aec3847d375328d8f67d54a7139323cc.ppt
- Количество слайдов: 35
 CIT 380: Securing Computer Systems Denial of Service CIT 380: Securing Computer Systems 1
CIT 380: Securing Computer Systems Denial of Service CIT 380: Securing Computer Systems 1
 Topics 1. 2. 3. 4. 5. 6. 7. Introduction History of Do. S Modes of Attack Technical Attacks Distributed DOS (DDOS) Botnets Defending against Do. S CIT 380: Securing Computer Systems 2
Topics 1. 2. 3. 4. 5. 6. 7. Introduction History of Do. S Modes of Attack Technical Attacks Distributed DOS (DDOS) Botnets Defending against Do. S CIT 380: Securing Computer Systems 2
 Denial of Service • Attacks against availability of services. • Common attacks: – CAIDA conservatively estimated 4000/week. – Attacks have increased since 2001 estimate. • Most Do. S vs. small site for short duration. • However, Do. S attacks can be very big – Millions of packets/second. – Many thousands of hosts involved. • Do. S attacks are very difficult to stop. CIT 380: Securing Computer Systems 3
Denial of Service • Attacks against availability of services. • Common attacks: – CAIDA conservatively estimated 4000/week. – Attacks have increased since 2001 estimate. • Most Do. S vs. small site for short duration. • However, Do. S attacks can be very big – Millions of packets/second. – Many thousands of hosts involved. • Do. S attacks are very difficult to stop. CIT 380: Securing Computer Systems 3
 Denial of Service Motives Attacker Competitions – Take over IRC channels. – Fame: take down a well-known target. – Revenge for being Do. Sed. Political – Take down computers of political opponents. Financial – Take down competitor web site. – Extortion: pay attacker or be Do. Sed. CIT 380: Securing Computer Systems 4
Denial of Service Motives Attacker Competitions – Take over IRC channels. – Fame: take down a well-known target. – Revenge for being Do. Sed. Political – Take down computers of political opponents. Financial – Take down competitor web site. – Extortion: pay attacker or be Do. Sed. CIT 380: Securing Computer Systems 4
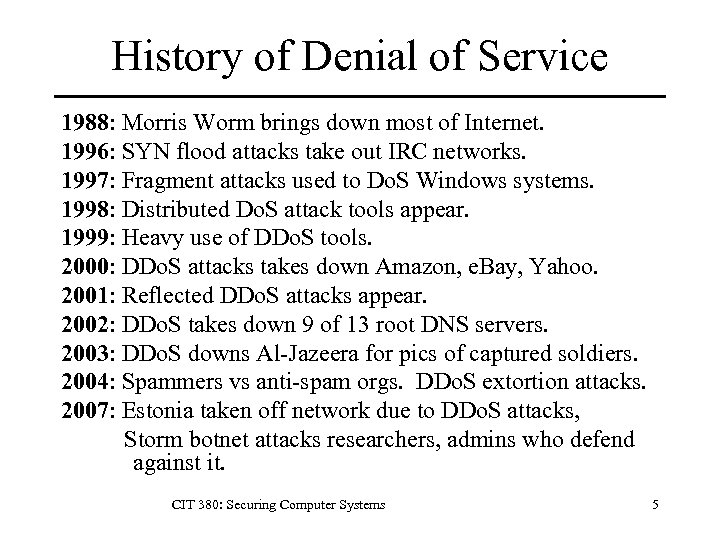 History of Denial of Service 1988: Morris Worm brings down most of Internet. 1996: SYN flood attacks take out IRC networks. 1997: Fragment attacks used to Do. S Windows systems. 1998: Distributed Do. S attack tools appear. 1999: Heavy use of DDo. S tools. 2000: DDo. S attacks takes down Amazon, e. Bay, Yahoo. 2001: Reflected DDo. S attacks appear. 2002: DDo. S takes down 9 of 13 root DNS servers. 2003: DDo. S downs Al-Jazeera for pics of captured soldiers. 2004: Spammers vs anti-spam orgs. DDo. S extortion attacks. 2007: Estonia taken off network due to DDo. S attacks, Storm botnet attacks researchers, admins who defend against it. CIT 380: Securing Computer Systems 5
History of Denial of Service 1988: Morris Worm brings down most of Internet. 1996: SYN flood attacks take out IRC networks. 1997: Fragment attacks used to Do. S Windows systems. 1998: Distributed Do. S attack tools appear. 1999: Heavy use of DDo. S tools. 2000: DDo. S attacks takes down Amazon, e. Bay, Yahoo. 2001: Reflected DDo. S attacks appear. 2002: DDo. S takes down 9 of 13 root DNS servers. 2003: DDo. S downs Al-Jazeera for pics of captured soldiers. 2004: Spammers vs anti-spam orgs. DDo. S extortion attacks. 2007: Estonia taken off network due to DDo. S attacks, Storm botnet attacks researchers, admins who defend against it. CIT 380: Securing Computer Systems 5
