b549f735156a18b00bbbcb597e525efe.ppt
- Количество слайдов: 95
 Chapter 5: Data. Link Layer Course on Computer Communication and Networks, CTH/GU The slides are adaptation of the slides made available by the authors of the course’s main textbook Computer Networking: A Top Down Approach 4 th edition. Jim Kurose, Keith Ross Addison-Wesley, July 2007. 5: Data. Link Layer 5 -1
Chapter 5: Data. Link Layer Course on Computer Communication and Networks, CTH/GU The slides are adaptation of the slides made available by the authors of the course’s main textbook Computer Networking: A Top Down Approach 4 th edition. Jim Kurose, Keith Ross Addison-Wesley, July 2007. 5: Data. Link Layer 5 -1
 Chapter 5: The Data Link Layer data-link layer has responsibility of transferring frames from one node to adjacent node over a link Our goals: r understand principles behind data link layer services: m m error detection, correction sharing a broadcast channel: multiple access link layer addressing reliable data transfer, flow control: done! r instantiation and implementation of various link layer technologies 5: Data. Link Layer 5 -2
Chapter 5: The Data Link Layer data-link layer has responsibility of transferring frames from one node to adjacent node over a link Our goals: r understand principles behind data link layer services: m m error detection, correction sharing a broadcast channel: multiple access link layer addressing reliable data transfer, flow control: done! r instantiation and implementation of various link layer technologies 5: Data. Link Layer 5 -2
 Link Layer r 5. 1 Introduction and r r r services Framing 5. 2 Error detection and correction 5. 3 Multiple access protocols 5. 4 Link-Layer Addressing 5. 5 Ethernet r 5. 6 Hubs and switches r 5. 7 PPP r (5. 8 Link Virtualization: ATM and MPLS) 5: Data. Link Layer 5 -3
Link Layer r 5. 1 Introduction and r r r services Framing 5. 2 Error detection and correction 5. 3 Multiple access protocols 5. 4 Link-Layer Addressing 5. 5 Ethernet r 5. 6 Hubs and switches r 5. 7 PPP r (5. 8 Link Virtualization: ATM and MPLS) 5: Data. Link Layer 5 -3
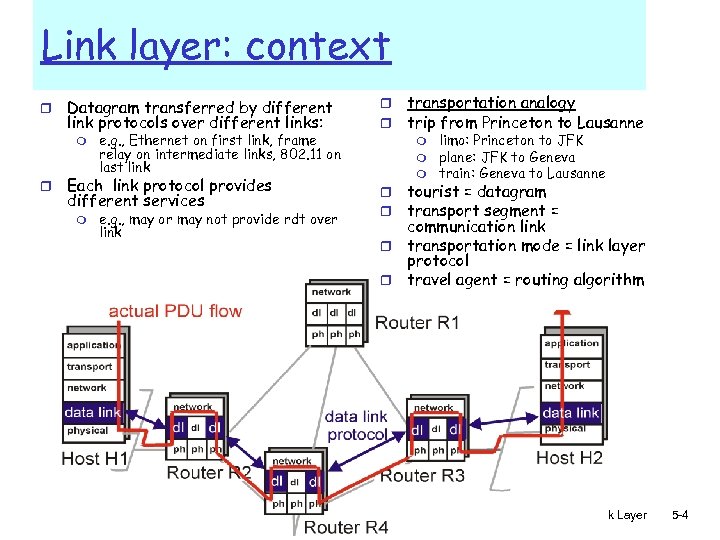 Link layer: context r Datagram transferred by different link protocols over different links: m r e. g. , Ethernet on first link, frame relay on intermediate links, 802. 11 on last link Each link protocol provides different services m e. g. , may or may not provide rdt over link r r transportation analogy trip from Princeton to Lausanne m m m limo: Princeton to JFK plane: JFK to Geneva train: Geneva to Lausanne tourist = datagram transport segment = communication link r transportation mode = link layer protocol r travel agent = routing algorithm r r 5: Data. Link Layer 5 -4
Link layer: context r Datagram transferred by different link protocols over different links: m r e. g. , Ethernet on first link, frame relay on intermediate links, 802. 11 on last link Each link protocol provides different services m e. g. , may or may not provide rdt over link r r transportation analogy trip from Princeton to Lausanne m m m limo: Princeton to JFK plane: JFK to Geneva train: Geneva to Lausanne tourist = datagram transport segment = communication link r transportation mode = link layer protocol r travel agent = routing algorithm r r 5: Data. Link Layer 5 -4
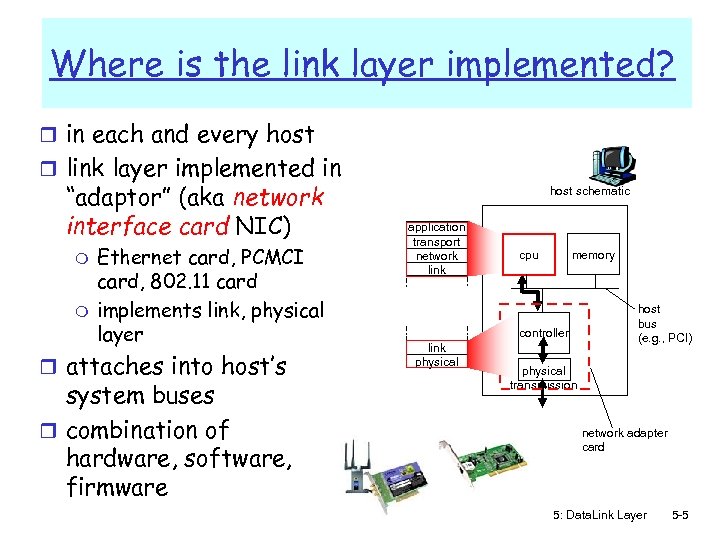 Where is the link layer implemented? r in each and every host r link layer implemented in “adaptor” (aka network interface card NIC) m m Ethernet card, PCMCI card, 802. 11 card implements link, physical layer r attaches into host’s system buses r combination of hardware, software, firmware host schematic application transport network link cpu memory controller link physical host bus (e. g. , PCI) physical transmission network adapter card 5: Data. Link Layer 5 -5
Where is the link layer implemented? r in each and every host r link layer implemented in “adaptor” (aka network interface card NIC) m m Ethernet card, PCMCI card, 802. 11 card implements link, physical layer r attaches into host’s system buses r combination of hardware, software, firmware host schematic application transport network link cpu memory controller link physical host bus (e. g. , PCI) physical transmission network adapter card 5: Data. Link Layer 5 -5
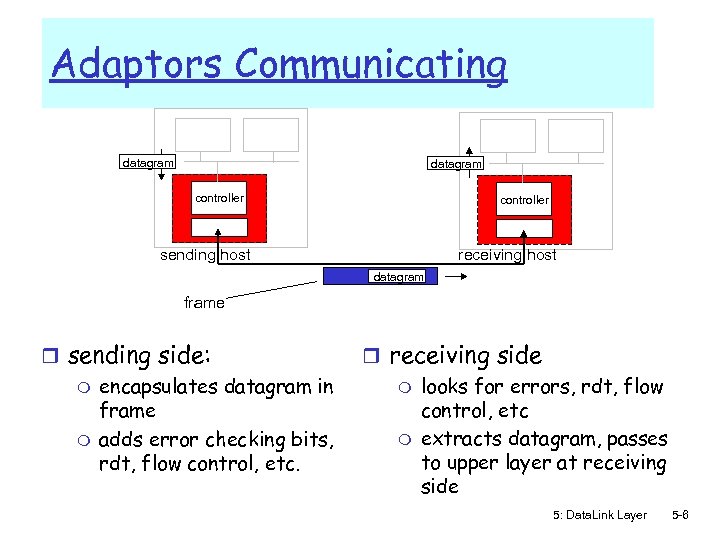 Adaptors Communicating datagram controller receiving host sending host datagram frame r sending side: m encapsulates datagram in frame m adds error checking bits, rdt, flow control, etc. r receiving side m looks for errors, rdt, flow control, etc m extracts datagram, passes to upper layer at receiving side 5: Data. Link Layer 5 -6
Adaptors Communicating datagram controller receiving host sending host datagram frame r sending side: m encapsulates datagram in frame m adds error checking bits, rdt, flow control, etc. r receiving side m looks for errors, rdt, flow control, etc m extracts datagram, passes to upper layer at receiving side 5: Data. Link Layer 5 -6
 Link Layer Services r Framing, link access: m encapsulate datagram into frame, adding header, trailer m channel access if shared medium m “MAC” addresses used in frame headers to identify source, dest • different from IP address! r Reliable delivery between adjacent nodes, flow ctrl m we learned how to do this already (chapter 3)! m seldom used on low bit error link (fiber, some twisted pair) m wireless links: high error rates • Q: why both link-level and end-end reliability? 5: Data. Link Layer 5 -7
Link Layer Services r Framing, link access: m encapsulate datagram into frame, adding header, trailer m channel access if shared medium m “MAC” addresses used in frame headers to identify source, dest • different from IP address! r Reliable delivery between adjacent nodes, flow ctrl m we learned how to do this already (chapter 3)! m seldom used on low bit error link (fiber, some twisted pair) m wireless links: high error rates • Q: why both link-level and end-end reliability? 5: Data. Link Layer 5 -7
 Link Layer Services (more) r Flow Control: m pacing between adjacent sending and receiving nodes (also learned ch. 3) r Error Detection: m errors caused by signal attenuation, noise. m receiver detects presence of errors: • signals sender for retransmission or drops frame r Error Correction: m receiver identifies and corrects bit error(s) without resorting to retransmission 5: Data. Link Layer 5 -8
Link Layer Services (more) r Flow Control: m pacing between adjacent sending and receiving nodes (also learned ch. 3) r Error Detection: m errors caused by signal attenuation, noise. m receiver detects presence of errors: • signals sender for retransmission or drops frame r Error Correction: m receiver identifies and corrects bit error(s) without resorting to retransmission 5: Data. Link Layer 5 -8
 Link Layer r 5. 1 Introduction and r r r services Framing 5. 2 Error detection and correction 5. 3 Multiple access protocols 5. 4 Link-Layer Addressing 5. 5 Ethernet r 5. 6 Hubs and switches r 5. 7 PPP r 5. 8 Virtualization 5: Data. Link Layer 5 -9
Link Layer r 5. 1 Introduction and r r r services Framing 5. 2 Error detection and correction 5. 3 Multiple access protocols 5. 4 Link-Layer Addressing 5. 5 Ethernet r 5. 6 Hubs and switches r 5. 7 PPP r 5. 8 Virtualization 5: Data. Link Layer 5 -9
 Framing r to detect possible bit stream errors in the physical layer, the data link layer groups bits from the network layer into discrete frames where a checksum could be applied r the receiver must be able to detect the beginning and the end of the frame Example methods: r Clock-based + Character count : physical-clock synchronization: much dependent on clock drifts + the counter could be garbled up during transmission 5: Data. Link Layer 5 -10
Framing r to detect possible bit stream errors in the physical layer, the data link layer groups bits from the network layer into discrete frames where a checksum could be applied r the receiver must be able to detect the beginning and the end of the frame Example methods: r Clock-based + Character count : physical-clock synchronization: much dependent on clock drifts + the counter could be garbled up during transmission 5: Data. Link Layer 5 -10
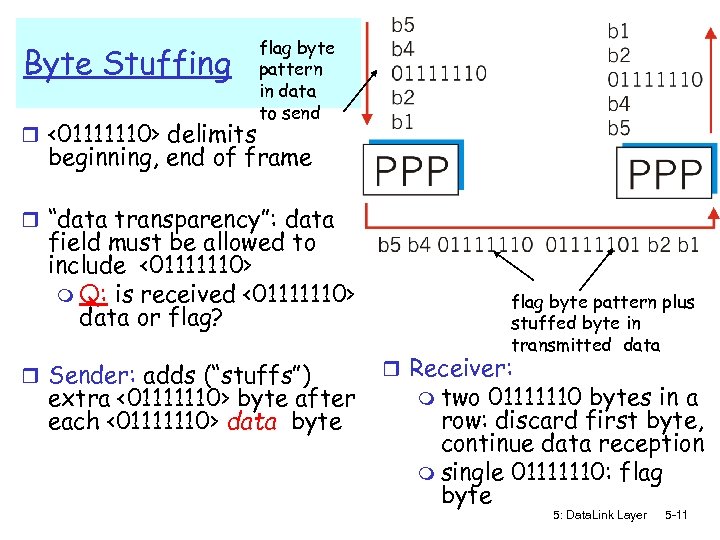 Byte Stuffing r <01111110> delimits flag byte pattern in data to send beginning, end of frame r “data transparency”: data field must be allowed to include <01111110> m Q: is received <01111110> data or flag? r Sender: adds (“stuffs”) extra <01111110> byte after each <01111110> data byte flag byte pattern plus stuffed byte in transmitted data r Receiver: m two 01111110 bytes in a row: discard first byte, continue data reception m single 01111110: flag byte 5: Data. Link Layer 5 -11
