4148ce77a2560e60861a3ce2bcd7c6d0.ppt
- Количество слайдов: 21

Comb-e-Chem PKI Mike Surridge, Steve Taylor IT Innovation
Public Key Infrastructure (PKI) • Requirements: – – – be able to authenticate remote users be easy to operate by Chemists (e. g. NCS) be secure enough for academic users • Analysis of existing NCS authentication: – – – uses personal knowledge of user community uses contextual information (e. g. EPSRC project codes) lightweight for both NCS and their customers • Public key infrastructure developments: – Comb-e-Chem certification policy agreed – procedures developed for NCS to certify remote users – operational responsibility transferred to Chemistry

PKI Roles • Grid community – defines security policy and certificate policy (CP) – approves certification authorities • Certification Authority (CA) – defines certification practise statement (CPS) – engages registration authorities – issues certificates in accordance with policy • Registration Authority (RA) – checks credentials of certificate applicants – enforces security and certificate policy
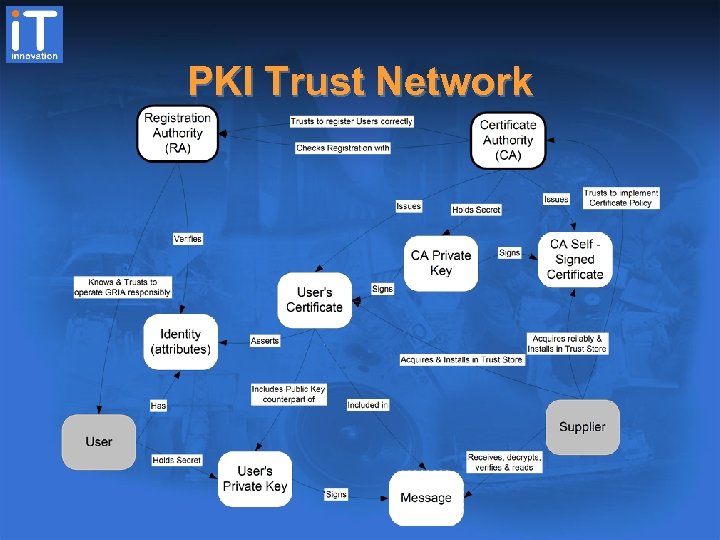
PKI Trust Network
Comb-e-Chem CP • CP is Certification Policy – a set of rules by which a PKI must operate – follows a format described in RFC 2527 – areas such as user registration, physical security, certificate life cycle, etc… • Comb-e-Chem CP pays particular attention to – user registration – certificate life cycle
NCS CPS • CPS is Certificate Practice Statement • A description of how the NCS CA (Sam) abides by and implements the rules in the CP – describes operational procedures for implementing the CP’s requirements – contains a number of agreement forms to be signed by the parties involved
PKI - Lessons Learned • The PKI must have well-defined procedures and strict adherence to them – CP & CPS • The CA must exercise rigour in operational procedures – – – checking of credentials following procedures to the letter physical security audit trails backups revocation
PKI - Lessons Learned 2 • User education must be addressed – the concepts of PKI are complex – the overhead of education can be a barrier to takeup – ill-informed users can worsen security – do users understand what is meant by (for example) a private key and a certificate? – do they understand their security obligations? – in the NCS case, users are guided by the RA

