1609f71649351262ad1cd697efa5cee4.ppt
- Количество слайдов: 21
 Center of Excellence Wireless and Information Technology Keys To Secure Your Wireless Enterprise Toby Weiss SVP, e. Trust Computer Associates International CEWIT 2003
Center of Excellence Wireless and Information Technology Keys To Secure Your Wireless Enterprise Toby Weiss SVP, e. Trust Computer Associates International CEWIT 2003
 Center of Excellence Wireless and Information Technology Agenda • Overview of Wireless Networks • Security Issues • Keys to a Secure Wireless Environment CEWIT 2003 2
Center of Excellence Wireless and Information Technology Agenda • Overview of Wireless Networks • Security Issues • Keys to a Secure Wireless Environment CEWIT 2003 2
 Center of Excellence Wireless and Information Technology Wireless Networks Today • WPAN (Wireless Personal Area Network) – Bluetooth • WLAN (Wireless Local Area Network) – 802. 11 b, 802. 11 a, g, i, … • WWAN (Wireless Wide Area Network) – Through wireless operators using GPRS, CDMA, etc. CEWIT 2003 3
Center of Excellence Wireless and Information Technology Wireless Networks Today • WPAN (Wireless Personal Area Network) – Bluetooth • WLAN (Wireless Local Area Network) – 802. 11 b, 802. 11 a, g, i, … • WWAN (Wireless Wide Area Network) – Through wireless operators using GPRS, CDMA, etc. CEWIT 2003 3
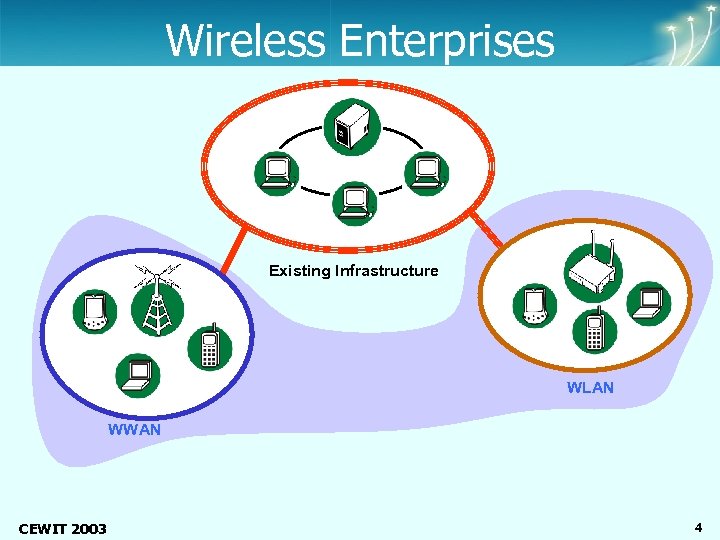 Center of Excellence Wireless and Information Technology Wireless Enterprises Existing Infrastructure WLAN WWAN CEWIT 2003 4
Center of Excellence Wireless and Information Technology Wireless Enterprises Existing Infrastructure WLAN WWAN CEWIT 2003 4
 Center of Excellence Wireless and Information Technology Wireless LANs • Wireless ethernet • Wireless access point (AP) connected to a desktop or server or an existing network • Mobile devices with compatible network cards are required CEWIT 2003 5
Center of Excellence Wireless and Information Technology Wireless LANs • Wireless ethernet • Wireless access point (AP) connected to a desktop or server or an existing network • Mobile devices with compatible network cards are required CEWIT 2003 5
