5c1244e8aa7766f165190da7c6aa9e1a.ppt
- Количество слайдов: 40
 Citrix Extranet 2. 0 Product Overview
Citrix Extranet 2. 0 Product Overview
 Agenda What is Citrix Extranet 2. 0? n Architecture n System Requirements Citrix Extranet Features n Access Control n Identification & Authentication n Encryption n On-line Registration n Citrix Extranet Admin n Event Logging Citrix Extranet Advantages Commonly Used Terms
Agenda What is Citrix Extranet 2. 0? n Architecture n System Requirements Citrix Extranet Features n Access Control n Identification & Authentication n Encryption n On-line Registration n Citrix Extranet Admin n Event Logging Citrix Extranet Advantages Commonly Used Terms
 What Is Citrix Extranet 2. 0? Citrix Extranet provides a virtual private network (VPN) which allows you to securely deploy the latest businesscritical applications to users around the world, via the Internet – all while maintaining the manageability, scalability, reliability and control you’ve grown to expect from Citrix.
What Is Citrix Extranet 2. 0? Citrix Extranet provides a virtual private network (VPN) which allows you to securely deploy the latest businesscritical applications to users around the world, via the Internet – all while maintaining the manageability, scalability, reliability and control you’ve grown to expect from Citrix.
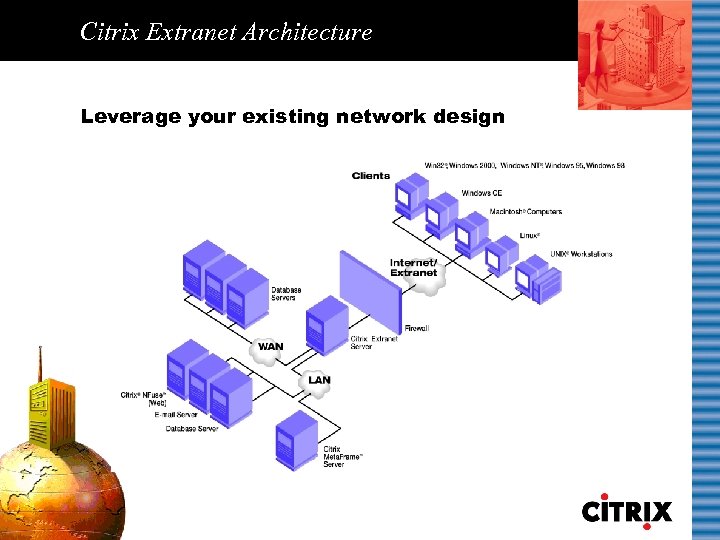 Citrix Extranet Architecture Leverage your existing network design
Citrix Extranet Architecture Leverage your existing network design
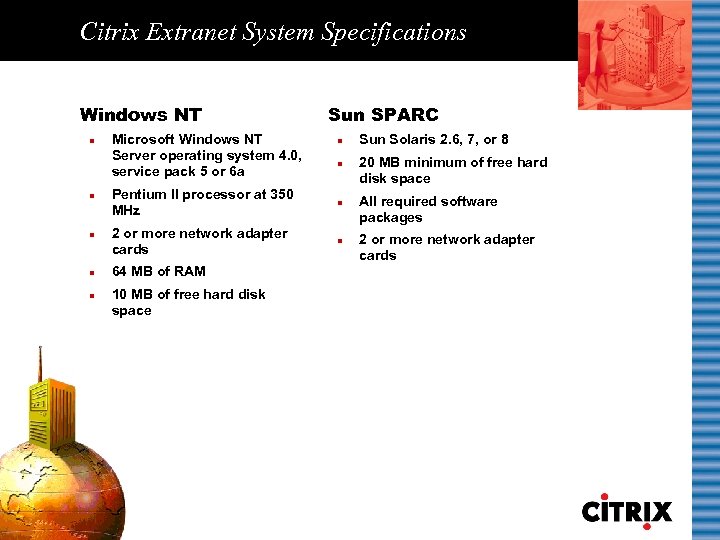 Citrix Extranet System Specifications Windows NT n n n Microsoft Windows NT Server operating system 4. 0, service pack 5 or 6 a Sun SPARC n n Pentium II processor at 350 MHz n 2 or more network adapter cards n 64 MB of RAM 10 MB of free hard disk space Sun Solaris 2. 6, 7, or 8 20 MB minimum of free hard disk space All required software packages 2 or more network adapter cards