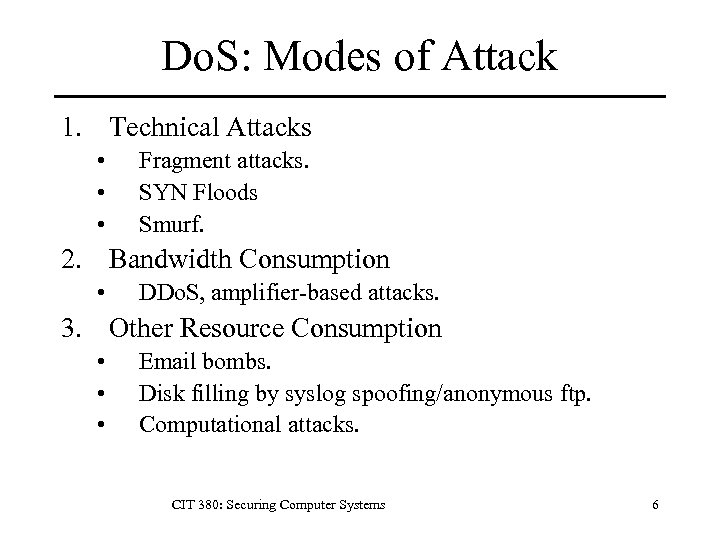 Do. S: Modes of Attack 1. Technical Attacks • • • Fragment attacks. SYN Floods Smurf. 2. Bandwidth Consumption • DDo. S, amplifier-based attacks. 3. Other Resource Consumption • • • Email bombs. Disk filling by syslog spoofing/anonymous ftp. Computational attacks. CIT 380: Securing Computer Systems 6
Do. S: Modes of Attack 1. Technical Attacks • • • Fragment attacks. SYN Floods Smurf. 2. Bandwidth Consumption • DDo. S, amplifier-based attacks. 3. Other Resource Consumption • • • Email bombs. Disk filling by syslog spoofing/anonymous ftp. Computational attacks. CIT 380: Securing Computer Systems 6
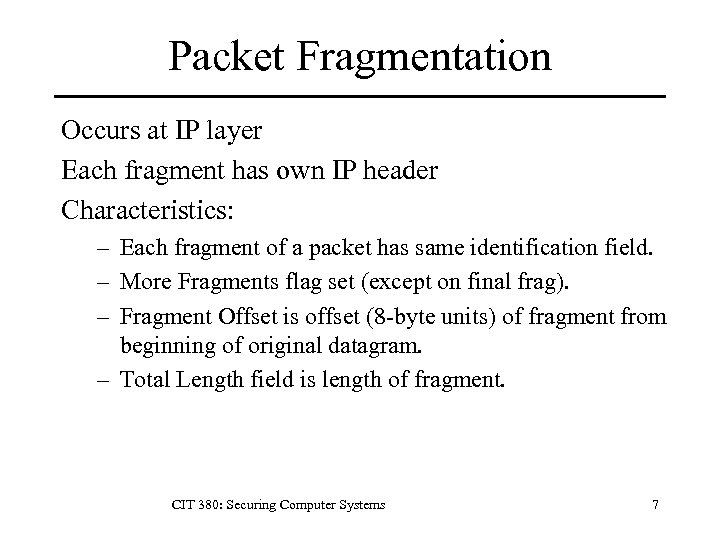 Packet Fragmentation Occurs at IP layer Each fragment has own IP header Characteristics: – Each fragment of a packet has same identification field. – More Fragments flag set (except on final frag). – Fragment Offset is offset (8 -byte units) of fragment from beginning of original datagram. – Total Length field is length of fragment. CIT 380: Securing Computer Systems 7
Packet Fragmentation Occurs at IP layer Each fragment has own IP header Characteristics: – Each fragment of a packet has same identification field. – More Fragments flag set (except on final frag). – Fragment Offset is offset (8 -byte units) of fragment from beginning of original datagram. – Total Length field is length of fragment. CIT 380: Securing Computer Systems 7
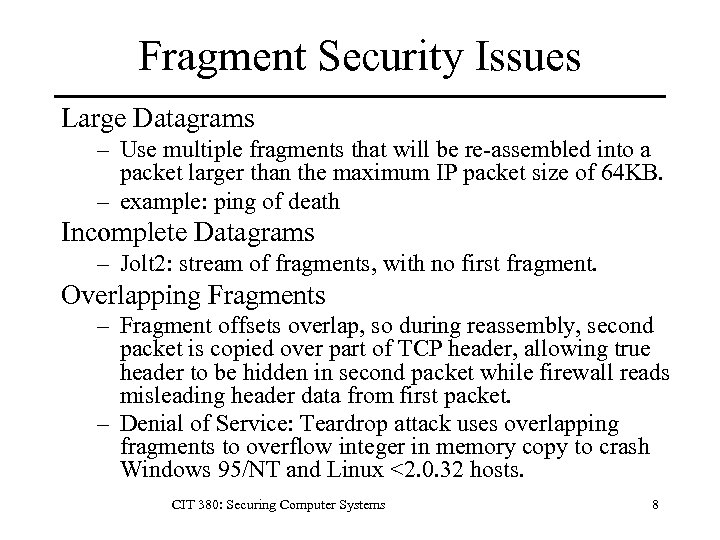 Fragment Security Issues Large Datagrams – Use multiple fragments that will be re-assembled into a packet larger than the maximum IP packet size of 64 KB. – example: ping of death Incomplete Datagrams – Jolt 2: stream of fragments, with no first fragment. Overlapping Fragments – Fragment offsets overlap, so during reassembly, second packet is copied over part of TCP header, allowing true header to be hidden in second packet while firewall reads misleading header data from first packet. – Denial of Service: Teardrop attack uses overlapping fragments to overflow integer in memory copy to crash Windows 95/NT and Linux <2. 0. 32 hosts. CIT 380: Securing Computer Systems 8
Fragment Security Issues Large Datagrams – Use multiple fragments that will be re-assembled into a packet larger than the maximum IP packet size of 64 KB. – example: ping of death Incomplete Datagrams – Jolt 2: stream of fragments, with no first fragment. Overlapping Fragments – Fragment offsets overlap, so during reassembly, second packet is copied over part of TCP header, allowing true header to be hidden in second packet while firewall reads misleading header data from first packet. – Denial of Service: Teardrop attack uses overlapping fragments to overflow integer in memory copy to crash Windows 95/NT and Linux <2. 0. 32 hosts. CIT 380: Securing Computer Systems 8
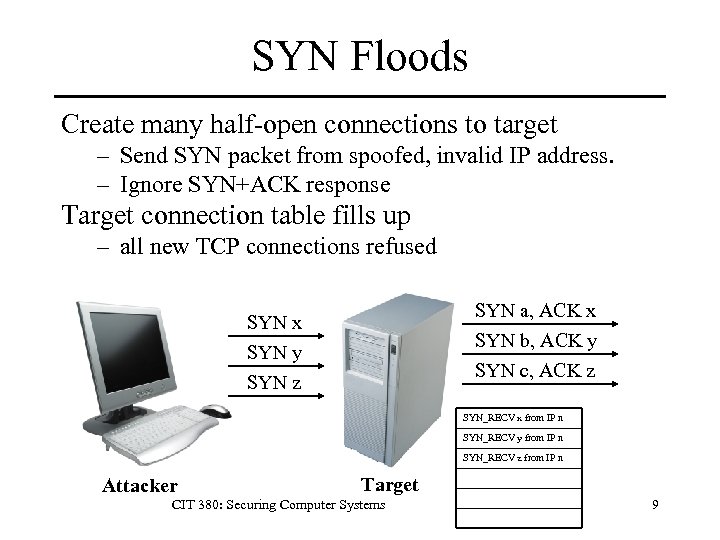 SYN Floods Create many half-open connections to target – Send SYN packet from spoofed, invalid IP address. – Ignore SYN+ACK response Target connection table fills up – all new TCP connections refused SYN a, ACK x SYN b, ACK y SYN c, ACK z SYN x SYN y SYN z SYN_RECV x from IP n SYN_RECV y from IP n SYN_RECV z from IP n Attacker Target CIT 380: Securing Computer Systems 9
SYN Floods Create many half-open connections to target – Send SYN packet from spoofed, invalid IP address. – Ignore SYN+ACK response Target connection table fills up – all new TCP connections refused SYN a, ACK x SYN b, ACK y SYN c, ACK z SYN x SYN y SYN z SYN_RECV x from IP n SYN_RECV y from IP n SYN_RECV z from IP n Attacker Target CIT 380: Securing Computer Systems 9
