25a377ac9c6abe8ff75a3c7748cbbac6.ppt
- Количество слайдов: 16
Cloud Security Research Based On The Internet of Things Group 4 FAN Junzhou 1155098542 LIN Jiao 1155101259
PART 01 The relationship between cloud computing and the Internet of Things PART 02 Security issues for the Internet of Things PART 03 Solution to cloud security problem in the Io. T ------Alibaba cloud PART 04 Perspective -----Deep learning Catalog
01 The relationship between cloud computing and the Io. T
The relationship between cloud and the Io. T Cloud is the control center like the brain. The Io. T generates behaviors The benefits of applying the cloud flexible computing services improve the reliability of information processing

02 Security issues for the Internet of Things
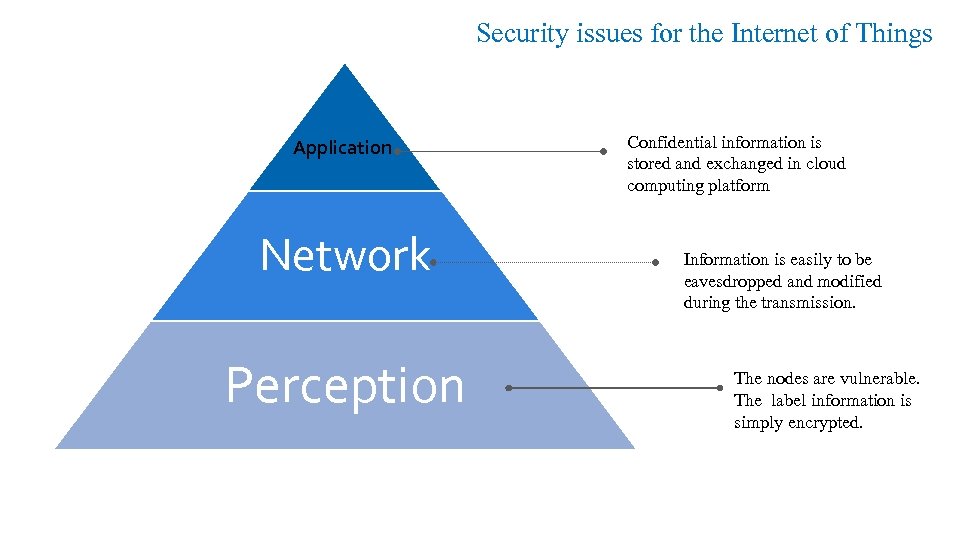
Security issues for the Internet of Things Application Network Perception Confidential information is stored and exchanged in cloud computing platform Information is easily to be eavesdropped and modified during the transmission. The nodes are vulnerable. The label information is simply encrypted.
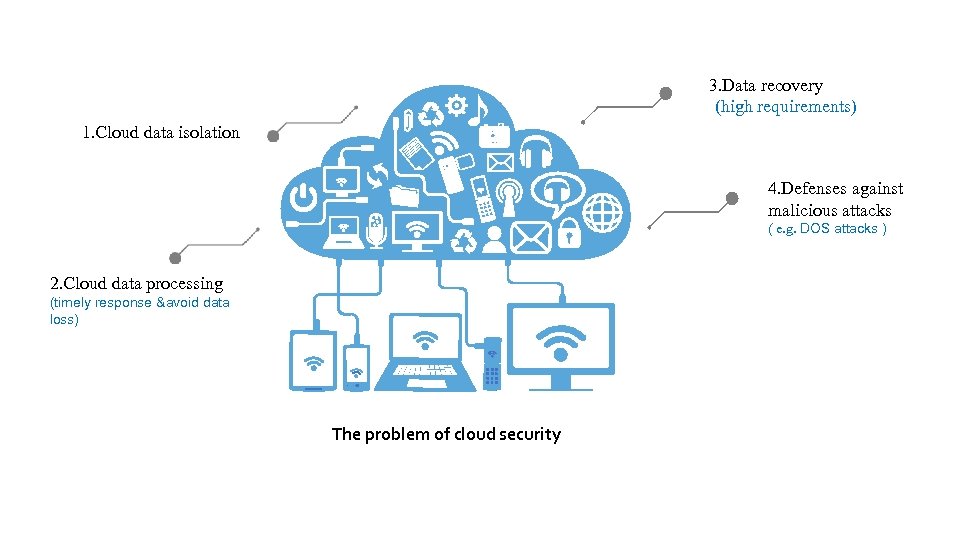
3. Data recovery (high requirements) 1. Cloud data isolation 4. Defenses against malicious attacks ( e. g. DOS attacks ) 2. Cloud data processing (timely response &avoid data loss) The problem of cloud security

03 Solution to cloud security problem in the Io. T ------Alibaba cloud
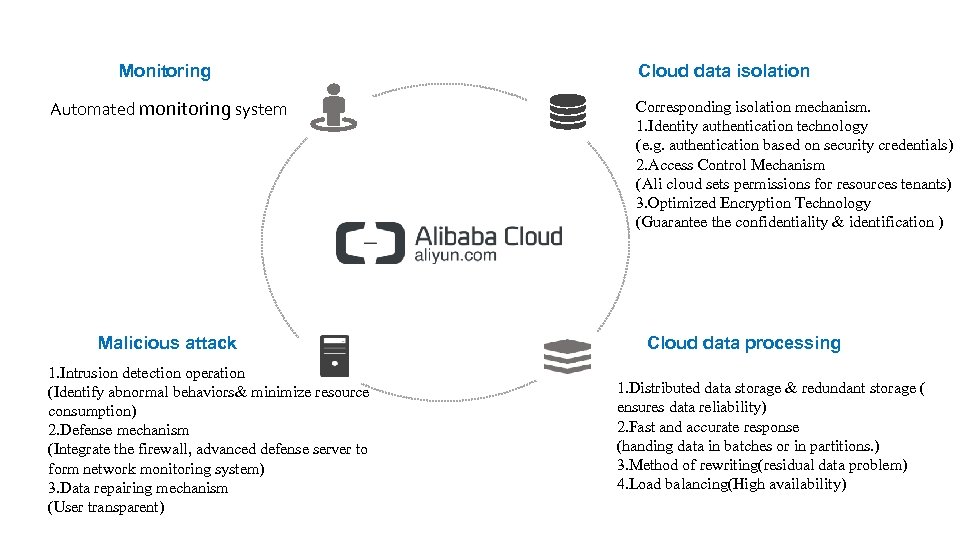
