919db69fe5f999c99a67f4d2182f9474.ppt
- Количество слайдов: 17
Chapter 9 Information Systems Controls for System Reliability— Part 2: Confidentiality and Privacy Copyright © 2012 Pearson Education, Inc. publishing as Prentice Hall 9 -
Learning Objectives Identify and explain controls designed to protect the confidentiality of sensitive corporate information. Identify and explain controls designed to protect the privacy of customers’ personal information. Explain how the two basic types of encryption systems work. Copyright © 2012 Pearson Education, Inc. publishing as Prentice Hall 9 -2
Trust Services Framework Security (Chapter 8) Access to the system and its data is controlled and restricted to legitimate users. Confidentiality (Chapter 8) Sensitive organizational information (e. g. , marketing plans, trade secrets) is protected from unauthorized disclosure. Privacy Personal information about customers is collected, used, disclosed, and maintained only in compliance with internal policies and external regulatory requirements and is protected from unauthorized disclosure. Processing Integrity (Chapter 10) Data are processed accurately, completely, in a timely manner, and only with proper authorization. Availability (Chapter 10) System and its information are available to meet operational and contractual obligations. 9 -3
Intellectual Property (IP) Strategic plans Trade secrets Cost information Legal documents Process improvements All need to be secured Copyright © 2012 Pearson Education, Inc. publishing as Prentice Hall 9 -4
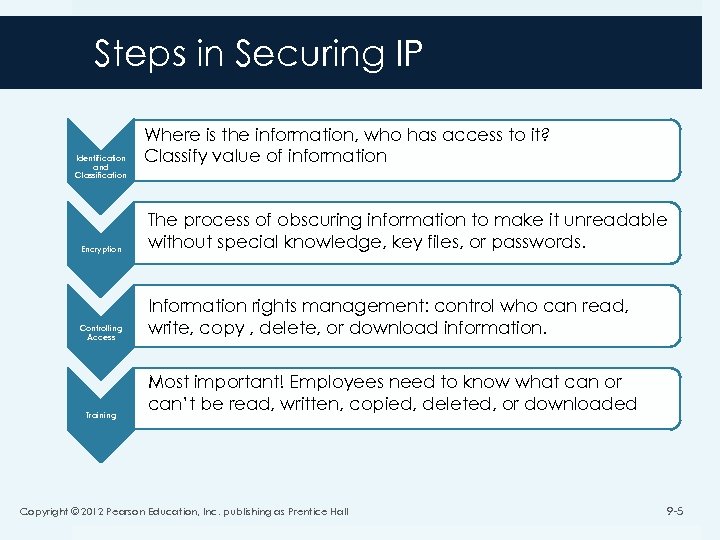
Steps in Securing IP Identification and Classification Where is the information, who has access to it? Classify value of information Encryption The process of obscuring information to make it unreadable without special knowledge, key files, or passwords. Controlling Access Information rights management: control who can read, write, copy , delete, or download information. Training Most important! Employees need to know what can or can’t be read, written, copied, deleted, or downloaded Copyright © 2012 Pearson Education, Inc. publishing as Prentice Hall 9 -5
Privacy Deals with protecting customer information vs. internal company information Same controls Identification and classification Encryption Access control Training Copyright © 2012 Pearson Education, Inc. publishing as Prentice Hall 9 -6
Privacy Concerns SPAM Unsolicited e-mail that contains either advertising or offensive content CAN-SPAM (2003) Criminal and civil penalties for spamming Identity Theft The unauthorized use of someone’s personal information for the perpetrator’s benefit. Companies have access to and thus must control customer’s personal information. Copyright © 2012 Pearson Education, Inc. publishing as Prentice Hall 9 -7
