f9d28def6d6a710ee47987f3ff00ae86.ppt
- Количество слайдов: 55
Campus Wireless Introduction 資訊網路中心 朱朝昑 E-mail : alex@mail. ltc. edu. tw TEL : 04 -23895624 ext 230 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 1
嶺東技術學院無線網路介紹 無線區域網路通訊協定 無線網路認證機制 本校無線網路介紹 無線網卡安裝設定 client manager 安裝介紹 Q&A 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 2
無線區域網路通訊協定 Wireless Local Area Network (IEEE 802. 11) 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. Wireless LAN Topologies-3 3
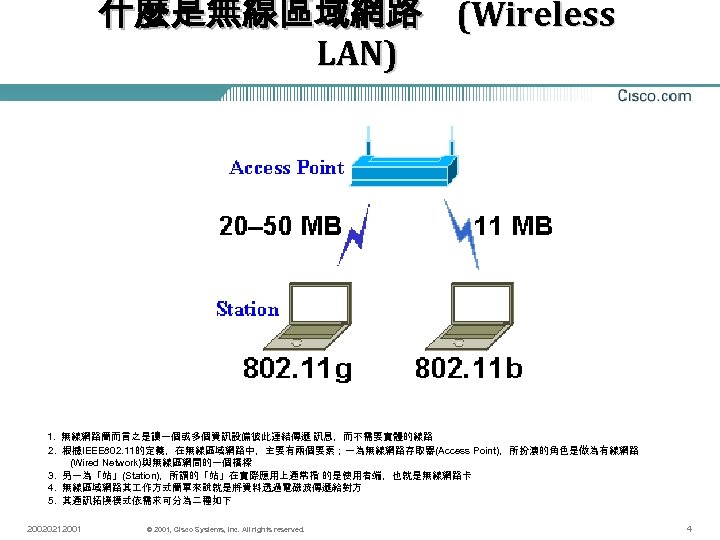
什麼是無線區域網路 (Wireless LAN) 1. 無線網路簡而言之是讓一個或多個資訊設備彼此連結傳遞 訊息,而不需要實體的線路 2. 根據IEEE 802. 11的定義,在無線區域網路中,主要有兩個要素;一為無線網路存取器(Access Point),所扮演的角色是做為有線網路 (Wired Network)與無線區網間的一個橋樑 3. 另一為「站」(Station),所謂的「站」在實際應用上通常指 的是使用者端,也就是無線網路卡 4. 無線區域網路其 作方式簡單來說就是將資料透過電磁波傳遞給對方 5. 其通訊拓撲模式依需求可分為二種如下 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 4
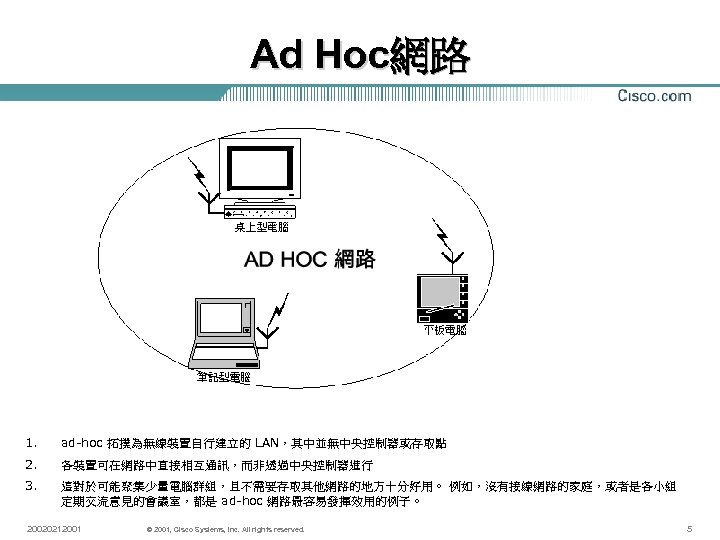
Ad Hoc網路 1. ad-hoc 拓撲為無線裝置自行建立的 LAN,其中並無中央控制器或存取點 2. 各裝置可在網路中直接相互通訊,而非透過中央控制器進行 3. 這對於可能聚集少量電腦群組,且不需要存取其他網路的地方十分好用。 例如,沒有接線網路的家庭,或者是各小組 定期交流意見的會議室,都是 ad-hoc 網路最容易發揮效用的例子。 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 5
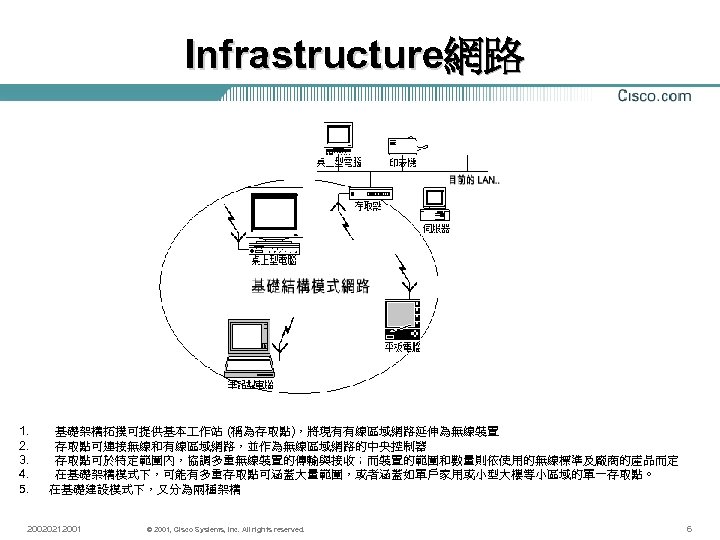
Infrastructure網路 1. 基礎架構拓撲可提供基本 作站 (稱為存取點),將現有有線區域網路延伸為無線裝置 2. 存取點可連接無線和有線區域網路,並作為無線區域網路的中央控制器 3. 存取點可於特定範圍內,協調多重無線裝置的傳輸與接收;而裝置的範圍和數量則依使用的無線標準及廠商的產品而定 4. 在基礎架構模式下,可能有多重存取點可涵蓋大量範圍,或者涵蓋如單戶家用或小型大樓等小區域的單一存取點。 5. 在基礎建設模式下,又分為兩種架構 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 6
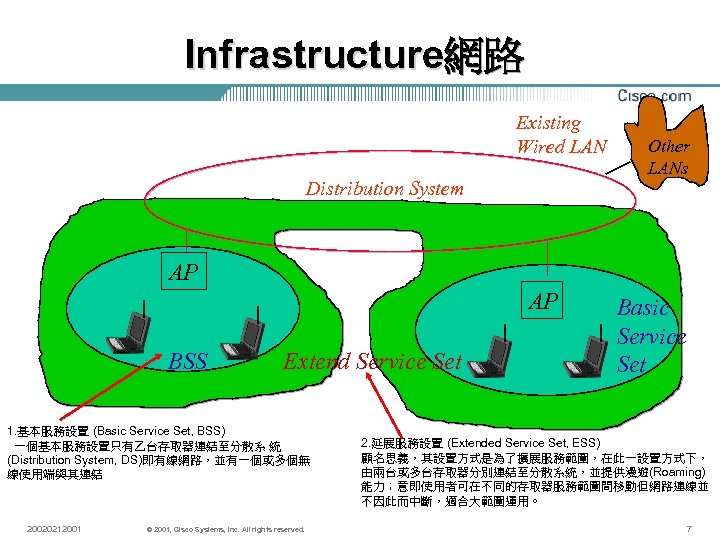
Infrastructure網路 Existing Wired LAN Distribution System Other LANs AP AP BSS Extend Service Set 1. 基本服務設置 (Basic Service Set, BSS) 一個基本服務設置只有乙台存取器連結至分散系 統 (Distribution System, DS)即有線網路,並有一個或多個無 線使用端與其連結 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. Basic Service Set 2. 延展服務設置 (Extended Service Set, ESS) 顧名思義,其設置方式是為了擴展服務範圍,在此一設置方式下, 由兩台或多台存取器分別連結至分散系統,並提供漫遊(Roaming) 能力;意即使用者可在不同的存取器服務範圍間移動但網路連線並 不因此而中斷,適合大範圍運用。 7
