a9c3c70b8349404b8f0e3ddb641ef7e8.ppt
- Количество слайдов: 183
CICS (Customer Information Control System) 1
Table of Contents • • • Introduction to CICS Basic Mapping Support Program Control File Processing Error Handling Queues Interval and Task Control Recovery and Restart Program preparation CICS Supplied Transactions Case Study 2
Introduction to CICS • Customer Information Control System -CICS developed in late 1960 s as a DB/DC control system • CICS provides an interface between the Operating System and application programs • Macro Level CICS - initial version Assembler macro to request CICS services • Command Level CICS - high level lang. version - commands to request CICS services - Single command can replace series of macros 3
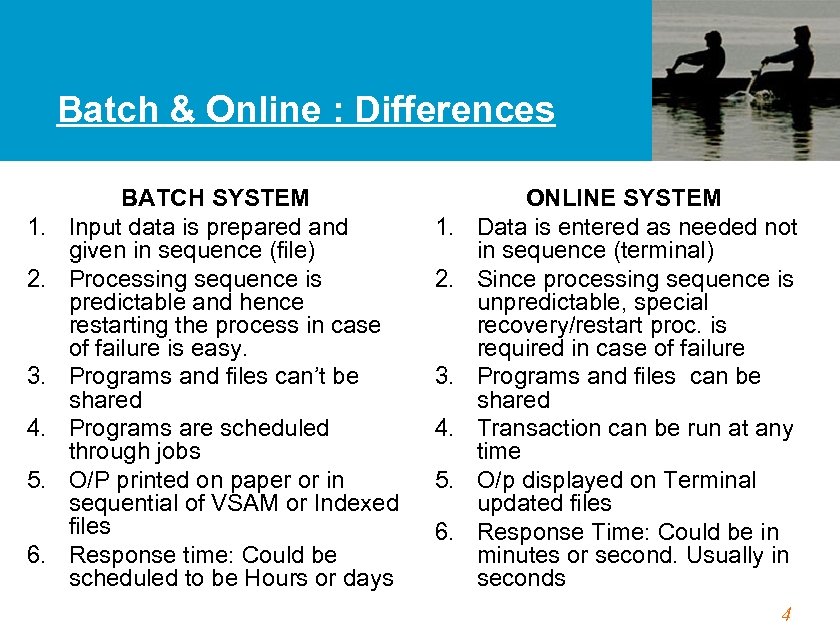
Batch & Online : Differences 1. 2. 3. 4. 5. 6. BATCH SYSTEM Input data is prepared and given in sequence (file) Processing sequence is predictable and hence restarting the process in case of failure is easy. Programs and files can’t be shared Programs are scheduled through jobs O/P printed on paper or in sequential of VSAM or Indexed files Response time: Could be scheduled to be Hours or days 1. 2. 3. 4. 5. 6. ONLINE SYSTEM Data is entered as needed not in sequence (terminal) Since processing sequence is unpredictable, special recovery/restart proc. is required in case of failure Programs and files can be shared Transaction can be run at any time O/p displayed on Terminal updated files Response Time: Could be in minutes or second. Usually in seconds 4
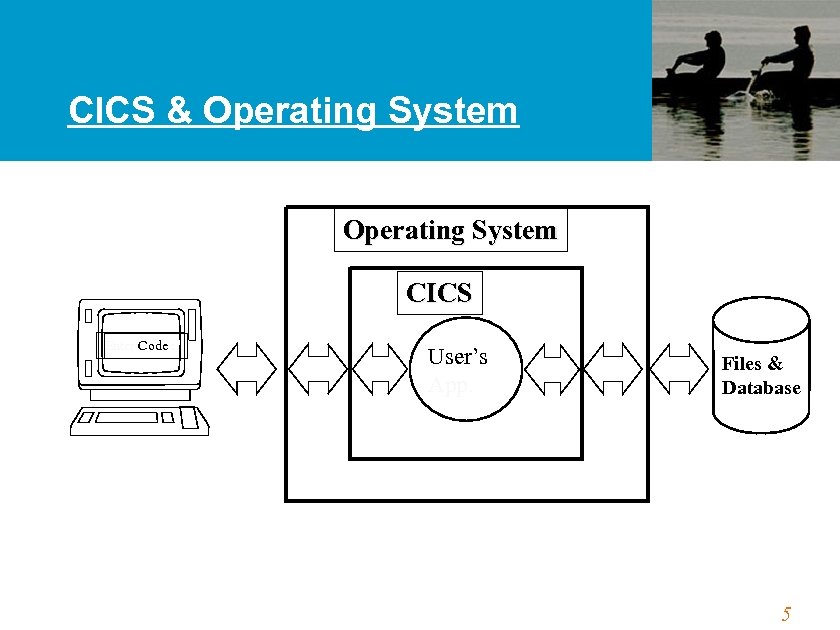
CICS & Operating System CICS Enter Code : User’s App. Files & Database 5
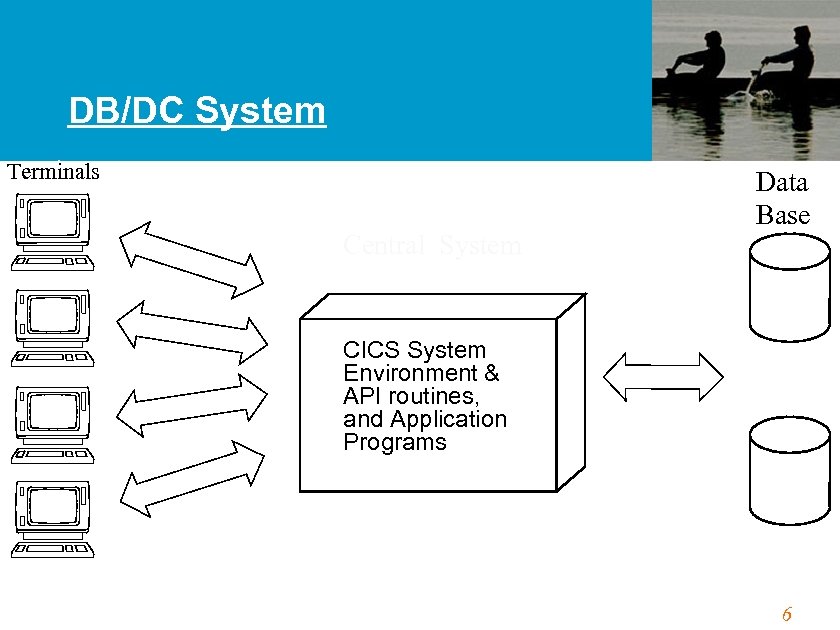
DB/DC System Terminals Central System Data Base CICS System Environment & API routines, and Application Programs 6
CICS System Services • Data-Communication Functions • Data-Handling Functions • Application Program Services • System Services • Monitoring Functions 7
Task & Transaction • Task : - A basic unit of work which is scheduled by the operating system or CICS Ex -Read from and write to the terminal • Transaction : - An entity which initiates execution of a task. In CICS, transaction is identified by the transaction identifier (Transid) 8
Application Programming Concepts • Pseudo-Conversational • Multitasking • Multithreading • Quasi-Reentrancy 9
Terminal Conversation • Conversational : A mode of dialogue between program and terminal based on a combination of sending message and receiving message within the same task – Since human response is slower than the CPU speed, a significant amount of resource will be wasted just waiting • Pseudo-Conversational. A mode of dialogue between program and terminal which appears to the operator as a continuous conversation but which is actually carried by a series of tasks 10
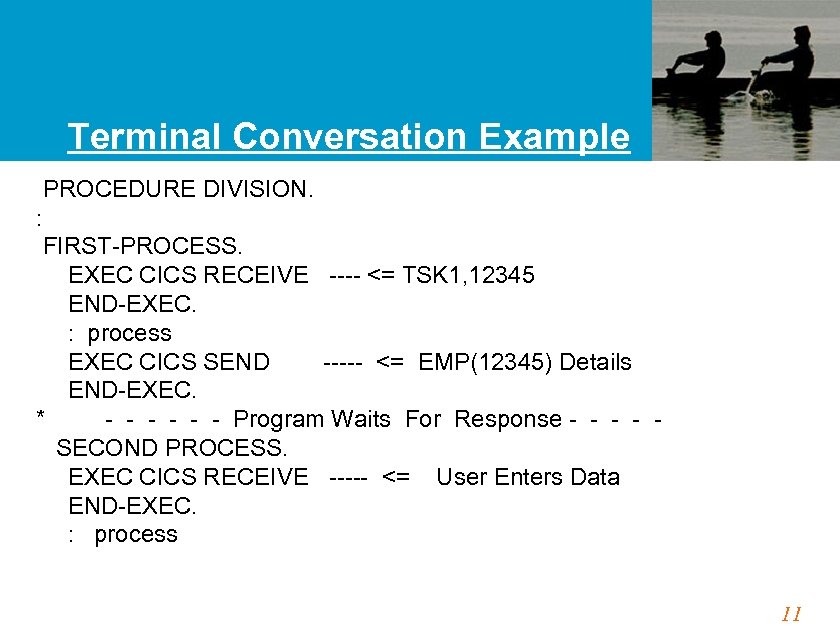
Terminal Conversation Example PROCEDURE DIVISION. : FIRST-PROCESS. EXEC CICS RECEIVE ---- <= TSK 1, 12345 END-EXEC. : process EXEC CICS SEND ----- <= EMP(12345) Details END-EXEC. * - - - Program Waits For Response - - SECOND PROCESS. EXEC CICS RECEIVE ----- <= User Enters Data END-EXEC. : process 11
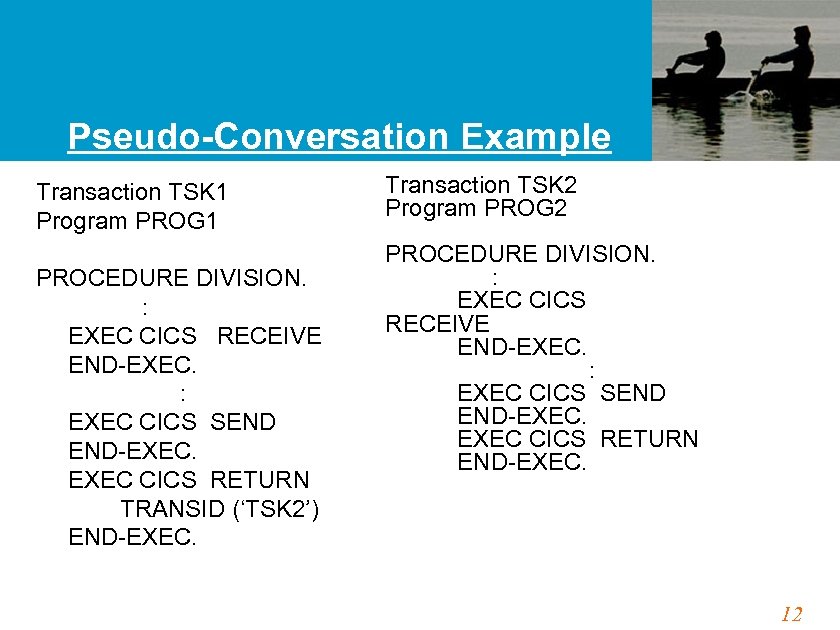
Pseudo-Conversation Example Transaction TSK 1 Program PROG 1 PROCEDURE DIVISION. : EXEC CICS RECEIVE END-EXEC. : EXEC CICS SEND END-EXEC CICS RETURN TRANSID (‘TSK 2’) END-EXEC. Transaction TSK 2 Program PROG 2 PROCEDURE DIVISION. : EXEC CICS RECEIVE END-EXEC. : EXEC CICS SEND END-EXEC CICS RETURN END-EXEC. 12
CICS Components • Control Programs (or Management Modules) Programs that interface between OS and app. pgm Handle the general functions that are crucial to operation of CICS • Control Tables Define the CICS environment Functionally associated with the management module • Control Blocks (or Areas) Contain system type information. Eg. Task Control Area contains information about the task 13
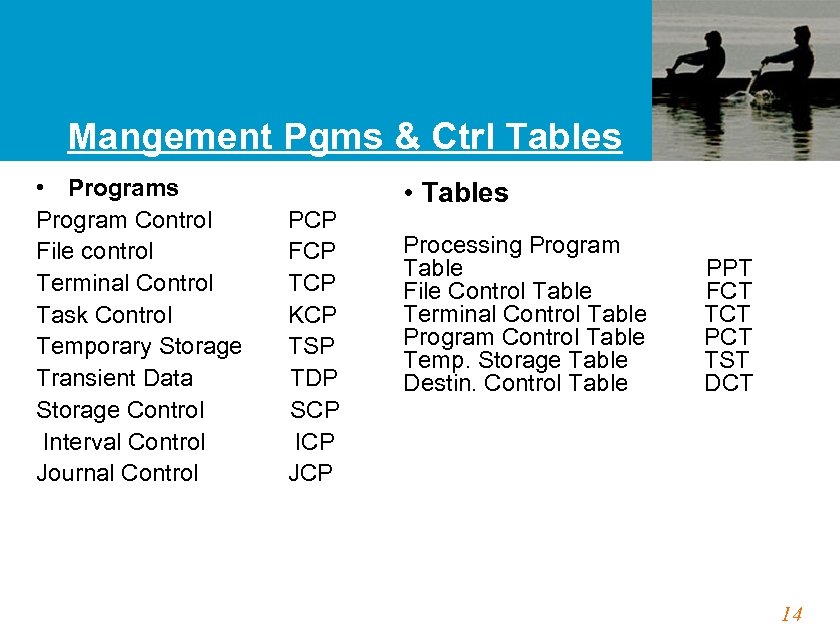
Mangement Pgms & Ctrl Tables • Programs Program Control PCP File control FCP Terminal Control TCP Task Control KCP Temporary Storage TSP Transient Data TDP Storage Control SCP Interval Control ICP Journal Control JCP • Tables Processing Program Table PPT File Control Table FCT Terminal Control Table TCT Program Control Table PCT Temp. Storage Table TST Destin. Control Table DCT 14
CICS Program Considerations: • Must eventually return control to CICS • Can’t modify procedure division instructions because CICS programs may be shared by many tasks • Can modify working storage since a unique copy of working storage is created for each task 15
CICS Program Restrictions: • No CONFIG. SECTION, I/O SECTION to be specified in the ENVIRONMENT DIVISION. • FILE SECTION, OPEN, CLOSE, and non-CICS READ & WRITE statements are not permitted because file management is handled by CICS. • COBOL commands such as ACCEPT, DISPLAY, EXHIBIT, TRACE, STOP RUN, GOBACK are avoided. (STOP RUN & GOBACK are sometimes included in order to eliminate compiler diagnostic but never executed) 16
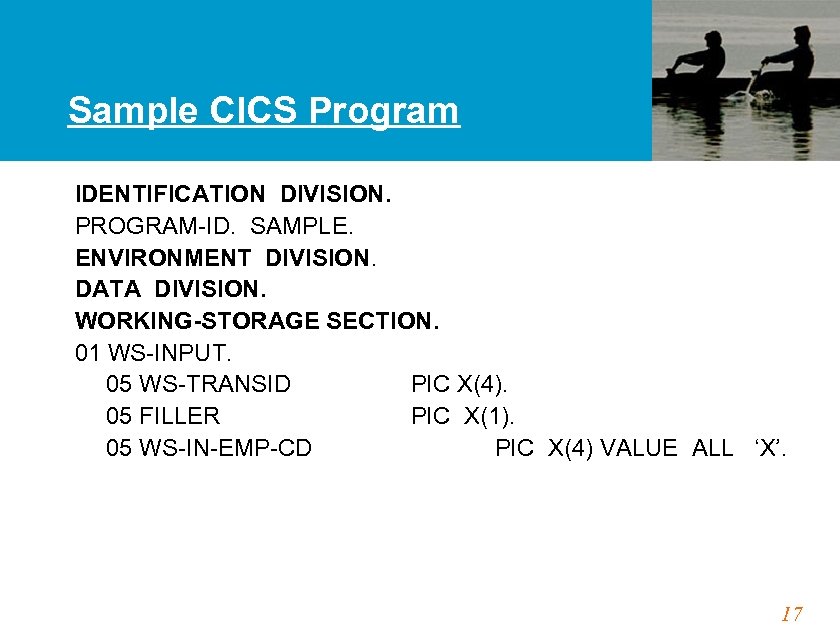
Sample CICS Program IDENTIFICATION DIVISION. PROGRAM-ID. SAMPLE. ENVIRONMENT DIVISION. DATA DIVISION. WORKING-STORAGE SECTION. 01 WS-INPUT. 05 WS-TRANSID PIC X(4). 05 FILLER PIC X(1). 05 WS-IN-EMP-CD PIC X(4) VALUE ALL ‘X’. 17
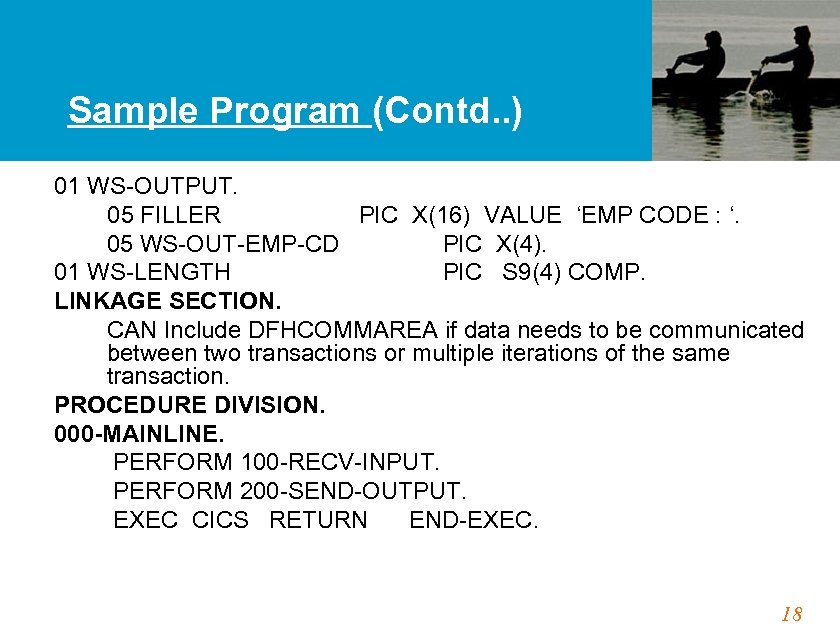
Sample Program (Contd. . ) 01 WS-OUTPUT. 05 FILLER PIC X(16) VALUE ‘EMP CODE : ‘. 05 WS-OUT-EMP-CD PIC X(4). 01 WS-LENGTH PIC S 9(4) COMP. LINKAGE SECTION. CAN Include DFHCOMMAREA if data needs to be communicated between two transactions or multiple iterations of the same transaction. PROCEDURE DIVISION. 000 -MAINLINE. PERFORM 100 -RECV-INPUT. PERFORM 200 -SEND-OUTPUT. EXEC CICS RETURN END-EXEC. 18
