144d9bb2370a0712bca04951a05ee2f9.ppt
- Количество слайдов: 54
Chapter 2. Application Layer Business Data Communications and Networking Fitzgerald and Dennis, 7 th Edition Copyright © 2002 John Wiley & Sons, Inc. 1
Copyright ã 2002 John Wiley & Sons, Inc. All rights reserved. Reproduction or translation of this work beyond that named in Section 117 of the United States Copyright Act without the express written consent of the copyright owner is unlawful. Requests for further information should be addressed to the Permissions Department, John Wiley & Sons, Inc. Adopters of the textbook are granted permission to make back-up copies for their own use only, to make copies for distribution to students of the course the textbook is used in, and to modify this material to best suit their instructional needs. Under no circumstances can copies be made for resale. The Publisher assumes no responsibility for errors, omissions, or damages, caused by the use of these programs or from the use of the information contained herein. 2
Chapter 2. Learning Objectives • Understand host-based, client-based, and client-server architectures • Understand how the Web works • Understand how e-mail works • Be aware of how FTP, Telnet, and Instant Messaging work 3
Chapter 2. Outline • Introduction • Application Architectures – Host-Based, Client-Based, and Client-Server Architectures, Choosing Architectures • World Wide Web – How the Web Works, Inside an HTTP Request & HTTP Response • Electronic Mail – How E-Mail Works, Inside an SMTP Packet – Listserv, Attachments in MIME • Other Applications – Ftp, Telnet, Instant Messaging, Videoconferencing 4
Servers • • Mainframe Minicomputer Microcomputer Cluster 5
Clients • • • Microcomputer Terminal (dumb vs. smart) Workstation Network Computer Transaction Terminal, e. g. ATM Machine 6
Application Architectures 7
Application Architectures • Application programs can be thought of as being made up of four functions: – – Data storage Data access logic Application logic Presentation logic • Application architectures are determined by how these functions are split between clients and servers. • Three basic application architectures are in use today: – Host-based Architectures – Client-based architectures – Client-server architectures 8