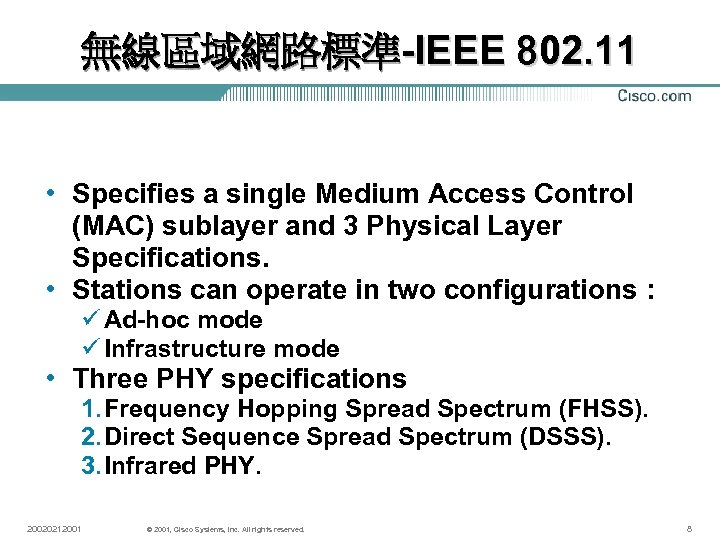
無線區域網路標準-IEEE 802. 11 • Specifies a single Medium Access Control (MAC) sublayer and 3 Physical Layer Specifications. • Stations can operate in two configurations : ü Ad-hoc mode ü Infrastructure mode • Three PHY specifications 1. Frequency Hopping Spread Spectrum (FHSS). 2. Direct Sequence Spread Spectrum (DSSS). 3. Infrared PHY. 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 8
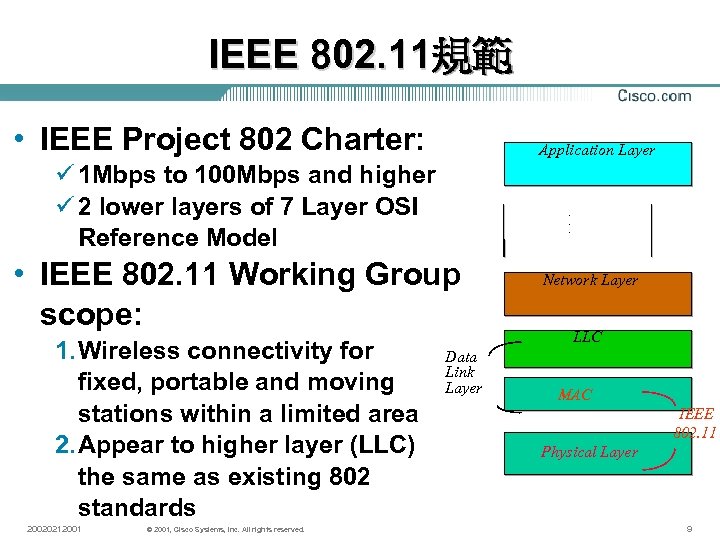
IEEE 802. 11規範 • IEEE Project 802 Charter: Application Layer ü 1 Mbps to 100 Mbps and higher ü 2 lower layers of 7 Layer OSI Reference Model . . . • IEEE 802. 11 Working Group scope: 1. Wireless connectivity for fixed, portable and moving stations within a limited area 2. Appear to higher layer (LLC) the same as existing 802 standards 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. Network Layer LLC Data Link Layer MAC IEEE 802. 11 Physical Layer 9
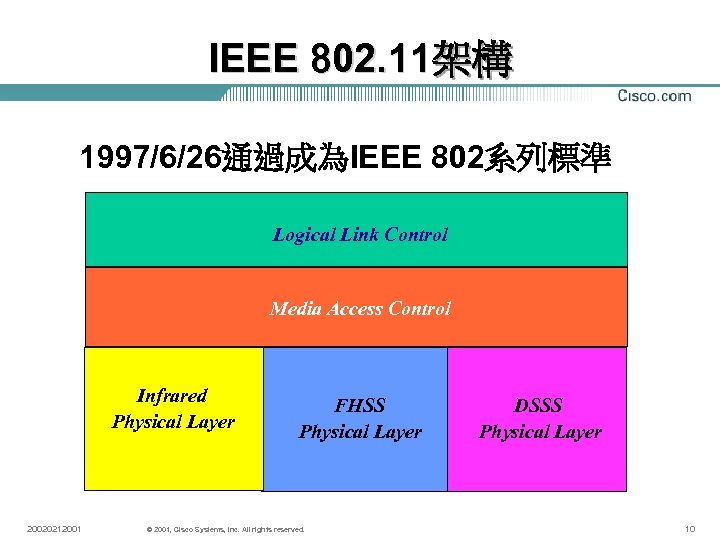
IEEE 802. 11架構 1997/6/26通過成為IEEE 802系列標準 Logical Link Control Media Access Control Infrared Physical Layer 20020212001 FHSS Physical Layer © 2001, Cisco Systems, Inc. All rights reserved. DSSS Physical Layer 10
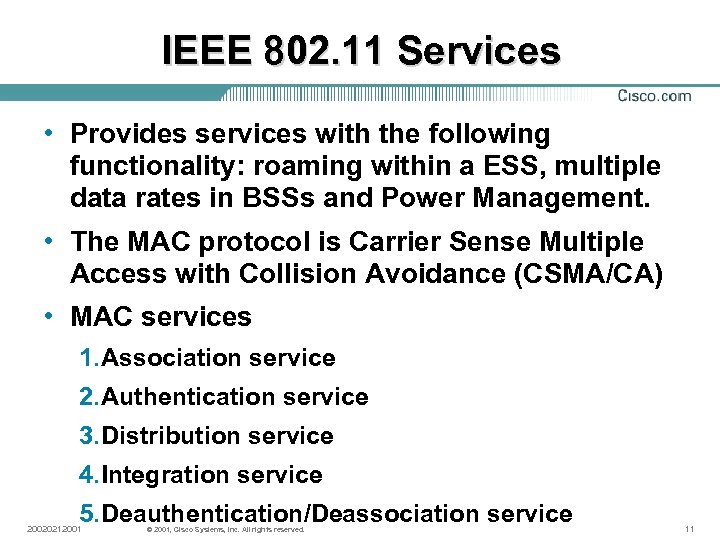
IEEE 802. 11 Services • Provides services with the following functionality: roaming within a ESS, multiple data rates in BSSs and Power Management. • The MAC protocol is Carrier Sense Multiple Access with Collision Avoidance (CSMA/CA) • MAC services 1. Association service 2. Authentication service 3. Distribution service 4. Integration service 5. Deauthentication/Deassociation service 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 11
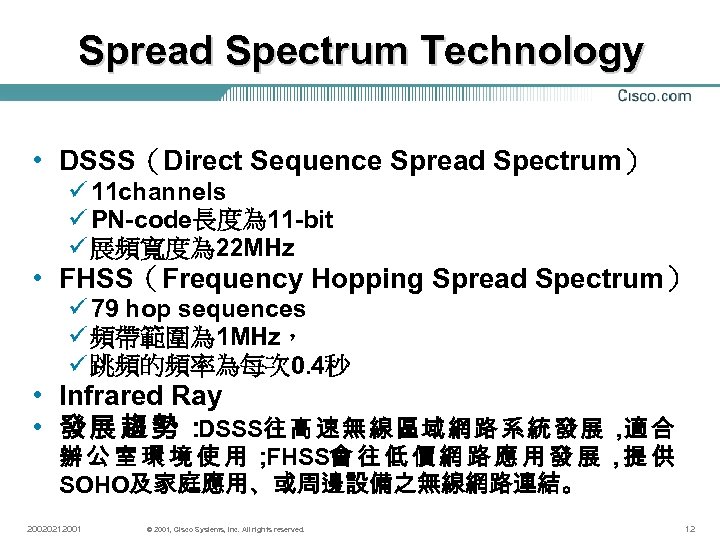
