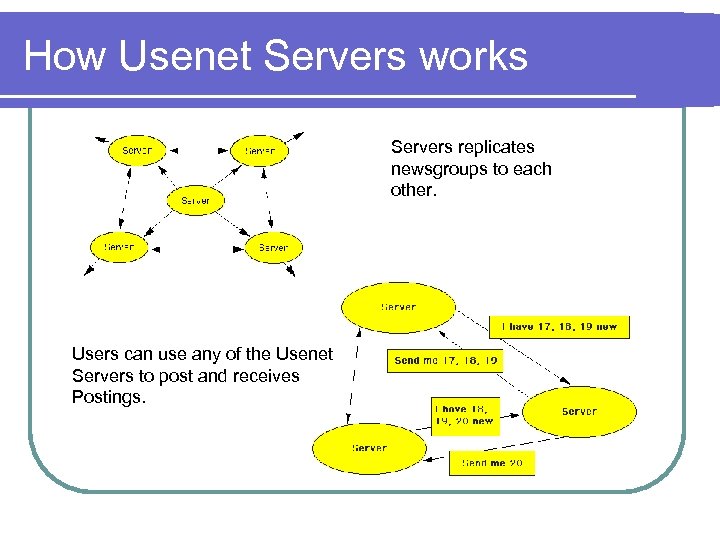 How Usenet Servers works Servers replicates newsgroups to each other. Users can use any of the Usenet Servers to post and receives Postings.
How Usenet Servers works Servers replicates newsgroups to each other. Users can use any of the Usenet Servers to post and receives Postings.
 Problems with USENET With the advent of instant messaging, MSN, AOL and Yahoo groups, blogs and other new internet inventions Usenet isn’t used by much of the Internet population l Many ISP’s don’t support USENET l A lot of what’s “bad” with the internet is on USENET . . the equivalent of the Internet “bad part of town” l l l Hate groups & terrorists Pornography Hackers and crackers Perverts & pedophiles Better places for discussions groups l l MSN groups Yahoo groups
Problems with USENET With the advent of instant messaging, MSN, AOL and Yahoo groups, blogs and other new internet inventions Usenet isn’t used by much of the Internet population l Many ISP’s don’t support USENET l A lot of what’s “bad” with the internet is on USENET . . the equivalent of the Internet “bad part of town” l l l Hate groups & terrorists Pornography Hackers and crackers Perverts & pedophiles Better places for discussions groups l l MSN groups Yahoo groups
 How Internet Chat works Live keyboard conversation on the Internet l Most popular is Internet Relay Chat l l l Chat works on Client/Server model l Topic are channels (Chat Rooms) Users are on clients The chat room is on a server There are many proprietary Chat solutions l Blackboard
How Internet Chat works Live keyboard conversation on the Internet l Most popular is Internet Relay Chat l l l Chat works on Client/Server model l Topic are channels (Chat Rooms) Users are on clients The chat room is on a server There are many proprietary Chat solutions l Blackboard
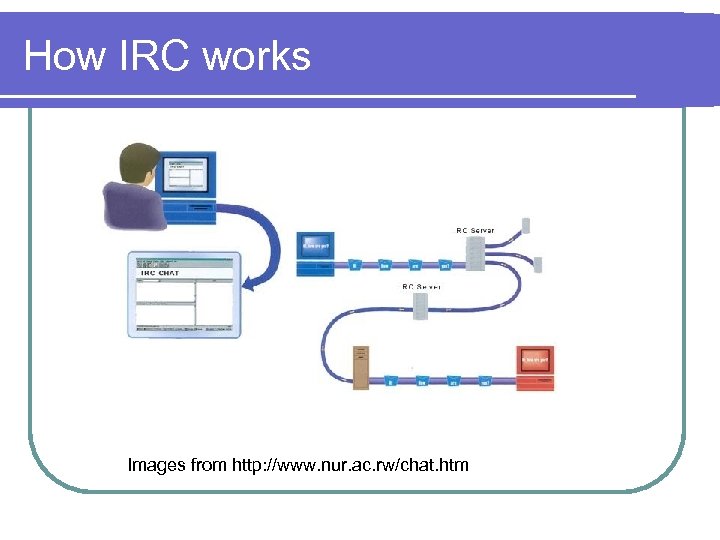 How IRC works Images from http: //www. nur. ac. rw/chat. htm
How IRC works Images from http: //www. nur. ac. rw/chat. htm
 Chat stuff l Acronyms l brb = be right back bbl = be back later btw = by the way np = no problem lol = laughing out loud re = hi again, as in 're hi' rotfl = rolling on the floor laughing bbiaf = be back in a flash ttfn = ta ta for now imho = in my humble opinion j/k = just kidding wb = welcome back