Comb-e-Chem Security Mike Surridge, Steve Taylor IT Innovation

Overview of Activities • Security risk management – applied to the NCS service • Security implementation – operating policies and public key infrastructure – deployment of security features at NCS
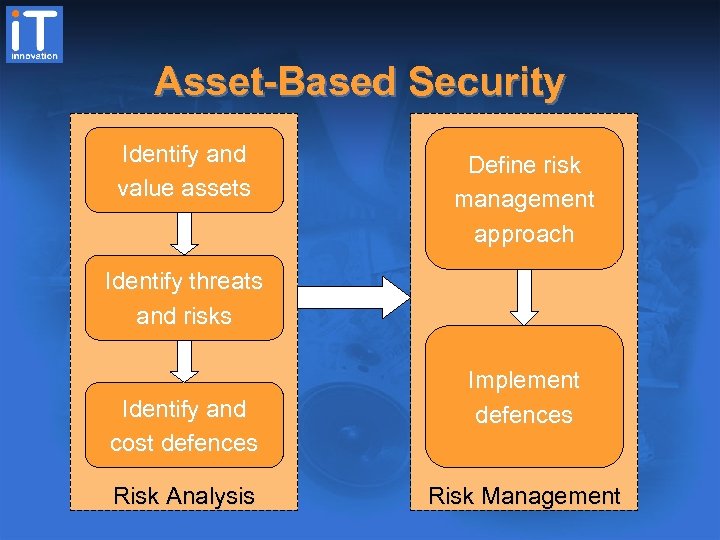
Asset-Based Security Identify and value assets Define risk management approach Identify threats and risks Identify and cost defences Risk Analysis Implement defences Risk Management
Risk Analysis • Value assets based on impact of compromise – high: likely to cause total business failure – med: significant but not fatal impact – low: irritating but no significant impact • Threats based on likelihood of attack – high: attacks will definitely take place – med: attacks may occur from time to time – low: attacks are unlikely • Risks based on likelihood of success – taking account of existing defences
Risk Management • Determine appropriate response to threats – acceptance: live with the potential consequences – reduction: introduce defences – avoidance: don’t use the system • Leads to cost-effective security – as much security as you need – not more than you can afford
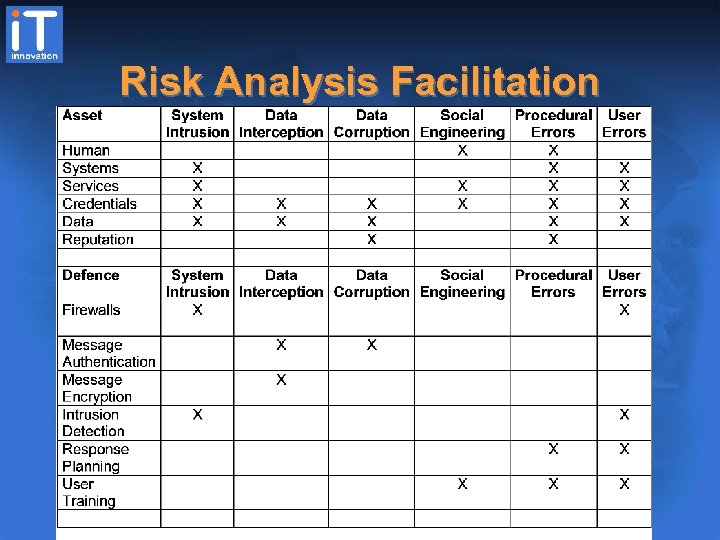
Risk Analysis Facilitation
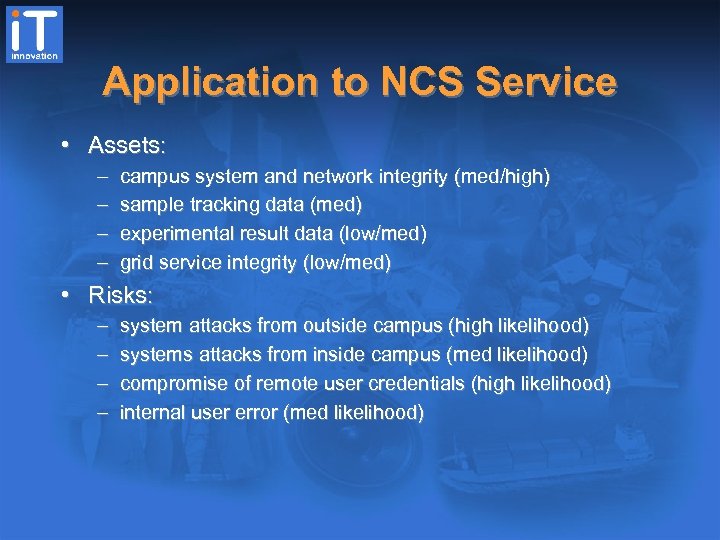
Application to NCS Service • Assets: – – campus system and network integrity (med/high) sample tracking data (med) experimental result data (low/med) grid service integrity (low/med) • Risks: – – system attacks from outside campus (high likelihood) systems attacks from inside campus (med likelihood) compromise of remote user credentials (high likelihood) internal user error (med likelihood)
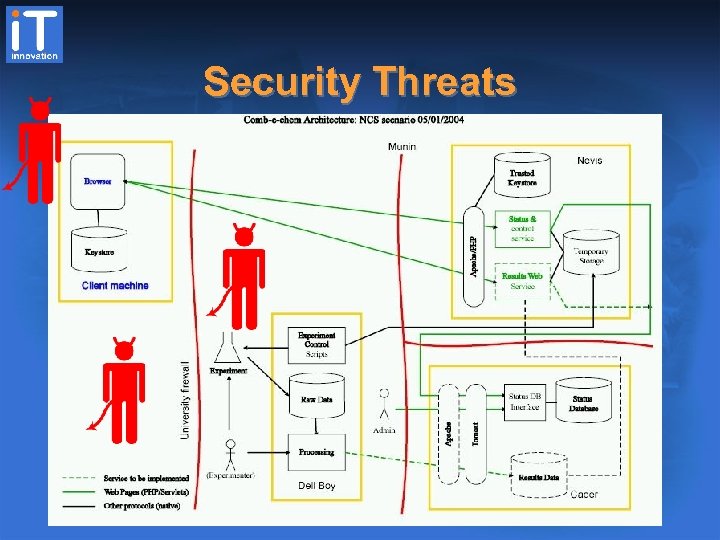
Security Threats
Conclusions • Progress with core technology developments – authorisation and WS-Security – relevant for service integration • NCS security risks analysed – appropriate defences identified • Security procedures and infrastructure implemented – public key infrastructure (CA, RAs, policies) – firewalls and protocols for NCS deployment