Byte Stuffing r <01111110> delimits flag byte pattern in data to send beginning, end of frame r “data transparency”: data field must be allowed to include <01111110> m Q: is received <01111110> data or flag? r Sender: adds (“stuffs”) extra <01111110> byte after each <01111110> data byte flag byte pattern plus stuffed byte in transmitted data r Receiver: m two 01111110 bytes in a row: discard first byte, continue data reception m single 01111110: flag byte 5: Data. Link Layer 5 -11
 Framing techniques: examples (cont). . . Physical layer coding violation: exploits special encodings at the physical layer, e. g. Manchester encoding (see next …) 5: Data. Link Layer 5 -12
Framing techniques: examples (cont). . . Physical layer coding violation: exploits special encodings at the physical layer, e. g. Manchester encoding (see next …) 5: Data. Link Layer 5 -12
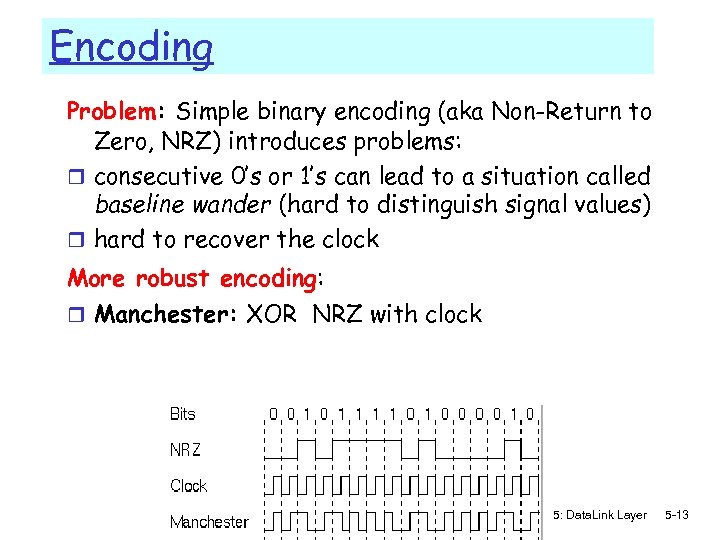 Encoding Problem: Simple binary encoding (aka Non-Return to Zero, NRZ) introduces problems: r consecutive 0’s or 1’s can lead to a situation called baseline wander (hard to distinguish signal values) r hard to recover the clock More robust encoding: r Manchester: XOR NRZ with clock 5: Data. Link Layer 5 -13
Encoding Problem: Simple binary encoding (aka Non-Return to Zero, NRZ) introduces problems: r consecutive 0’s or 1’s can lead to a situation called baseline wander (hard to distinguish signal values) r hard to recover the clock More robust encoding: r Manchester: XOR NRZ with clock 5: Data. Link Layer 5 -13
 Link Layer r 5. 1 Introduction and r r r services Framing 5. 2 Error detection and correction 5. 3 Multiple access protocols 5. 4 Link-Layer Addressing 5. 5 Ethernet r 5. 6 Hubs and switches r 5. 7 PPP r 5. 8 virtualization 5: Data. Link Layer 5 -14
Link Layer r 5. 1 Introduction and r r r services Framing 5. 2 Error detection and correction 5. 3 Multiple access protocols 5. 4 Link-Layer Addressing 5. 5 Ethernet r 5. 6 Hubs and switches r 5. 7 PPP r 5. 8 virtualization 5: Data. Link Layer 5 -14
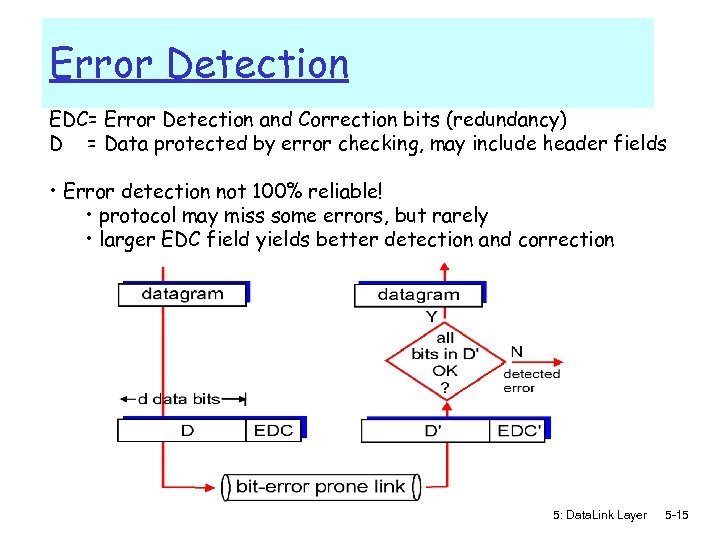 Error Detection EDC= Error Detection and Correction bits (redundancy) D = Data protected by error checking, may include header fields • Error detection not 100% reliable! • protocol may miss some errors, but rarely • larger EDC field yields better detection and correction 5: Data. Link Layer 5 -15
Error Detection EDC= Error Detection and Correction bits (redundancy) D = Data protected by error checking, may include header fields • Error detection not 100% reliable! • protocol may miss some errors, but rarely • larger EDC field yields better detection and correction 5: Data. Link Layer 5 -15
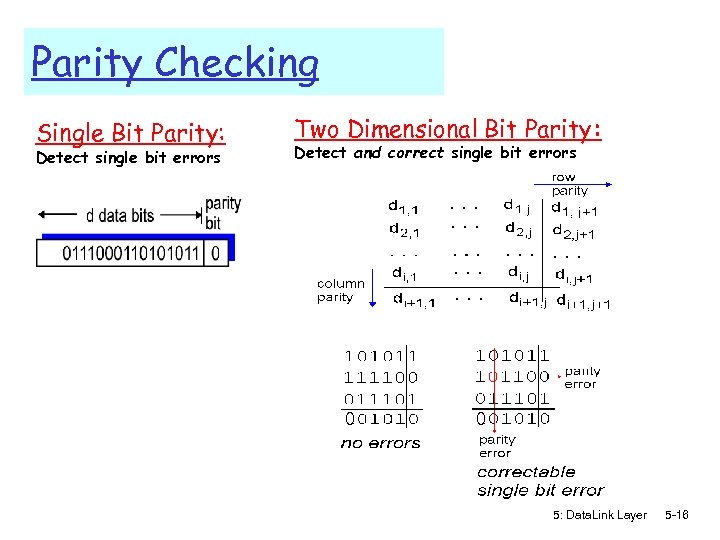 Parity Checking Single Bit Parity: Detect single bit errors Two Dimensional Bit Parity: Detect and correct single bit errors 0 0 5: Data. Link Layer 5 -16
Parity Checking Single Bit Parity: Detect single bit errors Two Dimensional Bit Parity: Detect and correct single bit errors 0 0 5: Data. Link Layer 5 -16
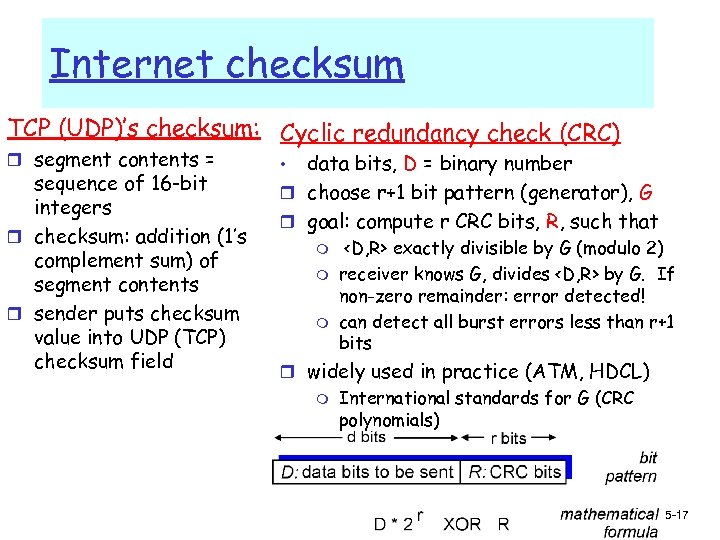 Internet checksum TCP (UDP)’s checksum: Cyclic redundancy check (CRC) r segment contents = sequence of 16 -bit integers r checksum: addition (1’s complement sum) of segment contents r sender puts checksum value into UDP (TCP) checksum field data bits, D = binary number r choose r+1 bit pattern (generator), G r goal: compute r CRC bits, R, such that • m m m
Internet checksum TCP (UDP)’s checksum: Cyclic redundancy check (CRC) r segment contents = sequence of 16 -bit integers r checksum: addition (1’s complement sum) of segment contents r sender puts checksum value into UDP (TCP) checksum field data bits, D = binary number r choose r+1 bit pattern (generator), G r goal: compute r CRC bits, R, such that • m m m
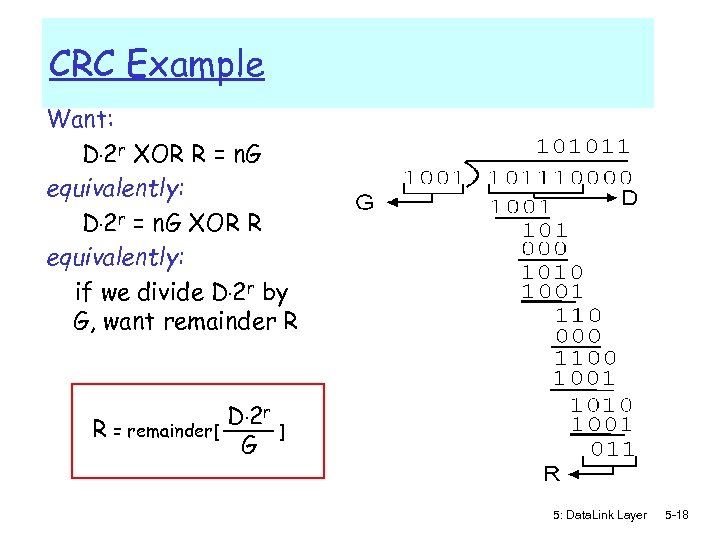 CRC Example Want: D. 2 r XOR R = n. G equivalently: D. 2 r = n. G XOR R equivalently: if we divide D. 2 r by G, want remainder R R = remainder[ D. 2 r G ] 5: Data. Link Layer 5 -18
CRC Example Want: D. 2 r XOR R = n. G equivalently: D. 2 r = n. G XOR R equivalently: if we divide D. 2 r by G, want remainder R R = remainder[ D. 2 r G ] 5: Data. Link Layer 5 -18
 Link Layer r 5. 1 Introduction and r r r services Framing 5. 2 Error detection and correction 5. 3 Multiple access protocols 5. 4 Link-Layer Addressing 5. 5 Ethernet r 5. 6 Hubs and switches r 5. 7 PPP r 5. 8 Virtualization 5: Data. Link Layer 5 -19
Link Layer r 5. 1 Introduction and r r r services Framing 5. 2 Error detection and correction 5. 3 Multiple access protocols 5. 4 Link-Layer Addressing 5. 5 Ethernet r 5. 6 Hubs and switches r 5. 7 PPP r 5. 8 Virtualization 5: Data. Link Layer 5 -19
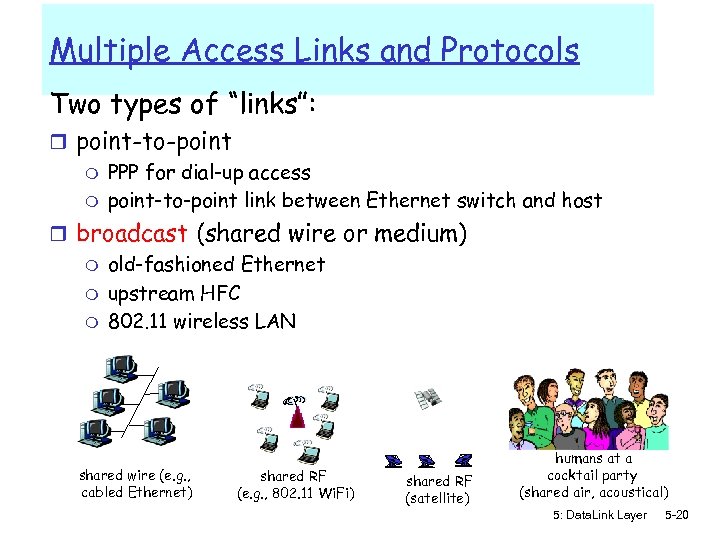 Multiple Access Links and Protocols Two types of “links”: r point-to-point m PPP for dial-up access m point-to-point link between Ethernet switch and host r broadcast (shared wire or medium) m old-fashioned Ethernet m upstream HFC m 802. 11 wireless LAN shared wire (e. g. , cabled Ethernet) shared RF (e. g. , 802. 11 Wi. Fi) shared RF (satellite) humans at a cocktail party (shared air, acoustical) 5: Data. Link Layer 5 -20
Multiple Access Links and Protocols Two types of “links”: r point-to-point m PPP for dial-up access m point-to-point link between Ethernet switch and host r broadcast (shared wire or medium) m old-fashioned Ethernet m upstream HFC m 802. 11 wireless LAN shared wire (e. g. , cabled Ethernet) shared RF (e. g. , 802. 11 Wi. Fi) shared RF (satellite) humans at a cocktail party (shared air, acoustical) 5: Data. Link Layer 5 -20
 Multiple Access protocols r single shared broadcast channel r two or more simultaneous transmissions by nodes: interference m collision if node receives two or more signals at the same time multiple access protocol r distributed algorithm that determines how nodes share channel, i. e. , determine when node can transmit r communication about channel sharing must use channel itself! m no out-of-band channel for coordination 5: Data. Link Layer 5 -21
Multiple Access protocols r single shared broadcast channel r two or more simultaneous transmissions by nodes: interference m collision if node receives two or more signals at the same time multiple access protocol r distributed algorithm that determines how nodes share channel, i. e. , determine when node can transmit r communication about channel sharing must use channel itself! m no out-of-band channel for coordination 5: Data. Link Layer 5 -21
 Ideal Mulitple Access Protocol Broadcast channel of rate R bps 1. When one node wants to transmit, it can send at rate R. 2. When M nodes want to transmit, each can send at average rate R/M 3. Fully decentralized: m m no special node to coordinate transmissions no synchronization of clocks, slots 4. Simple 5: Data. Link Layer 5 -22
Ideal Mulitple Access Protocol Broadcast channel of rate R bps 1. When one node wants to transmit, it can send at rate R. 2. When M nodes want to transmit, each can send at average rate R/M 3. Fully decentralized: m m no special node to coordinate transmissions no synchronization of clocks, slots 4. Simple 5: Data. Link Layer 5 -22
 MAC Protocols: a taxonomy Three broad classes: r Channel Partitioning m divide channel into smaller “pieces” (time slots, frequency); allocate piece to node for exclusive use r Random Access m allow collisions; “recover” from collisions r “Taking turns” m tightly coordinate shared access to avoid collisions Recall goal: efficient, fair, simple, decentralized 5: Data. Link Layer 5 -23
MAC Protocols: a taxonomy Three broad classes: r Channel Partitioning m divide channel into smaller “pieces” (time slots, frequency); allocate piece to node for exclusive use r Random Access m allow collisions; “recover” from collisions r “Taking turns” m tightly coordinate shared access to avoid collisions Recall goal: efficient, fair, simple, decentralized 5: Data. Link Layer 5 -23
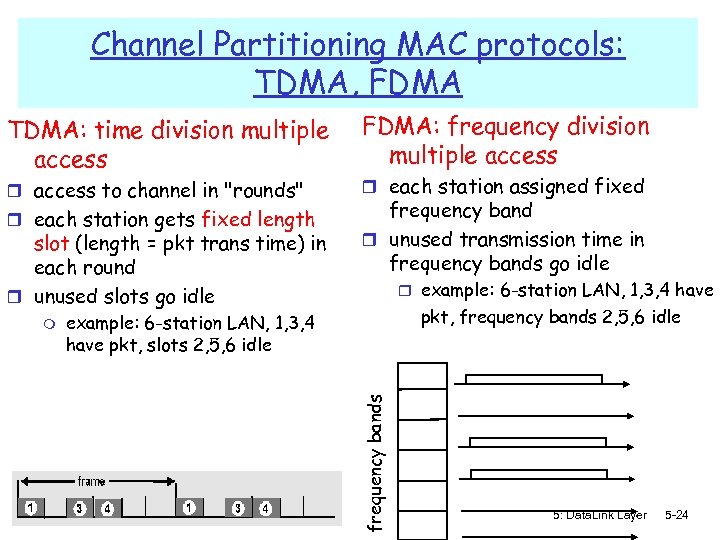 Channel Partitioning MAC protocols: TDMA, FDMA TDMA: time division multiple access r access to channel in "rounds" r each station gets fixed length slot (length = pkt trans time) in each round r unused slots go idle r each station assigned fixed frequency band r unused transmission time in frequency bands go idle r example: 6 -station LAN, 1, 3, 4 have pkt, frequency bands 2, 5, 6 idle example: 6 -station LAN, 1, 3, 4 have pkt, slots 2, 5, 6 idle frequency bands m FDMA: frequency division multiple access 5: Data. Link Layer 5 -24
Channel Partitioning MAC protocols: TDMA, FDMA TDMA: time division multiple access r access to channel in "rounds" r each station gets fixed length slot (length = pkt trans time) in each round r unused slots go idle r each station assigned fixed frequency band r unused transmission time in frequency bands go idle r example: 6 -station LAN, 1, 3, 4 have pkt, frequency bands 2, 5, 6 idle example: 6 -station LAN, 1, 3, 4 have pkt, slots 2, 5, 6 idle frequency bands m FDMA: frequency division multiple access 5: Data. Link Layer 5 -24
