fed7aacd3a872ff9ce9b5091167c0fe6.ppt
- Количество слайдов: 49
Code Security Gordon College Stephen Brinton
Virtual Machine Security • Building a fence around your code – JVM – Java Virtual Machine • Originally developed by Sun Microsystems • Executes Java Bytecode – Execution by: Interpretation (JVM) or Compilation (JIT) – Common Language Runtime • Developed by Microsoft • Executes Common Intermediate Language (CIL) – Verified and then run as native code on machine
Java’s Security • Strongly Typed Compiler – Eliminate programming bugs – Help enforce language semantics • Bytecode verifier – Makes sure the rules of Java are followed in the compiled code • Classloader – Finds, loads, and defines classes (runs verifier on them) • Security Manager – Main interface between the system and the Java Code
Trusted vs Untrusted Code • Trusted – Java API code – Code loaded from the classpath – resides outside the “sandbox” • Untrusted – Code loaded from outside the classpath (usually from a network) – Confined to the “sandbox” • Java Apps (by default) live outside the sandbox and Java Applets are confined within the sandbox
What’s a “Sandbox”? • Applets run inside a “sandbox” – If you download code, it has to play within the JVM (Sandbox) – Security. Manager is called for certain methods, and can forbid access • JDK 1. 1 introduced the notions of codesigning and “trusted applets”
Sandboxes How do you protect your computer bad code? • The solution: Make untrusted code play within a sandbox. • Need for varying security policies increases – You assign “permissions” to pieces of code – JDK 1. 1 (digital signatures) – if user trusts the digitally signed code – users could allow normally untrusted code to access resources • Enforcement Mechanism for Policy (sandbox)? – Security Managers
Java Sandbox The sandbox for untrusted Java applets, for example, prohibits many activities, including: • Reading or writing to the local disk • Making a network connection to any host, except the host from which the applet came • Creating a new process • Loading a new dynamic library and directly calling a native method