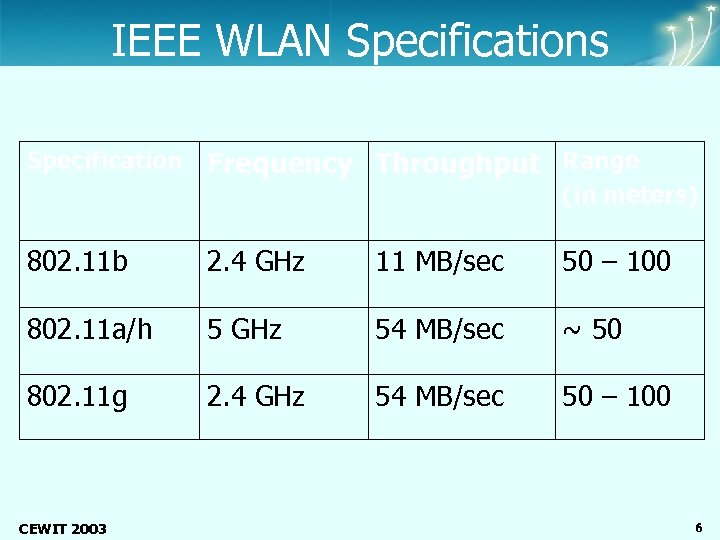 Center of Excellence Wireless and Information Technology IEEE WLAN Specifications Specification Frequency Throughput Range (in meters) 802. 11 b 2. 4 GHz 11 MB/sec 50 – 100 802. 11 a/h 5 GHz 54 MB/sec ~ 50 802. 11 g 2. 4 GHz 54 MB/sec 50 – 100 CEWIT 2003 6
Center of Excellence Wireless and Information Technology IEEE WLAN Specifications Specification Frequency Throughput Range (in meters) 802. 11 b 2. 4 GHz 11 MB/sec 50 – 100 802. 11 a/h 5 GHz 54 MB/sec ~ 50 802. 11 g 2. 4 GHz 54 MB/sec 50 – 100 CEWIT 2003 6
 Center of Excellence Wireless and Information Technology Hotspots • Public Access WLANs • The ones you find at airports, hotels, and other public places • On the rise, but still many issues to deal with – Billing – Roaming – Security CEWIT 2003 7
Center of Excellence Wireless and Information Technology Hotspots • Public Access WLANs • The ones you find at airports, hotels, and other public places • On the rise, but still many issues to deal with – Billing – Roaming – Security CEWIT 2003 7
 Center of Excellence Wireless and Information Technology WWANs • Service offered by wireless operators like Vodafone, NTT Do. Co. Mo, Verizon Wireless, Cingular and others • Data transfer over cellular networks • Cover global geography • Use technologies like GPRS, CDMA, and others CEWIT 2003 8
Center of Excellence Wireless and Information Technology WWANs • Service offered by wireless operators like Vodafone, NTT Do. Co. Mo, Verizon Wireless, Cingular and others • Data transfer over cellular networks • Cover global geography • Use technologies like GPRS, CDMA, and others CEWIT 2003 8
 Center of Excellence Wireless and Information Technology What’s Available Today • Most infrastructure is either 2 G or 2. 5 G, not quite 3 G yet • 3 G promises throughputs of: – ~384 Kbps for semi-stationary devices – ~128 Kbps when in a car – ~ 2 Mbps in fixed applications CEWIT 2003 9
Center of Excellence Wireless and Information Technology What’s Available Today • Most infrastructure is either 2 G or 2. 5 G, not quite 3 G yet • 3 G promises throughputs of: – ~384 Kbps for semi-stationary devices – ~128 Kbps when in a car – ~ 2 Mbps in fixed applications CEWIT 2003 9
 Center of Excellence Wireless and Information Technology The #1 Barrier • Security is the #1 issue for enterprises deploying wireless environments CEWIT 2003 10
