7e980f6521eec705008cc559310b9f1e.ppt
- Количество слайдов: 97
 Chapter 1 Introduction A note on the use of these ppt slides: We’re making these slides freely available to all (faculty, students, readers). They’re in Power. Point form so you can add, modify, and delete slides (including this one) and slide content to suit your needs. They obviously represent a lot of work on our part. In return for use, we only ask the following: q If you use these slides (e. g. , in a class) in substantially unaltered form, that you mention their source (after all, we’d like people to use our book!) q If you post any slides in substantially unaltered form on a www site, that you note that they are adapted from (or perhaps identical to) our slides, and note our copyright of this material. Thanks and enjoy! JFK/KWR Computer Networking: A Top Down Approach , 5 th edition. Jim Kurose, Keith Ross Addison-Wesley, April 2009. All material copyright 1996 -2009 J. F Kurose and K. W. Ross, All Rights Reserved Introduction 1 -1
Chapter 1 Introduction A note on the use of these ppt slides: We’re making these slides freely available to all (faculty, students, readers). They’re in Power. Point form so you can add, modify, and delete slides (including this one) and slide content to suit your needs. They obviously represent a lot of work on our part. In return for use, we only ask the following: q If you use these slides (e. g. , in a class) in substantially unaltered form, that you mention their source (after all, we’d like people to use our book!) q If you post any slides in substantially unaltered form on a www site, that you note that they are adapted from (or perhaps identical to) our slides, and note our copyright of this material. Thanks and enjoy! JFK/KWR Computer Networking: A Top Down Approach , 5 th edition. Jim Kurose, Keith Ross Addison-Wesley, April 2009. All material copyright 1996 -2009 J. F Kurose and K. W. Ross, All Rights Reserved Introduction 1 -1
 Acknowledgements q This lecture and all subsequent lectures include slides taken from course slides by Kurose/Ross. q This lecture also contains a few slides adapted from Srini Seshan’s Computer Networking course at http: //www. cs. cmu. edu/~srini/15 -744/S 01/ Introduction 1 -2
Acknowledgements q This lecture and all subsequent lectures include slides taken from course slides by Kurose/Ross. q This lecture also contains a few slides adapted from Srini Seshan’s Computer Networking course at http: //www. cs. cmu. edu/~srini/15 -744/S 01/ Introduction 1 -2
 Course Logistics q MW 4: 40 -6: 30 pm, EB 103 q Instructor: Nirupama Bulusu Email: nbulusu@cs. pdx. edu v Phone: 503 725 2404 Text v Office Hours: MW 3: 30 -4 pm pm FAB 120 -11 v q TA: TBA q Class Web Page: http: //web. cecs. pdx. edu/~nbulusu/courses /cs 494 -sp 11/ q Mail List: cs 494 -sp 11@googlegroups. com
Course Logistics q MW 4: 40 -6: 30 pm, EB 103 q Instructor: Nirupama Bulusu Email: nbulusu@cs. pdx. edu v Phone: 503 725 2404 Text v Office Hours: MW 3: 30 -4 pm pm FAB 120 -11 v q TA: TBA q Class Web Page: http: //web. cecs. pdx. edu/~nbulusu/courses /cs 494 -sp 11/ q Mail List: cs 494 -sp 11@googlegroups. com
 Text. Book q Computer Networking: A Top-Down Approach (5 th edition), Jim Kurose and Keith Ross, ISBN-10: 0136079679, ISBN-13: 978 -0136079675
Text. Book q Computer Networking: A Top-Down Approach (5 th edition), Jim Kurose and Keith Ross, ISBN-10: 0136079679, ISBN-13: 978 -0136079675
 Grading Criteria q HW: 25% q Project: 25% q Midterm: 25% q Final: 25% q Note: 594 Students are expected to also review research papers as part of their homework.
Grading Criteria q HW: 25% q Project: 25% q Midterm: 25% q Final: 25% q Note: 594 Students are expected to also review research papers as part of their homework.
 Grade Distribution q Total Score: • • • 90. 01 -100: A 83. 01 -90: A 76. 01 -83: B+ 69. 01 -76: B 62. 01 -69: B 55. 01 -62: C+ 48. 01 -55: C 41. 01 -48: C 34. 01 -41: D+ 27. 01 -34: D 20. 01 -27: DF <20: F
Grade Distribution q Total Score: • • • 90. 01 -100: A 83. 01 -90: A 76. 01 -83: B+ 69. 01 -76: B 62. 01 -69: B 55. 01 -62: C+ 48. 01 -55: C 41. 01 -48: C 34. 01 -41: D+ 27. 01 -34: D 20. 01 -27: DF <20: F
 Learning Objectives • Explain ◦ fundamental ideas associated with point-to-point protocols, such as PPP, and the Ethernet, such as CSMA/CD and MAC addresses ◦ fundamental concepts associated with modern Ethernet switches, including fullduplex and collision-free networks, VLANs, spanning-trees, and adaptivelearning ◦ how ARP works in IPv 4 and explain how broadcast can be used for link reachability ◦ how traceroute and ping work as well as other ICMP mechanisms ◦ network attacks based on arp-spoofing, and IP address spoofing ◦ the basic ideas behind sliding window protocols in general and TCP in particular. ◦ how application-layer protocols such as HTTP, FTP, TELNET, SMTP and DNS work. ◦ techniques involved in the Morris worm, and other network-based attacks ◦ how layer 3 and layer 7 network devices operate. • Compare and contrast
Learning Objectives • Explain ◦ fundamental ideas associated with point-to-point protocols, such as PPP, and the Ethernet, such as CSMA/CD and MAC addresses ◦ fundamental concepts associated with modern Ethernet switches, including fullduplex and collision-free networks, VLANs, spanning-trees, and adaptivelearning ◦ how ARP works in IPv 4 and explain how broadcast can be used for link reachability ◦ how traceroute and ping work as well as other ICMP mechanisms ◦ network attacks based on arp-spoofing, and IP address spoofing ◦ the basic ideas behind sliding window protocols in general and TCP in particular. ◦ how application-layer protocols such as HTTP, FTP, TELNET, SMTP and DNS work. ◦ techniques involved in the Morris worm, and other network-based attacks ◦ how layer 3 and layer 7 network devices operate. • Compare and contrast
 Internet Architecture q http: //www. nap. edu/html/coming_of_age/ q http: //www. ietf. org/rfc 1958. txt q Why did the Internet win? Packet switching over circuit switching v End-to-end architecture and “Hourglass” design v Layering of functionality v Distributed design, decentralized control v Superior organizational process v Introduction 1 -3
Internet Architecture q http: //www. nap. edu/html/coming_of_age/ q http: //www. ietf. org/rfc 1958. txt q Why did the Internet win? Packet switching over circuit switching v End-to-end architecture and “Hourglass” design v Layering of functionality v Distributed design, decentralized control v Superior organizational process v Introduction 1 -3
 A closer look at network structure: q network edge: applications and hosts q access networks, physical media: wired, wireless communication links q network core: v interconnected routers v network of networks Introduction 1 -66
A closer look at network structure: q network edge: applications and hosts q access networks, physical media: wired, wireless communication links q network core: v interconnected routers v network of networks Introduction 1 -66
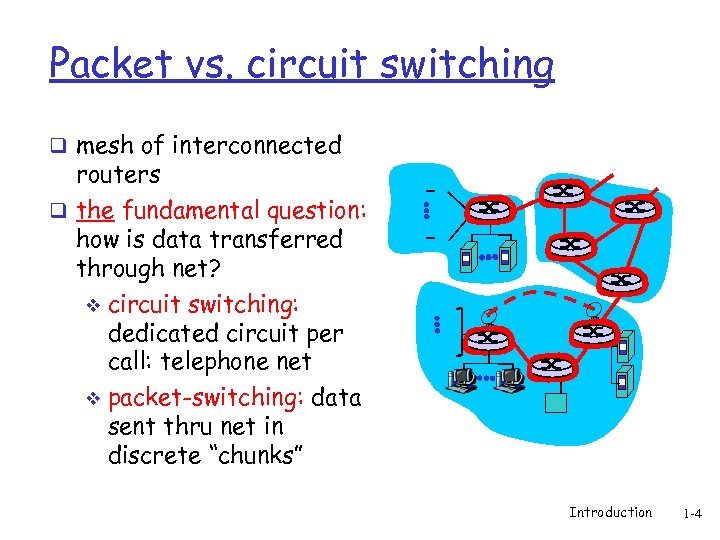 Packet vs. circuit switching q mesh of interconnected routers q the fundamental question: how is data transferred through net? v circuit switching: dedicated circuit per call: telephone net v packet-switching: data sent thru net in discrete “chunks” Introduction 1 -4
Packet vs. circuit switching q mesh of interconnected routers q the fundamental question: how is data transferred through net? v circuit switching: dedicated circuit per call: telephone net v packet-switching: data sent thru net in discrete “chunks” Introduction 1 -4
 Case study: Circuit Switching q 1890 -current: Phone network v Fixed bit rate Mostly voice v Not fault-tolerant v Components extremely reliable v Global application-level knowledge throughout network v Introduction 1 -5
Case study: Circuit Switching q 1890 -current: Phone network v Fixed bit rate Mostly voice v Not fault-tolerant v Components extremely reliable v Global application-level knowledge throughout network v Introduction 1 -5
 Case study: Packet Switching q 1981 -current: Internet network v Variable bit rate Mostly data v Fault-tolerant v Components not extremely reliable (versus phone components) v Distributed control and management v Introduction 1 -6