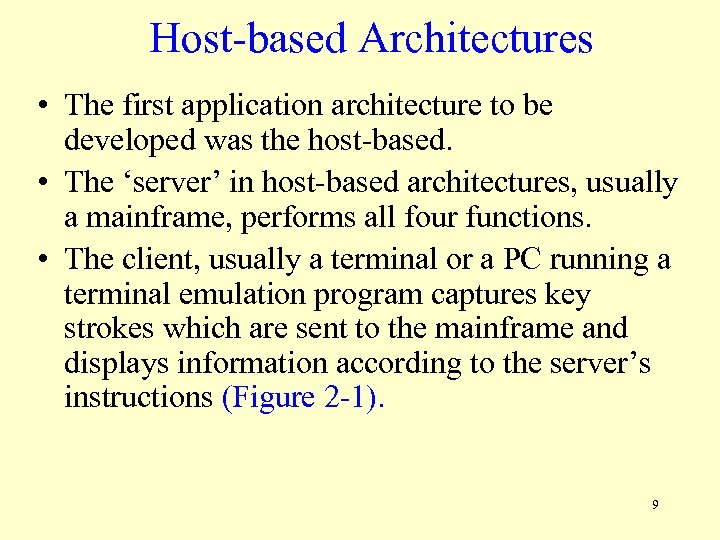
Host-based Architectures • The first application architecture to be developed was the host-based. • The ‘server’ in host-based architectures, usually a mainframe, performs all four functions. • The client, usually a terminal or a PC running a terminal emulation program captures key strokes which are sent to the mainframe and displays information according to the server’s instructions (Figure 2 -1). 9
Figure 2 -1 Host-Based Architectures 10
Host-based Architectures • There are two main problems with host-based architectures: – Since all processing is by the host, the host becomes a bottleneck which can severely limit network performance. – Upgrades are typically expensive and “lumpy”, meaning available upgrades require big jumps in processing and memory. Network demand grows more incrementally, so this often means a poor fit (too much or too little) between host performance and network demand. 11
Client-Based Architectures • Client-based architectures became important in the late 1980 s with the widespread use of PCs, local area networks, and low-cost PC-based application programs such as spreadsheets and word processors. • In client-based architectures, application programs on the clients are responsible for the data access, application, and presentation logic. • The server is responsible for data storage only (Figure 2 -2). 12
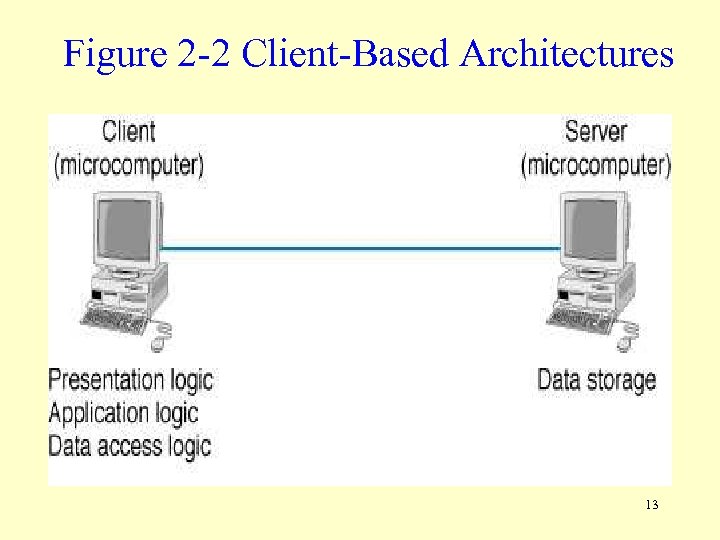
Figure 2 -2 Client-Based Architectures 13
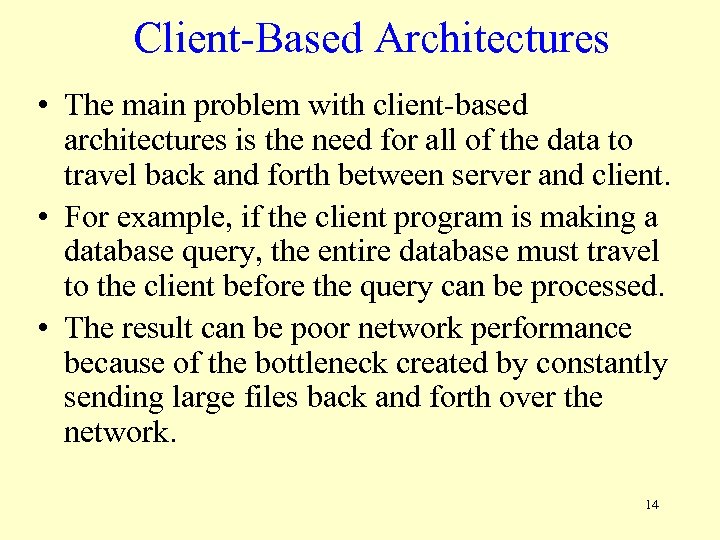
Client-Based Architectures • The main problem with client-based architectures is the need for all of the data to travel back and forth between server and client. • For example, if the client program is making a database query, the entire database must travel to the client before the query can be processed. • The result can be poor network performance because of the bottleneck created by constantly sending large files back and forth over the network. 14
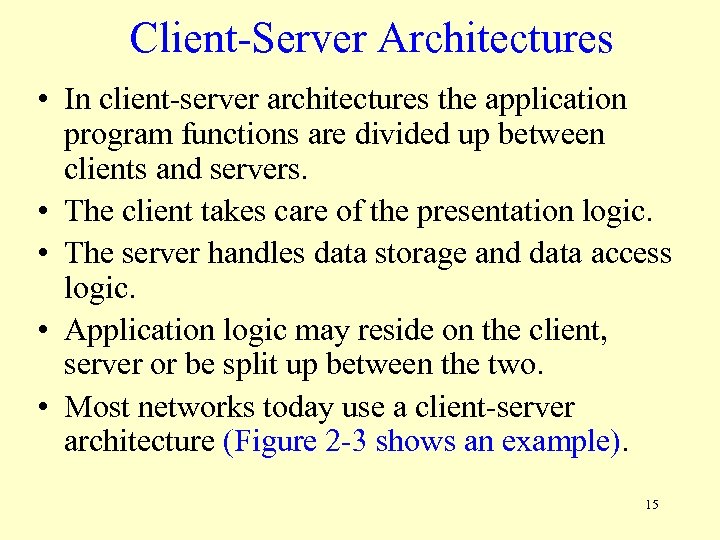