Center of Excellence Wireless and Information Technology The #1 Barrier • Security is the #1 issue for enterprises deploying wireless environments CEWIT 2003 10
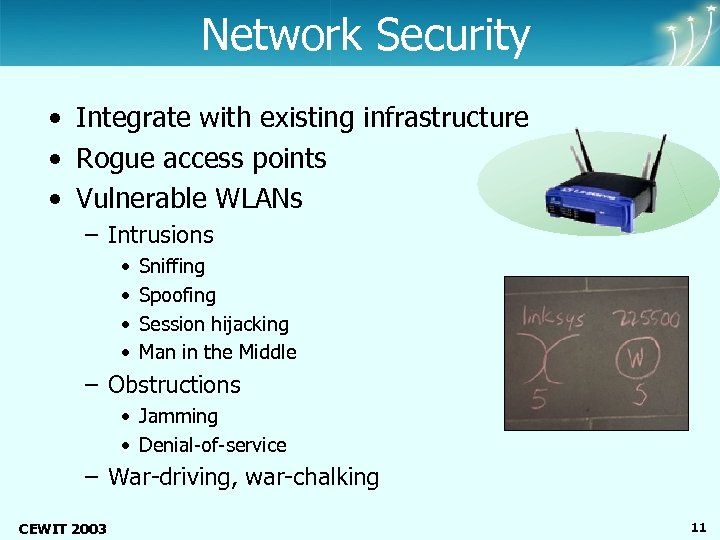 Center of Excellence Wireless and Information Technology Network Security • Integrate with existing infrastructure • Rogue access points • Vulnerable WLANs – Intrusions • • Sniffing Spoofing Session hijacking Man in the Middle – Obstructions • Jamming • Denial-of-service – War-driving, war-chalking CEWIT 2003 11
Center of Excellence Wireless and Information Technology Network Security • Integrate with existing infrastructure • Rogue access points • Vulnerable WLANs – Intrusions • • Sniffing Spoofing Session hijacking Man in the Middle – Obstructions • Jamming • Denial-of-service – War-driving, war-chalking CEWIT 2003 11
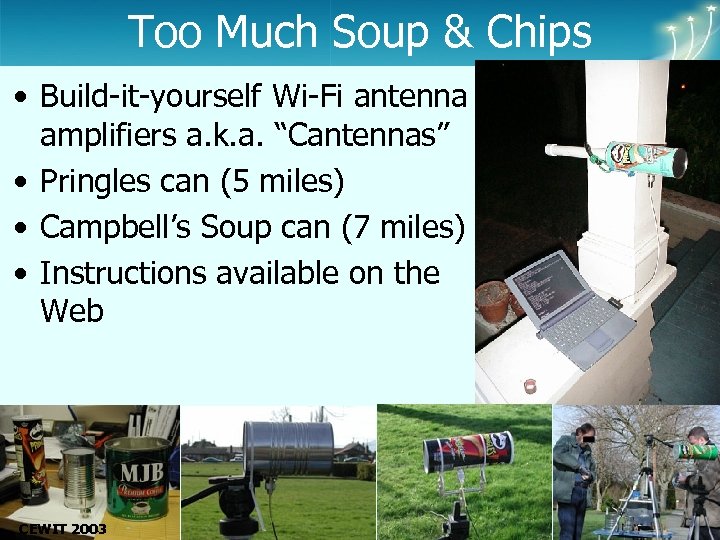 Too Much Soup & Chips Center of Excellence Wireless and Information Technology • Build-it-yourself Wi-Fi antenna amplifiers a. k. a. “Cantennas” • Pringles can (5 miles) • Campbell’s Soup can (7 miles) • Instructions available on the Web CEWIT 2003 12
Too Much Soup & Chips Center of Excellence Wireless and Information Technology • Build-it-yourself Wi-Fi antenna amplifiers a. k. a. “Cantennas” • Pringles can (5 miles) • Campbell’s Soup can (7 miles) • Instructions available on the Web CEWIT 2003 12
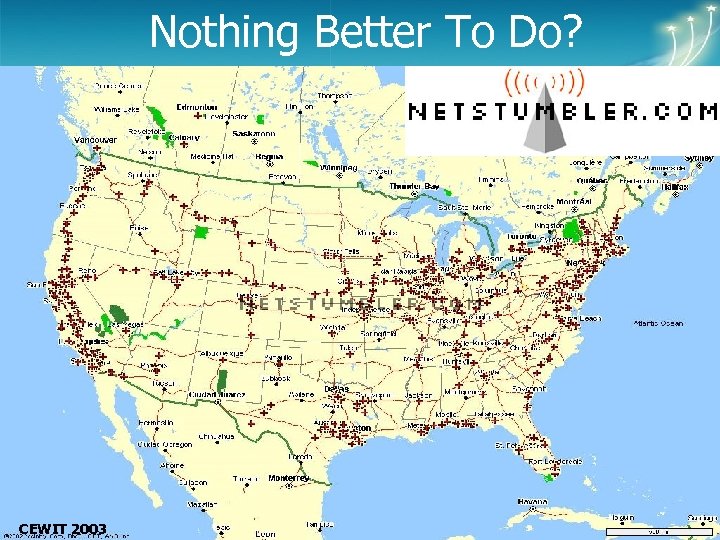 Nothing Better To Do? Center of Excellence Wireless and Information Technology CEWIT 2003 13
Nothing Better To Do? Center of Excellence Wireless and Information Technology CEWIT 2003 13
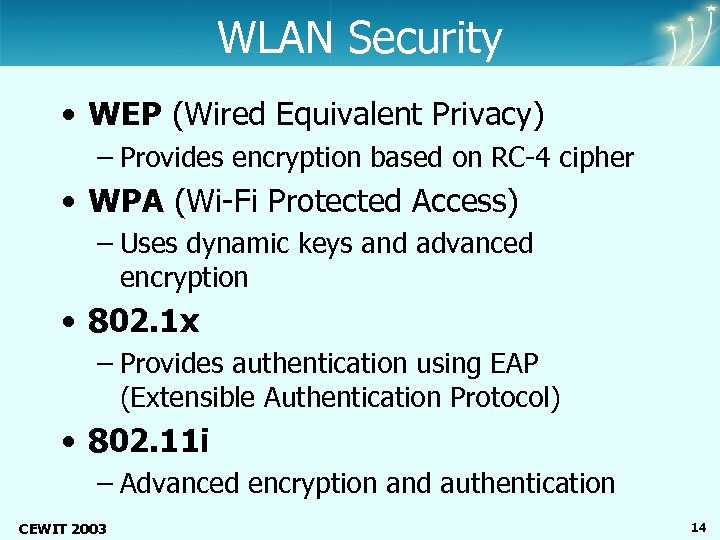 Center of Excellence Wireless and Information Technology WLAN Security • WEP (Wired Equivalent Privacy) – Provides encryption based on RC-4 cipher • WPA (Wi-Fi Protected Access) – Uses dynamic keys and advanced encryption • 802. 1 x – Provides authentication using EAP (Extensible Authentication Protocol) • 802. 11 i – Advanced encryption and authentication CEWIT 2003 14