Citrix Extranet System Specifications Windows NT n n n Microsoft Windows NT Server operating system 4. 0, service pack 5 or 6 a Sun SPARC n n Pentium II processor at 350 MHz n 2 or more network adapter cards n 64 MB of RAM 10 MB of free hard disk space Sun Solaris 2. 6, 7, or 8 20 MB minimum of free hard disk space All required software packages 2 or more network adapter cards
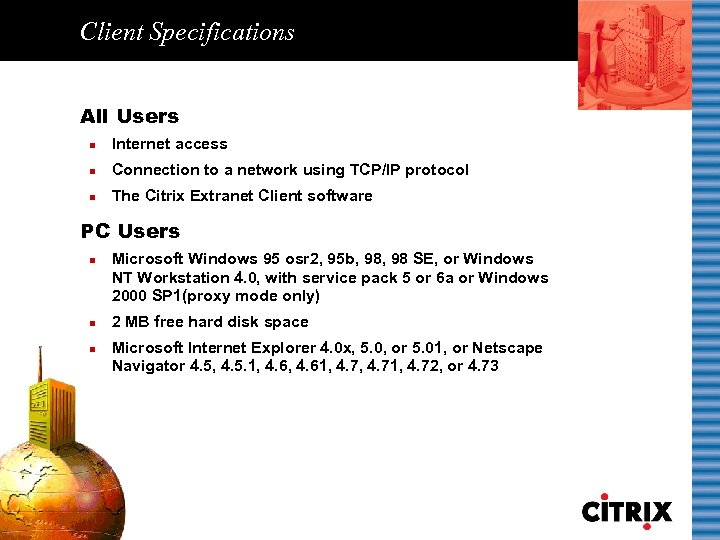 Client Specifications All Users n Internet access n Connection to a network using TCP/IP protocol n The Citrix Extranet Client software PC Users n n n Microsoft Windows 95 osr 2, 95 b, 98 SE, or Windows NT Workstation 4. 0, with service pack 5 or 6 a or Windows 2000 SP 1(proxy mode only) 2 MB free hard disk space Microsoft Internet Explorer 4. 0 x, 5. 0, or 5. 01, or Netscape Navigator 4. 5, 4. 5. 1, 4. 61, 4. 71, 4. 72, or 4. 73
Client Specifications All Users n Internet access n Connection to a network using TCP/IP protocol n The Citrix Extranet Client software PC Users n n n Microsoft Windows 95 osr 2, 95 b, 98 SE, or Windows NT Workstation 4. 0, with service pack 5 or 6 a or Windows 2000 SP 1(proxy mode only) 2 MB free hard disk space Microsoft Internet Explorer 4. 0 x, 5. 0, or 5. 01, or Netscape Navigator 4. 5, 4. 5. 1, 4. 61, 4. 71, 4. 72, or 4. 73
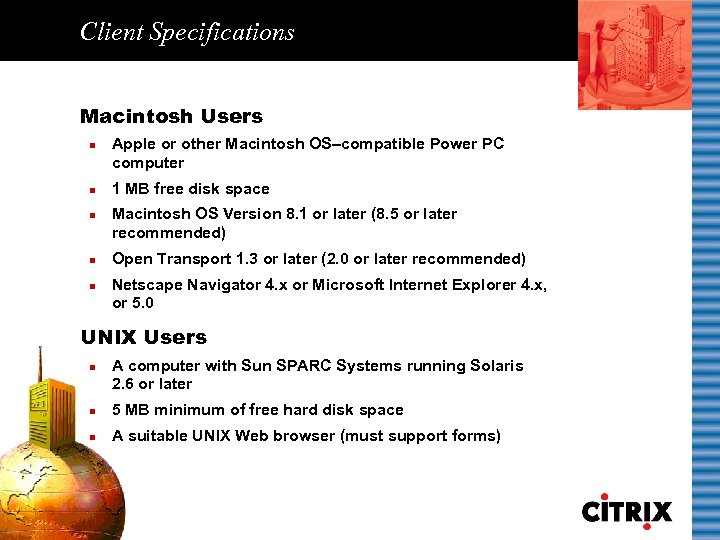 Client Specifications Macintosh Users n n n Apple or other Macintosh OS–compatible Power PC computer 1 MB free disk space Macintosh OS Version 8. 1 or later (8. 5 or later recommended) Open Transport 1. 3 or later (2. 0 or later recommended) Netscape Navigator 4. x or Microsoft Internet Explorer 4. x, or 5. 0 UNIX Users n A computer with Sun SPARC Systems running Solaris 2. 6 or later n 5 MB minimum of free hard disk space n A suitable UNIX Web browser (must support forms)
Client Specifications Macintosh Users n n n Apple or other Macintosh OS–compatible Power PC computer 1 MB free disk space Macintosh OS Version 8. 1 or later (8. 5 or later recommended) Open Transport 1. 3 or later (2. 0 or later recommended) Netscape Navigator 4. x or Microsoft Internet Explorer 4. x, or 5. 0 UNIX Users n A computer with Sun SPARC Systems running Solaris 2. 6 or later n 5 MB minimum of free hard disk space n A suitable UNIX Web browser (must support forms)