Client-Server Architectures • In client-server architectures the application program functions are divided up between clients and servers. • The client takes care of the presentation logic. • The server handles data storage and data access logic. • Application logic may reside on the client, server or be split up between the two. • Most networks today use a client-server architecture (Figure 2 -3 shows an example). 15
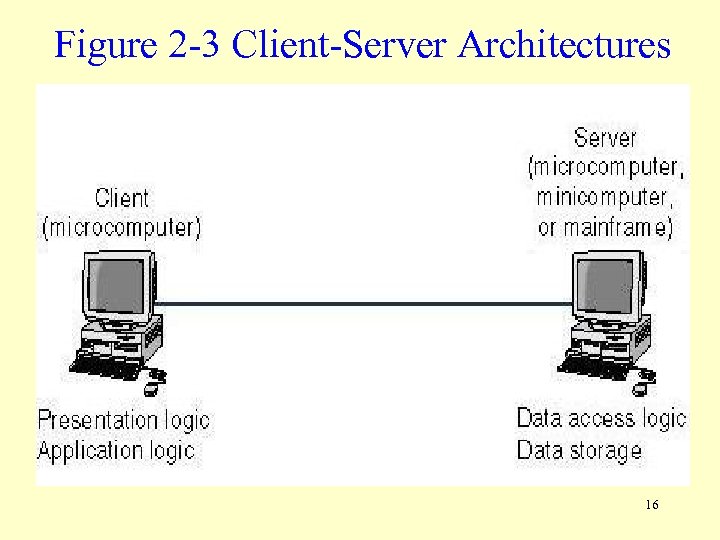
Figure 2 -3 Client-Server Architectures 16
Client-Server Architectures • Client-server architectures are more efficient since they distribute processing between client and server. • Another strength is that they allow hardware and software from different servers to be used together. • This is also a weakness, since it is sometimes difficult to get software from different vendors to work together smoothly. • For this reason, a third category of software, called Middleware was developed. 17
Middleware • Middleware provides an interface for allowing client application programs to interact with server application programs. • Middleware’s two main functions are: – Providing a standard way of translating between software from different vendors. – Managing message transfer between client and server, thus insulating network changes (such as adding a new server) from the clients. • Two of the most important middleware standards are: Distributed Computing Environment (DCE) and Common Object Request Broker Architecture (CORBA). 18
Two-tier, Three-tier and N-tier Architectures • Figure 2 -3 gives an example of a 2 -tier client-server architecture. • In a three-tier architecture the application program logic is split up between three computers. For example (see Figure 2 -4), – the client handles the presentation logic. – an application server handles the application logic. – a database server handles the data storage and data access logic. • In an N-tier architecture more than three sets of computers are used (see Figure 2 -5). 19
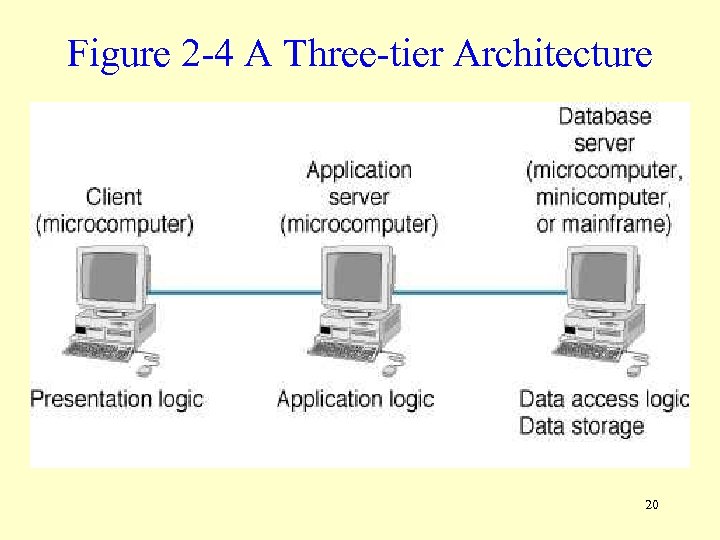
Figure 2 -4 A Three-tier Architecture 20
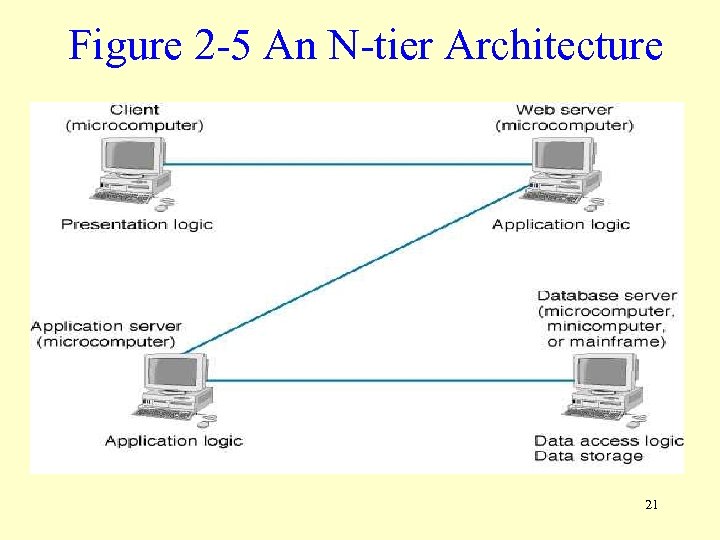
Figure 2 -5 An N-tier Architecture 21