Case study: Packet Switching q 1981 -current: Internet network v Variable bit rate Mostly data v Fault-tolerant v Components not extremely reliable (versus phone components) v Distributed control and management v Introduction 1 -6
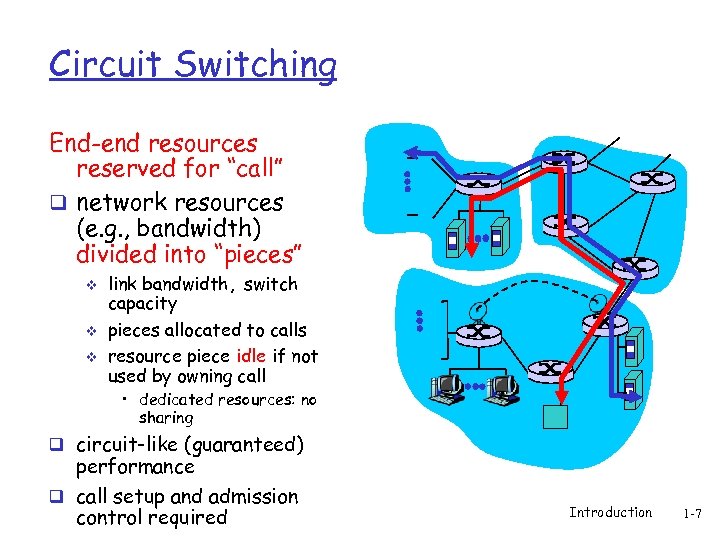 Circuit Switching End-end resources reserved for “call” q network resources (e. g. , bandwidth) divided into “pieces” v v v link bandwidth, switch capacity pieces allocated to calls resource piece idle if not used by owning call • dedicated resources: no sharing q circuit-like (guaranteed) performance q call setup and admission control required Introduction 1 -7
Circuit Switching End-end resources reserved for “call” q network resources (e. g. , bandwidth) divided into “pieces” v v v link bandwidth, switch capacity pieces allocated to calls resource piece idle if not used by owning call • dedicated resources: no sharing q circuit-like (guaranteed) performance q call setup and admission control required Introduction 1 -7
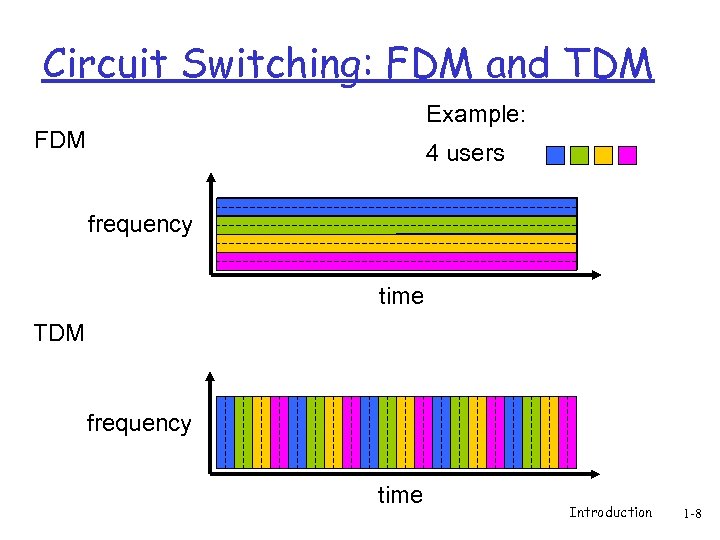 Circuit Switching: FDM and TDM Example: FDM 4 users frequency time TDM frequency time Introduction 1 -8
Circuit Switching: FDM and TDM Example: FDM 4 users frequency time TDM frequency time Introduction 1 -8
 Numerical example q How long does it take to send a file of 640, 000 bits from host A to host B over a circuit-switched network? All links are 1. 536 Mbps v Each link uses TDM with 24 slots/sec v 500 msec to establish end-to-end circuit v Let’s work it out! Introduction 1 -9
Numerical example q How long does it take to send a file of 640, 000 bits from host A to host B over a circuit-switched network? All links are 1. 536 Mbps v Each link uses TDM with 24 slots/sec v 500 msec to establish end-to-end circuit v Let’s work it out! Introduction 1 -9
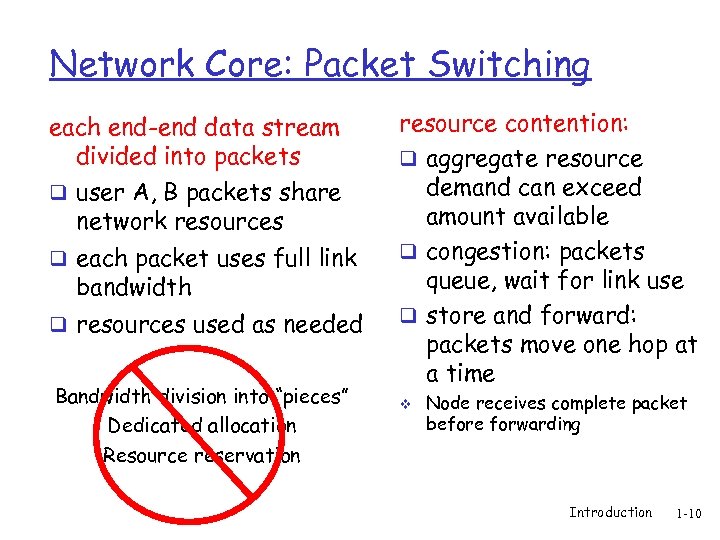 Network Core: Packet Switching each end-end data stream divided into packets q user A, B packets share network resources q each packet uses full link bandwidth q resources used as needed Bandwidth division into “pieces” Dedicated allocation Resource reservation resource contention: q aggregate resource demand can exceed amount available q congestion: packets queue, wait for link use q store and forward: packets move one hop at a time v Node receives complete packet before forwarding Introduction 1 -10
Network Core: Packet Switching each end-end data stream divided into packets q user A, B packets share network resources q each packet uses full link bandwidth q resources used as needed Bandwidth division into “pieces” Dedicated allocation Resource reservation resource contention: q aggregate resource demand can exceed amount available q congestion: packets queue, wait for link use q store and forward: packets move one hop at a time v Node receives complete packet before forwarding Introduction 1 -10
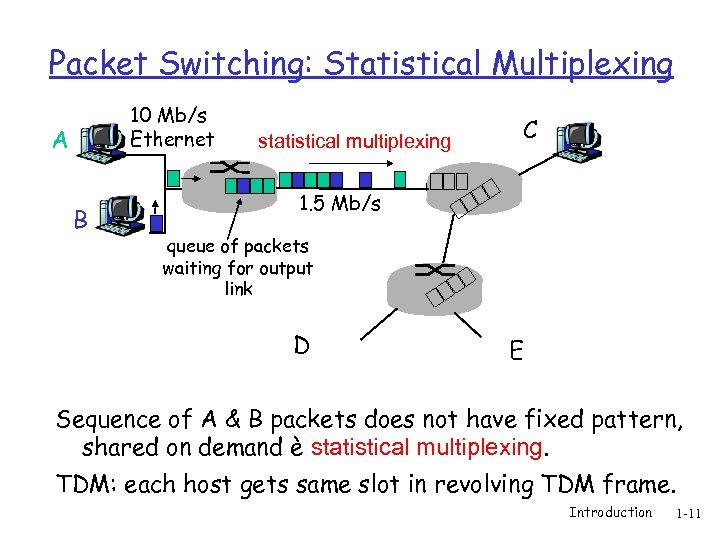 Packet Switching: Statistical Multiplexing 10 Mb/s Ethernet A B statistical multiplexing C 1. 5 Mb/s queue of packets waiting for output link D E Sequence of A & B packets does not have fixed pattern, shared on demand è statistical multiplexing. TDM: each host gets same slot in revolving TDM frame. Introduction 1 -11
Packet Switching: Statistical Multiplexing 10 Mb/s Ethernet A B statistical multiplexing C 1. 5 Mb/s queue of packets waiting for output link D E Sequence of A & B packets does not have fixed pattern, shared on demand è statistical multiplexing. TDM: each host gets same slot in revolving TDM frame. Introduction 1 -11
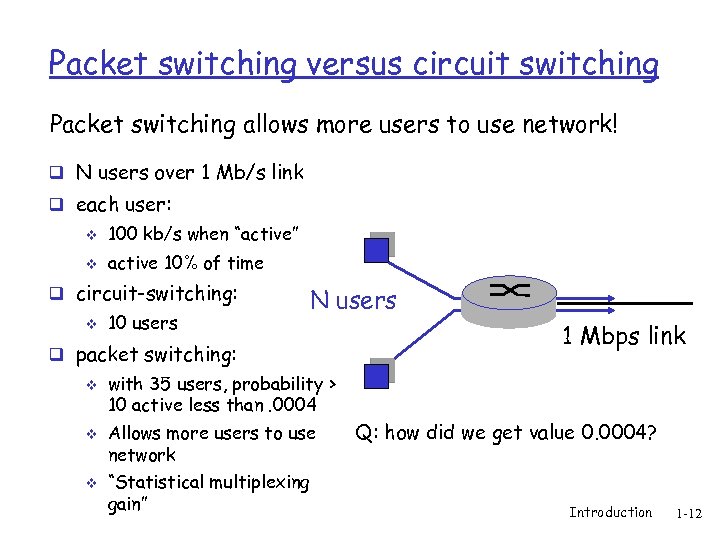 Packet switching versus circuit switching Packet switching allows more users to use network! q N users over 1 Mb/s link q each user: v 100 kb/s when “active” v active 10% of time q circuit-switching: v 10 users N users q packet switching: v v v with 35 users, probability > 10 active less than. 0004 Allows more users to use network “Statistical multiplexing gain” 1 Mbps link Q: how did we get value 0. 0004? Introduction 1 -12
Packet switching versus circuit switching Packet switching allows more users to use network! q N users over 1 Mb/s link q each user: v 100 kb/s when “active” v active 10% of time q circuit-switching: v 10 users N users q packet switching: v v v with 35 users, probability > 10 active less than. 0004 Allows more users to use network “Statistical multiplexing gain” 1 Mbps link Q: how did we get value 0. 0004? Introduction 1 -12
 Packet switching versus circuit switching Is packet switching a “slam dunk winner? ” q Great for bursty data resource sharing v simpler, no call setup q Bad for applications with hard resource requirements v v Excessive congestion: packet delay and loss Need protocols for reliable data transfer, congestion control v Applications must be written to handle congestion q Q: How to provide circuit-like behavior? v bandwidth guarantees needed for audio/video apps v still an unsolved problem (chapter 7) v Common practice: over-provision v Q: human analogies of reserved resources (circuit switching) Introduction 1 -13
Packet switching versus circuit switching Is packet switching a “slam dunk winner? ” q Great for bursty data resource sharing v simpler, no call setup q Bad for applications with hard resource requirements v v Excessive congestion: packet delay and loss Need protocols for reliable data transfer, congestion control v Applications must be written to handle congestion q Q: How to provide circuit-like behavior? v bandwidth guarantees needed for audio/video apps v still an unsolved problem (chapter 7) v Common practice: over-provision v Q: human analogies of reserved resources (circuit switching) Introduction 1 -13
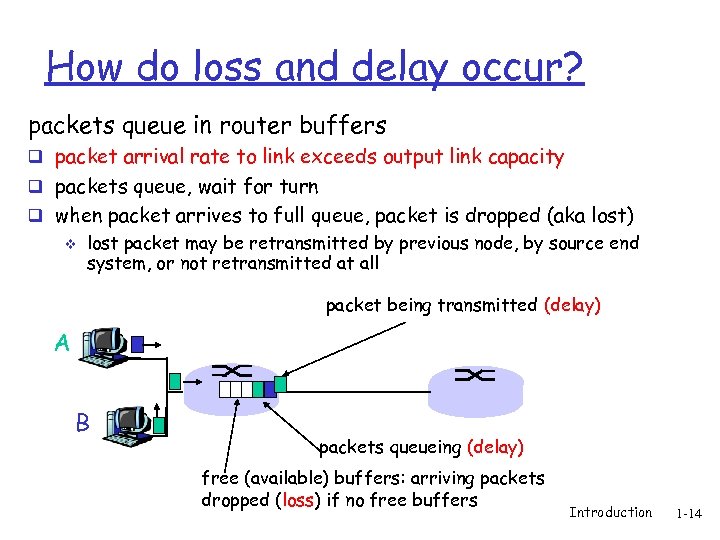 How do loss and delay occur? packets queue in router buffers q packet arrival rate to link exceeds output link capacity q packets queue, wait for turn q when packet arrives to full queue, packet is dropped (aka lost) v lost packet may be retransmitted by previous node, by source end system, or not retransmitted at all packet being transmitted (delay) A B packets queueing (delay) free (available) buffers: arriving packets dropped (loss) if no free buffers Introduction 1 -14
How do loss and delay occur? packets queue in router buffers q packet arrival rate to link exceeds output link capacity q packets queue, wait for turn q when packet arrives to full queue, packet is dropped (aka lost) v lost packet may be retransmitted by previous node, by source end system, or not retransmitted at all packet being transmitted (delay) A B packets queueing (delay) free (available) buffers: arriving packets dropped (loss) if no free buffers Introduction 1 -14
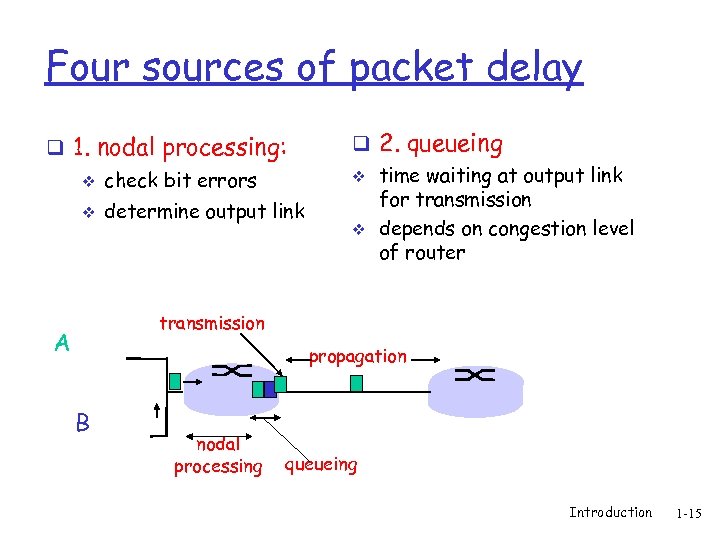 Four sources of packet delay q 1. nodal processing: v check bit errors v determine output link q 2. queueing v time waiting at output link for transmission v depends on congestion level of router transmission A propagation B nodal processing queueing Introduction 1 -15
Four sources of packet delay q 1. nodal processing: v check bit errors v determine output link q 2. queueing v time waiting at output link for transmission v depends on congestion level of router transmission A propagation B nodal processing queueing Introduction 1 -15
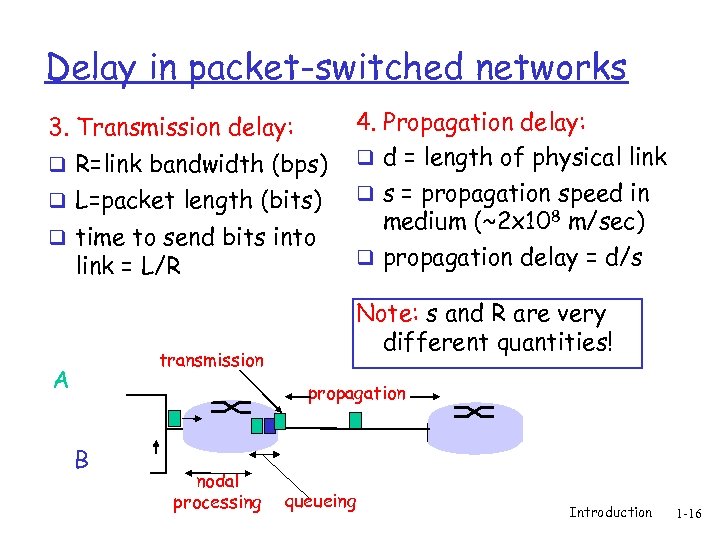 Delay in packet-switched networks 3. Transmission delay: q R=link bandwidth (bps) q L=packet length (bits) q time to send bits into link = L/R transmission A 4. Propagation delay: q d = length of physical link q s = propagation speed in medium (~2 x 108 m/sec) q propagation delay = d/s Note: s and R are very different quantities! propagation B nodal processing queueing Introduction 1 -16
Delay in packet-switched networks 3. Transmission delay: q R=link bandwidth (bps) q L=packet length (bits) q time to send bits into link = L/R transmission A 4. Propagation delay: q d = length of physical link q s = propagation speed in medium (~2 x 108 m/sec) q propagation delay = d/s Note: s and R are very different quantities! propagation B nodal processing queueing Introduction 1 -16
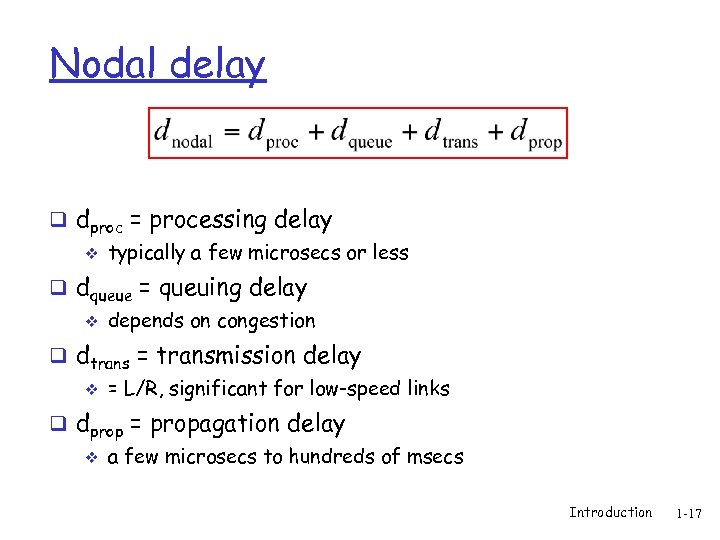 Nodal delay q dproc = processing delay v typically a few microsecs or less q dqueue = queuing delay v depends on congestion q dtrans = transmission delay v = L/R, significant for low-speed links q dprop = propagation delay v a few microsecs to hundreds of msecs Introduction 1 -17