Spread Spectrum Technology • DSSS(Direct Sequence Spread Spectrum) ü 11 channels ü PN-code長度為 11 -bit ü 展頻寬度為 22 MHz • FHSS(Frequency Hopping Spread Spectrum) ü 79 hop sequences ü 頻帶範圍為 1 MHz, ü 跳頻的頻率為每次 0. 4秒 • Infrared Ray • 發展趨勢: DSSS往 高 速 無 線 區 域 網 路 系 統 發 展 , 合 適 辦公室環境使用; FHSS會 往 低 價 網 路 應 用 發 展 , 供 提 SOHO及家庭應用、或周邊設備之無線網路連結。 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 12
CSMA/CD (LAN) 1. Send data if the medium is sensed “idle” 2. If collides with other host(s), then backoff for a random number of times 3. Re-send data later 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 13
802. 11 Media Access Control Wireless LANs use the Carrier Sense Multiple Access (CSMA) algorithm with a Collision Avoidance (CA) mechanism • each unit senses the media before it starts to transmit. • If the media is free for several microseconds, the unit can transmit for a limited time. • If the media is busy, the unit will back off for a random time before it senses again. • Since transmitting units compete for air time, the protocol should ensure equal fairness between the stations. 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 資料來源: Dr. Edward Chow 14
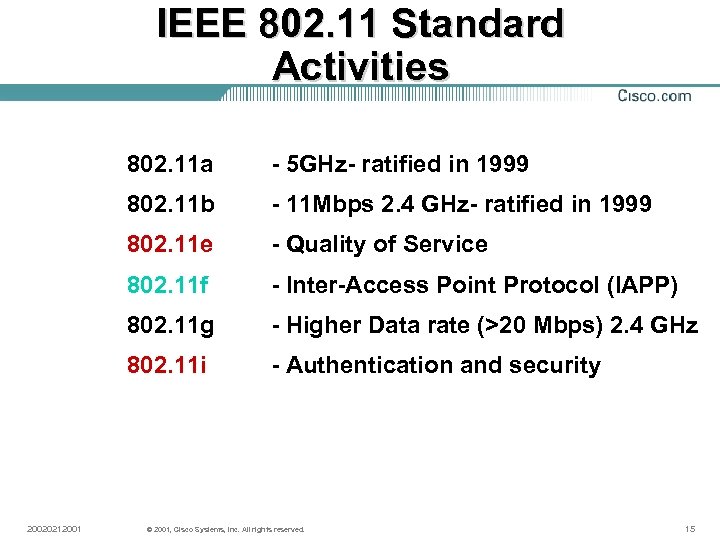
IEEE 802. 11 Standard Activities 802. 11 a 802. 11 b - 11 Mbps 2. 4 GHz- ratified in 1999 802. 11 e - Quality of Service 802. 11 f - Inter-Access Point Protocol (IAPP) 802. 11 g - Higher Data rate (>20 Mbps) 2. 4 GHz 802. 11 i 20020212001 - 5 GHz- ratified in 1999 - Authentication and security © 2001, Cisco Systems, Inc. All rights reserved. 15
802. 11 b 11 Mb 2. 4 GHz Direct Sequence Ratified as Standard in September, 1999. 11 Mb 2. 4 Gz 11 US channels 13 ETSI (European Telecommunications Standards Institute)channels 14 Japan Channels 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 16
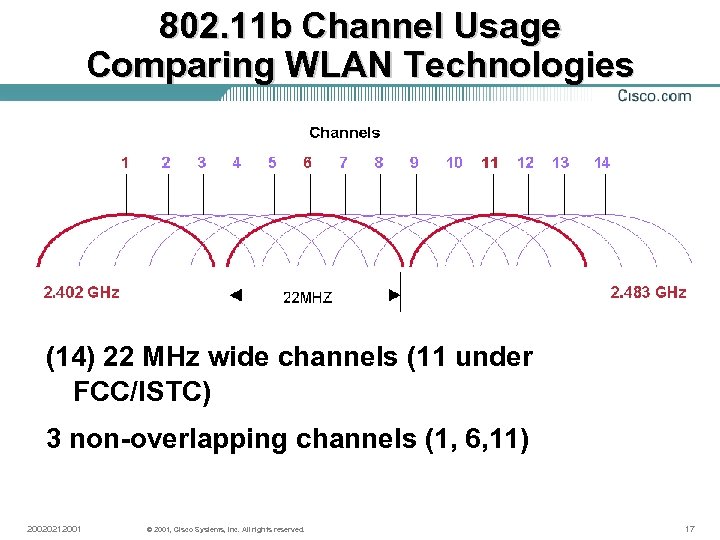
802. 11 b Channel Usage Comparing WLAN Technologies (14) 22 MHz wide channels (11 under FCC/ISTC) 3 non-overlapping channels (1, 6, 11) 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 17