Two-tier, Three-tier and N-tier Architectures • The primary advantage of N-tier architectures is that they make load balancing possible. Since the application logic is distributed between several servers, processing can then be more evenly distributed among those servers. • N-tiered architectures are also more easily scalable, since only servers experiencing high demand, such as the application server, need be upgraded. • The primary disadvantage is that more distributed processing means a more heavily loaded network. • It is also more difficult to program and test an N-tier architecture due to its increased complexity. 22
Thin versus Fat Clients • Thin and Fat (or thick) clients describe how much of the application logic resides on the client. – Little or no application logic resides on a thin client. – All or most of the application logic resides on a fat client. • Thin clients are becoming popular because they are easier to manage, since only the server application logic generally needs to be updated. • The best example of a thin client is World Wide Web architecture which uses a two-tier, thin client architecture (Figure 2 -6). 23
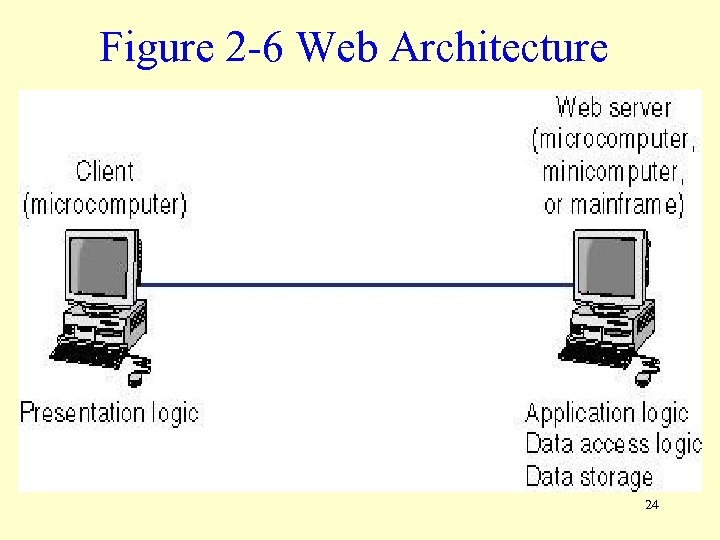
Figure 2 -6 Web Architecture 24
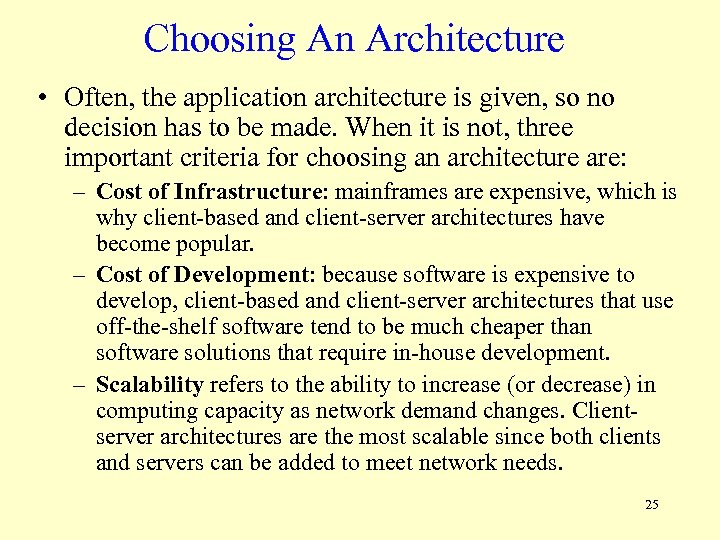
Choosing An Architecture • Often, the application architecture is given, so no decision has to be made. When it is not, three important criteria for choosing an architecture are: – Cost of Infrastructure: mainframes are expensive, which is why client-based and client-server architectures have become popular. – Cost of Development: because software is expensive to develop, client-based and client-server architectures that use off-the-shelf software tend to be much cheaper than software solutions that require in-house development. – Scalability refers to the ability to increase (or decrease) in computing capacity as network demand changes. Clientserver architectures are the most scalable since both clients and servers can be added to meet network needs. 25
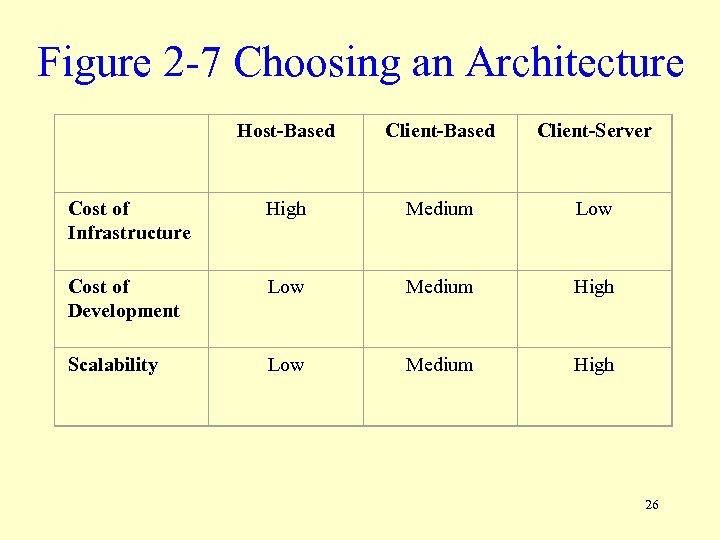
Figure 2 -7 Choosing an Architecture Host-Based Client-Server Cost of Infrastructure High Medium Low Cost of Development Low Medium High Scalability Low Medium High 26
The World Wide Web 27