 Channel Partitioning CDMA: Code Division Multiple Access Alternative to multiplexing: r allows each station to transmit over the entire frequency spectrum all the time. r simultaneous transmissions are separated using coding theory. r used mostly in wireless broadcast channels (cellular, satellite, etc) – we will study it in the wireless context r relatively young technology; (has been used in the military, though Observe: MUX = speak person-to-person in designated space CDMA = ”shout” using different languages: the ones who know the language will get what you say 5: Data. Link Layer 5 -25
Channel Partitioning CDMA: Code Division Multiple Access Alternative to multiplexing: r allows each station to transmit over the entire frequency spectrum all the time. r simultaneous transmissions are separated using coding theory. r used mostly in wireless broadcast channels (cellular, satellite, etc) – we will study it in the wireless context r relatively young technology; (has been used in the military, though Observe: MUX = speak person-to-person in designated space CDMA = ”shout” using different languages: the ones who know the language will get what you say 5: Data. Link Layer 5 -25
 Random Access Protocols r When node has packet to send m transmit at full channel data rate R. m no a priori coordination among nodes r two or more transmitting nodes ➜ “collision”, r random access MAC protocol specifies: m how to detect collisions m how to recover from collisions (e. g. , via delayed retransmissions) r Examples of random access MAC protocols: m slotted ALOHA m CSMA, CSMA/CD, CSMA/CA 5: Data. Link Layer 5 -26
Random Access Protocols r When node has packet to send m transmit at full channel data rate R. m no a priori coordination among nodes r two or more transmitting nodes ➜ “collision”, r random access MAC protocol specifies: m how to detect collisions m how to recover from collisions (e. g. , via delayed retransmissions) r Examples of random access MAC protocols: m slotted ALOHA m CSMA, CSMA/CD, CSMA/CA 5: Data. Link Layer 5 -26
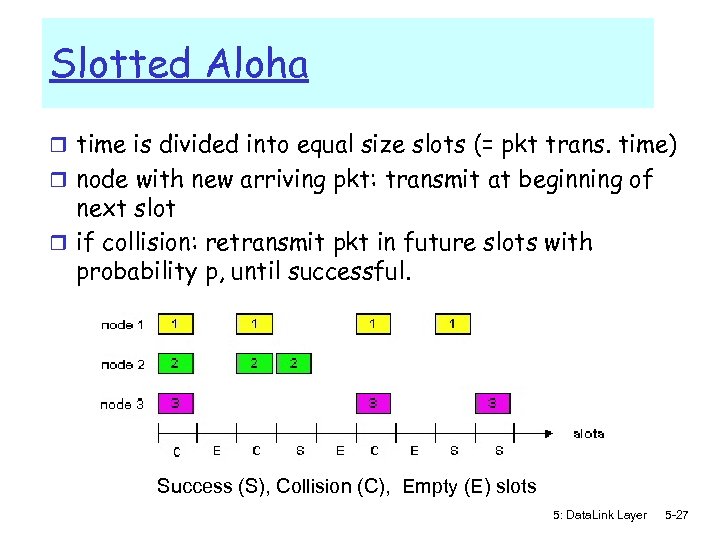 Slotted Aloha r time is divided into equal size slots (= pkt trans. time) r node with new arriving pkt: transmit at beginning of next slot r if collision: retransmit pkt in future slots with probability p, until successful. Success (S), Collision (C), Empty (E) slots 5: Data. Link Layer 5 -27
Slotted Aloha r time is divided into equal size slots (= pkt trans. time) r node with new arriving pkt: transmit at beginning of next slot r if collision: retransmit pkt in future slots with probability p, until successful. Success (S), Collision (C), Empty (E) slots 5: Data. Link Layer 5 -27
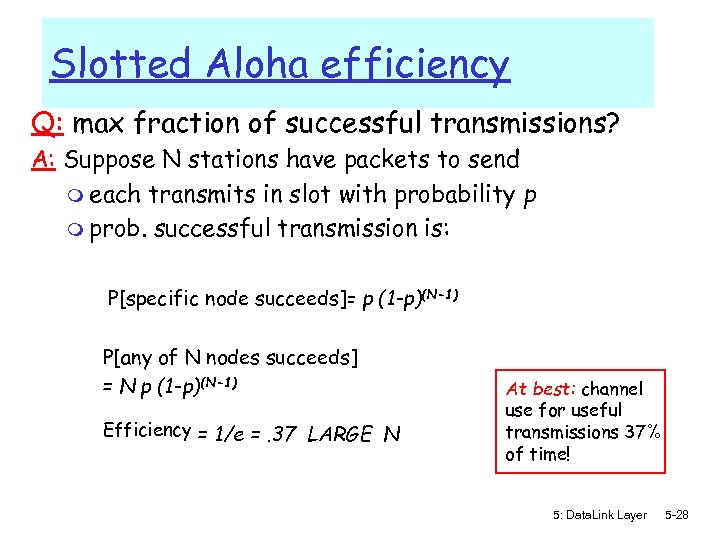 Slotted Aloha efficiency Q: max fraction of successful transmissions? A: Suppose N stations have packets to send m each transmits in slot with probability p m prob. successful transmission is: P[specific node succeeds]= p (1 -p)(N-1) P[any of N nodes succeeds] = N p (1 -p)(N-1) Efficiency = 1/e =. 37 LARGE N At best: channel use for useful transmissions 37% of time! 5: Data. Link Layer 5 -28
Slotted Aloha efficiency Q: max fraction of successful transmissions? A: Suppose N stations have packets to send m each transmits in slot with probability p m prob. successful transmission is: P[specific node succeeds]= p (1 -p)(N-1) P[any of N nodes succeeds] = N p (1 -p)(N-1) Efficiency = 1/e =. 37 LARGE N At best: channel use for useful transmissions 37% of time! 5: Data. Link Layer 5 -28
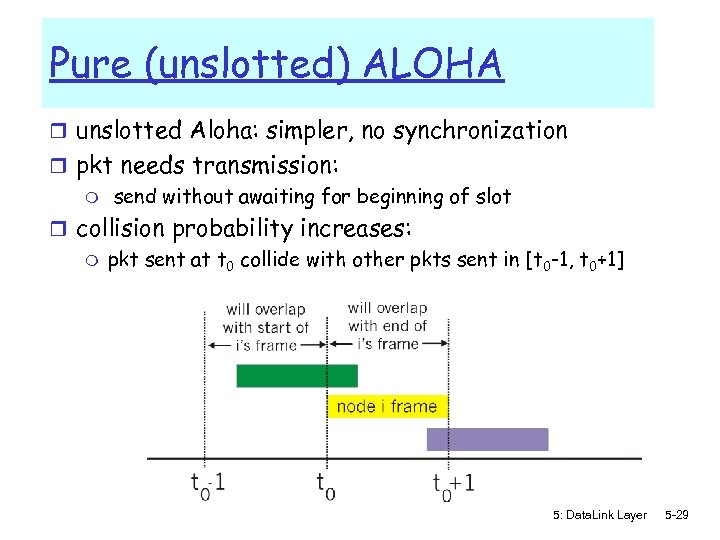 Pure (unslotted) ALOHA r unslotted Aloha: simpler, no synchronization r pkt needs transmission: m send without awaiting for beginning of slot r collision probability increases: m pkt sent at t 0 collide with other pkts sent in [t 0 -1, t 0+1] 5: Data. Link Layer 5 -29
Pure (unslotted) ALOHA r unslotted Aloha: simpler, no synchronization r pkt needs transmission: m send without awaiting for beginning of slot r collision probability increases: m pkt sent at t 0 collide with other pkts sent in [t 0 -1, t 0+1] 5: Data. Link Layer 5 -29
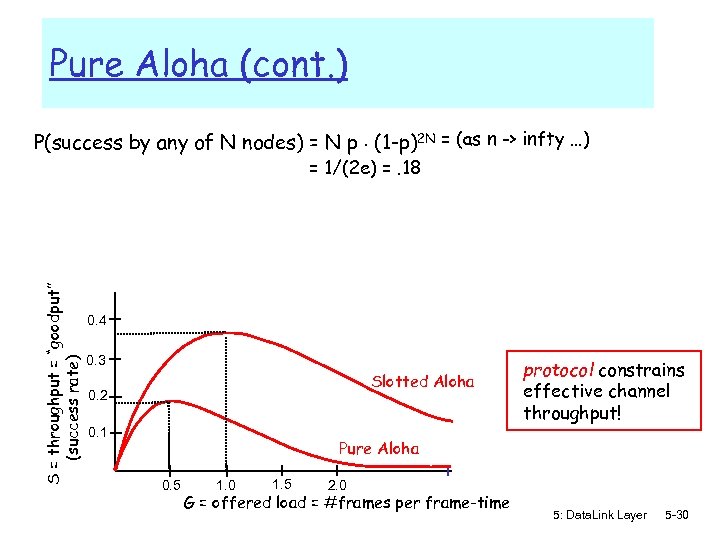 Pure Aloha (cont. ) P(success by any of N nodes) = N p. (1 -p)2 N = (as n -> infty …) S = throughput = “goodput” (success rate) = 1/(2 e) =. 18 0. 4 0. 3 Slotted Aloha 0. 2 0. 1 protocol constrains effective channel throughput! Pure Aloha 0. 5 1. 0 1. 5 2. 0 G = offered load = #frames per frame-time 5: Data. Link Layer 5 -30
Pure Aloha (cont. ) P(success by any of N nodes) = N p. (1 -p)2 N = (as n -> infty …) S = throughput = “goodput” (success rate) = 1/(2 e) =. 18 0. 4 0. 3 Slotted Aloha 0. 2 0. 1 protocol constrains effective channel throughput! Pure Aloha 0. 5 1. 0 1. 5 2. 0 G = offered load = #frames per frame-time 5: Data. Link Layer 5 -30
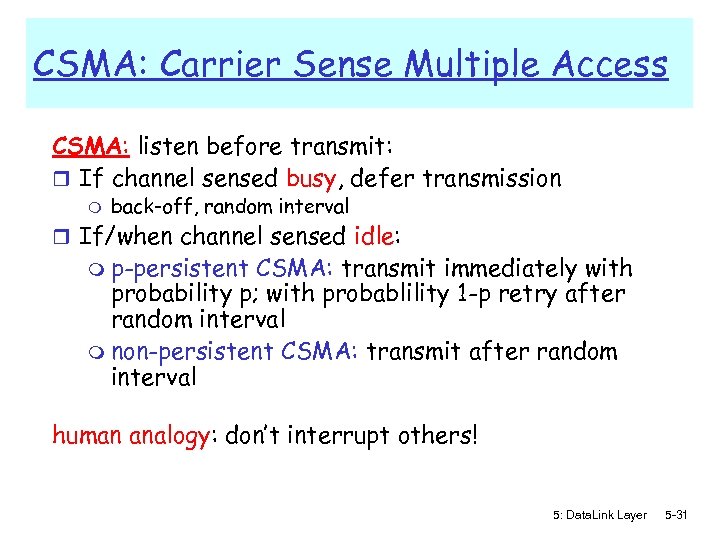 CSMA: Carrier Sense Multiple Access CSMA: listen before transmit: r If channel sensed busy, defer transmission m back-off, random interval r If/when channel sensed idle: m p-persistent CSMA: transmit immediately with probability p; with probablility 1 -p retry after random interval m non-persistent CSMA: transmit after random interval human analogy: don’t interrupt others! 5: Data. Link Layer 5 -31
CSMA: Carrier Sense Multiple Access CSMA: listen before transmit: r If channel sensed busy, defer transmission m back-off, random interval r If/when channel sensed idle: m p-persistent CSMA: transmit immediately with probability p; with probablility 1 -p retry after random interval m non-persistent CSMA: transmit after random interval human analogy: don’t interrupt others! 5: Data. Link Layer 5 -31
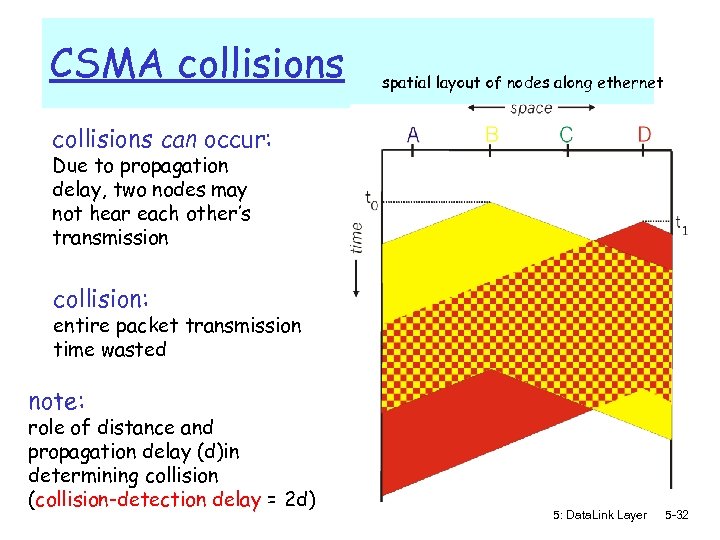 CSMA collisions spatial layout of nodes along ethernet collisions can occur: Due to propagation delay, two nodes may not hear each other’s transmission collision: entire packet transmission time wasted note: role of distance and propagation delay (d)in determining collision (collision-detection delay = 2 d) 5: Data. Link Layer 5 -32
CSMA collisions spatial layout of nodes along ethernet collisions can occur: Due to propagation delay, two nodes may not hear each other’s transmission collision: entire packet transmission time wasted note: role of distance and propagation delay (d)in determining collision (collision-detection delay = 2 d) 5: Data. Link Layer 5 -32
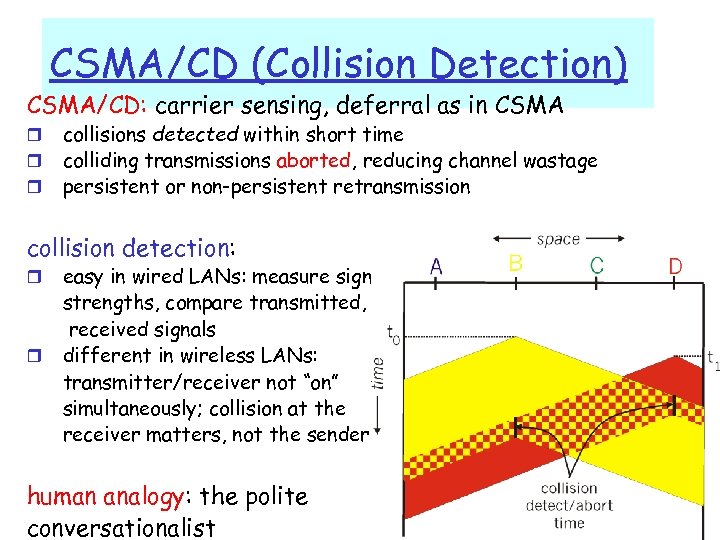 CSMA/CD (Collision Detection) CSMA/CD: carrier sensing, deferral as in CSMA r r r collisions detected within short time colliding transmissions aborted, reducing channel wastage persistent or non-persistent retransmission collision detection: r r easy in wired LANs: measure signal strengths, compare transmitted, received signals different in wireless LANs: transmitter/receiver not “on” simultaneously; collision at the receiver matters, not the sender human analogy: the polite conversationalist 5: Data. Link Layer 5 -33
CSMA/CD (Collision Detection) CSMA/CD: carrier sensing, deferral as in CSMA r r r collisions detected within short time colliding transmissions aborted, reducing channel wastage persistent or non-persistent retransmission collision detection: r r easy in wired LANs: measure signal strengths, compare transmitted, received signals different in wireless LANs: transmitter/receiver not “on” simultaneously; collision at the receiver matters, not the sender human analogy: the polite conversationalist 5: Data. Link Layer 5 -33
 “Taking Turns” MAC protocols channel partitioning MAC protocols: m share channel efficiently and fairly at high load m inefficient at low load: delay in channel access, 1/N bandwidth allocated even if only 1 active node! Random access MAC protocols m efficient at low load: single node can fully utilize channel m high load: collision overhead “taking turns” protocols look for best of both worlds! 5: Data. Link Layer 5 -34
“Taking Turns” MAC protocols channel partitioning MAC protocols: m share channel efficiently and fairly at high load m inefficient at low load: delay in channel access, 1/N bandwidth allocated even if only 1 active node! Random access MAC protocols m efficient at low load: single node can fully utilize channel m high load: collision overhead “taking turns” protocols look for best of both worlds! 5: Data. Link Layer 5 -34
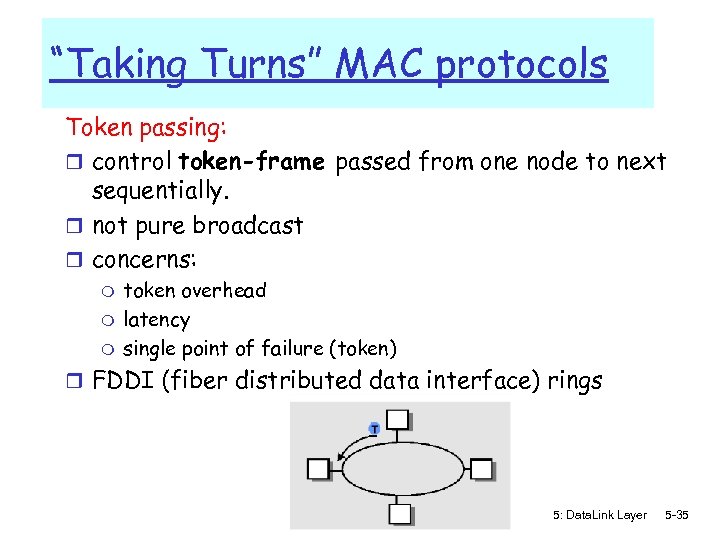 “Taking Turns” MAC protocols Token passing: r control token-frame passed from one node to next sequentially. r not pure broadcast r concerns: m m m token overhead latency single point of failure (token) r FDDI (fiber distributed data interface) rings 5: Data. Link Layer 5 -35