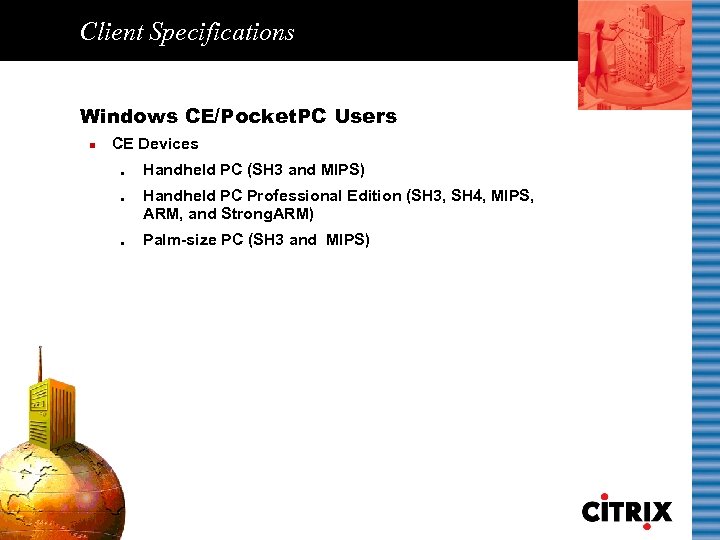 Client Specifications Windows CE/Pocket. PC Users n CE Devices l l l Handheld PC (SH 3 and MIPS) Handheld PC Professional Edition (SH 3, SH 4, MIPS, ARM, and Strong. ARM) Palm-size PC (SH 3 and MIPS)
Client Specifications Windows CE/Pocket. PC Users n CE Devices l l l Handheld PC (SH 3 and MIPS) Handheld PC Professional Edition (SH 3, SH 4, MIPS, ARM, and Strong. ARM) Palm-size PC (SH 3 and MIPS)
 Citrix Extranet 2. 0 Features
Citrix Extranet 2. 0 Features
 Citrix Extranet Features Access Control Identification and Authentication Event Logging Encryption Citrix Extranet Admin On-Line Registration (OLR)
Citrix Extranet Features Access Control Identification and Authentication Event Logging Encryption Citrix Extranet Admin On-Line Registration (OLR)
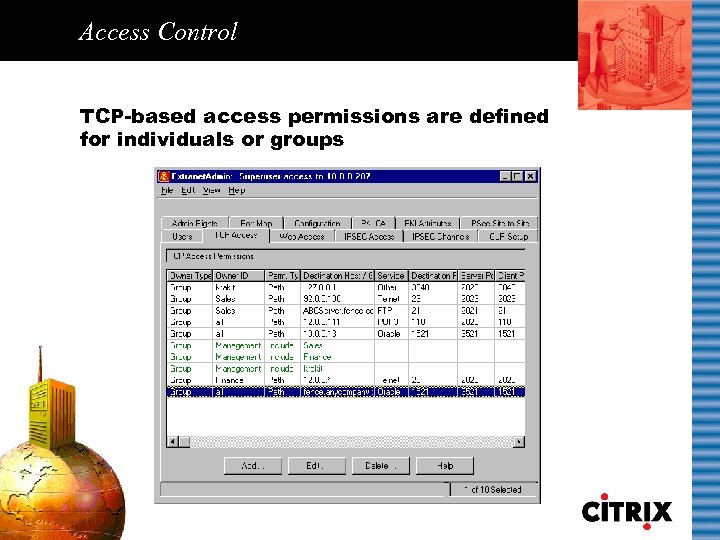 Access Control TCP-based access permissions are defined for individuals or groups
Access Control TCP-based access permissions are defined for individuals or groups
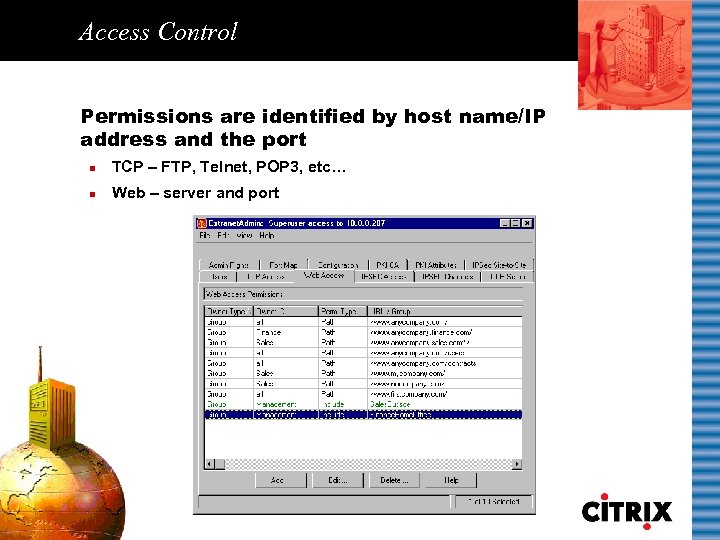 Access Control Permissions are identified by host name/IP address and the port n TCP – FTP, Telnet, POP 3, etc… n Web – server and port
Access Control Permissions are identified by host name/IP address and the port n TCP – FTP, Telnet, POP 3, etc… n Web – server and port
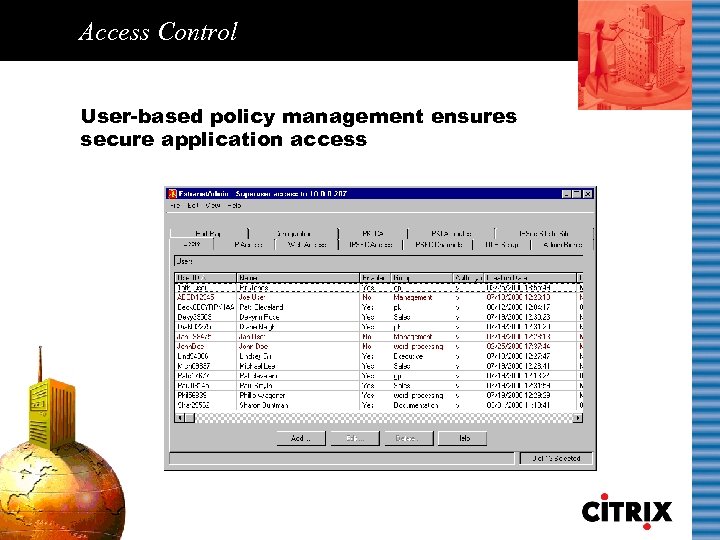 Access Control User-based policy management ensures secure application access
Access Control User-based policy management ensures secure application access
 Access Control Access permissions are received: n At the time the Citrix Extranet Client initiates n At regular user-defined intervals Permission sources: n Users’ group n “All” users *Assigning permissions to groups avoids unnecessary duplication and is more efficient than assigning permissions to individual users.
