4604fb30db5751ed866ab041b63efefc.ppt
- Количество слайдов: 21
Computer Science Public Key Management Lecture 5
Outline • Key management with asymmetric encryption • Diffie-Hellman key exchange Computer Science
Key Management (public) Computer Science • public-key encryption helps address key distribution problems • have two aspects of this: – distribution of public keys – use of public-key encryption to distribute secret keys
Distribution of Public Keys • can be considered as using one of: – Public announcement – Publicly available directory – Public-key authority – Public-key certificates Computer Science
Public Announcement Computer Science • users distribute public keys to recipients or broadcast to community at large – (e. g. post to a newsgroup) • major weakness is forgery • Weakness: anyone can create a key claiming to be someone else and broadcast it (impersonation attack)
Publicly available directory. Computer Science • Publicly available directory: Achieve greater security by registering keys with a public directory • Weakness: directory must be trusted and still vulnerable to forgery – Public-key certificates (next slide) – Public-key authority (a few slides later)
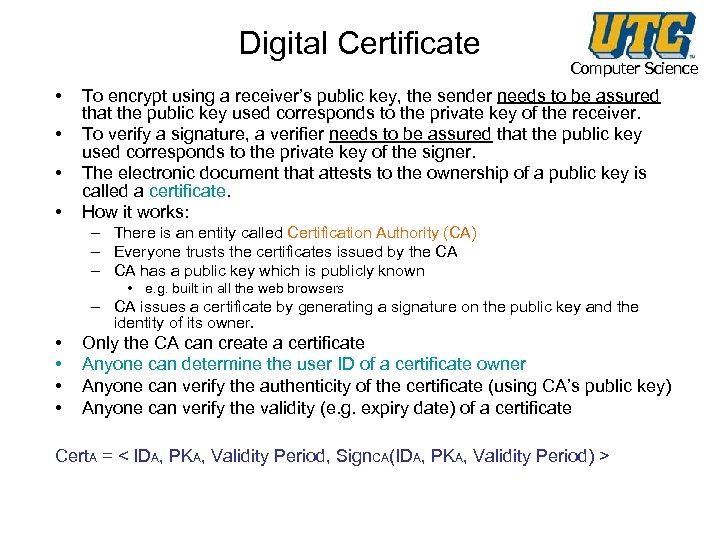