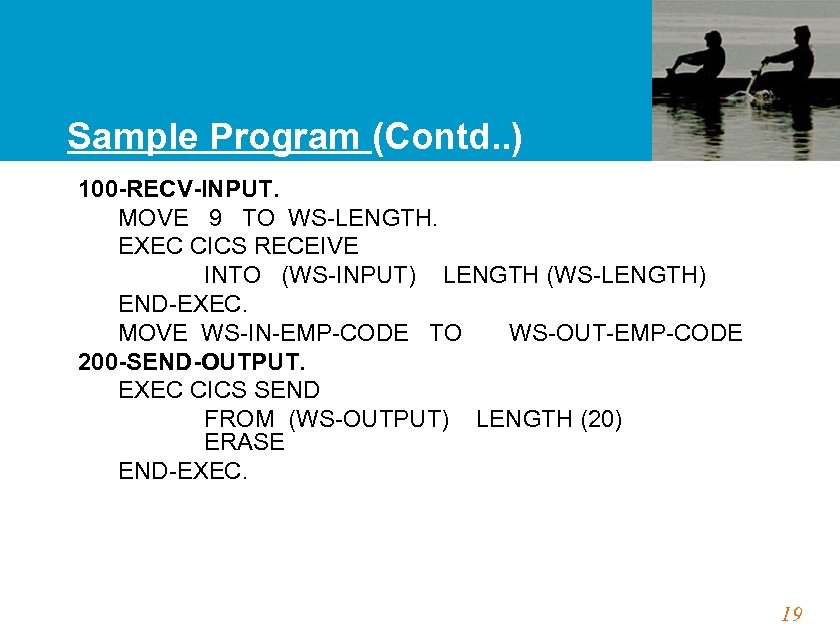
Sample Program (Contd. . ) 100 -RECV-INPUT. MOVE 9 TO WS-LENGTH. EXEC CICS RECEIVE INTO (WS-INPUT) LENGTH (WS-LENGTH) END-EXEC. MOVE WS-IN-EMP-CODE TO WS-OUT-EMP-CODE 200 -SEND-OUTPUT. EXEC CICS SEND FROM (WS-OUTPUT) LENGTH (20) ERASE END-EXEC. 19
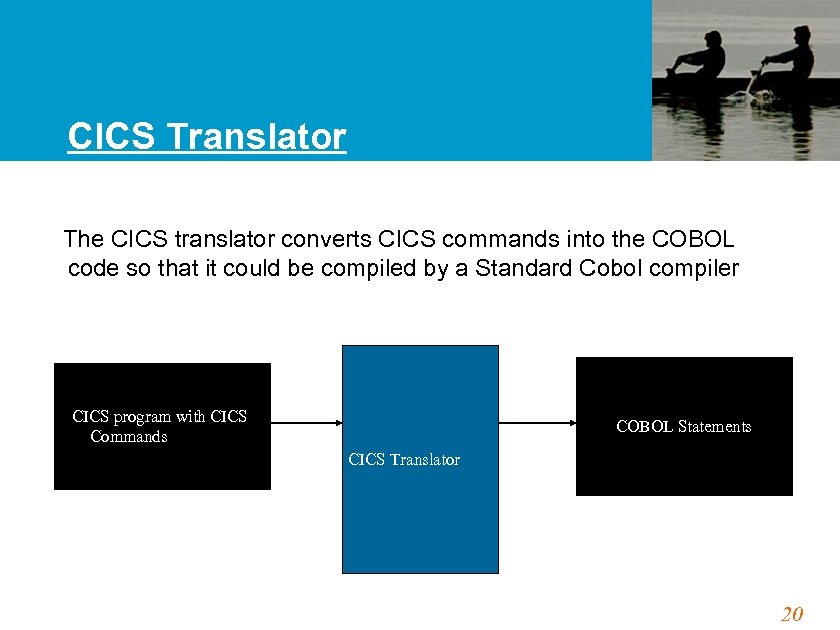
CICS Translator The CICS translator converts CICS commands into the COBOL code so that it could be compiled by a Standard Cobol compiler CICS program with CICS Commands COBOL Statements CICS Translator 20
Translator • When you compile a CICS/VS program the translator will automatically add many lines of code to your program, which can be seen in the compiled listing 21
Basic Mapping Support 22
Topics in BMS • Introduction to BMS • Map and Mapset • Physical and Symbolic Map • Map Definition Macros • Screen Manipulation/Handling • Screen Design Considerations • Interfacing with Terminal using a Map 23
Introduction to BMS Introductory concepts In online systems, formatted screens are used. In order to display formatted screen, a terminal (e. g. 3278) must receive a series of data stream called Native Mode Data Stream (NMDS) based on the hardware protocol; this NMDS is a mixture of Buffer Control Characters (BCCs) and text data. NMDS is designed for a particular terminal and is thus both device dependent and format dependent. So if NMDS is used, re-coding is required whenever there is change in the terminal device or screen format. To remove this device and format dependency from application program, CICS provides a facility called Basic Mapping Support (BMS). 24
Primary Functions of BMS • Removal of device dependent codes from Application Program • Removal of constant information from Application program (Headers, Titles. . . ) • Construct NMDS - Native Mode Data Stream • Text handling • Terminal Paging & Message routing • Contents of the screen defined thru’ BMS is called Map. • Map is a program written in assembly language. • BMS macros are available for Map coding. The BMS Macros are coded in the form of Maps, and Mapsets to define the screen attributes, screen field positions, and field characteristics. 25
Map and Mapset • Representation of one screen format is called Map (screen panel). • One or more maps, link edited together, makes up a Mapset (load module). • Mapset must have a entry in PPT as given below: Or DFHPPT TYPE=ENTRY, MAPSET=name TYPE=ENTRY, PROGRAM=name 26
Map and Mapset (Contd. . ) • Mapset name has two parts. – Generic name 1 - 7 chars. Used in App. Program. – Suffix 1 char. To identify the device type • Multimap Panel • Dynamically constructing a screen panel with multiple maps at the execution time 27
Map and Mapset (Contd. . ) The concepts of map and mapset can be utilized in two type of cases as given below: Case 1: A mapset consist of a single map. For e. g. MAPSET 1 MAPNUM 1 Case 2: A mapset consists of several maps. For e. g. MAPSET 2 MAPNUM 1 MAPNUM 2 28
Types of MAPS There are 2 types of MAPS • Physical Map is a map used by CICS (CSECT) Ensure device independence in the application program BMS macro coding ==> Assembly==> Link edit ==> Load module ==> LOADLIB ===> To be used by CICS • Symbolic Map Ensure device and format independence in the application program Symbolic Map is a map used by Application Program (DSECT) BMS macro coding ==> Assembly ==> Symbolic map definition ==> COPYLIB ==> Copied (COPY) into CICS application program. 29
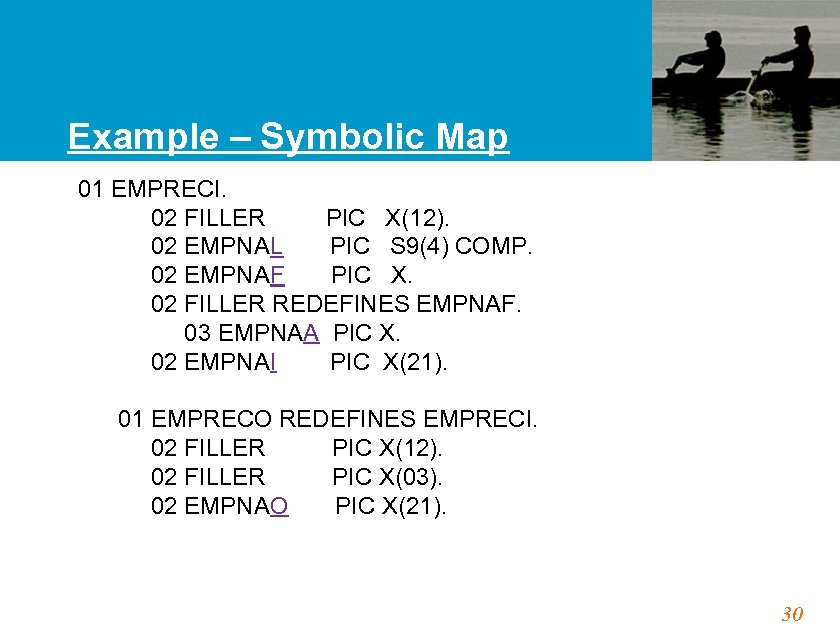
Example – Symbolic Map 01 EMPRECI. 02 FILLER PIC X(12). 02 EMPNAL PIC S 9(4) COMP. 02 EMPNAF PIC X. 02 FILLER REDEFINES EMPNAF. 03 EMPNAA PIC X. 02 EMPNAI PIC X(21). 01 EMPRECO REDEFINES EMPRECI. 02 FILLER PIC X(12). 02 FILLER PIC X(03). 02 EMPNAO PIC X(21). 30
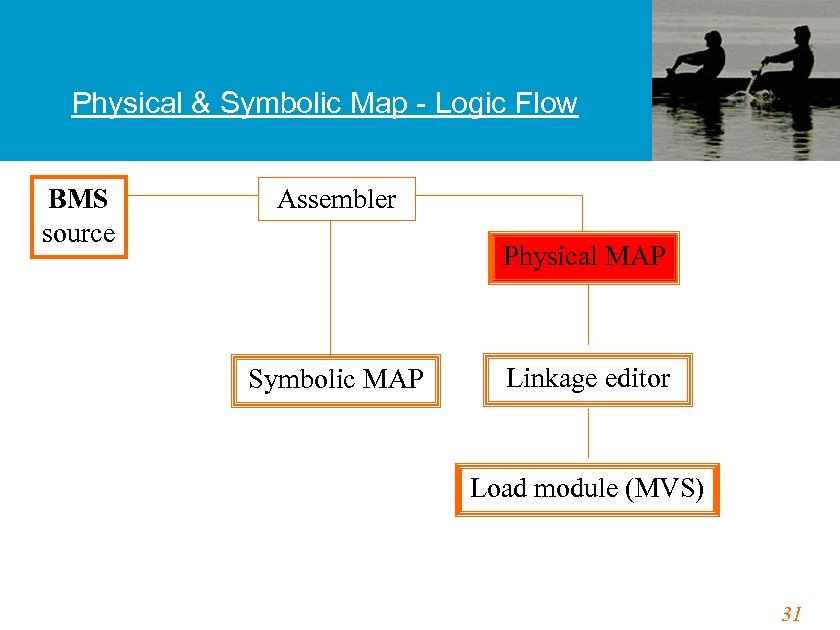
Physical & Symbolic Map - Logic Flow BMS source Assembler Physical MAP Symbolic MAP Linkage editor Load module (MVS) 31
Physical Map • • • Physical Map. The BMS macros are assembled and link-edited into CICS load library to create the physical map. The mapset like any other CICS program is stored in CICS runtime library the PPT(Program Processing Table). At the program execution time the physical map is being used by CICS to load the screen image. In case of input operations, the physical map defines the maximum length, the starting position for each field to be read and allows BMS to interpret an input NMDS. In case of output operations, the physical map defines the starting position, length, field characteristics and the default data for each field and allows BMS to construct an output NMDS. 32
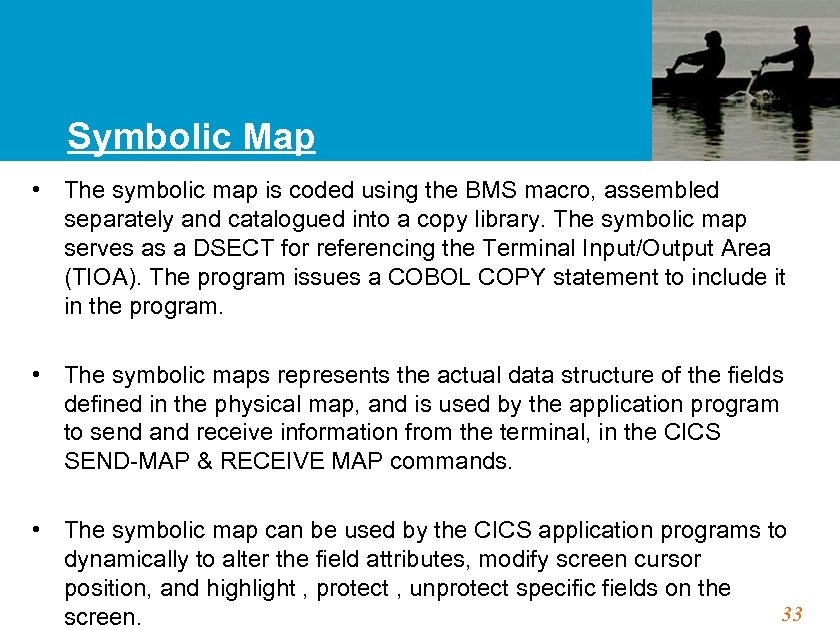
Symbolic Map • The symbolic map is coded using the BMS macro, assembled separately and catalogued into a copy library. The symbolic map serves as a DSECT for referencing the Terminal Input/Output Area (TIOA). The program issues a COBOL COPY statement to include it in the program. • The symbolic maps represents the actual data structure of the fields defined in the physical map, and is used by the application program to send and receive information from the terminal, in the CICS SEND-MAP & RECEIVE MAP commands. • The symbolic map can be used by the CICS application programs to dynamically to alter the field attributes, modify screen cursor position, and highlight , protect , unprotect specific fields on the 33 screen.