Monitoring Automated monitoring system Malicious attack 1. Intrusion detection operation (Identify abnormal behaviors& minimize resource consumption) 2. Defense mechanism (Integrate the firewall, advanced defense server to form network monitoring system) 3. Data repairing mechanism (User transparent) Cloud data isolation Corresponding isolation mechanism. 1. Identity authentication technology (e. g. authentication based on security credentials) 2. Access Control Mechanism (Ali cloud sets permissions for resources tenants) 3. Optimized Encryption Technology (Guarantee the confidentiality & identification ) Cloud data processing 1. Distributed data storage & redundant storage ( ensures data reliability) 2. Fast and accurate response (handing data in batches or in partitions. ) 3. Method of rewriting(residual data problem) 4. Load balancing(High availability)
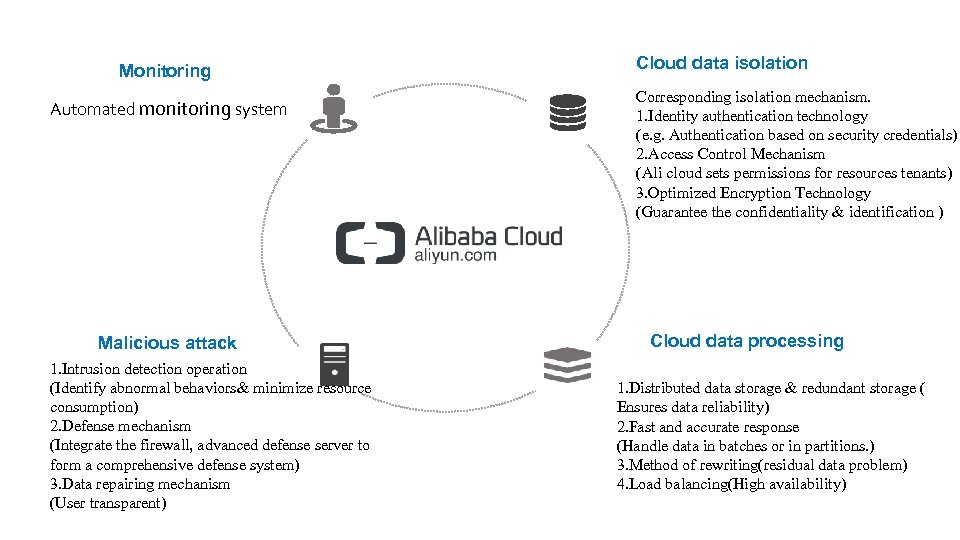
Monitoring Automated monitoring system Malicious attack 1. Intrusion detection operation (Identify abnormal behaviors& minimize resource consumption) 2. Defense mechanism (Integrate the firewall, advanced defense server to form a comprehensive defense system) 3. Data repairing mechanism (User transparent) Cloud data isolation Corresponding isolation mechanism. 1. Identity authentication technology (e. g. Authentication based on security credentials) 2. Access Control Mechanism (Ali cloud sets permissions for resources tenants) 3. Optimized Encryption Technology (Guarantee the confidentiality & identification ) Cloud data processing 1. Distributed data storage & redundant storage ( Ensures data reliability) 2. Fast and accurate response (Handle data in batches or in partitions. ) 3. Method of rewriting(residual data problem) 4. Load balancing(High availability)

04 Perspective -----Deep learning
In May 2017, the ransomware swept the world, which had caused enormous losses. The ransomware occupies terminal equipment in the Io. T and affects the normal operation, so the loss is even more serious. 01 02 03 More proactive defense mechanisms are needed. (Deep learning algorithm)
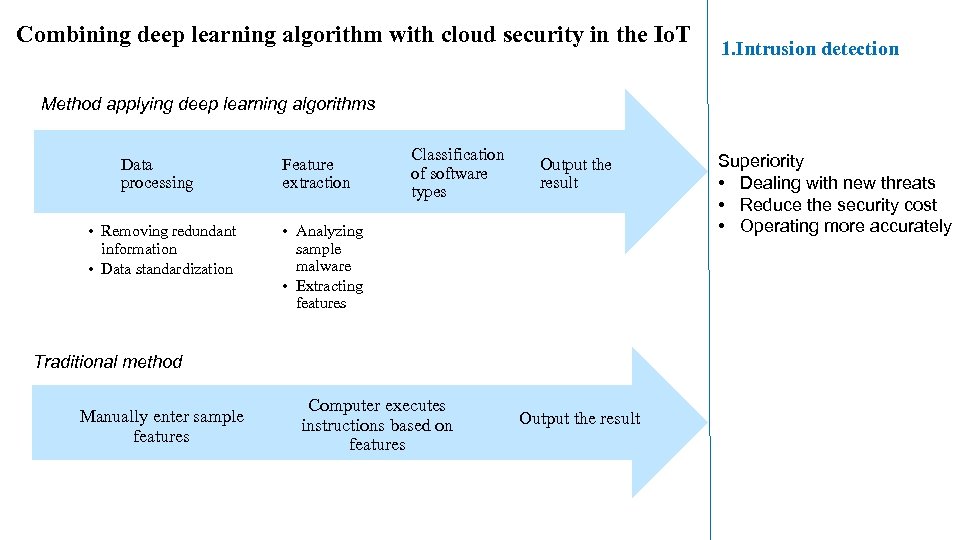
Combining deep learning algorithm with cloud security in the Io. T 1. Intrusion detection Method applying deep learning algorithms Data processing • Removing redundant information • Data standardization Feature extraction Classification of software types Output the result • Analyzing sample malware • Extracting features Traditional method Manually enter sample features Computer executes instructions based on features Output the result Superiority • Dealing with new threats • Reduce the security cost • Operating more accurately
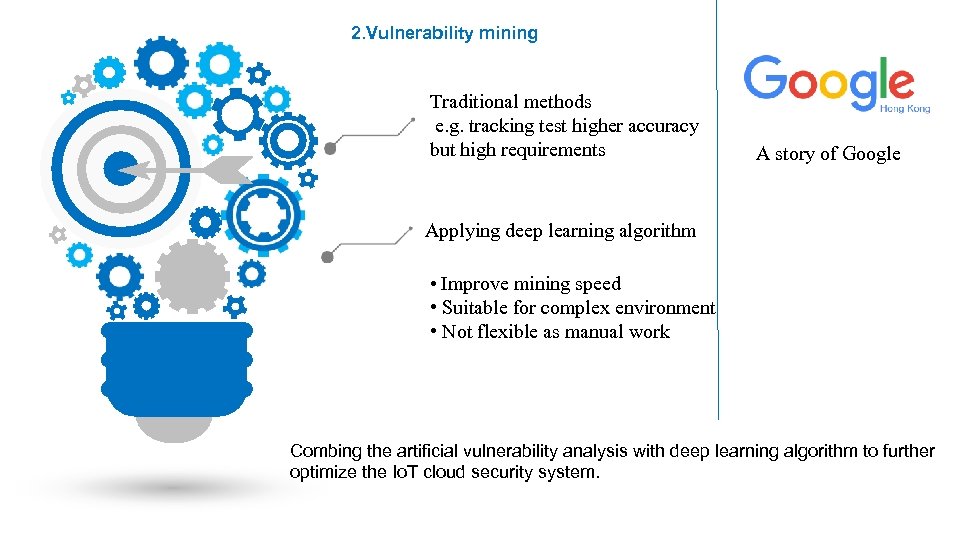
2. Vulnerability mining Traditional methods e. g. tracking test higher accuracy but high requirements A story of Google Applying deep learning algorithm • Improve mining speed • Suitable for complex environment • Not flexible as manual work Combing the artificial vulnerability analysis with deep learning algorithm to further optimize the Io. T cloud security system.