Origin of the World Wide Web • Invented in 1989 by Tim Berners-Lee at the Centre Européan pour Rechèrche Nucleaire (CERN) in Geneva. • Two central WWW ideas are hyperlinks and Uniform Resource Locators (URLs). • Mosaic, the first web reader (browser) to gain widespread use, was written in 1993 at the National Center for Supercomputing Applications (NCSA) by Marc Andressen, who later founded Netscape. 28
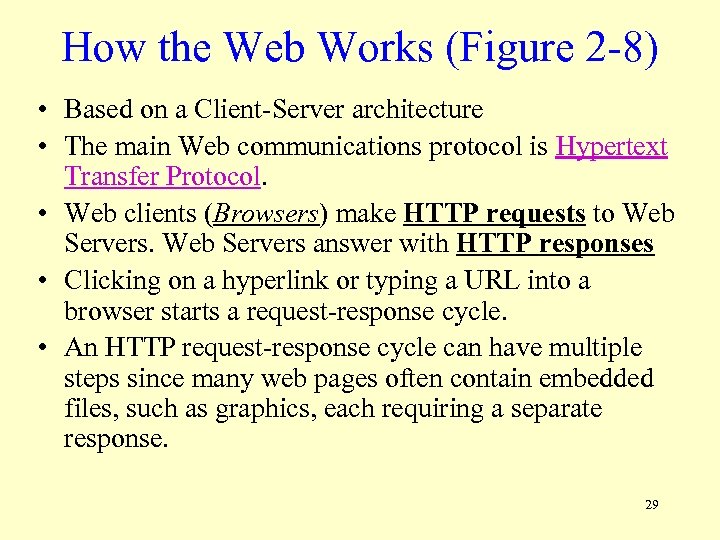
How the Web Works (Figure 2 -8) • Based on a Client-Server architecture • The main Web communications protocol is Hypertext Transfer Protocol. • Web clients (Browsers) make HTTP requests to Web Servers answer with HTTP responses • Clicking on a hyperlink or typing a URL into a browser starts a request-response cycle. • An HTTP request-response cycle can have multiple steps since many web pages often contain embedded files, such as graphics, each requiring a separate response. 29
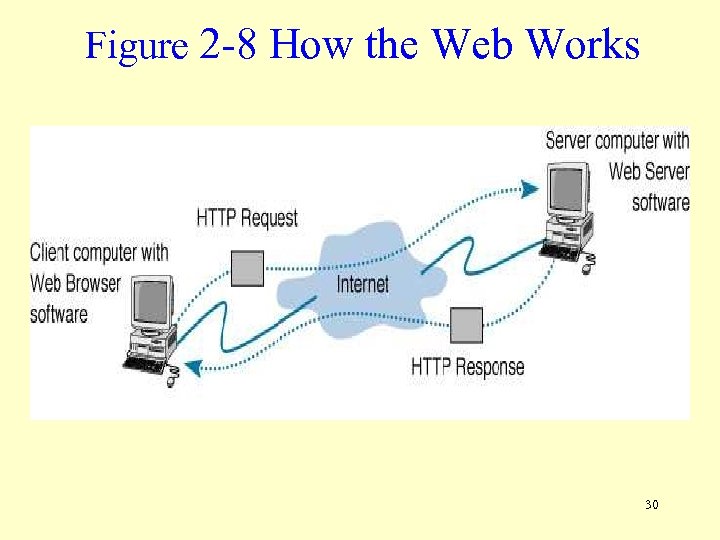
Figure 2 -8 How the Web Works 30
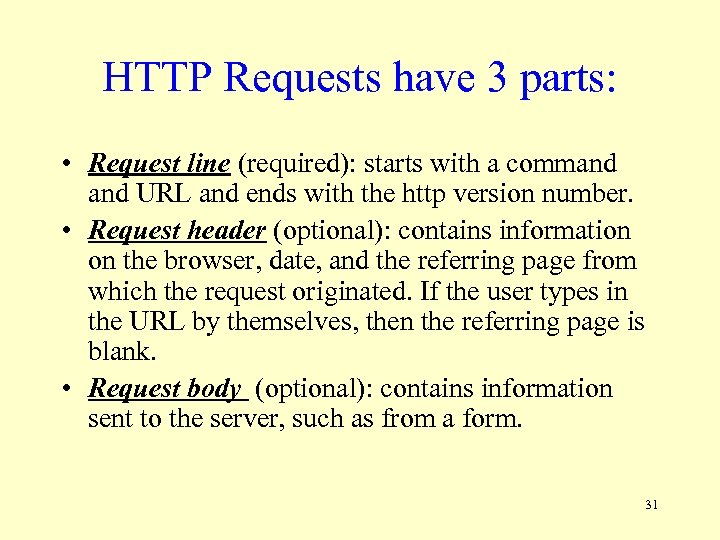
HTTP Requests have 3 parts: • Request line (required): starts with a command URL and ends with the http version number. • Request header (optional): contains information on the browser, date, and the referring page from which the request originated. If the user types in the URL by themselves, then the referring page is blank. • Request body (optional): contains information sent to the server, such as from a form. 31
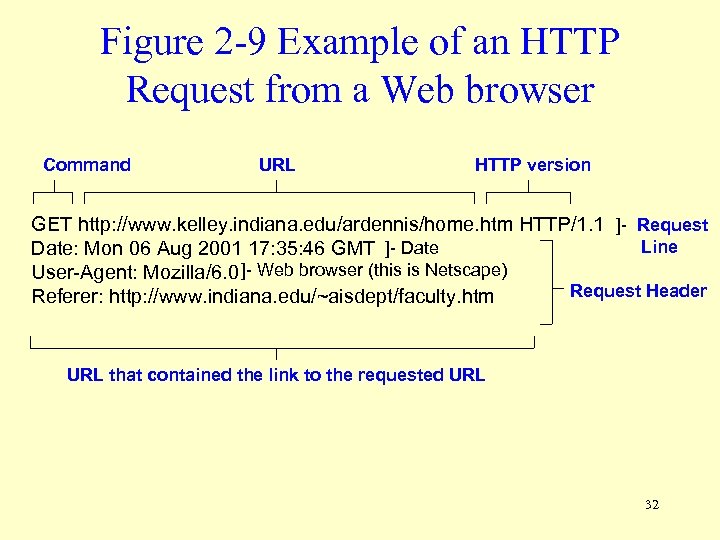
Figure 2 -9 Example of an HTTP Request from a Web browser Command URL HTTP version GET http: //www. kelley. indiana. edu/ardennis/home. htm HTTP/1. 1 ]- Request Line Date: Mon 06 Aug 2001 17: 35: 46 GMT ]- Date User-Agent: Mozilla/6. 0 ]- Web browser (this is Netscape) Request Header Referer: http: //www. indiana. edu/~aisdept/faculty. htm URL that contained the link to the requested URL 32
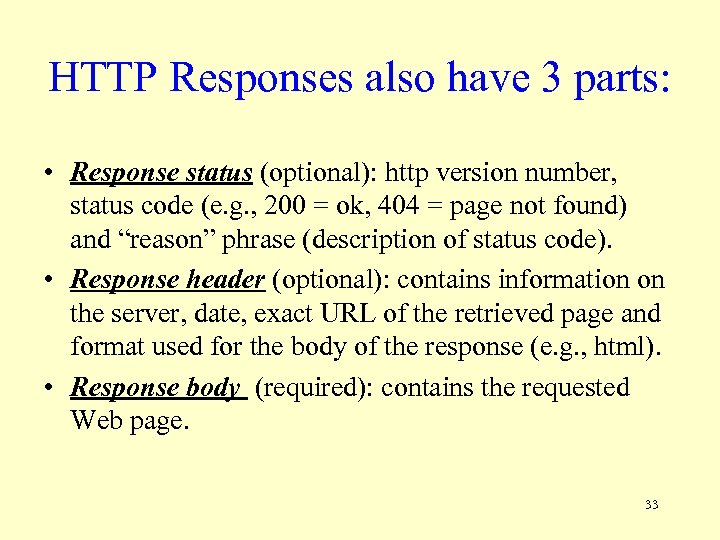
HTTP Responses also have 3 parts: • Response status (optional): http version number, status code (e. g. , 200 = ok, 404 = page not found) and “reason” phrase (description of status code). • Response header (optional): contains information on the server, date, exact URL of the retrieved page and format used for the body of the response (e. g. , html). • Response body (required): contains the requested Web page. 33
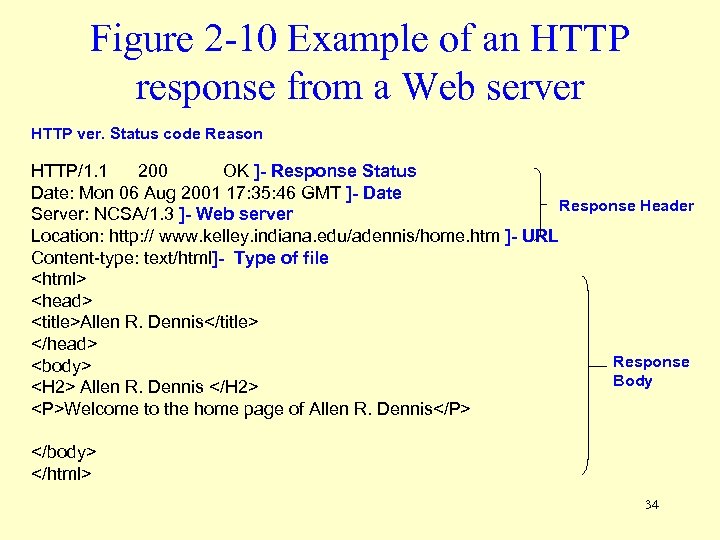
