88b42fe0a68cac1954be8d1a13ea769b.ppt
- Количество слайдов: 16

Computer Security By: Edward Woltersdorf & Jim Young
Keylogger Definition – diagnostic tool used in software development captures the user’s keystrokes. Purposes – monitors employee productivity, police use, illegal spying. How it effects computer – Captures keystrokes and records them in a file. This file is usually sent to another computer for analysis.
Spam Definition – unsolicited bulk email messages. Sometimes used to transmit viruses. Purpose – sell products, market products, scam people, lead people to sites for ID theft. How it effects computer – Puts a virus or program into the computer to track or accomplish tasks without the user’s knowledge.
Spyware Definition – computer software that is installed secretly (very rarely knowingly) on a personal computer to intercept or take partial control over the user’s interaction with the computer, generally without the user’s consent. Purpose – to collect, organize and transmit data back to a centralized location for purposes of marketing, ID theft, or corruption of system resources. How it effects computer – runs programs in the background slowing computer’s process to a crawl. Some data transmitted can be done illegally.
Virus Definition - computer program that can copy itself and infect a computer without permission or knowledge of the user. Purpose – generally made for malicious intent, but sometimes for humor or fun. How it effects the computer - Some viruses are programmed to damage the computer by damaging programs, deleting files, or reformatting the hard disk. Others are not designed to do any damage, but simply replicate themselves and perhaps make their presence known by presenting text, video, or audio messages. Even these benign viruses can create problems for the computer user. They typically take up computer memory used by legitimate programs. As a result, they often cause erratic behavior and can result in system crashes. In addition, many viruses are bug-ridden, and these bugs may lead to system crashes and data loss.
Why Do You Care? ID Theft n Surveys in the USA from 2003 to 2006 showed a decrease in the total number of victims but an increase in the total value of identity fraud to US$56. 6 billion in 2006. The average fraud person rose from $5, 249 in 2003 to $6, 383 in 2006. Recent Surveys and Studies, Privacy Clearing House, retrieved June 30, 2006
Why Do You Care? II Erratic behavior and can result in system crashes Work place n n n Data theft Transmission of illegal files Usage of computer/bandwidth of illegal purposes Erratic behavior and can result in system crashes Academic dishonesty Grade changes Stolen work
How Do You Know if You’re Infected? New Toolbars in Internet Explorer Browser crashes unexpectedly Home page changes Bandwidth traffic causes internet speeds to decrease Ads always seem to be similar to your interests Pages opening as you start up your computer Pop-ups “Helpful” programs start up – Bonsi Buddy, Cool. Web. Search, Weather Bug Ctrl-Alt-Delete msconfig
How to Remove Spyware Please note: Some programs you install require that you download spyware in order to use them. By removing some spyware, you may be in in violation of licensing agreements for some programs (Morpheus, Sony’s Extended Copy Protection, Div. X, AIM)! Download a free program (see below for recommended programs and cautions) Buy a program Run the program often (and at full scanning capabilities) Usually the combination of several programs is the most effective