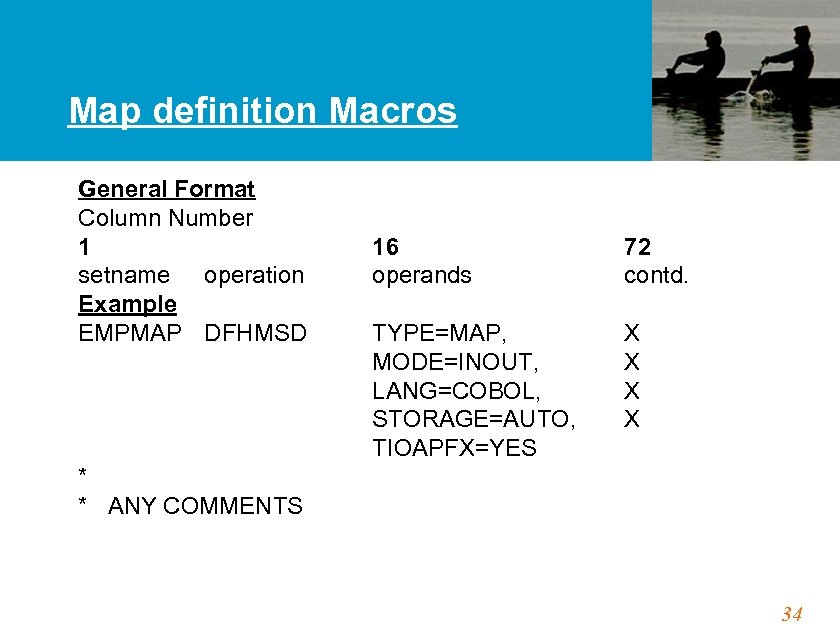
Map definition Macros General Format Column Number 1 setname operation Example EMPMAP DFHMSD 16 operands 72 contd. TYPE=MAP, MODE=INOUT, LANG=COBOL, STORAGE=AUTO, TIOAPFX=YES X X * * ANY COMMENTS 34
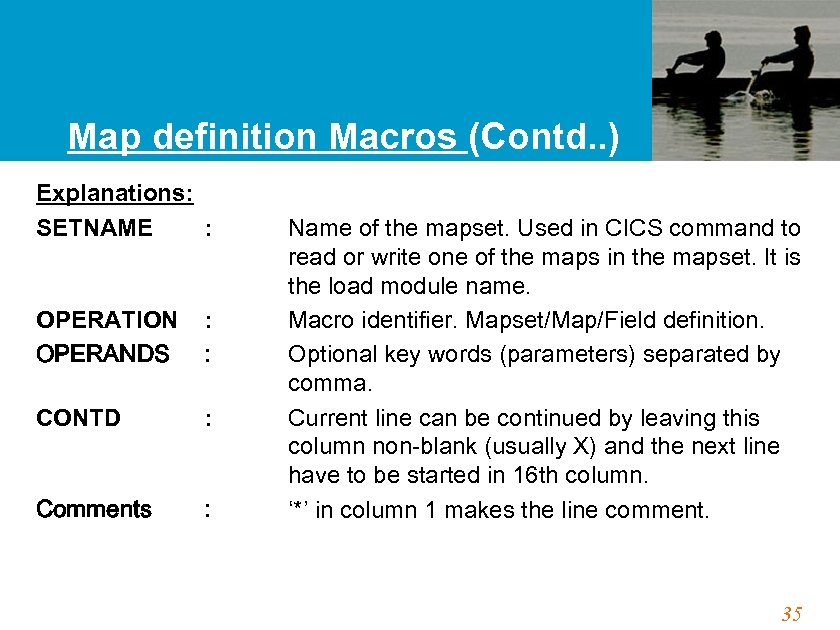
Map definition Macros (Contd. . ) Explanations: SETNAME : OPERATION OPERANDS : : CONTD : Comments : Name of the mapset. Used in CICS command to read or write one of the maps in the mapset. It is the load module name. Macro identifier. Mapset/Map/Field definition. Optional key words (parameters) separated by comma. Current line can be continued by leaving this column non-blank (usually X) and the next line have to be started in 16 th column. ‘*’ in column 1 makes the line comment. 35
Map definition Macros (Contd. . ) INITIAL VALUES : Escape Chars : by. Always values surround initial single quote marks ‘ and & 36
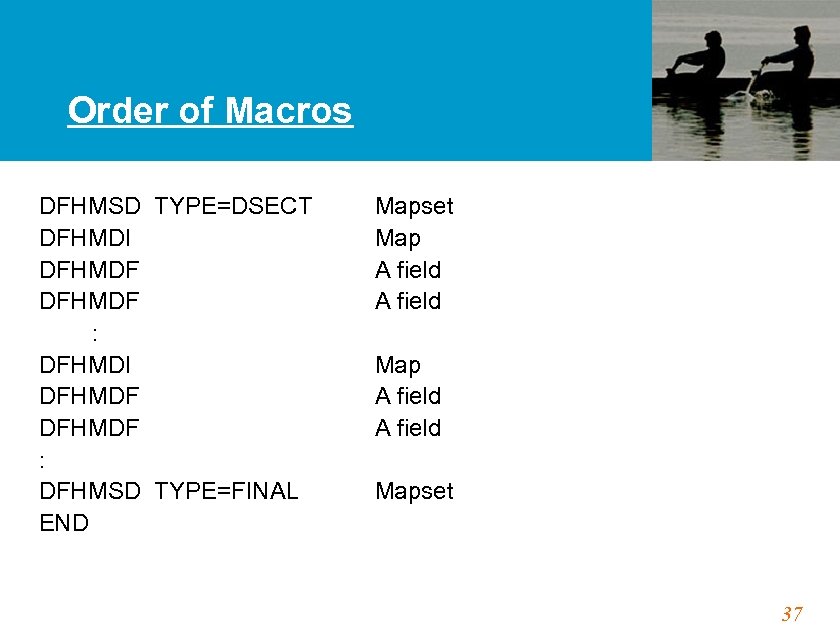
Order of Macros DFHMSD TYPE=DSECT Mapset DFHMDI Map DFHMDF A field : DFHMDI Map DFHMDF A field : DFHMSD TYPE=FINAL Mapset END 37
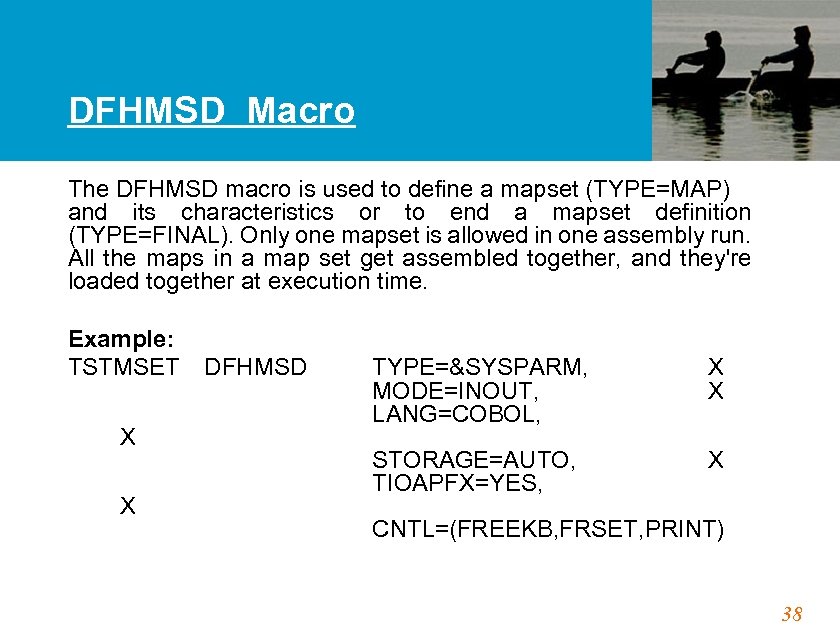
DFHMSD Macro The DFHMSD macro is used to define a mapset (TYPE=MAP) and its characteristics or to end a mapset definition (TYPE=FINAL). Only one mapset is allowed in one assembly run. All the maps in a map set get assembled together, and they're loaded together at execution time. Example: TSTMSET DFHMSD TYPE=&SYSPARM, X MODE=INOUT, X LANG=COBOL, X STORAGE=AUTO, X TIOAPFX=YES, X CNTL=(FREEKB, FRSET, PRINT) 38
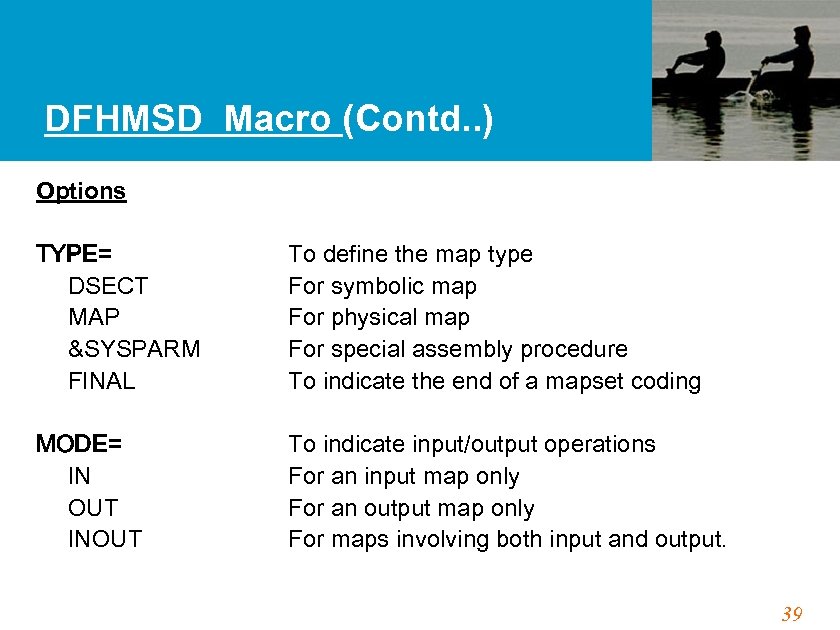
DFHMSD Macro (Contd. . ) Options TYPE= DSECT MAP &SYSPARM FINAL MODE= IN OUT INOUT To define the map type For symbolic map For physical map For special assembly procedure To indicate the end of a mapset coding To indicate input/output operations For an input map only For an output map only For maps involving both input and output. 39
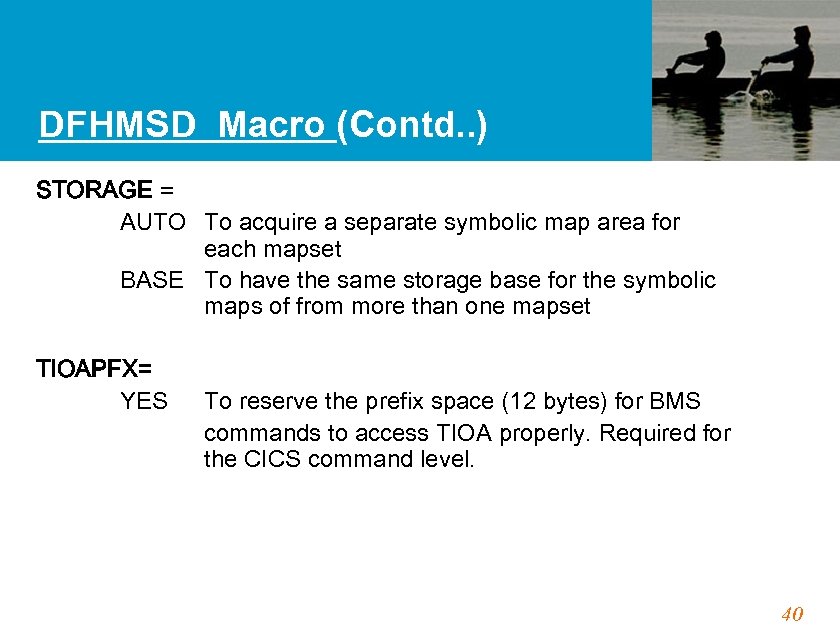
DFHMSD Macro (Contd. . ) STORAGE = AUTO To acquire a separate symbolic map area for each mapset BASE To have the same storage base for the symbolic maps of from more than one mapset TIOAPFX= YES To reserve the prefix space (12 bytes) for BMS commands to access TIOA properly. Required for the CICS command level. 40
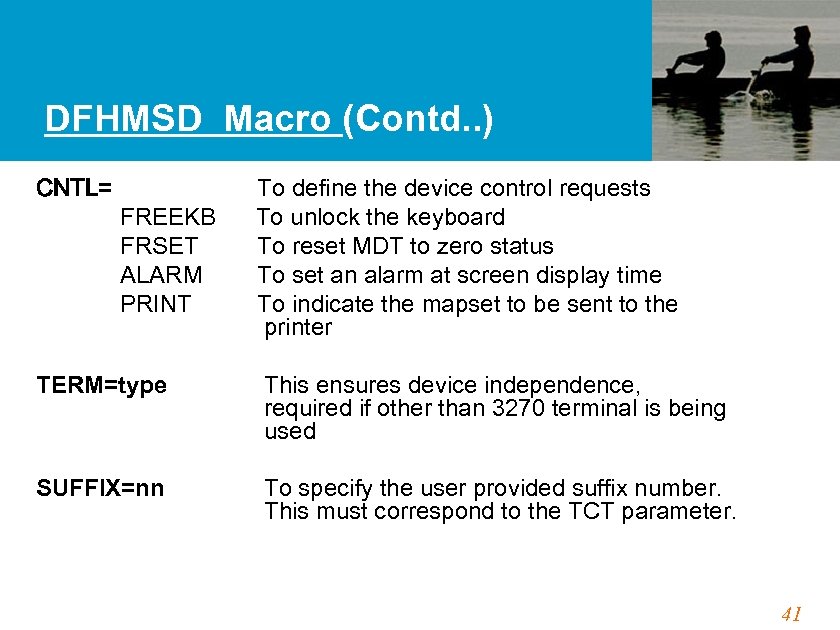
DFHMSD Macro (Contd. . ) CNTL= FREEKB FRSET ALARM PRINT To define the device control requests To unlock the keyboard To reset MDT to zero status To set an alarm at screen display time To indicate the mapset to be sent to the printer TERM=type This ensures device independence, required if other than 3270 terminal is being used SUFFIX=nn To specify the user provided suffix number. This must correspond to the TCT parameter. 41
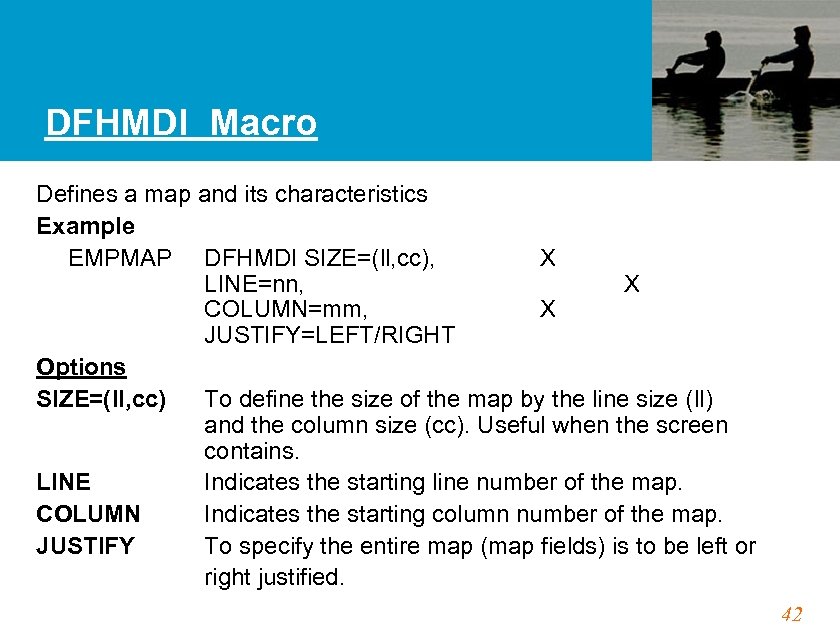
DFHMDI Macro Defines a map and its characteristics Example EMPMAP DFHMDI SIZE=(ll, cc), X LINE=nn, X COLUMN=mm, X JUSTIFY=LEFT/RIGHT Options SIZE=(ll, cc) To define the size of the map by the line size (ll) and the column size (cc). Useful when the screen contains. LINE Indicates the starting line number of the map. COLUMN Indicates the starting column number of the map. JUSTIFY To specify the entire map (map fields) is to be left or right justified. 42
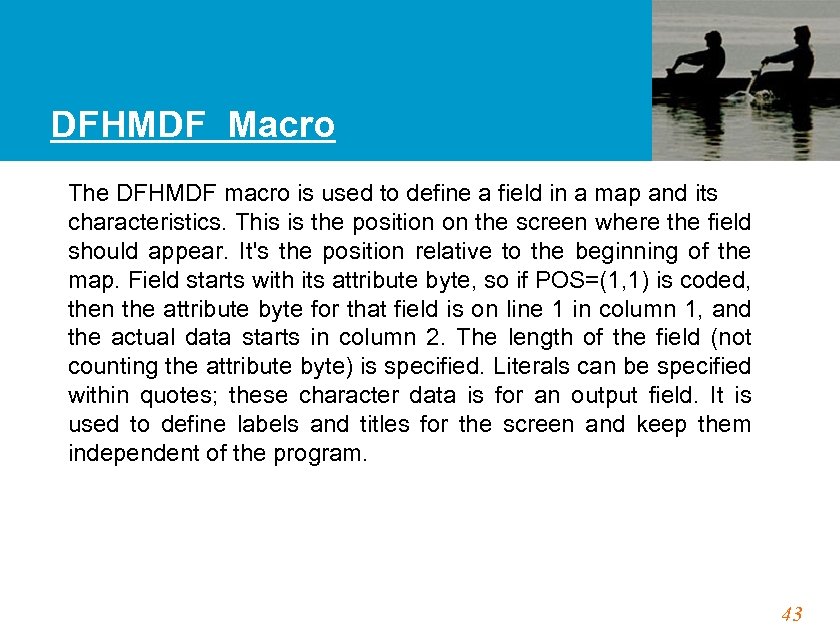
DFHMDF Macro The DFHMDF macro is used to define a field in a map and its characteristics. This is the position on the screen where the field should appear. It's the position relative to the beginning of the map. Field starts with its attribute byte, so if POS=(1, 1) is coded, then the attribute byte for that field is on line 1 in column 1, and the actual data starts in column 2. The length of the field (not counting the attribute byte) is specified. Literals can be specified within quotes; these character data is for an output field. It is used to define labels and titles for the screen and keep them independent of the program. 43
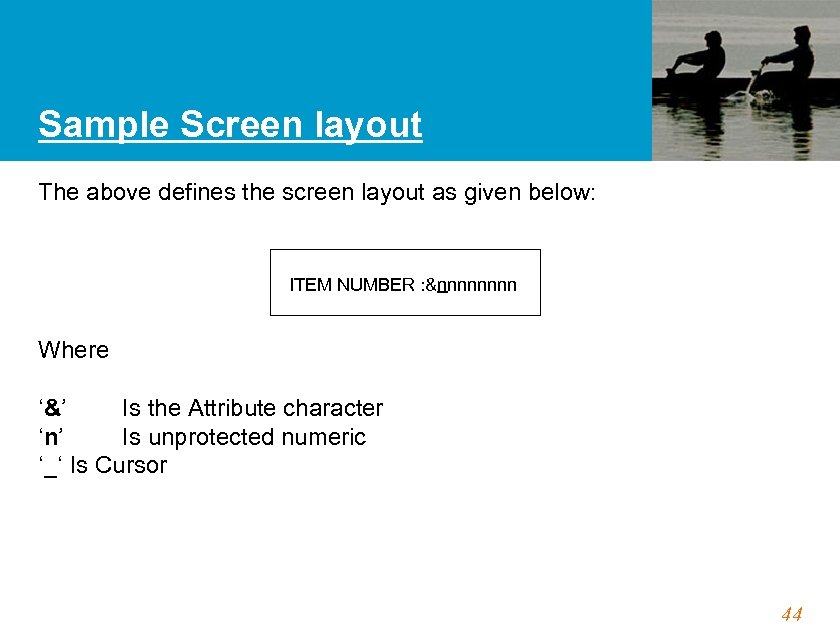
Sample Screen layout The above defines the screen layout as given below: ITEM NUMBER : &nnnn Where ‘&’ Is the Attribute character ‘n’ Is unprotected numeric ‘_‘ Is Cursor 44
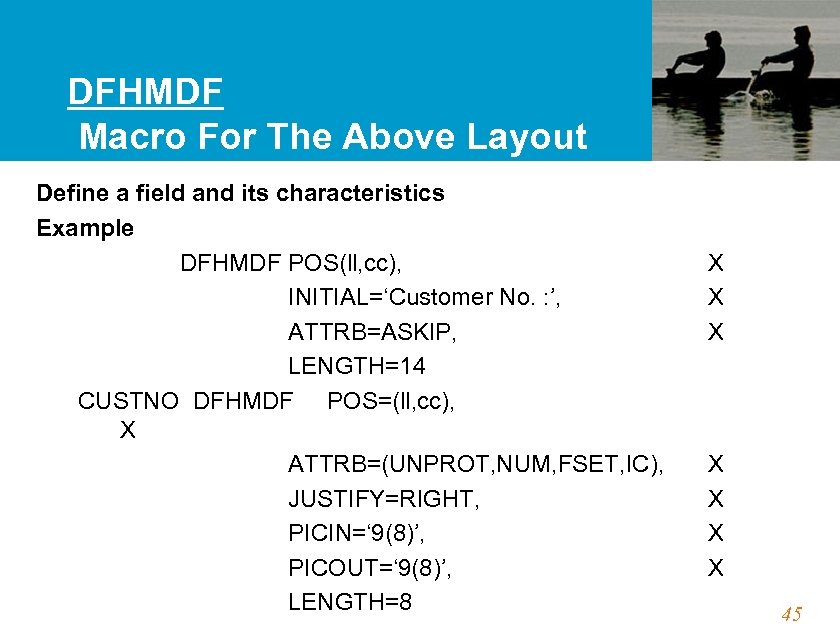
DFHMDF Macro For The Above Layout Define a field and its characteristics Example DFHMDF POS(ll, cc), INITIAL=‘Customer No. : ’, ATTRB=ASKIP, LENGTH=14 CUSTNO DFHMDF POS=(ll, cc), X ATTRB=(UNPROT, NUM, FSET, IC), JUSTIFY=RIGHT, PICIN=‘ 9(8)’, PICOUT=‘ 9(8)’, LENGTH=8 X X X X 45
Attribute character Function: The attribute character is an invisible 1 -byte character, which precedes a screen field and determines the characteristics of a field. ASKIP Autoskip. Data cannot be entered in this field. The cursor skips to the next field. PROT Protected field. Data cannot be entered into this field. If data is entered, it will cause the input-inhibit status. UNPROT Unprotected field. Data can be entered and this is used for all input fields. NUM Numeric field. Only numbers (0 to 9) and special characters (“. ” and “-“) are allowed. 46
Attribute character (Contd. . ) BRT Bright display of a field (highlight). NORM Normal display. DRK Dark display. IC Insert cursor. The cursor will be positioned in this field. In case, IC is specified more than once, the cursor is placed in the last field. FSET Field set. MDT is set on so that the field data is to be sent from the terminal to the host computer regardless of whether the field is actually modified by the user. 47
Modified Data Tag Function: Modified Data Tag (MDT) is a one bit of the attribute character. If it is off (0), it indicates that the terminal operator has not modified the field. If it is on (1), it indicates that the operator has modified this field. Only when MDT is on, the data of the field will be sent by the terminal hardware to the host computer. An effective use of MDT drastically reduces the amount of data traffic in the communication line and thus improves performance. Three ways of setting and resetting the MDT. 1. Terminal user modifies a field on the screen, it is automatically set to “ 1” (on) by the terminal hardware. 48
Modified Data Tag (Contd. . ) 2. If CNTL=FRSET is specified in the DFHMSD or DFHMDI macro, when the mapset or the map is sent to the terminal, MDT will be reset to “ 0” (off) i. e. not modified for all the fields of the mapset or the map. 3. If FSET is specified in the ATTRB parameter of the DFHMDF macro for a field, when the map is sent to the terminal, MDT will be set to “ 1”. (on i. e. modified) for the field regardless of whether the field has been modified by the terminal user. 49
Skipper Technique • Unlabelled 1 -byte field with the autoskip attribute • DFHMDF POS(ll, cc), ATTRB=ASKIP, LENGTH=1 • To skip the cursor to the next unprotected field after one unprotected field. • Screen Layout : &xxxxx&$ &xx where $ Skipper field & Attribute byte X Unprotected field 50
Stopper Technique • Unlabelled 1 -byte field with the protect attribute • DFHMDF POS(ll, cc), ATTRB=PROT, LENGTH=1 • To stop the cursor in order to prevent erroneous field overflow by terminal user. • Screen Layout : &xxxxx&$#&$ where # Stopper field 51
Format Of the Symbolic Map Format of Symbolic Map • Once the symbolic map is assembled and is placed in the COPY library, the COBOL COPY statement can be used to include it in the application program. • The symbolic map starts with the 01 level definition of the map name specified in the DFHMDI macro with the suffix ‘I’ for the input map and the suffix ‘O’ for the output map. • Next is the definition of FILLER PIC X(12), which is the TIOA prefix created by the TIOAPFX=YES of the DFHMSD macro; this is required by the BMS under the CICS command level. 52
Format Of the Symbolic Map (Contd. . ) For each field name (1 to 7 characters) specified in the DFHMDF macro, BMS creates three fields for inputs and three fields for outputs, by placing one character suffix to the original field name. The meaning of these fields are given below: • Name + L: The half-word binary (PIC S 9(4) COMP) field. For the input field, the actual number of characters typed in the field will be placed by the BMS when the map is received. For the output field, this is used for the dynamic cursor positioning. 53