Digital Certificate • • Computer Science To encrypt using a receiver’s public key, the sender needs to be assured that the public key used corresponds to the private key of the receiver. To verify a signature, a verifier needs to be assured that the public key used corresponds to the private key of the signer. The electronic document that attests to the ownership of a public key is called a certificate. How it works: – There is an entity called Certification Authority (CA) – Everyone trusts the certificates issued by the CA – CA has a public key which is publicly known • e. g. built in all the web browsers – CA issues a certificate by generating a signature on the public key and the identity of its owner. • • Only the CA can create a certificate Anyone can determine the user ID of a certificate owner Anyone can verify the authenticity of the certificate (using CA’s public key) Anyone can verify the validity (e. g. expiry date) of a certificate Cert. A = < IDA, PKA, Validity Period, Sign. CA(IDA, PKA, Validity Period) >
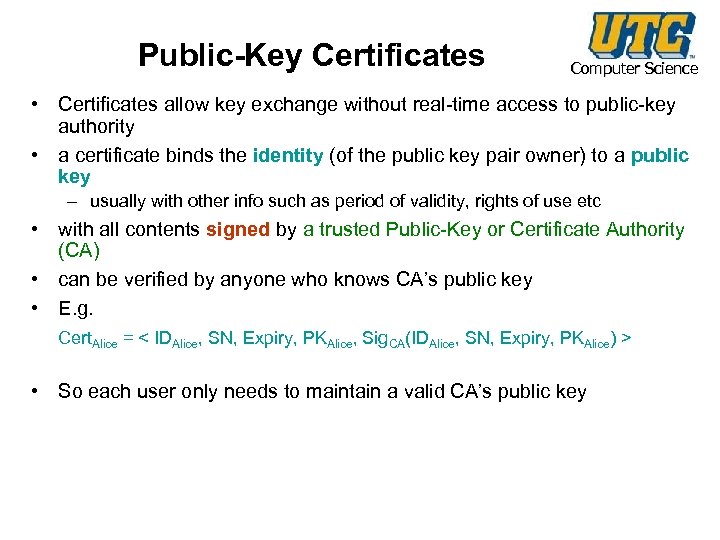
Public-Key Certificates Computer Science • Certificates allow key exchange without real-time access to public-key authority • a certificate binds the identity (of the public key pair owner) to a public key – usually with other info such as period of validity, rights