2. 4 GHz 頻道設定 Regulatory Domain Channel Identifier Center Frequency 1 2412 MHz X X X 2 2417 MHz X X X 3 2422 MHz X X 4 2427 MHz X X 5 2432 MHz X X 6 2437 MHz X X 7 2442 MHz X X 8 2447 MHz X X 9 2452 MHz X X X 10 2457 MHz X X X 11 2462 MHz X X X 12 2467 MHz X X X 13 2472 MHz X X X 14 2484 MHz North America & ANZ ETSI Mexico France Japan Israel X 註:台灣跟隨北美規格,新加坡跟隨歐洲規格 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 18
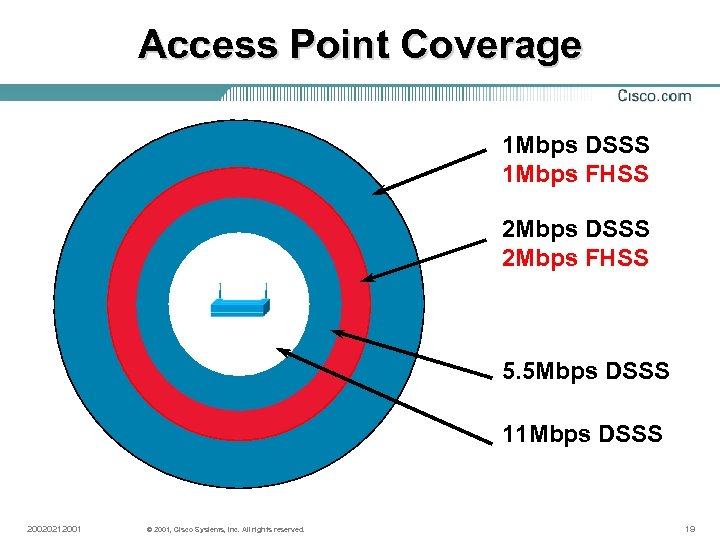
Access Point Coverage 1 Mbps DSSS 1 Mbps FHSS 2 Mbps DSSS 2 Mbps FHSS 5. 5 Mbps DSSS 11 Mbps DSSS 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 19
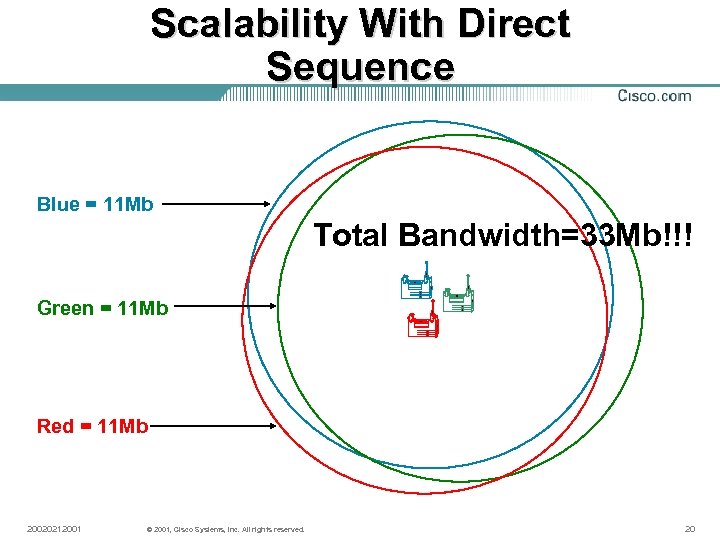
Scalability With Direct Sequence Blue = 11 Mb Total Bandwidth=33 Mb!!! Green = 11 Mb Red = 11 Mb 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 20
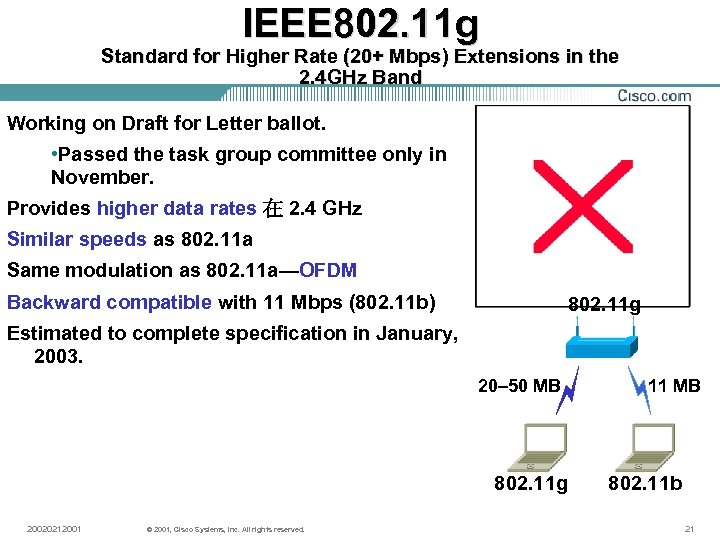
IEEE 802. 11 g Standard for Higher Rate (20+ Mbps) Extensions in the 2. 4 GHz Band Working on Draft for Letter ballot. • Passed the task group committee only in November. Provides higher data rates 在 2. 4 GHz Similar speeds as 802. 11 a Same modulation as 802. 11 a—OFDM Backward compatible with 11 Mbps (802. 11 b) 802. 11 g Estimated to complete specification in January, 2003. 20– 50 MB 802. 11 g 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 11 MB 802. 11 b 21
802. 11 g VS 802. 11 b 傳輸速度 雖說是同時支援 802. 11 b/802. 11 g,但並不是說最高傳輸速度總是可以達到 54 Mbps。究其原因,802. 11 g產品有可同時使用 802. 11 b與802. 11 g的「 802. 11 b相容模式」。在這一模式下,802. 11 b用戶的最高通信速度為 11 Mbps。 這是可以理解的。但是,這時802. 11 g用戶也只有11 Mbps。總之,該相容模式是「 平時以高速的802. 11 g通信,只要有一個802. 11 b用戶進入,所有人員均轉換到 802. 11 b」。如果想達到 54 Mbps,所有用戶必須是 802. 11 g用戶。 通信距離 802. 11 g較802. 11 b通信距離短。在通常情況下,802. 11 b模式的通信距離是「以 存取點為中心的半徑約45米」。如果是 802. 11 g模式,那麼通信距離是「以存取點為 中心的半徑 15米」。總之,根據環境,必須將此前一台就足夠的存取點增加到 2台以上, 必須能夠提供能夠無線連接多個存取點的橋接功能,但是,此時必須購買多個AP橋接 器。 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 22