Java Sandbox • The fundamental components responsible for Java's sandbox are: * Safety features built into the Java virtual machine (and the language) * The class loader architecture * The class file verifier * The security manager and the Java API
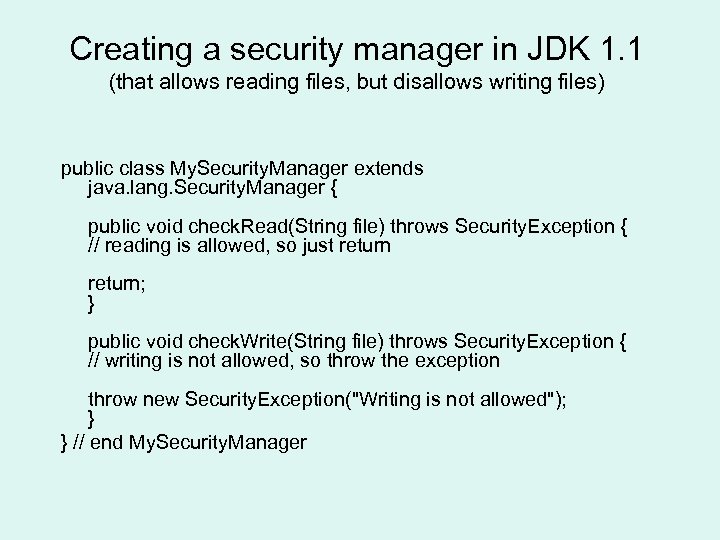
Creating a security manager in JDK 1. 1 (that allows reading files, but disallows writing files) public class My. Security. Manager extends java. lang. Security. Manager { public void check. Read(String file) throws Security. Exception { // reading is allowed, so just return; } public void check. Write(String file) throws Security. Exception { // writing is not allowed, so throw the exception throw new Security. Exception("Writing is not allowed"); } } // end My. Security. Manager
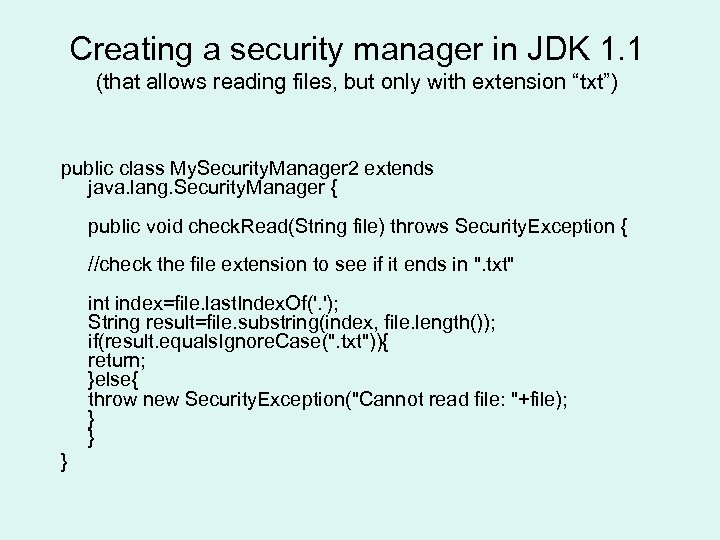
Creating a security manager in JDK 1. 1 (that allows reading files, but only with extension “txt”) public class My. Security. Manager 2 extends java. lang. Security. Manager { public void check. Read(String file) throws Security. Exception { //check the file extension to see if it ends in ". txt" int index=file. last. Index. Of('. '); String result=file. substring(index, file. length()); if(result. equals. Ignore. Case(". txt")){ return; }else{ throw new Security. Exception("Cannot read file: "+file); } } }
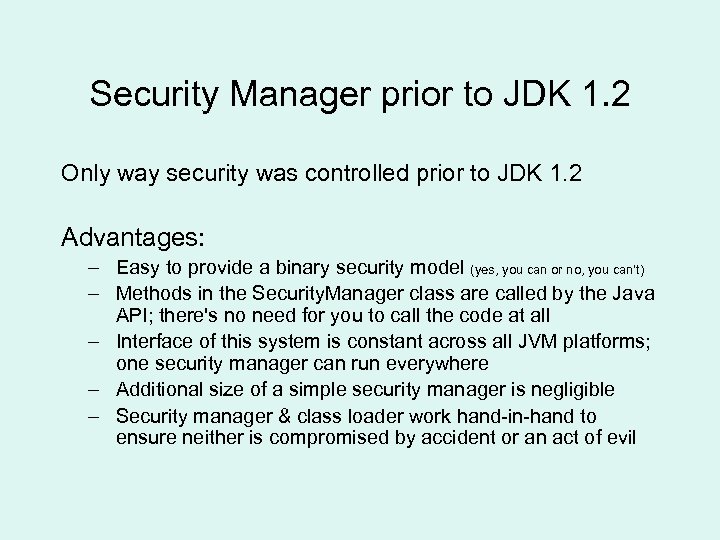
Security Manager prior to JDK 1. 2 Only way security was controlled prior to JDK 1. 2 Advantages: – Easy to provide a binary security model (yes, you can or no, you can't) – Methods in the Security. Manager class are called by the Java API; there's no need for you to call the code at all – Interface of this system is constant across all JVM platforms; one security manager can run everywhere – Additional size of a simple security manager is negligible – Security manager & class loader work hand-in-hand to ensure neither is compromised by accident or an act of evil
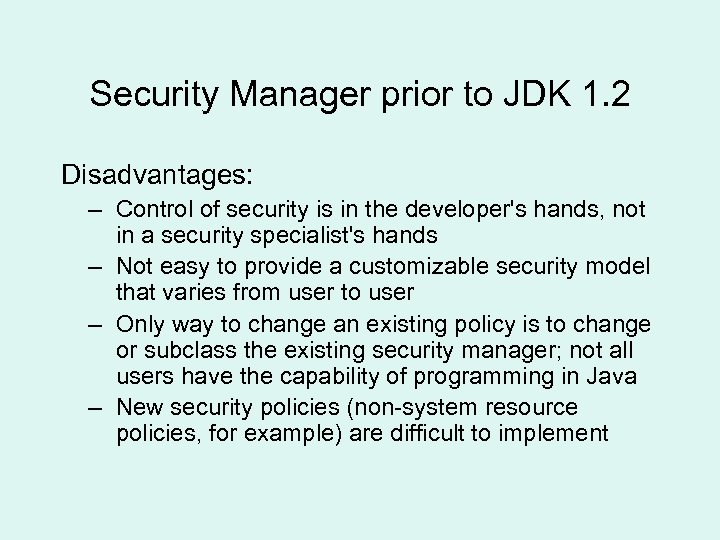