of use etc • with all contents signed by a trusted Public-Key or Certificate Authority (CA) • can be verified by anyone who knows CA’s public key • E. g. Cert. Alice = < IDAlice, SN, Expiry, PKAlice, Sig. CA(IDAlice, SN, Expiry, PKAlice) > • So each user only needs to maintain a valid CA’s public key
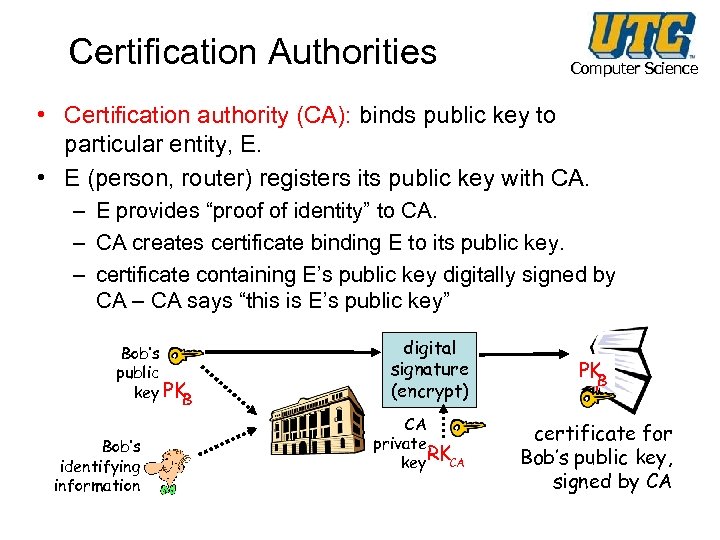
Certification Authorities Computer Science • Certification authority (CA): binds public key to particular entity, E. • E (person, router) registers its public key with CA. – E provides “proof of identity” to CA. – CA creates certificate binding E to its public key. – certificate containing E’s public key digitally signed by CA – CA says “this is E’s public key” Bob’s public key PK B Bob’s identifying information digital signature (encrypt) CA private RK key CA PK B certificate for Bob’s public key, signed by CA
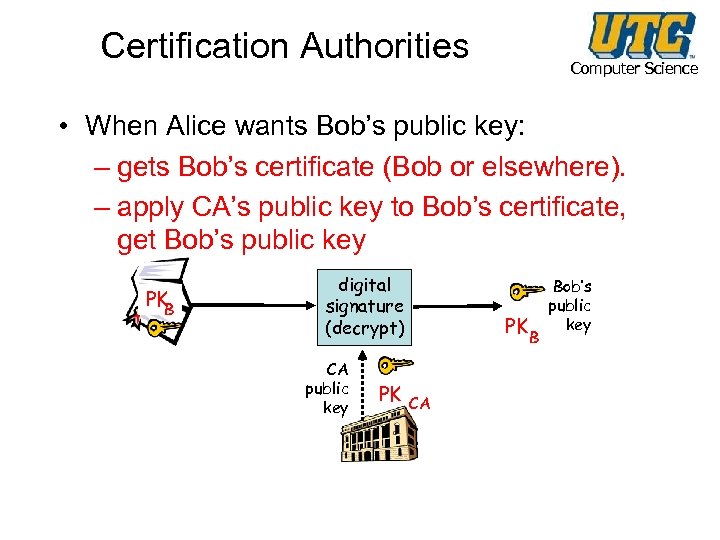
Certification Authorities Computer Science • When Alice wants Bob’s public key: – gets Bob’s certificate (Bob or elsewhere). – apply CA’s public key to Bob’s certificate, get Bob’s public key PK B digital signature (decrypt) CA public key PK PK B CA Bob’s public key
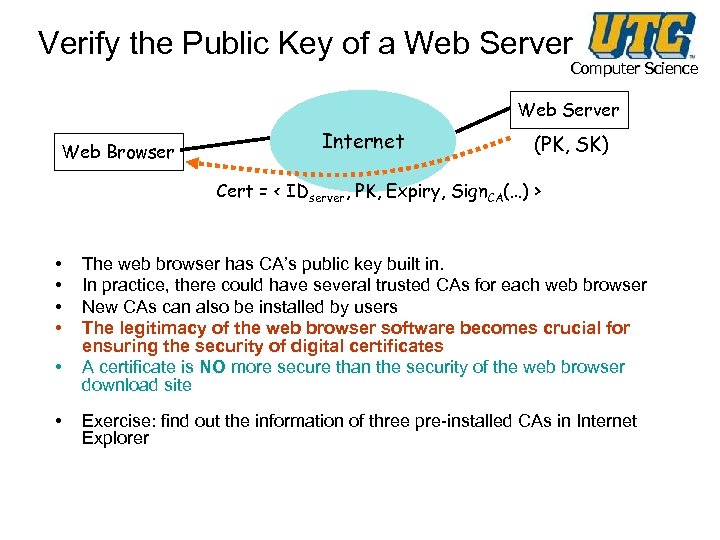