“Taking Turns” MAC protocols Token passing: r control token-frame passed from one node to next sequentially. r not pure broadcast r concerns: m m m token overhead latency single point of failure (token) r FDDI (fiber distributed data interface) rings 5: Data. Link Layer 5 -35
 IEEE 802. 4 Standard (General Motors Token Bus) Contention systems limitation: worst-case delay until successful transmission is unlimited => not suitable for real-time traffic Solution: token-passing, round robin r token = special control frame; only the holding station can transmit; then it passes it to another station, i. e. for token bus, the next in the logical ring r 4 priority classes of traffic, using timers r Logical ring-maintenance: distributed strategy m Robust, somehow complicated though 5: Data. Link Layer 5 -36
IEEE 802. 4 Standard (General Motors Token Bus) Contention systems limitation: worst-case delay until successful transmission is unlimited => not suitable for real-time traffic Solution: token-passing, round robin r token = special control frame; only the holding station can transmit; then it passes it to another station, i. e. for token bus, the next in the logical ring r 4 priority classes of traffic, using timers r Logical ring-maintenance: distributed strategy m Robust, somehow complicated though 5: Data. Link Layer 5 -36
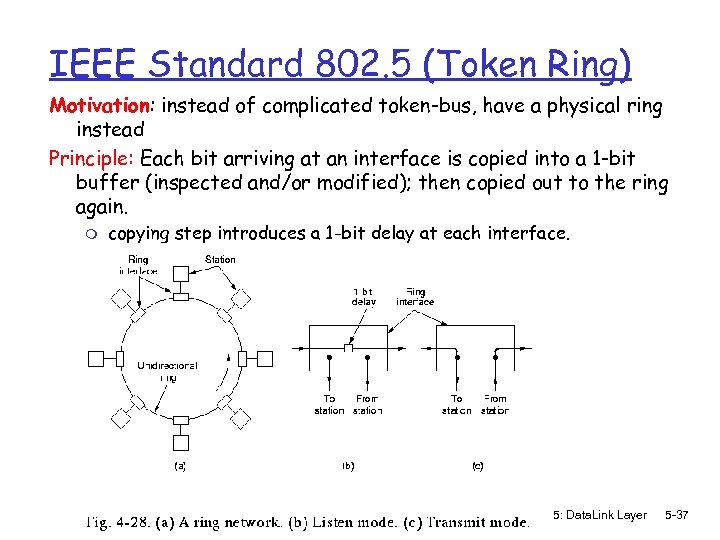 IEEE Standard 802. 5 (Token Ring) Motivation: instead of complicated token-bus, have a physical ring instead Principle: Each bit arriving at an interface is copied into a 1 -bit buffer (inspected and/or modified); then copied out to the ring again. m copying step introduces a 1 -bit delay at each interface. 5: Data. Link Layer 5 -37
IEEE Standard 802. 5 (Token Ring) Motivation: instead of complicated token-bus, have a physical ring instead Principle: Each bit arriving at an interface is copied into a 1 -bit buffer (inspected and/or modified); then copied out to the ring again. m copying step introduces a 1 -bit delay at each interface. 5: Data. Link Layer 5 -37
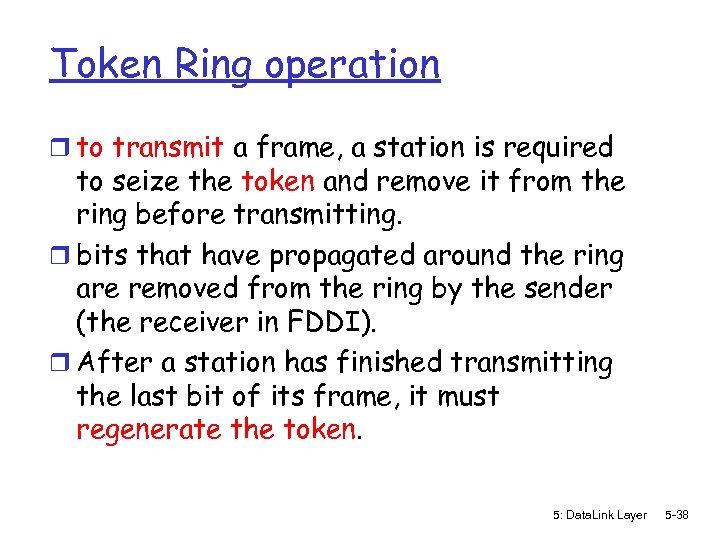 Token Ring operation r to transmit a frame, a station is required to seize the token and remove it from the ring before transmitting. r bits that have propagated around the ring are removed from the ring by the sender (the receiver in FDDI). r After a station has finished transmitting the last bit of its frame, it must regenerate the token. 5: Data. Link Layer 5 -38
Token Ring operation r to transmit a frame, a station is required to seize the token and remove it from the ring before transmitting. r bits that have propagated around the ring are removed from the ring by the sender (the receiver in FDDI). r After a station has finished transmitting the last bit of its frame, it must regenerate the token. 5: Data. Link Layer 5 -38
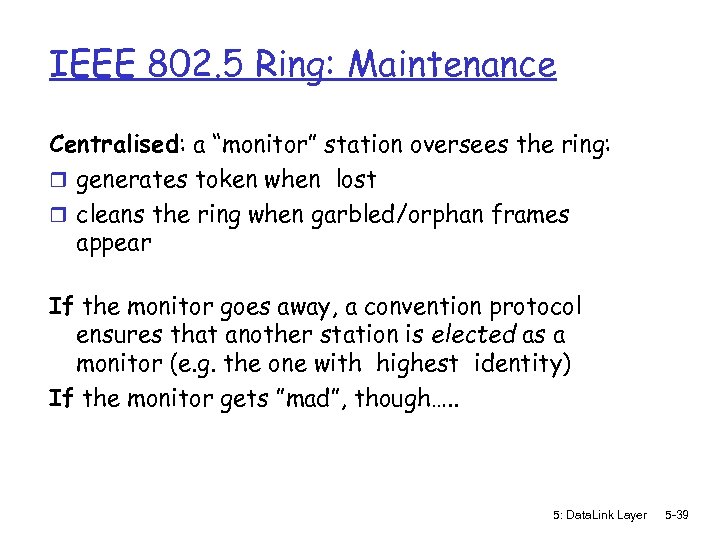 IEEE 802. 5 Ring: Maintenance Centralised: a “monitor” station oversees the ring: r generates token when lost r cleans the ring when garbled/orphan frames appear If the monitor goes away, a convention protocol ensures that another station is elected as a monitor (e. g. the one with highest identity) If the monitor gets ”mad”, though…. . 5: Data. Link Layer 5 -39
IEEE 802. 5 Ring: Maintenance Centralised: a “monitor” station oversees the ring: r generates token when lost r cleans the ring when garbled/orphan frames appear If the monitor goes away, a convention protocol ensures that another station is elected as a monitor (e. g. the one with highest identity) If the monitor gets ”mad”, though…. . 5: Data. Link Layer 5 -39
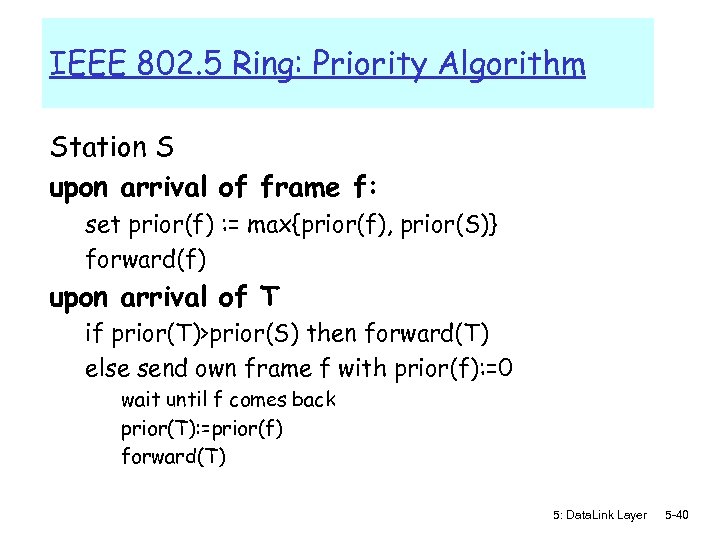 IEEE 802. 5 Ring: Priority Algorithm Station S upon arrival of frame f: set prior(f) : = max{prior(f), prior(S)} forward(f) upon arrival of T if prior(T)>prior(S) then forward(T) else send own frame f with prior(f): =0 wait until f comes back prior(T): =prior(f) forward(T) 5: Data. Link Layer 5 -40
IEEE 802. 5 Ring: Priority Algorithm Station S upon arrival of frame f: set prior(f) : = max{prior(f), prior(S)} forward(f) upon arrival of T if prior(T)>prior(S) then forward(T) else send own frame f with prior(f): =0 wait until f comes back prior(T): =prior(f) forward(T) 5: Data. Link Layer 5 -40
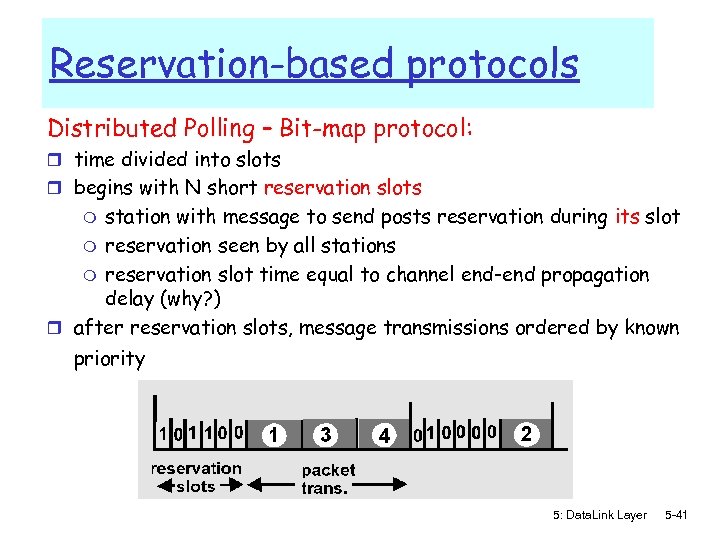 Reservation-based protocols Distributed Polling – Bit-map protocol: r time divided into slots r begins with N short reservation slots station with message to send posts reservation during its slot m reservation seen by all stations m reservation slot time equal to channel end-end propagation delay (why? ) r after reservation slots, message transmissions ordered by known m priority 5: Data. Link Layer 5 -41
Reservation-based protocols Distributed Polling – Bit-map protocol: r time divided into slots r begins with N short reservation slots station with message to send posts reservation during its slot m reservation seen by all stations m reservation slot time equal to channel end-end propagation delay (why? ) r after reservation slots, message transmissions ordered by known m priority 5: Data. Link Layer 5 -41
 Summary of MAC protocols r What do you do with a shared media? m Channel Partitioning, by time, frequency or code • Time Division, Frequency Division m Random partitioning (dynamic), • ALOHA, S-ALOHA, CSMA/CD • carrier sensing: easy in some technologies (wire), hard in others (wireless) • CSMA/CD used in Ethernet • CSMA/CA used in 802. 11 m Taking Turns • polling, token passing 5: Data. Link Layer 5 -42
Summary of MAC protocols r What do you do with a shared media? m Channel Partitioning, by time, frequency or code • Time Division, Frequency Division m Random partitioning (dynamic), • ALOHA, S-ALOHA, CSMA/CD • carrier sensing: easy in some technologies (wire), hard in others (wireless) • CSMA/CD used in Ethernet • CSMA/CA used in 802. 11 m Taking Turns • polling, token passing 5: Data. Link Layer 5 -42
 LAN technologies Data link layer so far: m services, access error detection/correction, multiple Next: LAN technologies m addressing m Ethernet m hubs, switches m PPP 5: Data. Link Layer 5 -43
LAN technologies Data link layer so far: m services, access error detection/correction, multiple Next: LAN technologies m addressing m Ethernet m hubs, switches m PPP 5: Data. Link Layer 5 -43
 Link Layer r 5. 1 Introduction and r r r services Framing 5. 2 Error detection and correction 5. 3 Multiple access protocols 5. 4 Link-Layer Addressing 5. 5 Ethernet r 5. 6 Hubs and switches r 5. 7 PPP 5: Data. Link Layer 5 -44
Link Layer r 5. 1 Introduction and r r r services Framing 5. 2 Error detection and correction 5. 3 Multiple access protocols 5. 4 Link-Layer Addressing 5. 5 Ethernet r 5. 6 Hubs and switches r 5. 7 PPP 5: Data. Link Layer 5 -44
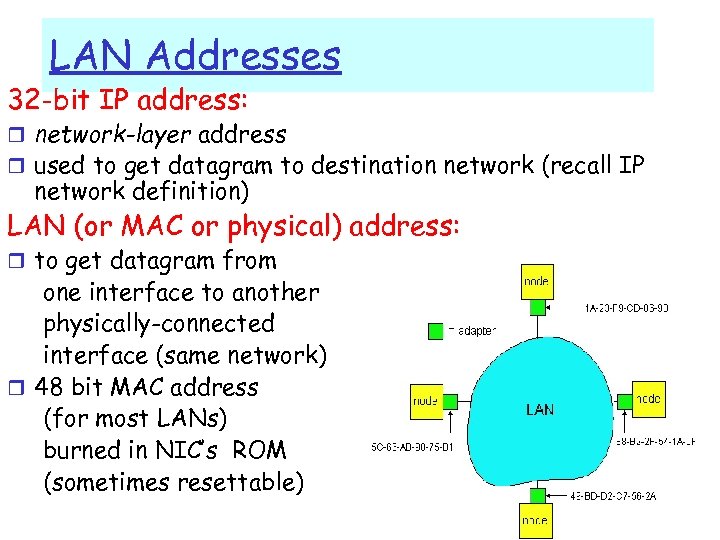 LAN Addresses 32 -bit IP address: r network-layer address r used to get datagram to destination network (recall IP network definition) LAN (or MAC or physical) address: r to get datagram from one interface to another physically-connected interface (same network) r 48 bit MAC address (for most LANs) burned in NIC’s ROM (sometimes resettable) 5: Data. Link Layer 5 -45
LAN Addresses 32 -bit IP address: r network-layer address r used to get datagram to destination network (recall IP network definition) LAN (or MAC or physical) address: r to get datagram from one interface to another physically-connected interface (same network) r 48 bit MAC address (for most LANs) burned in NIC’s ROM (sometimes resettable) 5: Data. Link Layer 5 -45
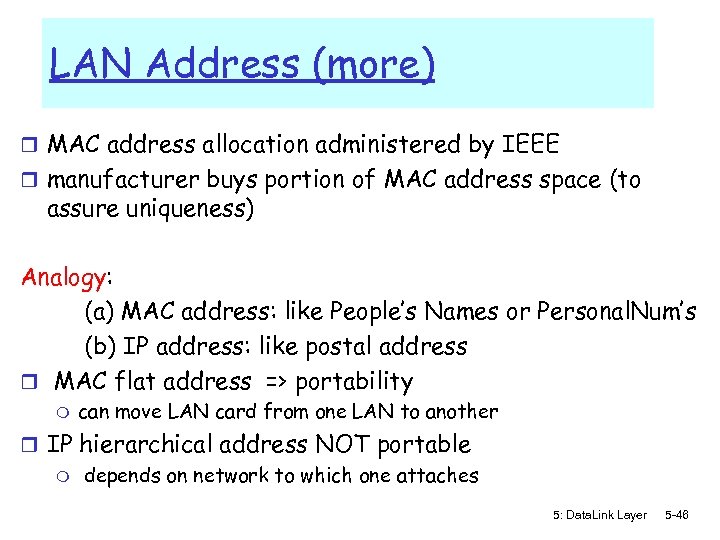 LAN Address (more) r MAC address allocation administered by IEEE r manufacturer buys portion of MAC address space (to assure uniqueness) Analogy: (a) MAC address: like People’s Names or Personal. Num’s (b) IP address: like postal address r MAC flat address => portability m can move LAN card from one LAN to another r IP hierarchical address NOT portable m depends on network to which one attaches 5: Data. Link Layer 5 -46
LAN Address (more) r MAC address allocation administered by IEEE r manufacturer buys portion of MAC address space (to assure uniqueness) Analogy: (a) MAC address: like People’s Names or Personal. Num’s (b) IP address: like postal address r MAC flat address => portability m can move LAN card from one LAN to another r IP hierarchical address NOT portable m depends on network to which one attaches 5: Data. Link Layer 5 -46
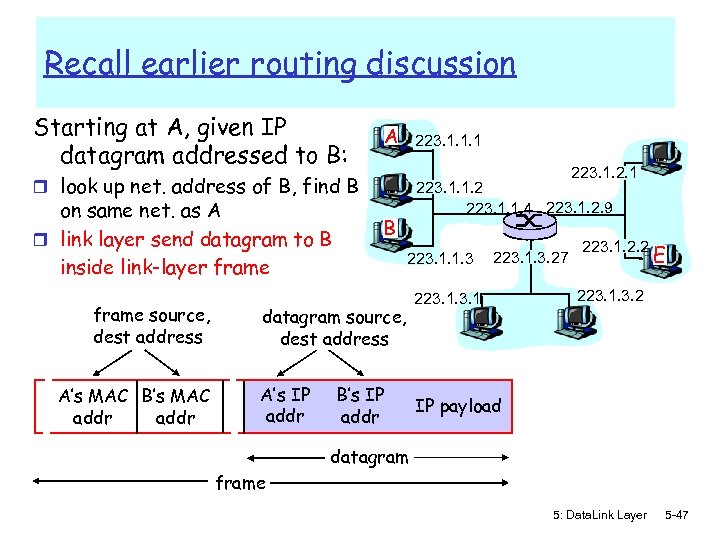 Recall earlier routing discussion Starting at A, given IP datagram addressed to B: A 223. 1. 1. 1 223. 1. 2. 1 r look up net. address of B, find B on same net. as A r link layer send datagram to B inside link-layer frame source, dest address A’s MAC B’s MAC addr 223. 1. 1. 2 223. 1. 1. 4 223. 1. 2. 9 B 223. 1. 1. 3 datagram source, dest address A’s IP addr B’s IP addr 223. 1. 3. 27 223. 1. 2. 2 E 223. 1. 3. 2 IP payload datagram frame 5: Data. Link Layer 5 -47
