53fae780b468adc9276ebfca2f5c4c0b.ppt
- Количество слайдов: 32
 Chapter 30 Message Security, User Authentication, and Key Management Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2004
Chapter 30 Message Security, User Authentication, and Key Management Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2004
 Applications of Cryptography n Message Security n n User Authentication n n It involves confidentiality, integrity, authentication and finally non-repudiation. It means verifying the identity of the person or process that wants to communicate with a system. Key management n Mc. Graw-Hill It involves the distribution of symmetric keys and the certification of the public keys. ©The Mc. Graw-Hill Companies, Inc. , 2004
Applications of Cryptography n Message Security n n User Authentication n n It involves confidentiality, integrity, authentication and finally non-repudiation. It means verifying the identity of the person or process that wants to communicate with a system. Key management n Mc. Graw-Hill It involves the distribution of symmetric keys and the certification of the public keys. ©The Mc. Graw-Hill Companies, Inc. , 2004
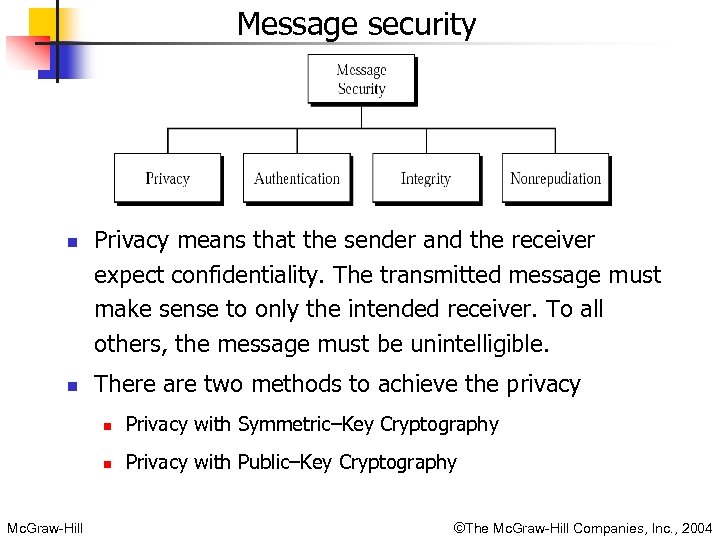 Message security n n Privacy means that the sender and the receiver expect confidentiality. The transmitted message must make sense to only the intended receiver. To all others, the message must be unintelligible. There are two methods to achieve the privacy n n Mc. Graw-Hill Privacy with Symmetric–Key Cryptography Privacy with Public–Key Cryptography ©The Mc. Graw-Hill Companies, Inc. , 2004
Message security n n Privacy means that the sender and the receiver expect confidentiality. The transmitted message must make sense to only the intended receiver. To all others, the message must be unintelligible. There are two methods to achieve the privacy n n Mc. Graw-Hill Privacy with Symmetric–Key Cryptography Privacy with Public–Key Cryptography ©The Mc. Graw-Hill Companies, Inc. , 2004
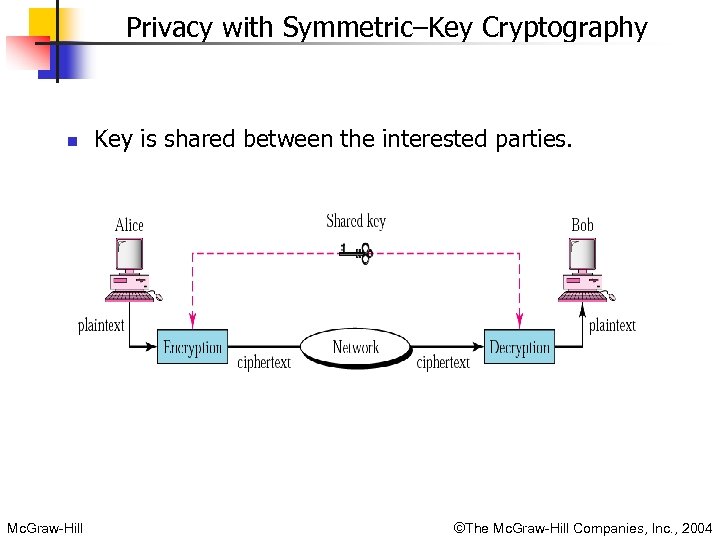 Privacy with Symmetric–Key Cryptography n Mc. Graw-Hill Key is shared between the interested parties. ©The Mc. Graw-Hill Companies, Inc. , 2004
Privacy with Symmetric–Key Cryptography n Mc. Graw-Hill Key is shared between the interested parties. ©The Mc. Graw-Hill Companies, Inc. , 2004
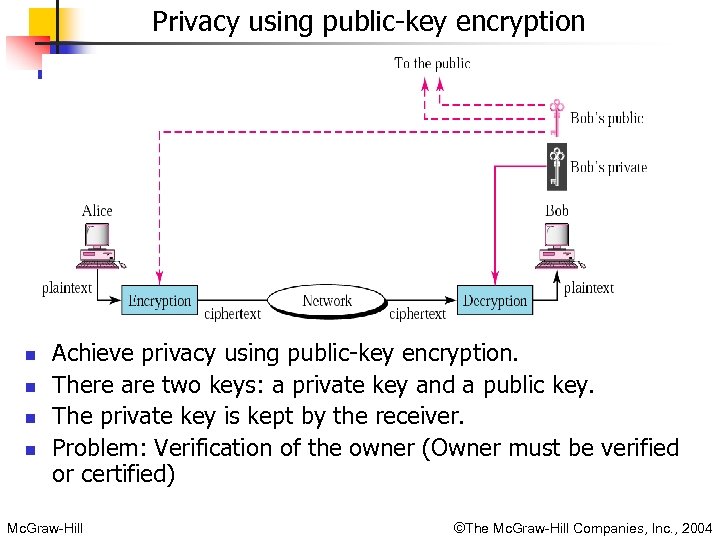 Privacy using public-key encryption n n Achieve privacy using public-key encryption. There are two keys: a private key and a public key. The private key is kept by the receiver. Problem: Verification of the owner (Owner must be verified or certified) Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2004
Privacy using public-key encryption n n Achieve privacy using public-key encryption. There are two keys: a private key and a public key. The private key is kept by the receiver. Problem: Verification of the owner (Owner must be verified or certified) Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2004
 Message Security (cont. ) n Message Authentication: Receiver needs to be sure of n Integrity: the sender’s identity and that an imposter has not sent the message. n Using Digital signature. n n n Data must arrive at the receiver exactly as they were sent. Using Digital Signature. Non-repudiation: n n n Mc. Graw-Hill Receiver must be able to prove that a received message came from a specific sender. The sender must not be able to deny sending a message that he or she, in fact, did send. The burden of proof falls on the receiver. ©The Mc. Graw-Hill Companies, Inc. , 2004
Message Security (cont. ) n Message Authentication: Receiver needs to be sure of n Integrity: the sender’s identity and that an imposter has not sent the message. n Using Digital signature. n n n Data must arrive at the receiver exactly as they were sent. Using Digital Signature. Non-repudiation: n n n Mc. Graw-Hill Receiver must be able to prove that a received message came from a specific sender. The sender must not be able to deny sending a message that he or she, in fact, did send. The burden of proof falls on the receiver. ©The Mc. Graw-Hill Companies, Inc. , 2004