 SYN Flood Defences • Micro-connections: Allocate few resources (~16 bytes) micro-record until ACK recv’d • RST Cookies: – Server sends incorrect SYN+ACK to first client connection request, eliciting RST as response. Thereafter, connections from that client are accepted. • SYN Cookies: Store state in ISN, not on server. – Compute ISN using hash of src + dst IP addresses and ports. – Valid clients will respond with ISN+1, allowing server to compute connection table entry. CIT 380: Securing Computer Systems 10
SYN Flood Defences • Micro-connections: Allocate few resources (~16 bytes) micro-record until ACK recv’d • RST Cookies: – Server sends incorrect SYN+ACK to first client connection request, eliciting RST as response. Thereafter, connections from that client are accepted. • SYN Cookies: Store state in ISN, not on server. – Compute ISN using hash of src + dst IP addresses and ports. – Valid clients will respond with ISN+1, allowing server to compute connection table entry. CIT 380: Securing Computer Systems 10
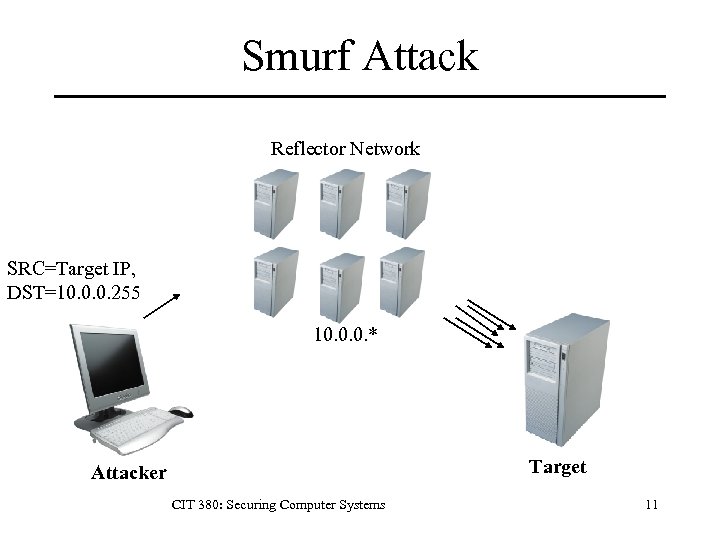 Smurf Attack Reflector Network SRC=Target IP, DST=10. 0. 0. 255 10. 0. 0. * Target Attacker CIT 380: Securing Computer Systems 11
Smurf Attack Reflector Network SRC=Target IP, DST=10. 0. 0. 255 10. 0. 0. * Target Attacker CIT 380: Securing Computer Systems 11
 Smurf Attack Build special ICMP/UDP echo packet Forge IP source address to be that of target. Destination address is a broadcast address. Each host that receives broadcast will respond to the spoofed target address with an echo packet, overwhelming target host. Most current routers refuse to pass on directed broadcast packets. CIT 380: Securing Computer Systems 12
Smurf Attack Build special ICMP/UDP echo packet Forge IP source address to be that of target. Destination address is a broadcast address. Each host that receives broadcast will respond to the spoofed target address with an echo packet, overwhelming target host. Most current routers refuse to pass on directed broadcast packets. CIT 380: Securing Computer Systems 12
 DNS Amplification Spoof DNS query from victim – 60 -byte query returns 512 -byte response (1999) – Extended DNS allows up to 4320 byte response. – 73: 1 amplification of traffic Requires open resolvers – DNS servers that will recursively resolve requests from any host on Internet. DNS servers should: – Return authoritative answers to anyone. – Recursively resolve for local authenticated hosts. CIT 380: Securing Computer Systems 13
DNS Amplification Spoof DNS query from victim – 60 -byte query returns 512 -byte response (1999) – Extended DNS allows up to 4320 byte response. – 73: 1 amplification of traffic Requires open resolvers – DNS servers that will recursively resolve requests from any host on Internet. DNS servers should: – Return authoritative answers to anyone. – Recursively resolve for local authenticated hosts. CIT 380: Securing Computer Systems 13
 Computational Attacks • Goal: Exhaust CPU resources of target. • Target: Application Layer • Examples: – 2002. BBCode markup language of php. BB could consume 100% CPU in infinite expansion of multiply nested tags. – 2003. Crosby and Wallach show to select input to reduce hash (O(1) performance) to linked list (O(n) performance). Attacks vs. Bro IDS, perl. – 2005. Tomcat 5. 5 directory listing of large directories could use large amounts of CPU. CIT 380: Securing Computer Systems 14