Recall earlier routing discussion Starting at A, given IP datagram addressed to B: A 223. 1. 1. 1 223. 1. 2. 1 r look up net. address of B, find B on same net. as A r link layer send datagram to B inside link-layer frame source, dest address A’s MAC B’s MAC addr 223. 1. 1. 2 223. 1. 1. 4 223. 1. 2. 9 B 223. 1. 1. 3 datagram source, dest address A’s IP addr B’s IP addr 223. 1. 3. 27 223. 1. 2. 2 E 223. 1. 3. 2 IP payload datagram frame 5: Data. Link Layer 5 -47
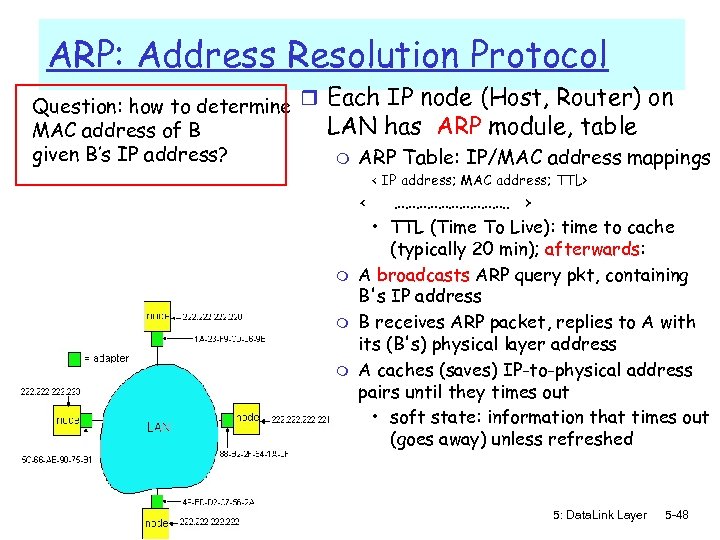 ARP: Address Resolution Protocol Question: how to determine r MAC address of B given B’s IP address? Each IP node (Host, Router) on LAN has ARP module, table m ARP Table: IP/MAC address mappings < IP address; MAC address; TTL> < m m m ……………. . > • TTL (Time To Live): time to cache (typically 20 min); afterwards: A broadcasts ARP query pkt, containing B's IP address B receives ARP packet, replies to A with its (B's) physical layer address A caches (saves) IP-to-physical address pairs until they times out • soft state: information that times out (goes away) unless refreshed 5: Data. Link Layer 5 -48
ARP: Address Resolution Protocol Question: how to determine r MAC address of B given B’s IP address? Each IP node (Host, Router) on LAN has ARP module, table m ARP Table: IP/MAC address mappings < IP address; MAC address; TTL> < m m m ……………. . > • TTL (Time To Live): time to cache (typically 20 min); afterwards: A broadcasts ARP query pkt, containing B's IP address B receives ARP packet, replies to A with its (B's) physical layer address A caches (saves) IP-to-physical address pairs until they times out • soft state: information that times out (goes away) unless refreshed 5: Data. Link Layer 5 -48
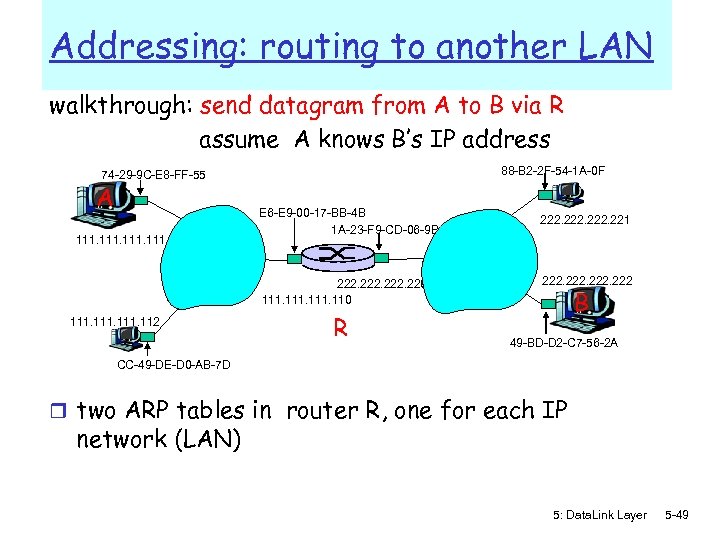 Addressing: routing to another LAN walkthrough: send datagram from A to B via R assume A knows B’s IP address 88 -B 2 -2 F-54 -1 A-0 F 74 -29 -9 C-E 8 -FF-55 A 111 E 6 -E 9 -00 -17 -BB-4 B 1 A-23 -F 9 -CD-06 -9 B 222. 220 111. 112 R 222. 221 222 B 49 -BD-D 2 -C 7 -56 -2 A CC-49 -DE-D 0 -AB-7 D r two ARP tables in router R, one for each IP network (LAN) 5: Data. Link Layer 5 -49
Addressing: routing to another LAN walkthrough: send datagram from A to B via R assume A knows B’s IP address 88 -B 2 -2 F-54 -1 A-0 F 74 -29 -9 C-E 8 -FF-55 A 111 E 6 -E 9 -00 -17 -BB-4 B 1 A-23 -F 9 -CD-06 -9 B 222. 220 111. 112 R 222. 221 222 B 49 -BD-D 2 -C 7 -56 -2 A CC-49 -DE-D 0 -AB-7 D r two ARP tables in router R, one for each IP network (LAN) 5: Data. Link Layer 5 -49
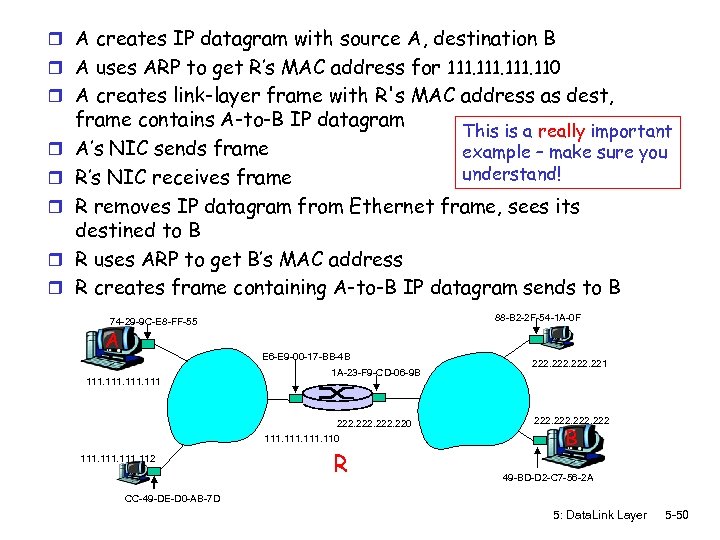 r A creates IP datagram with source A, destination B r A uses ARP to get R’s MAC address for 111. 110 r A creates link-layer frame with R's MAC address as dest, r r r frame contains A-to-B IP datagram This is a really important A’s NIC sends frame example – make sure you understand! R’s NIC receives frame R removes IP datagram from Ethernet frame, sees its destined to B R uses ARP to get B’s MAC address R creates frame containing A-to-B IP datagram sends to B 88 -B 2 -2 F-54 -1 A-0 F 74 -29 -9 C-E 8 -FF-55 A E 6 -E 9 -00 -17 -BB-4 B 111 1 A-23 -F 9 -CD-06 -9 B 222. 220 111. 112 R 222. 221 222 B 49 -BD-D 2 -C 7 -56 -2 A CC-49 -DE-D 0 -AB-7 D 5: Data. Link Layer 5 -50
r A creates IP datagram with source A, destination B r A uses ARP to get R’s MAC address for 111. 110 r A creates link-layer frame with R's MAC address as dest, r r r frame contains A-to-B IP datagram This is a really important A’s NIC sends frame example – make sure you understand! R’s NIC receives frame R removes IP datagram from Ethernet frame, sees its destined to B R uses ARP to get B’s MAC address R creates frame containing A-to-B IP datagram sends to B 88 -B 2 -2 F-54 -1 A-0 F 74 -29 -9 C-E 8 -FF-55 A E 6 -E 9 -00 -17 -BB-4 B 111 1 A-23 -F 9 -CD-06 -9 B 222. 220 111. 112 R 222. 221 222 B 49 -BD-D 2 -C 7 -56 -2 A CC-49 -DE-D 0 -AB-7 D 5: Data. Link Layer 5 -50
 Link Layer r 5. 1 Introduction and r r services 5. 2 Error detection and correction 5. 3 Multiple access protocols 5. 4 Link-Layer Addressing 5. 5 Ethernet r 5. 6 Hubs and switches r 5. 7 PPP r 5. 8 Link Virtualization: ATM 5: Data. Link Layer 5 -51
Link Layer r 5. 1 Introduction and r r services 5. 2 Error detection and correction 5. 3 Multiple access protocols 5. 4 Link-Layer Addressing 5. 5 Ethernet r 5. 6 Hubs and switches r 5. 7 PPP r 5. 8 Link Virtualization: ATM 5: Data. Link Layer 5 -51
 Ethernet “dominant” wired LAN technology: r cheap $20 for 100 Mbs! r first widely used LAN technology r Simpler, cheaper than token LANs and ATM r Kept up with speed race: 10 Mbps – 10 Gbps Metcalfe’s Ethernet sketch 5: Data. Link Layer 5 -52
Ethernet “dominant” wired LAN technology: r cheap $20 for 100 Mbs! r first widely used LAN technology r Simpler, cheaper than token LANs and ATM r Kept up with speed race: 10 Mbps – 10 Gbps Metcalfe’s Ethernet sketch 5: Data. Link Layer 5 -52
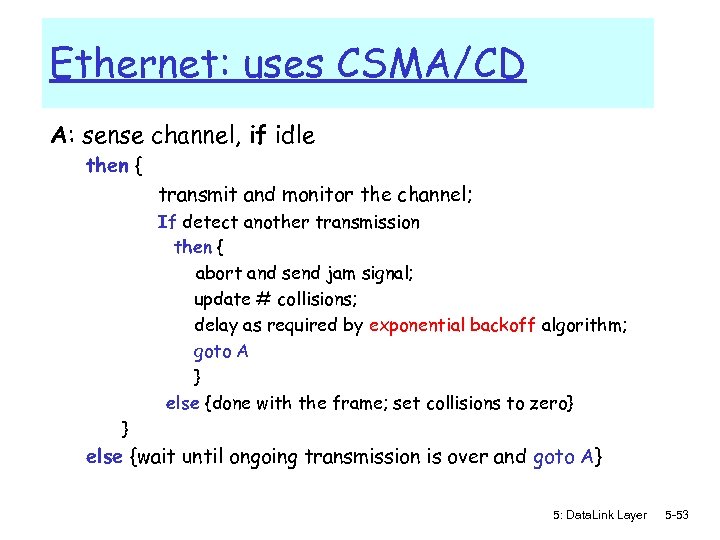 Ethernet: uses CSMA/CD A: sense channel, if idle then { transmit and monitor the channel; If detect another transmission then { abort and send jam signal; update # collisions; delay as required by exponential backoff algorithm; goto A } else {done with the frame; set collisions to zero} } else {wait until ongoing transmission is over and goto A} 5: Data. Link Layer 5 -53
Ethernet: uses CSMA/CD A: sense channel, if idle then { transmit and monitor the channel; If detect another transmission then { abort and send jam signal; update # collisions; delay as required by exponential backoff algorithm; goto A } else {done with the frame; set collisions to zero} } else {wait until ongoing transmission is over and goto A} 5: Data. Link Layer 5 -53
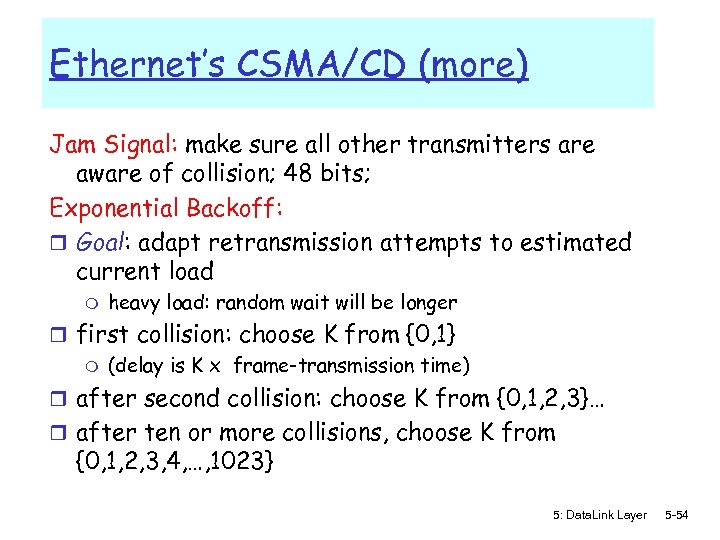 Ethernet’s CSMA/CD (more) Jam Signal: make sure all other transmitters are aware of collision; 48 bits; Exponential Backoff: r Goal: adapt retransmission attempts to estimated current load m heavy load: random wait will be longer r first collision: choose K from {0, 1} m (delay is K x frame-transmission time) r after second collision: choose K from {0, 1, 2, 3}… r after ten or more collisions, choose K from {0, 1, 2, 3, 4, …, 1023} 5: Data. Link Layer 5 -54
Ethernet’s CSMA/CD (more) Jam Signal: make sure all other transmitters are aware of collision; 48 bits; Exponential Backoff: r Goal: adapt retransmission attempts to estimated current load m heavy load: random wait will be longer r first collision: choose K from {0, 1} m (delay is K x frame-transmission time) r after second collision: choose K from {0, 1, 2, 3}… r after ten or more collisions, choose K from {0, 1, 2, 3, 4, …, 1023} 5: Data. Link Layer 5 -54
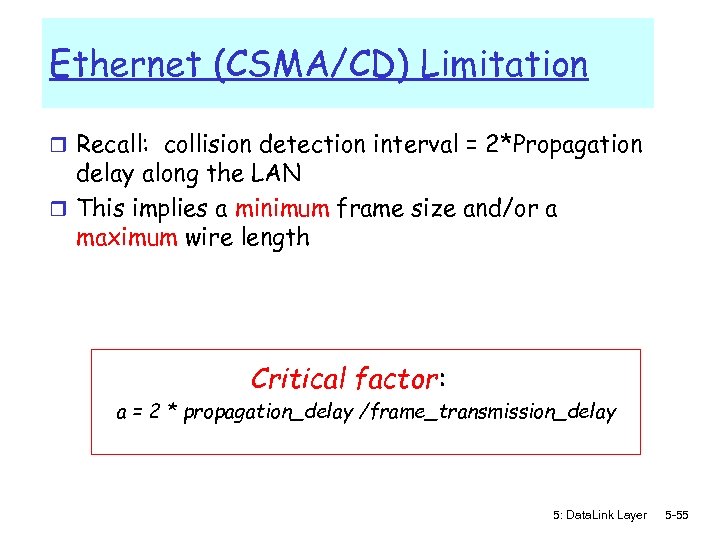 Ethernet (CSMA/CD) Limitation r Recall: collision detection interval = 2*Propagation delay along the LAN r This implies a minimum frame size and/or a maximum wire length Critical factor: a = 2 * propagation_delay /frame_transmission_delay 5: Data. Link Layer 5 -55
Ethernet (CSMA/CD) Limitation r Recall: collision detection interval = 2*Propagation delay along the LAN r This implies a minimum frame size and/or a maximum wire length Critical factor: a = 2 * propagation_delay /frame_transmission_delay 5: Data. Link Layer 5 -55
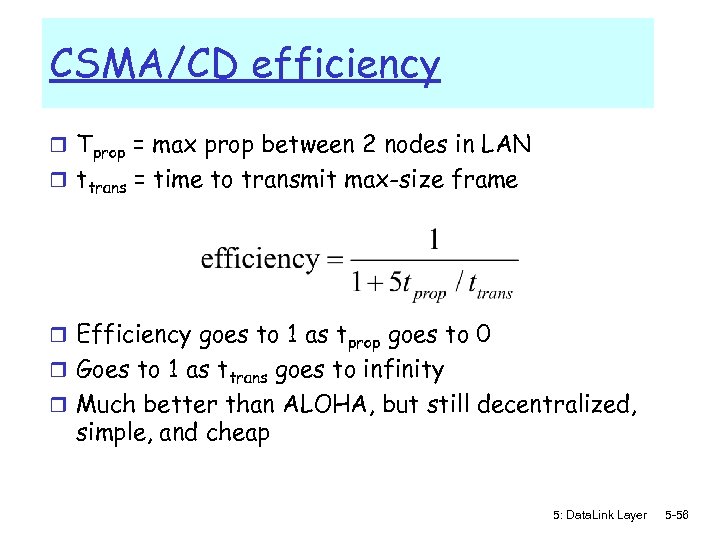 CSMA/CD efficiency r Tprop = max prop between 2 nodes in LAN r ttrans = time to transmit max-size frame r Efficiency goes to 1 as tprop goes to 0 r Goes to 1 as ttrans goes to infinity r Much better than ALOHA, but still decentralized, simple, and cheap 5: Data. Link Layer 5 -56
CSMA/CD efficiency r Tprop = max prop between 2 nodes in LAN r ttrans = time to transmit max-size frame r Efficiency goes to 1 as tprop goes to 0 r Goes to 1 as ttrans goes to infinity r Much better than ALOHA, but still decentralized, simple, and cheap 5: Data. Link Layer 5 -56
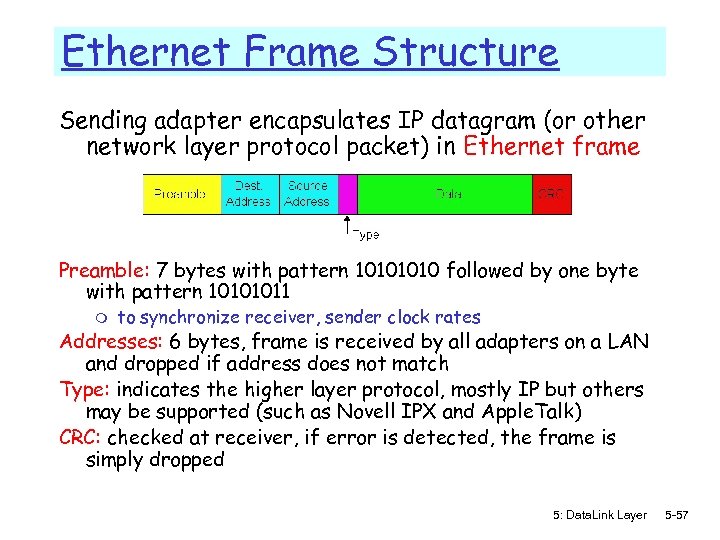 Ethernet Frame Structure Sending adapter encapsulates IP datagram (or other network layer protocol packet) in Ethernet frame Preamble: 7 bytes with pattern 1010 followed by one byte with pattern 10101011 m to synchronize receiver, sender clock rates Addresses: 6 bytes, frame is received by all adapters on a LAN and dropped if address does not match Type: indicates the higher layer protocol, mostly IP but others may be supported (such as Novell IPX and Apple. Talk) CRC: checked at receiver, if error is detected, the frame is simply dropped 5: Data. Link Layer 5 -57
Ethernet Frame Structure Sending adapter encapsulates IP datagram (or other network layer protocol packet) in Ethernet frame Preamble: 7 bytes with pattern 1010 followed by one byte with pattern 10101011 m to synchronize receiver, sender clock rates Addresses: 6 bytes, frame is received by all adapters on a LAN and dropped if address does not match Type: indicates the higher layer protocol, mostly IP but others may be supported (such as Novell IPX and Apple. Talk) CRC: checked at receiver, if error is detected, the frame is simply dropped 5: Data. Link Layer 5 -57