Spybot: Search and Destroy http: //www. safernetworking. org/en/index. html Removes programs based on reported threats Pros Removes many spyware programs (displayed in red) Can clean usage tracks (displayed in green) Can fix registry entries Cons Requires constant updates Many features only available through pay-version
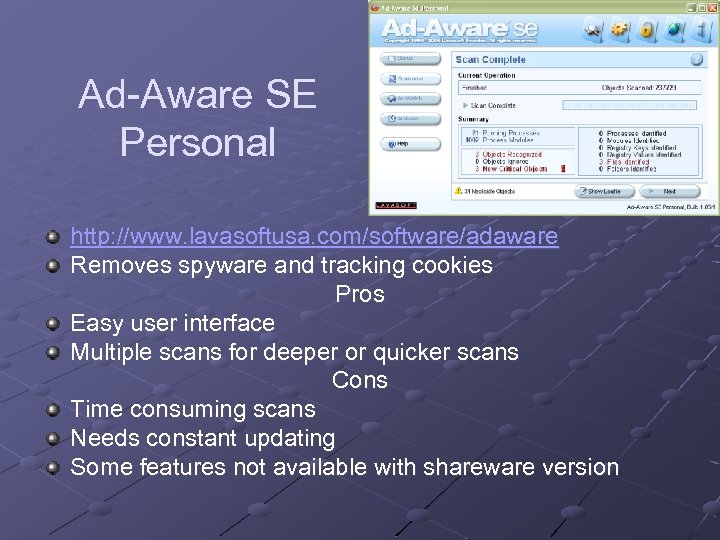
Ad-Aware SE Personal http: //www. lavasoftusa. com/software/adaware Removes spyware and tracking cookies Pros Easy user interface Multiple scans for deeper or quicker scans Cons Time consuming scans Needs constant updating Some features not available with shareware version
Spyware Blaster http: //www. javacoolsoftware. com/spywareblaster. html Works to actively prevent installation of Active. X-based spyware Pros Protects without being active in background Removes tracking cookies in IE Cons Requires constant updating to remain effective Only blocks limited programs Some features not available with shareware version
Hijack This http: //www. trendsecure. com/portal/en. US/threat_analytics/hijackthis. php Scans Windows OS files to compile a list of items to manually delete – for advanced users Pros Allows users to post log onto a web forum for “experts” to determine what should be removed Can find programs that self-replicate Cons One can delete files essential for their system and cause a system failure Automated tools for identifying “bad” entries are often not accurate or reliable
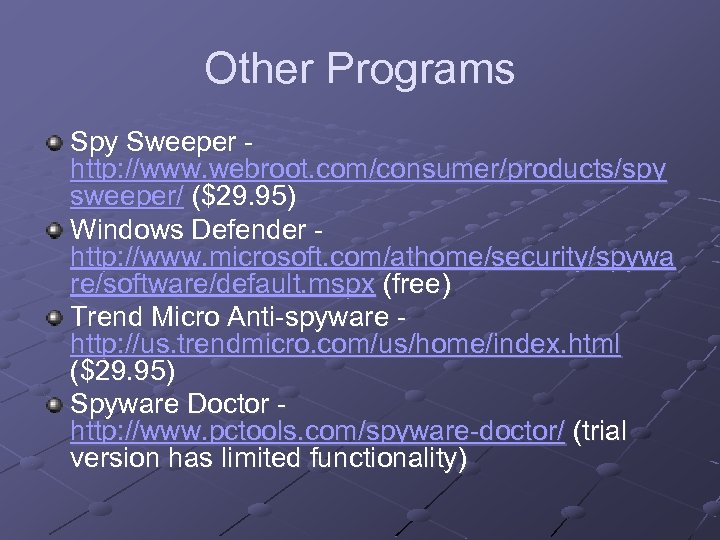
Other Programs Spy Sweeper http: //www. webroot. com/consumer/products/spy sweeper/ ($29. 95) Windows Defender http: //www. microsoft. com/athome/security/spywa re/software/default. mspx (free) Trend Micro Anti-spyware http: //us. trendmicro. com/us/home/index. html ($29. 95) Spyware Doctor http: //www. pctools. com/spyware-doctor/ (trial version has limited functionality)
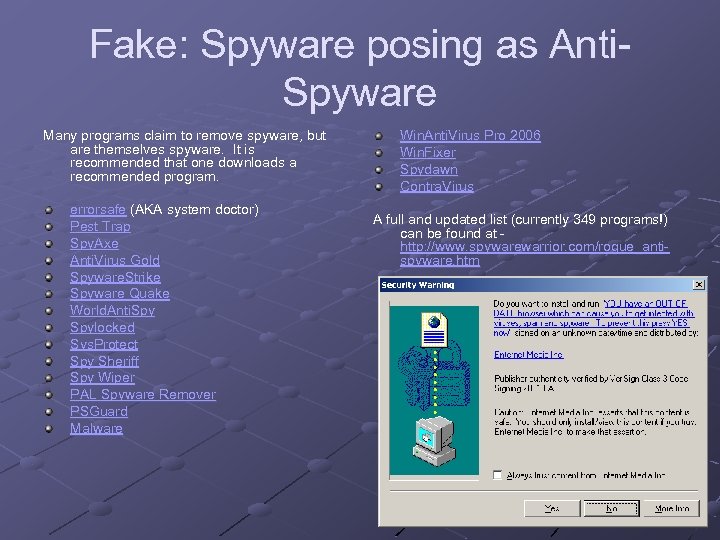
Fake: Spyware posing as Anti. Spyware Many programs claim to remove spyware, but are themselves spyware. It is recommended that one downloads a recommended program. errorsafe (AKA system doctor) Pest Trap Spy. Axe Anti. Virus Gold Spyware. Strike Spyware Quake World. Anti. Spylocked Sys. Protect Spy Sheriff Spy Wiper PAL Spyware Remover PSGuard Malware Win. Anti. Virus Pro 2006 Win. Fixer Spydawn Contra. Virus A full and updated list (currently 349 programs!) can be found at http: //www. spywarewarrior. com/rogue_antispyware. htm
Bibliography Image of crowded desktop from http: //upload. wikimedia. org/wikipedia/en/5/51/Spyware_infestation. png Image of spyware pop-up from http: //en. wikipedia. org/wiki/Image: Windows_Active. X_security_warning_%28 malware %29. png “Free” ad from http: //www. velnet. com/pictures/stop_popup_ads. gif AOL ad from http: //www. planetpoint. com/louisacopywriting/lsugar_aol. jpg Universal Studios ad from http: //vil. nai. com/IMAGES/123913_A. GIF Osama bin Laden ad from http: //www. petealbrecht. com/blog/osama. jpg Popular Mechanics ad from http: //static. howstuffworks. com/gif/web-advertising-popup -ad. gif Israel/Lebanon ad from http: //blog. pcformat. co. uk/resources/pcformat/lebanon. png MSN Today ad from http: //www. actsofvolition. com/images/msntoday. gif Tax relief ad from http: //www. taxreliefcoalition. org/docs/Chamber%20 Married%20 Pop%20 Up%20 Ad%2 003. 20. 03. jpg Weather ad from http: //vil. nai. com/images/133894_b. GIF Image of Ad-Aware from http: //en. wikipedia. org/wiki/Image: Ad-Aware_Personal. png Recent Surveys and Studies, Privacy Clearing House, retrieved June 30, 2006
88b42fe0a68cac1954be8d1a13ea769b.ppt