Security Manager prior to JDK 1. 2 Disadvantages: – Control of security is in the developer's hands, not in a security specialist's hands – Not easy to provide a customizable security model that varies from user to user – Only way to change an existing policy is to change or subclass the existing security manager; not all users have the capability of programming in Java – New security policies (non-system resource policies, for example) are difficult to implement

Install a Security. Manager • Applications don’t start, by default, with a Security. Manager • You must install one, either from within the code, or using a command line argument java -Djava. security. manager
Building a bigger and better sandbox • To provide greater control to user and developer – Traditional sandbox (java. security package) was expanded to include: • Access. Controller class – Muscle of the security manager – enforces policy • Permission class • Policy class
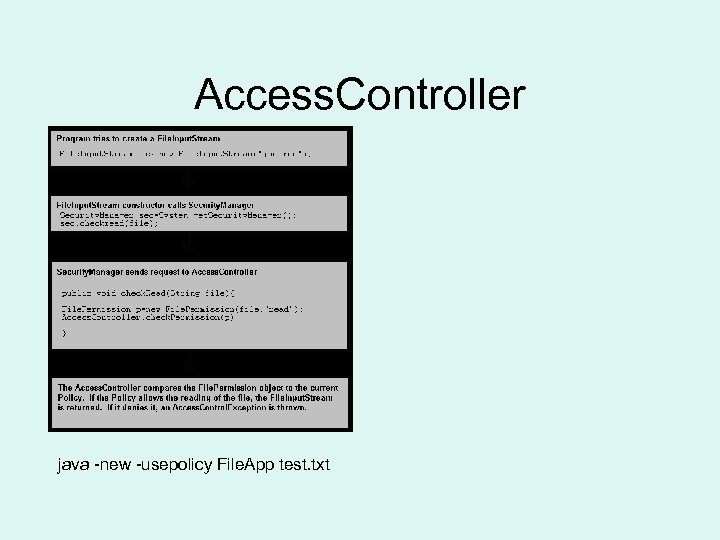
Access. Controller java -new -usepolicy File. App test. txt
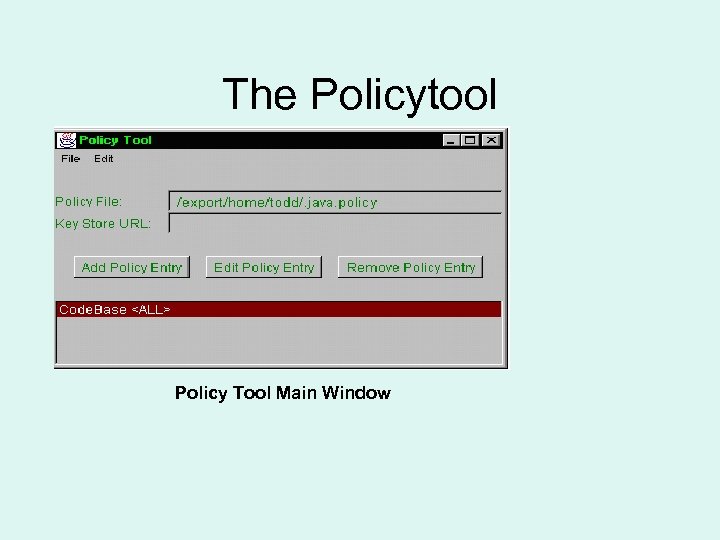
The Policytool Policy Tool Main Window
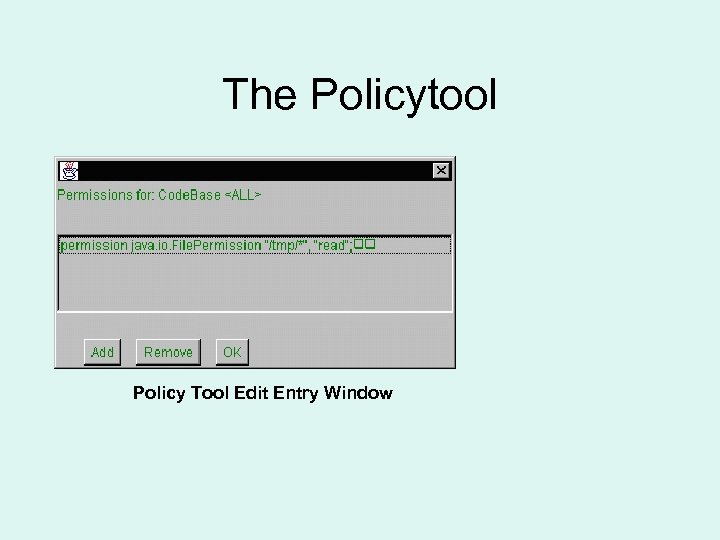
The Policytool Policy Tool Edit Entry Window
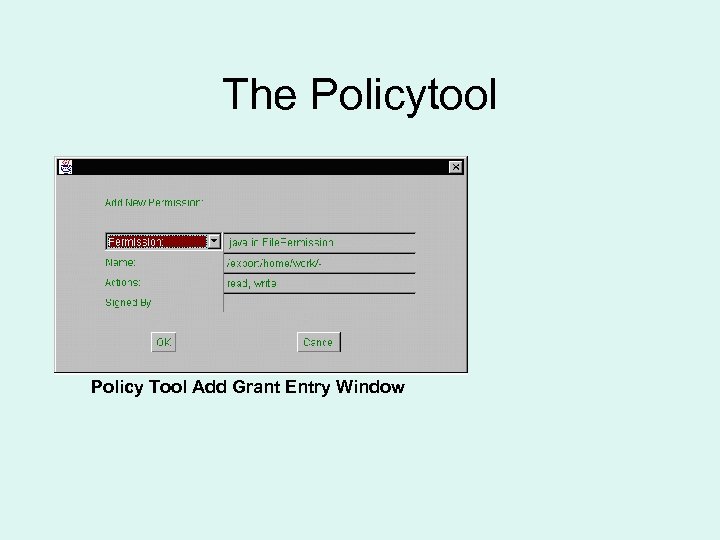
The Policytool Policy Tool Add Grant Entry Window
. NET Framework • Different administrative software model • Fixed location (traditional) • Dynamic nature of software (present) – Dynamic downloads and execution – Remote execution – Security is essential
Security Models • Role-based security – Users have access to resources based on roles – Model used by most operating systems • Code access security (new with. Net) – Also called “evidence-based security” – Even if user is trusted - the code may not be. – Tackles the problem with mobile code Both models are found in. Net framework
Code Access Security mechanism of the CLR – Manages code and depends on level of trust – CLR – will lessen and tighten its grip based on permission and trust level • Very similar to the sandbox view – Two aspects: • Control the access level given to an application (assembly) • Control access to a particular resource (like a database)