Format Of the Symbolic Map (Contd. . ) • Name + F: Flag For input it be Byte. the field, X’ 80’ will if the field has been modified but no data is sent (i. e. the field has been cleared). Otherwise this field is X’ 00’. • Name + A: fields. The Attribute byte for both input and output • Name + I: The input data field. X’ 00’ will be placed if no data is entered. Note that space X’ 40’ is data. The application program should differentiate X’ 00’ from space (X’ 40’). • Name + O: The output data field. 54
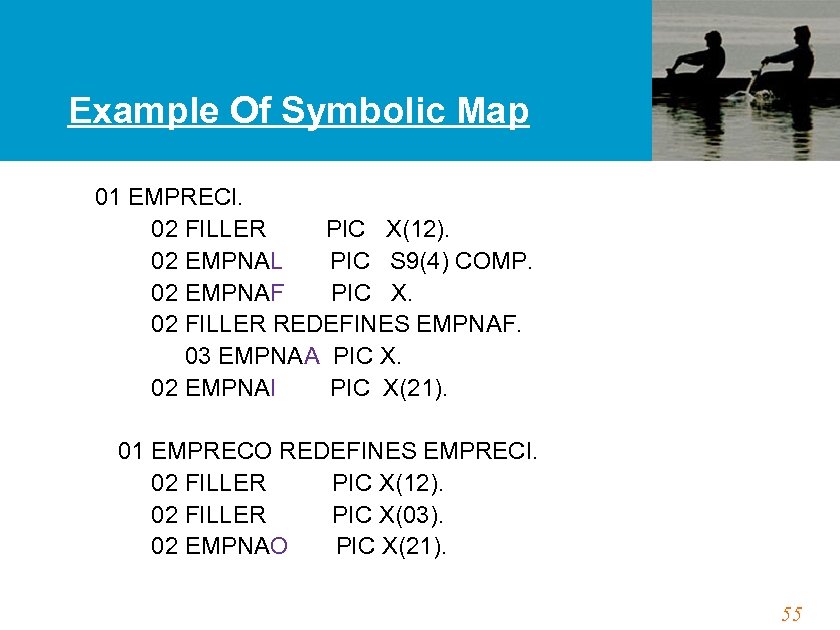
Example Of Symbolic Map 01 EMPRECI. 02 FILLER PIC X(12). 02 EMPNAL PIC S 9(4) COMP. 02 EMPNAF PIC X. 02 FILLER REDEFINES EMPNAF. 03 EMPNAA PIC X. 02 EMPNAI PIC X(21). 01 EMPRECO REDEFINES EMPRECI. 02 FILLER PIC X(12). 02 FILLER PIC X(03). 02 EMPNAO PIC X(21). 55
Cursor Positioning Techniques CICS provides multiple ways of to specify where to position the cursor on the screen. The cursor positioning is important to prompt an user of an entry he has to make, or to point to an error which has occurred during editing the user entries. • Static positioning (Achieved thru Map definition ATTRIB=IC). Example : DFHMDF POS=(5, 8), ATTRB=(UNPROT, FSET, IC), LENGTH=10 56
Cursor Positioning Techniques (Contd. . ) • Dynamic/Symbolic Positioning. The cursor is placed dynamically through an application program by moving -1 to the symbolic map field-length field (i. e. fieldname + L) for the field where the cursor is to be placed. The SEND MAP command must be issued with the CURSOR option (without value). Also, the mapset should be coded with MODE=INOUT in the DFHMSD macro. This approach is very useful when the cursor is to be placed at the field where data entry error has been detected by the data edit routine. 57
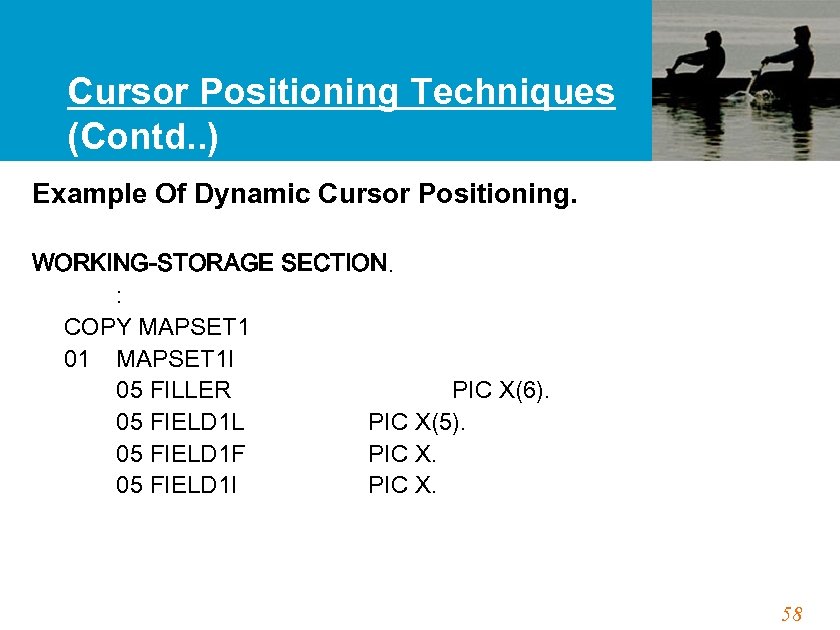
Cursor Positioning Techniques (Contd. . ) Example Of Dynamic Cursor Positioning. WORKING-STORAGE SECTION. : COPY MAPSET 1 01 MAPSET 1 I 05 FILLER PIC X(6). 05 FIELD 1 L PIC X(5). 05 FIELD 1 F PIC X. 05 FIELD 1 I PIC X. 58
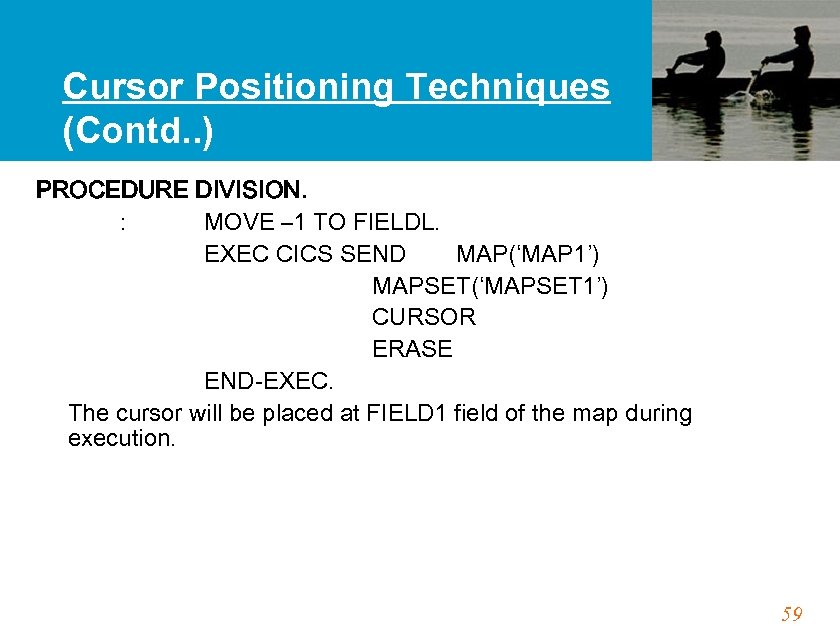
Cursor Positioning Techniques (Contd. . ) PROCEDURE DIVISION. : MOVE – 1 TO FIELDL. EXEC CICS SEND MAP(‘MAP 1’) MAPSET(‘MAPSET 1’) CURSOR ERASE END-EXEC. The cursor will be placed at FIELD 1 field of the map during execution. 59
Cursor Positioning Techniques (Contd. . ) Dynamic/Relative Positioning (application program) The cursor is placed dynamically through an application program using the CURSOR(data-value) option in the SEND MAP command with the value of the relative position (starting from zero) of the terminal. At the completion of the SEND MAP command, the map will be displayed with the cursor placed at the specified position, overriding the static cursor position defined at the map definition time. 60
Cursor Positioning Techniques (Contd. . ) Example EXEC CICS SEND MAP(‘MAP 1’) MAPSET(‘MAPSET 1’) CURSOR(100) ERASE END-EXEC. The cursor will be placed at FIELD 1 field of the map MAP 1 during execution. 61
Interfacing with a Terminal using a Map 1. 2. 3. The BMS maps are used in the application programs for the actual terminal input/output operation. These operations are performed by a set of CICS commands for BMS. The following are three basic functions performed by CICS commands: Map Sending function – using the data in the symbolic map, BMS prepares the output NMDS, the corresponding physical map, and sends to the terminal. Map Receiving Function – using the input NDMS from the terminal, BMS prepares data in the symbolic map through the corresponding physical map. Text Handling Function – BMS prepares text without using a map and sends to the terminal. 62
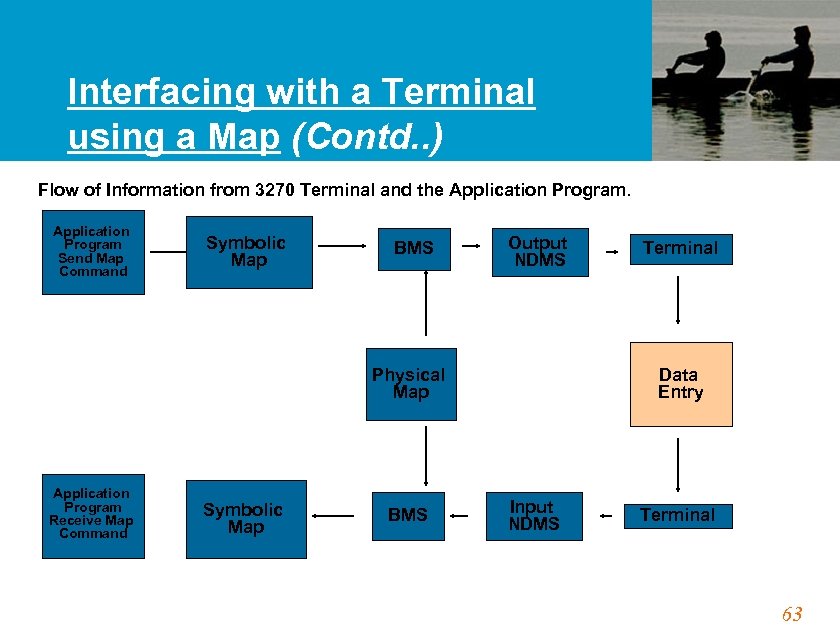
Interfacing with a Terminal using a Map (Contd. . ) Flow of Information from 3270 Terminal and the Application Program Send Map Command Symbolic Map BMS Output NDMS Physical Map Application Program Receive Map Command Symbolic Map BMS Terminal Data Entry Input NDMS Terminal 63
Interfacing with a Terminal using a Map (Contd. . ) The following are the available commands: • RECEIVE MAP : • SEND MAP : ol • SEND CONTROL : a send • SEND TEXT or • SEND PAGE accumulated text the : send : To receive a map To send a map To terminal To send a text To maps as a logical message 64
Receive Map Command RECEIVE MAP Command is used to receive input from a terminal. At the completion of the command, the symbolic map will contain valid data from the terminal in the following three fields as per each field defined by the DFHMDF macro: Field name + L Field name + F Field name + I : The length field, which contains the actual number of characters, typed in the screen field. : The Flag Byte which is normally X’ 00’. It will be X’ 80’ if the field has been modified but cleared. : The actual input data field. X’ 00’ will be placed if no data is entered. 65
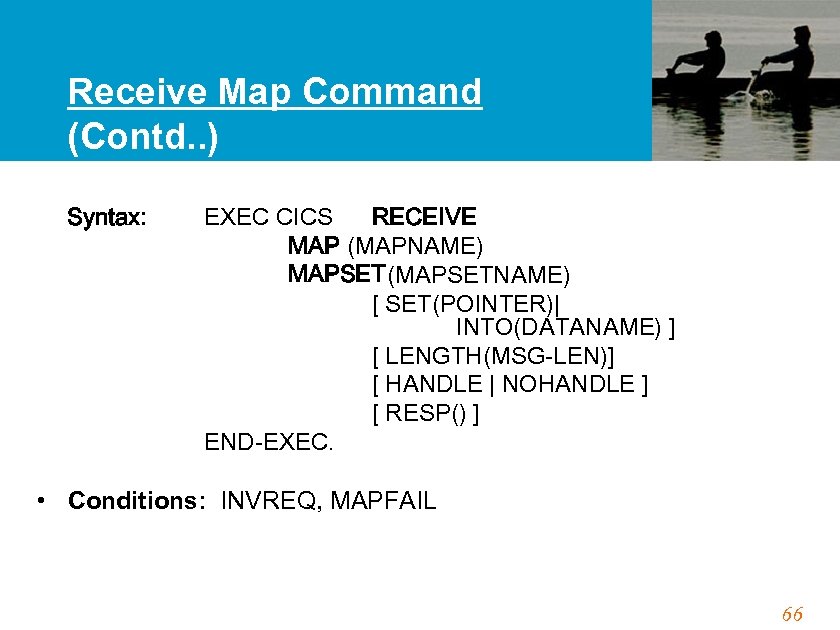
Receive Map Command (Contd. . ) Syntax: EXEC CICS RECEIVE MAP (MAPNAME) MAPSET(MAPSETNAME) [ SET(POINTER)| INTO(DATANAME) ] [ LENGTH(MSG-LEN)] [ HANDLE | NOHANDLE ] [ RESP() ] END-EXEC. • Conditions: INVREQ, MAPFAIL 66
Receive Map Command (Contd. . ) MAP specified the name of the MAP defined thru DFHMDI command , which describes the screen details. MAPSET specified the name of the MAPSET defined thru DFHMSD command which includes the MAP. INTO is used to specify the area in the working storage section to which the data from the terminal is to be placed. SET is used when the address pointer is to be set to the address of the symbolic map (by CICS) so that the application program can directly refer to the record without moving the record content into the working storage area defined in the program. 67
Receive Map Command (Contd. . ) RESP will be used by CICS to place a response code at a completion of the command. HANDLE is used to transfer control to the procedure label specified if the exceptional condition specified occurs. NOHANDLE will cause no action to be taken for any exceptional condition occurring during execution of the CICS command. Conditions : INVMPSZ , INVREQR , LENGERR, MAPFAIL is set when the data being mapped has a length of zero. It occurs when the following keys are pressed in response to the RECEIVE MAP command: CLEAR or Attention Keys & ENTER or PF keys without entering data. 68
SEND MAP Command The SEND MAP command is used to send formatted output to a terminal. Before issuing this command, the application program must prepare the data in the symbolic map of the map to be sent, which has the following three fields per each field defined by the DFHMDF macro: Name + L: The length field, for which the application program need not prepare except when used for the dynamic cursor positioning. Name + A: The Attribute byte for output fields. Application program will use it for dynamic cursor positioning. Name + O: The actual output data field, where the application program places the data. 69
![SEND MAP Command (Contd. . ) EXEC CICS SEND MAP(MAP 1) MAPSET(MAPSET 1) ] SEND MAP Command (Contd. . ) EXEC CICS SEND MAP(MAP 1) MAPSET(MAPSET 1) ]](https://present5.com/presentation/a9c3c70b8349404b8f0e3ddb641ef7e8/image-70.jpg)
SEND MAP Command (Contd. . ) EXEC CICS SEND MAP(MAP 1) MAPSET(MAPSET 1) ] [FROM(DATANAME) ], [DATAONLY] | MAPONLY], [ CURSOR(VALUE) ], [ FREEKB ] , [ ERASE ] , [ FRSET ] , [ HANDLE | NOHANDLE ] , [ RESP (DATANAME) ] END-EXEC. • Conditions : INVREQ, LENGERR 70
SEND MAP Command (Contd. . ) MAP specified the name of the MAP defined thru DFHMDI command , which describes the screen details. MAPSET specified the name of the MAPSET defined thru DFHMSD command which includes the MAPONLY is used when no data from your program is to be merged into the map. DATAONLY is used when only the data from the program is to be sent to the screen. The constants in the map are not sent. 71
SEND MAP Command (Contd. . ) FROM is used to specify the area in the working storage section from which the data is to be sent to the terminal. 72