Comb-e-Chem Security Mike Surridge, Steve Taylor IT Innovation
Conclusions • Progress with core technology developments – authorisation and WS-Security – relevant for service integration • NCS security risks analysed – appropriate defences identified • Security procedures and infrastructure implemented – public key infrastructure (CA, RAs, policies) – firewalls and protocols for NCS deployment
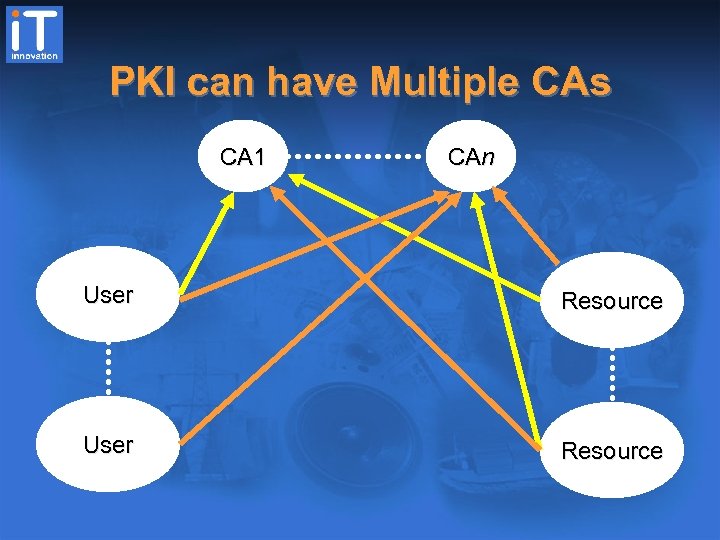
PKI can have Multiple CAs CA 1 CAn User Resource
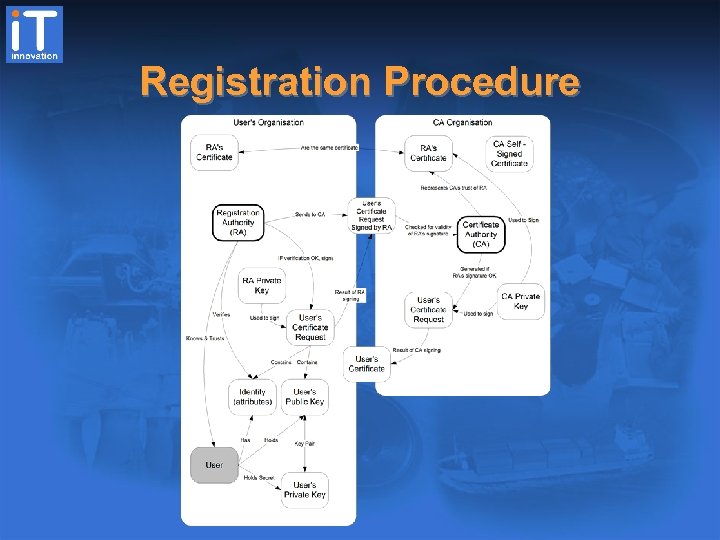
Registration Procedure
4148ce77a2560e60861a3ce2bcd7c6d0.ppt