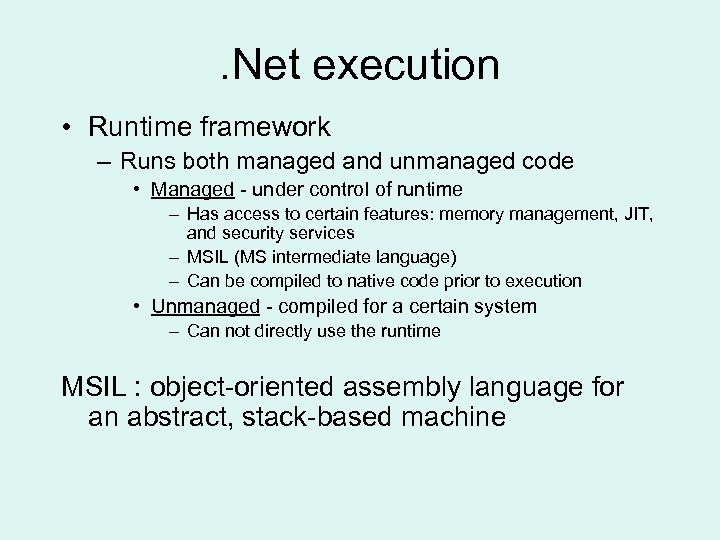
. Net execution • Runtime framework – Runs both managed and unmanaged code • Managed - under control of runtime – Has access to certain features: memory management, JIT, and security services – MSIL (MS intermediate language) – Can be compiled to native code prior to execution • Unmanaged - compiled for a certain system – Can not directly use the runtime MSIL : object-oriented assembly language for an abstract, stack-based machine
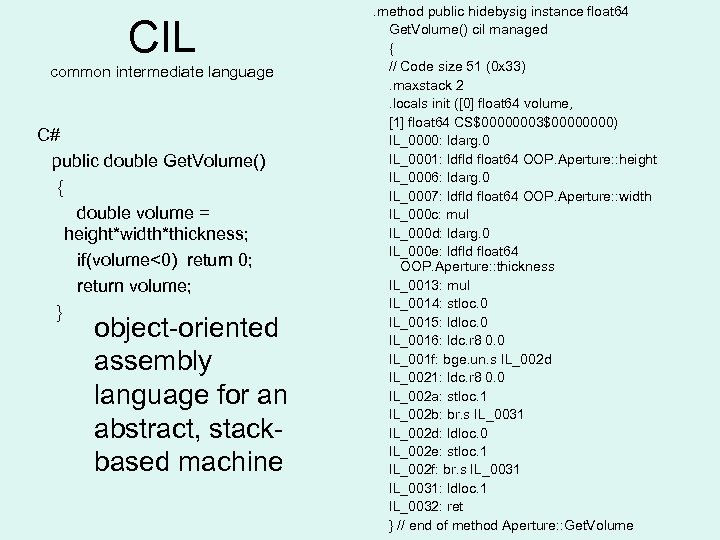
CIL common intermediate language C# public double Get. Volume() { double volume = height*width*thickness; if(volume<0) return 0; return volume; } object-oriented assembly language for an abstract, stackbased machine . method public hidebysig instance float 64 Get. Volume() cil managed { // Code size 51 (0 x 33). maxstack 2. locals init ([0] float 64 volume, [1] float 64 CS$00000003$0000) IL_0000: ldarg. 0 IL_0001: ldfld float 64 OOP. Aperture: : height IL_0006: ldarg. 0 IL_0007: ldfld float 64 OOP. Aperture: : width IL_000 c: mul IL_000 d: ldarg. 0 IL_000 e: ldfld float 64 OOP. Aperture: : thickness IL_0013: mul IL_0014: stloc. 0 IL_0015: ldloc. 0 IL_0016: ldc. r 8 0. 0 IL_001 f: bge. un. s IL_002 d IL_0021: ldc. r 8 0. 0 IL_002 a: stloc. 1 IL_002 b: br. s IL_0031 IL_002 d: ldloc. 0 IL_002 e: stloc. 1 IL_002 f: br. s IL_0031: ldloc. 1 IL_0032: ret } // end of method Aperture: : Get. Volume
CLR common language runtime
CLR common language runtime 3 different runtimes 1. A single CLR that runs all ASP. NET apps 2. Browsers (IE) uses a single CLR that executes all dowloaded controls 3. CLR used to execute commands run from the OS shell.
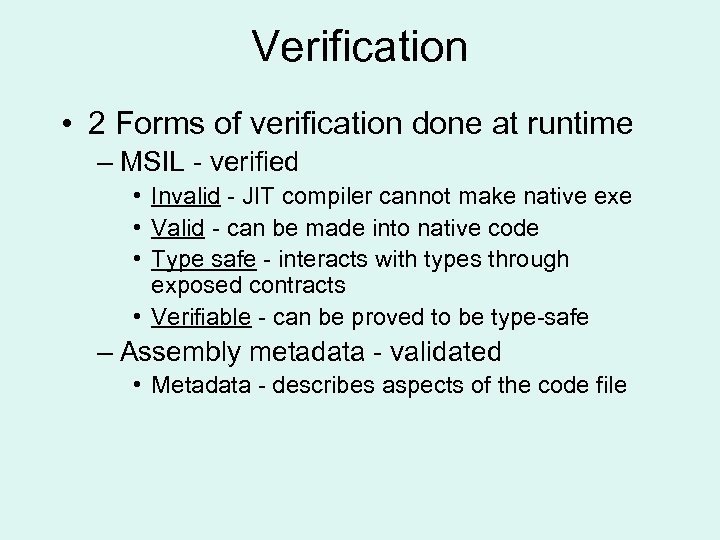
Verification • 2 Forms of verification done at runtime – MSIL - verified • Invalid - JIT compiler cannot make native exe • Valid - can be made into native code • Type safe - interacts with types through exposed contracts • Verifiable - can be proved to be type-safe – Assembly metadata - validated • Metadata - describes aspects of the code file