AID KEYS First time when a transaction is initiated the application program throws the screen image on the terminal thru SEND MAP command. Once the screen appears, the AID (Attention Identifier ) Keys are being used to send the information back from the terminal to CICS to application program. CICS application program needs to trap the attention identifier keys and process various functions related to the AID keys. Salient Points • PF keys, PA keys, ENTER & CLEAR key • EIBAID in the CICS Executive Interface Block contains, recently used AID key. 73
AID KEYS (Contd. . ) • DFHAID – CICS System copybook which stores the values of the EIBAID field for the various AID keys. Flow : User hits AID key – Control goes to CICS – To Application program. EIBAID contains information about the last AID key pressed. Program compares EIBAID to the DFHAID field and performs processing logic as per the AID key pressed. • HANDLE AID establish the routines that are to be invoked when the aid is detected by a RECEIVE MAP command. Syntax : EXEC CICS HANDLE AID Option (label) END-EXEC Conditions : INVREQ 74
Screen Design Considerations Functional Screen Design • Screen layout should be similar to source where terminal users enter data. • Screen id should be placed at the top right corner of a screen. This helps at problem determination time. • Screen title and field descriptions should be self-explanatory. Instructions should be concise. 75
Screen Design Considerations (Contd. . ) • Large fields can be broken into a number of small fields. E. g. the field contact information can be split into contact numbers, email ids and postal address. • In case of repeated fields or group of fields, sequence numbers helps. • Error messages should be provided. Preferably the last few lines can be used for the error messages. 76
Screen Design Considerations User-Friendly Screen Design • Screens should be simple and friendly. • Default values in fields helps in reducing keystrokes by the users. Also, in case the user forgets to enter a field data, defaults values are assigned according to the field. • Calculations should be done by program and not by users. • The cursors should be placed in the appropriate fields. • Highlight the error field. Using a different colour or blinking the error field can achieve this. This enables users to identify the erroneous field easily. 77
Screen Design Considerations (Contd. . ) • Alarm sound can be used for error entries. • Provide suitable help messages for erroneous entries. The help message should be instructive and kind and should not be rude. • Provide help on fields and their meanings. Using an attention key for a help menu, which has details on each field, makes a screen user-friendly. Artistic Screen Design • A simple screen layout is always preferred. • Proper use of indentations, spaces, and lines makes a screen look good. 78
Screen Design Considerations (Contd. . ) • Colour can help in improving the screen design; however the colour used should be in accordance with the norms and standards followed. Considerations for Human Errors • Important and useful fields can be placed at the top part of the screen. • Related fields can be grouped together. • Protected fields should be skipped automatically. This reduces manual skipping and is preferred. • Skipper/Stopper techniques can be used at appropriate places. 79
Exercise - 1 80
CICS File Processing Techniques 81
CICS VS FILE PROCESSING • • File handling in CICS is achieved thru a set of file handling commands. It is essential to know the various file handling commands for application programming. File Specific functions to be performed are the following. Defining a specific file to the CICS system. Reading a file sequentially Reading a Key Sequenced file randomly Reading a file sequentially starting from a specific point. Reading and Updating a record Deleting a Record. Handle any errors that occur during file processing 82
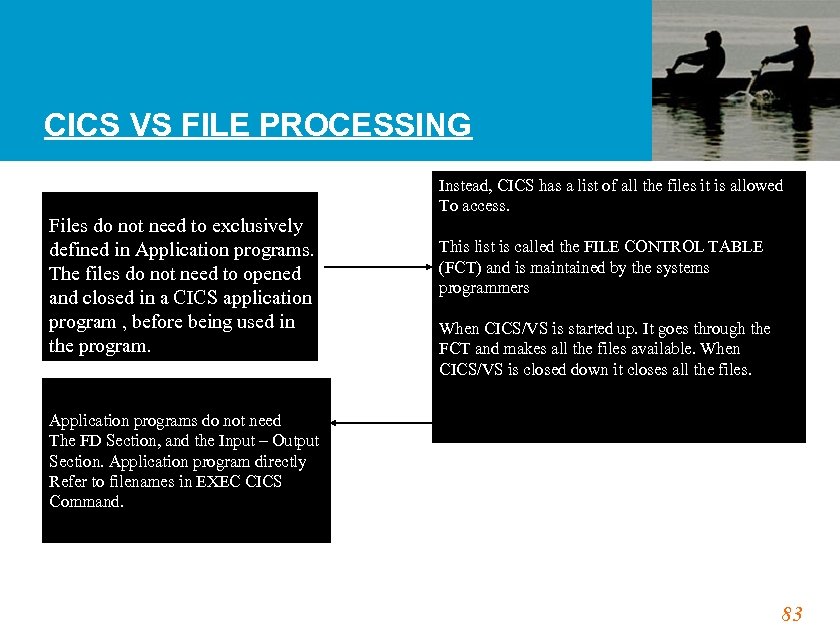
CICS VS FILE PROCESSING Files do not need to exclusively defined in Application programs. The files do not need to opened and closed in a CICS application program , before being used in the program. Instead, CICS has a list of all the files it is allowed To access. This list is called the FILE CONTROL TABLE (FCT) and is maintained by the systems programmers When CICS/VS is started up. It goes through the FCT and makes all the files available. When CICS/VS is closed down it closes all the files. Application programs do not need The FD Section, and the Input – Output Section. Application program directly Refer to filenames in EXEC CICS Command. 83
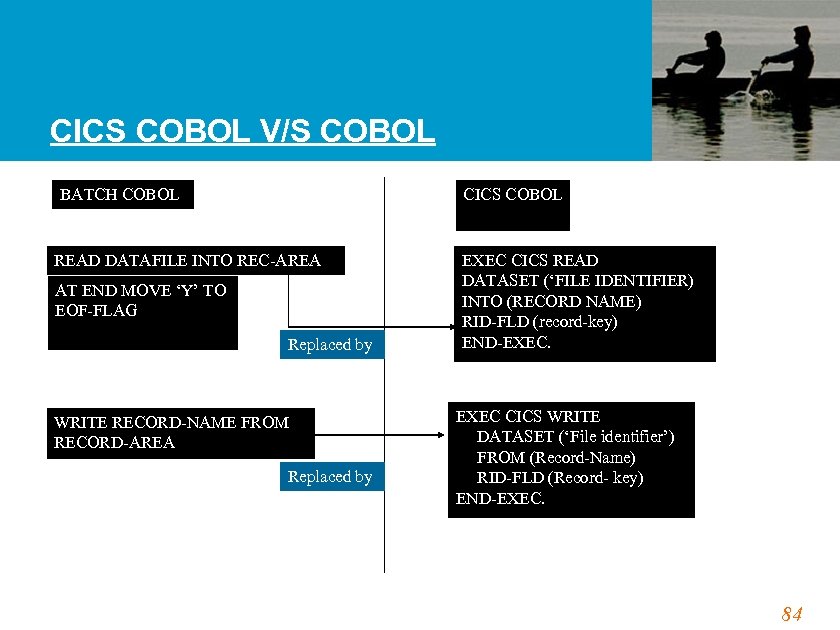
CICS COBOL V/S COBOL BATCH COBOL CICS COBOL READ DATAFILE INTO REC-AREA AT END MOVE ‘Y’ TO EOF-FLAG Replaced by WRITE RECORD-NAME FROM RECORD-AREA Replaced by EXEC CICS READ DATASET (‘FILE IDENTIFIER) INTO (RECORD NAME) RID-FLD (record-key) END-EXEC. EXEC CICS WRITE DATASET (‘File identifier’) FROM (Record-Name) RID-FLD (Record- key) END-EXEC. 84
VSAM Different types of VSAM Datasets used in CICS are : • ESDS • KSDS • RRDS Entry Sequenced Dataset Key Sequenced Dataset Relative Record Dataset 85
Services Provided By CICS • Basic Operations required for a file are Adding a Record. Modifying an Existing Record. Deleting an Existing Record. Browsing One or Selected or All Records. • In Addition, CICS Provides Exclusive Control. (Record Level Locking). Data Independence. Journaling. Opening and closing Files. 86
Defining A File in CICS • Files should be defined in FCT (File Control Table). • FCT will contain all the Information about a file (like dataset name, access methods, permissible file service request, etc. ) • Defining files can be done either by CEDA Transaction or DFHFCT Macro. 88
Syntax of DFHFCT Macro DFHFCT TYPE=FILE, ACCMETH=VSAM, DATASETNAME=NAME, SERVRQ=(ADD, BROWSE, DELETE, READ, UPDATE), FILSTAT=(ENABLED, OPENED) 89
File Handling in Programs • Files should not be defined in the Program. • Program should not open or close a File. • Records can be written in any order. A number of records can be added at a time. • Records can be inserted, updated or deleted. 90
Important Key-Words • Dataset/File : - Name in the FCT. • Into/From (WS-Rec) : - Working-Storage Area defined in the program where the CICS Puts/Gets the Data. • RIDFLD : - Contains the Record Key. • RESP : - Contains the return code of the executed command. • LENGTH : - Length of the Record to be Retrieved or Written. 91
![Random READ EXEC CICS READ File(filename) [SET() | Into()] RIdfld(Rec-Key) END-EXEC. Condition: DISABLED, NOTOPEN, Random READ EXEC CICS READ File(filename) [SET() | Into()] RIdfld(Rec-Key) END-EXEC. Condition: DISABLED, NOTOPEN,](https://present5.com/presentation/a9c3c70b8349404b8f0e3ddb641ef7e8/image-91.jpg)
Random READ EXEC CICS READ File(filename) [SET() | Into()] RIdfld(Rec-Key) END-EXEC. Condition: DISABLED, NOTOPEN, NOTFND, LENGERR, DUPKEY, IOERR. 92
Example for Random Read EXEC CICS READ File( 'INVMAS ') Into(WS-INVMAS-REC) Length(WS-INVMAS-LEN) RIdfld('7135950602') | RIdfld(WS-INVMAS-KEY) END-EXEC. 93
Sequential Read • Sequential Read is done by Browse Oper. • Establish the pointer to the First Record to be Read Using Start. Br. • Next and Previous Records can be Read as required Using Read. Next and Read. Prev. • End the Browse Operation at last. • Browse can be re-positioned. • During Browse Operation, Records cannot be Updated. 94
Syntax for STARTBR EXEC CICS STARTBR FILE(filename) RIDFLD(data-area) END-EXEC. Condition : DISABLED, IOERR, NOTFND, NOTOPEN. 95
Reading the Record after STARTBR • Sequentially the Next or Previous Record can be read by a READNEXT or READPREV. • The first READNEXT or READPREV will read the Record where the STARTBR has positioned the File Pointer. 96
Syntax of READNext/READPrev EXEC CICS READNext | READPrev FILE(name) INTO(data-area)|SET(ptr-ref) RIDFLD(data-area) END-EXEC. Condition : DUPKEY, ENDFILE, IOERR, LENGERR, NOTFND. 97
ENDBRowse • ENDBRowse terminates a Previously issued STARTBR. • SYNTAX : EXEC CICS ENDBR FILE(filename) END-EXEC. Condition: INVREQ 98
RESETBR • Its effect is the same as ENDBR and then giving another STARTBR. • Syntax : EXEC CICS RESETBR FILE(filename) RIDFLD(data-area) END-EXEC. Condition: IOERR, NOTFND. 99