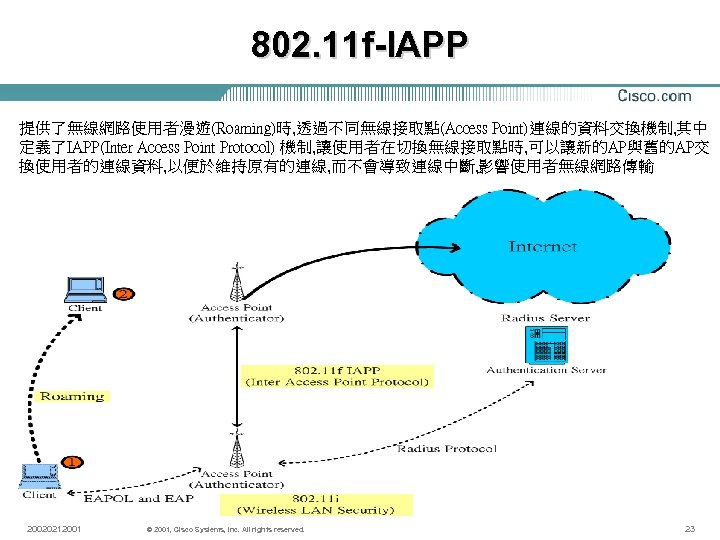
802. 11 f-IAPP 提供了無線網路使用者漫遊(Roaming)時, 透過不同無線接取點(Access Point)連線的資料交換機制, 其中 定義了IAPP(Inter Access Point Protocol) 機制, 讓使用者在切換無線接取點時, 可以讓新的AP與舊的AP交 換使用者的連線資料, 以便於維持原有的連線, 而不會導致連線中斷, 影響使用者無線網路傳輸 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 23
802. 11 i Security 1. 定義了在 802. 11 a/b/g MAC(Media Access Control) Layer的安全機制 , 主要以 EAP-802. 1 x做為認證的方 式 2. AES與 TKIP(Temporal Key Integrity Protocol)作為 加密的方法 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 24
Wireless LAN Topologies 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. Wireless LAN Topologies-25 25
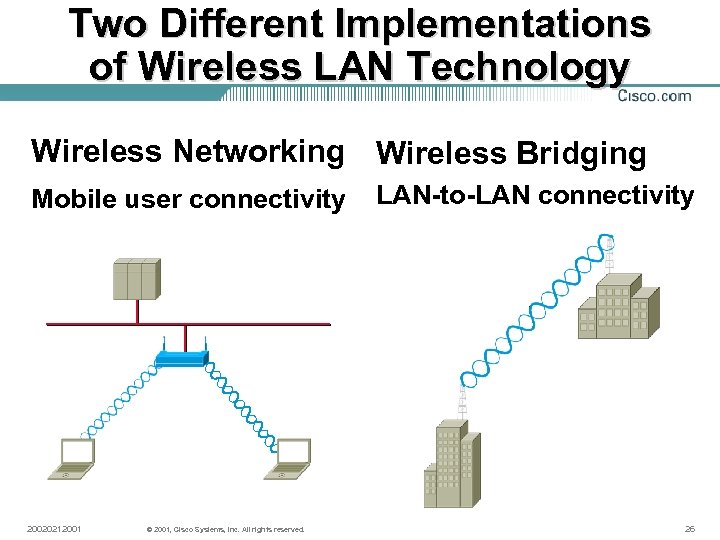
Two Different Implementations of Wireless LAN Technology Wireless Networking Wireless Bridging Mobile user connectivity 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. LAN-to-LAN connectivity 26
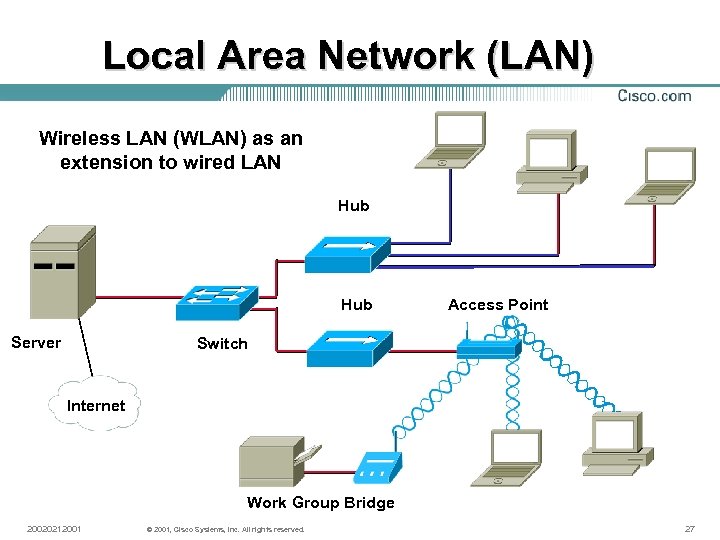
Local Area Network (LAN) Wireless LAN (WLAN) as an extension to wired LAN Hub Server Access Point Switch Internet Work Group Bridge 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 27
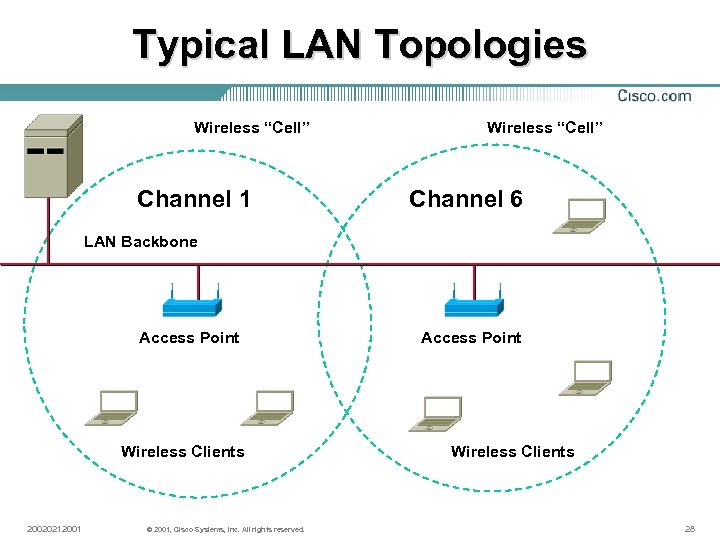
Typical LAN Topologies Wireless “Cell” Channel 1 Wireless “Cell” Channel 6 LAN Backbone Access Point Wireless Clients 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. Access Point Wireless Clients 28
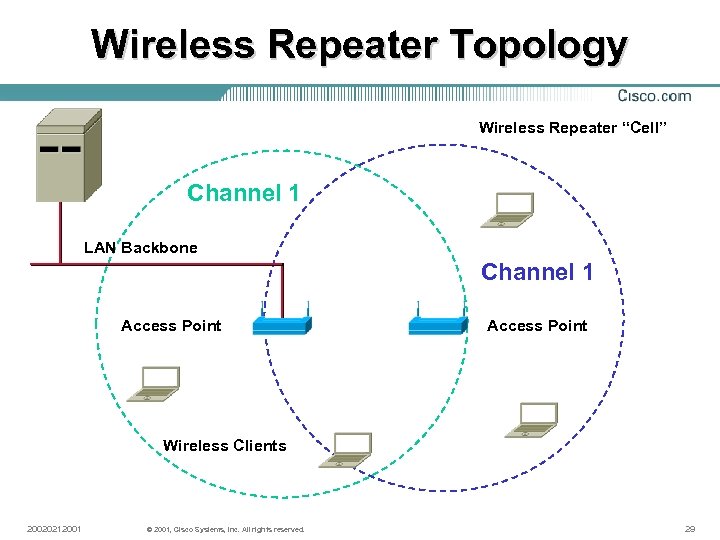
Wireless Repeater Topology Wireless Repeater “Cell” Channel 1 LAN Backbone Channel 1 Access Point Wireless Clients 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 29
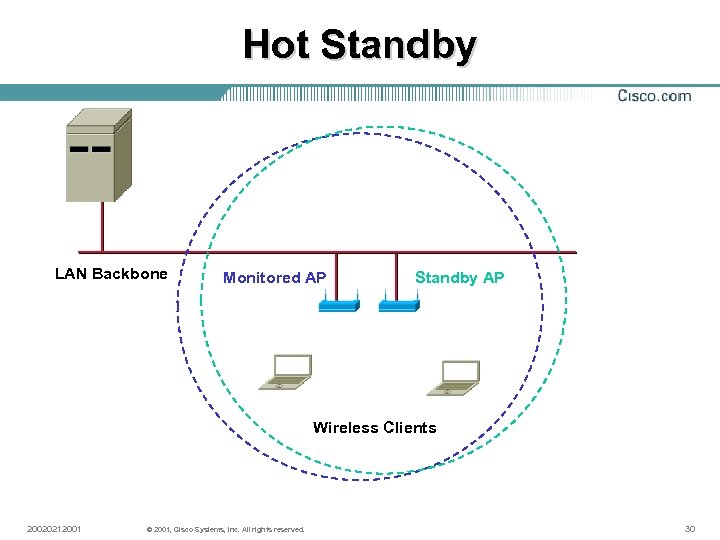
Hot Standby LAN Backbone Monitored AP Standby AP Wireless Clients 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 30
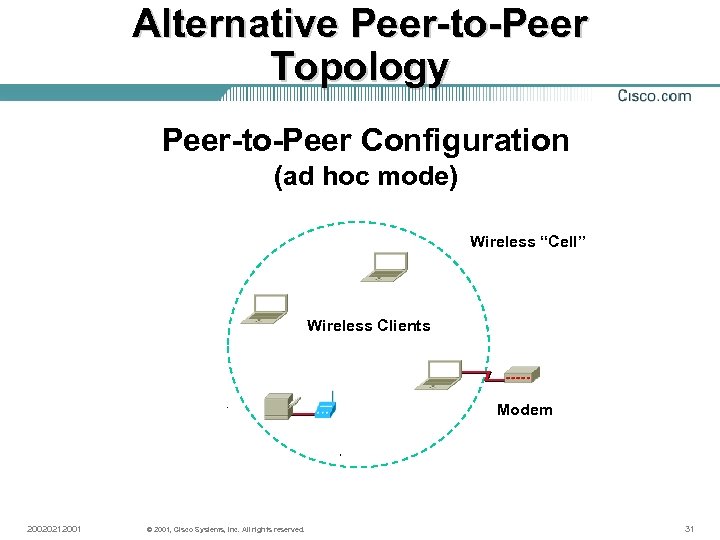