Access Control Access permissions are received: n At the time the Citrix Extranet Client initiates n At regular user-defined intervals Permission sources: n Users’ group n “All” users *Assigning permissions to groups avoids unnecessary duplication and is more efficient than assigning permissions to individual users.
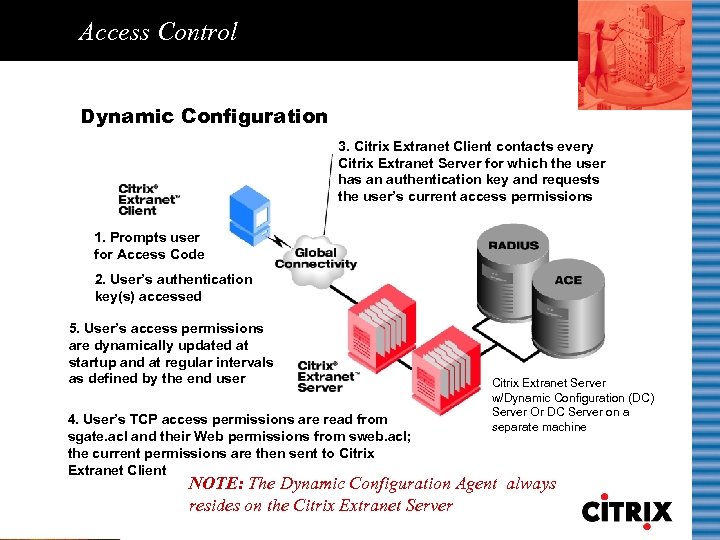 Access Control Dynamic Configuration 3. Citrix Extranet Client contacts every Citrix Extranet Server for which the user has an authentication key and requests the user’s current access permissions 1. Prompts user for Access Code 2. User’s authentication key(s) accessed 5. User’s access permissions are dynamically updated at startup and at regular intervals as defined by the end user 4. User’s TCP access permissions are read from sgate. acl and their Web permissions from sweb. acl; the current permissions are then sent to Citrix Extranet Client Citrix Extranet Server w/Dynamic Configuration (DC) Server Or DC Server on a separate machine NOTE: The Dynamic Configuration Agent always resides on the Citrix Extranet Server
Access Control Dynamic Configuration 3. Citrix Extranet Client contacts every Citrix Extranet Server for which the user has an authentication key and requests the user’s current access permissions 1. Prompts user for Access Code 2. User’s authentication key(s) accessed 5. User’s access permissions are dynamically updated at startup and at regular intervals as defined by the end user 4. User’s TCP access permissions are read from sgate. acl and their Web permissions from sweb. acl; the current permissions are then sent to Citrix Extranet Client Citrix Extranet Server w/Dynamic Configuration (DC) Server Or DC Server on a separate machine NOTE: The Dynamic Configuration Agent always resides on the Citrix Extranet Server
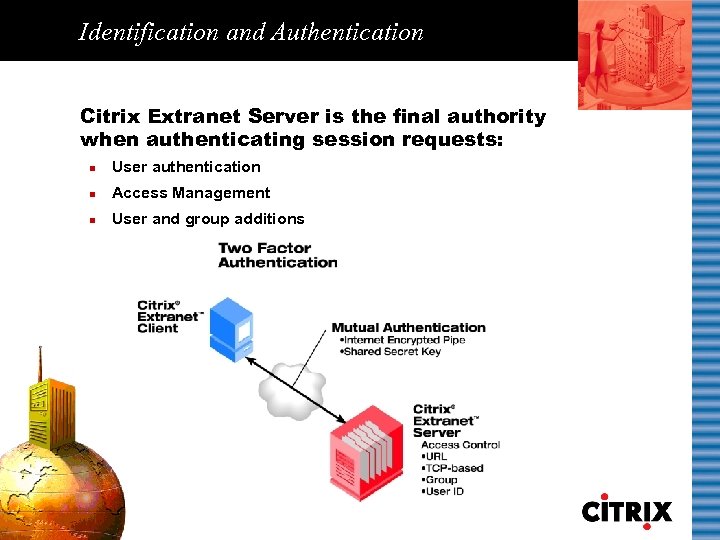 Identification and Authentication Citrix Extranet Server is the final authority when authenticating session requests: n User authentication n Access Management n User and group additions
Identification and Authentication Citrix Extranet Server is the final authority when authenticating session requests: n User authentication n Access Management n User and group additions
 Identification and Authentication Key exchange methods are flexible for the Administrator Tokens n FIPS token (FIPS 140 -1 compliant) Physical Smart Cards n MCOS n VCAT token n MCOS-B n RADIUS n STARCOS 2. 1 n Secur. ID n Entrust/Netrust Smart Card Readers PCAT n Smarty n CHIPDRIVE external PKI (X. 509) Certificates n n n Baltimore Entrust Microsoft Netscape Veri. Sign
Identification and Authentication Key exchange methods are flexible for the Administrator Tokens n FIPS token (FIPS 140 -1 compliant) Physical Smart Cards n MCOS n VCAT token n MCOS-B n RADIUS n STARCOS 2. 1 n Secur. ID n Entrust/Netrust Smart Card Readers PCAT n Smarty n CHIPDRIVE external PKI (X. 509) Certificates n n n Baltimore Entrust Microsoft Netscape Veri. Sign