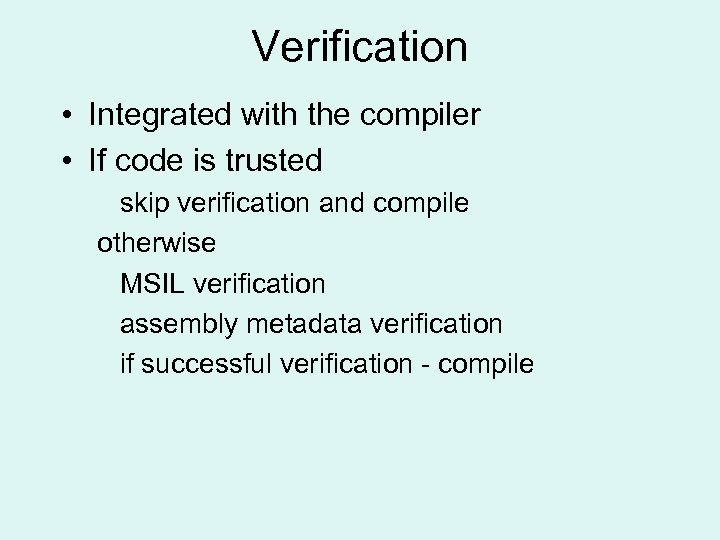
Verification • Integrated with the compiler • If code is trusted skip verification and compile otherwise MSIL verification assembly metadata verification if successful verification - compile
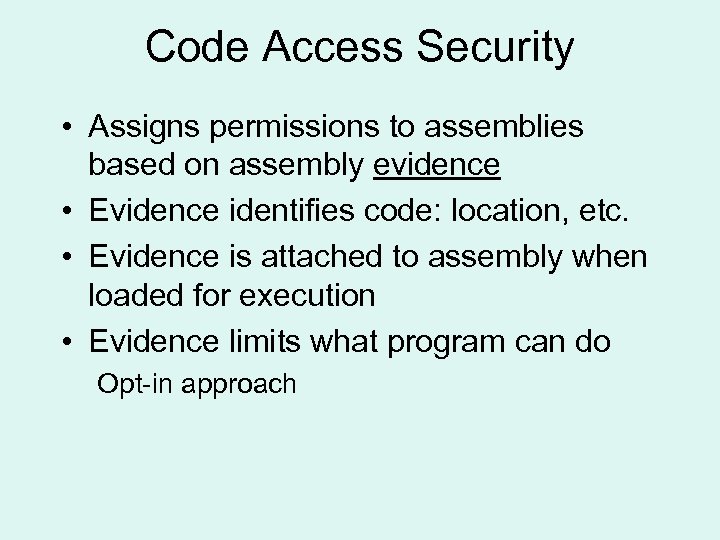
Code Access Security • Assigns permissions to assemblies based on assembly evidence • Evidence identifies code: location, etc. • Evidence is attached to assembly when loaded for execution • Evidence limits what program can do Opt-in approach
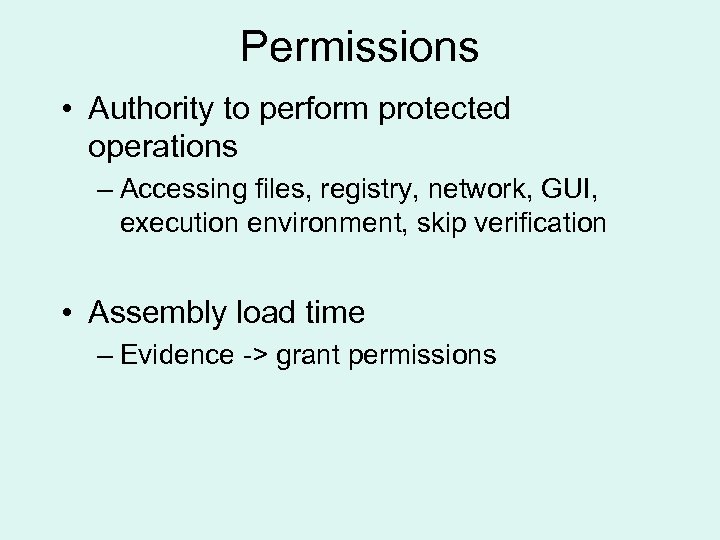
Permissions • Authority to perform protected operations – Accessing files, registry, network, GUI, execution environment, skip verification • Assembly load time – Evidence -> grant permissions
Evidence • • Zone URL Hash (encrypted value) Strong name - unique ID for program Site Application Directory Publisher certificate
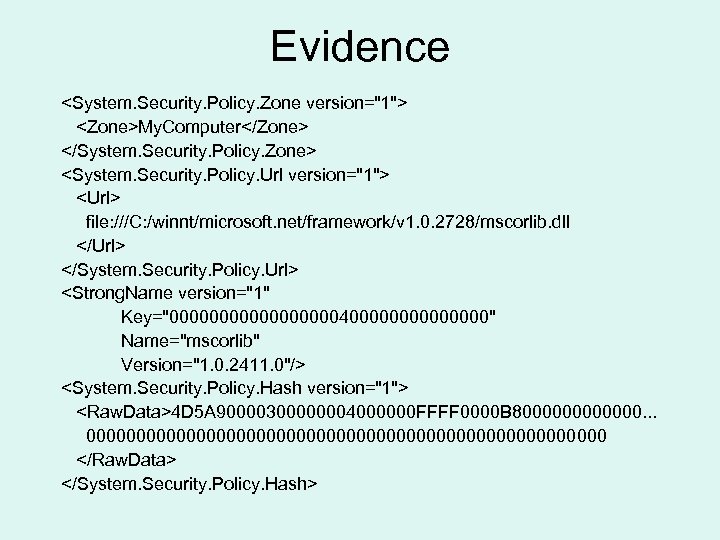
Evidence <System. Security. Policy. Zone version="1"> <Zone>My. Computer</Zone> </System. Security. Policy. Zone> <System. Security. Policy. Url version="1"> <Url> file: ///C: /winnt/microsoft. net/framework/v 1. 0. 2728/mscorlib. dll </Url> </System. Security. Policy. Url> <Strong. Name version="1" Key="00000000040000000" Name="mscorlib" Version="1. 0. 2411. 0"/> <System. Security. Policy. Hash version="1"> <Raw. Data>4 D 5 A 90000300000004000000 FFFF 0000 B 8000000. . . 00000000000000000000000000 </Raw. Data> </System. Security. Policy. Hash>
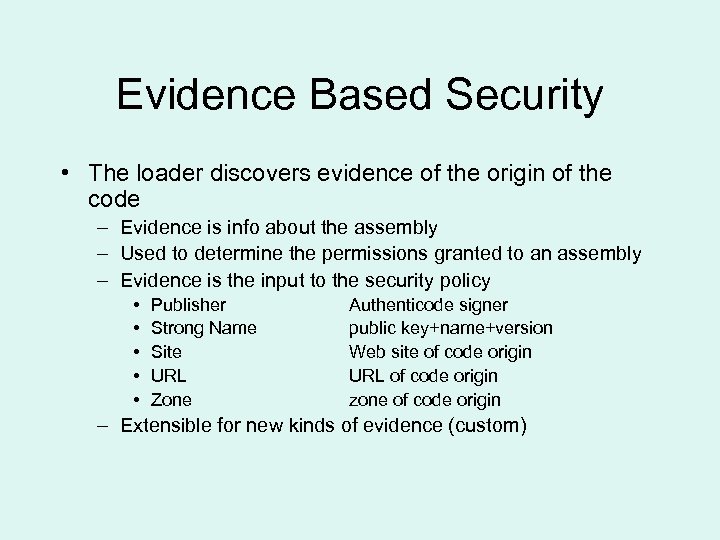
Evidence Based Security • The loader discovers evidence of the origin of the code – Evidence is info about the assembly – Used to determine the permissions granted to an assembly – Evidence is the input to the security policy • • • Publisher Strong Name Site URL Zone Authenticode signer public key+name+version Web site of code origin URL of code origin zone of code origin – Extensible for new kinds of evidence (custom)
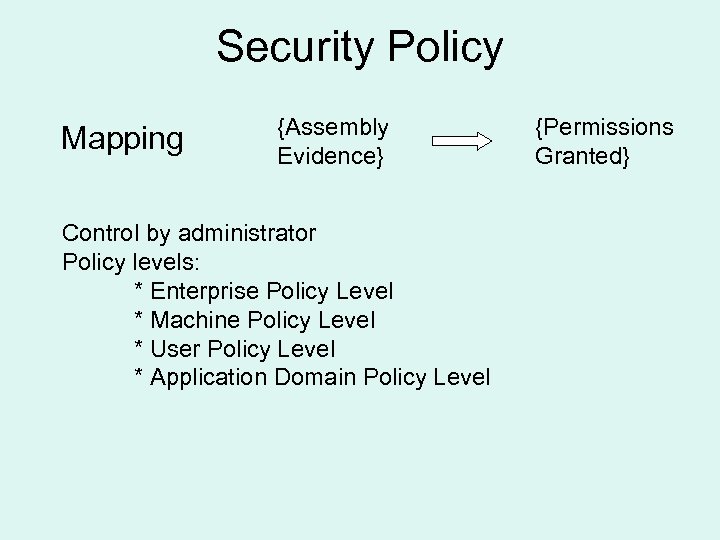