Nodal delay q dproc = processing delay v typically a few microsecs or less q dqueue = queuing delay v depends on congestion q dtrans = transmission delay v = L/R, significant for low-speed links q dprop = propagation delay v a few microsecs to hundreds of msecs Introduction 1 -17
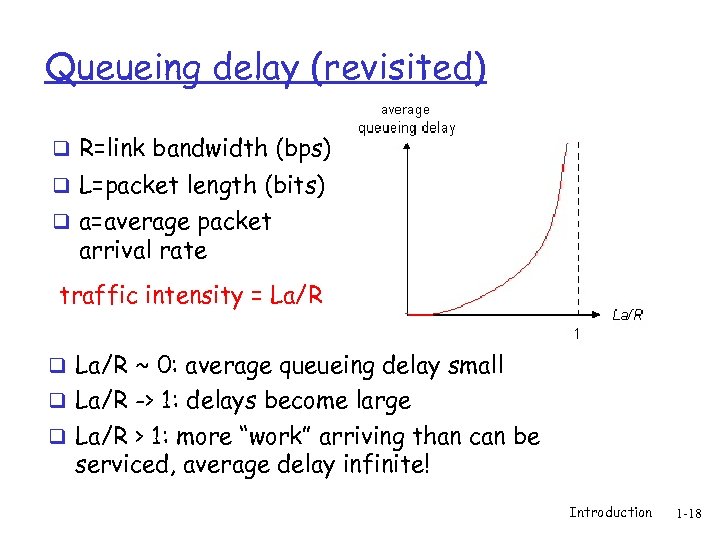 Queueing delay (revisited) q R=link bandwidth (bps) q L=packet length (bits) q a=average packet arrival rate traffic intensity = La/R q La/R ~ 0: average queueing delay small q La/R -> 1: delays become large q La/R > 1: more “work” arriving than can be serviced, average delay infinite! Introduction 1 -18
Queueing delay (revisited) q R=link bandwidth (bps) q L=packet length (bits) q a=average packet arrival rate traffic intensity = La/R q La/R ~ 0: average queueing delay small q La/R -> 1: delays become large q La/R > 1: more “work” arriving than can be serviced, average delay infinite! Introduction 1 -18
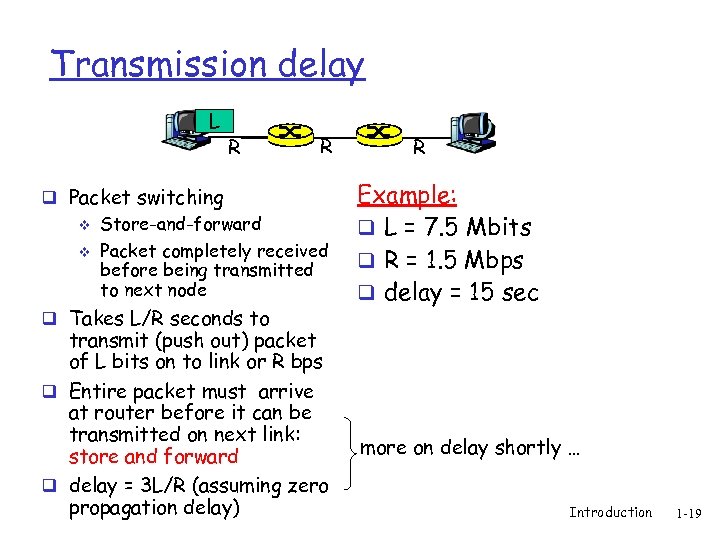 Transmission delay L R R q Packet switching v v Store-and-forward Packet completely received before being transmitted to next node q Takes L/R seconds to transmit (push out) packet of L bits on to link or R bps q Entire packet must arrive at router before it can be transmitted on next link: store and forward q delay = 3 L/R (assuming zero propagation delay) R Example: q L = 7. 5 Mbits q R = 1. 5 Mbps q delay = 15 sec more on delay shortly … Introduction 1 -19
Transmission delay L R R q Packet switching v v Store-and-forward Packet completely received before being transmitted to next node q Takes L/R seconds to transmit (push out) packet of L bits on to link or R bps q Entire packet must arrive at router before it can be transmitted on next link: store and forward q delay = 3 L/R (assuming zero propagation delay) R Example: q L = 7. 5 Mbits q R = 1. 5 Mbps q delay = 15 sec more on delay shortly … Introduction 1 -19
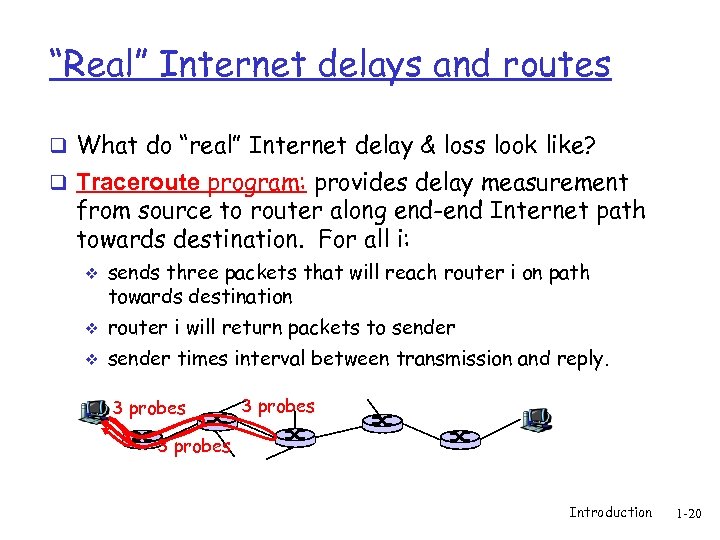 “Real” Internet delays and routes q What do “real” Internet delay & loss look like? q Traceroute program: provides delay measurement from source to router along end-end Internet path towards destination. For all i: v sends three packets that will reach router i on path towards destination v router i will return packets to sender v sender times interval between transmission and reply. 3 probes Introduction 1 -20
“Real” Internet delays and routes q What do “real” Internet delay & loss look like? q Traceroute program: provides delay measurement from source to router along end-end Internet path towards destination. For all i: v sends three packets that will reach router i on path towards destination v router i will return packets to sender v sender times interval between transmission and reply. 3 probes Introduction 1 -20
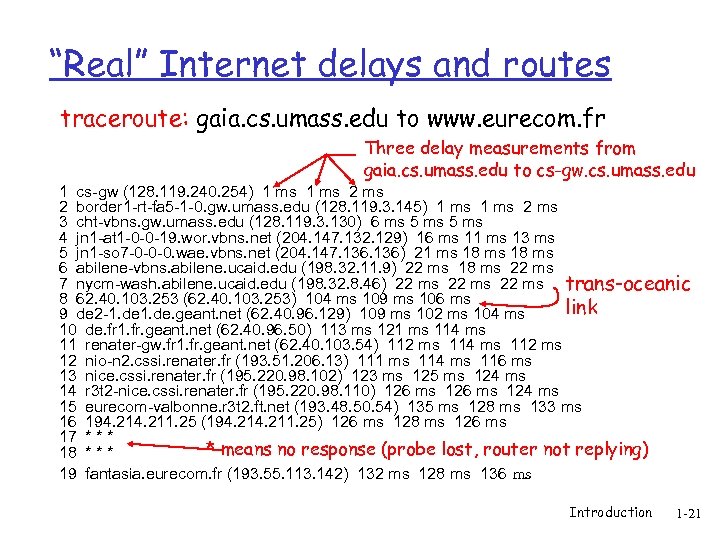 “Real” Internet delays and routes traceroute: gaia. cs. umass. edu to www. eurecom. fr Three delay measurements from gaia. cs. umass. edu to cs-gw. cs. umass. edu 1 cs-gw (128. 119. 240. 254) 1 ms 2 border 1 -rt-fa 5 -1 -0. gw. umass. edu (128. 119. 3. 145) 1 ms 2 ms 3 cht-vbns. gw. umass. edu (128. 119. 3. 130) 6 ms 5 ms 4 jn 1 -at 1 -0 -0 -19. wor. vbns. net (204. 147. 132. 129) 16 ms 11 ms 13 ms 5 jn 1 -so 7 -0 -0 -0. wae. vbns. net (204. 147. 136) 21 ms 18 ms 6 abilene-vbns. abilene. ucaid. edu (198. 32. 11. 9) 22 ms 18 ms 22 ms 7 nycm-wash. abilene. ucaid. edu (198. 32. 8. 46) 22 ms trans-oceanic 8 62. 40. 103. 253 (62. 40. 103. 253) 104 ms 109 ms 106 ms link 9 de 2 -1. de. geant. net (62. 40. 96. 129) 109 ms 102 ms 104 ms 10 de. fr 1. fr. geant. net (62. 40. 96. 50) 113 ms 121 ms 114 ms 11 renater-gw. fr 1. fr. geant. net (62. 40. 103. 54) 112 ms 114 ms 112 ms 12 nio-n 2. cssi. renater. fr (193. 51. 206. 13) 111 ms 114 ms 116 ms 13 nice. cssi. renater. fr (195. 220. 98. 102) 123 ms 125 ms 124 ms 14 r 3 t 2 -nice. cssi. renater. fr (195. 220. 98. 110) 126 ms 124 ms 15 eurecom-valbonne. r 3 t 2. ft. net (193. 48. 50. 54) 135 ms 128 ms 133 ms 16 194. 211. 25 (194. 211. 25) 126 ms 128 ms 126 ms 17 * * means no response (probe lost, router not replying) 18 * * * 19 fantasia. eurecom. fr (193. 55. 113. 142) 132 ms 128 ms 136 ms Introduction 1 -21
“Real” Internet delays and routes traceroute: gaia. cs. umass. edu to www. eurecom. fr Three delay measurements from gaia. cs. umass. edu to cs-gw. cs. umass. edu 1 cs-gw (128. 119. 240. 254) 1 ms 2 border 1 -rt-fa 5 -1 -0. gw. umass. edu (128. 119. 3. 145) 1 ms 2 ms 3 cht-vbns. gw. umass. edu (128. 119. 3. 130) 6 ms 5 ms 4 jn 1 -at 1 -0 -0 -19. wor. vbns. net (204. 147. 132. 129) 16 ms 11 ms 13 ms 5 jn 1 -so 7 -0 -0 -0. wae. vbns. net (204. 147. 136) 21 ms 18 ms 6 abilene-vbns. abilene. ucaid. edu (198. 32. 11. 9) 22 ms 18 ms 22 ms 7 nycm-wash. abilene. ucaid. edu (198. 32. 8. 46) 22 ms trans-oceanic 8 62. 40. 103. 253 (62. 40. 103. 253) 104 ms 109 ms 106 ms link 9 de 2 -1. de. geant. net (62. 40. 96. 129) 109 ms 102 ms 104 ms 10 de. fr 1. fr. geant. net (62. 40. 96. 50) 113 ms 121 ms 114 ms 11 renater-gw. fr 1. fr. geant. net (62. 40. 103. 54) 112 ms 114 ms 112 ms 12 nio-n 2. cssi. renater. fr (193. 51. 206. 13) 111 ms 114 ms 116 ms 13 nice. cssi. renater. fr (195. 220. 98. 102) 123 ms 125 ms 124 ms 14 r 3 t 2 -nice. cssi. renater. fr (195. 220. 98. 110) 126 ms 124 ms 15 eurecom-valbonne. r 3 t 2. ft. net (193. 48. 50. 54) 135 ms 128 ms 133 ms 16 194. 211. 25 (194. 211. 25) 126 ms 128 ms 126 ms 17 * * means no response (probe lost, router not replying) 18 * * * 19 fantasia. eurecom. fr (193. 55. 113. 142) 132 ms 128 ms 136 ms Introduction 1 -21
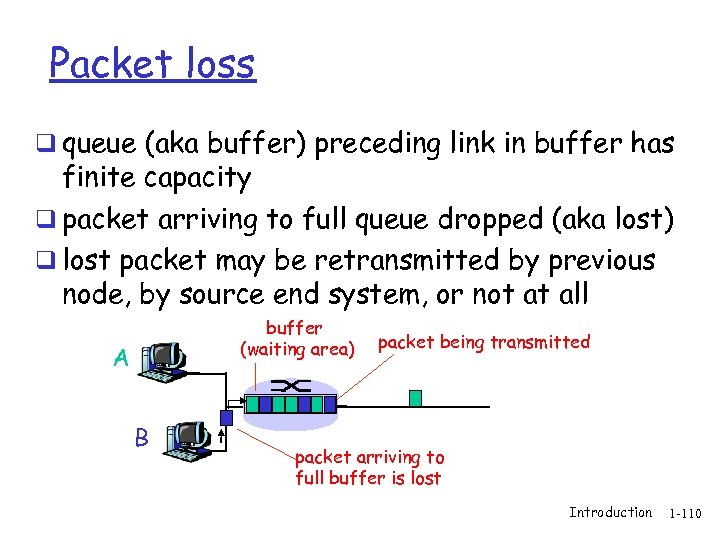 Packet loss q queue (aka buffer) preceding link in buffer has finite capacity q packet arriving to full queue dropped (aka lost) q lost packet may be retransmitted by previous node, by source end system, or not at all buffer (waiting area) A B packet being transmitted packet arriving to full buffer is lost Introduction 1 -110
Packet loss q queue (aka buffer) preceding link in buffer has finite capacity q packet arriving to full queue dropped (aka lost) q lost packet may be retransmitted by previous node, by source end system, or not at all buffer (waiting area) A B packet being transmitted packet arriving to full buffer is lost Introduction 1 -110
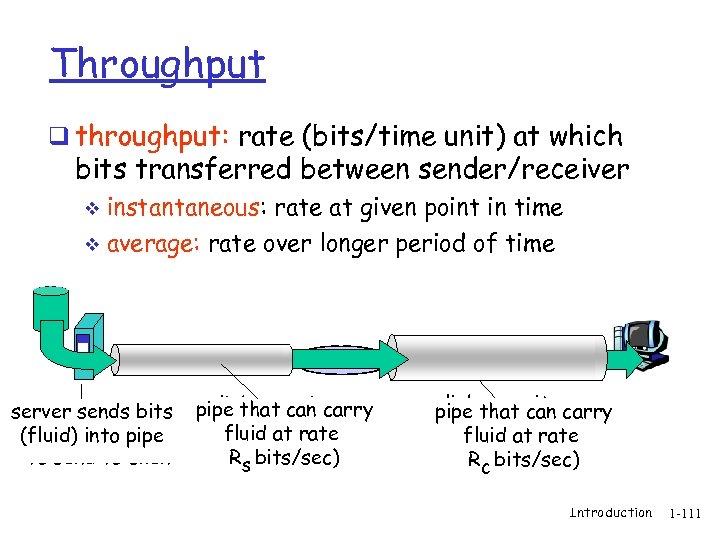 Throughput q throughput: rate (bits/time unit) at which bits transferred between sender/receiver instantaneous: rate at given point in time v average: rate over longer period of time v link capacity server, with server sends bits pipe that can carry Rs bits/sec fluid at rate file into pipe (fluid) of F bits Rs bits/sec) to send to client link capacity pipe that can carry Rfluid at rate c bits/sec Rc bits/sec) Introduction 1 -111
Throughput q throughput: rate (bits/time unit) at which bits transferred between sender/receiver instantaneous: rate at given point in time v average: rate over longer period of time v link capacity server, with server sends bits pipe that can carry Rs bits/sec fluid at rate file into pipe (fluid) of F bits Rs bits/sec) to send to client link capacity pipe that can carry Rfluid at rate c bits/sec Rc bits/sec) Introduction 1 -111
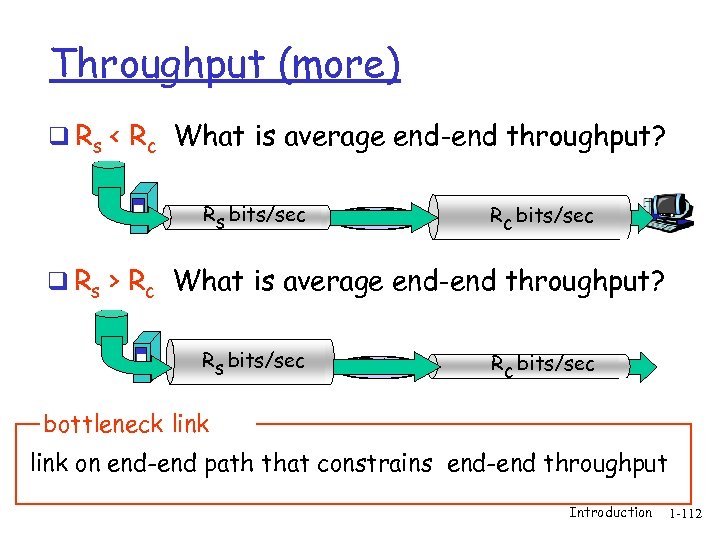 Throughput (more) q Rs < Rc What is average end-end throughput? Rs bits/sec Rc bits/sec q Rs > Rc What is average end-end throughput? Rs bits/sec Rc bits/sec bottleneck link on end-end path that constrains end-end throughput Introduction 1 -112
Throughput (more) q Rs < Rc What is average end-end throughput? Rs bits/sec Rc bits/sec q Rs > Rc What is average end-end throughput? Rs bits/sec Rc bits/sec bottleneck link on end-end path that constrains end-end throughput Introduction 1 -112
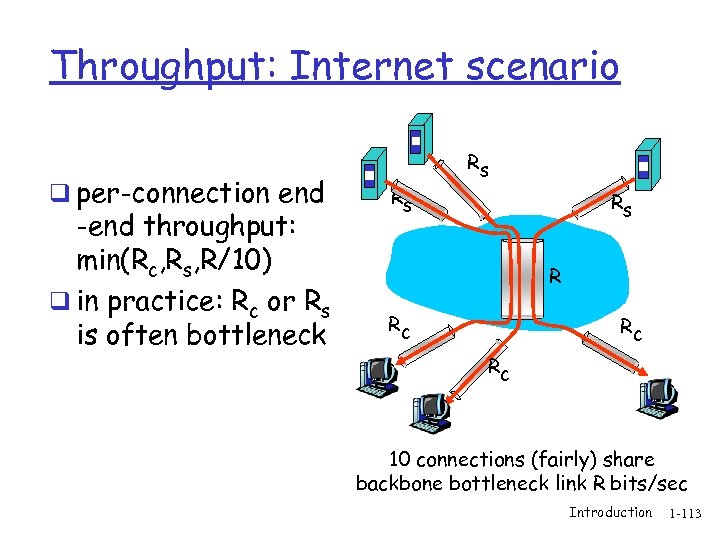 Throughput: Internet scenario q per-connection end -end throughput: min(Rc, Rs, R/10) q in practice: Rc or Rs is often bottleneck Rs Rs Rs R Rc Rc Rc 10 connections (fairly) share backbone bottleneck link R bits/sec Introduction 1 -113
Throughput: Internet scenario q per-connection end -end throughput: min(Rc, Rs, R/10) q in practice: Rc or Rs is often bottleneck Rs Rs Rs R Rc Rc Rc 10 connections (fairly) share backbone bottleneck link R bits/sec Introduction 1 -113
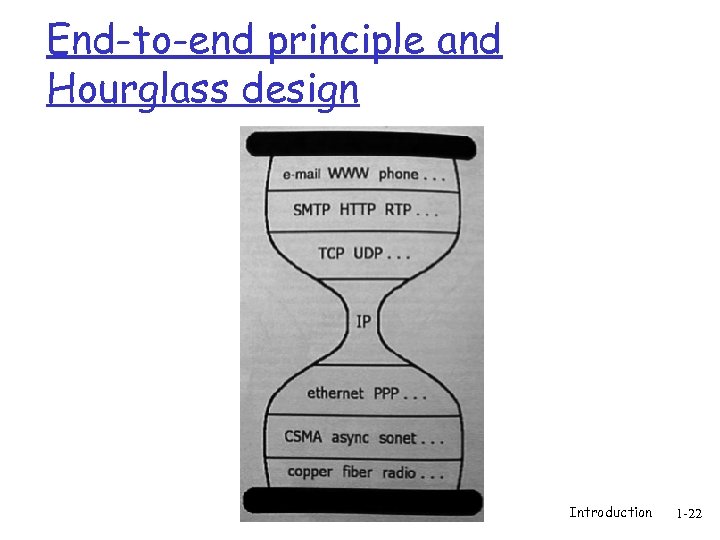 End-to-end principle and Hourglass design Introduction 1 -22
End-to-end principle and Hourglass design Introduction 1 -22