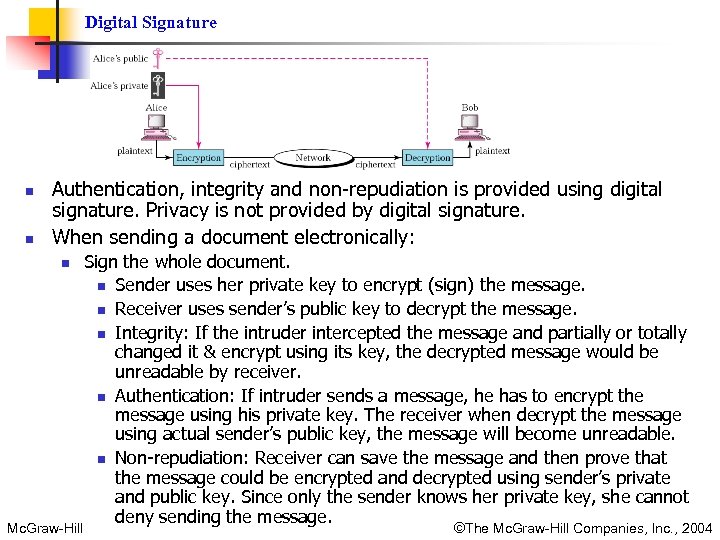 Digital Signature n n Authentication, integrity and non-repudiation is provided using digital signature. Privacy is not provided by digital signature. When sending a document electronically: n Mc. Graw-Hill Sign the whole document. n Sender uses her private key to encrypt (sign) the message. n Receiver uses sender’s public key to decrypt the message. n Integrity: If the intruder intercepted the message and partially or totally changed it & encrypt using its key, the decrypted message would be unreadable by receiver. n Authentication: If intruder sends a message, he has to encrypt the message using his private key. The receiver when decrypt the message using actual sender’s public key, the message will become unreadable. n Non-repudiation: Receiver can save the message and then prove that the message could be encrypted and decrypted using sender’s private and public key. Since only the sender knows her private key, she cannot deny sending the message. ©The Mc. Graw-Hill Companies, Inc. , 2004
Digital Signature n n Authentication, integrity and non-repudiation is provided using digital signature. Privacy is not provided by digital signature. When sending a document electronically: n Mc. Graw-Hill Sign the whole document. n Sender uses her private key to encrypt (sign) the message. n Receiver uses sender’s public key to decrypt the message. n Integrity: If the intruder intercepted the message and partially or totally changed it & encrypt using its key, the decrypted message would be unreadable by receiver. n Authentication: If intruder sends a message, he has to encrypt the message using his private key. The receiver when decrypt the message using actual sender’s public key, the message will become unreadable. n Non-repudiation: Receiver can save the message and then prove that the message could be encrypted and decrypted using sender’s private and public key. Since only the sender knows her private key, she cannot deny sending the message. ©The Mc. Graw-Hill Companies, Inc. , 2004
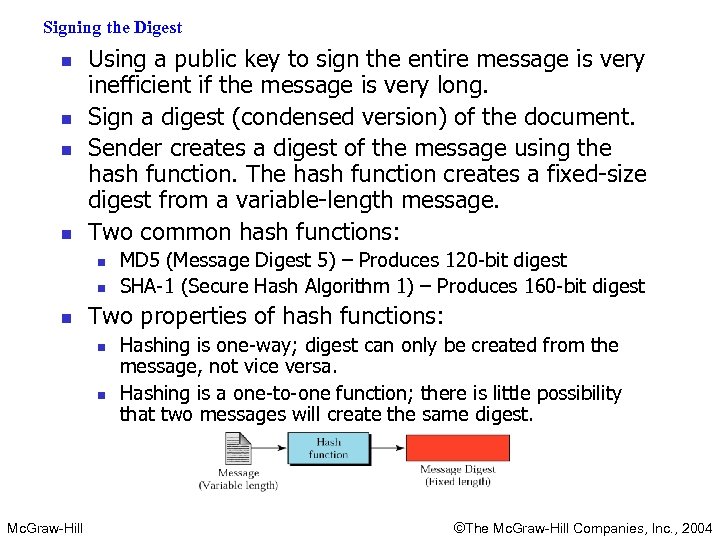 Signing the Digest n n Using a public key to sign the entire message is very inefficient if the message is very long. Sign a digest (condensed version) of the document. Sender creates a digest of the message using the hash function. The hash function creates a fixed-size digest from a variable-length message. Two common hash functions: n n n Two properties of hash functions: n n Mc. Graw-Hill MD 5 (Message Digest 5) – Produces 120 -bit digest SHA-1 (Secure Hash Algorithm 1) – Produces 160 -bit digest Hashing is one-way; digest can only be created from the message, not vice versa. Hashing is a one-to-one function; there is little possibility that two messages will create the same digest. ©The Mc. Graw-Hill Companies, Inc. , 2004
Signing the Digest n n Using a public key to sign the entire message is very inefficient if the message is very long. Sign a digest (condensed version) of the document. Sender creates a digest of the message using the hash function. The hash function creates a fixed-size digest from a variable-length message. Two common hash functions: n n n Two properties of hash functions: n n Mc. Graw-Hill MD 5 (Message Digest 5) – Produces 120 -bit digest SHA-1 (Secure Hash Algorithm 1) – Produces 160 -bit digest Hashing is one-way; digest can only be created from the message, not vice versa. Hashing is a one-to-one function; there is little possibility that two messages will create the same digest. ©The Mc. Graw-Hill Companies, Inc. , 2004
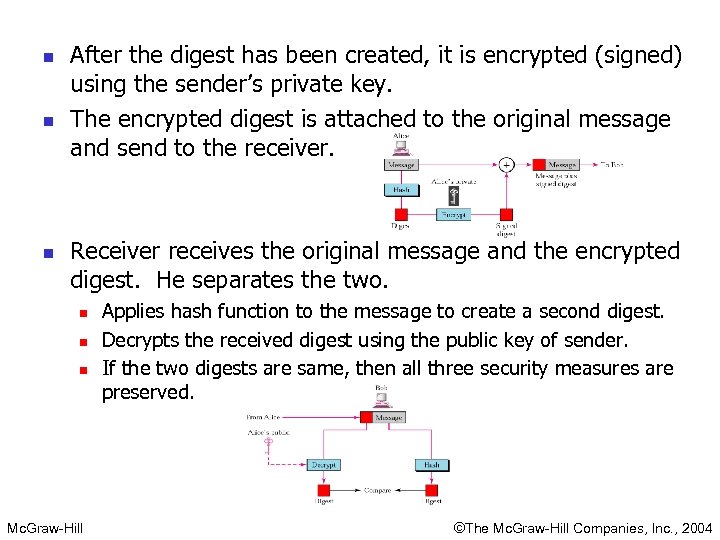 n n n After the digest has been created, it is encrypted (signed) using the sender’s private key. The encrypted digest is attached to the original message and send to the receiver. Receiver receives the original message and the encrypted digest. He separates the two. n n n Mc. Graw-Hill Applies hash function to the message to create a second digest. Decrypts the received digest using the public key of sender. If the two digests are same, then all three security measures are preserved. ©The Mc. Graw-Hill Companies, Inc. , 2004