Figure 2 -10 Example of an HTTP response from a Web server HTTP ver. Status code Reason HTTP/1. 1 200 OK ]- Response Status Date: Mon 06 Aug 2001 17: 35: 46 GMT ]- Date Response Header Server: NCSA/1. 3 ]- Web server Location: http: // www. kelley. indiana. edu/adennis/home. htm ]- URL Content-type: text/html]- Type of file <html> <head> <title>Allen R. Dennis</title> </head> Response <body> Body <H 2> Allen R. Dennis </H 2> <P>Welcome to the home page of Allen R. Dennis</P> </body> </html> 34
Rex Swain’s HTTP Viewer • To see an example of what happens when an HTTP request is made, follow this link. 35
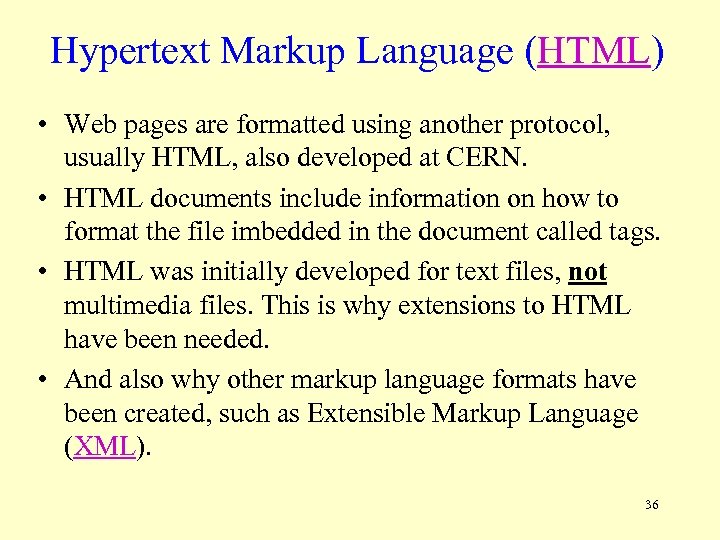
Hypertext Markup Language (HTML) • Web pages are formatted using another protocol, usually HTML, also developed at CERN. • HTML documents include information on how to format the file imbedded in the document called tags. • HTML was initially developed for text files, not multimedia files. This is why extensions to HTML have been needed. • And also why other markup language formats have been created, such as Extensible Markup Language (XML). 36
Electronic Mail 37
Electronic Mail • Still the most heavily used Internet application because: – It’s much, much faster than regular mail. – It’s extremely inexpensive. – It can substitute for other forms of communication, such as telephone calls. – E-mail users don’t have to play “telephone tag”, since the respondent can answer at his/her convenience, instead of time of call. 38
E-mail standards • Simple Mail Transfer Protocol (SMTP): part of the TCP/IP protocol suite. • SMTP is the main e-mail standard for mail transfer agents in use today, but was written to only handle text files. • SMTP is usually implemented using a twotier client-server architecture. • Two other competing standards for e-mail are Common Messaging Calls (CMC) and X. 400. 39
Two-Tier E-mail Architecture • SMTP uses two types of programs: • User agents, also called e-mail clients, are programs running on client computers that send email to e-mail servers and download e-mail from mailboxes on those servers. – Examples: Eudora, Outlook, Netscape Messenger. • Mail transfer agents, also called mail server software, are used by e-mail servers. They send email between e-mail servers and maintain individual mailboxes. – Post Office Protocol (POP) & Internet Mail Access Protocol (IMAP) are the main protocols for user agent to receive e-mail from mail server. 40