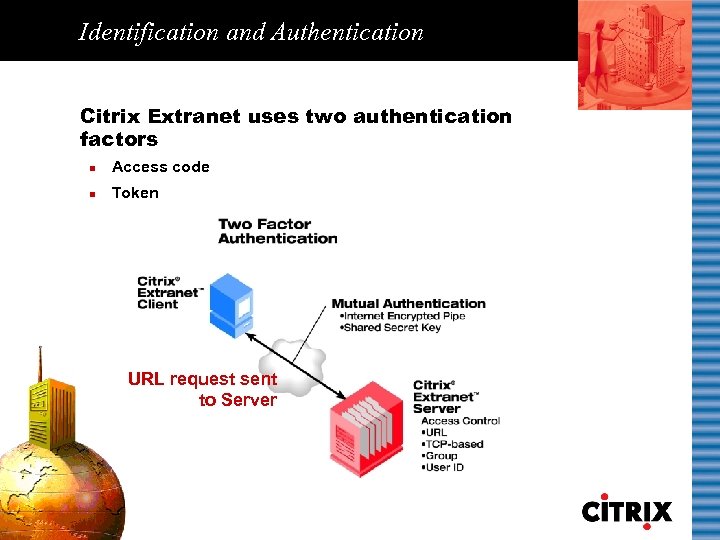 Identification and Authentication Citrix Extranet uses two authentication factors n Access code n Token URL request sent to Server
Identification and Authentication Citrix Extranet uses two authentication factors n Access code n Token URL request sent to Server
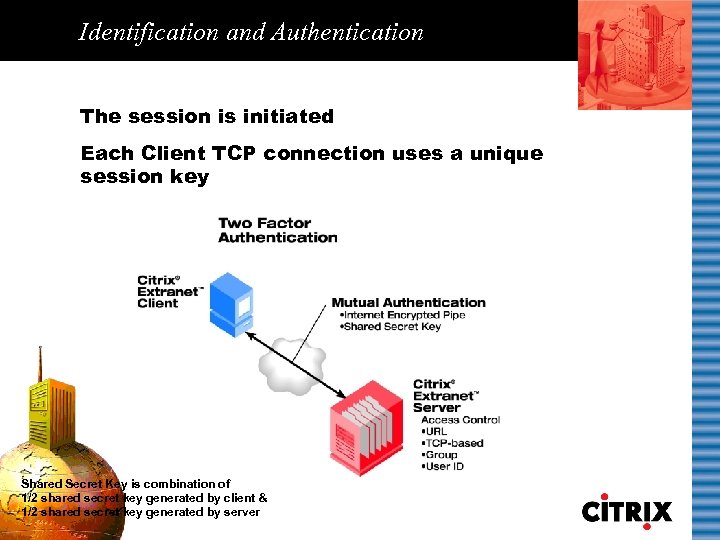 Identification and Authentication The session is initiated Each Client TCP connection uses a unique session key Shared Secret Key is combination of 1/2 shared secret key generated by client & 1/2 shared secret key generated by server
Identification and Authentication The session is initiated Each Client TCP connection uses a unique session key Shared Secret Key is combination of 1/2 shared secret key generated by client & 1/2 shared secret key generated by server
 Encryption The ticket contents are encrypted n Initialization Vector (IVEC) n User ID n Ticket time/TTL n Encryption algorithm n Session key n Destination n MD 5
Encryption The ticket contents are encrypted n Initialization Vector (IVEC) n User ID n Ticket time/TTL n Encryption algorithm n Session key n Destination n MD 5
 On-line Registration (OLR) Automated registration of the Citrix Extranet Client is via the Internet n n n User registers IDs automatically generated Flexible UID server assignments
On-line Registration (OLR) Automated registration of the Citrix Extranet Client is via the Internet n n n User registers IDs automatically generated Flexible UID server assignments
 On-line Registration (OLR) Seamless registration process Shared Secret Key is combination of 1/2 shared secret key generated by client & 1/2 shared secret key generated by server
On-line Registration (OLR) Seamless registration process Shared Secret Key is combination of 1/2 shared secret key generated by client & 1/2 shared secret key generated by server
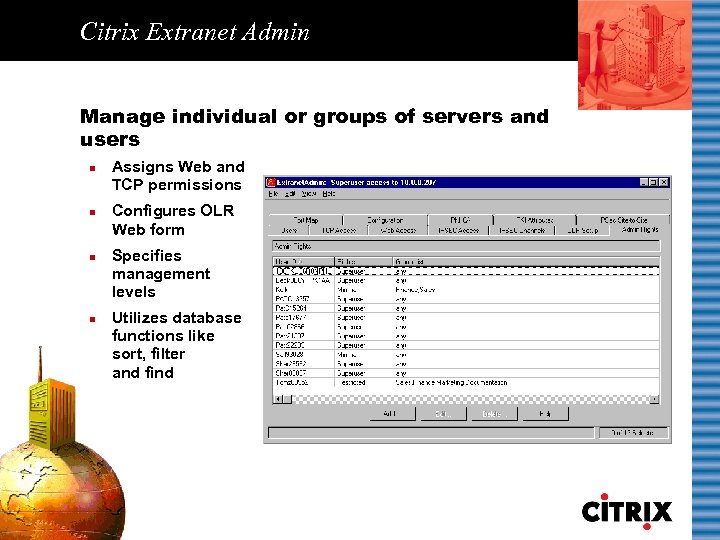 Citrix Extranet Admin Manage individual or groups of servers and users n n Assigns Web and TCP permissions Configures OLR Web form Specifies management levels Utilizes database functions like sort, filter and find
Citrix Extranet Admin Manage individual or groups of servers and users n n Assigns Web and TCP permissions Configures OLR Web form Specifies management levels Utilizes database functions like sort, filter and find
 Event Logging Allows for easy troubleshooting by logging critical information n Session start/end n User added/deleted n User enabled/disabled n User key changed n Successful/ unsuccessful user login n Server up/down
Event Logging Allows for easy troubleshooting by logging critical information n Session start/end n User added/deleted n User enabled/disabled n User key changed n Successful/ unsuccessful user login n Server up/down
 Citrix Extranet 2. 0 Advantages