Computational Attacks • Goal: Exhaust CPU resources of target. • Target: Application Layer • Examples: – 2002. BBCode markup language of php. BB could consume 100% CPU in infinite expansion of multiply nested tags. – 2003. Crosby and Wallach show to select input to reduce hash (O(1) performance) to linked list (O(n) performance). Attacks vs. Bro IDS, perl. – 2005. Tomcat 5. 5 directory listing of large directories could use large amounts of CPU. CIT 380: Securing Computer Systems 14
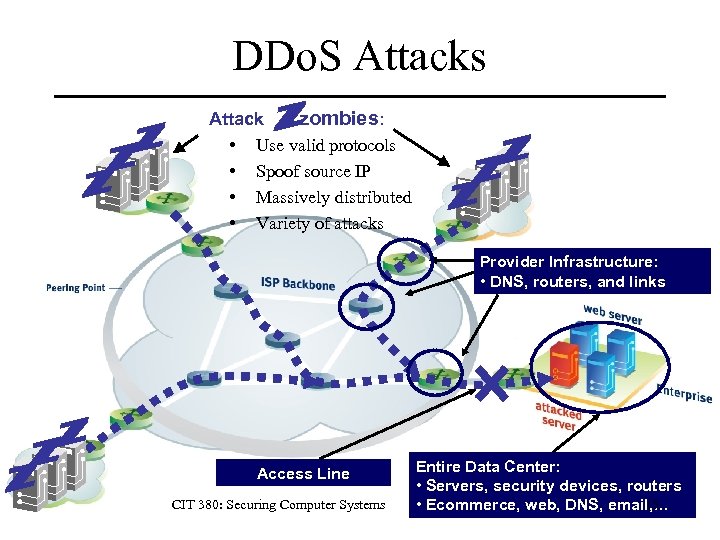 DDo. S Attacks Attack zombies: • Use valid protocols • Spoof source IP • Massively distributed • Variety of attacks Provider Infrastructure: • DNS, routers, and links Access Line CIT 380: Securing Computer Systems Entire Data Center: • Servers, security devices, routers 15 • Ecommerce, web, DNS, email, …
DDo. S Attacks Attack zombies: • Use valid protocols • Spoof source IP • Massively distributed • Variety of attacks Provider Infrastructure: • DNS, routers, and links Access Line CIT 380: Securing Computer Systems Entire Data Center: • Servers, security devices, routers 15 • Ecommerce, web, DNS, email, …
 Timeline of a DDOS Attack 1. Set up DDOS Network (Botnet) 1. Manual compromise by group of crackers. 2. Automated comprise by a worm. 2. Launch Attack 3. Victim networks become unresponsive Identification difficult due to router/host failures and lack of logging of packets. 4. Third party effects Victim responses sent to spoofed IP addresses. CIT 380: Securing Computer Systems 16
Timeline of a DDOS Attack 1. Set up DDOS Network (Botnet) 1. Manual compromise by group of crackers. 2. Automated comprise by a worm. 2. Launch Attack 3. Victim networks become unresponsive Identification difficult due to router/host failures and lack of logging of packets. 4. Third party effects Victim responses sent to spoofed IP addresses. CIT 380: Securing Computer Systems 16
 Distributed Reflection DOS Combine SYN Flood + DDOS attacks – Forge target’s IP address in SYN flood on multiple reflection servers. – Amplification: most OSes send multiple SYN+ACK responses to SYN packet. – Concealment: packets come from multiple reflection servers, not actual attacker host. – Difficult to block: attacker may rotate attacks from large pool of reflection servers, many of which may be important hosts which you need to receive traffic from. CIT 380: Securing Computer Systems 17
Distributed Reflection DOS Combine SYN Flood + DDOS attacks – Forge target’s IP address in SYN flood on multiple reflection servers. – Amplification: most OSes send multiple SYN+ACK responses to SYN packet. – Concealment: packets come from multiple reflection servers, not actual attacker host. – Difficult to block: attacker may rotate attacks from large pool of reflection servers, many of which may be important hosts which you need to receive traffic from. CIT 380: Securing Computer Systems 17
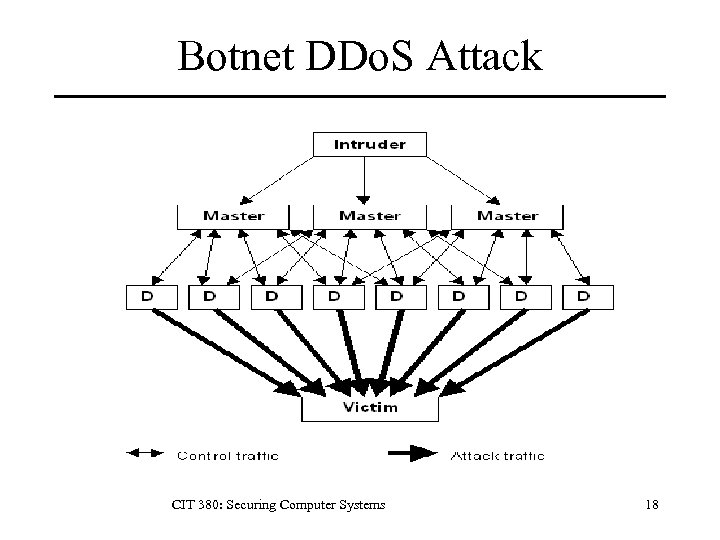 Botnet DDo. S Attack CIT 380: Securing Computer Systems 18
Botnet DDo. S Attack CIT 380: Securing Computer Systems 18
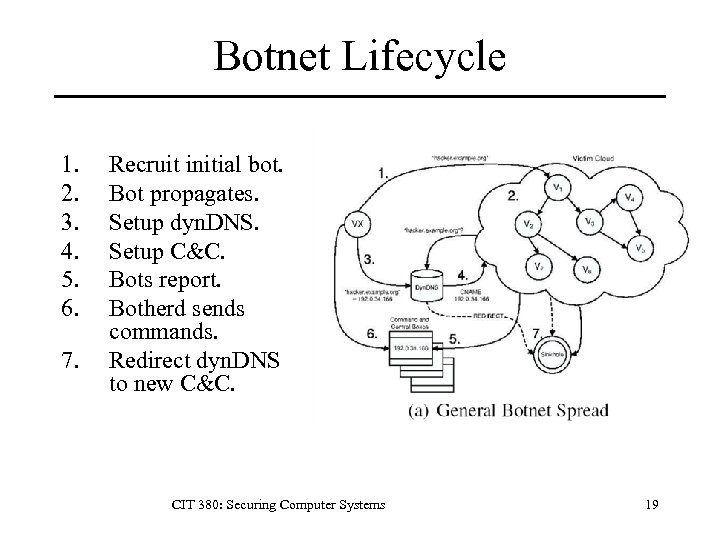 Botnet Lifecycle 1. 2. 3. 4. 5. 6. 7. Recruit initial bot. Bot propagates. Setup dyn. DNS. Setup C&C. Bots report. Botherd sends commands. Redirect dyn. DNS to new C&C. CIT 380: Securing Computer Systems 19
Botnet Lifecycle 1. 2. 3. 4. 5. 6. 7. Recruit initial bot. Bot propagates. Setup dyn. DNS. Setup C&C. Bots report. Botherd sends commands. Redirect dyn. DNS to new C&C. CIT 380: Securing Computer Systems 19