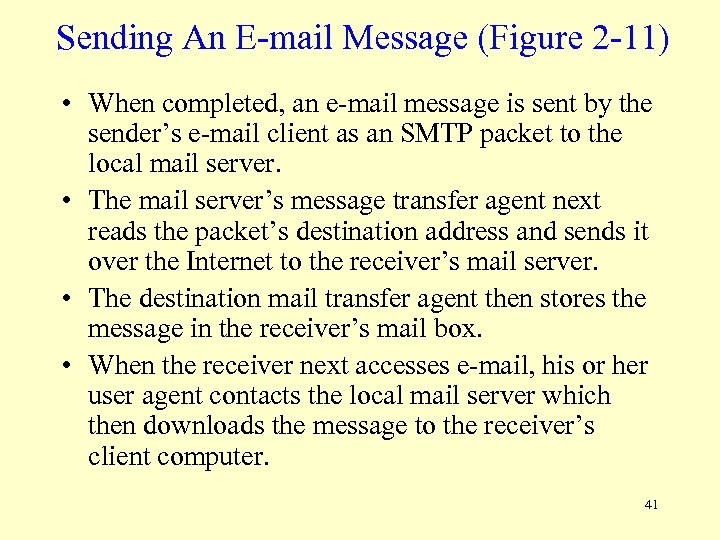
Sending An E-mail Message (Figure 2 -11) • When completed, an e-mail message is sent by the sender’s e-mail client as an SMTP packet to the local mail server. • The mail server’s message transfer agent next reads the packet’s destination address and sends it over the Internet to the receiver’s mail server. • The destination mail transfer agent then stores the message in the receiver’s mail box. • When the receiver next accesses e-mail, his or her user agent contacts the local mail server which then downloads the message to the receiver’s client computer. 41
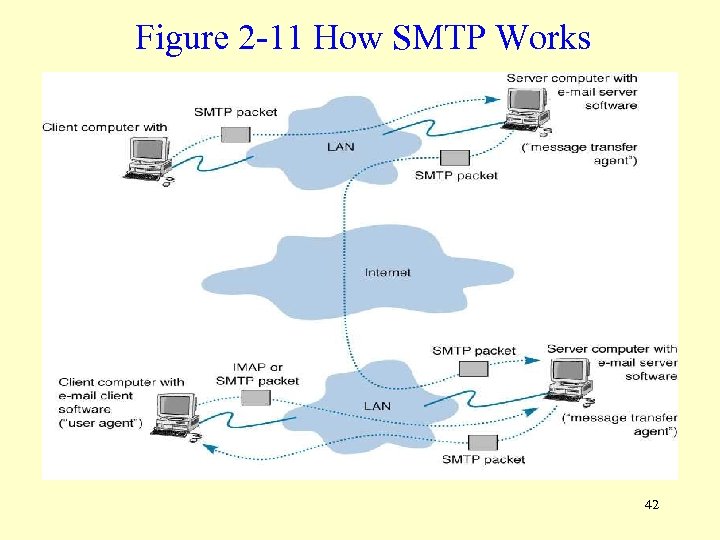
Figure 2 -11 How SMTP Works 42
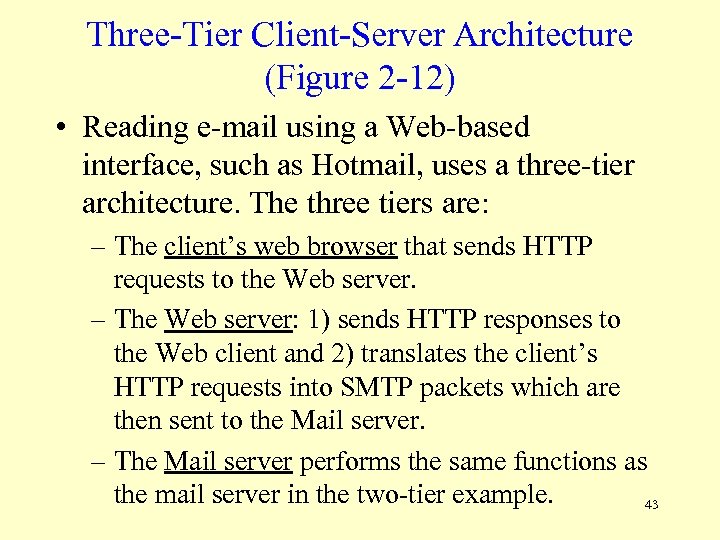
Three-Tier Client-Server Architecture (Figure 2 -12) • Reading e-mail using a Web-based interface, such as Hotmail, uses a three-tier architecture. The three tiers are: – The client’s web browser that sends HTTP requests to the Web server. – The Web server: 1) sends HTTP responses to the Web client and 2) translates the client’s HTTP requests into SMTP packets which are then sent to the Mail server. – The Mail server performs the same functions as the mail server in the two-tier example. 43
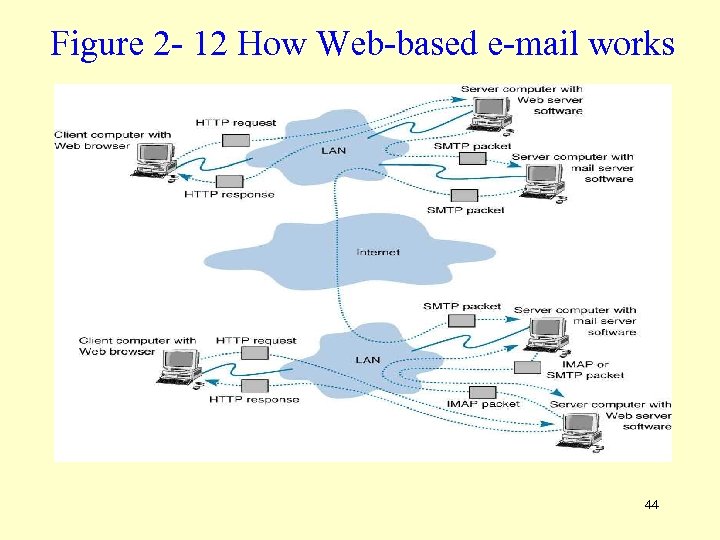
Figure 2 - 12 How Web-based e-mail works 44
Simple Mail Transfer Protocol • SMTP E-mail messages have the following structure: – Header: lists source and destination addresses, date, subject, and other information about the email message. – Body: the message itself. – Attachments: additional files that have been included along with the e-mail message. 45
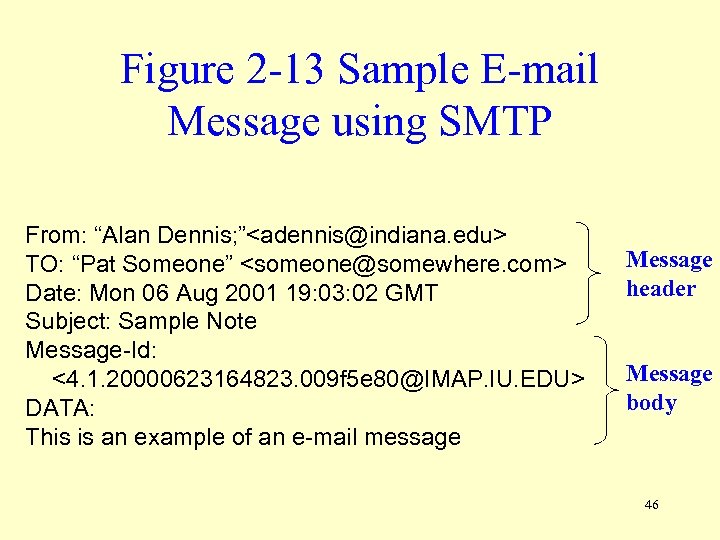
Figure 2 -13 Sample E-mail Message using SMTP From: “Alan Dennis; ”<adennis@indiana. edu> TO: “Pat Someone” <someone@somewhere. com> Date: Mon 06 Aug 2001 19: 03: 02 GMT Subject: Sample Note Message-Id: <4. 1. 20000623164823. 009 f 5 e 80@IMAP. IU. EDU> DATA: This is an example of an e-mail message Message header Message body 46