Security Policy Mapping {Assembly Evidence} Control by administrator Policy levels: * Enterprise Policy Level * Machine Policy Level * User Policy Level * Application Domain Policy Level {Permissions Granted}
Security Policy Determining the set of granted permissions: 1. Policy levels evaluate the evidence and generate a set of permissions. 2. Permission sets calculated for each policy level are intersected with each other. 3. Resulting permission set is compared with the set of permissions the assembly declared necessary to run.
Security Policy
. NET Framework • Code groups – Bring together code with similar characteristics • Evidence – Information used to place code into code groups – where code is from (internet or intranet), publisher, strong name, URI from download, etc. • Arranged in a hierarchy • Permissions – Actions you allow each code group to perform • For example: “able to access the user interface” – Managed by system admin. at the enterprise, machine and user levels
. NET Framework
. NET Framework Condition: All code, Permission Set: Nothing Condition: Zone: Internet, Permission Set: Internet Condition: URL: www. monash. edu. au, Permission Set: Monash. PSet Condition: Strong Name: m-Commerce, Permission Set: m-Commerce. PSet
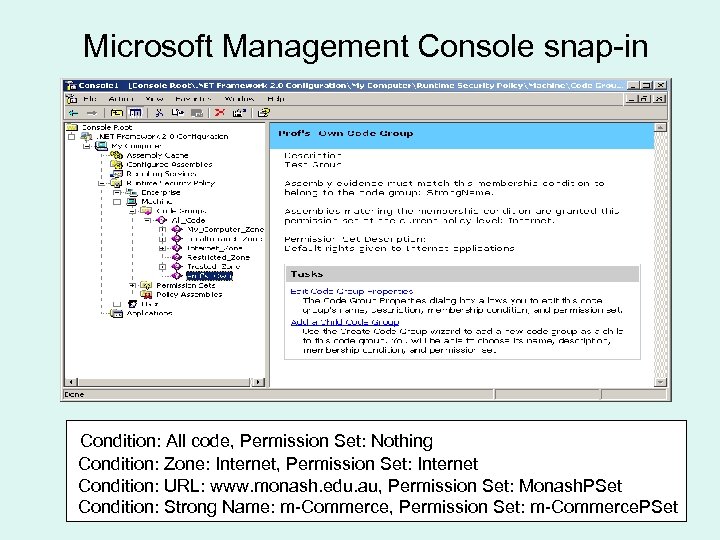
Microsoft Management Console snap-in Condition: All code, Permission Set: Nothing Condition: Zone: Internet, Permission Set: Internet Condition: URL: www. monash. edu. au, Permission Set: Monash. PSet Condition: Strong Name: m-Commerce, Permission Set: m-Commerce. PSet
Permission Sets • • Full. Trust: Allows unrestricted access to system resources. Skip. Verification: Allows an assembly to skip verification. Execution: Allows code to execute. Nothing: No permissions. Not granting the permission to execute effectively stops code from running • Internet: Appropriate for code coming from the Internet. (Limited) Code will not receive access to the file system or registry, but can do limited user interface actions as well as use the safe file system called Isolated Storage. Predefined Psets - can be accessed within code.