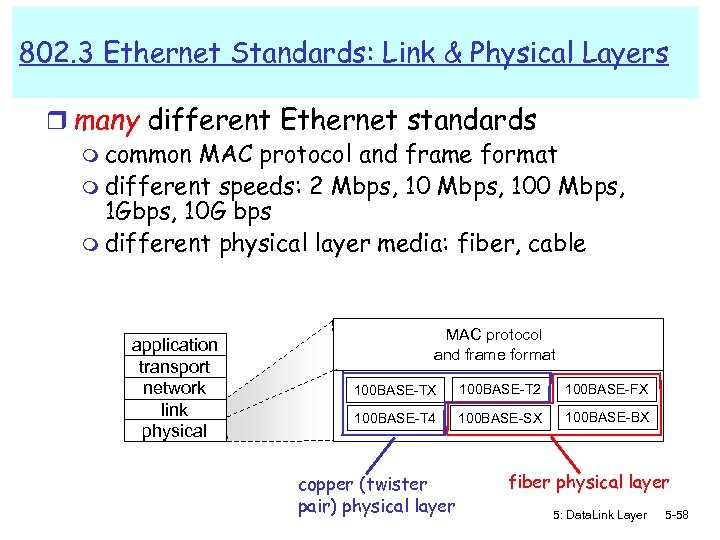 802. 3 Ethernet Standards: Link & Physical Layers r many different Ethernet standards m common MAC protocol and frame format m different speeds: 2 Mbps, 100 Mbps, 1 Gbps, 10 G bps m different physical layer media: fiber, cable application transport network link physical MAC protocol and frame format 100 BASE-TX 100 BASE-T 2 100 BASE-FX 100 BASE-T 4 100 BASE-SX 100 BASE-BX copper (twister pair) physical layer fiber physical layer 5: Data. Link Layer 5 -58
802. 3 Ethernet Standards: Link & Physical Layers r many different Ethernet standards m common MAC protocol and frame format m different speeds: 2 Mbps, 100 Mbps, 1 Gbps, 10 G bps m different physical layer media: fiber, cable application transport network link physical MAC protocol and frame format 100 BASE-TX 100 BASE-T 2 100 BASE-FX 100 BASE-T 4 100 BASE-SX 100 BASE-BX copper (twister pair) physical layer fiber physical layer 5: Data. Link Layer 5 -58
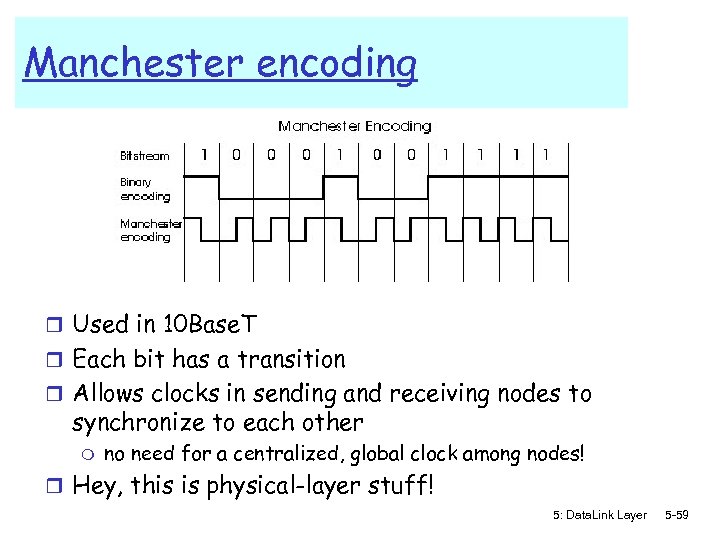 Manchester encoding r Used in 10 Base. T r Each bit has a transition r Allows clocks in sending and receiving nodes to synchronize to each other m no need for a centralized, global clock among nodes! r Hey, this is physical-layer stuff! 5: Data. Link Layer 5 -59
Manchester encoding r Used in 10 Base. T r Each bit has a transition r Allows clocks in sending and receiving nodes to synchronize to each other m no need for a centralized, global clock among nodes! r Hey, this is physical-layer stuff! 5: Data. Link Layer 5 -59
 Ethernet: Unreliable, connectionless r connectionless: No handshaking between sending and receiving NICs r unreliable: receiving NIC doesn’t send acks or nacks to sending NIC m m m stream of datagrams passed to network layer can have gaps (missing datagrams) gaps will be filled if app is using TCP otherwise, app will see gaps 5: Data. Link Layer 5 -60
Ethernet: Unreliable, connectionless r connectionless: No handshaking between sending and receiving NICs r unreliable: receiving NIC doesn’t send acks or nacks to sending NIC m m m stream of datagrams passed to network layer can have gaps (missing datagrams) gaps will be filled if app is using TCP otherwise, app will see gaps 5: Data. Link Layer 5 -60
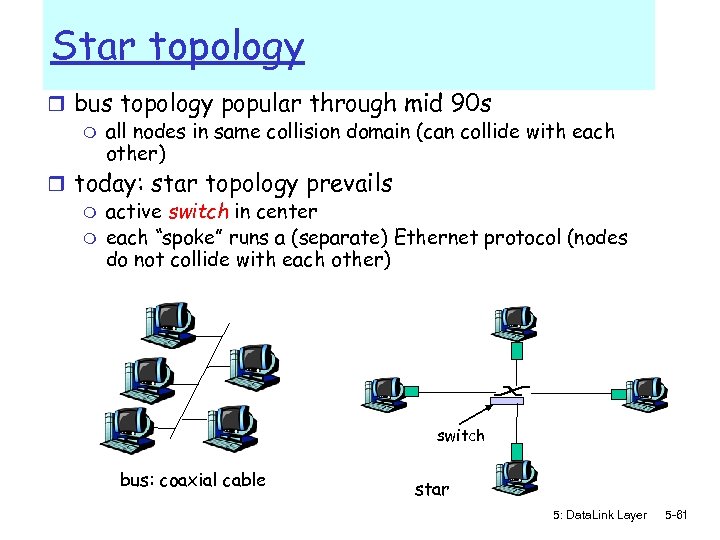 Star topology r bus topology popular through mid 90 s m all nodes in same collision domain (can collide with each other) r today: star topology prevails m active switch in center m each “spoke” runs a (separate) Ethernet protocol (nodes do not collide with each other) switch bus: coaxial cable star 5: Data. Link Layer 5 -61
Star topology r bus topology popular through mid 90 s m all nodes in same collision domain (can collide with each other) r today: star topology prevails m active switch in center m each “spoke” runs a (separate) Ethernet protocol (nodes do not collide with each other) switch bus: coaxial cable star 5: Data. Link Layer 5 -61
 Link Layer r 5. 1 Introduction and r r services 5. 2 Error detection and correction 5. 3 Multiple access protocols 5. 4 Link-Layer Addressing 5. 5 Ethernet r 5. 6 Interconnections: Hubs and switches r 5. 7 PPP 5: Data. Link Layer 5 -62
Link Layer r 5. 1 Introduction and r r services 5. 2 Error detection and correction 5. 3 Multiple access protocols 5. 4 Link-Layer Addressing 5. 5 Ethernet r 5. 6 Interconnections: Hubs and switches r 5. 7 PPP 5: Data. Link Layer 5 -62
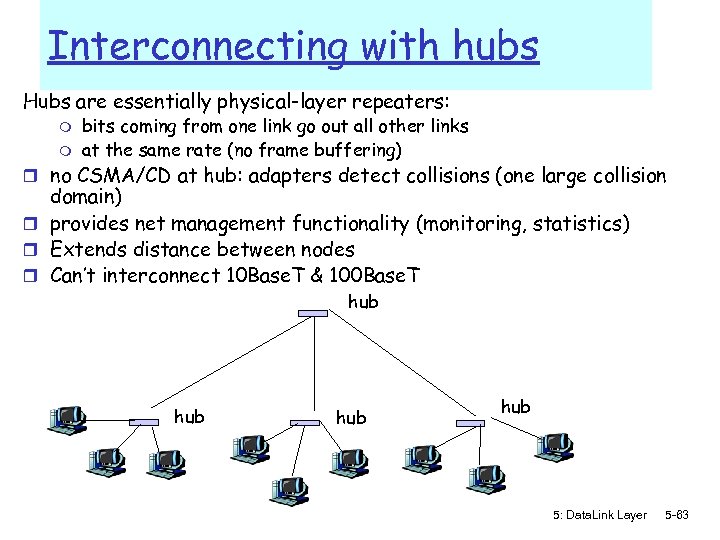 Interconnecting with hubs Hubs are essentially physical-layer repeaters: m m bits coming from one link go out all other links at the same rate (no frame buffering) r no CSMA/CD at hub: adapters detect collisions (one large collision domain) r provides net management functionality (monitoring, statistics) r Extends distance between nodes r Can’t interconnect 10 Base. T & 100 Base. T hub hub 5: Data. Link Layer 5 -63
Interconnecting with hubs Hubs are essentially physical-layer repeaters: m m bits coming from one link go out all other links at the same rate (no frame buffering) r no CSMA/CD at hub: adapters detect collisions (one large collision domain) r provides net management functionality (monitoring, statistics) r Extends distance between nodes r Can’t interconnect 10 Base. T & 100 Base. T hub hub 5: Data. Link Layer 5 -63
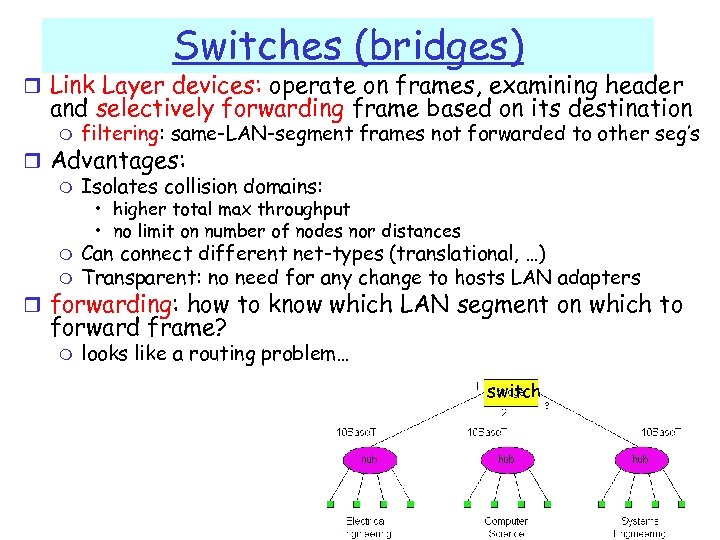 Switches (bridges) r Link Layer devices: operate on frames, examining header and selectively forwarding frame based on its destination m filtering: same-LAN-segment frames not forwarded to other seg’s r Advantages: m Isolates collision domains: • higher total max throughput • no limit on number of nodes nor distances m m Can connect different net-types (translational, …) Transparent: no need for any change to hosts LAN adapters r forwarding: how to know which LAN segment on which to forward frame? m looks like a routing problem… switch 5: Data. Link Layer 5 -64
Switches (bridges) r Link Layer devices: operate on frames, examining header and selectively forwarding frame based on its destination m filtering: same-LAN-segment frames not forwarded to other seg’s r Advantages: m Isolates collision domains: • higher total max throughput • no limit on number of nodes nor distances m m Can connect different net-types (translational, …) Transparent: no need for any change to hosts LAN adapters r forwarding: how to know which LAN segment on which to forward frame? m looks like a routing problem… switch 5: Data. Link Layer 5 -64
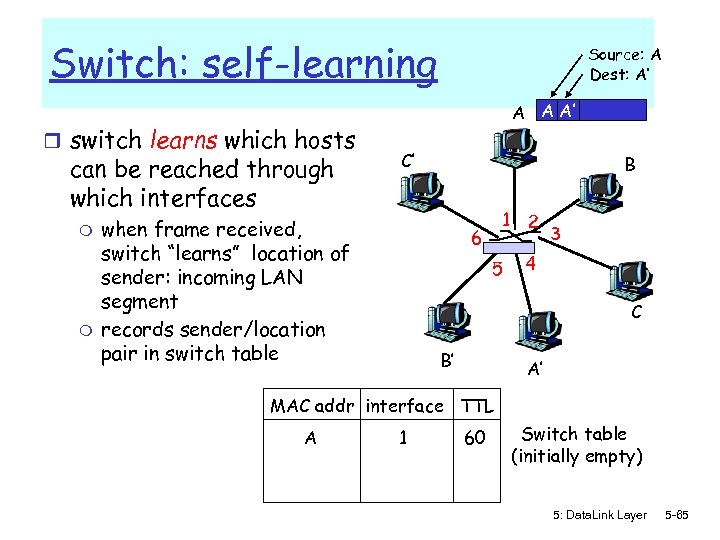 Switch: self-learning r switch learns which hosts can be reached through which interfaces m m Source: A Dest: A’ A A A’ C’ when frame received, switch “learns” location of sender: incoming LAN segment records sender/location pair in switch table B 1 6 5 2 3 4 C B’ A’ MAC addr interface TTL A 1 60 Switch table (initially empty) 5: Data. Link Layer 5 -65
Switch: self-learning r switch learns which hosts can be reached through which interfaces m m Source: A Dest: A’ A A A’ C’ when frame received, switch “learns” location of sender: incoming LAN segment records sender/location pair in switch table B 1 6 5 2 3 4 C B’ A’ MAC addr interface TTL A 1 60 Switch table (initially empty) 5: Data. Link Layer 5 -65
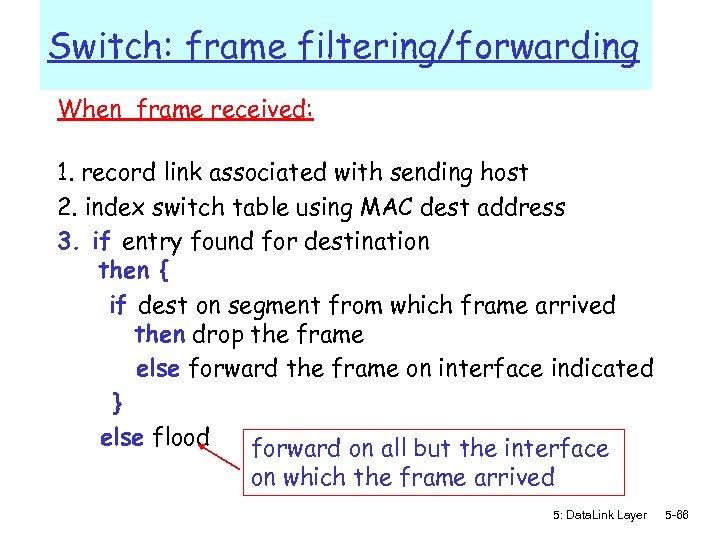 Switch: frame filtering/forwarding When frame received: 1. record link associated with sending host 2. index switch table using MAC dest address 3. if entry found for destination then { if dest on segment from which frame arrived then drop the frame else forward the frame on interface indicated } else flood forward on all but the interface on which the frame arrived 5: Data. Link Layer 5 -66
Switch: frame filtering/forwarding When frame received: 1. record link associated with sending host 2. index switch table using MAC dest address 3. if entry found for destination then { if dest on segment from which frame arrived then drop the frame else forward the frame on interface indicated } else flood forward on all but the interface on which the frame arrived 5: Data. Link Layer 5 -66
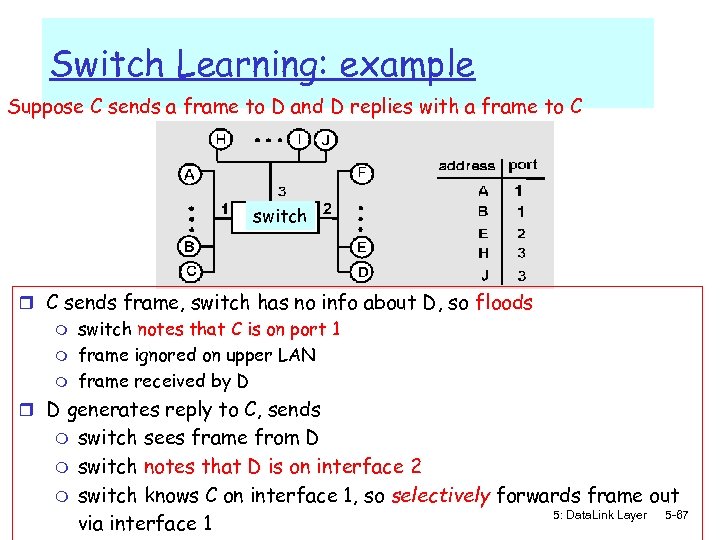 Switch Learning: example Suppose C sends a frame to D and D replies with a frame to C switch r C sends frame, switch has no info about D, so floods m m m switch notes that C is on port 1 frame ignored on upper LAN frame received by D r D generates reply to C, sends m m m switch sees frame from D switch notes that D is on interface 2 switch knows C on interface 1, so selectively forwards frame out 5: Data. Link Layer 5 -67 via interface 1
Switch Learning: example Suppose C sends a frame to D and D replies with a frame to C switch r C sends frame, switch has no info about D, so floods m m m switch notes that C is on port 1 frame ignored on upper LAN frame received by D r D generates reply to C, sends m m m switch sees frame from D switch notes that D is on interface 2 switch knows C on interface 1, so selectively forwards frame out 5: Data. Link Layer 5 -67 via interface 1
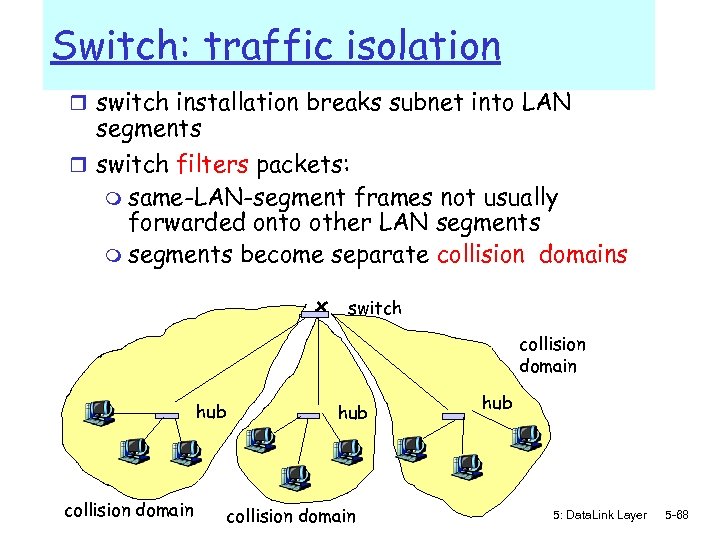 Switch: traffic isolation r switch installation breaks subnet into LAN segments r switch filters packets: m same-LAN-segment frames not usually forwarded onto other LAN segments m segments become separate collision domains switch collision domain hub 5: Data. Link Layer 5 -68
Switch: traffic isolation r switch installation breaks subnet into LAN segments r switch filters packets: m same-LAN-segment frames not usually forwarded onto other LAN segments m segments become separate collision domains switch collision domain hub 5: Data. Link Layer 5 -68