 Botnet Applications • • • DDo. S for extortion Spamming Proxying Phishing Spreading malware Spying – keylogging – network sniffing CIT 380: Securing Computer Systems 20
Botnet Applications • • • DDo. S for extortion Spamming Proxying Phishing Spreading malware Spying – keylogging – network sniffing CIT 380: Securing Computer Systems 20
 Roles and Responsibilities • Botherd – Collects and manages bots (zombies. ) – Rents botnet to users. • Sponsors – Recruits and employs spammers, cashers, etc. • Spammers • Developers – Develop bot code. – Develop exploits used by bots to compromise PCs. • Casher – Launders goods/money for sponsors. CIT 380: Securing Computer Systems 21
Roles and Responsibilities • Botherd – Collects and manages bots (zombies. ) – Rents botnet to users. • Sponsors – Recruits and employs spammers, cashers, etc. • Spammers • Developers – Develop bot code. – Develop exploits used by bots to compromise PCs. • Casher – Launders goods/money for sponsors. CIT 380: Securing Computer Systems 21
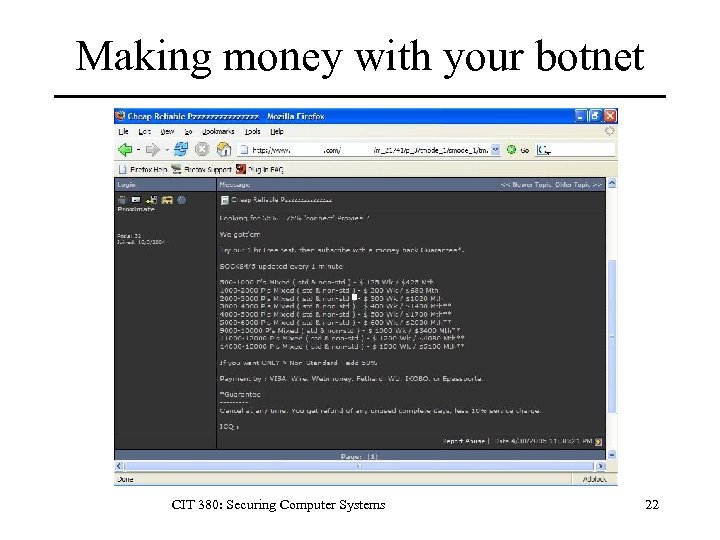 Making money with your botnet CIT 380: Securing Computer Systems 22
Making money with your botnet CIT 380: Securing Computer Systems 22
 Bot Lifecycle 1. 2. 3. 4. 5. 6. 7. Old agent scanner selects target host. Old agent attempts exploit against target. If exploit ok, agent transfers self to target. Agent begins running on target. Agent registers itself with master server. Master accepts agent as member w/ pw. Agent logs into communication channel with provided password. 8. Agent waits for commands from master. CIT 380: Securing Computer Systems 23
Bot Lifecycle 1. 2. 3. 4. 5. 6. 7. Old agent scanner selects target host. Old agent attempts exploit against target. If exploit ok, agent transfers self to target. Agent begins running on target. Agent registers itself with master server. Master accepts agent as member w/ pw. Agent logs into communication channel with provided password. 8. Agent waits for commands from master. CIT 380: Securing Computer Systems 23
 Bot Capabilities • DDOS Attacks – – – SYN floods Smurf UDP floods ICMP floods Mixed • Recruitment • • • – Scanning engine. – Many exploits. – Use other bot backdoors. CIT 380: Securing Computer Systems File transfer Proxying E-mail harvesting Sniffing Spamming Self-defence – Anti-virus – Polymorphism – Rootkit. 24
Bot Capabilities • DDOS Attacks – – – SYN floods Smurf UDP floods ICMP floods Mixed • Recruitment • • • – Scanning engine. – Many exploits. – Use other bot backdoors. CIT 380: Securing Computer Systems File transfer Proxying E-mail harvesting Sniffing Spamming Self-defence – Anti-virus – Polymorphism – Rootkit. 24
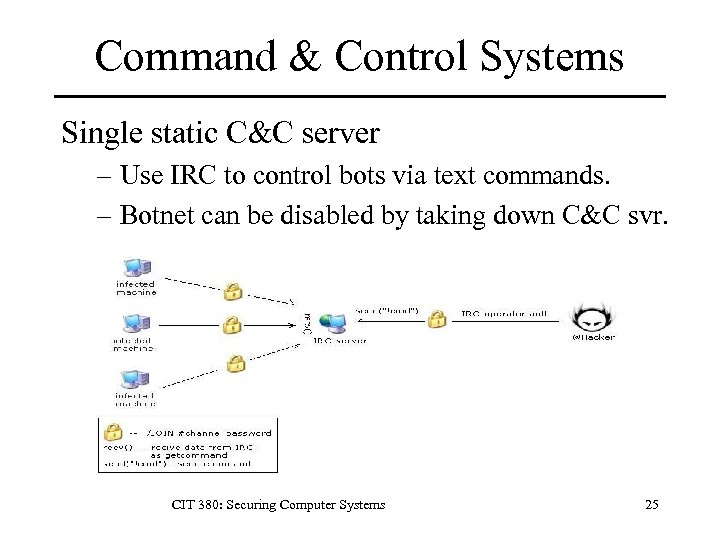 Command & Control Systems Single static C&C server – Use IRC to control bots via text commands. – Botnet can be disabled by taking down C&C svr. CIT 380: Securing Computer Systems 25
Command & Control Systems Single static C&C server – Use IRC to control bots via text commands. – Botnet can be disabled by taking down C&C svr. CIT 380: Securing Computer Systems 25
 Command & Control Systems Dynamic DNS – Bots access C&C through d. DNS address. – If C&C down, use d. DNS to point to new C&C. Decentralized DNS – Use bots as dynamic DNS servers. – Change DNS results regularly. – Change DNS servers regularly. CIT 380: Securing Computer Systems 26