n n n After the digest has been created, it is encrypted (signed) using the sender’s private key. The encrypted digest is attached to the original message and send to the receiver. Receiver receives the original message and the encrypted digest. He separates the two. n n n Mc. Graw-Hill Applies hash function to the message to create a second digest. Decrypts the received digest using the public key of sender. If the two digests are same, then all three security measures are preserved. ©The Mc. Graw-Hill Companies, Inc. , 2004
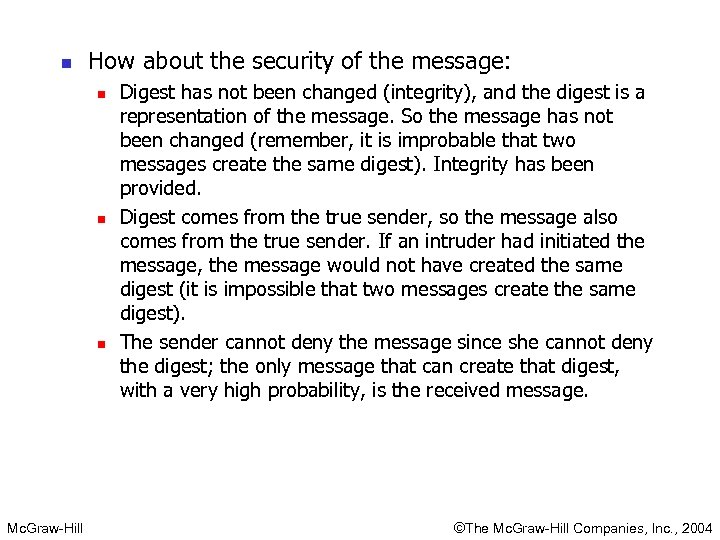 n How about the security of the message: n n n Mc. Graw-Hill Digest has not been changed (integrity), and the digest is a representation of the message. So the message has not been changed (remember, it is improbable that two messages create the same digest). Integrity has been provided. Digest comes from the true sender, so the message also comes from the true sender. If an intruder had initiated the message, the message would not have created the same digest (it is impossible that two messages create the same digest). The sender cannot deny the message since she cannot deny the digest; the only message that can create that digest, with a very high probability, is the received message. ©The Mc. Graw-Hill Companies, Inc. , 2004
n How about the security of the message: n n n Mc. Graw-Hill Digest has not been changed (integrity), and the digest is a representation of the message. So the message has not been changed (remember, it is improbable that two messages create the same digest). Integrity has been provided. Digest comes from the true sender, so the message also comes from the true sender. If an intruder had initiated the message, the message would not have created the same digest (it is impossible that two messages create the same digest). The sender cannot deny the message since she cannot deny the digest; the only message that can create that digest, with a very high probability, is the received message. ©The Mc. Graw-Hill Companies, Inc. , 2004
 User Authentication n Mc. Graw-Hill Verifies the identity of one entity for another. An entity can be person, a process, a client, or a server. In message authentication, the identity of the sender is verified for each single message. In user authentication, the user identity is verified once for the entire duration of system access. ©The Mc. Graw-Hill Companies, Inc. , 2004
User Authentication n Mc. Graw-Hill Verifies the identity of one entity for another. An entity can be person, a process, a client, or a server. In message authentication, the identity of the sender is verified for each single message. In user authentication, the user identity is verified once for the entire duration of system access. ©The Mc. Graw-Hill Companies, Inc. , 2004
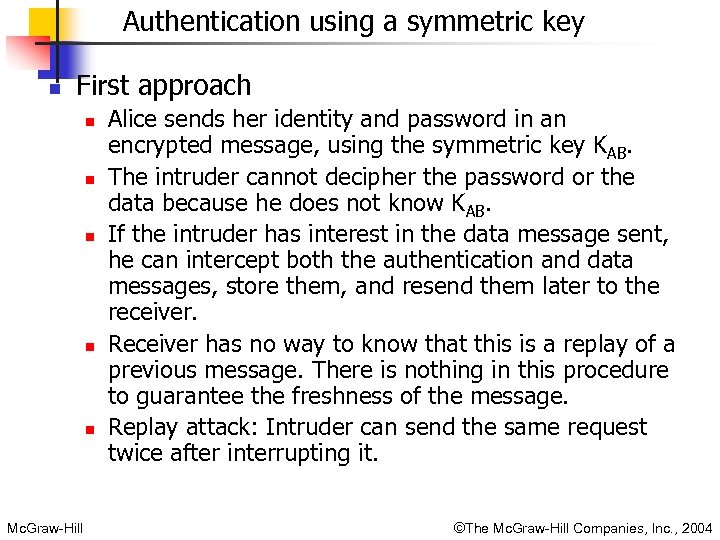 Authentication using a symmetric key n First approach n n n Mc. Graw-Hill Alice sends her identity and password in an encrypted message, using the symmetric key KAB. The intruder cannot decipher the password or the data because he does not know KAB. If the intruder has interest in the data message sent, he can intercept both the authentication and data messages, store them, and resend them later to the receiver. Receiver has no way to know that this is a replay of a previous message. There is nothing in this procedure to guarantee the freshness of the message. Replay attack: Intruder can send the same request twice after interrupting it. ©The Mc. Graw-Hill Companies, Inc. , 2004
Authentication using a symmetric key n First approach n n n Mc. Graw-Hill Alice sends her identity and password in an encrypted message, using the symmetric key KAB. The intruder cannot decipher the password or the data because he does not know KAB. If the intruder has interest in the data message sent, he can intercept both the authentication and data messages, store them, and resend them later to the receiver. Receiver has no way to know that this is a replay of a previous message. There is nothing in this procedure to guarantee the freshness of the message. Replay attack: Intruder can send the same request twice after interrupting it. ©The Mc. Graw-Hill Companies, Inc. , 2004