Alternative Peer-to-Peer Topology Peer-to-Peer Configuration (ad hoc mode) Wireless “Cell” Wireless Clients Modem 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 31
Wireless LAN Security 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 32
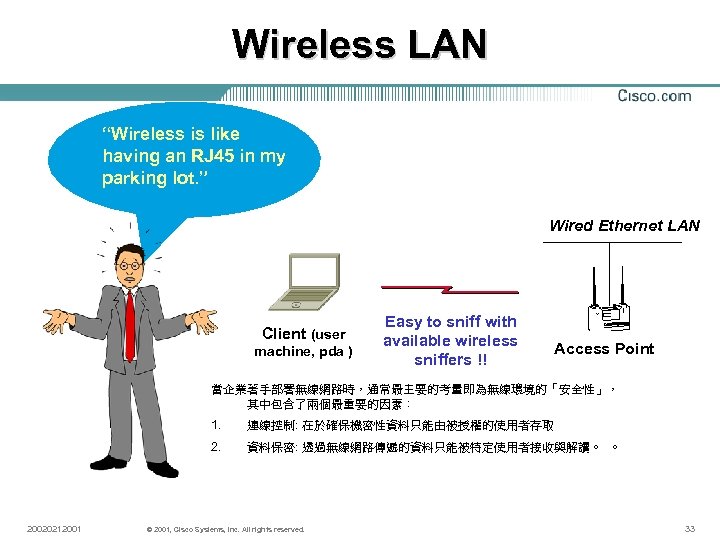
Wireless LAN “Wireless is like having an RJ 45 in my parking lot. ” Wired Ethernet LAN Client (user machine, pda ) Easy to sniff with available wireless sniffers !! Access Point 當企業著手部署無線網路時,通常最主要的考量即為無線環境的「安全性」, 其中包含了兩個最重要的因素: 1. 2. 20020212001 連線控制: 在於確保機密性資料只能由被授權的使用者存取 資料保密: 透過無線網路傳遞的資料只能被特定使用者接收與解讀。 。 © 2001, Cisco Systems, Inc. All rights reserved. 33
連線控制 802. 11標準在連線控制方面,制定了4種無線網路 客戶端認證機制 1. 開放式 2. 共享金鑰式 3. 服務識別碼SSID(Service Set Identifier) 4. MAC位址認證。 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 34
資料保密 1. 資料保密的設計,802. 11標準則採用WEP加密法來保 護無線網路基地台與客戶端網路介面間的資料安全 2. 其加密方式為利用 64位元或 128位元長度的金鑰,透過 RC 4演算法對資料進行加密 3. WEP金鑰還可被視為一種控制存取的機制,當使用者 缺少WEP金鑰時,將無法從無線網路存取點接收或傳送資料 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 35
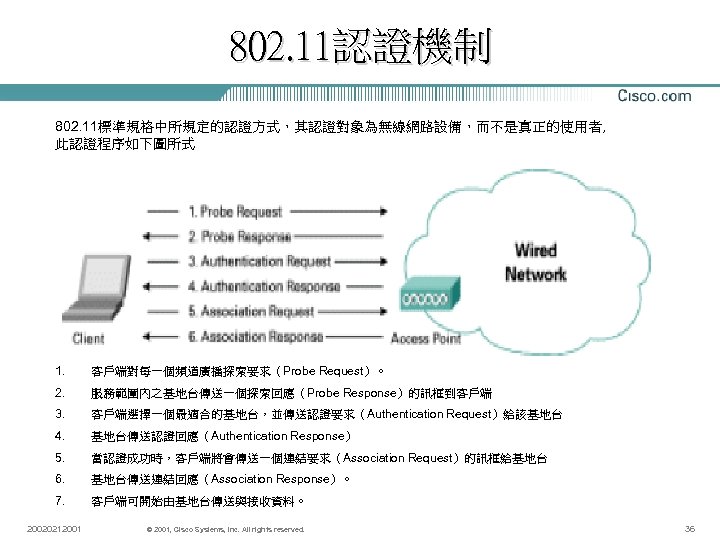
802. 11認證機制 802. 11標準規格中所規定的認證方式,其認證對象為無線網路設備,而不是真正的使用者, 此認證程序如下圖所式 1. 客戶端對每一個頻道廣播探索要求(Probe Request)。 2. 服務範圍內之基地台傳送一個探索回應(Probe Response)的訊框到客戶端 3. 客戶端選擇一個最適合的基地台,並傳送認證要求(Authentication Request)給該基地台 4. 基地台傳送認證回應(Authentication Response) 5. 當認證成功時,客戶端將會傳送一個連結要求(Association Request)的訊框給基地台 6. 基地台傳送連結回應(Association Response)。 7. 客戶端可開始由基地台傳送與接收資料。 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 36
開放式認證 開放式認證本身是一種無效的認證演算法,如果 沒有配合資料加密的技術,無線網路基地台將會 准予任何來自客戶端的認證要求,亦即任何知道 基地台 SSID的客戶端裝置,都可以連線到此網路中。 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 37
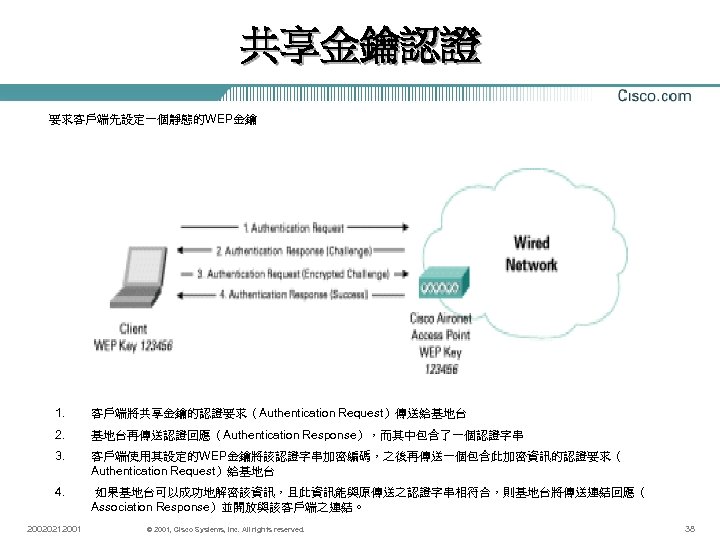
共享金鑰認證 要求客戶端先設定一個靜態的WEP金鑰 1. 客戶端將共享金鑰的認證要求(Authentication Request)傳送給基地台 2. 基地台再傳送認證回應(Authentication Response),而其中包含了一個認證字串 3. 客戶端使用其設定的WEP金鑰將該認證字串加密編碼,之後再傳送一個包含此加密資訊的認證要求( Authentication Request)給基地台 4. 如果基地台可以成功地解密該資訊,且此資訊能與原傳送之認證字串相符合,則基地台將傳送連結回應( Association Response)並開放與該客戶端之連結。 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 38