Command & Control Systems Dynamic DNS – Bots access C&C through d. DNS address. – If C&C down, use d. DNS to point to new C&C. Decentralized DNS – Use bots as dynamic DNS servers. – Change DNS results regularly. – Change DNS servers regularly. CIT 380: Securing Computer Systems 26
 Botnet Families • Agobot/Phatbot – Over 500 variants. – Modular structure: easy to add features. – Some use WASTE p 2 p communication. • SDBot – Simpler than Agobot, but common. • GTBot – Script m. IRC client for Windows. CIT 380: Securing Computer Systems 27
Botnet Families • Agobot/Phatbot – Over 500 variants. – Modular structure: easy to add features. – Some use WASTE p 2 p communication. • SDBot – Simpler than Agobot, but common. • GTBot – Script m. IRC client for Windows. CIT 380: Securing Computer Systems 27
 Storm Worm • Command & Control – Encrypted edonkey p 2 p. – Fast flux DNS network. – Bots hidden via rootkits. • Spreading techniques – Browser vulnerabilities – Malware sent via e-mail, IM, blog/forum posts • Activities – Pump-n-dump scams. – Phishing. – DDOS. CIT 380: Securing Computer Systems 28
Storm Worm • Command & Control – Encrypted edonkey p 2 p. – Fast flux DNS network. – Bots hidden via rootkits. • Spreading techniques – Browser vulnerabilities – Malware sent via e-mail, IM, blog/forum posts • Activities – Pump-n-dump scams. – Phishing. – DDOS. CIT 380: Securing Computer Systems 28
 Why DDo. S is Hard to Stop 1. Usability of DDo. S tools Attackers can d/l user friendly advanced tools. 2. IP spoofing DDo. S attacks can always be spoofed. 3. Numerous agents Attacker agents spread across networks. 4. Variety of traffic DDo. S attacks can be launched with any protocol. 5. High-volume traffic At DDo. S traffic volumes, firewalls and IDS must analyze each packet quickly, i. e. without deep packet inspection or cross-packet correlations. CIT 380: Securing Computer Systems 29
Why DDo. S is Hard to Stop 1. Usability of DDo. S tools Attackers can d/l user friendly advanced tools. 2. IP spoofing DDo. S attacks can always be spoofed. 3. Numerous agents Attacker agents spread across networks. 4. Variety of traffic DDo. S attacks can be launched with any protocol. 5. High-volume traffic At DDo. S traffic volumes, firewalls and IDS must analyze each packet quickly, i. e. without deep packet inspection or cross-packet correlations. CIT 380: Securing Computer Systems 29
 Filterable and non-Filterable Attacks – Attack non-essential services (ICMP echo) or ports (random UDP flood. ) Non-filterable Attacks – Attack essential services (email or web. ) – Packets may be partially valid for targeted protocol. CIT 380: Securing Computer Systems 30
Filterable and non-Filterable Attacks – Attack non-essential services (ICMP echo) or ports (random UDP flood. ) Non-filterable Attacks – Attack essential services (email or web. ) – Packets may be partially valid for targeted protocol. CIT 380: Securing Computer Systems 30
 DDOS Prevention • Apply patches against technical attacks. • Firewall rules to drop known attacks at perimeter. • Overprovisioning – Network bandwidth, NICs – Memory, disk – CPU • Load balancing • Caching – Create static page frequently instead of dynamically creating page whenever accessed. CIT 380: Securing Computer Systems 31
DDOS Prevention • Apply patches against technical attacks. • Firewall rules to drop known attacks at perimeter. • Overprovisioning – Network bandwidth, NICs – Memory, disk – CPU • Load balancing • Caching – Create static page frequently instead of dynamically creating page whenever accessed. CIT 380: Securing Computer Systems 31