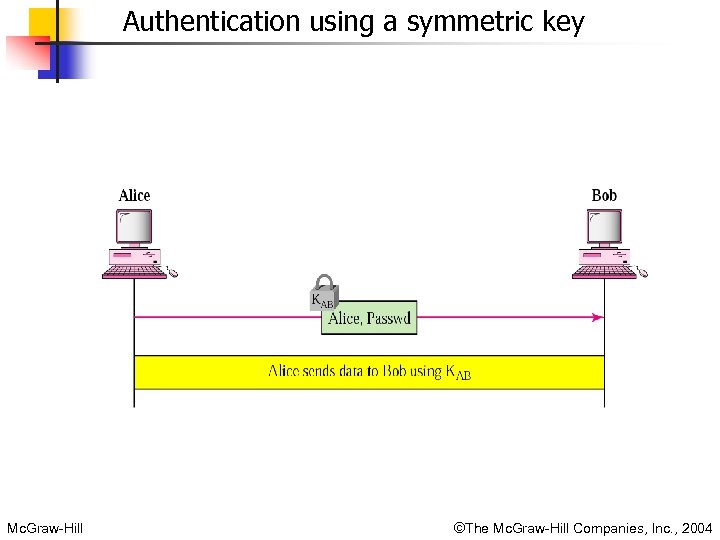 Authentication using a symmetric key Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2004
Authentication using a symmetric key Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2004
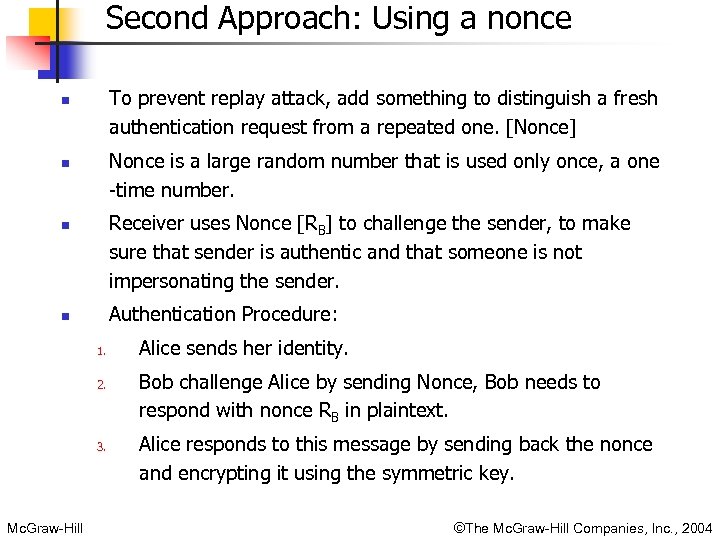 Second Approach: Using a nonce To prevent replay attack, add something to distinguish a fresh authentication request from a repeated one. [Nonce] n Nonce is a large random number that is used only once, a one -time number. n Receiver uses Nonce [RB] to challenge the sender, to make sure that sender is authentic and that someone is not impersonating the sender. n Authentication Procedure: n 1. 2. 3. Mc. Graw-Hill Alice sends her identity. Bob challenge Alice by sending Nonce, Bob needs to respond with nonce RB in plaintext. Alice responds to this message by sending back the nonce and encrypting it using the symmetric key. ©The Mc. Graw-Hill Companies, Inc. , 2004
Second Approach: Using a nonce To prevent replay attack, add something to distinguish a fresh authentication request from a repeated one. [Nonce] n Nonce is a large random number that is used only once, a one -time number. n Receiver uses Nonce [RB] to challenge the sender, to make sure that sender is authentic and that someone is not impersonating the sender. n Authentication Procedure: n 1. 2. 3. Mc. Graw-Hill Alice sends her identity. Bob challenge Alice by sending Nonce, Bob needs to respond with nonce RB in plaintext. Alice responds to this message by sending back the nonce and encrypting it using the symmetric key. ©The Mc. Graw-Hill Companies, Inc. , 2004
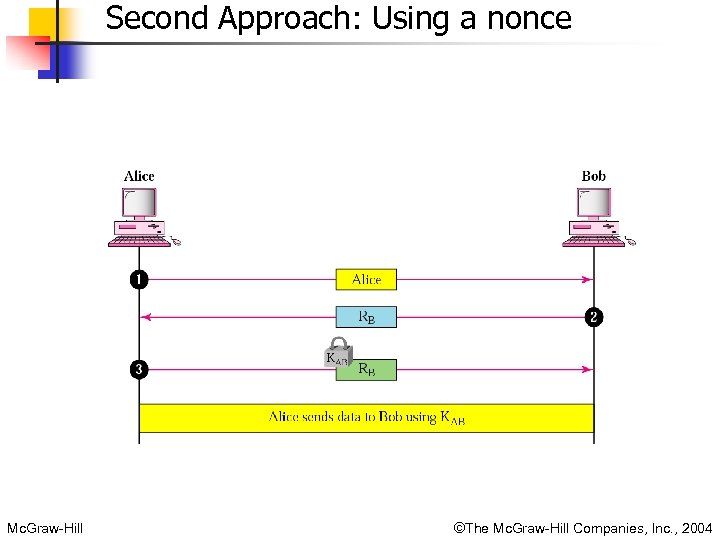 Second Approach: Using a nonce Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2004
Second Approach: Using a nonce Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2004
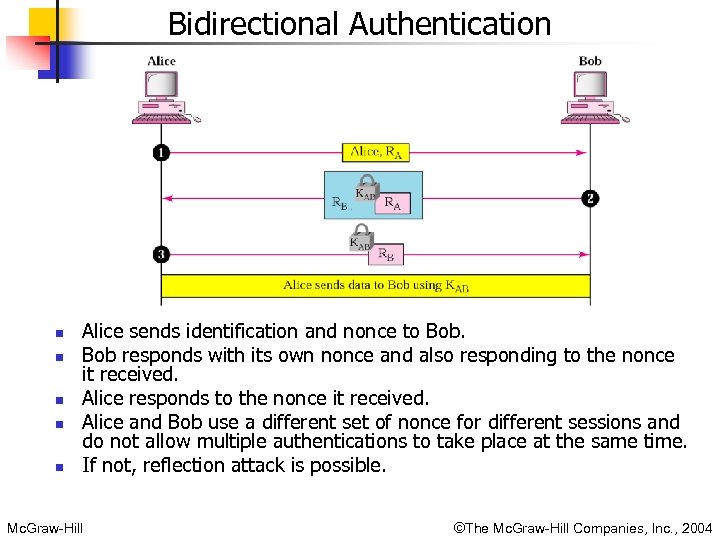 Bidirectional Authentication n n Alice sends identification and nonce to Bob responds with its own nonce and also responding to the nonce it received. Alice responds to the nonce it received. Alice and Bob use a different set of nonce for different sessions and do not allow multiple authentications to take place at the same time. If not, reflection attack is possible. Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2004
Bidirectional Authentication n n Alice sends identification and nonce to Bob responds with its own nonce and also responding to the nonce it received. Alice responds to the nonce it received. Alice and Bob use a different set of nonce for different sessions and do not allow multiple authentications to take place at the same time. If not, reflection attack is possible. Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2004
 User authentication with public-key cryptography n n Mc. Graw-Hill Sender can encrypt the message with its private key and let Receiver use Sender’s public key to decrypt the message and authenticate the sender. An intruder can announce its public key to the receiver in place of sender. Intruder can then encrypt the message containing a nonce with its private key. Receiver decrypts it with intruder’s public key, which he believes is Sender’s. An intruder can fool the receiver. Verification of Sender’s key is needed. ©The Mc. Graw-Hill Companies, Inc. , 2004
User authentication with public-key cryptography n n Mc. Graw-Hill Sender can encrypt the message with its private key and let Receiver use Sender’s public key to decrypt the message and authenticate the sender. An intruder can announce its public key to the receiver in place of sender. Intruder can then encrypt the message containing a nonce with its private key. Receiver decrypts it with intruder’s public key, which he believes is Sender’s. An intruder can fool the receiver. Verification of Sender’s key is needed. ©The Mc. Graw-Hill Companies, Inc. , 2004