Center of Excellence Wireless and Information Technology WLAN Security • WEP (Wired Equivalent Privacy) – Provides encryption based on RC-4 cipher • WPA (Wi-Fi Protected Access) – Uses dynamic keys and advanced encryption • 802. 1 x – Provides authentication using EAP (Extensible Authentication Protocol) • 802. 11 i – Advanced encryption and authentication CEWIT 2003 14
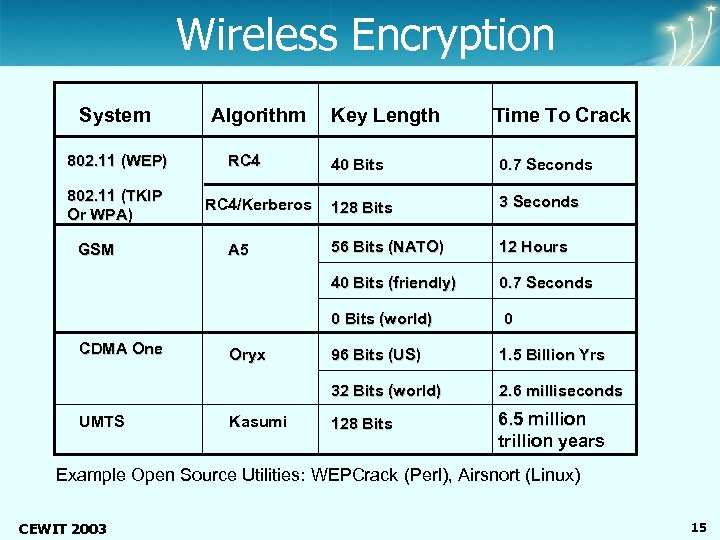 Center of Excellence Wireless and Information Technology Wireless Encryption System 802. 11 (WEP) Algorithm RC 4 Key Length Time To Crack UMTS Oryx Kasumi 3 Seconds 56 Bits (NATO) 12 Hours 0. 7 Seconds 0 96 Bits (US) 1. 5 Billion Yrs 32 Bits (world) CDMA One A 5 128 Bits 0 Bits (world) GSM RC 4/Kerberos 0. 7 Seconds 40 Bits (friendly) 802. 11 (TKIP Or WPA) 40 Bits 2. 6 milliseconds 128 Bits 6. 5 million trillion years Example Open Source Utilities: WEPCrack (Perl), Airsnort (Linux) CEWIT 2003 15
Center of Excellence Wireless and Information Technology Wireless Encryption System 802. 11 (WEP) Algorithm RC 4 Key Length Time To Crack UMTS Oryx Kasumi 3 Seconds 56 Bits (NATO) 12 Hours 0. 7 Seconds 0 96 Bits (US) 1. 5 Billion Yrs 32 Bits (world) CDMA One A 5 128 Bits 0 Bits (world) GSM RC 4/Kerberos 0. 7 Seconds 40 Bits (friendly) 802. 11 (TKIP Or WPA) 40 Bits 2. 6 milliseconds 128 Bits 6. 5 million trillion years Example Open Source Utilities: WEPCrack (Perl), Airsnort (Linux) CEWIT 2003 15
 Center of Excellence Wireless and Information Technology Device Security • Protection of mobile information • Configuration control • Virus attacks • Recovering from the effects of lost and stolen devices CEWIT 2003 16
Center of Excellence Wireless and Information Technology Device Security • Protection of mobile information • Configuration control • Virus attacks • Recovering from the effects of lost and stolen devices CEWIT 2003 16
 Center of Excellence Wireless and Information Technology User Security • Integrate mobile users into existing security policies • Context-based access control • Identity management • Authentication • Provisioning • Location-based security CEWIT 2003 17
Center of Excellence Wireless and Information Technology User Security • Integrate mobile users into existing security policies • Context-based access control • Identity management • Authentication • Provisioning • Location-based security CEWIT 2003 17