SSID : Service Set Identifier 一般而言,客戶端需要設定適當的服務識別碼才能存取到無線網路。 不過,SSID並不提供任何資料保密的功能,也不完全提供客戶端連接 到無線網路存取點的認證機制。 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 39
MAC位址認證 其運作邏輯為基地台可針對事先設定好的MAC位址名單,或是透過認證 伺服器來對客戶端進行認證;主要目的是加強開放式與共享金鑰式的認 證機制,進一步限制未經過授權的客戶端裝置對網路進行存取的動作 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 40
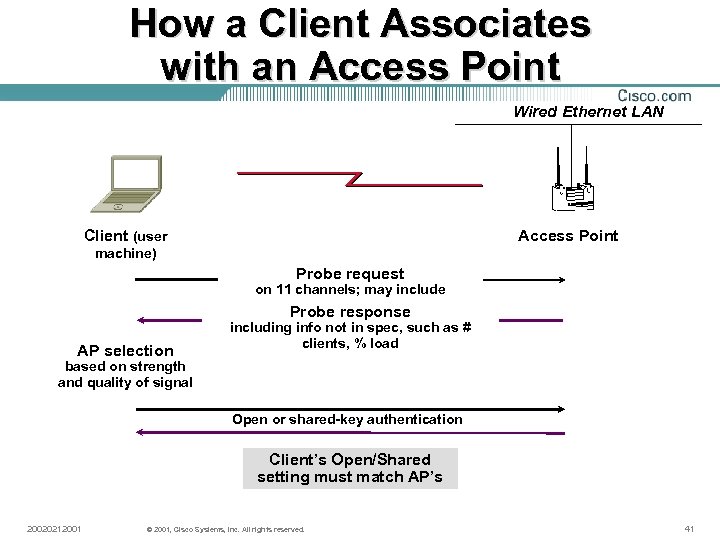
How a Client Associates with an Access Point Wired Ethernet LAN Client (user Access Point machine) Probe request on 11 channels; may include (broadcast) SSID Probe response AP selection including info not in spec, such as # clients, % load based on strength and quality of signal Open or shared-key authentication Client’s Open/Shared setting must match AP’s 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 41
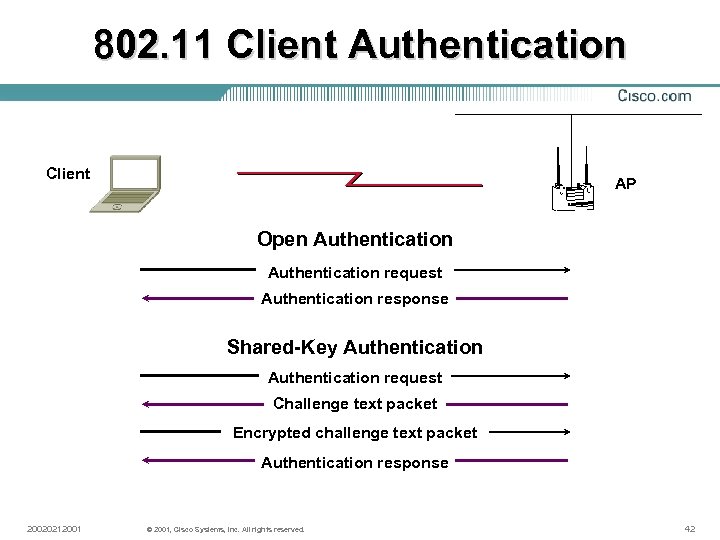
802. 11 Client Authentication Client AP Open Authentication request Authentication response Shared-Key Authentication request Challenge text packet Encrypted challenge text packet Authentication response 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 42
窺探認證機制的漏洞 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 43
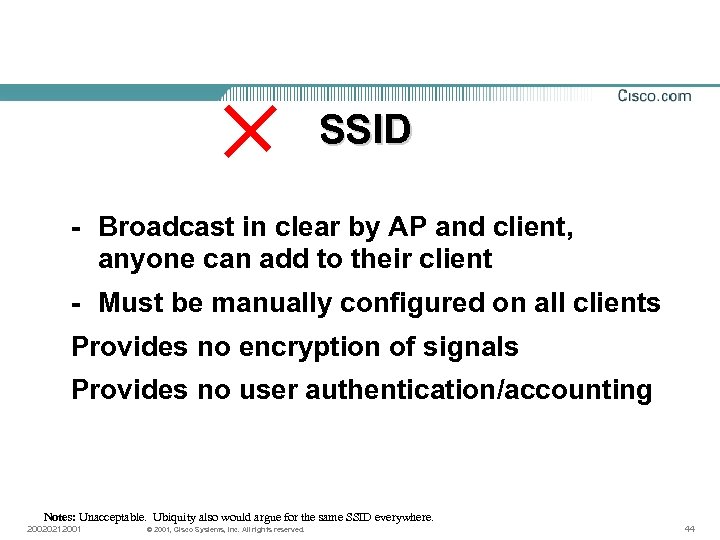
SSID - Broadcast in clear by AP and client, anyone can add to their client - Must be manually configured on all clients Provides no encryption of signals Provides no user authentication/accounting Notes: Unacceptable. Ubiquity also would argue for the same SSID everywhere. 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 44
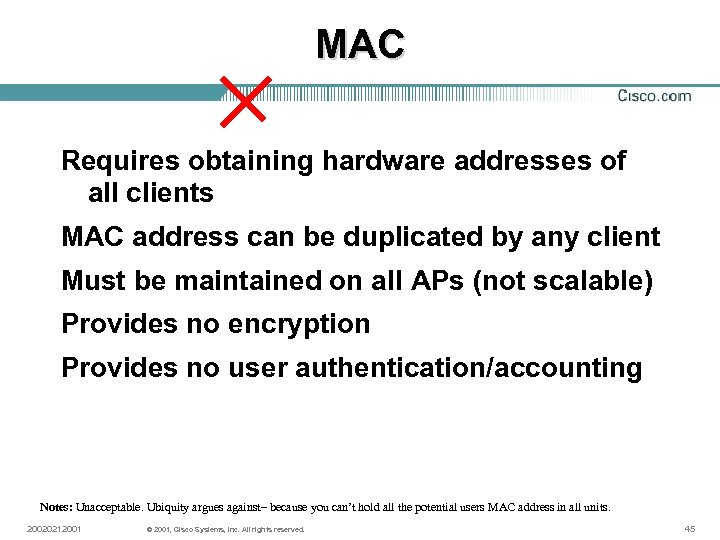
MAC Requires obtaining hardware addresses of all clients MAC address can be duplicated by any client Must be maintained on all APs (not scalable) Provides no encryption Provides no user authentication/accounting Notes: Unacceptable. Ubiquity argues against– because you can’t hold all the potential users MAC address in all units. 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 45