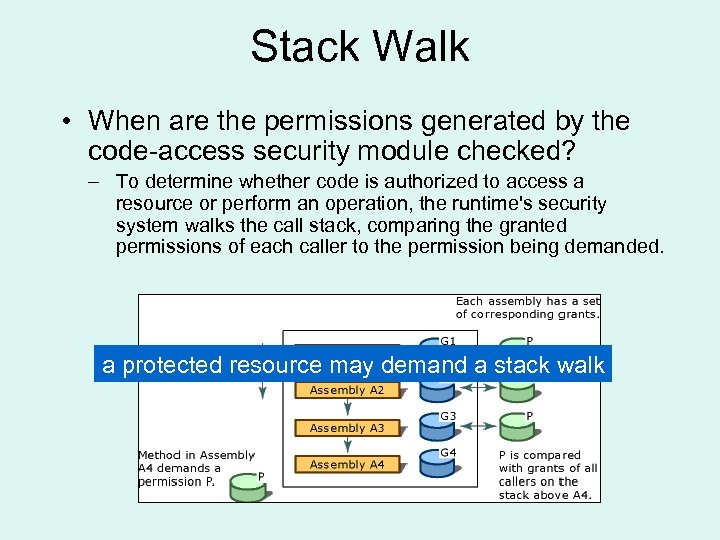
Stack Walk • When are the permissions generated by the code-access security module checked? – To determine whether code is authorized to access a resource or perform an operation, the runtime's security system walks the call stack, comparing the granted permissions of each caller to the permission being demanded. a protected resource may demand a stack walk
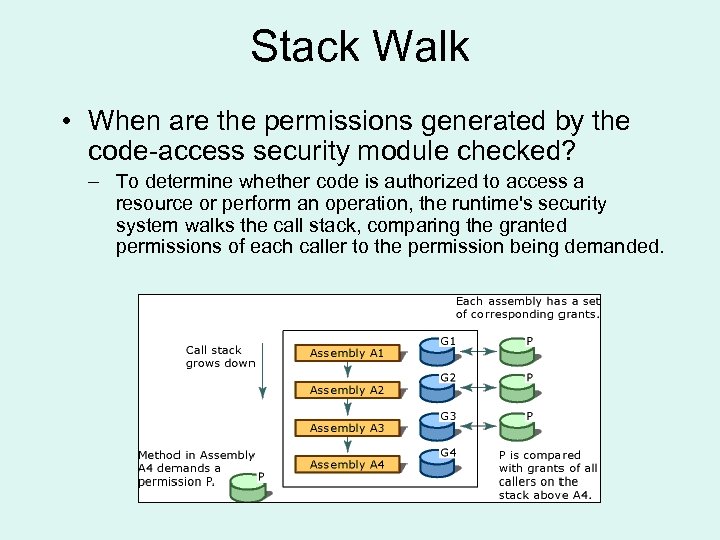
Stack Walk • When are the permissions generated by the code-access security module checked? – To determine whether code is authorized to access a resource or perform an operation, the runtime's security system walks the call stack, comparing the granted permissions of each caller to the permission being demanded.
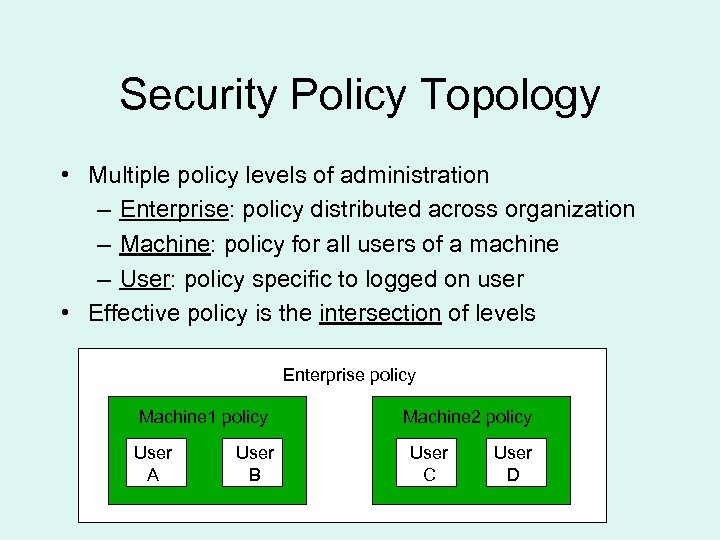
Security Policy Topology • Multiple policy levels of administration – Enterprise: policy distributed across organization – Machine: policy for all users of a machine – User: policy specific to logged on user • Effective policy is the intersection of levels Enterprise policy Machine 1 policy User A User B Machine 2 policy User C User D
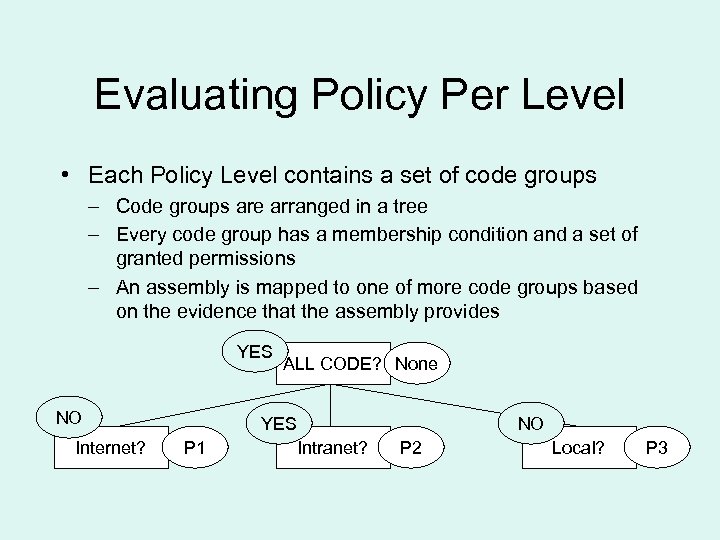
Evaluating Policy Per Level • Each Policy Level contains a set of code groups – Code groups are arranged in a tree – Every code group has a membership condition and a set of granted permissions – An assembly is mapped to one of more code groups based on the evidence that the assembly provides YES NO Internet? ALL CODE? None YES P 1 NO Intranet? P 2 Local? P 3