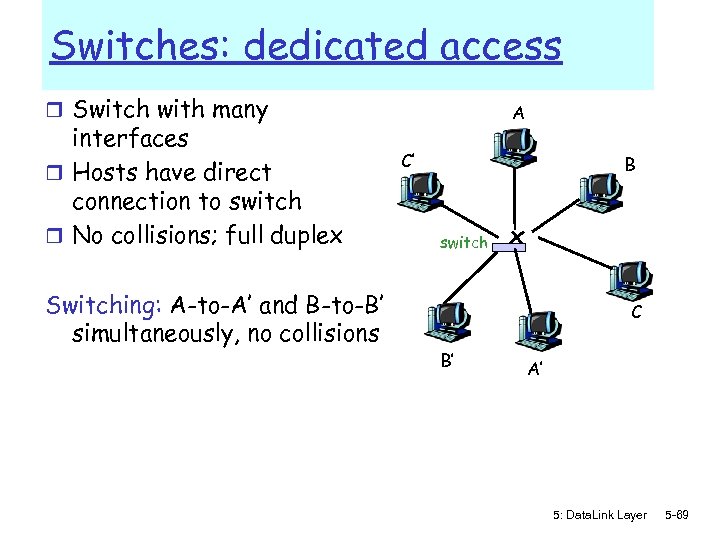 Switches: dedicated access r Switch with many interfaces r Hosts have direct connection to switch r No collisions; full duplex Switching: A-to-A’ and B-to-B’ simultaneously, no collisions A C’ B switch C B’ A’ 5: Data. Link Layer 5 -69
Switches: dedicated access r Switch with many interfaces r Hosts have direct connection to switch r No collisions; full duplex Switching: A-to-A’ and B-to-B’ simultaneously, no collisions A C’ B switch C B’ A’ 5: Data. Link Layer 5 -69
 More on Switches r cut-through switching: frame forwarded from input to output port without first collecting entire frame m slight reduction in latency r combinations of shared/dedicated, 10/1000 Mbps interfaces 5: Data. Link Layer 5 -70
More on Switches r cut-through switching: frame forwarded from input to output port without first collecting entire frame m slight reduction in latency r combinations of shared/dedicated, 10/1000 Mbps interfaces 5: Data. Link Layer 5 -70
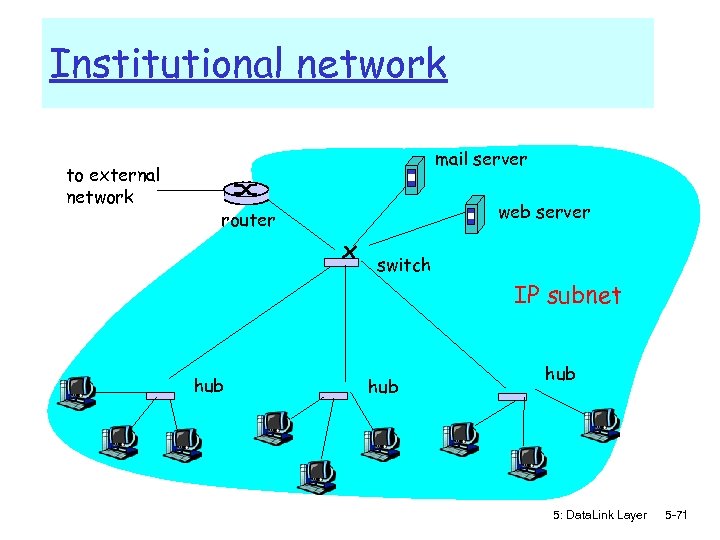 Institutional network to external network mail server web server router switch IP subnet hub hub 5: Data. Link Layer 5 -71
Institutional network to external network mail server web server router switch IP subnet hub hub 5: Data. Link Layer 5 -71
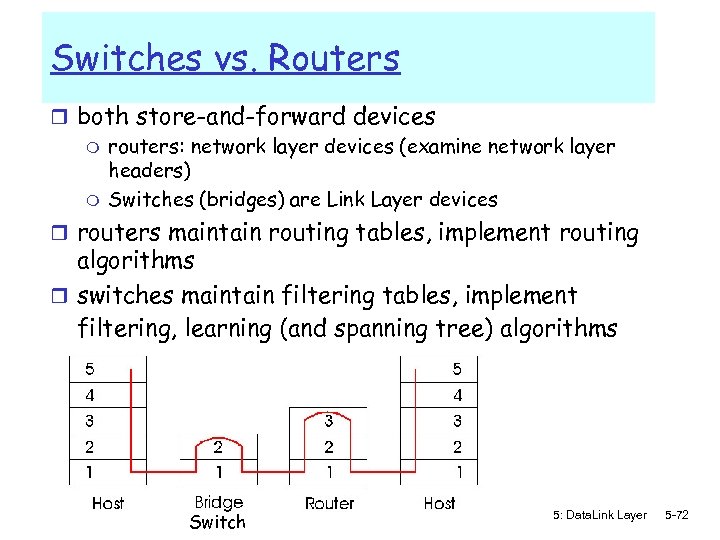 Switches vs. Routers r both store-and-forward devices m routers: network layer devices (examine network layer headers) m Switches (bridges) are Link Layer devices r routers maintain routing tables, implement routing algorithms r switches maintain filtering tables, implement filtering, learning (and spanning tree) algorithms Switch 5: Data. Link Layer 5 -72
Switches vs. Routers r both store-and-forward devices m routers: network layer devices (examine network layer headers) m Switches (bridges) are Link Layer devices r routers maintain routing tables, implement routing algorithms r switches maintain filtering tables, implement filtering, learning (and spanning tree) algorithms Switch 5: Data. Link Layer 5 -72
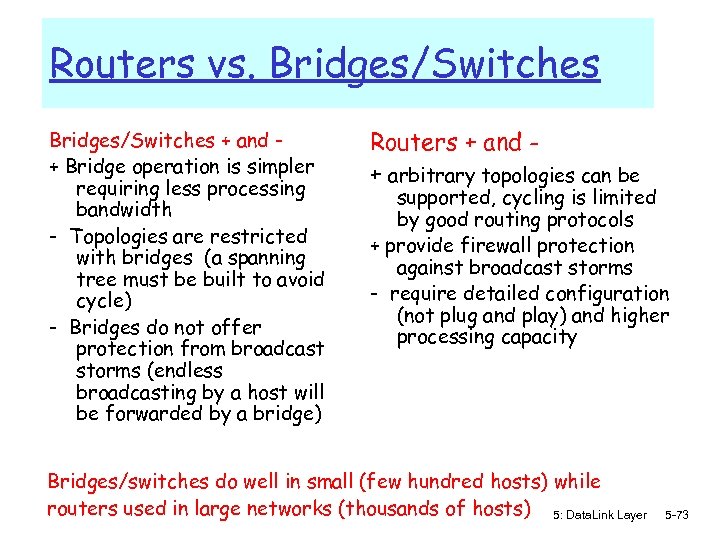 Routers vs. Bridges/Switches + and + Bridge operation is simpler requiring less processing bandwidth - Topologies are restricted with bridges (a spanning tree must be built to avoid cycle) - Bridges do not offer protection from broadcast storms (endless broadcasting by a host will be forwarded by a bridge) Routers + and + arbitrary topologies can be supported, cycling is limited by good routing protocols + provide firewall protection against broadcast storms - require detailed configuration (not plug and play) and higher processing capacity Bridges/switches do well in small (few hundred hosts) while routers used in large networks (thousands of hosts) 5: Data. Link Layer 5 -73
Routers vs. Bridges/Switches + and + Bridge operation is simpler requiring less processing bandwidth - Topologies are restricted with bridges (a spanning tree must be built to avoid cycle) - Bridges do not offer protection from broadcast storms (endless broadcasting by a host will be forwarded by a bridge) Routers + and + arbitrary topologies can be supported, cycling is limited by good routing protocols + provide firewall protection against broadcast storms - require detailed configuration (not plug and play) and higher processing capacity Bridges/switches do well in small (few hundred hosts) while routers used in large networks (thousands of hosts) 5: Data. Link Layer 5 -73
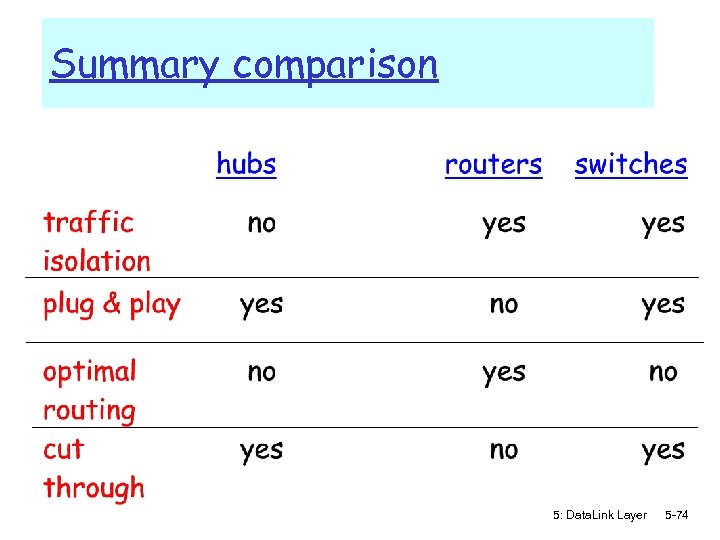 Summary comparison 5: Data. Link Layer 5 -74
Summary comparison 5: Data. Link Layer 5 -74
 Link Layer r 5. 1 Introduction and r r services 5. 2 Error detection and correction 5. 3 Multiple access protocols 5. 4 Link-Layer Addressing 5. 5 Ethernet r 5. 6 Hubs and switches r 5. 7 PPP r 5. 8 Virtualization 5: Data. Link Layer 5 -75
Link Layer r 5. 1 Introduction and r r services 5. 2 Error detection and correction 5. 3 Multiple access protocols 5. 4 Link-Layer Addressing 5. 5 Ethernet r 5. 6 Hubs and switches r 5. 7 PPP r 5. 8 Virtualization 5: Data. Link Layer 5 -75
 Point to Point Data Link Control r one sender, one receiver, one link: easier than broadcast link: m no Media Access Control m no need for explicit MAC addressing m e. g. , dialup link, ISDN line r popular point-to-point DLC protocols: m PPP (point-to-point protocol) m HDLC: High level data link control 5: Data. Link Layer 5 -76
Point to Point Data Link Control r one sender, one receiver, one link: easier than broadcast link: m no Media Access Control m no need for explicit MAC addressing m e. g. , dialup link, ISDN line r popular point-to-point DLC protocols: m PPP (point-to-point protocol) m HDLC: High level data link control 5: Data. Link Layer 5 -76
![PPP Design Requirements [RFC 1557] r packet framing: encapsulation of network-layer r r datagram PPP Design Requirements [RFC 1557] r packet framing: encapsulation of network-layer r r datagram](https://present5.com/presentation/b549f735156a18b00bbbcb597e525efe/image-77.jpg) PPP Design Requirements [RFC 1557] r packet framing: encapsulation of network-layer r r datagram in data link frame carry network layer data of any network layer protocol (not just IP) bit transparency: no constraints on bit pattern in the data field error detection (no correction) connection liveness: detect, signal link failure to network layer address negotiation: endpoint can learn/configure each other’s network address 5: Data. Link Layer 5 -77
PPP Design Requirements [RFC 1557] r packet framing: encapsulation of network-layer r r datagram in data link frame carry network layer data of any network layer protocol (not just IP) bit transparency: no constraints on bit pattern in the data field error detection (no correction) connection liveness: detect, signal link failure to network layer address negotiation: endpoint can learn/configure each other’s network address 5: Data. Link Layer 5 -77
 PPP non-requirements r no error correction/recovery r no flow control r out of order delivery OK r no need to support multipoint links (e. g. , polling) Error recovery, flow control, data re-ordering all relegated to higher layers! 5: Data. Link Layer 5 -78
PPP non-requirements r no error correction/recovery r no flow control r out of order delivery OK r no need to support multipoint links (e. g. , polling) Error recovery, flow control, data re-ordering all relegated to higher layers! 5: Data. Link Layer 5 -78
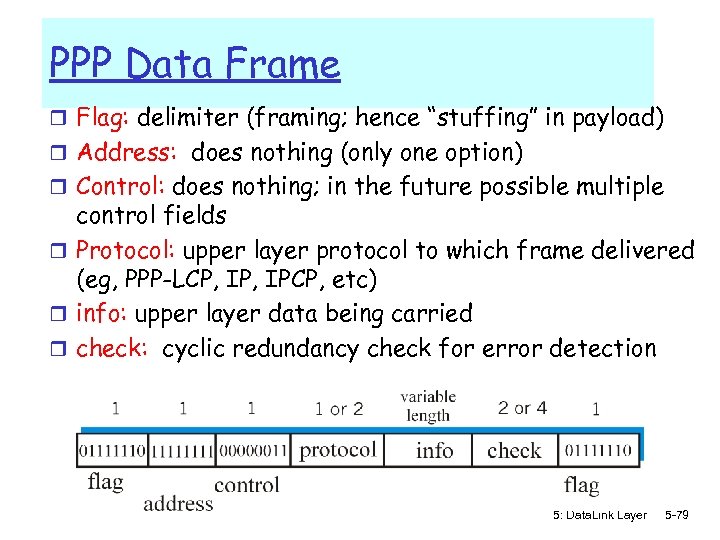 PPP Data Frame r Flag: delimiter (framing; hence “stuffing” in payload) r Address: does nothing (only one option) r Control: does nothing; in the future possible multiple control fields r Protocol: upper layer protocol to which frame delivered (eg, PPP-LCP, IPCP, etc) r info: upper layer data being carried r check: cyclic redundancy check for error detection 5: Data. Link Layer 5 -79
PPP Data Frame r Flag: delimiter (framing; hence “stuffing” in payload) r Address: does nothing (only one option) r Control: does nothing; in the future possible multiple control fields r Protocol: upper layer protocol to which frame delivered (eg, PPP-LCP, IPCP, etc) r info: upper layer data being carried r check: cyclic redundancy check for error detection 5: Data. Link Layer 5 -79
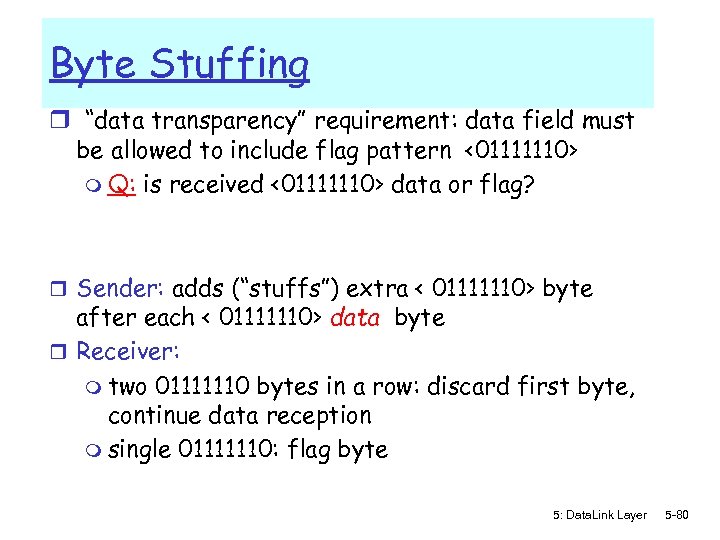 Byte Stuffing r “data transparency” requirement: data field must be allowed to include flag pattern <01111110> m Q: is received <01111110> data or flag? r Sender: adds (“stuffs”) extra < 01111110> byte after each < 01111110> data byte r Receiver: m two 01111110 bytes in a row: discard first byte, continue data reception m single 01111110: flag byte 5: Data. Link Layer 5 -80
Byte Stuffing r “data transparency” requirement: data field must be allowed to include flag pattern <01111110> m Q: is received <01111110> data or flag? r Sender: adds (“stuffs”) extra < 01111110> byte after each < 01111110> data byte r Receiver: m two 01111110 bytes in a row: discard first byte, continue data reception m single 01111110: flag byte 5: Data. Link Layer 5 -80
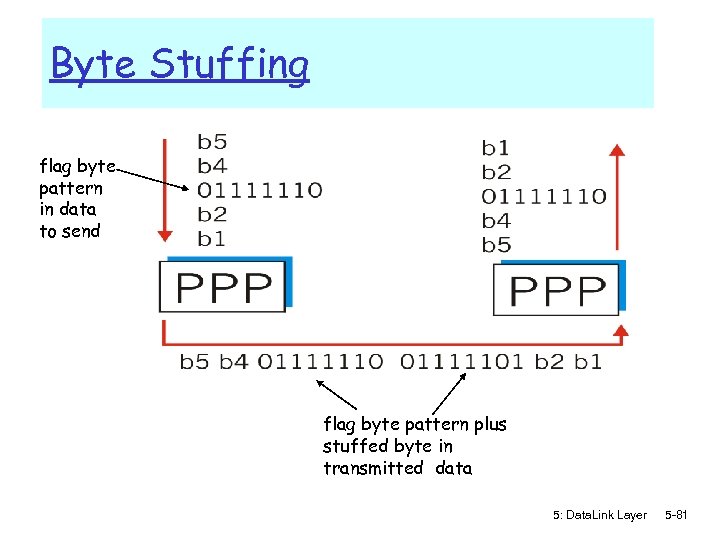 Byte Stuffing flag byte pattern in data to send flag byte pattern plus stuffed byte in transmitted data 5: Data. Link Layer 5 -81
Byte Stuffing flag byte pattern in data to send flag byte pattern plus stuffed byte in transmitted data 5: Data. Link Layer 5 -81
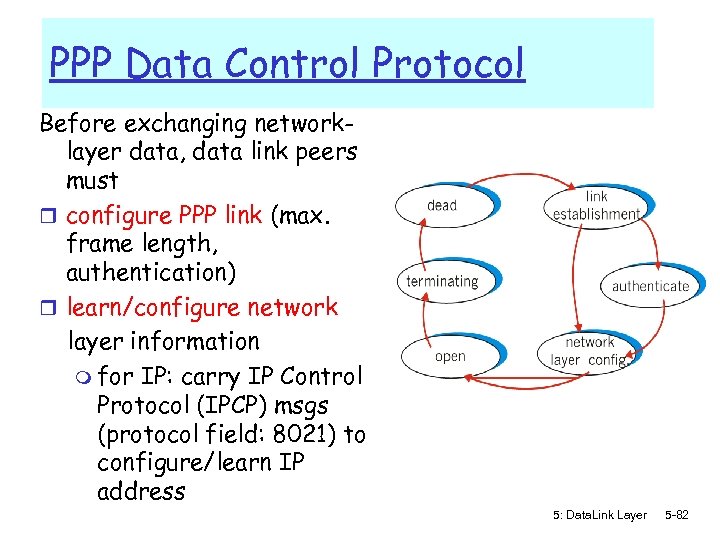 PPP Data Control Protocol Before exchanging networklayer data, data link peers must r configure PPP link (max. frame length, authentication) r learn/configure network layer information m for IP: carry IP Control Protocol (IPCP) msgs (protocol field: 8021) to configure/learn IP address 5: Data. Link Layer 5 -82
PPP Data Control Protocol Before exchanging networklayer data, data link peers must r configure PPP link (max. frame length, authentication) r learn/configure network layer information m for IP: carry IP Control Protocol (IPCP) msgs (protocol field: 8021) to configure/learn IP address 5: Data. Link Layer 5 -82