WRITE Command • Adds a new record into the File. • For ESDS, RIDFLD is not used but after write execution, RBA value is returned and Record will be written at the end of the File. • For KSDS, RIDFLD should be the Record Key. The record will be written depending on the Key. • MASSINSERTion must be done in ascending order of the Key. 100
Syntax for WRITE EXEC CICS WRITE FILE(filename) FROM(data-area) RIDFLD(data-area) END-EXEC. Condition: DISABLED, DUPREC, IOERR, LENGERR, NOSPACE, NOTOPEN. 101
REWRITE Command • Updates a Record which is Previously Read with UPDATE Option. • REWRITE automatically UNLOCKs the Record after execution. 102
Syntax for REWRITE EXEC CICS REWRITE FILE(filename) FROM(data-area) END-EXEC. Condition: DUPREC, IOERR, LENGERR, NOSPACE. 103
DELETE Command • Deletes a Record from a dataset. • Record can be deleted in two ways, 1. RIDFLD with the full key in it 2. The record read with READ with UPDATE will be deleted. • Multiple Records Delete is possible using Generic Option. 104
Syntax of DELETE EXEC CICS DELETE FILE(filename) RIDFLD(data-area) Optional END-EXEC. Condition: DISABLED, DUPKEY, IOERR, NOTFND, NOTOPEN. 105
UNLOCK • To Release the Record which has been locked by READ with UPDATE Command. • Syntax : EXEC CICS UNLOCK FILE(filename) : [other options] END-EXEC. Condition: DISABLED, IOERR, NOTOPEN. 106
General Exceptions • The following exceptions usually will occur for ALL CICS file handling commands. FILENOTFOUND, NOTAUTH, SYSIDERR, INVREQ 107
CICS Error Handling Procedures 108
Error Handling in CICS Possible Errors: • Conditions that aren't normal from CICS's point of view but that are expected in the program. • Conditions caused by user errors and input data errors. • Conditions caused by omissions or errors in the application code. • Errors caused by mismatches between applications and CICS tables, generation parameters and JCL • Errors related to hardware or other system conditions beyond the control of an application program. 109
Error Handling methods When the error (exceptional conditions) occur, the program can do any of the following • Take no action & let the program continue - Control returns to the next inst. following the command that has failed to execute. A return code is set in EIBRESP and EIBRCODE. This state occurs ‘cause of NO HANDLE /RESP/IGNORE conditions • Pass control to a specified label - Control goes to a label in the program defined earlier by a HANDLE CONDITION command. • Rely on the system default action - System will terminate or suspend the task depends on the exceptional condition occurred 110
![Error Handling methods (Contd. . ) • HANDLE CONDITION condition[(label)]. . . 'condition' specifies Error Handling methods (Contd. . ) • HANDLE CONDITION condition[(label)]. . . 'condition' specifies](https://present5.com/presentation/a9c3c70b8349404b8f0e3ddb641ef7e8/image-110.jpg)
Error Handling methods (Contd. . ) • HANDLE CONDITION condition[(label)]. . . 'condition' specifies the name of the condition, and 'label' specifies the location within the program to be branched • Remains active while the program is executing or until it encounters IGNORE/another HANDLE condition. • Syntax : EXEC CICS HANDLE CONDITION ERROR(ERRHANDL) LENGERR(LENGRTN) END-EXEC This example handles DUPREC condition separately, all the other Errors together. LENGERR will be handled by system 111
HANDLE Condition Example of Handle condition: EXEC CICS HANDLE CONDITION NOTFND(RECORD-NOT-FOUND) END-EXEC This condition catches the NOTFND condition and transfers control to the REC -NOT- FOUND paragraph in the program. The error handling logic can be coded in the REC-NOT-FND paragraph. 112
Alternative to Handle condition • NOHANDLE to specify “no action to be taken for any condition or attention identifier (AID) “ • RESP(xxx) "xxx" is a user-defined full word binary data area. On return from the command, it contains a return code. Later, it can be tested by means of DFHRESP as follows, If xxx=DFHRESP(NOSPACE). . . or If xxx=DFHRESP(NORMAL) . . . 113
IGNORE Condition • IGNORE CONDITION condition. . . • ‘condition’ specifies the name of the condition that is to be ignored( no action will be taken) • Syntax : EXEC CICS IGNORE CONDITION ITEMERR LENGERR END-EXEC • This command will not take any actions if the given two error occurs and will pass the control to the next instruction 114
Sample program to use Handle condition Here is an example of the CICS- COBOL code with proper handling of errors Procedure Division. EXEC CICS HANDLE CONDITION NOT-FND(REC-NOT-FOUND) END EXEC. : EXEC CICS READ DATASET(SAMPLE) RIDFLD(EMP-NO) INTO (EMP-REC) END-EXEC : GO TO LAST-PART 115
Sample program to use Handle condition (Contd. . ) REC-NOT-FOUND MOVE ‘NOT-ON-FILE’ TO NAMEO ( SYMBOLIC MAP PARAMETER) LAST-PART. EXEC CICS SEND MAP (‘TC 0 BM 31’) MAPSET(‘TC 0 BM 30’) FROM (‘TC 0 BM 310’) DATA-ONLY END-EXEC 116
PUSH & POP • To suspend all current HANDLE CONDITION, IGNORE CONDITION, HANDLE AID and HANDLE ABEND commands. • Used for eg. while calling sub-pgms (CALL). • While receiving the control, a sub-program can suspend Handle commands of the called program using PUSH HANDLE. • While returning the control, it can restore the Handle command using POP HANDLE. 117
Syntax of Push & Pop • Syntax of Push : EXEC CICS Push Handle END-EXEC. • Syntax of Pop : EXEC CICS Pop Handle END-EXEC. 118
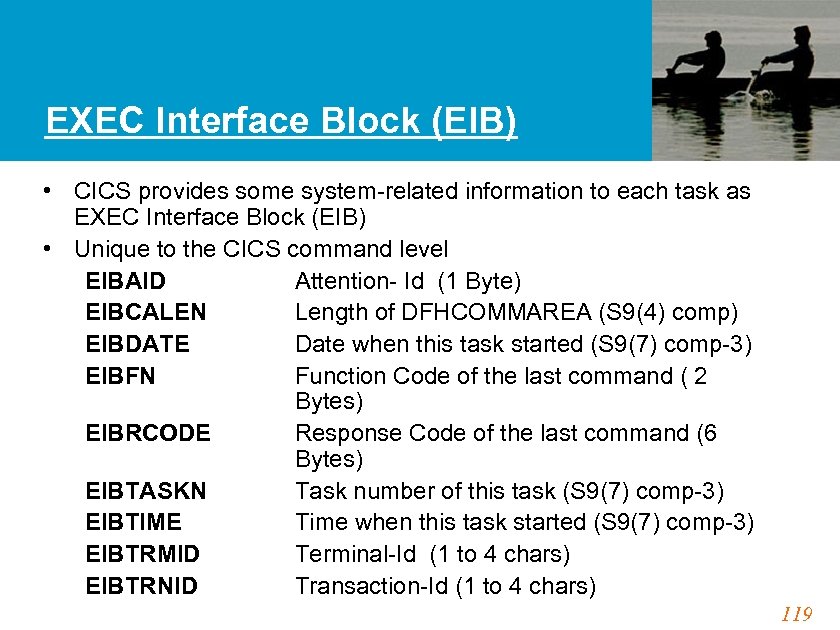
EXEC Interface Block (EIB) • CICS provides some system-related information to each task as EXEC Interface Block (EIB) • Unique to the CICS command level EIBAID Attention- Id (1 Byte) EIBCALEN Length of DFHCOMMAREA (S 9(4) comp) EIBDATE Date when this task started (S 9(7) comp-3) EIBFN Function Code of the last command ( 2 Bytes) EIBRCODE Response Code of the last command (6 Bytes) EIBTASKN Task number of this task (S 9(7) comp-3) EIBTIME Time when this task started (S 9(7) comp-3) EIBTRMID Terminal-Id (1 to 4 chars) EIBTRNID Transaction-Id (1 to 4 chars) 119
![Processing Program Table - PPT DFHPPT TYPE=ENTRY PROGRAM |MAPSET= name [PGMLANG= ASM|COBOL|PLI] [RES= NO|FIX|YES] Processing Program Table - PPT DFHPPT TYPE=ENTRY PROGRAM |MAPSET= name [PGMLANG= ASM|COBOL|PLI] [RES= NO|FIX|YES]](https://present5.com/presentation/a9c3c70b8349404b8f0e3ddb641ef7e8/image-119.jpg)
Processing Program Table - PPT DFHPPT TYPE=ENTRY PROGRAM |MAPSET= name [PGMLANG= ASM|COBOL|PLI] [RES= NO|FIX|YES] : other options : Eg. DFHPPT TYPE=ENTRY, PROGRAM=TEST, PGMLANG=COBOL 120
PCT Entry DFHPCT TYPE=ENTRY TRANSID= name PROGRAM=name TASKREQ=pf 6 RESTART=yes/no ( TRANSEC = 1 to 64) RSLKEY= 1 to 24 resource level key SCTYKEY= 1 to 64 security key : : other options 121

PROGRAM CONTROL 122
Program Control Commands • LINK • XCTL • RETURN • LOAD • RELEASE 123
LINK • Used to pass control from one application program to another • The calling program expects control to be returned to it • Data can be passed to the called program using COMMAREA • If the called program is not already in main storage it is loaded 124
![LINK Syntax EXEC CICS LINK PROGRAM(name) [COMMAREA(data-area) [LENGTH(data-value)]] END-EXEC. Conditions : PGMIDERR, NOTAUTH, LENGERR LINK Syntax EXEC CICS LINK PROGRAM(name) [COMMAREA(data-area) [LENGTH(data-value)]] END-EXEC. Conditions : PGMIDERR, NOTAUTH, LENGERR](https://present5.com/presentation/a9c3c70b8349404b8f0e3ddb641ef7e8/image-124.jpg)
LINK Syntax EXEC CICS LINK PROGRAM(name) [COMMAREA(data-area) [LENGTH(data-value)]] END-EXEC. Conditions : PGMIDERR, NOTAUTH, LENGERR 125
XCTL • To transfer control from one application program to another in the same logical level • The program from which control is transferred is released • Data can be passed to the called program using COMMAREA • If the called program is not already in main storage it is loaded 126
![XCTL Syntax EXEC CICS XCTL PROGRAM(name) [COMMAREA(data-area) [LENGTH(data-value)]] END-EXEC. Conditions : PGMIDERR, NOTAUTH, LENGERR XCTL Syntax EXEC CICS XCTL PROGRAM(name) [COMMAREA(data-area) [LENGTH(data-value)]] END-EXEC. Conditions : PGMIDERR, NOTAUTH, LENGERR](https://present5.com/presentation/a9c3c70b8349404b8f0e3ddb641ef7e8/image-126.jpg)
XCTL Syntax EXEC CICS XCTL PROGRAM(name) [COMMAREA(data-area) [LENGTH(data-value)]] END-EXEC. Conditions : PGMIDERR, NOTAUTH, LENGERR 127