 Key Management n n How symmetric keys are distributed and how public keys are certified. Symmetric key distribution n n Mc. Graw-Hill If n people want to communicate with one another, there is a need for n(n-1)/2 symmetric keys. If n is large, number of keys needed will be very huge. In a group of n people, each person must have and remember n-1 keys, one of every other person in the group. How can two parties securely acquire the shared key? It cannot be done over phone or Internet; these are not secure. Symmetric key between two parties is useful if it is used only once; it must be created for one session and destroyed when the session is over. ©The Mc. Graw-Hill Companies, Inc. , 2004
Key Management n n How symmetric keys are distributed and how public keys are certified. Symmetric key distribution n n Mc. Graw-Hill If n people want to communicate with one another, there is a need for n(n-1)/2 symmetric keys. If n is large, number of keys needed will be very huge. In a group of n people, each person must have and remember n-1 keys, one of every other person in the group. How can two parties securely acquire the shared key? It cannot be done over phone or Internet; these are not secure. Symmetric key between two parties is useful if it is used only once; it must be created for one session and destroyed when the session is over. ©The Mc. Graw-Hill Companies, Inc. , 2004
 n Diffie-Hellman Method n n One-time session key for two parties. Session key needed not be stored or remembered. Parties do not have to meet to agree on the key, it can be done through the Internet. Pre-requisite n n Mc. Graw-Hill Two parties choose two numbers N and G N is a large prime number with restriction that (N-1)/2 must also be a prime number. G is also a prime number. These numbers are not confidential and so they can be shared via Internet or made public ©The Mc. Graw-Hill Companies, Inc. , 2004
n Diffie-Hellman Method n n One-time session key for two parties. Session key needed not be stored or remembered. Parties do not have to meet to agree on the key, it can be done through the Internet. Pre-requisite n n Mc. Graw-Hill Two parties choose two numbers N and G N is a large prime number with restriction that (N-1)/2 must also be a prime number. G is also a prime number. These numbers are not confidential and so they can be shared via Internet or made public ©The Mc. Graw-Hill Companies, Inc. , 2004
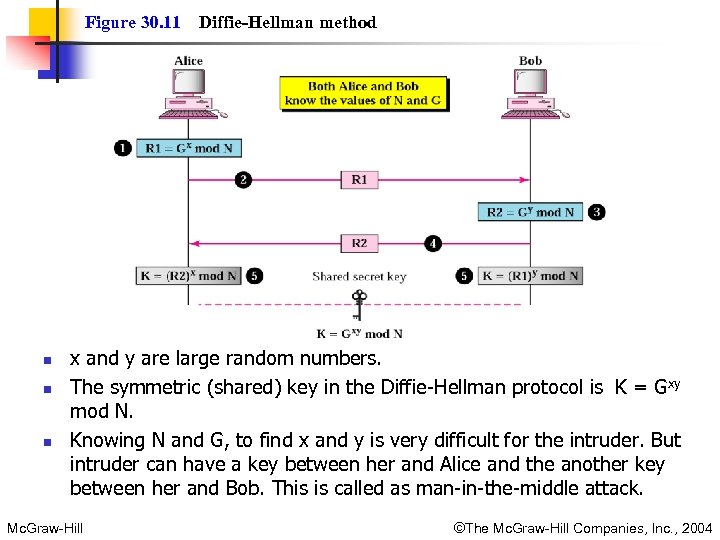 Figure 30. 11 n n n Diffie-Hellman method x and y are large random numbers. The symmetric (shared) key in the Diffie-Hellman protocol is K = Gxy mod N. Knowing N and G, to find x and y is very difficult for the intruder. But intruder can have a key between her and Alice and the another key between her and Bob. This is called as man-in-the-middle attack. Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2004
Figure 30. 11 n n n Diffie-Hellman method x and y are large random numbers. The symmetric (shared) key in the Diffie-Hellman protocol is K = Gxy mod N. Knowing N and G, to find x and y is very difficult for the intruder. But intruder can have a key between her and Alice and the another key between her and Bob. This is called as man-in-the-middle attack. Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2004
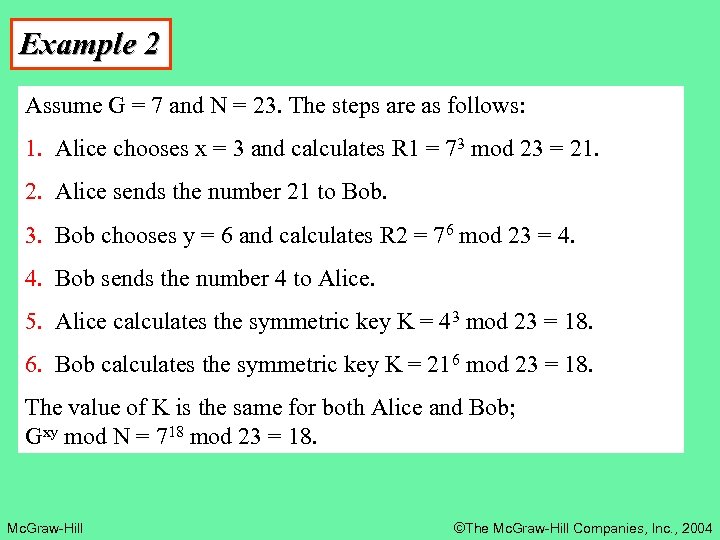 Example 2 Assume G = 7 and N = 23. The steps are as follows: 1. Alice chooses x = 3 and calculates R 1 = 73 mod 23 = 21. 2. Alice sends the number 21 to Bob. 3. Bob chooses y = 6 and calculates R 2 = 76 mod 23 = 4. 4. Bob sends the number 4 to Alice. 5. Alice calculates the symmetric key K = 43 mod 23 = 18. 6. Bob calculates the symmetric key K = 216 mod 23 = 18. The value of K is the same for both Alice and Bob; Gxy mod N = 718 mod 23 = 18. Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2004
Example 2 Assume G = 7 and N = 23. The steps are as follows: 1. Alice chooses x = 3 and calculates R 1 = 73 mod 23 = 21. 2. Alice sends the number 21 to Bob. 3. Bob chooses y = 6 and calculates R 2 = 76 mod 23 = 4. 4. Bob sends the number 4 to Alice. 5. Alice calculates the symmetric key K = 43 mod 23 = 18. 6. Bob calculates the symmetric key K = 216 mod 23 = 18. The value of K is the same for both Alice and Bob; Gxy mod N = 718 mod 23 = 18. Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2004