Chat stuff l Acronyms l brb = be right back bbl = be back later btw = by the way np = no problem lol = laughing out loud re = hi again, as in 're hi' rotfl = rolling on the floor laughing bbiaf = be back in a flash ttfn = ta ta for now imho = in my humble opinion j/k = just kidding wb = welcome back
 Emoticons l l l l l l : ) Smile : -) Basic Smile ; -) eye wink : -( sad : -I Indifference : -> Sarcastic >: -> Diabolic (-: left handed %-) Drunk 8 -) Uses glasses B: -) Sunglasses on head B-) dark sunglasses 8: -) little girl : -{) Mustache : -{}painted mouth {: -)with hair : -^) with flu : -)^ choking : '-( crying : -@ shouting : -& cant talk -: -) punk l l l l l l |: -) fall sleep : -O waking up 0: -) angel : -D laughing : -X lips seal : -Q smoker : -/ skeptic C=: -) chef @= nuclear bomb *: O) clown [: -) using walkman (: I egghead @: -) with turban X-( just died : ] friendly smile : D laugh : ( again sad : O shouting [] hugs : * kisses : *, ; * more kisses : *, more and more kisses
Emoticons l l l l l l : ) Smile : -) Basic Smile ; -) eye wink : -( sad : -I Indifference : -> Sarcastic >: -> Diabolic (-: left handed %-) Drunk 8 -) Uses glasses B: -) Sunglasses on head B-) dark sunglasses 8: -) little girl : -{) Mustache : -{}painted mouth {: -)with hair : -^) with flu : -)^ choking : '-( crying : -@ shouting : -& cant talk -: -) punk l l l l l l |: -) fall sleep : -O waking up 0: -) angel : -D laughing : -X lips seal : -Q smoker : -/ skeptic C=: -) chef @= nuclear bomb *: O) clown [: -) using walkman (: I egghead @: -) with turban X-( just died : ] friendly smile : D laugh : ( again sad : O shouting [] hugs : * kisses : *, ; * more kisses : *, more and more kisses
 Instant Messaging l Differs from chat in that it is one-to-one l l Four popular software applications that have little to no interoperability l l l Chat one-to-many MSN Messenger® AOL Instant Messenger® ICQ® YAHOO! Messenger® One instant messenger is trying to become protocol independent l Miranda supports the four listed above
Instant Messaging l Differs from chat in that it is one-to-one l l Four popular software applications that have little to no interoperability l l l Chat one-to-many MSN Messenger® AOL Instant Messenger® ICQ® YAHOO! Messenger® One instant messenger is trying to become protocol independent l Miranda supports the four listed above