Attachments in MIME • Since SMTP was developed for transferring text files, special techniques needed to be developed to send graphical information. • Graphics capable mail transfer agent protocols include MIME (Multipurpose Internet Mail Extension), uuencode and binhex. • Included as part of an e-mail client, MIME translates graphical information into text allowing the graphic to be sent as part of an SMTP message. • The receiver’s e-mail client then translates the MIME attachment from text back into graphical format. 47
Listserv Discussion Groups • Listserv Processor (SUBSCRIBE, HELP, LIST, etc. ) • Listserv Mailer 48
Other Applications 49
File Transfer Protocol (FTP) and Telnet • FTP enables sending and receiving files over the Internet. (closed vs. anonymous) • Telnet allows remote logins over the Internet. Security is an issue. • Both were much more commonly used during the pre-WWW days of the Internet. • FTP still commonly used today for uploading web pages. • Both require client and server programs. 50
IM: Instant Messaging (Figure 2 -14) • IM is a client-server program that allows real-time messages to be exchanged. Some types allow voice and video packets to be sent. Examples include AOL and ICQ. • IM works as follows: – Your IM client first sends a request to the IM server telling it that you are online. If a friend connects, the IM server sends a packet to your IM client and vice versa. – When you type some text, your IM client sends the text in a packet to the IM server which relays it to your friend. – If a chat session has more than two clients, multiple packets are sent by the IM servers can also relay information to other IM servers. 51
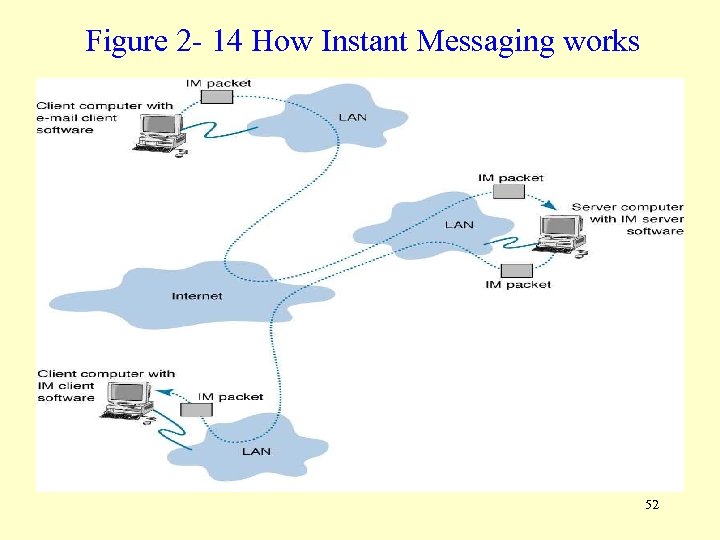
Figure 2 - 14 How Instant Messaging works 52
Videoconferencing • Allows people to meet at the same time in different locations, potentially saving money and time by not having to move people around. • Conference calling does the same thing. • Typically involves 2 meeting rooms only. • Desktop videoconferencing is a related, very low cost application linking small video cameras and microphones together over the Internet. • Webcasting: one-directional videoconferencing. 53
End of Chapter 2 54
144d9bb2370a0712bca04951a05ee2f9.ppt