Privacy Regulatory Acts Health Insurance Portability and Accountability Act (HIPAA) Health Information Technology for Economic and Clinical Health Act (HITECH) Financial Services Modernization Act Copyright © 2012 Pearson Education, Inc. publishing as Prentice Hall 9 -8
Generally Accepted Privacy Principles 1. Management Procedures and policies Assignment of responsibility 2. Notice To customers of policies 3. Choice and Consent Allow customers consent over information provided, stored 4. Collection Only what is necessary and stated in policy 5. Use and Retention Based on policy and only for as long as needed for the business 9 -9
Generally Accepted Privacy Principles 6. Access Customers should be capable of reviewing, editing, deleting information 7. Disclosure to 3 rd Parties Based on policy and only if 3 rd party has same privacy policy standard 8. Security Protection of personal information 9. Quality Allow customer review Information needs to be reasonably accurate 10. Monitor and Enforce Ensure compliance with policy 10
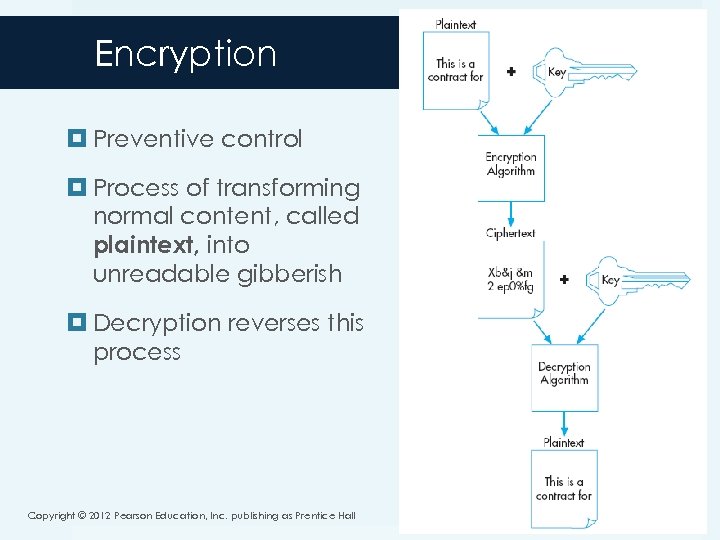
Encryption Preventive control Process of transforming normal content, called plaintext, into unreadable gibberish Decryption reverses this process Copyright © 2012 Pearson Education, Inc. publishing as Prentice Hall 9 -11
Encryption Strength Key length Number of bits (characters) used to convert text into blocks 256 is common Algorithm Manner in which key and text is combined to create scrambled text Policies concerning encryption keys Stored securely with strong access codes Copyright © 2012 Pearson Education, Inc. publishing as Prentice Hall 9 -12
Types of Encryption Symmetric One key used to both encrypt and decrypt Pro: fast Con: vulnerable Asymmetric Different key used to encrypt than to decrypt Pro: very secure Con: very slow Hybrid Solution Use symmetric for encrypting information Use asymmetric for encrypting symmetric key for decryption 9 -13
Hashing Converts information into a “hashed” code of fixed length. The code can not be converted back to the text. If any change is made to the information the hash code will change, thus enabling verification of information. Copyright © 2012 Pearson Education, Inc. publishing as Prentice Hall 9 -14
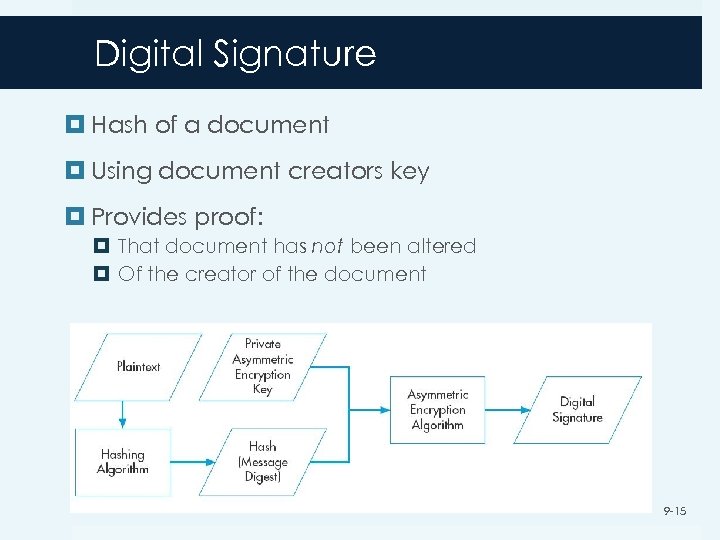
Digital Signature Hash of a document Using document creators key Provides proof: That document has not been altered Of the creator of the document 9 -15
Digital Certificate Electronic document that contains an entity’s public key Certifies the identity of the owner of that particular public key Issued by Certificate Authority Copyright © 2012 Pearson Education, Inc. publishing as Prentice Hall 9 -16
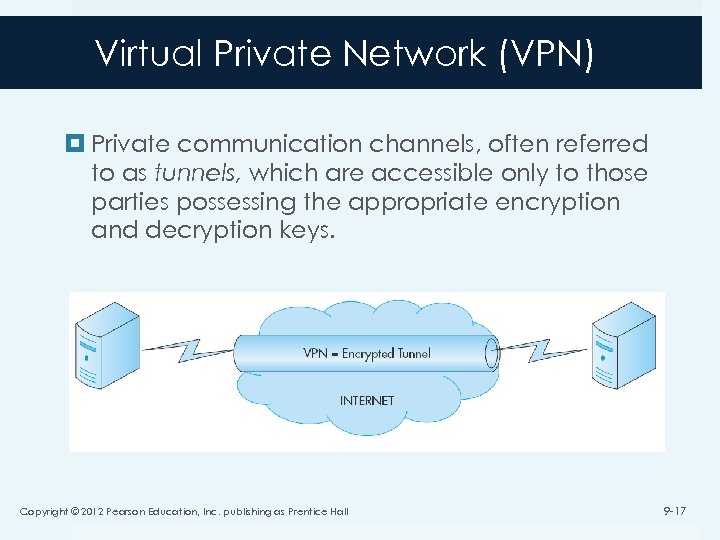
Virtual Private Network (VPN) Private communication channels, often referred to as tunnels, which are accessible only to those parties possessing the appropriate encryption and decryption keys. Copyright © 2012 Pearson Education, Inc. publishing as Prentice Hall 9 -17
919db69fe5f999c99a67f4d2182f9474.ppt