 How Instant Messaging works l Login to messaging server (AOL, MSN) l Send your buddy list to server l Server tells you which of your buddies are logged in l Select on inline buddy to talk to Some systems connect buddy to chat (MSN) l Other run all chats through the server (AIM) l
How Instant Messaging works l Login to messaging server (AOL, MSN) l Send your buddy list to server l Server tells you which of your buddies are logged in l Select on inline buddy to talk to Some systems connect buddy to chat (MSN) l Other run all chats through the server (AIM) l
 How Internet Phone Calls Work l This is using the Internet to replace the Public Switched Telephone system Save money on long distance l Called Voice over IP or Vo. IP l l Converts Voice (analog) to digital packets and vise versa l Digital packets sent over the internet
How Internet Phone Calls Work l This is using the Internet to replace the Public Switched Telephone system Save money on long distance l Called Voice over IP or Vo. IP l l Converts Voice (analog) to digital packets and vise versa l Digital packets sent over the internet
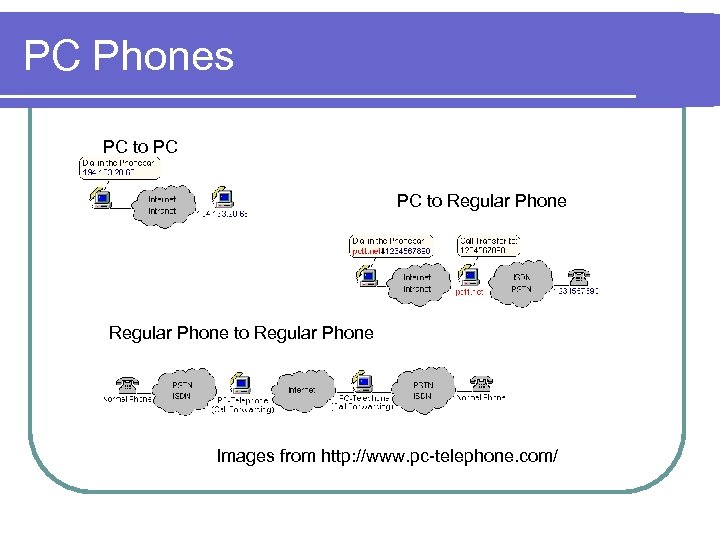 PC Phones PC to PC PC to Regular Phone Images from http: //www. pc-telephone. com/
PC Phones PC to PC PC to Regular Phone Images from http: //www. pc-telephone. com/
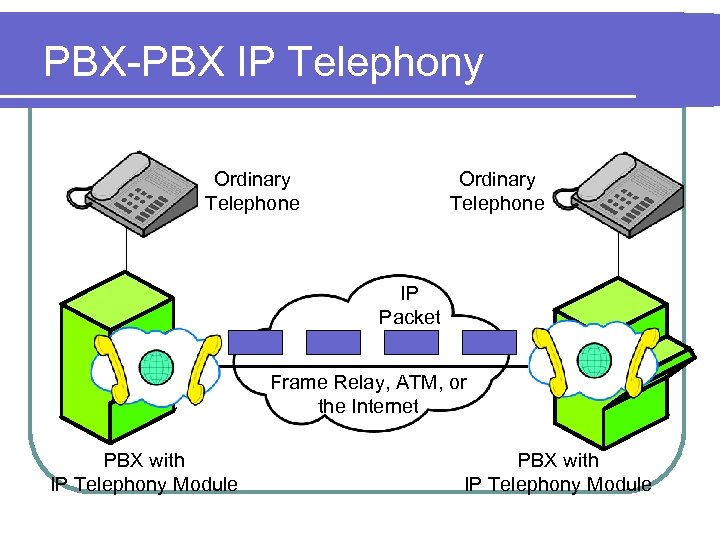 PBX-PBX IP Telephony Ordinary Telephone IP Packet Frame Relay, ATM, or the Internet PBX with IP Telephony Module
PBX-PBX IP Telephony Ordinary Telephone IP Packet Frame Relay, ATM, or the Internet PBX with IP Telephony Module
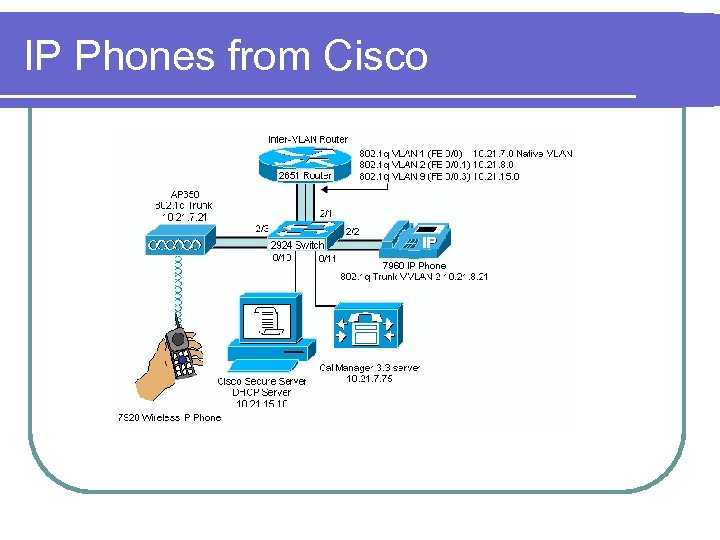 IP Phones from Cisco
IP Phones from Cisco
 How Skype works http: //share. skype. com http: //www. englishflow. net/en-skype. html
How Skype works http: //share. skype. com http: //www. englishflow. net/en-skype. html
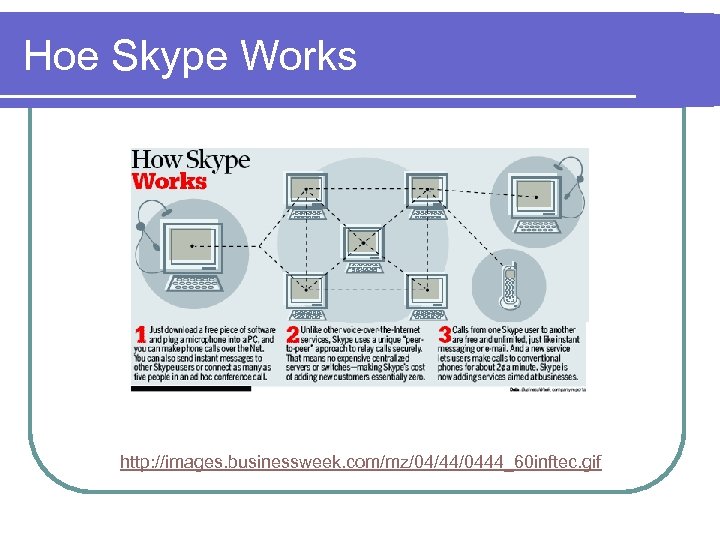 Hoe Skype Works http: //images. businessweek. com/mz/04/44/0444_60 inftec. gif
Hoe Skype Works http: //images. businessweek. com/mz/04/44/0444_60 inftec. gif
 Blogging l l http: //computer. howstuffworks. com/blog. htm A blog is any or many of the following l l l l online journal written by an individual method a self publication a diary career building – letting everyone know about your talents and ideas career suicide – venting about a company or person, taking a controversial position, blogging at work way to make money Get notice by search engines Bloggers require readers l The update problem- when do the readers know that there is new dialogue on the blog