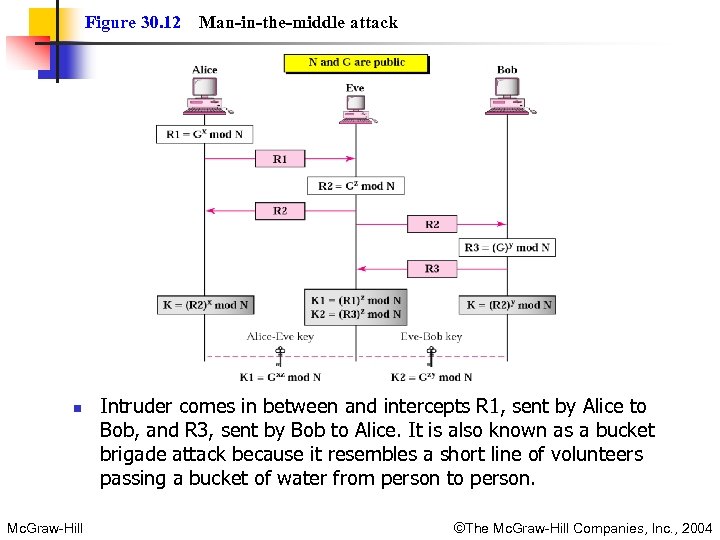 Figure 30. 12 n Mc. Graw-Hill Man-in-the-middle attack Intruder comes in between and intercepts R 1, sent by Alice to Bob, and R 3, sent by Bob to Alice. It is also known as a bucket brigade attack because it resembles a short line of volunteers passing a bucket of water from person to person. ©The Mc. Graw-Hill Companies, Inc. , 2004
Figure 30. 12 n Mc. Graw-Hill Man-in-the-middle attack Intruder comes in between and intercepts R 1, sent by Alice to Bob, and R 3, sent by Bob to Alice. It is also known as a bucket brigade attack because it resembles a short line of volunteers passing a bucket of water from person to person. ©The Mc. Graw-Hill Companies, Inc. , 2004
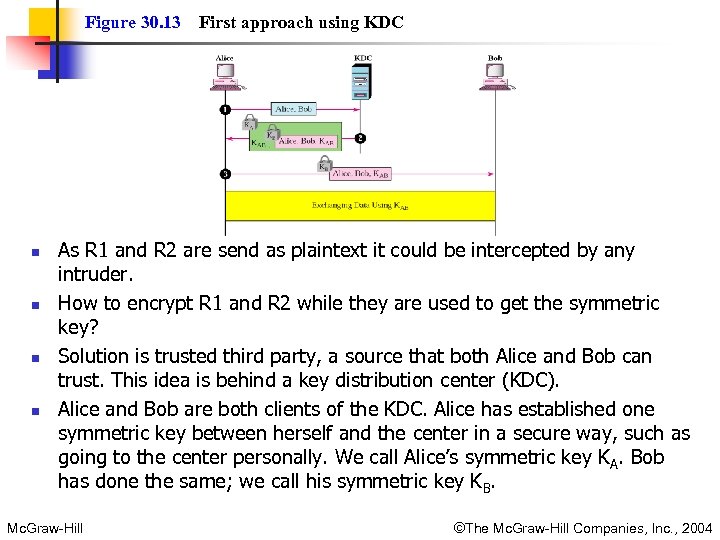 Figure 30. 13 n n First approach using KDC As R 1 and R 2 are send as plaintext it could be intercepted by any intruder. How to encrypt R 1 and R 2 while they are used to get the symmetric key? Solution is trusted third party, a source that both Alice and Bob can trust. This idea is behind a key distribution center (KDC). Alice and Bob are both clients of the KDC. Alice has established one symmetric key between herself and the center in a secure way, such as going to the center personally. We call Alice’s symmetric key KA. Bob has done the same; we call his symmetric key KB. Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2004
Figure 30. 13 n n First approach using KDC As R 1 and R 2 are send as plaintext it could be intercepted by any intruder. How to encrypt R 1 and R 2 while they are used to get the symmetric key? Solution is trusted third party, a source that both Alice and Bob can trust. This idea is behind a key distribution center (KDC). Alice and Bob are both clients of the KDC. Alice has established one symmetric key between herself and the center in a secure way, such as going to the center personally. We call Alice’s symmetric key KA. Bob has done the same; we call his symmetric key KB. Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2004
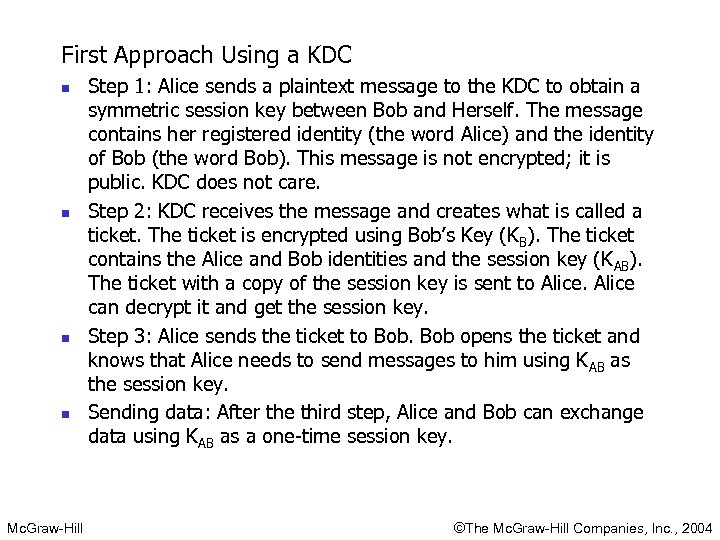 First Approach Using a KDC n n Mc. Graw-Hill Step 1: Alice sends a plaintext message to the KDC to obtain a symmetric session key between Bob and Herself. The message contains her registered identity (the word Alice) and the identity of Bob (the word Bob). This message is not encrypted; it is public. KDC does not care. Step 2: KDC receives the message and creates what is called a ticket. The ticket is encrypted using Bob’s Key (KB). The ticket contains the Alice and Bob identities and the session key (K AB). The ticket with a copy of the session key is sent to Alice can decrypt it and get the session key. Step 3: Alice sends the ticket to Bob opens the ticket and knows that Alice needs to send messages to him using KAB as the session key. Sending data: After the third step, Alice and Bob can exchange data using KAB as a one-time session key. ©The Mc. Graw-Hill Companies, Inc. , 2004
First Approach Using a KDC n n Mc. Graw-Hill Step 1: Alice sends a plaintext message to the KDC to obtain a symmetric session key between Bob and Herself. The message contains her registered identity (the word Alice) and the identity of Bob (the word Bob). This message is not encrypted; it is public. KDC does not care. Step 2: KDC receives the message and creates what is called a ticket. The ticket is encrypted using Bob’s Key (KB). The ticket contains the Alice and Bob identities and the session key (K AB). The ticket with a copy of the session key is sent to Alice can decrypt it and get the session key. Step 3: Alice sends the ticket to Bob opens the ticket and knows that Alice needs to send messages to him using KAB as the session key. Sending data: After the third step, Alice and Bob can exchange data using KAB as a one-time session key. ©The Mc. Graw-Hill Companies, Inc. , 2004
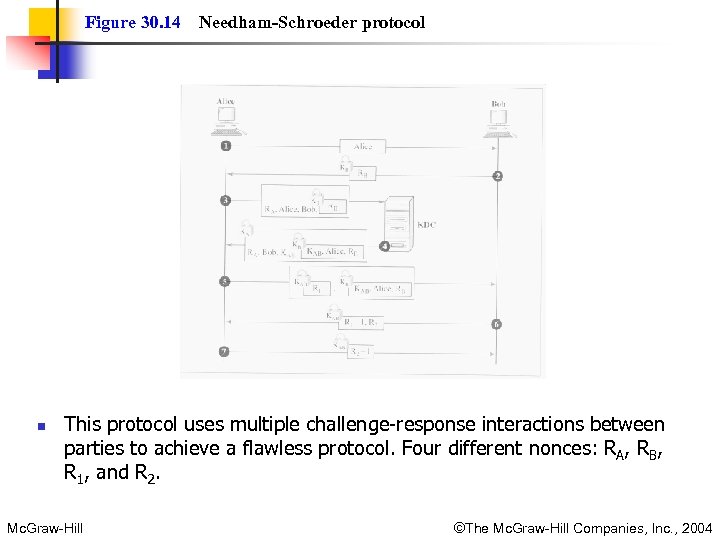 Figure 30. 14 n Needham-Schroeder protocol This protocol uses multiple challenge-response interactions between parties to achieve a flawless protocol. Four different nonces: RA, RB, R 1, and R 2. Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2004
Figure 30. 14 n Needham-Schroeder protocol This protocol uses multiple challenge-response interactions between parties to achieve a flawless protocol. Four different nonces: RA, RB, R 1, and R 2. Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2004