Citrix Extranet 2. 0 Advantages
 Citrix Extranet Advantages Flexible system integration Rapid deployment Centralized management Simplicity and ease of use Cost-effectiveness
Citrix Extranet Advantages Flexible system integration Rapid deployment Centralized management Simplicity and ease of use Cost-effectiveness
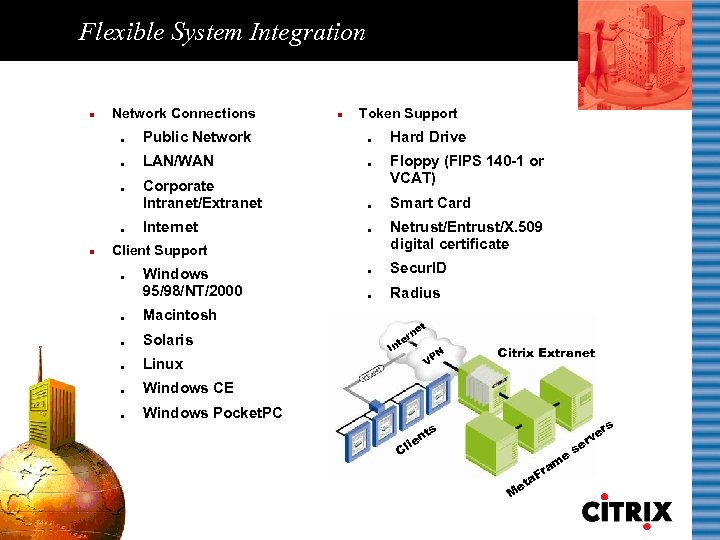 Flexible System Integration n Network Connections n Token Support l Public Network l l LAN/WAN l Corporate Intranet/Extranet l Internet l l l n Client Support l l Windows 95/98/NT/2000 Hard Drive Floppy (FIPS 140 -1 or VCAT) Smart Card Netrust/Entrust/X. 509 digital certificate l Secur. ID l Radius Macintosh l Solaris l Linux l Windows CE l t e rn te Windows Pocket. PC In VP N Citrix Extranet s nt lie C e a et M am Fr rs ve r se
Flexible System Integration n Network Connections n Token Support l Public Network l l LAN/WAN l Corporate Intranet/Extranet l Internet l l l n Client Support l l Windows 95/98/NT/2000 Hard Drive Floppy (FIPS 140 -1 or VCAT) Smart Card Netrust/Entrust/X. 509 digital certificate l Secur. ID l Radius Macintosh l Solaris l Linux l Windows CE l t e rn te Windows Pocket. PC In VP N Citrix Extranet s nt lie C e a et M am Fr rs ve r se
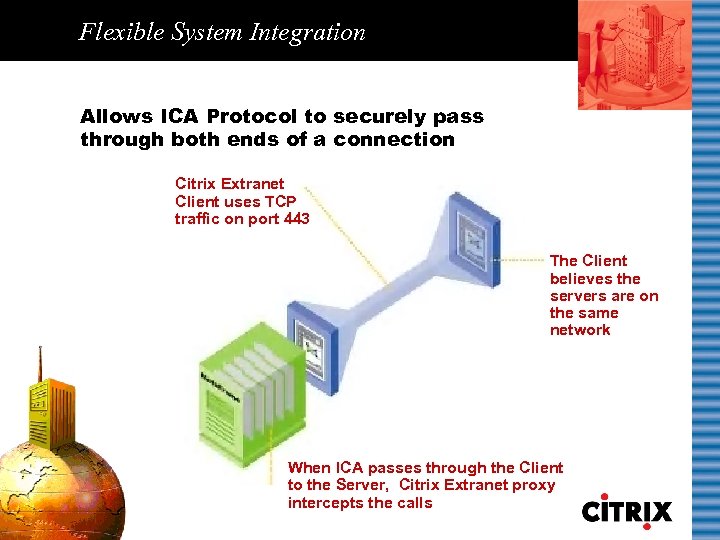 Flexible System Integration Allows ICA Protocol to securely pass through both ends of a connection Citrix Extranet Client uses TCP traffic on port 443 The Client believes the servers are on the same network When ICA passes through the Client to the Server, Citrix Extranet proxy intercepts the calls
Flexible System Integration Allows ICA Protocol to securely pass through both ends of a connection Citrix Extranet Client uses TCP traffic on port 443 The Client believes the servers are on the same network When ICA passes through the Client to the Server, Citrix Extranet proxy intercepts the calls
 Flexible System Integration Export ready for use at any available strength encryption n Triple DES (168 -bit) n RC 4 n DES (56 -bit) *Embargoed countries are Cuba, Libya, North Korea, Syria, Sudan, Iraq
Flexible System Integration Export ready for use at any available strength encryption n Triple DES (168 -bit) n RC 4 n DES (56 -bit) *Embargoed countries are Cuba, Libya, North Korea, Syria, Sudan, Iraq
 Rapid Deployment Easy deployment and token enrollment of large user bases via On-line Registration (OLR)
Rapid Deployment Easy deployment and token enrollment of large user bases via On-line Registration (OLR)
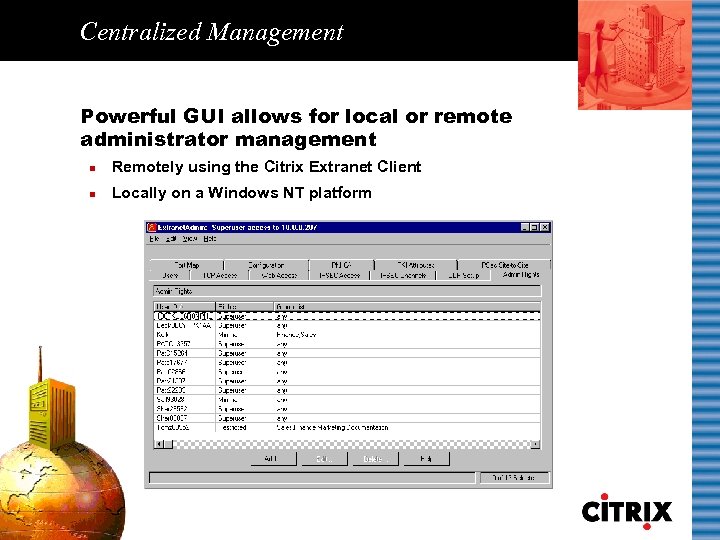 Centralized Management Powerful GUI allows for local or remote administrator management n Remotely using the Citrix Extranet Client n Locally on a Windows NT platform
Centralized Management Powerful GUI allows for local or remote administrator management n Remotely using the Citrix Extranet Client n Locally on a Windows NT platform