Blogging l l http: //computer. howstuffworks. com/blog. htm A blog is any or many of the following l l l l online journal written by an individual method a self publication a diary career building – letting everyone know about your talents and ideas career suicide – venting about a company or person, taking a controversial position, blogging at work way to make money Get notice by search engines Bloggers require readers l The update problem- when do the readers know that there is new dialogue on the blog
 RSS Really Simple Syndication l Addresses the “update” problem l Two (or three) parts l l l Publisher (feed) – special XML files contains title, description and link to the actual data Reader – Finds and reads the XML files and “pulls” the xml files. l l http: //blogspace. com/rss/readers Aggregators – pulls several RSS feeds together
RSS Really Simple Syndication l Addresses the “update” problem l Two (or three) parts l l l Publisher (feed) – special XML files contains title, description and link to the actual data Reader – Finds and reads the XML files and “pulls” the xml files. l l http: //blogspace. com/rss/readers Aggregators – pulls several RSS feeds together
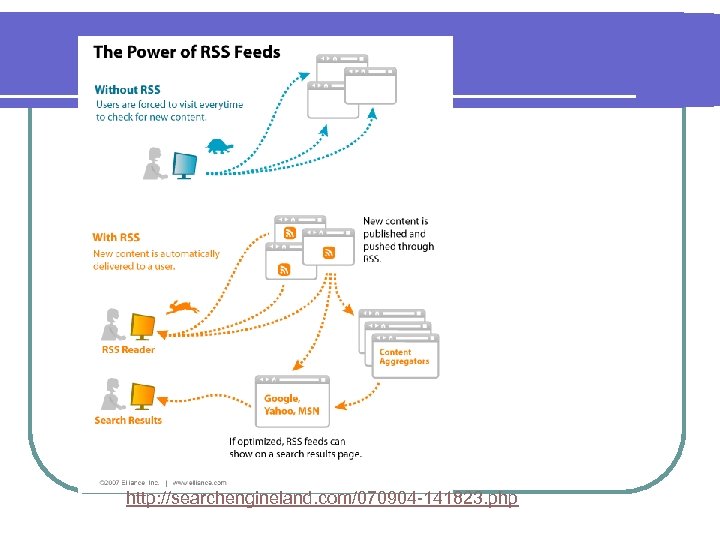 http: //searchengineland. com/070904 -141823. php
http: //searchengineland. com/070904 -141823. php
 http: //journal. plasticmind. com/tech-tips/feed-tip-for-facebook-status-junkies/
http: //journal. plasticmind. com/tech-tips/feed-tip-for-facebook-status-junkies/
 Maine’s Anti-Hacker laws l 432. Criminal invasion of computer privacy 1. A person is guilty of criminal invasion of computer privacy if the person intentionally accesses any computer resource knowing that the person is not authorized to do so. [1989, c. 620 (new). ] 2. Criminal invasion of computer privacy is a Class D crime. [1989, c. 620 (new). ] l § 433. Aggravated criminal invasion of computer privacy 1. A person is guilty of aggravated criminal invasion of computer privacy if the person: A. Intentionally makes an unauthorized copy of any computer program, computer software or computer information, knowing that the person is not authorized to do