 DDOS Detection Detecting zombie hosts – DDOSPing – Zombie Zapper Detecting a DDOS attack – Performance monitoring: network and host – Network intrusion detection systems CIT 380: Securing Computer Systems 32
DDOS Detection Detecting zombie hosts – DDOSPing – Zombie Zapper Detecting a DDOS attack – Performance monitoring: network and host – Network intrusion detection systems CIT 380: Securing Computer Systems 32
 DDOS Reaction • Filter out identifiable DDOS traffic. • Contact ISP for help with – Filtering and rate limiting. – Tracking down source of attack. • Move the target – White House avoided by changing IP address. • Use Alternate Infrastructure – Use caching to decrease server load. – Use anti-ddos provider like Akamai, Prolexic. CIT 380: Securing Computer Systems 33
DDOS Reaction • Filter out identifiable DDOS traffic. • Contact ISP for help with – Filtering and rate limiting. – Tracking down source of attack. • Move the target – White House avoided by changing IP address. • Use Alternate Infrastructure – Use caching to decrease server load. – Use anti-ddos provider like Akamai, Prolexic. CIT 380: Securing Computer Systems 33
 Key Points • Types of denial of service attack – Technical attacks (SYN flood, DNS amp, smurf) – Bandwidth attacks (DDOS) • DOS attacks are a serious threat – Can take down large sites (often for money. ) – DDOS prevention techniques. • Botnets make DDOS easy and effective – Command & control techniques. CIT 380: Securing Computer Systems 34
Key Points • Types of denial of service attack – Technical attacks (SYN flood, DNS amp, smurf) – Bandwidth attacks (DDOS) • DOS attacks are a serious threat – Can take down large sites (often for money. ) – DDOS prevention techniques. • Botnets make DDOS easy and effective – Command & control techniques. CIT 380: Securing Computer Systems 34
 References 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. 11. 12. 13. 14. 15. 16. 17. 18. 19. 20. “Al-Jazeera Hobbled by DDOS Attack, ” Info. World, http: //www. infoworld. com/article/03/03/26/HNjazeera_1. html, March 26, 2003. Scott Berinato, “How a Bookmaker and a Whiz Kid Took On an Extortionist—and Won, ” CSO Online, http: //www. csoonline. com/read/050105/extortion_pf. html, Nov 22 2003. CERT Coordination Center, “Results of the Distributed-Systems Intruder Tools Workshop, ” December 1999, http: //www. cert. org/reports/dsit_workshop-final. html David Dagon et. al. , “A Taxonomy of Botnets, ” http: //www. ensl. cs. gwu. edu/csnetsec/CSNet. Sec? action=Attach. File&do=get&target=taxonomy_botnets. pdf Dancho Danchev, http: //ddanchev. blogspot. com/2007/03/botnet-communication-platforms. html, 2007. David Dittrich, DDOS Archives, http: //staff. washington. edu/dittrich/misc/ddos/, 2006. Brandon Enright, “Exposing Stormworm, ” http: //noh. ucsd. edu/~bmenrigh/exposing_storm. ppt, 2007. Gadi Evron and Ronald Vaugn, “DNS Amplification Attacks, ” http: //www. isotf. org/news/DNS-Amplification-Attacks. pdf , 2006. Greene, “ISP Security 101 Primer, ” http: //www. nanog. org/mtg-0602/greene. html, 2003. The Honeynet Project, “Know Your Enemy: Tracking Botnets, ” http: //www. honeynet. org/papers/bots/, 2005. Steve Gibson, “Distributed Reflection Denial of Service, ” http: //www. grc. com/dos/drdos. htm, Feb 22 2002. Jim Lippard, “Botnets 101, ” http: //www. arizonatele. com/atic/show/lippard-botnets-0605. ppt Stuart