 Link Layer r 5. 1 Introduction and r r services 5. 2 Error detection and correction 5. 3 Multiple access protocols 5. 4 Link-Layer Addressing 5. 5 Ethernet r 5. 6 Hubs and switches r 5. 7 PPP r 5. 8 Virtualization 5: Data. Link Layer 5 -83
Link Layer r 5. 1 Introduction and r r services 5. 2 Error detection and correction 5. 3 Multiple access protocols 5. 4 Link-Layer Addressing 5. 5 Ethernet r 5. 6 Hubs and switches r 5. 7 PPP r 5. 8 Virtualization 5: Data. Link Layer 5 -83
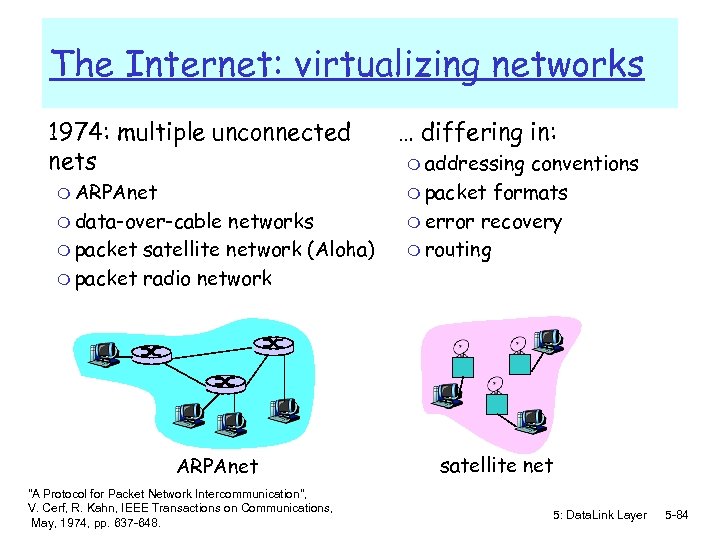 The Internet: virtualizing networks 1974: multiple unconnected nets m ARPAnet m data-over-cable networks m packet satellite network (Aloha) m packet radio network ARPAnet "A Protocol for Packet Network Intercommunication", V. Cerf, R. Kahn, IEEE Transactions on Communications, May, 1974, pp. 637 -648. … differing in: m addressing conventions m packet formats m error recovery m routing satellite net 5: Data. Link Layer 5 -84
The Internet: virtualizing networks 1974: multiple unconnected nets m ARPAnet m data-over-cable networks m packet satellite network (Aloha) m packet radio network ARPAnet "A Protocol for Packet Network Intercommunication", V. Cerf, R. Kahn, IEEE Transactions on Communications, May, 1974, pp. 637 -648. … differing in: m addressing conventions m packet formats m error recovery m routing satellite net 5: Data. Link Layer 5 -84
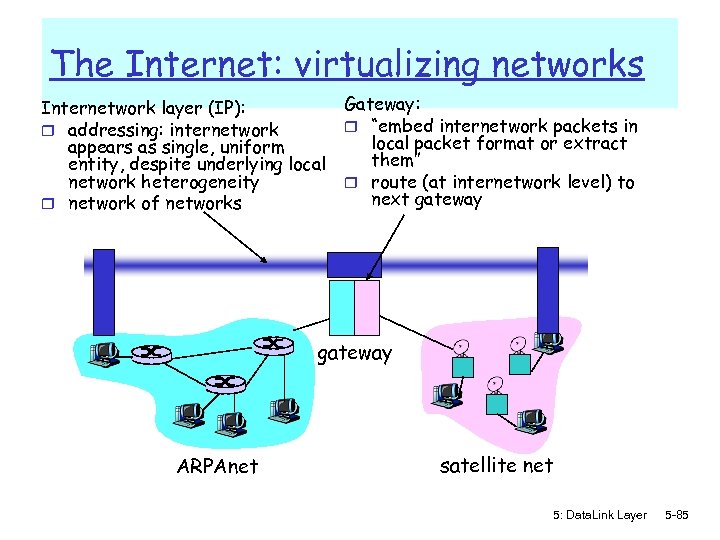 The Internet: virtualizing networks Internetwork layer (IP): r addressing: internetwork appears as single, uniform entity, despite underlying local network heterogeneity r network of networks Gateway: r “embed internetwork packets in local packet format or extract them” r route (at internetwork level) to next gateway ARPAnet satellite net 5: Data. Link Layer 5 -85
The Internet: virtualizing networks Internetwork layer (IP): r addressing: internetwork appears as single, uniform entity, despite underlying local network heterogeneity r network of networks Gateway: r “embed internetwork packets in local packet format or extract them” r route (at internetwork level) to next gateway ARPAnet satellite net 5: Data. Link Layer 5 -85
 Cerf & Kahn’s Internetwork Architecture What is virtualized? r two layers of addressing: internetwork and local network r new layer (IP) makes everything homogeneous at internetwork layer r underlying local network technology m cable m satellite m 56 K telephone modem m today: ATM, MPLS … “invisible” at internetwork layer. Looks like a link layer technology to IP! 5: Data. Link Layer 5 -86
Cerf & Kahn’s Internetwork Architecture What is virtualized? r two layers of addressing: internetwork and local network r new layer (IP) makes everything homogeneous at internetwork layer r underlying local network technology m cable m satellite m 56 K telephone modem m today: ATM, MPLS … “invisible” at internetwork layer. Looks like a link layer technology to IP! 5: Data. Link Layer 5 -86
 ATM and MPLS r ATM, MPLS separate networks in their own right m different service models, addressing, routing from Internet r viewed by Internet as logical link connecting IP routers m just like dialup link is really part of separate network (telephone network) r ATM, MPLS: of technical interest in their own right 5: Data. Link Layer 5 -87
ATM and MPLS r ATM, MPLS separate networks in their own right m different service models, addressing, routing from Internet r viewed by Internet as logical link connecting IP routers m just like dialup link is really part of separate network (telephone network) r ATM, MPLS: of technical interest in their own right 5: Data. Link Layer 5 -87
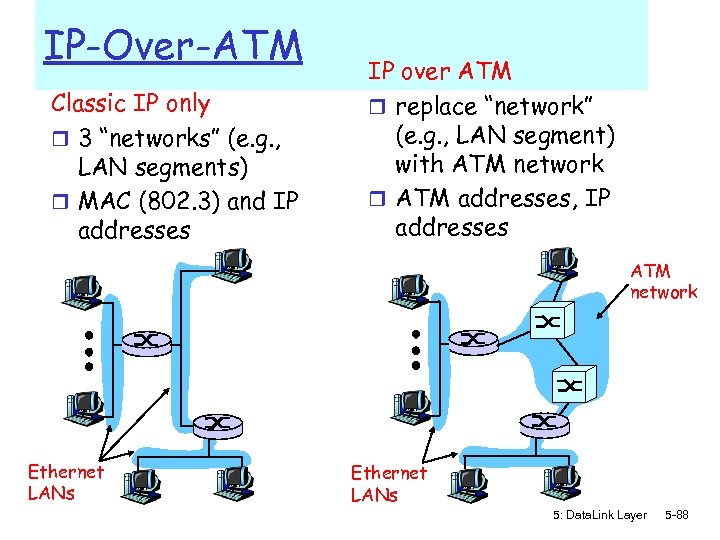 IP-Over-ATM Classic IP only r 3 “networks” (e. g. , LAN segments) r MAC (802. 3) and IP addresses IP over ATM r replace “network” (e. g. , LAN segment) with ATM network r ATM addresses, IP addresses ATM network Ethernet LANs 5: Data. Link Layer 5 -88
IP-Over-ATM Classic IP only r 3 “networks” (e. g. , LAN segments) r MAC (802. 3) and IP addresses IP over ATM r replace “network” (e. g. , LAN segment) with ATM network r ATM addresses, IP addresses ATM network Ethernet LANs 5: Data. Link Layer 5 -88
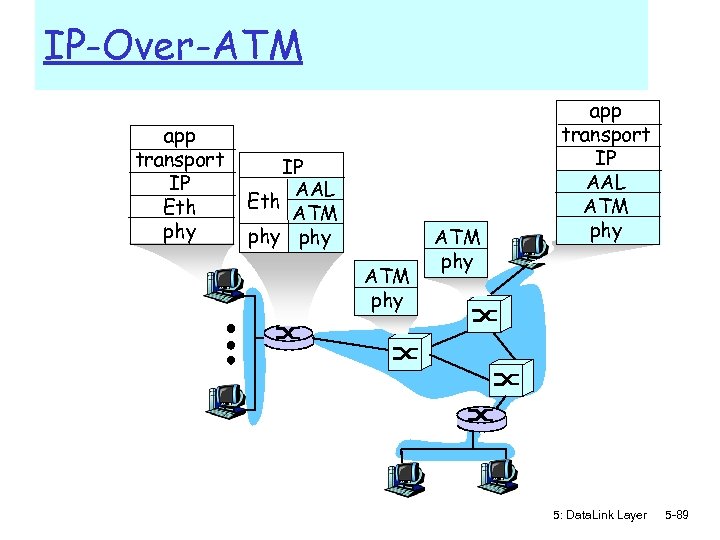 IP-Over-ATM app transport IP Eth phy IP AAL Eth ATM phy app transport IP AAL ATM phy 5: Data. Link Layer 5 -89
IP-Over-ATM app transport IP Eth phy IP AAL Eth ATM phy app transport IP AAL ATM phy 5: Data. Link Layer 5 -89
 Datagram Journey in IP-over-ATM Network r at Source Host: m IP layer maps between IP, ATM dest address (using ARP) m passes datagram to AAL 5 m AAL 5 encapsulates data, segments cells, passes to ATM layer r ATM network: moves cell along VC to destination r at Destination Host: m AAL 5 reassembles cells into original datagram m if CRC OK, datagram is passed to IP 5: Data. Link Layer 5 -90
Datagram Journey in IP-over-ATM Network r at Source Host: m IP layer maps between IP, ATM dest address (using ARP) m passes datagram to AAL 5 m AAL 5 encapsulates data, segments cells, passes to ATM layer r ATM network: moves cell along VC to destination r at Destination Host: m AAL 5 reassembles cells into original datagram m if CRC OK, datagram is passed to IP 5: Data. Link Layer 5 -90
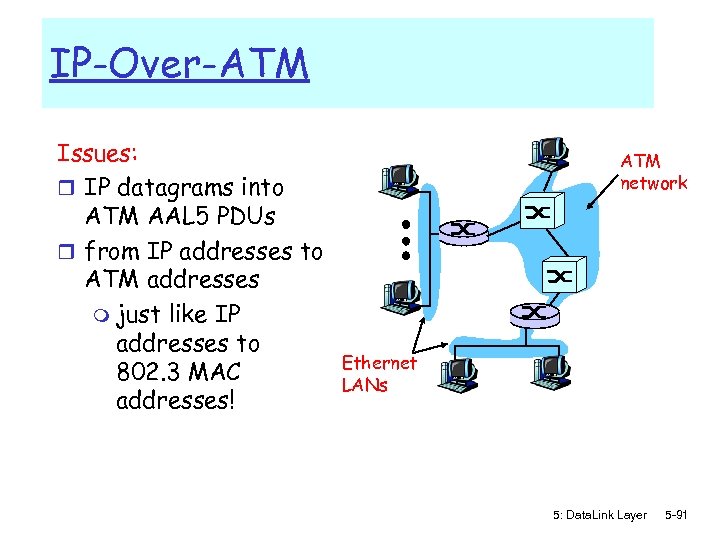 IP-Over-ATM Issues: r IP datagrams into ATM AAL 5 PDUs r from IP addresses to ATM addresses m just like IP addresses to 802. 3 MAC addresses! ATM network Ethernet LANs 5: Data. Link Layer 5 -91
IP-Over-ATM Issues: r IP datagrams into ATM AAL 5 PDUs r from IP addresses to ATM addresses m just like IP addresses to 802. 3 MAC addresses! ATM network Ethernet LANs 5: Data. Link Layer 5 -91
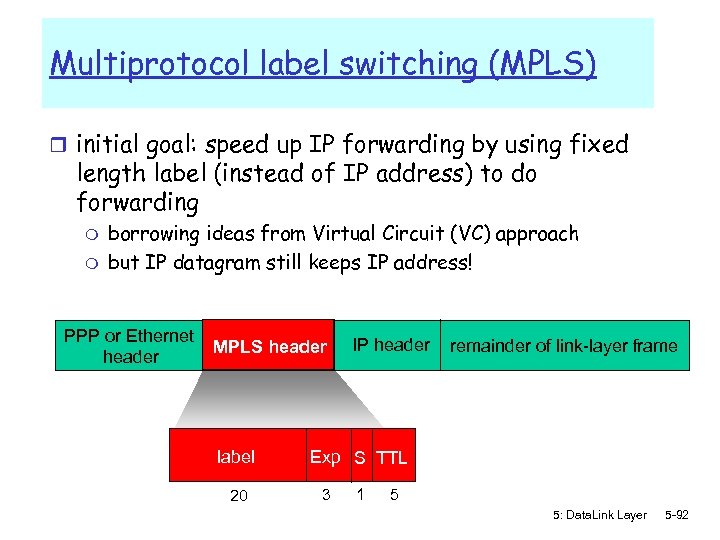 Multiprotocol label switching (MPLS) r initial goal: speed up IP forwarding by using fixed length label (instead of IP address) to do forwarding m m borrowing ideas from Virtual Circuit (VC) approach but IP datagram still keeps IP address! PPP or Ethernet header MPLS header label 20 IP header remainder of link-layer frame Exp S TTL 3 1 5 5: Data. Link Layer 5 -92
Multiprotocol label switching (MPLS) r initial goal: speed up IP forwarding by using fixed length label (instead of IP address) to do forwarding m m borrowing ideas from Virtual Circuit (VC) approach but IP datagram still keeps IP address! PPP or Ethernet header MPLS header label 20 IP header remainder of link-layer frame Exp S TTL 3 1 5 5: Data. Link Layer 5 -92
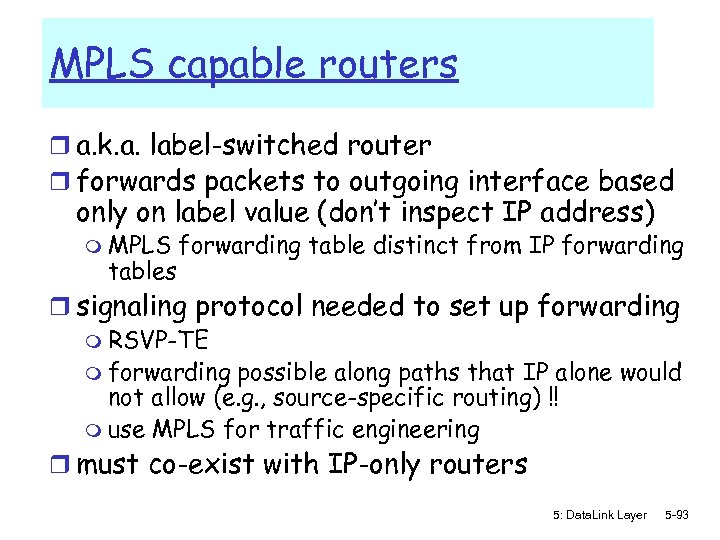 MPLS capable routers r a. k. a. label-switched router r forwards packets to outgoing interface based only on label value (don’t inspect IP address) m MPLS tables forwarding table distinct from IP forwarding r signaling protocol needed to set up forwarding m RSVP-TE m forwarding possible along paths that IP alone would not allow (e. g. , source-specific routing) !! m use MPLS for traffic engineering r must co-exist with IP-only routers 5: Data. Link Layer 5 -93
MPLS capable routers r a. k. a. label-switched router r forwards packets to outgoing interface based only on label value (don’t inspect IP address) m MPLS tables forwarding table distinct from IP forwarding r signaling protocol needed to set up forwarding m RSVP-TE m forwarding possible along paths that IP alone would not allow (e. g. , source-specific routing) !! m use MPLS for traffic engineering r must co-exist with IP-only routers 5: Data. Link Layer 5 -93
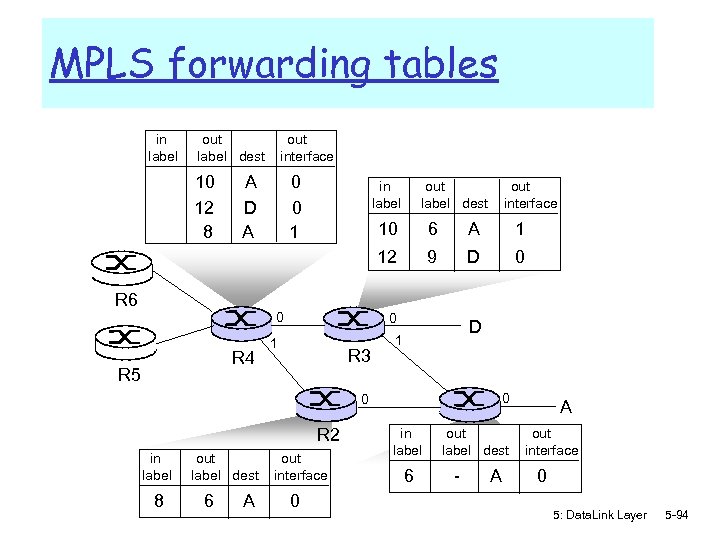 MPLS forwarding tables in label out label dest 10 12 8 out interface A D A 0 0 1 in label out label dest out interface 0 R 4 R 5 6 A 1 12 R 6 10 9 D 0 0 1 R 3 D 1 0 0 R 2 in label 8 out label dest 6 A out interface 0 in label 6 out. R 1 label dest - A A out interface 0 5: Data. Link Layer 5 -94
MPLS forwarding tables in label out label dest 10 12 8 out interface A D A 0 0 1 in label out label dest out interface 0 R 4 R 5 6 A 1 12 R 6 10 9 D 0 0 1 R 3 D 1 0 0 R 2 in label 8 out label dest 6 A out interface 0 in label 6 out. R 1 label dest - A A out interface 0 5: Data. Link Layer 5 -94
 Chapter 5: Summary r principles behind data link layer services: m error detection, correction m sharing a broadcast channel: multiple access m link layer addressing r instantiation and implementation of various link layer technologies m Ethernet m switched LANS m PPP m Link Virtualization: ATM and MPLS 5: Data. Link Layer 5 -95
Chapter 5: Summary r principles behind data link layer services: m error detection, correction m sharing a broadcast channel: multiple access m link layer addressing r instantiation and implementation of various link layer technologies m Ethernet m switched LANS m PPP m Link Virtualization: ATM and MPLS 5: Data. Link Layer 5 -95