so; [1989, c. 620 (new). ] B. Intentionally or knowingly damages any computer resource of another person, having no reasonable ground to believe that the person has the right to do so; or [1989, c. 620 (new). ] C. Intentionally or knowingly introduces or allows the introduction of a computer virus into any computer resource, having no reasonable ground to believe that the person has the right to do so. [1989, c. 620 (new). ] 2. Aggravated criminal invasion of computer privacy is a Class C crime. [1989, c. 620 (new). ]
Maine’s Anti-Hacker laws l 432. Criminal invasion of computer privacy 1. A person is guilty of criminal invasion of computer privacy if the person intentionally accesses any computer resource knowing that the person is not authorized to do so. [1989, c. 620 (new). ] 2. Criminal invasion of computer privacy is a Class D crime. [1989, c. 620 (new). ] l § 433. Aggravated criminal invasion of computer privacy 1. A person is guilty of aggravated criminal invasion of computer privacy if the person: A. Intentionally makes an unauthorized copy of any computer program, computer software or computer information, knowing that the person is not authorized to do so; [1989, c. 620 (new). ] B. Intentionally or knowingly damages any computer resource of another person, having no reasonable ground to believe that the person has the right to do so; or [1989, c. 620 (new). ] C. Intentionally or knowingly introduces or allows the introduction of a computer virus into any computer resource, having no reasonable ground to believe that the person has the right to do so. [1989, c. 620 (new). ] 2. Aggravated criminal invasion of computer privacy is a Class C crime. [1989, c. 620 (new). ]
 For next class l Read through Chapter 26 (page 184) l Quiz 1 on Feb 12 (one week from today) l Extra Credit Question on Next exam l How many Hackers have been arrested in Maine? Can you name any successful prosecutions of Hackers in the state of Maine? What is the problem in catching and prosecuting Hackers in Maine?
For next class l Read through Chapter 26 (page 184) l Quiz 1 on Feb 12 (one week from today) l Extra Credit Question on Next exam l How many Hackers have been arrested in Maine? Can you name any successful prosecutions of Hackers in the state of Maine? What is the problem in catching and prosecuting Hackers in Maine?