 Ease of Use Simple 2 -step client activation n Install Citrix Extranet client software n Register online 1 2
Ease of Use Simple 2 -step client activation n Install Citrix Extranet client software n Register online 1 2
 Cost-effectiveness Leverage existing systems No costly leased lines or modem banks Minimal client management and user support costs
Cost-effectiveness Leverage existing systems No costly leased lines or modem banks Minimal client management and user support costs
 Connect Business Securely Permit secure online information exchange via the Internet n Mobile users n Suppliers n Business partners n End-customers n Branch and international offices
Connect Business Securely Permit secure online information exchange via the Internet n Mobile users n Suppliers n Business partners n End-customers n Branch and international offices
 Citrix Extranet 2. 0 Powerful End-to-end security Centralized management
Citrix Extranet 2. 0 Powerful End-to-end security Centralized management
 Commonly Used Terms 3 DES: Cipher that applies the DES cipher three times with either two or three different DES keys. The Citrix Extranet implementation uses three DES keys (2168 combinations). Access Code: The secret code, similar to a PIN on an ATM card—required to unlock the authentication key stored on the user’s token each time the user accesses a secure service. This code, defined by the user during registration, must be at least four characters in length with a maximum of 16, and can be any combination of letters and numbers. Access Control: Allowing or denying connections through the use of access permissions. Access Permissions: The associations between users and connections, as defined by a User ID, group name, service (TCP or Web), or destination. Citrix Extranet access permissions can be either individual user permissions or group permissions. Authentication: The process of determining the identity of a user attempting to access a system.
Commonly Used Terms 3 DES: Cipher that applies the DES cipher three times with either two or three different DES keys. The Citrix Extranet implementation uses three DES keys (2168 combinations). Access Code: The secret code, similar to a PIN on an ATM card—required to unlock the authentication key stored on the user’s token each time the user accesses a secure service. This code, defined by the user during registration, must be at least four characters in length with a maximum of 16, and can be any combination of letters and numbers. Access Control: Allowing or denying connections through the use of access permissions. Access Permissions: The associations between users and connections, as defined by a User ID, group name, service (TCP or Web), or destination. Citrix Extranet access permissions can be either individual user permissions or group permissions. Authentication: The process of determining the identity of a user attempting to access a system.