Verify the Public Key of a Web Server Computer Science Web Server Web Browser Internet (PK, SK) Cert = < IDserver, PK, Expiry, Sign. CA(…) > • • • The web browser has CA’s public key built in. In practice, there could have several trusted CAs for each web browser New CAs can also be installed by users The legitimacy of the web browser software becomes crucial for ensuring the security of digital certificates A certificate is NO more secure than the security of the web browser download site Exercise: find out the information of three pre-installed CAs in Internet Explorer
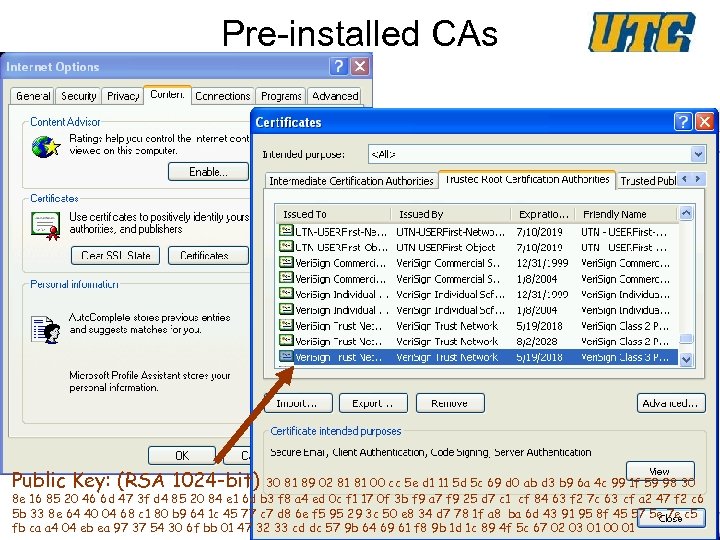
Pre-installed CAs Computer Science Public Key: (RSA 1024 -bit) 30 81 89 02 81 81 00 cc 5 e d 1 11 5 d 5 c 69 d 0 ab d 3 b 9 6 a 4 c 99 1 f 59 98 30 8 e 16 85 20 46 6 d 47 3 f d 4 85 20 84 e 1 6 d b 3 f 8 a 4 ed 0 c f 1 17 0 f 3 b f 9 a 7 f 9 25 d 7 c 1 cf 84 63 f 2 7 c 63 cf a 2 47 f 2 c 6 5 b 33 8 e 64 40 04 68 c 1 80 b 9 64 1 c 45 77 c 7 d 8 6 e f 5 95 29 3 c 50 e 8 34 d 7 78 1 f a 8 ba 6 d 43 91 95 8 f 45 57 5 e 7 e c 5 fb ca a 4 04 eb ea 97 37 54 30 6 f bb 01 47 32 33 cd dc 57 9 b 64 69 61 f 8 9 b 1 d 1 c 89 4 f 5 c 67 02 03 01 00 01
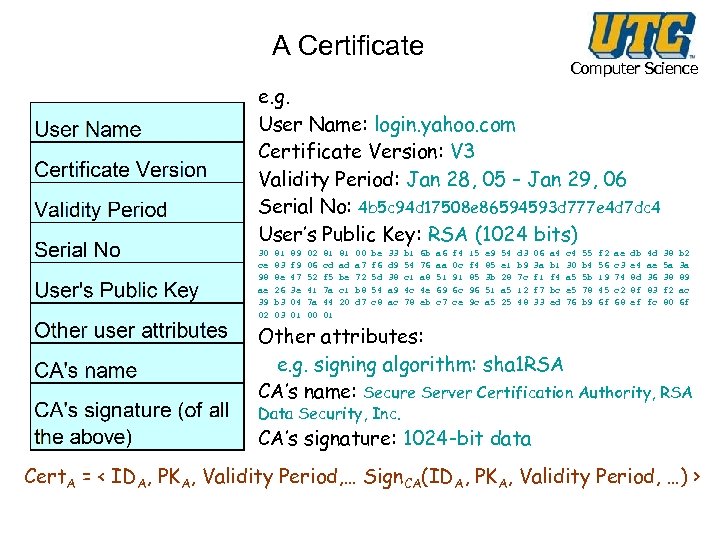