 Center of Excellence Wireless and Information Technology Security Best Practices • Get your wired security in order first • Take an enterprise-wide perspective • Define clear goals and security policies for your wireless environment – Networks – Devices – Users • Identify and audit the wireless users • Research the technology thoroughly and choose what best meets your business objectives • Partner with trusted business and technology advisors CEWIT 2003 18
Center of Excellence Wireless and Information Technology Security Best Practices • Get your wired security in order first • Take an enterprise-wide perspective • Define clear goals and security policies for your wireless environment – Networks – Devices – Users • Identify and audit the wireless users • Research the technology thoroughly and choose what best meets your business objectives • Partner with trusted business and technology advisors CEWIT 2003 18
 Center of Excellence Wireless and Information Technology Basic WLAN security • • Use WEP or AES for encryption Maintain an updated MAC list Do not broadcast the SSID If you can, don’t use DHCP for wireless devices • Use WPA so that the keys are dynamically rotated • Use 802. 1 x to authenticate your users • Require WLAN users to log in through VPN CEWIT 2003 19
Center of Excellence Wireless and Information Technology Basic WLAN security • • Use WEP or AES for encryption Maintain an updated MAC list Do not broadcast the SSID If you can, don’t use DHCP for wireless devices • Use WPA so that the keys are dynamically rotated • Use 802. 1 x to authenticate your users • Require WLAN users to log in through VPN CEWIT 2003 19
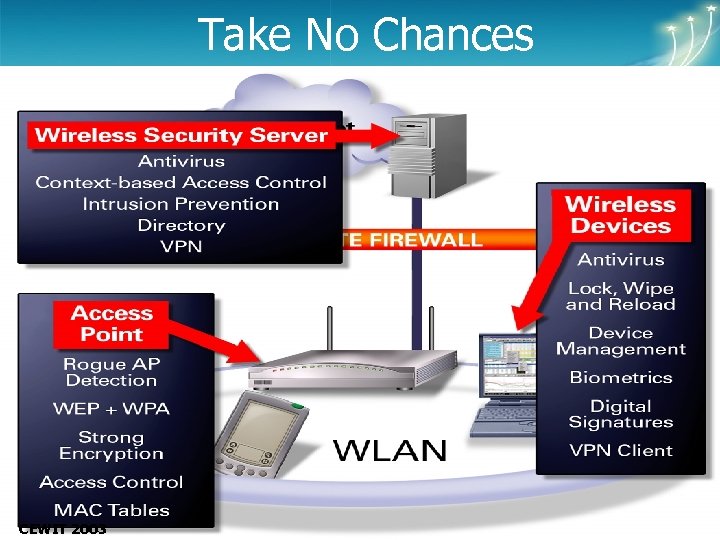 Center of Excellence Wireless and Information Technology Take No Chances CEWIT 2003 20
Center of Excellence Wireless and Information Technology Take No Chances CEWIT 2003 20
 Center of Excellence Wireless and Information Technology Keys To Secure Your Wireless Enterprise Toby Weiss SVP, e. Trust Computer Associates International CEWIT 2003
Center of Excellence Wireless and Information Technology Keys To Secure Your Wireless Enterprise Toby Weiss SVP, e. Trust Computer Associates International CEWIT 2003