 End-to-end principle q J. H. Saltzer, D. P. Reed and D. D. Clark “End-to-end arguments in system design”, Transactions on Computer Systems, Vol. 2, No. 4, 1984 q http: //www. acm. org/pubs/citations/journals /tocs/1984 -2 -4/p 277 -saltzer/ Introduction 1 -23
End-to-end principle q J. H. Saltzer, D. P. Reed and D. D. Clark “End-to-end arguments in system design”, Transactions on Computer Systems, Vol. 2, No. 4, 1984 q http: //www. acm. org/pubs/citations/journals /tocs/1984 -2 -4/p 277 -saltzer/ Introduction 1 -23
 Hourglass design q D. Clark, “The design philosophy of the DARPA Internet”, SIGCOMM 1988, August 16 - 18, 1988. http: //www. acm. org/pubs/citations/proceedings/comm/52324/p 106 -clark/ Introduction 1 -24
Hourglass design q D. Clark, “The design philosophy of the DARPA Internet”, SIGCOMM 1988, August 16 - 18, 1988. http: //www. acm. org/pubs/citations/proceedings/comm/52324/p 106 -clark/ Introduction 1 -24
 End-to-end principle q Where to put the functionality? v In the network? At the edges? q End-to-end functions best handled by end-to-end protocols v v v Network provides basic service: data transport Intelligence and applications located in or close to devices at the edge Violate principle as a performance enhancement q Leads to innovation at the edges v Phone network: dumb edge devices, intelligent network v Internet: dumb network, intelligent edge devices Introduction 1 -25
End-to-end principle q Where to put the functionality? v In the network? At the edges? q End-to-end functions best handled by end-to-end protocols v v v Network provides basic service: data transport Intelligence and applications located in or close to devices at the edge Violate principle as a performance enhancement q Leads to innovation at the edges v Phone network: dumb edge devices, intelligent network v Internet: dumb network, intelligent edge devices Introduction 1 -25
 Hourglass design q End-to-end principle leads to “Hourglass” design of protocols q Only one protocol at the Internet level v Minimal required elements at narrowest point q IP – Internet Protocol v http: //www. rfc-editor. org/rfc 791. txt v http: //www. rfc-editor. org/rfc 1812. txt v Unreliable datagram service v Addressing and connectionless connectivity v Fragmentation and assembly Introduction 1 -26
Hourglass design q End-to-end principle leads to “Hourglass” design of protocols q Only one protocol at the Internet level v Minimal required elements at narrowest point q IP – Internet Protocol v http: //www. rfc-editor. org/rfc 791. txt v http: //www. rfc-editor. org/rfc 1812. txt v Unreliable datagram service v Addressing and connectionless connectivity v Fragmentation and assembly Introduction 1 -26
 Hourglass design q Simplicity allowed fast deployment of multi-vendor, multi-provider public network v Ease of implementation v Limited hardware requirements (important in 1970 s) • Is it relevant now with today’s semiconductor speeds? v Eventual economies of scale q Designed independently of hardware v Hardware addresses decoupled from IP addresses v IP header contains no data/physical link specific information v Allows IP to run over any fabric Introduction 1 -27
Hourglass design q Simplicity allowed fast deployment of multi-vendor, multi-provider public network v Ease of implementation v Limited hardware requirements (important in 1970 s) • Is it relevant now with today’s semiconductor speeds? v Eventual economies of scale q Designed independently of hardware v Hardware addresses decoupled from IP addresses v IP header contains no data/physical link specific information v Allows IP to run over any fabric Introduction 1 -27
 Hourglass design q Waist expands at transport layer q Two dominant services layered above IP q TCP – Transmission Control Protocol Connection-oriented service v http: //www. rfc-editor. org/rfc 793. txt v q UDP – User Datagram Protocol Connectionless service v http: //www. rfc-editor. org/rfc 768. txt v Introduction 1 -28
Hourglass design q Waist expands at transport layer q Two dominant services layered above IP q TCP – Transmission Control Protocol Connection-oriented service v http: //www. rfc-editor. org/rfc 793. txt v q UDP – User Datagram Protocol Connectionless service v http: //www. rfc-editor. org/rfc 768. txt v Introduction 1 -28
 Hourglass design q TCP – Transmission Control Protocol v Reliable, in-order byte-stream data transfer • Acknowledgements and retransmissions v Flow control • Sender won’t overwhelm receiver v Congestion control • Senders won’t overwhelm network Introduction 1 -29
Hourglass design q TCP – Transmission Control Protocol v Reliable, in-order byte-stream data transfer • Acknowledgements and retransmissions v Flow control • Sender won’t overwhelm receiver v Congestion control • Senders won’t overwhelm network Introduction 1 -29
 Hourglass design q UDP – User Datagram Protocol v Unreliable data transfer No flow control v No congestion control v Introduction 1 -30
Hourglass design q UDP – User Datagram Protocol v Unreliable data transfer No flow control v No congestion control v Introduction 1 -30
 Hourglass design q What uses TCP? v HTTP, FTP, Telnet, SMTP, NNTP, BGP, IMAP, POP q What uses (mainly) UDP? v SNMP, NTP, NFS, RTP (streaming media, IP telephony, teleconferencing), multicast applications v Many protocols can use both q Check out /etc/services on *nix or C: WIN*system 32services q IANA v http: //www. iana. org/assignments/port-numbers Introduction 1 -31
Hourglass design q What uses TCP? v HTTP, FTP, Telnet, SMTP, NNTP, BGP, IMAP, POP q What uses (mainly) UDP? v SNMP, NTP, NFS, RTP (streaming media, IP telephony, teleconferencing), multicast applications v Many protocols can use both q Check out /etc/services on *nix or C: WIN*system 32services q IANA v http: //www. iana. org/assignments/port-numbers Introduction 1 -31
 Hourglass design q Security? q Quality-of-service? q Reliable, out-of-order delivery service? q Handling greedy sources? q Accounting and pricing support? q IPsec, Diff. Serv, SCTP, …. Back Introduction 1 -32
Hourglass design q Security? q Quality-of-service? q Reliable, out-of-order delivery service? q Handling greedy sources? q Accounting and pricing support? q IPsec, Diff. Serv, SCTP, …. Back Introduction 1 -32
 Hourglass design q Security? q Quality-of-service? q Reliable, out-of-order delivery service? q Handling greedy sources? q Accounting and pricing support? q IPsec, Diff. Serv, SCTP, …. Back Introduction 1 -33
Hourglass design q Security? q Quality-of-service? q Reliable, out-of-order delivery service? q Handling greedy sources? q Accounting and pricing support? q IPsec, Diff. Serv, SCTP, …. Back Introduction 1 -33
 End-to-end principle/Hourglass design q The good v Basic network functionality allowed for extremely quick adoption and deployment using simple devices q The bad New network features and functionality are impossible to deploy, requiring widespread adoption within the network v IP Multicast, Qo. S v Back Introduction 1 -34
End-to-end principle/Hourglass design q The good v Basic network functionality allowed for extremely quick adoption and deployment using simple devices q The bad New network features and functionality are impossible to deploy, requiring widespread adoption within the network v IP Multicast, Qo. S v Back Introduction 1 -34
 Why layering? Dealing with complex systems: q explicit structure allows identification, relationship of complex system’s pieces v layered reference model for discussion q modularization eases maintenance, updating of system v change of implementation of layer’s service transparent to rest of system v e. g. , change in gate procedure doesn’t affect rest of system q layering considered harmful? Introduction 1 -118
Why layering? Dealing with complex systems: q explicit structure allows identification, relationship of complex system’s pieces v layered reference model for discussion q modularization eases maintenance, updating of system v change of implementation of layer’s service transparent to rest of system v e. g. , change in gate procedure doesn’t affect rest of system q layering considered harmful? Introduction 1 -118
 Layering q Modular approach to network functionality v Simplifies complex systems Each layer relies on services from layer below and exports services to layer above v Hides implementation, eases maintenance and updating of system v • Layer implementations can change without disturbing other layers (black box) Introduction 1 -35