![Reference [1] Help. aliyun. com. (2017)阿里云数据安全白皮书_信任中心-阿里云. [online] Available at: https: //help. aliyun. com/knowledge_detail/42566. html Reference [1] Help. aliyun. com. (2017)阿里云数据安全白皮书_信任中心-阿里云. [online] Available at: https: //help. aliyun. com/knowledge_detail/42566. html](https://present5.com/presentation/25a377ac9c6abe8ff75a3c7748cbbac6/image-15.jpg)
Reference [1] Help. aliyun. com. (2017)阿里云数据安全白皮书_信任中心-阿里云. [online] Available at: https: //help. aliyun. com/knowledge_detail/42566. html [Accessed 1 Nov. 2017] [2]Security and Privacy for Cloud-Based Io. T: Challenges Zhou, Jun ; Cao, Zhenfu ; Dong, Xiaolei ; Vasilakos, Athanasios V. IEEE Communications Magazine, January 2017, Vol. 55(1), pp. 26 -33[Peer Reviewed Journal] [3] Cloud security issues and challenges: A survey Singh, Ashish ; Chatterjee, Kakali Journal of Network and Computer Applications, 1 February 2017, Vol. 79, pp. 88 -115[Peer Reviewed Journal] [4]En. wikipedia. org. (2017). Cloud computing. [online] Available at: https: //en. wikipedia. org/wiki/Cloud_computing [Accessed 13 Nov. 2017]. [5]Jiang, Z. and Liu, B. (2012). The Security Threats and Risk Analysis of Cloud Computing. Ph. D. Graduate of University. [6]Yang, J. , Wang, H. , Wang, J. and Yu, D. (2012). Survey on some Security Issues of Cloud Computing. Journal of Chinese Computer System, 33(3), p. 8

Thank you!
25a377ac9c6abe8ff75a3c7748cbbac6.ppt