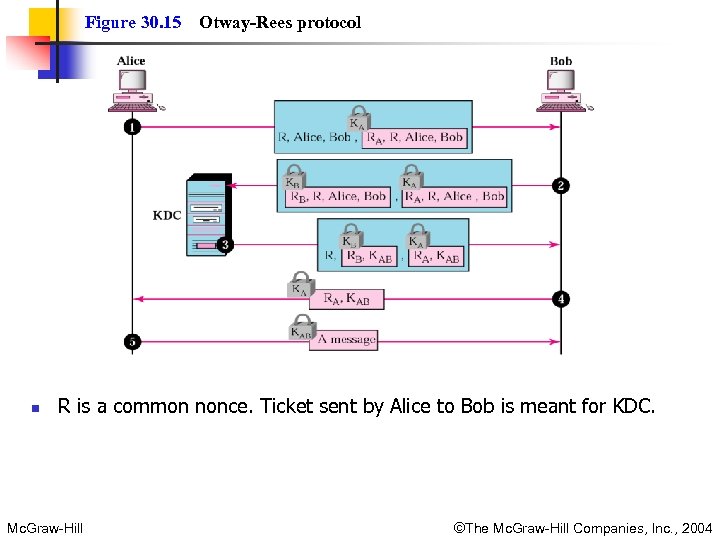 Figure 30. 15 n Otway-Rees protocol R is a common nonce. Ticket sent by Alice to Bob is meant for KDC. Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2004
Figure 30. 15 n Otway-Rees protocol R is a common nonce. Ticket sent by Alice to Bob is meant for KDC. Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2004
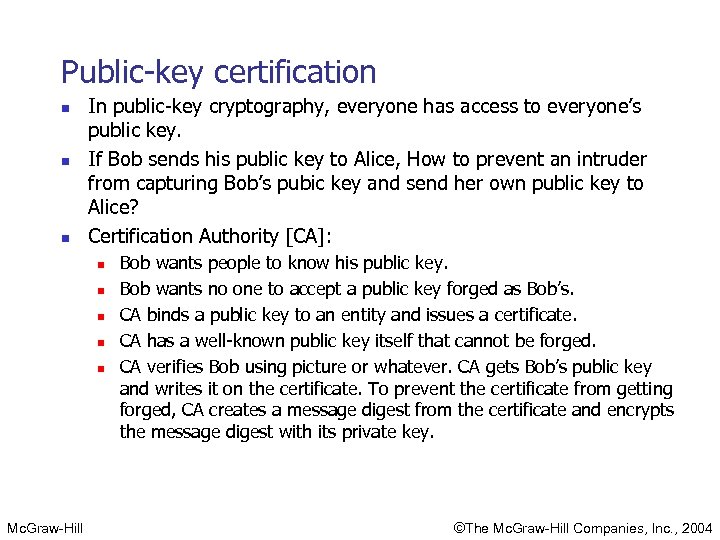 Public-key certification n In public-key cryptography, everyone has access to everyone’s public key. If Bob sends his public key to Alice, How to prevent an intruder from capturing Bob’s pubic key and send her own public key to Alice? Certification Authority [CA]: n n n Mc. Graw-Hill Bob wants people to know his public key. Bob wants no one to accept a public key forged as Bob’s. CA binds a public key to an entity and issues a certificate. CA has a well-known public key itself that cannot be forged. CA verifies Bob using picture or whatever. CA gets Bob’s public key and writes it on the certificate. To prevent the certificate from getting forged, CA creates a message digest from the certificate and encrypts the message digest with its private key. ©The Mc. Graw-Hill Companies, Inc. , 2004
Public-key certification n In public-key cryptography, everyone has access to everyone’s public key. If Bob sends his public key to Alice, How to prevent an intruder from capturing Bob’s pubic key and send her own public key to Alice? Certification Authority [CA]: n n n Mc. Graw-Hill Bob wants people to know his public key. Bob wants no one to accept a public key forged as Bob’s. CA binds a public key to an entity and issues a certificate. CA has a well-known public key itself that cannot be forged. CA verifies Bob using picture or whatever. CA gets Bob’s public key and writes it on the certificate. To prevent the certificate from getting forged, CA creates a message digest from the certificate and encrypts the message digest with its private key. ©The Mc. Graw-Hill Companies, Inc. , 2004
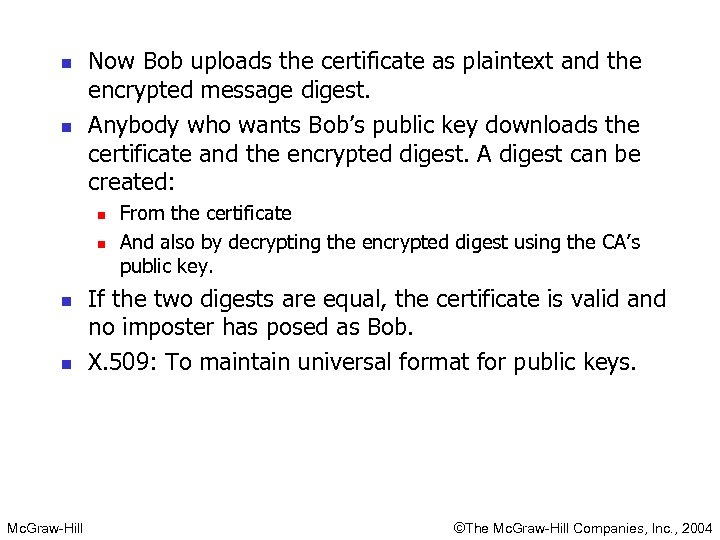 n n Now Bob uploads the certificate as plaintext and the encrypted message digest. Anybody who wants Bob’s public key downloads the certificate and the encrypted digest. A digest can be created: n n Mc. Graw-Hill From the certificate And also by decrypting the encrypted digest using the CA’s public key. If the two digests are equal, the certificate is valid and no imposter has posed as Bob. X. 509: To maintain universal format for public keys. ©The Mc. Graw-Hill Companies, Inc. , 2004
n n Now Bob uploads the certificate as plaintext and the encrypted message digest. Anybody who wants Bob’s public key downloads the certificate and the encrypted digest. A digest can be created: n n Mc. Graw-Hill From the certificate And also by decrypting the encrypted digest using the CA’s public key. If the two digests are equal, the certificate is valid and no imposter has posed as Bob. X. 509: To maintain universal format for public keys. ©The Mc. Graw-Hill Companies, Inc. , 2004
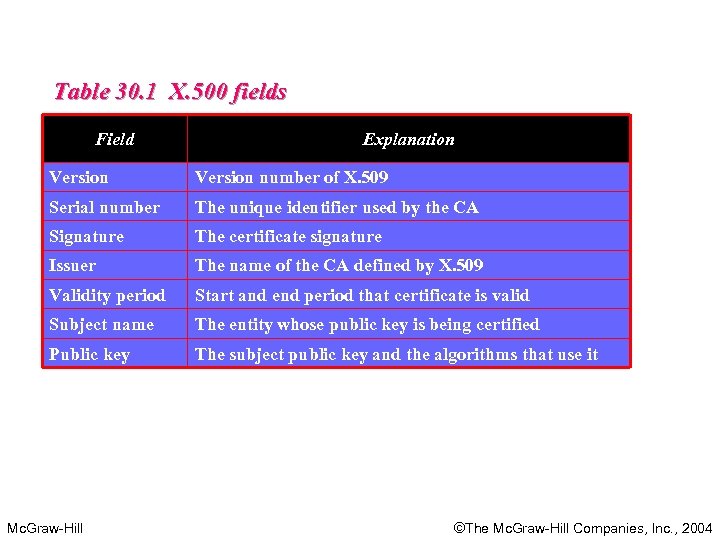 Table 30. 1 X. 500 fields Field Explanation Version number of X. 509 Serial number The unique identifier used by the CA Signature The certificate signature Issuer The name of the CA defined by X. 509 Validity period Start and end period that certificate is valid Subject name The entity whose public key is being certified Public key The subject public key and the algorithms that use it Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2004
Table 30. 1 X. 500 fields Field Explanation Version number of X. 509 Serial number The unique identifier used by the CA Signature The certificate signature Issuer The name of the CA defined by X. 509 Validity period Start and end period that certificate is valid Subject name The entity whose public key is being certified Public key The subject public key and the algorithms that use it Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2004