Layering q Modular approach to network functionality v Simplifies complex systems Each layer relies on services from layer below and exports services to layer above v Hides implementation, eases maintenance and updating of system v • Layer implementations can change without disturbing other layers (black box) Introduction 1 -35
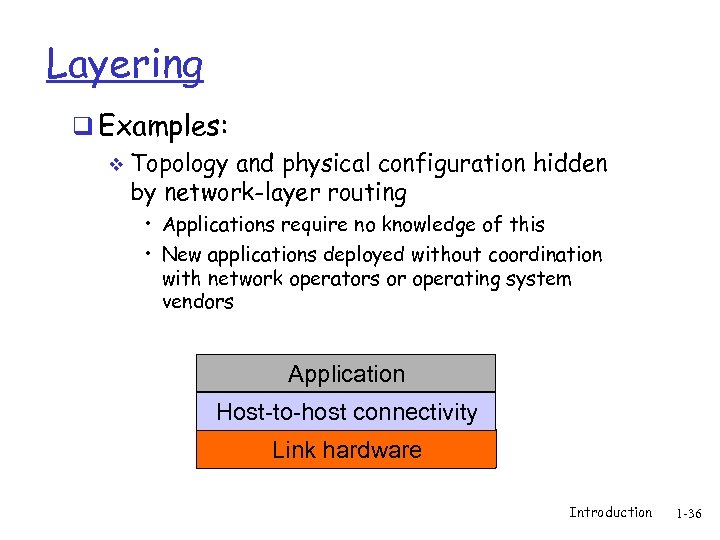 Layering q Examples: v Topology and physical configuration hidden by network-layer routing • Applications require no knowledge of this • New applications deployed without coordination with network operators or operating system vendors Application Host-to-host connectivity Link hardware Introduction 1 -36
Layering q Examples: v Topology and physical configuration hidden by network-layer routing • Applications require no knowledge of this • New applications deployed without coordination with network operators or operating system vendors Application Host-to-host connectivity Link hardware Introduction 1 -36
 Layering in Protocols q Set of rules governing communication between network elements (applications, hosts, routers) q Protocols specify: Interface to higher layers (API) v Interface to peer v • Format and order of messages • Actions taken on receipt of a message v Interface defines interaction Introduction 1 -37
Layering in Protocols q Set of rules governing communication between network elements (applications, hosts, routers) q Protocols specify: Interface to higher layers (API) v Interface to peer v • Format and order of messages • Actions taken on receipt of a message v Interface defines interaction Introduction 1 -37
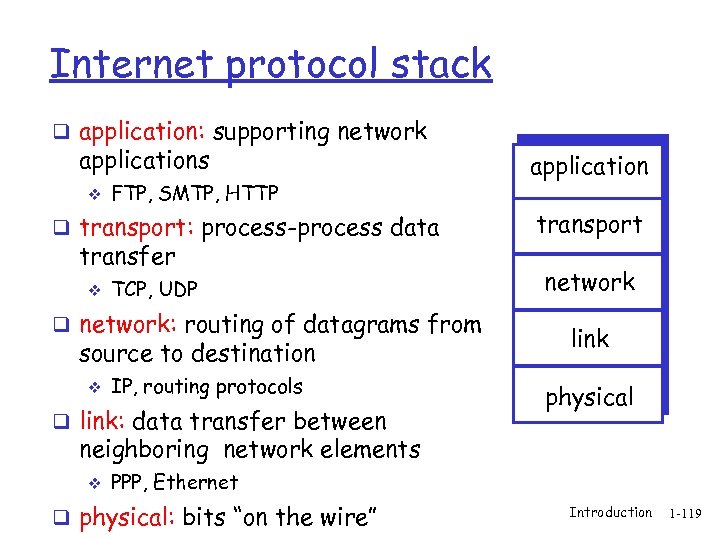 Internet protocol stack q application: supporting network applications v FTP, SMTP, HTTP q transport: process-process data transfer v TCP, UDP q network: routing of datagrams from source to destination v IP, routing protocols q link: data transfer between application transport network link physical neighboring network elements v PPP, Ethernet q physical: bits “on the wire” Introduction 1 -119
Internet protocol stack q application: supporting network applications v FTP, SMTP, HTTP q transport: process-process data transfer v TCP, UDP q network: routing of datagrams from source to destination v IP, routing protocols q link: data transfer between application transport network link physical neighboring network elements v PPP, Ethernet q physical: bits “on the wire” Introduction 1 -119
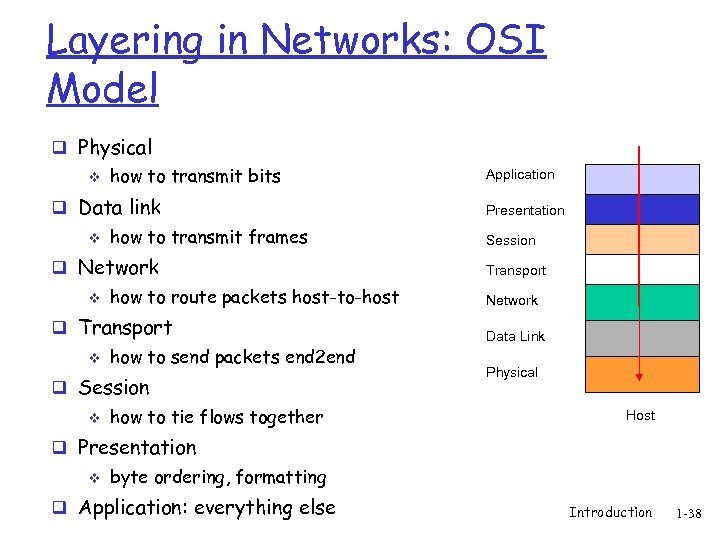 Layering in Networks: OSI Model q Physical v how to transmit bits q Data link v how to transmit frames q Network v how to route packets host-to-host q Transport v how to send packets end 2 end q Session v how to tie flows together Application Presentation Session Transport Network Data Link Physical Host q Presentation v byte ordering, formatting q Application: everything else Introduction 1 -38
Layering in Networks: OSI Model q Physical v how to transmit bits q Data link v how to transmit frames q Network v how to route packets host-to-host q Transport v how to send packets end 2 end q Session v how to tie flows together Application Presentation Session Transport Network Data Link Physical Host q Presentation v byte ordering, formatting q Application: everything else Introduction 1 -38
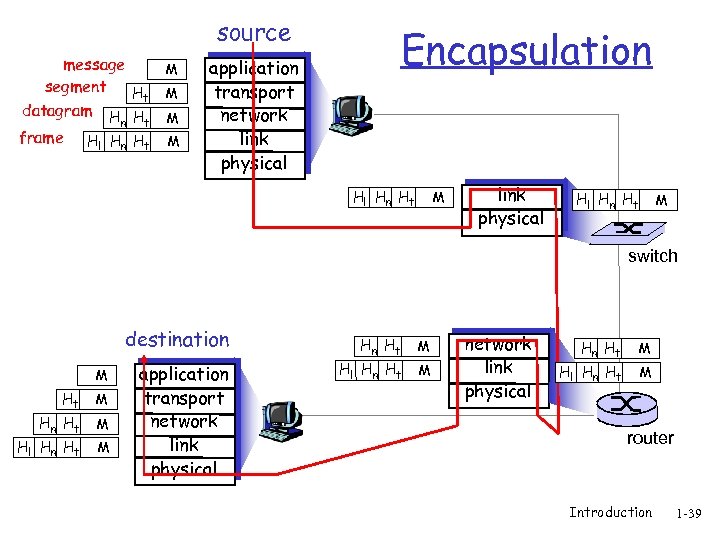 source message segment Ht datagram H H M t M Hl Hn Ht M frame n M application transport network link physical Encapsulation Hl Hn Ht M link physical Hl Hn Ht M switch destination M Ht M Hn Ht Hl Hn Ht M M application transport network link physical Hn Ht Hl Hn Ht M M router Introduction 1 -39
source message segment Ht datagram H H M t M Hl Hn Ht M frame n M application transport network link physical Encapsulation Hl Hn Ht M link physical Hl Hn Ht M switch destination M Ht M Hn Ht Hl Hn Ht M M application transport network link physical Hn Ht Hl Hn Ht M M router Introduction 1 -39
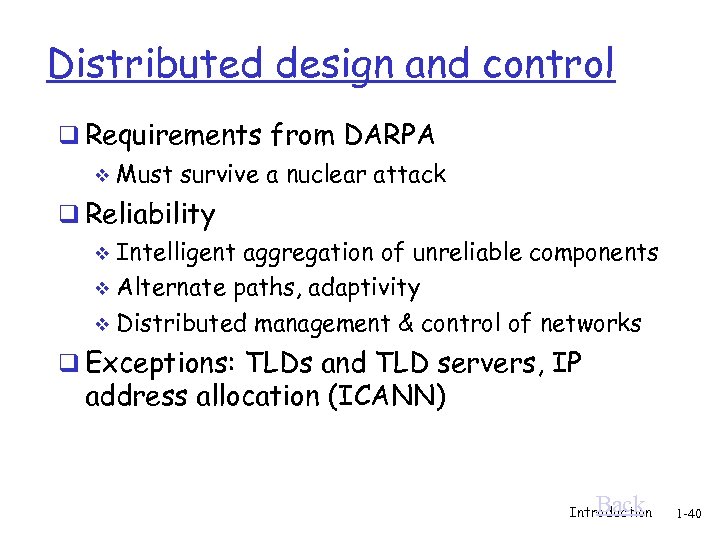 Distributed design and control q Requirements from DARPA v Must survive a nuclear attack q Reliability Intelligent aggregation of unreliable components v Alternate paths, adaptivity v Distributed management & control of networks v q Exceptions: TLDs and TLD servers, IP address allocation (ICANN) Back Introduction 1 -40
Distributed design and control q Requirements from DARPA v Must survive a nuclear attack q Reliability Intelligent aggregation of unreliable components v Alternate paths, adaptivity v Distributed management & control of networks v q Exceptions: TLDs and TLD servers, IP address allocation (ICANN) Back Introduction 1 -40
 Superior organizational process q IAB/IETF process allowed for quick specification, implementation, and deployment of new standards Free and easy download of standards v Rough consensus and running code v 2 interoperable implementations v Bake-offs v http: //www. ietf. org/ v q ISO/OSI v Comparison to IETF left as an exercise Back Introduction 1 -41
Superior organizational process q IAB/IETF process allowed for quick specification, implementation, and deployment of new standards Free and easy download of standards v Rough consensus and running code v 2 interoperable implementations v Bake-offs v http: //www. ietf. org/ v q ISO/OSI v Comparison to IETF left as an exercise Back Introduction 1 -41
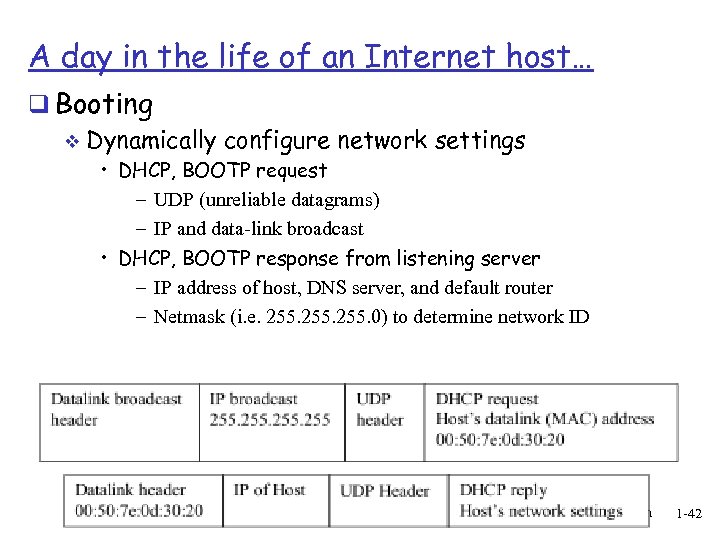 A day in the life of an Internet host… q Booting v Dynamically configure network settings • DHCP, BOOTP request – UDP (unreliable datagrams) – IP and data-link broadcast • DHCP, BOOTP response from listening server – IP address of host, DNS server, and default router – Netmask (i. e. 255. 0) to determine network ID Introduction 1 -42
A day in the life of an Internet host… q Booting v Dynamically configure network settings • DHCP, BOOTP request – UDP (unreliable datagrams) – IP and data-link broadcast • DHCP, BOOTP response from listening server – IP address of host, DNS server, and default router – Netmask (i. e. 255. 0) to determine network ID Introduction 1 -42
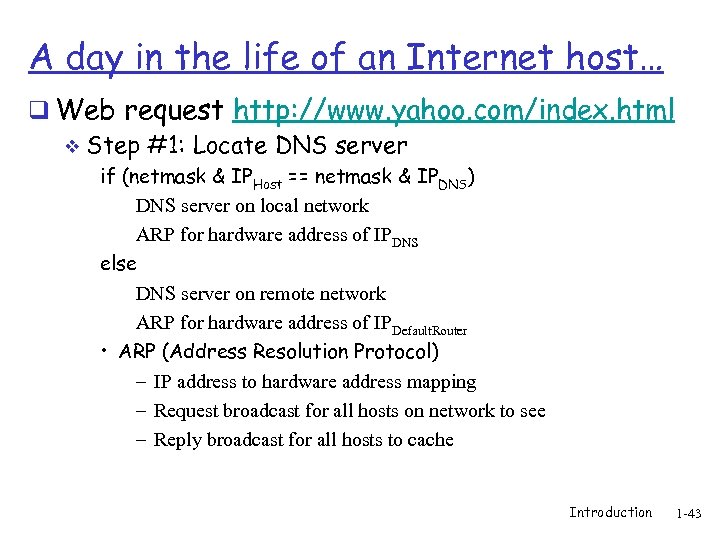 A day in the life of an Internet host… q Web request http: //www. yahoo. com/index. html v Step #1: Locate DNS server if (netmask & IPHost == netmask & IPDNS) DNS server on local network ARP for hardware address of IPDNS else DNS server on remote network ARP for hardware address of IPDefault. Router • ARP (Address Resolution Protocol) – IP address to hardware address mapping – Request broadcast for all hosts on network to see – Reply broadcast for all hosts to cache Introduction 1 -43
A day in the life of an Internet host… q Web request http: //www. yahoo. com/index. html v Step #1: Locate DNS server if (netmask & IPHost == netmask & IPDNS) DNS server on local network ARP for hardware address of IPDNS else DNS server on remote network ARP for hardware address of IPDefault. Router • ARP (Address Resolution Protocol) – IP address to hardware address mapping – Request broadcast for all hosts on network to see – Reply broadcast for all hosts to cache Introduction 1 -43
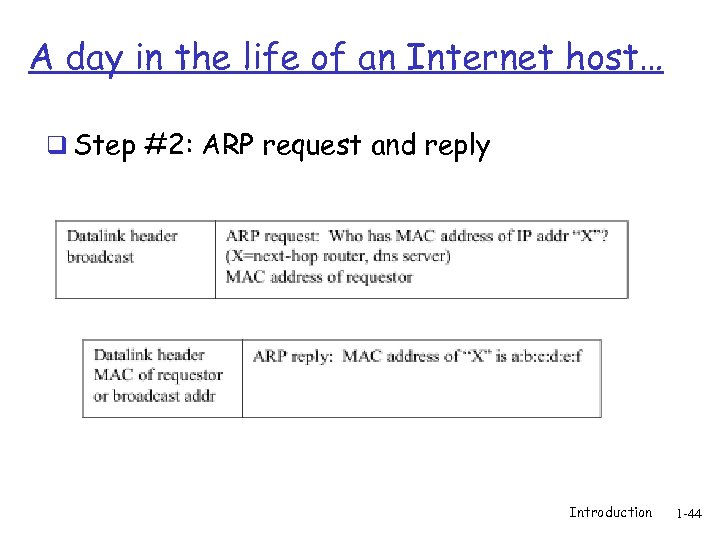 A day in the life of an Internet host… q Step #2: ARP request and reply Introduction 1 -44
A day in the life of an Internet host… q Step #2: ARP request and reply Introduction 1 -44
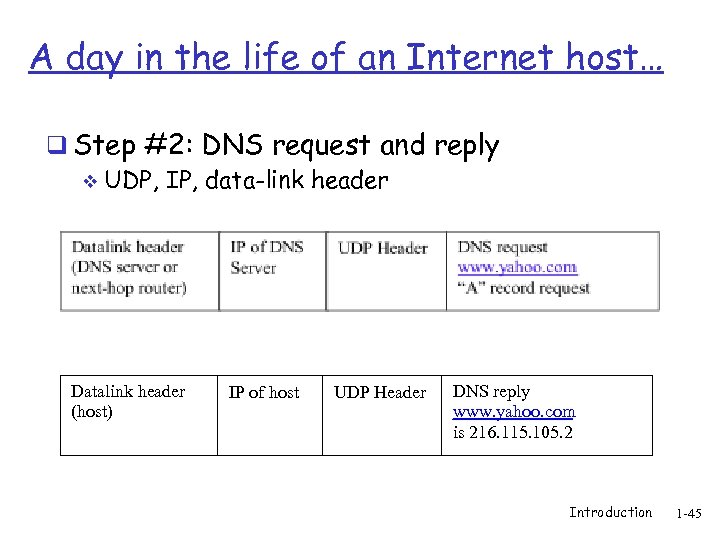 A day in the life of an Internet host… q Step #2: DNS request and reply v UDP, IP, data-link header Datalink header (host) IP of host UDP Header DNS reply www. yahoo. com is 216. 115. 105. 2 Introduction 1 -45
A day in the life of an Internet host… q Step #2: DNS request and reply v UDP, IP, data-link header Datalink header (host) IP of host UDP Header DNS reply www. yahoo. com is 216. 115. 105. 2 Introduction 1 -45
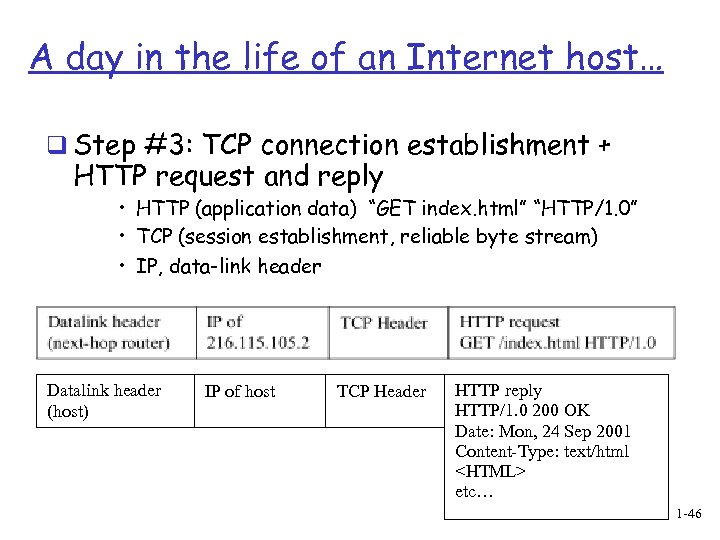 A day in the life of an Internet host… q Step #3: TCP connection establishment + HTTP request and reply • HTTP (application data) “GET index. html” “HTTP/1. 0” • TCP (session establishment, reliable byte stream) • IP, data-link header Datalink header (host) IP of host TCP Header HTTP reply HTTP/1. 0 200 OK Date: Mon, 24 Sep 2001 Content-Type: text/html etc… Introduction 1 -46
A day in the life of an Internet host… q Step #3: TCP connection establishment + HTTP request and reply • HTTP (application data) “GET index. html” “HTTP/1. 0” • TCP (session establishment, reliable byte stream) • IP, data-link header Datalink header (host) IP of host TCP Header HTTP reply HTTP/1. 0 200 OK Date: Mon, 24 Sep 2001 Content-Type: text/html etc… Introduction 1 -46