A Certificate Computer Science e. g. User Name: login. yahoo. com Certificate Version: V 3 Validity Period: Jan 28, 05 – Jan 29, 06 Serial No: 4 b 5 c 94 d 17508 e 86594593 d 777 e 4 d 7 dc 4 User’s Public Key: RSA (1024 bits) 30 ce 98 ae 39 02 81 83 8 e 26 b 3 03 89 f 9 47 3 e 04 01 02 06 52 41 7 a 00 81 cd f 5 7 a 44 01 81 ad be c 1 20 00 a 7 72 b 8 d 7 be f 6 5 d 54 c 8 33 d 9 38 a 9 ac b 1 54 c 1 4 c 78 6 b 76 a 8 4 e eb a 6 aa 51 69 c 7 f 4 0 c 91 6 c ce 15 f 4 85 96 9 c e 9 85 3 b 51 a 5 54 e 1 28 a 5 25 d 3 b 9 7 c 12 48 06 3 a f 1 f 7 33 a 4 b 1 f 4 bc ed c 4 30 a 5 e 5 76 55 b 4 5 b 78 b 9 f 2 56 19 45 6 f ae c 3 74 c 2 68 db e 4 8 d 8 f ef 4 d ae 36 83 fc 38 5 a 38 f 2 80 b 2 3 a 89 ac 6 f Other attributes: e. g. signing algorithm: sha 1 RSA CA’s name: Secure Server Certification Authority, RSA Data Security, Inc. CA’s signature: 1024 -bit data Cert. A = < IDA, PKA, Validity Period, … Sign. CA(IDA, PKA, Validity Period, …) >
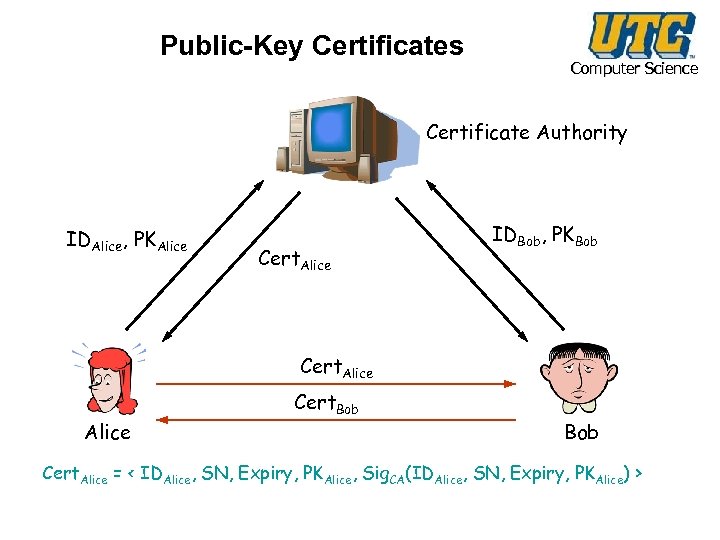
Public-Key Certificates Computer Science Certificate Authority IDAlice, PKAlice Cert. Alice IDBob, PKBob Cert. Alice Cert. Bob Cert. Alice = < IDAlice, SN, Expiry, PKAlice, Sig. CA(IDAlice, SN, Expiry, PKAlice) >
Computer Science Distribution of Secret Keys using Public Key
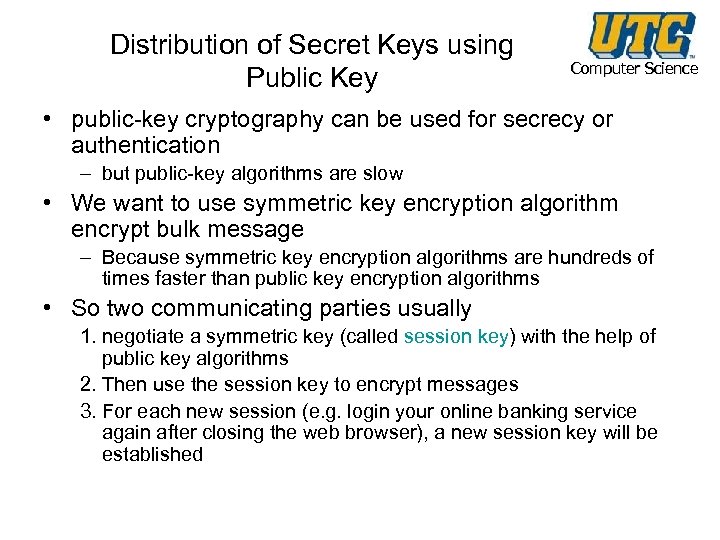