Mc. Clure, Joel Scambray, and George Kurtz, Hacking Exposed, 5/e, Mc. Graw-Hill, 2005. Jelena Mirkovic, Sven Dietrich, David Dittrich, and Peter Reiher, Internet Denial of Service: Attack and Defense Mechanisms, Prentice Hall, 2005. C. Nuttall, “Crime Gangs Extort Money with Hacking Threat, ” The Financial Times, 11 Dec 2003, http: //www. rense. com/general 44/hack. htm Andy Patrizio, “The Storm that Keeps Blowing, ” http: //www. internetnews. com/bus-news/article. php/3707106, Oct 24 2007. Joel Scambray, Mike Shema, Caleb Sima, Hacking Exposed Web Applications, Second Edition, Mc. Graw-Hill, 2006. Secure Computing, “Zombie Statistics, ” http: //www. ciphertrust. com/resources/statistics/zombie. php Ed Skoudis, Counter Hack Reloaded, Prentice Hall, 2006. Scott A Crosby and Dan S Wallach, “Denial of Service via Algorithmic Complexity Attacks, ” USENIX Security 2003, http: //www. cs. rice. edu/~scrosby/hash/, 2003. CIT 380: Securing Computer Systems 35
References 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. 11. 12. 13. 14. 15. 16. 17. 18. 19. 20. “Al-Jazeera Hobbled by DDOS Attack, ” Info. World, http: //www. infoworld. com/article/03/03/26/HNjazeera_1. html, March 26, 2003. Scott Berinato, “How a Bookmaker and a Whiz Kid Took On an Extortionist—and Won, ” CSO Online, http: //www. csoonline. com/read/050105/extortion_pf. html, Nov 22 2003. CERT Coordination Center, “Results of the Distributed-Systems Intruder Tools Workshop, ” December 1999, http: //www. cert. org/reports/dsit_workshop-final. html David Dagon et. al. , “A Taxonomy of Botnets, ” http: //www. ensl. cs. gwu. edu/csnetsec/CSNet. Sec? action=Attach. File&do=get&target=taxonomy_botnets. pdf Dancho Danchev, http: //ddanchev. blogspot. com/2007/03/botnet-communication-platforms. html, 2007. David Dittrich, DDOS Archives, http: //staff. washington. edu/dittrich/misc/ddos/, 2006. Brandon Enright, “Exposing Stormworm, ” http: //noh. ucsd. edu/~bmenrigh/exposing_storm. ppt, 2007. Gadi Evron and Ronald Vaugn, “DNS Amplification Attacks, ” http: //www. isotf. org/news/DNS-Amplification-Attacks. pdf , 2006. Greene, “ISP Security 101 Primer, ” http: //www. nanog. org/mtg-0602/greene. html, 2003. The Honeynet Project, “Know Your Enemy: Tracking Botnets, ” http: //www. honeynet. org/papers/bots/, 2005. Steve Gibson, “Distributed Reflection Denial of Service, ” http: //www. grc. com/dos/drdos. htm, Feb 22 2002. Jim Lippard, “Botnets 101, ” http: //www. arizonatele. com/atic/show/lippard-botnets-0605. ppt Stuart Mc. Clure, Joel Scambray, and George Kurtz, Hacking Exposed, 5/e, Mc. Graw-Hill, 2005. Jelena Mirkovic, Sven Dietrich, David Dittrich, and Peter Reiher, Internet Denial of Service: Attack and Defense Mechanisms, Prentice Hall, 2005. C. Nuttall, “Crime Gangs Extort Money with Hacking Threat, ” The Financial Times, 11 Dec 2003, http: //www. rense. com/general 44/hack. htm Andy Patrizio, “The Storm that Keeps Blowing, ” http: //www. internetnews. com/bus-news/article. php/3707106, Oct 24 2007. Joel Scambray, Mike Shema, Caleb Sima, Hacking Exposed Web Applications, Second Edition, Mc. Graw-Hill, 2006. Secure Computing, “Zombie Statistics, ” http: //www. ciphertrust. com/resources/statistics/zombie. php Ed Skoudis, Counter Hack Reloaded, Prentice Hall, 2006. Scott A Crosby and Dan S Wallach, “Denial of Service via Algorithmic Complexity Attacks, ” USENIX Security 2003, http: //www. cs. rice. edu/~scrosby/hash/, 2003. CIT 380: Securing Computer Systems 35