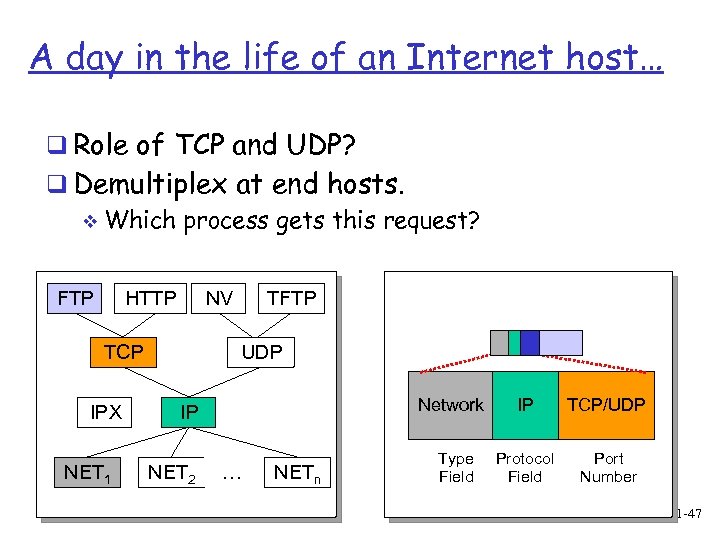 A day in the life of an Internet host… q Role of TCP and UDP? q Demultiplex at end hosts. v Which process gets this request? FTP HTTP NV TCP IPX NET 1 TFTP UDP Network IP NET 2 … NETn Type Field IP TCP/UDP Protocol Field Port Number Introduction 1 -47
A day in the life of an Internet host… q Role of TCP and UDP? q Demultiplex at end hosts. v Which process gets this request? FTP HTTP NV TCP IPX NET 1 TFTP UDP Network IP NET 2 … NETn Type Field IP TCP/UDP Protocol Field Port Number Introduction 1 -47
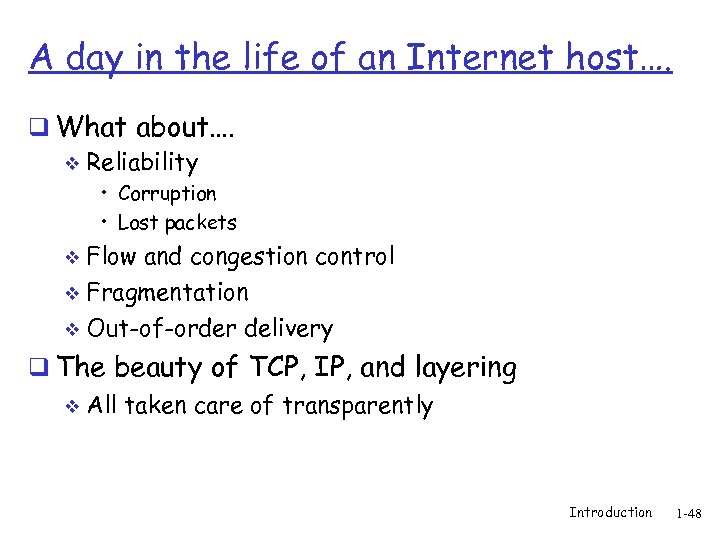 A day in the life of an Internet host…. q What about…. v Reliability • Corruption • Lost packets Flow and congestion control v Fragmentation v Out-of-order delivery v q The beauty of TCP, IP, and layering v All taken care of transparently Introduction 1 -48
A day in the life of an Internet host…. q What about…. v Reliability • Corruption • Lost packets Flow and congestion control v Fragmentation v Out-of-order delivery v q The beauty of TCP, IP, and layering v All taken care of transparently Introduction 1 -48
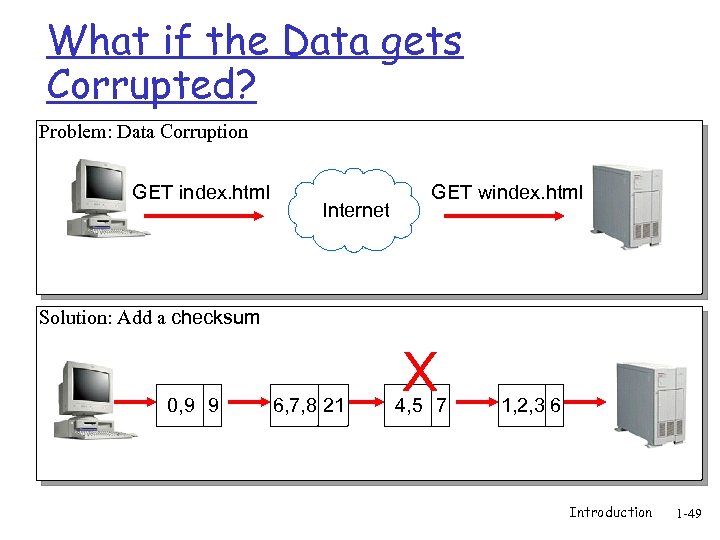 What if the Data gets Corrupted? Problem: Data Corruption GET index. html Internet GET windex. html Solution: Add a checksum 0, 9 9 6, 7, 8 21 X 4, 5 7 1, 2, 3 6 Introduction 1 -49
What if the Data gets Corrupted? Problem: Data Corruption GET index. html Internet GET windex. html Solution: Add a checksum 0, 9 9 6, 7, 8 21 X 4, 5 7 1, 2, 3 6 Introduction 1 -49
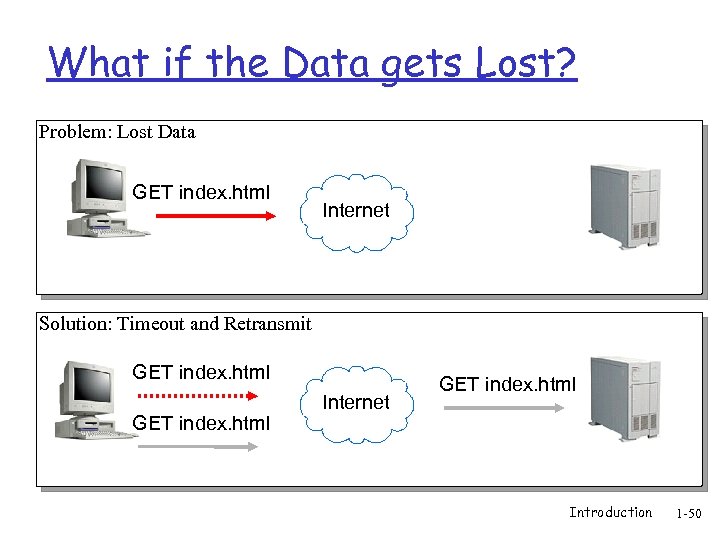 What if the Data gets Lost? Problem: Lost Data GET index. html Internet Solution: Timeout and Retransmit GET index. html Internet GET index. html Introduction 1 -50
What if the Data gets Lost? Problem: Lost Data GET index. html Internet Solution: Timeout and Retransmit GET index. html Internet GET index. html Introduction 1 -50
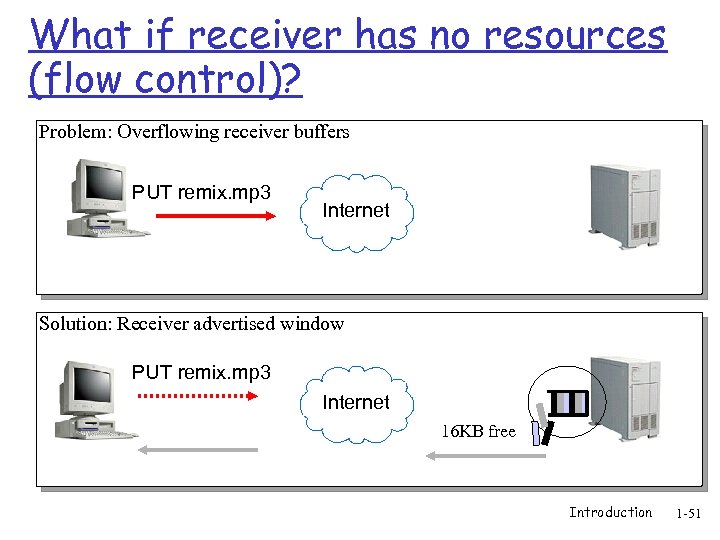 What if receiver has no resources (flow control)? Problem: Overflowing receiver buffers PUT remix. mp 3 Internet Solution: Receiver advertised window PUT remix. mp 3 Internet 16 KB free Introduction 1 -51
What if receiver has no resources (flow control)? Problem: Overflowing receiver buffers PUT remix. mp 3 Internet Solution: Receiver advertised window PUT remix. mp 3 Internet 16 KB free Introduction 1 -51
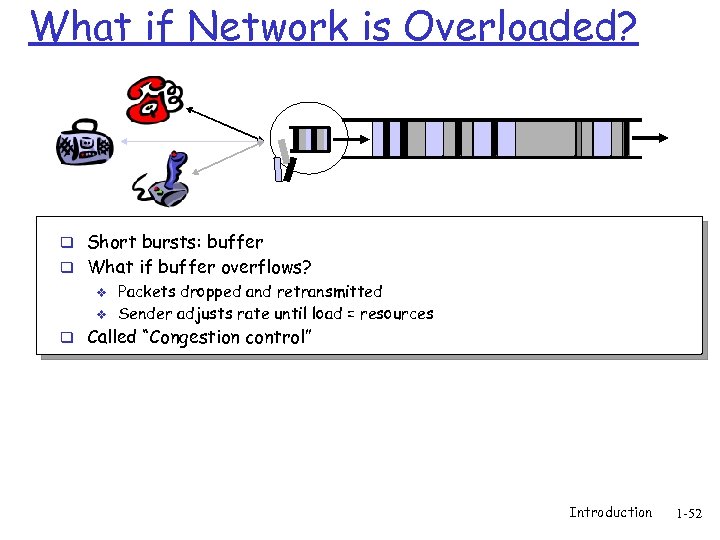 What if Network is Overloaded? q Short bursts: buffer q What if buffer overflows? v Packets dropped and retransmitted v Sender adjusts rate until load = resources q Called “Congestion control” Introduction 1 -52
What if Network is Overloaded? q Short bursts: buffer q What if buffer overflows? v Packets dropped and retransmitted v Sender adjusts rate until load = resources q Called “Congestion control” Introduction 1 -52
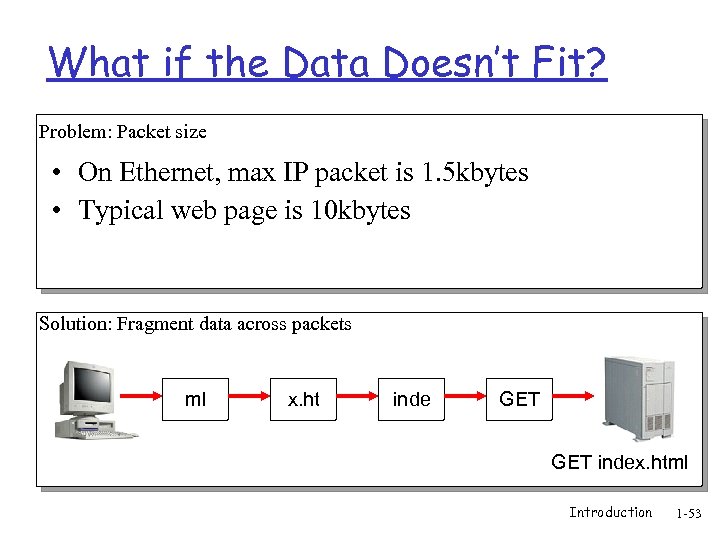 What if the Data Doesn’t Fit? Problem: Packet size • On Ethernet, max IP packet is 1. 5 kbytes • Typical web page is 10 kbytes Solution: Fragment data across packets ml x. ht inde GET index. html Introduction 1 -53
What if the Data Doesn’t Fit? Problem: Packet size • On Ethernet, max IP packet is 1. 5 kbytes • Typical web page is 10 kbytes Solution: Fragment data across packets ml x. ht inde GET index. html Introduction 1 -53
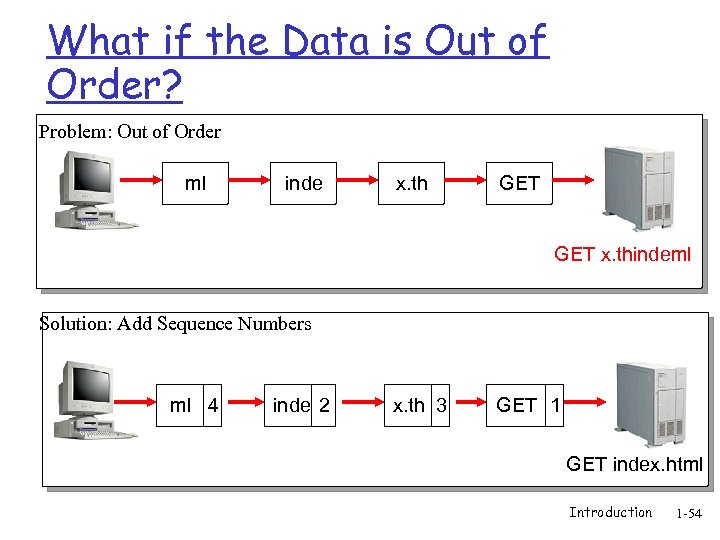 What if the Data is Out of Order? Problem: Out of Order ml inde x. th GET x. thindeml Solution: Add Sequence Numbers ml 4 inde 2 x. th 3 GET 1 GET index. html Introduction 1 -54
What if the Data is Out of Order? Problem: Out of Order ml inde x. th GET x. thindeml Solution: Add Sequence Numbers ml 4 inde 2 x. th 3 GET 1 GET index. html Introduction 1 -54
 The rest of the course q From birds-eye view, we will now focus on specific components q Review these lectures for perspective when looking at the components q Mostly classical material with some references to newer technologies Introduction 1 -55
The rest of the course q From birds-eye view, we will now focus on specific components q Review these lectures for perspective when looking at the components q Mostly classical material with some references to newer technologies Introduction 1 -55
 Extra slides Introduction 1 -56
Extra slides Introduction 1 -56
 Chapter 1: Introduction Our goal: Overview: q get “feel” and q what’s the Internet? terminology q more depth, detail later in course q approach: v use Internet as example q what’s a protocol? q network edge; hosts, access net, q q q physical media network core: packet/circuit switching, Internet structure performance: loss, delay, throughput security protocol layers, service models history Introduction 1 -57
Chapter 1: Introduction Our goal: Overview: q get “feel” and q what’s the Internet? terminology q more depth, detail later in course q approach: v use Internet as example q what’s a protocol? q network edge; hosts, access net, q q q physical media network core: packet/circuit switching, Internet structure performance: loss, delay, throughput security protocol layers, service models history Introduction 1 -57
 Chapter 1: roadmap 1. 1 What is the Internet? 1. 2 Network edge q end systems, access networks, links 1. 3 Network core q circuit switching, packet switching, network structure 1. 4 Delay, loss and throughput in packet-switched networks 1. 5 Protocol layers, service models 1. 6 Networks under attack: security 1. 7 History Introduction 1 -58
Chapter 1: roadmap 1. 1 What is the Internet? 1. 2 Network edge q end systems, access networks, links 1. 3 Network core q circuit switching, packet switching, network structure 1. 4 Delay, loss and throughput in packet-switched networks 1. 5 Protocol layers, service models 1. 6 Networks under attack: security 1. 7 History Introduction 1 -58
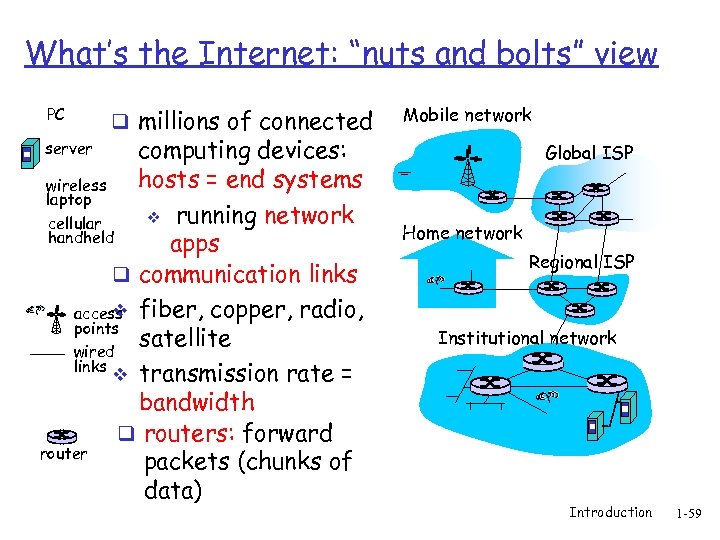 What’s the Internet: “nuts and bolts” view PC q millions of connected computing devices: hosts = end systems wireless laptop v running network cellular handheld apps q communication links v access fiber, copper, radio, points satellite wired links v transmission rate = bandwidth q routers: forward router packets (chunks of data) server Mobile network Global ISP Home network Regional ISP Institutional network Introduction 1 -59
What’s the Internet: “nuts and bolts” view PC q millions of connected computing devices: hosts = end systems wireless laptop v running network cellular handheld apps q communication links v access fiber, copper, radio, points satellite wired links v transmission rate = bandwidth q routers: forward router packets (chunks of data) server Mobile network Global ISP Home network Regional ISP Institutional network Introduction 1 -59
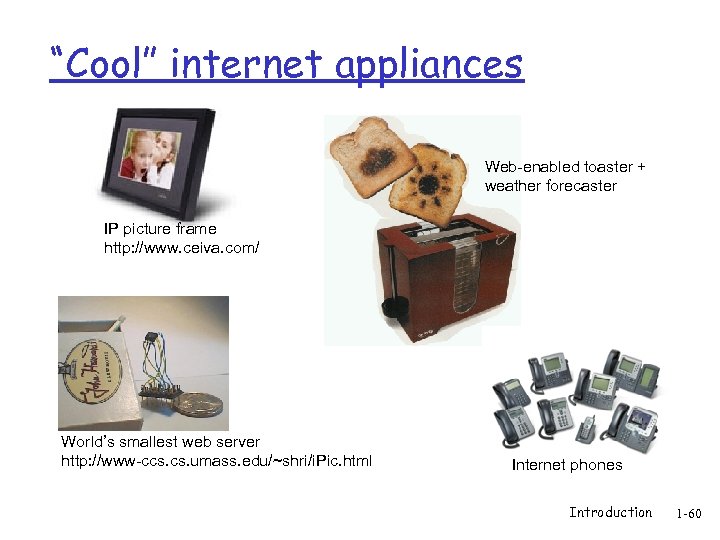 “Cool” internet appliances Web-enabled toaster + weather forecaster IP picture frame http: //www. ceiva. com/ World’s smallest web server http: //www-ccs. umass. edu/~shri/i. Pic. html Internet phones Introduction 1 -60
“Cool” internet appliances Web-enabled toaster + weather forecaster IP picture frame http: //www. ceiva. com/ World’s smallest web server http: //www-ccs. umass. edu/~shri/i. Pic. html Internet phones Introduction 1 -60
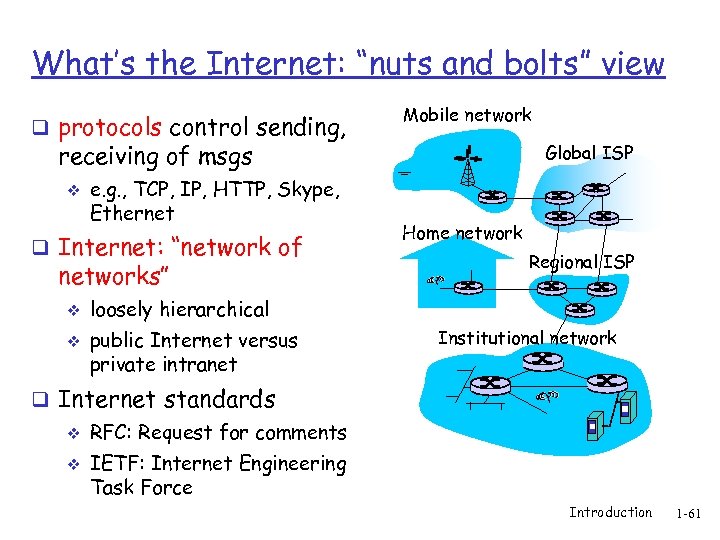 What’s the Internet: “nuts and bolts” view q protocols control sending, Mobile network receiving of msgs v e. g. , TCP, IP, HTTP, Skype, Ethernet q Internet: “network of networks” v v Global ISP Home network Regional ISP loosely hierarchical public Internet versus private intranet Institutional network q Internet standards v v RFC: Request for comments IETF: Internet Engineering Task Force Introduction 1 -61
What’s the Internet: “nuts and bolts” view q protocols control sending, Mobile network receiving of msgs v e. g. , TCP, IP, HTTP, Skype, Ethernet q Internet: “network of networks” v v Global ISP Home network Regional ISP loosely hierarchical public Internet versus private intranet Institutional network q Internet standards v v RFC: Request for comments IETF: Internet Engineering Task Force Introduction 1 -61
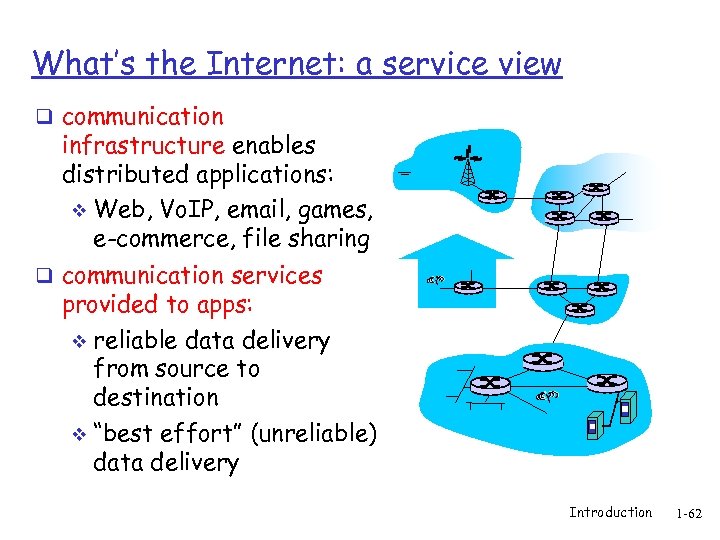 What’s the Internet: a service view q communication infrastructure enables distributed applications: v Web, Vo. IP, email, games, e-commerce, file sharing q communication services provided to apps: v reliable data delivery from source to destination v “best effort” (unreliable) data delivery Introduction 1 -62