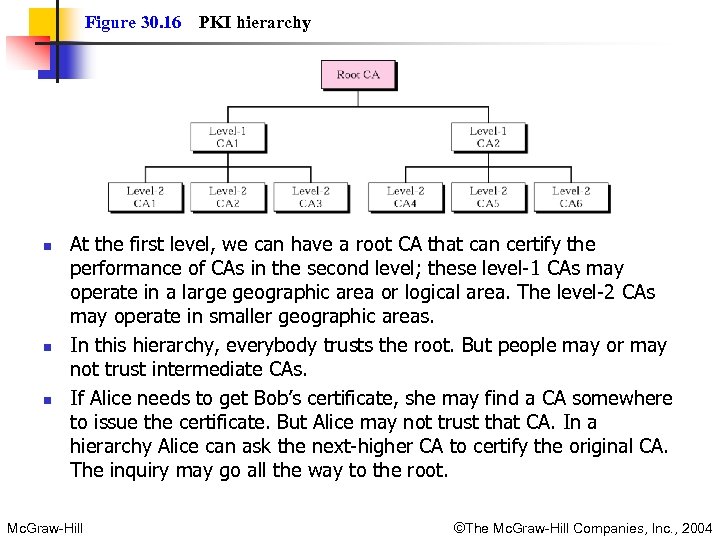 Figure 30. 16 n n n PKI hierarchy At the first level, we can have a root CA that can certify the performance of CAs in the second level; these level-1 CAs may operate in a large geographic area or logical area. The level-2 CAs may operate in smaller geographic areas. In this hierarchy, everybody trusts the root. But people may or may not trust intermediate CAs. If Alice needs to get Bob’s certificate, she may find a CA somewhere to issue the certificate. But Alice may not trust that CA. In a hierarchy Alice can ask the next-higher CA to certify the original CA. The inquiry may go all the way to the root. Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2004
Figure 30. 16 n n n PKI hierarchy At the first level, we can have a root CA that can certify the performance of CAs in the second level; these level-1 CAs may operate in a large geographic area or logical area. The level-2 CAs may operate in smaller geographic areas. In this hierarchy, everybody trusts the root. But people may or may not trust intermediate CAs. If Alice needs to get Bob’s certificate, she may find a CA somewhere to issue the certificate. But Alice may not trust that CA. In a hierarchy Alice can ask the next-higher CA to certify the original CA. The inquiry may go all the way to the root. Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2004
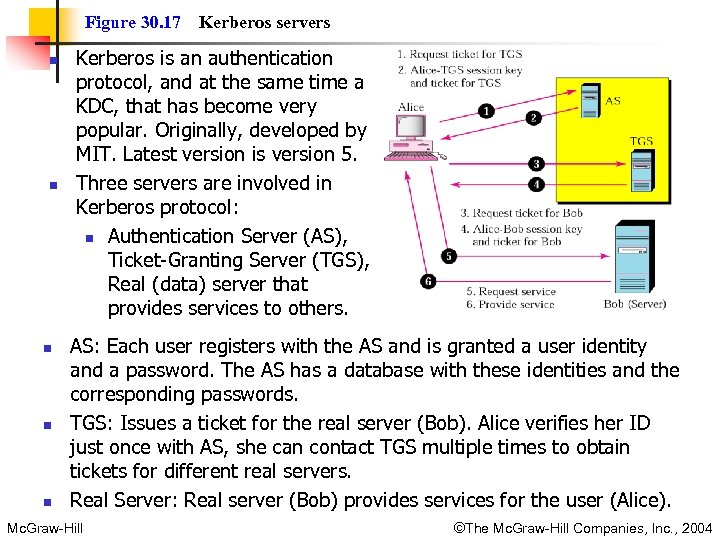 Figure 30. 17 n n n Kerberos servers Kerberos is an authentication protocol, and at the same time a KDC, that has become very popular. Originally, developed by MIT. Latest version is version 5. Three servers are involved in Kerberos protocol: n Authentication Server (AS), Ticket-Granting Server (TGS), Real (data) server that provides services to others. AS: Each user registers with the AS and is granted a user identity and a password. The AS has a database with these identities and the corresponding passwords. TGS: Issues a ticket for the real server (Bob). Alice verifies her ID just once with AS, she can contact TGS multiple times to obtain tickets for different real servers. Real Server: Real server (Bob) provides services for the user (Alice). Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2004
Figure 30. 17 n n n Kerberos servers Kerberos is an authentication protocol, and at the same time a KDC, that has become very popular. Originally, developed by MIT. Latest version is version 5. Three servers are involved in Kerberos protocol: n Authentication Server (AS), Ticket-Granting Server (TGS), Real (data) server that provides services to others. AS: Each user registers with the AS and is granted a user identity and a password. The AS has a database with these identities and the corresponding passwords. TGS: Issues a ticket for the real server (Bob). Alice verifies her ID just once with AS, she can contact TGS multiple times to obtain tickets for different real servers. Real Server: Real server (Bob) provides services for the user (Alice). Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2004
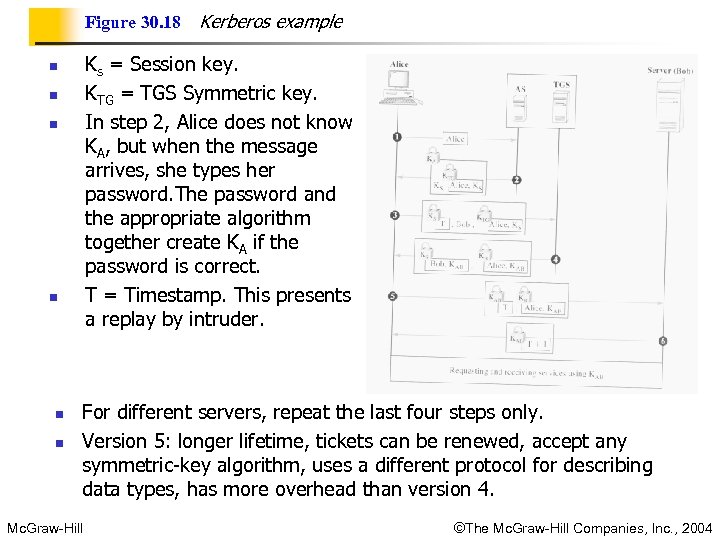 Figure 30. 18 Ks = Session key. KTG = TGS Symmetric key. In step 2, Alice does not know KA, but when the message arrives, she types her password. The password and the appropriate algorithm together create KA if the password is correct. T = Timestamp. This presents a replay by intruder. n n n Kerberos example For different servers, repeat the last four steps only. Version 5: longer lifetime, tickets can be renewed, accept any symmetric-key algorithm, uses a different protocol for describing data types, has more overhead than version 4. Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2004
Figure 30. 18 Ks = Session key. KTG = TGS Symmetric key. In step 2, Alice does not know KA, but when the message arrives, she types her password. The password and the appropriate algorithm together create KA if the password is correct. T = Timestamp. This presents a replay by intruder. n n n Kerberos example For different servers, repeat the last four steps only. Version 5: longer lifetime, tickets can be renewed, accept any symmetric-key algorithm, uses a different protocol for describing data types, has more overhead than version 4. Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2004