RETURN • To return control from one application program to another at a higher logical level or to CICS • Data can be passed using COMMAREA when returning to CICS to the next task 128
![RETURN Syntax EXEC CICS RETURN [TRANSID(name) [COMMAREA(data-area) [LENGTH(data-value)]]] END-EXEC. Conditions : INVREQ, LENGERR 129 RETURN Syntax EXEC CICS RETURN [TRANSID(name) [COMMAREA(data-area) [LENGTH(data-value)]]] END-EXEC. Conditions : INVREQ, LENGERR 129](https://present5.com/presentation/a9c3c70b8349404b8f0e3ddb641ef7e8/image-128.jpg)
RETURN Syntax EXEC CICS RETURN [TRANSID(name) [COMMAREA(data-area) [LENGTH(data-value)]]] END-EXEC. Conditions : INVREQ, LENGERR 129
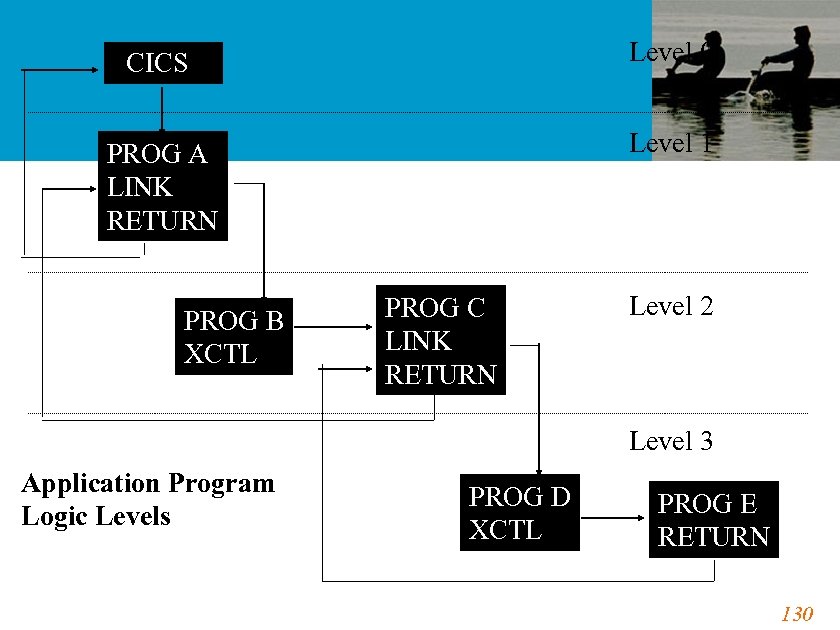
CICS Level 0 PROG A LINK RETURN Level 1 PROG B XCTL PROG C LINK RETURN Level 2 Level 3 Application Program Logic Levels PROG D XCTL PROG E RETURN 130
LOAD • To load program/table/map from the CICS DFHRPL concatenation library into the main storage • Using load reduces system overhead • Syntax : EXEC CICS Load Program(name) [SET (pointer-ref)] [LENGTH (data-area)] END-EXEC. Condition : NOTAUTH, PGMIDER 131
RELEASE • To RELEASE a loaded program/table/map • Syntax : EXEC CICS RELEASE PROGRAM(name) END-EXEC. Conditions : PGMIDERR, NOTAUTH, INVREQ 132
COMMAREA • Data passed to called program using COMMAREA in LINK and XCTL • Calling program - Working Storage definition • Called program - Linkage section definition under DFHCOMMAREA • Called program can alter data and this will automatically available in calling program after the RETURN command ( need not use COMMAREA option in the return for this purpose ) • EIBCALEN is set when COMMAREA is passed 133

Communication With Databases 134
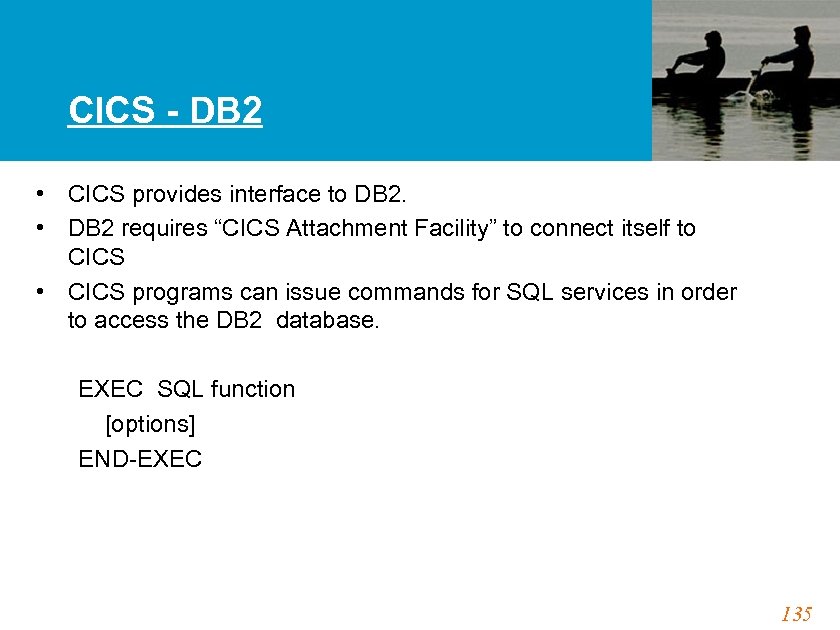
CICS - DB 2 • CICS provides interface to DB 2. • DB 2 requires “CICS Attachment Facility” to connect itself to CICS • CICS programs can issue commands for SQL services in order to access the DB 2 database. EXEC SQL function [options] END-EXEC 135
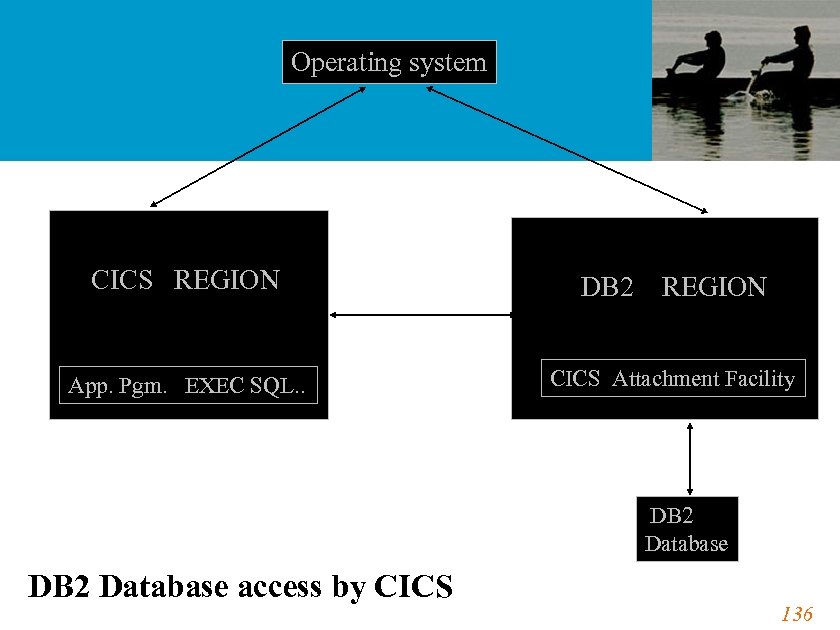
Operating system CICS REGION App. Pgm. EXEC SQL. . DB 2 REGION CICS Attachment Facility DB 2 Database access by CICS 136
RCT Entry • The CICS-to-DB 2 connection is defined by creating and assembling the resource control table (RCT) • The information in RCT is used to control the interactions between CICS & DB 2 resources • DB 2 attachment facility provides a macro (DSNCRCT) to generate the RCT. • The RCT must be link-edited into a library that is accessible to MVS 137
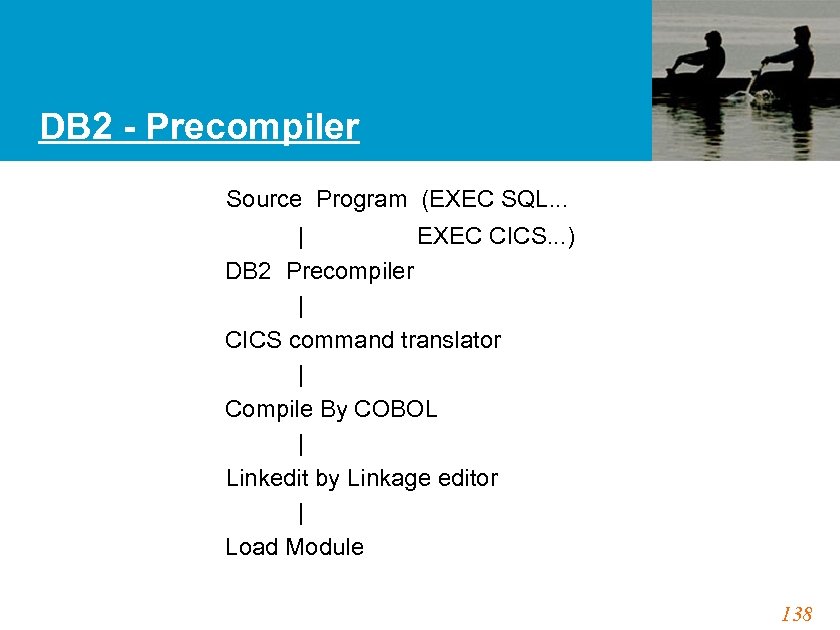
DB 2 - Precompiler Source Program (EXEC SQL. . . | EXEC CICS. . . ) DB 2 Precompiler | CICS command translator | Compile By COBOL | Linkedit by Linkage editor | Load Module 138

QUEUES 139
Transient data Control • Provides application programmer with a queuing facility • Data can be stored/queued for subsequent internal or external processing • Stored data can be routed to symbolic destinations • TDQs require a DCT entry • Identified by Destination id - 1 to 4 bytes 140
TDQs • Intra-partitioned - association within the same CICS subsystem Typical uses are - ATI (Automatic Task Initiation) associated with trigger level - Message switching - Broadcasting etc • Extra-partitioned - association external to the CICS subsystem, Can associate with any sequential device - Tape, DASD, Printer etc Typical uses are - Logging data, statistics, transaction error messages - Create files for subsequent processing by Non-CICS / Batch programs. 141
TDQs • Operations Write data to a transient data queue (WRITEQ TD) Read data from a transient data queue (READQ TD) Delete an intra partition transient data queue (DELETEQ TD). 142
![WRITEQ TD • Syntax : EXEC CICS WRITEQ TD QUEUE(name) FROM(data-area) [LENGTH(data-value)] [SYSID(systemname)] END-EXEC. WRITEQ TD • Syntax : EXEC CICS WRITEQ TD QUEUE(name) FROM(data-area) [LENGTH(data-value)] [SYSID(systemname)] END-EXEC.](https://present5.com/presentation/a9c3c70b8349404b8f0e3ddb641ef7e8/image-142.jpg)
WRITEQ TD • Syntax : EXEC CICS WRITEQ TD QUEUE(name) FROM(data-area) [LENGTH(data-value)] [SYSID(systemname)] END-EXEC. Conditions: DISABLED, INVREQ, IOERR, ISCINVREQ, LENGERR, NOSPACE, NOTAUTH, NOTOPEN, QIDERR, SYSIDERR 143
READQ TD • Reads the queue destructively - Data record not available in the queue after the read. • Syntax : EXEC CICS READQ TD QUEUE(name) {INTO(data-area) | SET(ptr-ref) } [LENGTH(data-value)] [NOSUSPEND] END-EXEC. Conditions : DISABLED, IOERR, INVREQ, ISCINVREQ, LENGERR, NOTAUTH, NOTOPEN, QBUSY, QIDERR, QZERO, SYSIDERR 144
DELETEQ TD • Deletes all entries in the queue • Syntax : EXEC CICS DELETEQ TD QUEUE(name) END-EXEC. Conditions: INVREQ, ISCINVREQ, NOTAUTH, QIDERR, SYSIDERR 145
Destination Control Table • DCT is to register the information of all TDQs • Destination Control Program (DCP) uses DCT to identify all TDQs and perform all I/O operations. • DFHDCT is a macro to define intra & extra partition TDQs TYPE=INTRA/EXTRA • REUSE option specified along with intra partition TDQ tells whether the space used by TDQ record will be removed & reused after it has been read. 146
Automatic Task Initiation • Facility through which a CICS transaction can be initiated automatically DFHDCT TYPE=INTRA DESTID=MSGS TRANSID=MSW 1 TRIGLEV=500 When the number of TDQ records reaches 500, the transaction MSW 1 will be initiated automatically • Applications Message switching & Report printing 147
Temporary Storage Control • Provides application programmer the ability to store and retrieve data in a TSQ • Application can use the TSQ like a scratch pad • TSQs are - Created and deleted dynamically - No CICS table entry required if recovery not required - Identified by Queue id - 1 to 8 bytes - Typically a combination of termid/tranid/operid • Each record in TSQ identified by relative position, called the item number 148
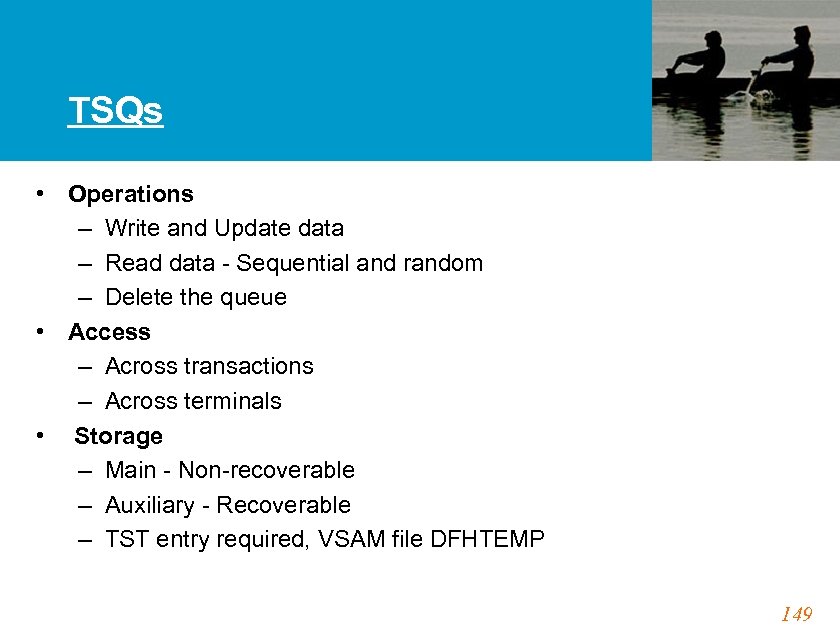
TSQs • Operations – Write and Update data – Read data - Sequential and random – Delete the queue • Access – Across transactions – Across terminals • Storage – Main - Non-recoverable – Auxiliary - Recoverable – TST entry required, VSAM file DFHTEMP 149
TSQs - Typical uses • Data passing among transactions • Terminal Paging • Report printing 150
![WRITEQ TS • Syntax : EXEC CICS WRITEQ TS QUEUE(name) FROM(data-area) [LENGTH(data-value)] [NUMITEMS(data-area) | WRITEQ TS • Syntax : EXEC CICS WRITEQ TS QUEUE(name) FROM(data-area) [LENGTH(data-value)] [NUMITEMS(data-area) |](https://present5.com/presentation/a9c3c70b8349404b8f0e3ddb641ef7e8/image-150.jpg)
WRITEQ TS • Syntax : EXEC CICS WRITEQ TS QUEUE(name) FROM(data-area) [LENGTH(data-value)] [NUMITEMS(data-area) | ITEM(data-area) [REWRITE] ] [MAIN|AUXILIARY] [NOSUSPEND] END-EXEC. Conditions : ITEMERR, LENGERR, QIDERR, NOSPACE, NOTAUTH, SYSIDERR, IOERR, INVREQ, ISCINVREQ 151
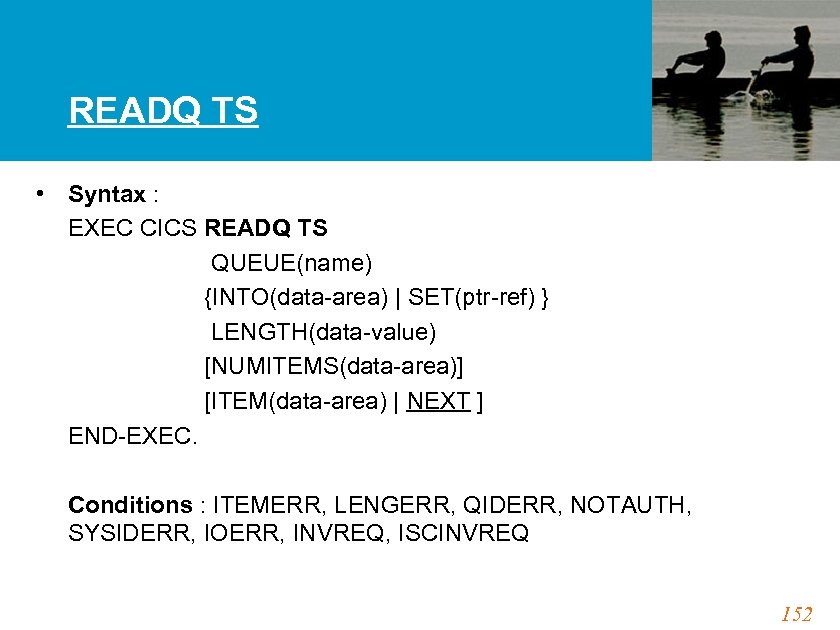
READQ TS • Syntax : EXEC CICS READQ TS QUEUE(name) {INTO(data-area) | SET(ptr-ref) } LENGTH(data-value) [NUMITEMS(data-area)] [ITEM(data-area) | NEXT ] END-EXEC. Conditions : ITEMERR, LENGERR, QIDERR, NOTAUTH, SYSIDERR, IOERR, INVREQ, ISCINVREQ 152
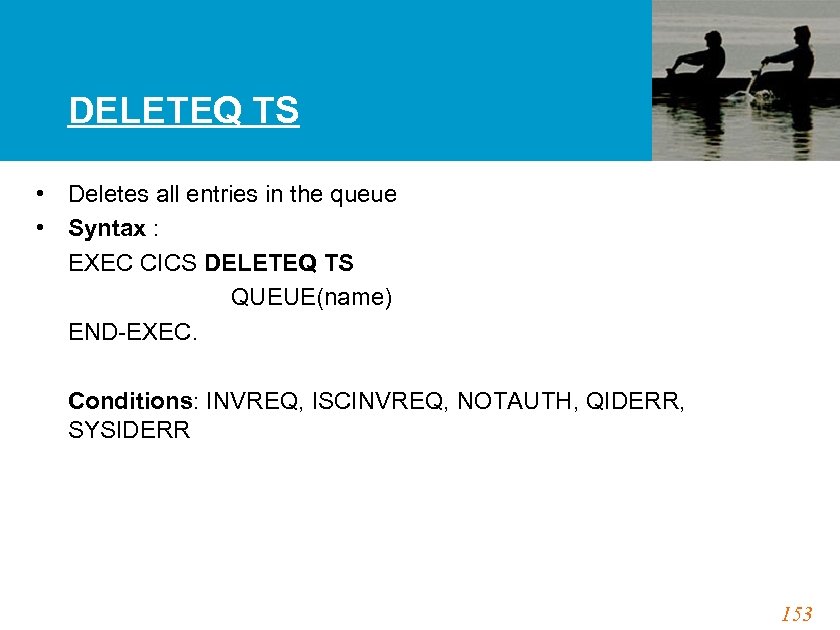
DELETEQ TS • Deletes all entries in the queue • Syntax : EXEC CICS DELETEQ TS QUEUE(name) END-EXEC. Conditions: INVREQ, ISCINVREQ, NOTAUTH, QIDERR, SYSIDERR 153

INTERVAL & TASK CONTROL 154
ASKTIME • Used to obtain current date and time • Syntax : EXEC CICS ASKTIME[ABSTIME(data-area)] END-EXEC. • EIBDATE and EIBTIME updated with current date and time • ABSTIME returns value of time in packed decimal format 155
![FORMATTIME • Syntax : EXEC CICS FORMATTIME ABSTIME(data-ref) [YYDDD(data-area)] [YYMMDD(data-area)]. . . etc. [DATE(data-area) FORMATTIME • Syntax : EXEC CICS FORMATTIME ABSTIME(data-ref) [YYDDD(data-area)] [YYMMDD(data-area)]. . . etc. [DATE(data-area)](https://present5.com/presentation/a9c3c70b8349404b8f0e3ddb641ef7e8/image-155.jpg)
FORMATTIME • Syntax : EXEC CICS FORMATTIME ABSTIME(data-ref) [YYDDD(data-area)] [YYMMDD(data-area)]. . . etc. [DATE(data-area) [DATEFORM[(data-area)]]] [DATESEP[(data-value)]] [DAYOFMONTH(data-area)] [MONTHOFYEAR(data-area)] [YEAR(data-area)]. . . [TIME(data-area) [TIMESEP[(data-value)]]] END-EXEC. Condition: INVREQ 156