What’s the Internet: a service view q communication infrastructure enables distributed applications: v Web, Vo. IP, email, games, e-commerce, file sharing q communication services provided to apps: v reliable data delivery from source to destination v “best effort” (unreliable) data delivery Introduction 1 -62
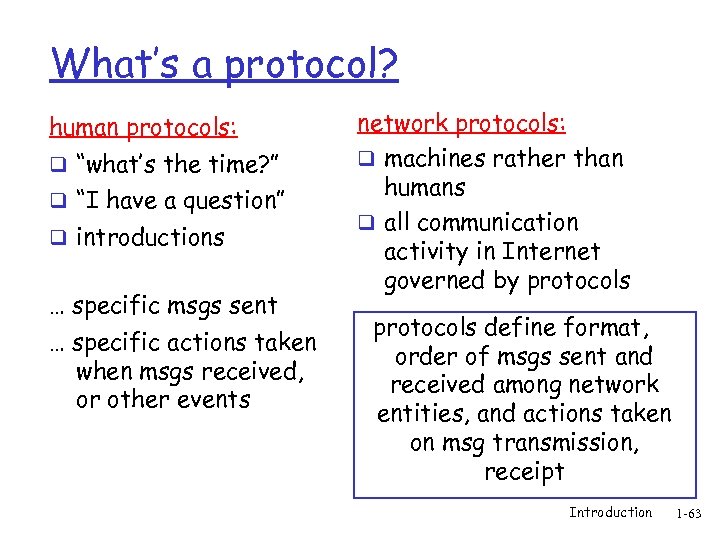 What’s a protocol? human protocols: q “what’s the time? ” q “I have a question” q introductions … specific msgs sent … specific actions taken when msgs received, or other events network protocols: q machines rather than humans q all communication activity in Internet governed by protocols define format, order of msgs sent and received among network entities, and actions taken on msg transmission, receipt Introduction 1 -63
What’s a protocol? human protocols: q “what’s the time? ” q “I have a question” q introductions … specific msgs sent … specific actions taken when msgs received, or other events network protocols: q machines rather than humans q all communication activity in Internet governed by protocols define format, order of msgs sent and received among network entities, and actions taken on msg transmission, receipt Introduction 1 -63
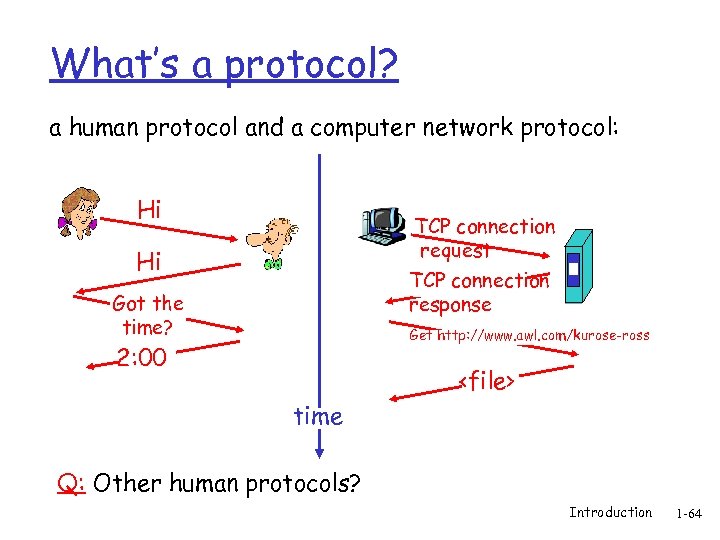 What’s a protocol? a human protocol and a computer network protocol: Hi TCP connection request Hi TCP connection response Got the time? Get http: //www. awl. com/kurose-ross 2: 00
What’s a protocol? a human protocol and a computer network protocol: Hi TCP connection request Hi TCP connection response Got the time? Get http: //www. awl. com/kurose-ross 2: 00
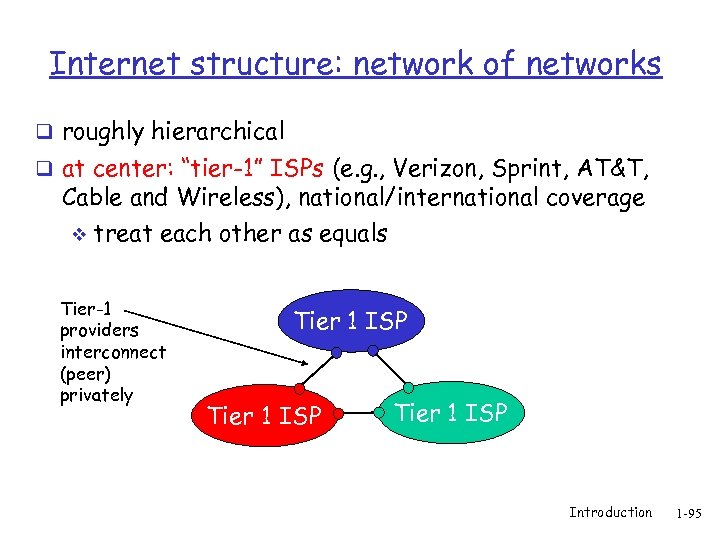 Internet structure: network of networks q roughly hierarchical q at center: “tier-1” ISPs (e. g. , Verizon, Sprint, AT&T, Cable and Wireless), national/international coverage v treat each other as equals Tier-1 providers interconnect (peer) privately Tier 1 ISP Introduction 1 -95
Internet structure: network of networks q roughly hierarchical q at center: “tier-1” ISPs (e. g. , Verizon, Sprint, AT&T, Cable and Wireless), national/international coverage v treat each other as equals Tier-1 providers interconnect (peer) privately Tier 1 ISP Introduction 1 -95
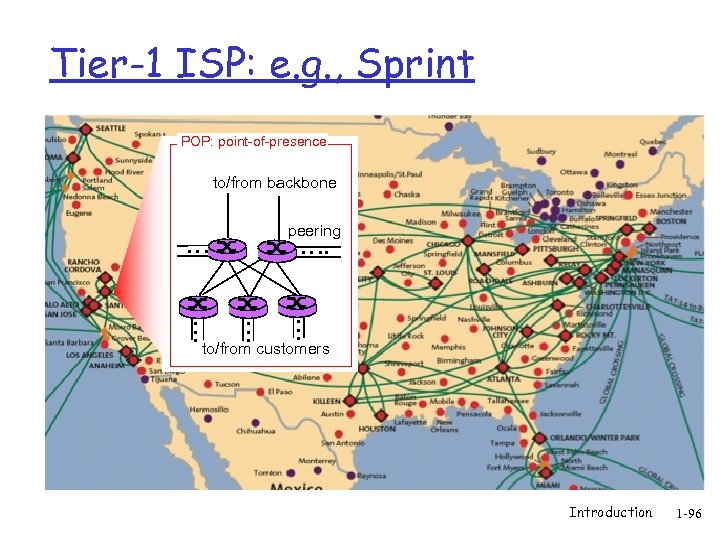 Tier-1 ISP: e. g. , Sprint POP: point-of-presence to/from backbone peering … … … to/from customers Introduction 1 -96
Tier-1 ISP: e. g. , Sprint POP: point-of-presence to/from backbone peering … … … to/from customers Introduction 1 -96
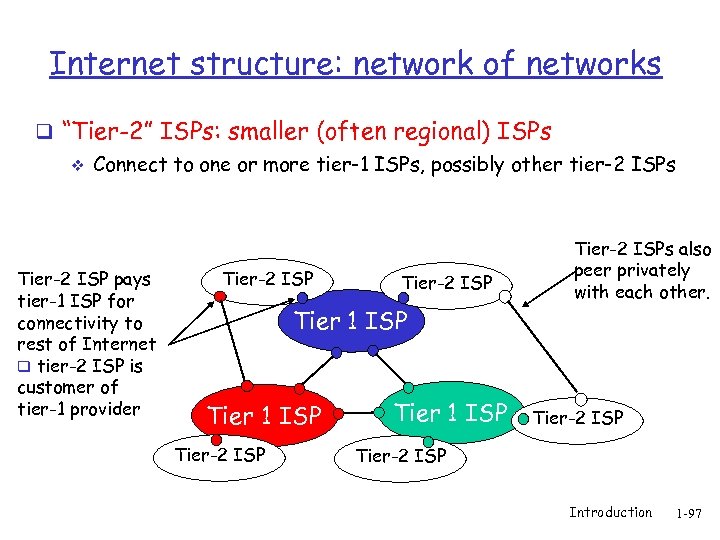 Internet structure: network of networks q “Tier-2” ISPs: smaller (often regional) ISPs v Connect to one or more tier-1 ISPs, possibly other tier-2 ISPs Tier-2 ISP pays tier-1 ISP for connectivity to rest of Internet q tier-2 ISP is customer of tier-1 provider Tier-2 ISP Tier 1 ISP Tier-2 ISPs also peer privately with each other. Tier-2 ISP Introduction 1 -97
Internet structure: network of networks q “Tier-2” ISPs: smaller (often regional) ISPs v Connect to one or more tier-1 ISPs, possibly other tier-2 ISPs Tier-2 ISP pays tier-1 ISP for connectivity to rest of Internet q tier-2 ISP is customer of tier-1 provider Tier-2 ISP Tier 1 ISP Tier-2 ISPs also peer privately with each other. Tier-2 ISP Introduction 1 -97
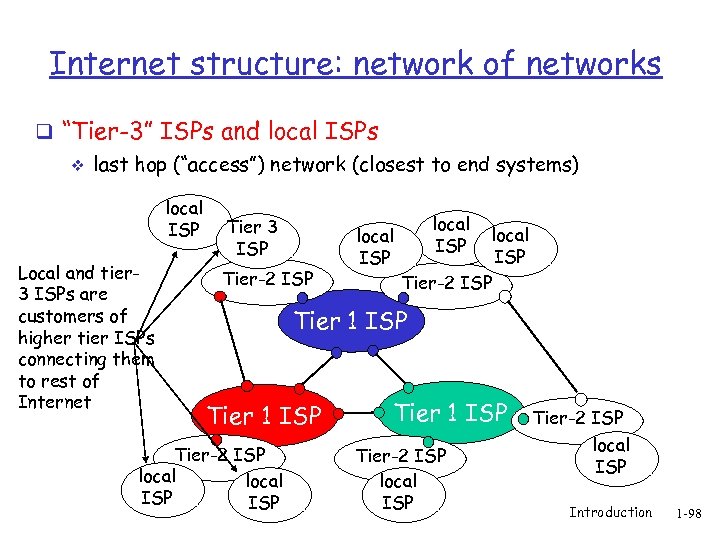 Internet structure: network of networks q “Tier-3” ISPs and local ISPs v last hop (“access”) network (closest to end systems) local ISP Local and tier 3 ISPs are customers of higher tier ISPs connecting them to rest of Internet Tier 3 ISP Tier-2 ISP local ISP Tier-2 ISP Tier 1 ISP Tier-2 ISP local ISP Introduction 1 -98
Internet structure: network of networks q “Tier-3” ISPs and local ISPs v last hop (“access”) network (closest to end systems) local ISP Local and tier 3 ISPs are customers of higher tier ISPs connecting them to rest of Internet Tier 3 ISP Tier-2 ISP local ISP Tier-2 ISP Tier 1 ISP Tier-2 ISP local ISP Introduction 1 -98
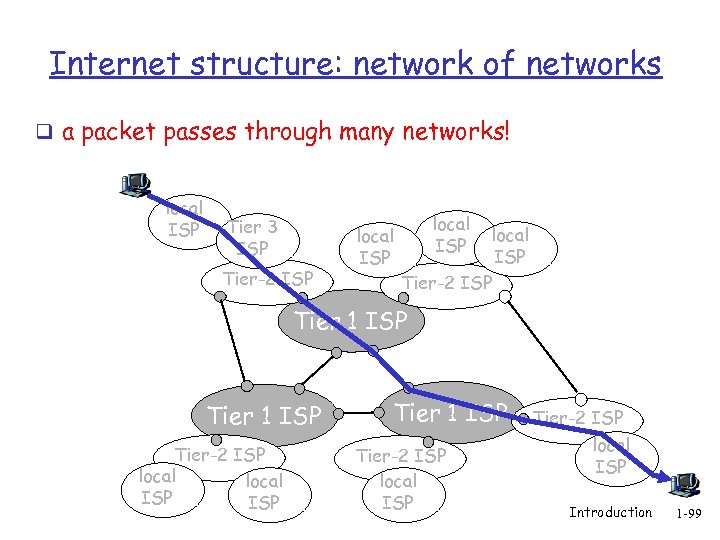 Internet structure: network of networks q a packet passes through many networks! local ISP Tier 3 ISP Tier-2 ISP local ISP Tier-2 ISP Tier 1 ISP Tier-2 ISP local ISP Introduction 1 -99
Internet structure: network of networks q a packet passes through many networks! local ISP Tier 3 ISP Tier-2 ISP local ISP Tier-2 ISP Tier 1 ISP Tier-2 ISP local ISP Introduction 1 -99
 Chapter 1: roadmap 1. 1 What is the Internet? 1. 2 Network edge q end systems, access networks, links 1. 3 Network core q circuit switching, packet switching, network structure 1. 4 Delay, loss and throughput in packet-switched networks 1. 5 Protocol layers, service models 1. 6 Networks under attack: security 1. 7 History Introduction 1 -122
Chapter 1: roadmap 1. 1 What is the Internet? 1. 2 Network edge q end systems, access networks, links 1. 3 Network core q circuit switching, packet switching, network structure 1. 4 Delay, loss and throughput in packet-switched networks 1. 5 Protocol layers, service models 1. 6 Networks under attack: security 1. 7 History Introduction 1 -122
 Network Security q The field of network security is about: how bad guys can attack computer networks v how we can defend networks against attacks v how to design architectures that are immune to attacks v q Internet not originally designed with (much) security in mind original vision: “a group of mutually trusting users attached to a transparent network” v Internet protocol designers playing “catch-up” v Security considerations in all layers! v Introduction 1 -123
Network Security q The field of network security is about: how bad guys can attack computer networks v how we can defend networks against attacks v how to design architectures that are immune to attacks v q Internet not originally designed with (much) security in mind original vision: “a group of mutually trusting users attached to a transparent network” v Internet protocol designers playing “catch-up” v Security considerations in all layers! v Introduction 1 -123
 Bad guys can put malware into hosts via Internet q Malware can get in host from a virus, worm, or trojan horse. q Spyware malware can record keystrokes, web sites visited, upload info to collection site. q Infected host can be enrolled in a botnet, used for spam and DDo. S attacks. q Malware is often self-replicating: from an infected host, seeks entry into other hosts Introduction 1 -124
Bad guys can put malware into hosts via Internet q Malware can get in host from a virus, worm, or trojan horse. q Spyware malware can record keystrokes, web sites visited, upload info to collection site. q Infected host can be enrolled in a botnet, used for spam and DDo. S attacks. q Malware is often self-replicating: from an infected host, seeks entry into other hosts Introduction 1 -124
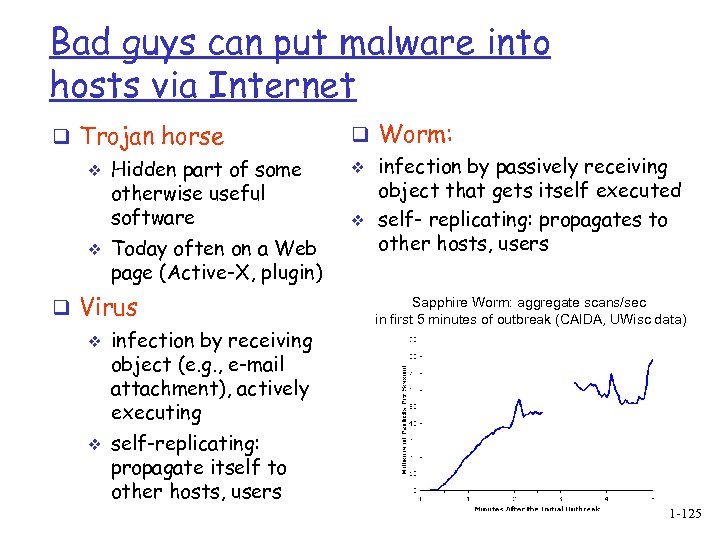 Bad guys can put malware into hosts via Internet q Trojan horse v v Hidden part of some otherwise useful software Today often on a Web page (Active-X, plugin) q Virus v v infection by receiving object (e. g. , e-mail attachment), actively executing self-replicating: propagate itself to other hosts, users q Worm: v infection by passively receiving object that gets itself executed v self- replicating: propagates to other hosts, users Sapphire Worm: aggregate scans/sec in first 5 minutes of outbreak (CAIDA, UWisc data) Introduction 1 -125
Bad guys can put malware into hosts via Internet q Trojan horse v v Hidden part of some otherwise useful software Today often on a Web page (Active-X, plugin) q Virus v v infection by receiving object (e. g. , e-mail attachment), actively executing self-replicating: propagate itself to other hosts, users q Worm: v infection by passively receiving object that gets itself executed v self- replicating: propagates to other hosts, users Sapphire Worm: aggregate scans/sec in first 5 minutes of outbreak (CAIDA, UWisc data) Introduction 1 -125
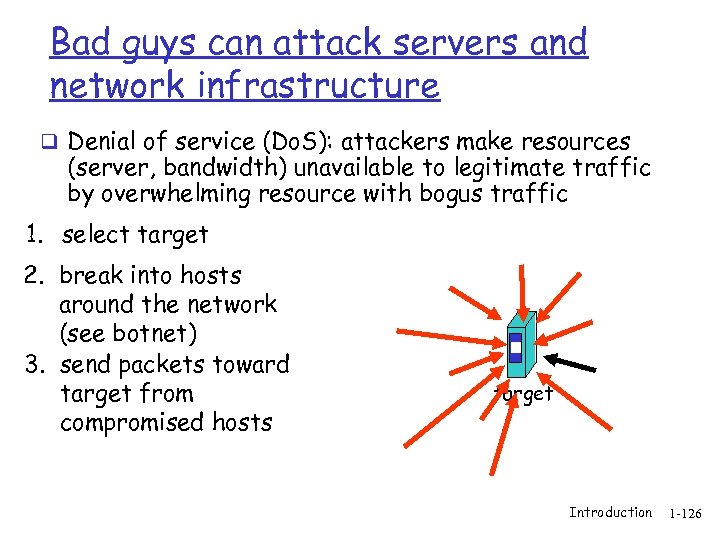 Bad guys can attack servers and network infrastructure q Denial of service (Do. S): attackers make resources (server, bandwidth) unavailable to legitimate traffic by overwhelming resource with bogus traffic 1. select target 2. break into hosts around the network (see botnet) 3. send packets toward target from compromised hosts target Introduction 1 -126