Distribution of Secret Keys using Public Key Computer Science • public-key cryptography can be used for secrecy or authentication – but public-key algorithms are slow • We want to use symmetric key encryption algorithm encrypt bulk message – Because symmetric key encryption algorithms are hundreds of times faster than public key encryption algorithms • So two communicating parties usually 1. negotiate a symmetric key (called session key) with the help of public key algorithms 2. Then use the session key to encrypt messages 3. For each new session (e. g. login your online banking service again after closing the web browser), a new session key will be established
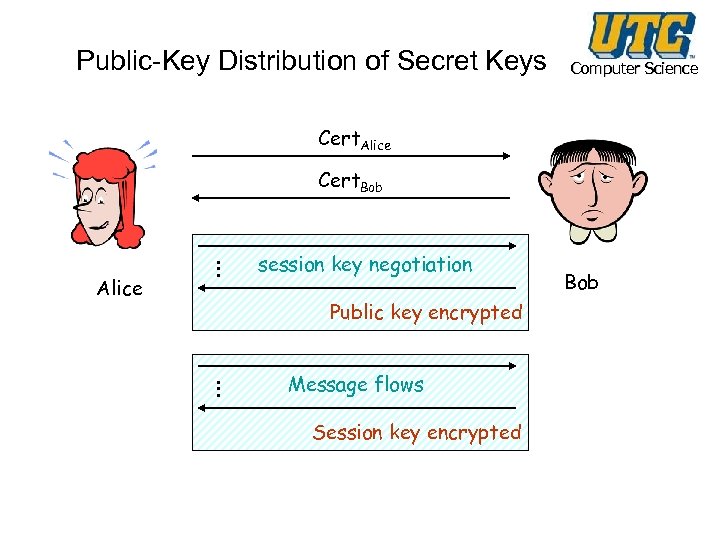
Public-Key Distribution of Secret Keys Computer Science Cert. Alice Cert. Bob … Alice session key negotiation Public key encrypted … Message flows Session key encrypted Bob
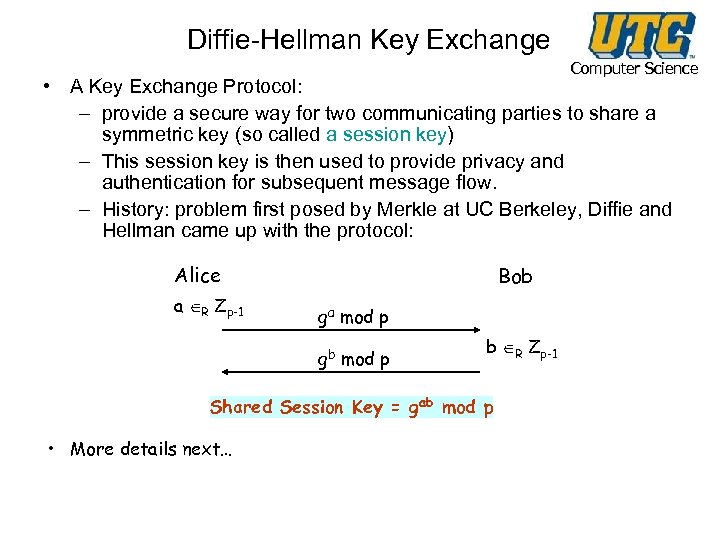
Diffie-Hellman Key Exchange Computer Science • A Key Exchange Protocol: – provide a secure way for two communicating parties to share a symmetric key (so called a session key) – This session key is then used to provide privacy and authentication for subsequent message flow. – History: problem first posed by Merkle at UC Berkeley, Diffie and Hellman came up with the protocol: Alice a R Zp-1 Bob ga mod p gb mod p b R Zp-1 Shared Session Key = gab mod p • More details next…