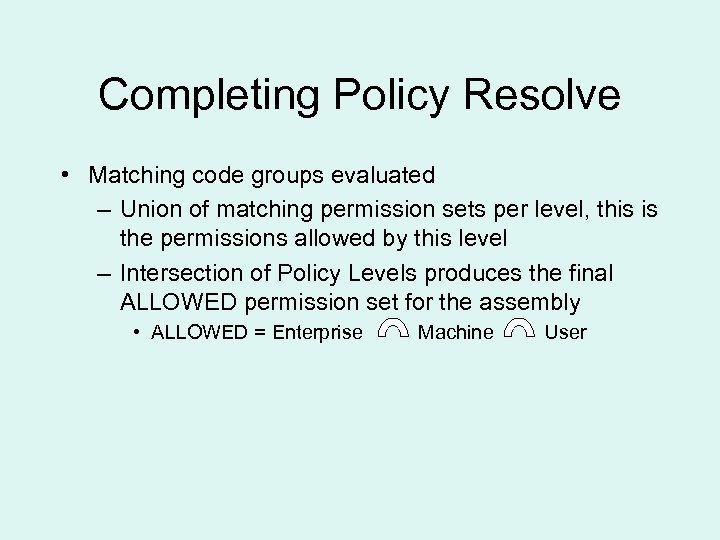
Completing Policy Resolve • Matching code groups evaluated – Union of matching permission sets per level, this is the permissions allowed by this level – Intersection of Policy Levels produces the final ALLOWED permission set for the assembly • ALLOWED = Enterprise Machine User
Policy Tools • caspol. exe • Console Management snap-in –. NET Framework 2. 0 Configuration
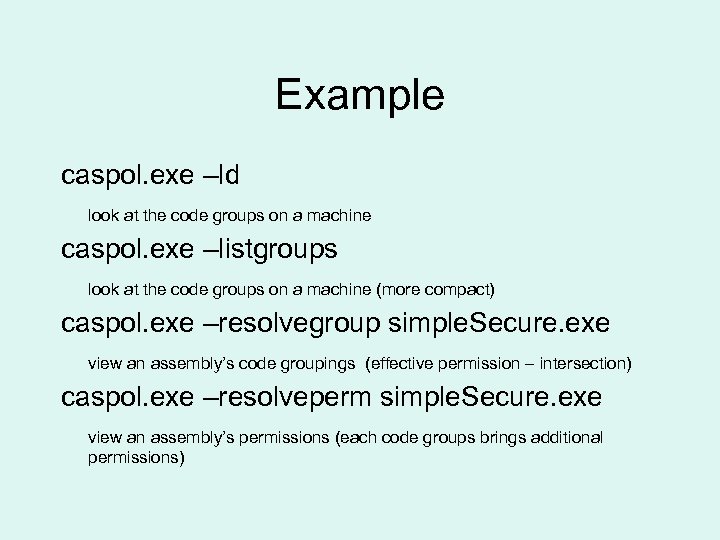
Example caspol. exe –ld look at the code groups on a machine caspol. exe –listgroups look at the code groups on a machine (more compact) caspol. exe –resolvegroup simple. Secure. exe view an assembly’s code groupings (effective permission – intersection) caspol. exe –resolveperm simple. Secure. exe view an assembly’s permissions (each code groups brings additional permissions)
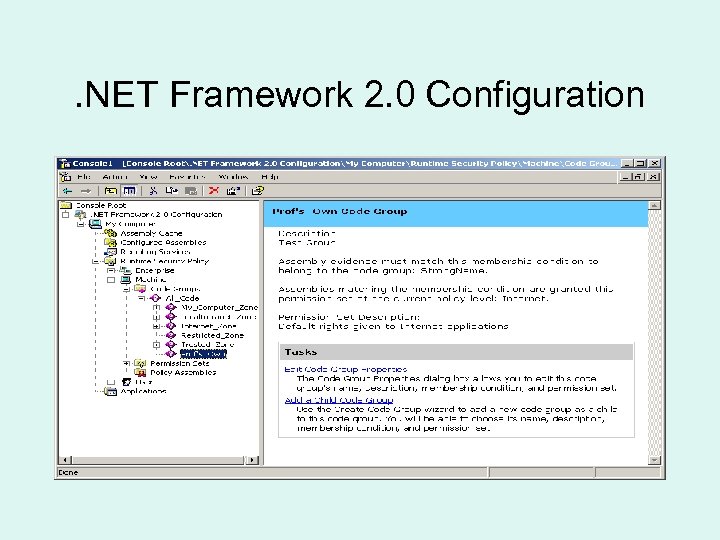
. NET Framework 2. 0 Configuration
Detail Information “Building a bigger sandbox” http: //www. javaworld. com/javaworld/jw-08 -1998/jw-08 -sandbox-p 2. html “Security in the. NET Framework” http: //msdn 2. microsoft. com/en-us/library/fkytk 30 f(vs. 80). aspx “Java vs. . NET Security” http: //www. onjava. com/pub/a/onjava/2003/11/26/javavsdotnet. html
fed7aacd3a872ff9ce9b5091167c0fe6.ppt