DELAY • Used to DELAY the processing of a task • The issuing task is suspended for a specified interval or Until the specified time • Syntax : EXEC CICS DELAY INTERVAL(hhmmss) | TIME(hhmmss) END-EXEC Conditions: EXPIRED, INVREQ 157
START • Used to start a transaction at the specified terminal and at the specified time or interval • Data can be passed to the new transaction • Syntax : EXEC CICS START TRANSID(transid) [TERMID(termid) TIME(hhmmss) | INTERVAL(hhmmss) ] END-EXEC Conditions : INVREQ, LENGERR, TERMIDERR, TRANSIDERR 158
Other Interval Control Commands • POST - to request notification when the specified time has expired. • WAIT EVENT - to wait for an event to occur. • RETRIEVE - Used to retrieve the data passed by the START • CANCEL -Used to cancel the Interval Control requests. eg. DELAY, POST and START identified by REQID. • SUSPEND - Used to suspend a task • ENQ - to gain exclusive control over a resource • DNQ - to free the exclusive control from the resource gained by ENQ 159

Recovery & Restart 160
The Need for Recovery/Restart • The possible failures that can occur outside the CICS system are Communication failures (in online systems) Data set or database failures Application or system program failures Processor failures & Power supply failures. • Recovery/Restart facilities are required to minimize or if possible, eliminate the damage done to the online system, in case of the above failures to maintain the system & data integrity. 161
RECOVERY • An attempt to come back to where the CICS system or the transaction was when the failure occurred • Recoverable Resources VSAM files Intrapartition TDQ TSQ in the auxiliary storage DATA tables Resource definitions & System definition files 162
RESTART • To resume the operation of the CICS system or the transaction when the recovery is completed 163
Facilities for Recovery/Restart Facilities for CICS Recovery/Restart • • • Dynamic Transaction Backout Automatic Transaction Restart Resource Recovery Using System Log Resource Recovery Using Journal System Restart Extended Recovery Facility (XRF) 164
Dynamic Transaction Backout (DTB) • When the transaction fails, backing out the changes made by the transaction while the rest of the CICS system continues normally is called DTB • CICS automatically writes the ‘before image’ information of the record into the dynamic log for the duration of one LUW , the work between the two consecutive SYNC points • When an ABEND occurs, CICS automatically recovers all recoverable resources using the info. in dynamic log (Set DTB=YES in PCT) 165
LUW & SYNC point • The period between the start of a particular set of changes and the point at which they are complete is called a logical unit of work - LUW • The end of a logical unit of work is indicated to CICS by a synchronization point (sync pt). • Intermediate SYNC pt. can be done by • Syntax : EXEC CICS SYNCPOINT [ROLLBACK] END-EXEC 166
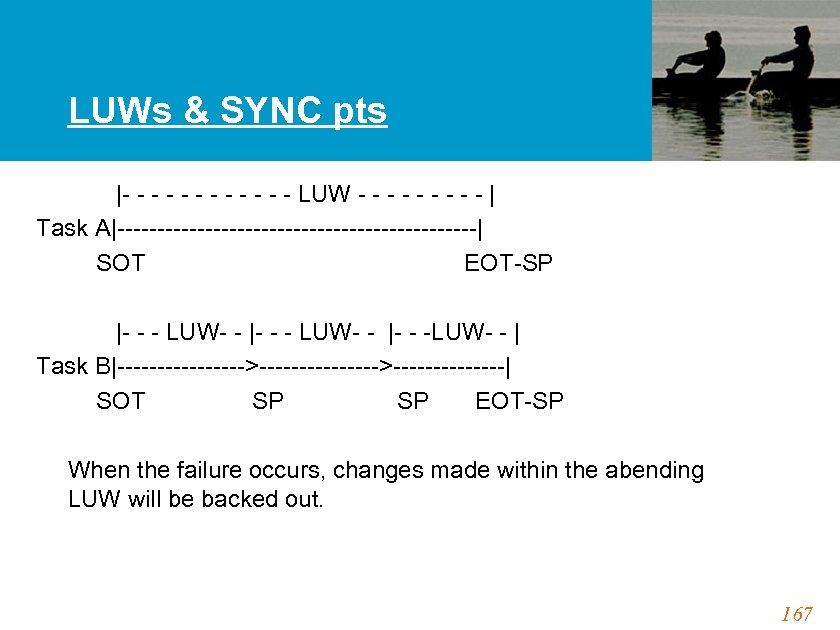
LUWs & SYNC pts |- - - LUW - - - - - | Task A|-----------------------| SOT EOT-SP |- - - LUW- - |- - -LUW- - | Task B|-------->-------->-------| SOT SP EOT-SP When the failure occurs, changes made within the abending LUW will be backed out. 167
Automatic Transaction Restart • CICS capability to automatically restart a transaction after all resources are recovered through DTB • If the transaction requires automatic restart facility, set RESTART=YES in PCT • Care should be taken in order to restart the task at the point where DTB completes in the case of intermediate SYNC point 168

Program Preparation 169
Introduction • Preparing a Program to run in CICS Environment. • Defining the Program in the CICS Region. • Executing the Program. 170
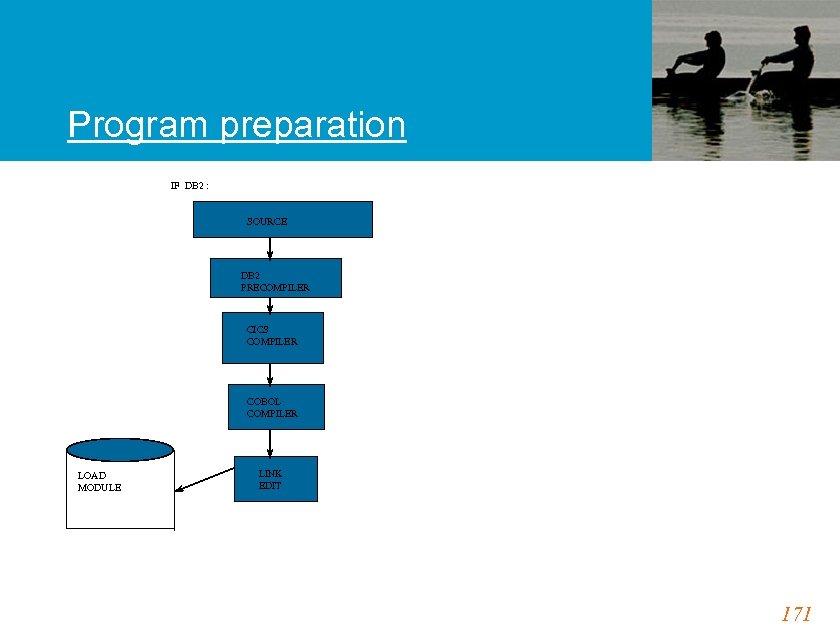
Program preparation IF DB 2 : SOURCE DB 2 PRECOMPILER CICS COMPILER COBOL COMPILER LOAD MODULE LINK EDIT 171
Preparing a Program CICS requires the following steps to prepare a program • Translating the Program. • Assemble or Compile the Translator Output. & • Link the Program. 172
Translation • Translates the ‘EXEC CICS’ Statements into the Statements your Language (COBOL) Compiler can Understand. • The Translator gives two outputs, a Program Listing as SYSPRINT and a Translated Source in SYSPUNCH. • The SYSPUNCH is given as the input to the Program Compiler. • If any Copy Books are used in the Program, there should not be any CICS Statements in the Copy Book. 173
Compiling or Linking • As the CICS Commands have been translated, the compilation of the CICS program is the same as language program. • Hence, the compiler options can be specified as required. 174
Defining the Program • The Application should be defined and installed into the PPT. • This can be done either by using CEDA trans or DFHPPT. 175

CICS Supplied Transactions 176
![CESN/CESF Transactions • To sign on to CICS system • CESN [USERID=userid] [, PS=password] CESN/CESF Transactions • To sign on to CICS system • CESN [USERID=userid] [, PS=password]](https://present5.com/presentation/a9c3c70b8349404b8f0e3ddb641ef7e8/image-176.jpg)
CESN/CESF Transactions • To sign on to CICS system • CESN [USERID=userid] [, PS=password] [, NEWPS=newpassword][, LANGUAGE=l] • Userid & password values can be from 1 -8 chars. • In RACF, the Userid given in CESN is verified. • NEWPS to change the password and LANGUAGE to choose national language • Sign off by CESF which breaks the connection between the user and CICS • If the Sign on is done twice for the same userid at the terminal, the previous operator will be signed off 177
CECI - Command Level Interpreter • To build and test the effect of EXEC CICS commands • CECI ASSIGN is used to get the current userid, sysid, terminal id, application id etc. . • Before using the maps in programs, it can be tested using CECI to check how it appears on the screen. • CECI gives the complete command syntax of the specified command. • CECI READQ TD QUEUE(TESTL 001) will read the current record of the given TDQ 178
CEMT-Master Terminal Transaction CEMT provides the following services • • Displays the status of CICS & system resources Alter the status of CICS & system resources Remove the installed resource definitions Perform few functions that are not related to resources 179
![CEDF-Execution Diagnostic Facility • To test command level application programs interactively • CEDF [termid/sysid/sessionid] CEDF-Execution Diagnostic Facility • To test command level application programs interactively • CEDF [termid/sysid/sessionid]](https://present5.com/presentation/a9c3c70b8349404b8f0e3ddb641ef7e8/image-179.jpg)
CEDF-Execution Diagnostic Facility • To test command level application programs interactively • CEDF [termid/sysid/sessionid] [, ON/, OFF] • Termid - the identifier of the terminal on which the transaction to be tested is being run • Sessionid - To test/monitor a transaction attached across an MRO/ISC session • Sysid - To test a transaction across an APPC session 180
CEDF (Contd. . ) The points at which EDF interrupts execution of the program and sends a display to the terminal • At transaction initialization, after EIB has been initialized and before the app. pgm given control • Start of execution of each CICS command (auguement values can be changed at this point) • End of execution of each CICS command before the Handle condition mechanism is invoked (response code values can be changed) • At program termination & at normal task termination • When an ABEND occurs & at abnormal task termination. • EIB values can be changed. . & CEBR can be invoked 181
CEBR-Temporary Storage Browse • To browse the contents of CICS temporary storage queues (TSQ) • CEBR by default will show the queue associated with the current terminal ‘CEBRL 001’ which can be overridden to view any other queue • TERM to browse TSQ for another terminal • QUEUE to make the named queue, current • PUT to copy the current queue contents into TDQ • GET to fetch TDQ for browsing • PURGE erases the contents of the current queue 182
Exercise - 2 183

Thank You 184
a9c3c70b8349404b8f0e3ddb641ef7e8.ppt