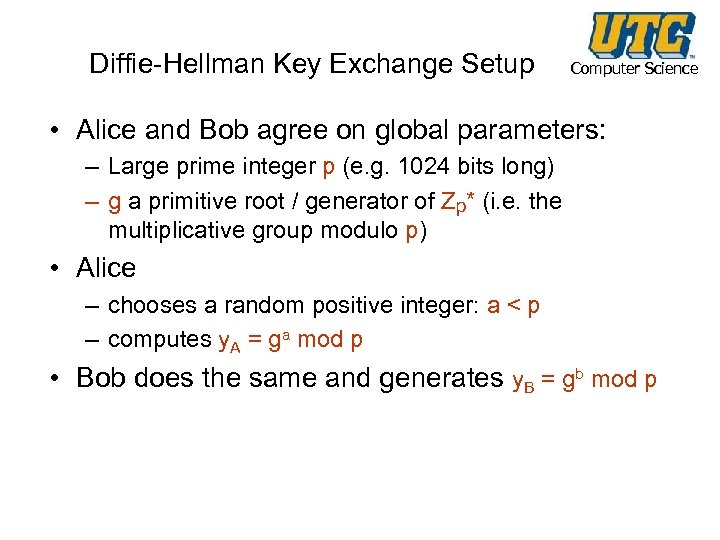
Diffie-Hellman Key Exchange Setup Computer Science • Alice and Bob agree on global parameters: – Large prime integer p (e. g. 1024 bits long) – g a primitive root / generator of Zp* (i. e. the multiplicative group modulo p) • Alice – chooses a random positive integer: a < p – computes y. A = ga mod p • Bob does the same and generates y. B = gb mod p
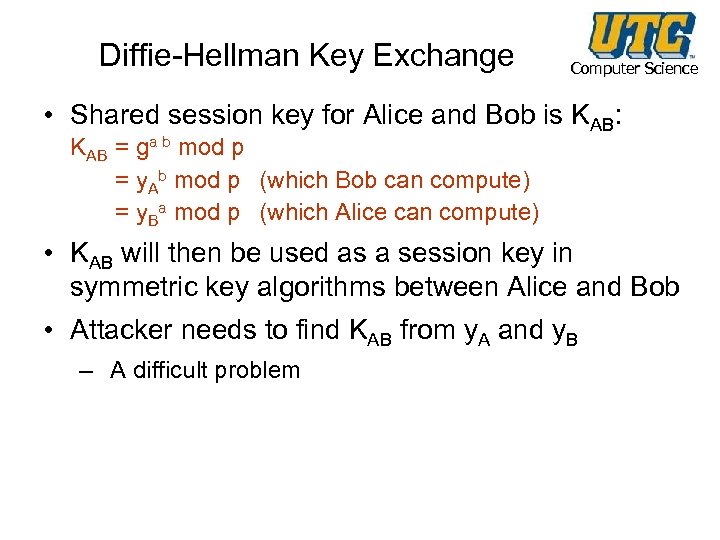
Diffie-Hellman Key Exchange Computer Science • Shared session key for Alice and Bob is KAB: KAB = ga b mod p = y. Ab mod p (which Bob can compute) = y. Ba mod p (which Alice can compute) • KAB will then be used as a session key in symmetric key algorithms between Alice and Bob • Attacker needs to find KAB from y. A and y. B – A difficult problem
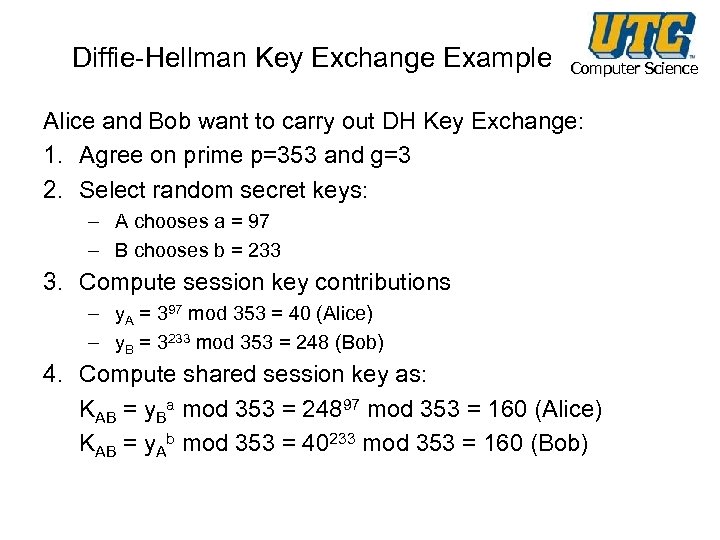
Diffie-Hellman Key Exchange Example Computer Science Alice and Bob want to carry out DH Key Exchange: 1. Agree on prime p=353 and g=3 2. Select random secret keys: – A chooses a = 97 – B chooses b = 233 3. Compute session key contributions – y. A = 397 mod 353 = 40 (Alice) – y. B = 3233 mod 353 = 248 (Bob) 4. Compute shared session key as: KAB = y. Ba mod 353 = 24897 mod 353 = 160 (Alice) KAB = y. Ab mod 353 = 40233 mod 353 = 160 (Bob)
4604fb30db5751ed866ab041b63efefc.ppt