 Commonly Used Terms Authentication Key: The key is a 32 -character hexadecimal key assigned to a user during installation by the registration server administrator, consisting of the numbers 0 to 9 and letters A to F. n n The Citrix Extranet authentication system supports virtual smart cards and ISO-standard smart cards for both authentication and stored data. A user with a physical smart card must use a smart card reader connected to their PC. Virtual smart card information (FIPS or VCAT token) may be stored on either the PC hard drive or a removable (floppy) disk. The user’s Citrix Extranet authentication key is stored on the smart card, whether physical or virtual. This information is shared with the Citrix Extranet Server, where it is stored in the Citrix Extranet Server’s user database. Authentication Token: A portable device used for authenticating a user. Authentication tokens operate by challenge/response, time-based code sequences, or other techniques.
Commonly Used Terms Authentication Key: The key is a 32 -character hexadecimal key assigned to a user during installation by the registration server administrator, consisting of the numbers 0 to 9 and letters A to F. n n The Citrix Extranet authentication system supports virtual smart cards and ISO-standard smart cards for both authentication and stored data. A user with a physical smart card must use a smart card reader connected to their PC. Virtual smart card information (FIPS or VCAT token) may be stored on either the PC hard drive or a removable (floppy) disk. The user’s Citrix Extranet authentication key is stored on the smart card, whether physical or virtual. This information is shared with the Citrix Extranet Server, where it is stored in the Citrix Extranet Server’s user database. Authentication Token: A portable device used for authenticating a user. Authentication tokens operate by challenge/response, time-based code sequences, or other techniques.
 Commonly Used Terms Authenticator: The name assigned to a Citrix Extranet Server through which users can access a particular service. This name can be up to 14 alphanumeric characters in length and it is recommended that it be a derivative of your Citrix Extranet Server hostname. Domain Name: Identifies a ‘location’ on the Internet (e. g. , citrix. com) that has been registered with the Internet Network Information Center (Inter. NIC). Currently the domain name is limited to 47 characters. Through the use of aliases, however, it is possible to accommodate longer names. DES: Data Encryption Standard is a NIST-standard encryption algorithm for secure data protection. A binary number is used as an encryption key with 720 quadrillion possible combinations (256). The key is randomly generated for each session (TCP connection). FIPS Token: (Virtual Smart Card or Soft Token) A software emulation of a hardware authentication token that is in compliance with the FIPS 140– 1 coding standards. It stores your private information (authentication key) in an single encrypted file, either on a floppy disk or on your hard drive. FIPS Token is the default authentication method.
Commonly Used Terms Authenticator: The name assigned to a Citrix Extranet Server through which users can access a particular service. This name can be up to 14 alphanumeric characters in length and it is recommended that it be a derivative of your Citrix Extranet Server hostname. Domain Name: Identifies a ‘location’ on the Internet (e. g. , citrix. com) that has been registered with the Internet Network Information Center (Inter. NIC). Currently the domain name is limited to 47 characters. Through the use of aliases, however, it is possible to accommodate longer names. DES: Data Encryption Standard is a NIST-standard encryption algorithm for secure data protection. A binary number is used as an encryption key with 720 quadrillion possible combinations (256). The key is randomly generated for each session (TCP connection). FIPS Token: (Virtual Smart Card or Soft Token) A software emulation of a hardware authentication token that is in compliance with the FIPS 140– 1 coding standards. It stores your private information (authentication key) in an single encrypted file, either on a floppy disk or on your hard drive. FIPS Token is the default authentication method.
 Commonly Used Terms OLR: Citrix Extranet provides On-Line Registration (OLR) services which you may wish to implement depending on your system configuration and the functional requirements of your organization. RC 4: Is a stream cipher developed by RSA Data Security, Inc. This variable key-size stream cipher uses byte-oriented operations to perform random permutations. The typical cipher period is greater than 10100. Since eight to sixteen machine operations are required per output byte, the cipher runs very quickly in software. It is commonly used for secure communications, such as encrypting secure web site traffic using the SSL protocol. VCAT Token: Identical to the FIPS Token, except that it stores your private information (authentication key) in an encrypted file system, rather than a single file. Virtual Private Network (VPN): A private network created over a public network (e. g. , the Internet) by using encryption, where exclusive client and host communications can occur.
Commonly Used Terms OLR: Citrix Extranet provides On-Line Registration (OLR) services which you may wish to implement depending on your system configuration and the functional requirements of your organization. RC 4: Is a stream cipher developed by RSA Data Security, Inc. This variable key-size stream cipher uses byte-oriented operations to perform random permutations. The typical cipher period is greater than 10100. Since eight to sixteen machine operations are required per output byte, the cipher runs very quickly in software. It is commonly used for secure communications, such as encrypting secure web site traffic using the SSL protocol. VCAT Token: Identical to the FIPS Token, except that it stores your private information (authentication key) in an encrypted file system, rather than a single file. Virtual Private Network (VPN): A private network created over a public network (e. g. , the Internet) by using encryption, where exclusive client and host communications can occur.