Bad guys can attack servers and network infrastructure q Denial of service (Do. S): attackers make resources (server, bandwidth) unavailable to legitimate traffic by overwhelming resource with bogus traffic 1. select target 2. break into hosts around the network (see botnet) 3. send packets toward target from compromised hosts target Introduction 1 -126
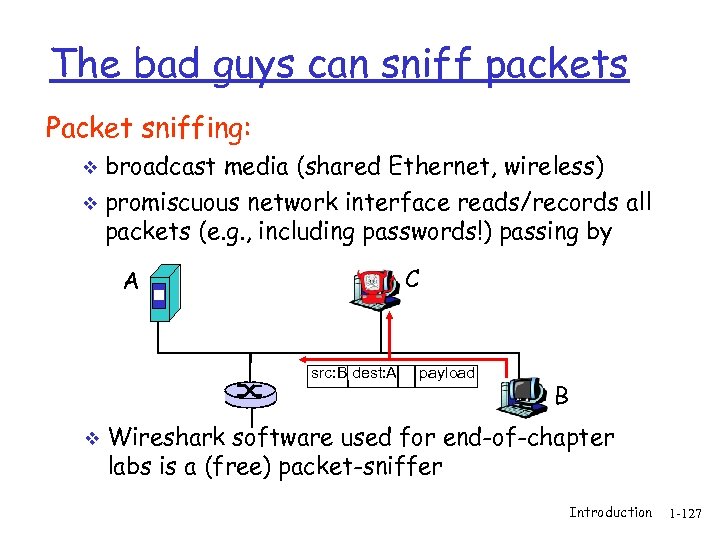 The bad guys can sniff packets Packet sniffing: broadcast media (shared Ethernet, wireless) v promiscuous network interface reads/records all packets (e. g. , including passwords!) passing by v C A src: B dest: A v payload B Wireshark software used for end-of-chapter labs is a (free) packet-sniffer Introduction 1 -127
The bad guys can sniff packets Packet sniffing: broadcast media (shared Ethernet, wireless) v promiscuous network interface reads/records all packets (e. g. , including passwords!) passing by v C A src: B dest: A v payload B Wireshark software used for end-of-chapter labs is a (free) packet-sniffer Introduction 1 -127
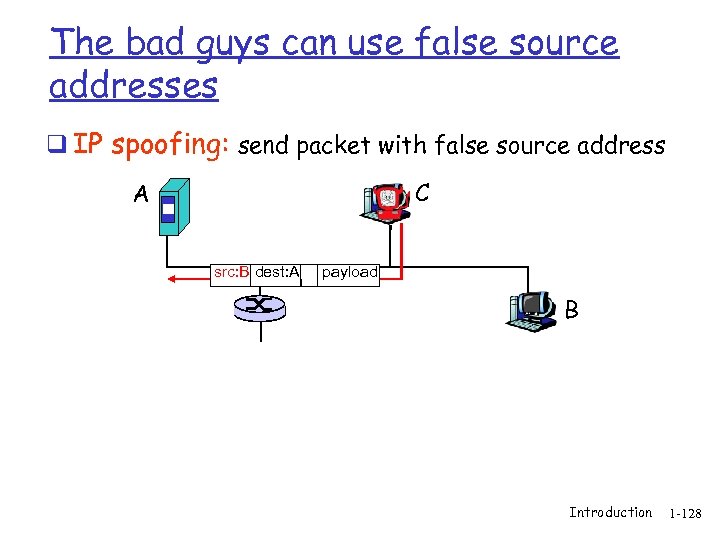 The bad guys can use false source addresses q IP spoofing: send packet with false source address C A src: B dest: A payload B Introduction 1 -128
The bad guys can use false source addresses q IP spoofing: send packet with false source address C A src: B dest: A payload B Introduction 1 -128
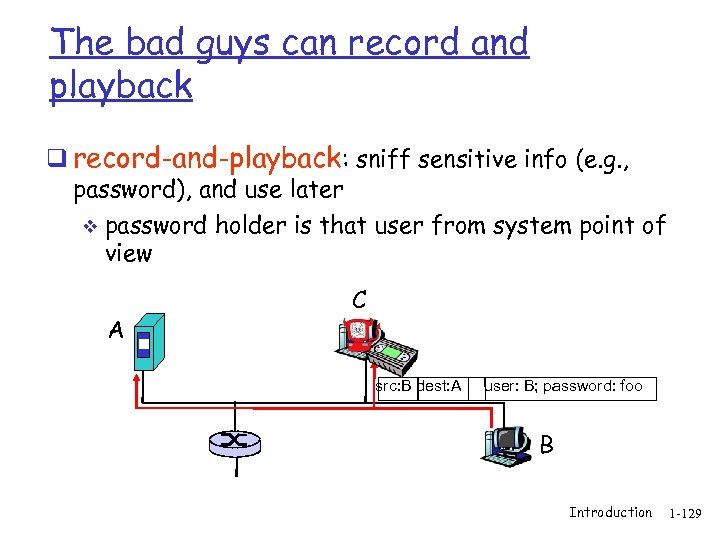 The bad guys can record and playback q record-and-playback: sniff sensitive info (e. g. , password), and use later v password holder is that user from system point of view A C src: B dest: A user: B; password: foo B Introduction 1 -129
The bad guys can record and playback q record-and-playback: sniff sensitive info (e. g. , password), and use later v password holder is that user from system point of view A C src: B dest: A user: B; password: foo B Introduction 1 -129
 Network Security q more throughout this course q chapter 8: focus on security q crypographic techniques: obvious uses and not so obvious uses Introduction 1 -130
Network Security q more throughout this course q chapter 8: focus on security q crypographic techniques: obvious uses and not so obvious uses Introduction 1 -130
 Chapter 1: roadmap 1. 1 What is the Internet? 1. 2 Network edge q end systems, access networks, links 1. 3 Network core q circuit switching, packet switching, network structure 1. 4 Delay, loss and throughput in packet-switched networks 1. 5 Protocol layers, service models 1. 6 Networks under attack: security 1. 7 History Introduction 1 -131
Chapter 1: roadmap 1. 1 What is the Internet? 1. 2 Network edge q end systems, access networks, links 1. 3 Network core q circuit switching, packet switching, network structure 1. 4 Delay, loss and throughput in packet-switched networks 1. 5 Protocol layers, service models 1. 6 Networks under attack: security 1. 7 History Introduction 1 -131
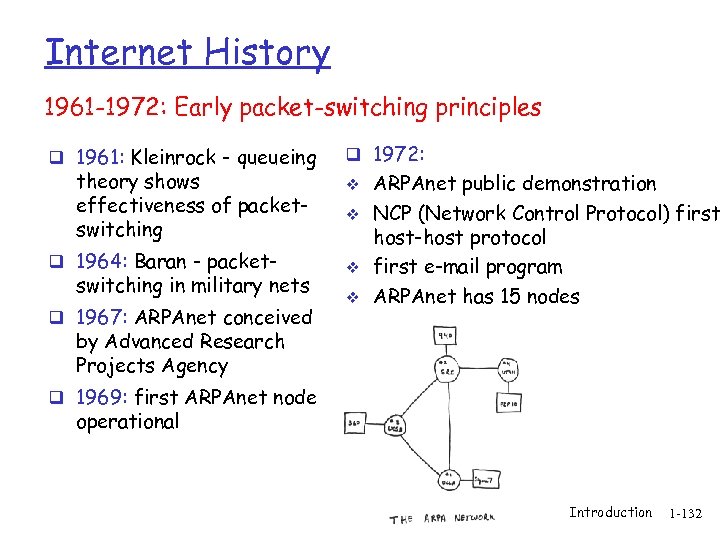 Internet History 1961 -1972: Early packet-switching principles q 1961: Kleinrock - queueing theory shows effectiveness of packetswitching q 1964: Baran - packet- switching in military nets q 1967: ARPAnet conceived q 1972: v v ARPAnet public demonstration NCP (Network Control Protocol) first host-host protocol first e-mail program ARPAnet has 15 nodes by Advanced Research Projects Agency q 1969: first ARPAnet node operational Introduction 1 -132
Internet History 1961 -1972: Early packet-switching principles q 1961: Kleinrock - queueing theory shows effectiveness of packetswitching q 1964: Baran - packet- switching in military nets q 1967: ARPAnet conceived q 1972: v v ARPAnet public demonstration NCP (Network Control Protocol) first host-host protocol first e-mail program ARPAnet has 15 nodes by Advanced Research Projects Agency q 1969: first ARPAnet node operational Introduction 1 -132
 Internet History 1972 -1980: Internetworking, new and proprietary nets q 1970: ALOHAnet satellite q q q network in Hawaii 1974: Cerf and Kahn architecture for interconnecting networks 1976: Ethernet at Xerox PARC ate 70’s: proprietary architectures: DECnet, SNA, XNA late 70’s: switching fixed length packets (ATM precursor) 1979: ARPAnet has 200 nodes Cerf and Kahn’s internetworking principles: v minimalism, autonomy - no internal changes required to interconnect networks v best effort service model v stateless routers v decentralized control define today’s Internet architecture Introduction 1 -133
Internet History 1972 -1980: Internetworking, new and proprietary nets q 1970: ALOHAnet satellite q q q network in Hawaii 1974: Cerf and Kahn architecture for interconnecting networks 1976: Ethernet at Xerox PARC ate 70’s: proprietary architectures: DECnet, SNA, XNA late 70’s: switching fixed length packets (ATM precursor) 1979: ARPAnet has 200 nodes Cerf and Kahn’s internetworking principles: v minimalism, autonomy - no internal changes required to interconnect networks v best effort service model v stateless routers v decentralized control define today’s Internet architecture Introduction 1 -133
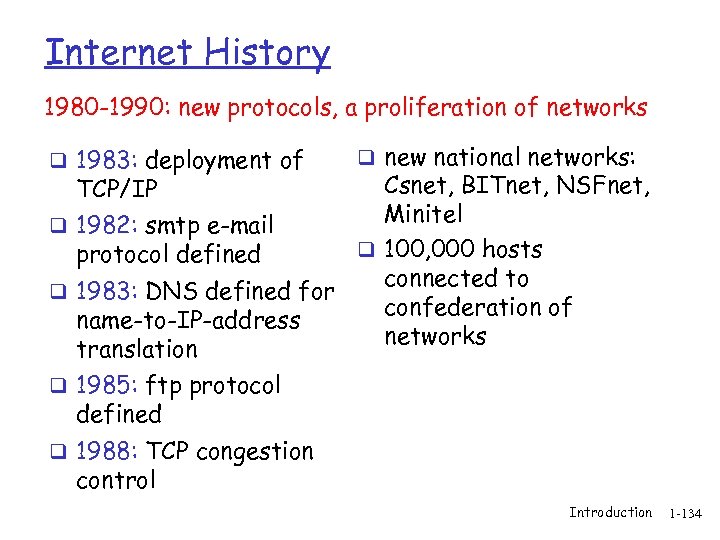 Internet History 1980 -1990: new protocols, a proliferation of networks q 1983: deployment of q new national networks: Csnet, BITnet, NSFnet, Minitel q 1982: smtp e-mail q 100, 000 hosts protocol defined connected to q 1983: DNS defined for confederation of name-to-IP-address networks translation TCP/IP q 1985: ftp protocol defined q 1988: TCP congestion control Introduction 1 -134
Internet History 1980 -1990: new protocols, a proliferation of networks q 1983: deployment of q new national networks: Csnet, BITnet, NSFnet, Minitel q 1982: smtp e-mail q 100, 000 hosts protocol defined connected to q 1983: DNS defined for confederation of name-to-IP-address networks translation TCP/IP q 1985: ftp protocol defined q 1988: TCP congestion control Introduction 1 -134
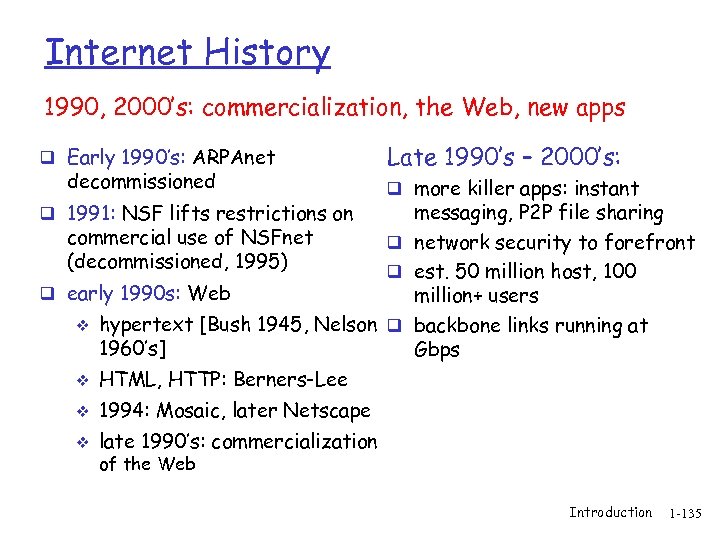 Internet History 1990, 2000’s: commercialization, the Web, new apps q Early 1990’s: ARPAnet decommissioned Late 1990’s – 2000’s: q more killer apps: instant messaging, P 2 P file sharing commercial use of NSFnet q network security to forefront (decommissioned, 1995) q est. 50 million host, 100 q early 1990 s: Web million+ users v hypertext [Bush 1945, Nelson q backbone links running at 1960’s] Gbps q 1991: NSF lifts restrictions on v HTML, HTTP: Berners-Lee v 1994: Mosaic, later Netscape v late 1990’s: commercialization of the Web Introduction 1 -135
Internet History 1990, 2000’s: commercialization, the Web, new apps q Early 1990’s: ARPAnet decommissioned Late 1990’s – 2000’s: q more killer apps: instant messaging, P 2 P file sharing commercial use of NSFnet q network security to forefront (decommissioned, 1995) q est. 50 million host, 100 q early 1990 s: Web million+ users v hypertext [Bush 1945, Nelson q backbone links running at 1960’s] Gbps q 1991: NSF lifts restrictions on v HTML, HTTP: Berners-Lee v 1994: Mosaic, later Netscape v late 1990’s: commercialization of the Web Introduction 1 -135
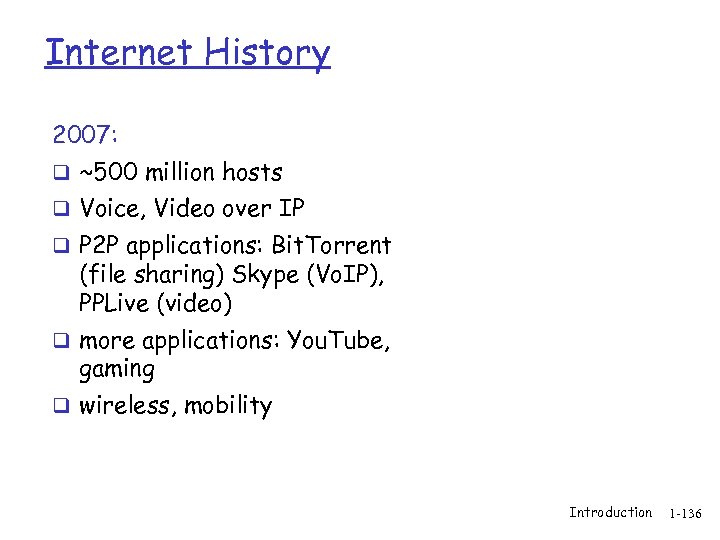 Internet History 2007: q ~500 million hosts q Voice, Video over IP q P 2 P applications: Bit. Torrent (file sharing) Skype (Vo. IP), PPLive (video) q more applications: You. Tube, gaming q wireless, mobility Introduction 1 -136
Internet History 2007: q ~500 million hosts q Voice, Video over IP q P 2 P applications: Bit. Torrent (file sharing) Skype (Vo. IP), PPLive (video) q more applications: You. Tube, gaming q wireless, mobility Introduction 1 -136
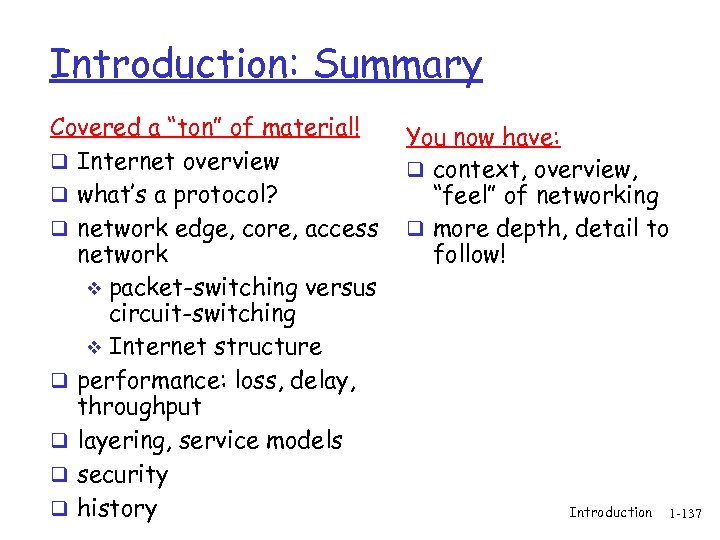 Introduction: Summary Covered a “ton” of material! q Internet overview q what’s a protocol? q network edge, core, access network v packet-switching versus circuit-switching v Internet structure q performance: loss, delay, throughput q layering, service models q security q history You now have: q context, overview, “feel” of networking q more depth, detail to follow! Introduction 1 -137
Introduction: Summary Covered a “ton” of material! q Internet overview q what’s a protocol? q network edge, core, access network v packet-switching versus circuit-switching v Internet structure q performance: loss, delay, throughput q layering, service models q security q history You now have: q context, overview, “feel” of networking q more depth, detail to follow! Introduction 1 -137