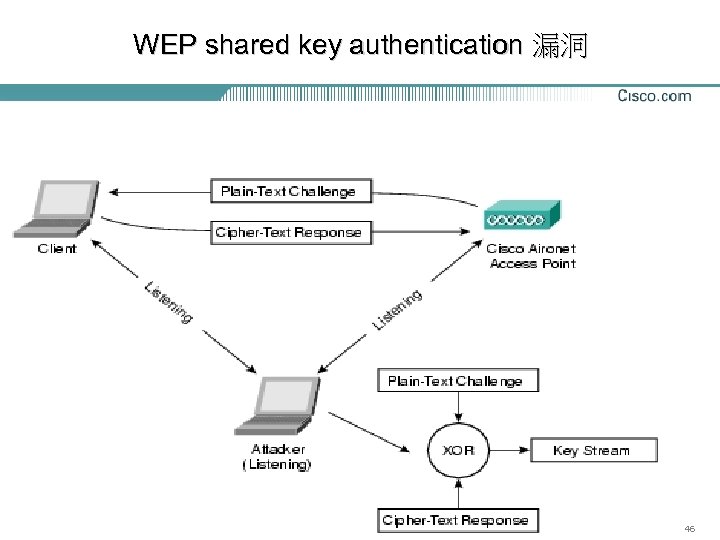
WEP shared key authentication 漏洞 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 46
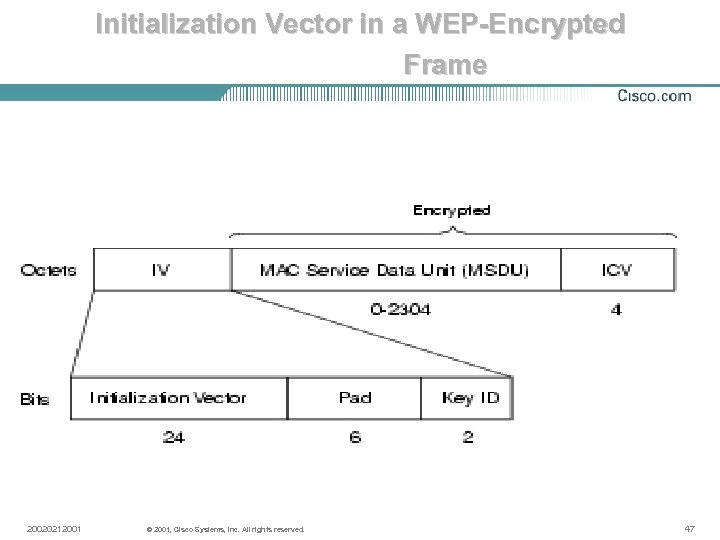
Initialization Vector in a WEP-Encrypted Frame 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 47
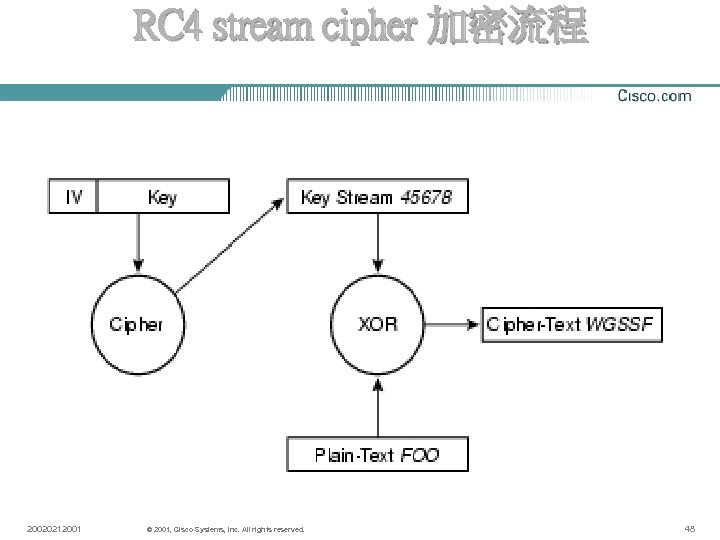
RC 4 stream cipher 加密流程 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 48
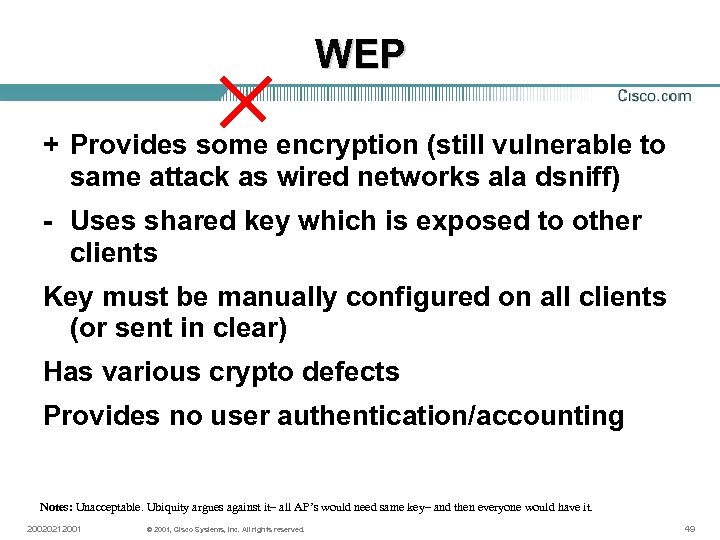
WEP + Provides some encryption (still vulnerable to same attack as wired networks ala dsniff) - Uses shared key which is exposed to other clients Key must be manually configured on all clients (or sent in clear) Has various crypto defects Provides no user authentication/accounting Notes: Unacceptable. Ubiquity argues against it– all AP’s would need same key– and then everyone would have it. 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 49
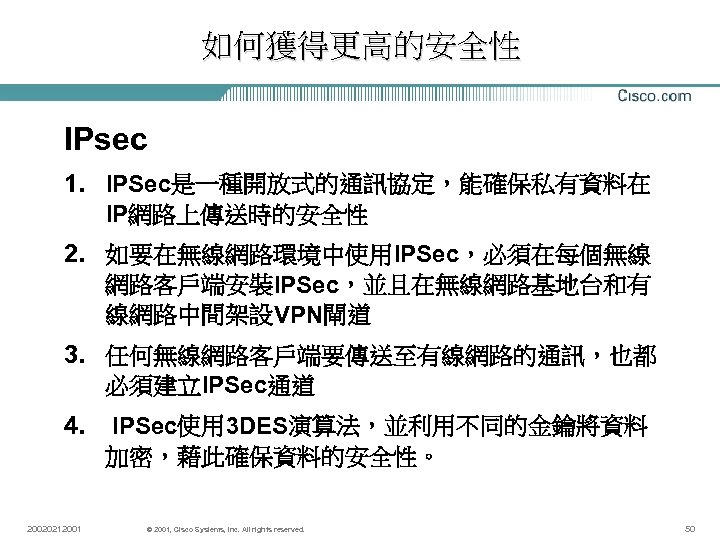
如何獲得更高的安全性 IPsec 1. IPSec是一種開放式的通訊協定,能確保私有資料在 IP網路上傳送時的安全性 2. 如要在無線網路環境中使用IPSec,必須在每個無線 網路客戶端安裝IPSec,並且在無線網路基地台和有 線網路中間架設VPN閘道 3. 任何無線網路客戶端要傳送至有線網路的通訊,也都 必須建立IPSec通道 4. 20020212001 IPSec使用 3 DES演算法,並利用不同的金鑰將資料 加密,藉此確保資料的安全性。 © 2001, Cisco Systems, Inc. All rights reserved. 50
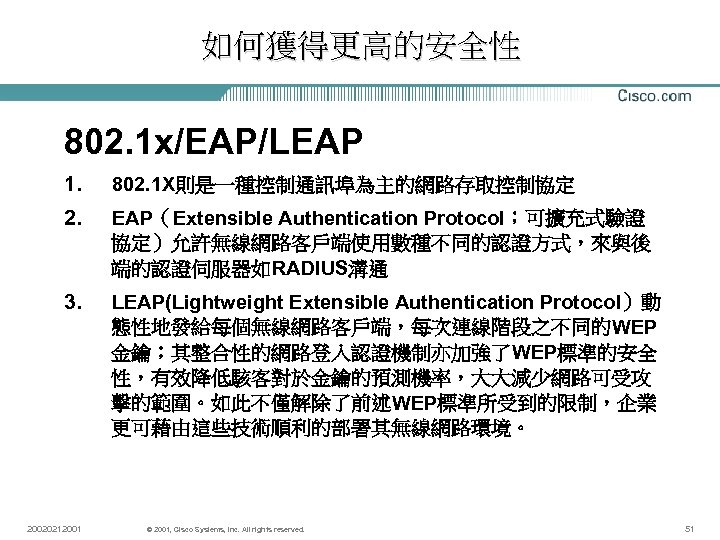
如何獲得更高的安全性 802. 1 x/EAP/LEAP 1. 802. 1 X則是一種控制通訊埠為主的網路存取控制協定 2. EAP(Extensible Authentication Protocol;可擴充式驗證 協定)允許無線網路客戶端使用數種不同的認證方式,來與後 端的認證伺服器如RADIUS溝通 3. LEAP(Lightweight Extensible Authentication Protocol)動 態性地發給每個無線網路客戶端,每次連線階段之不同的WEP 金鑰;其整合性的網路登入認證機制亦加強了WEP標準的安全 性,有效降低駭客對於金鑰的預測機率,大大減少網路可受攻 擊的範圍。如此不僅解除了前述WEP標準所受到的限制,企業 更可藉由這些技術順利的部署其無線網路環境。 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 51
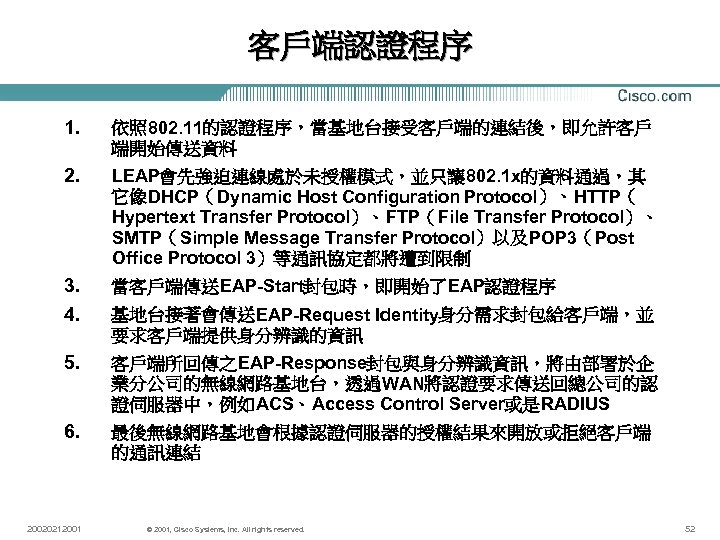
客戶端認證程序 1. 依照 802. 11的認證程序,當基地台接受客戶端的連結後,即允許客戶 端開始傳送資料 2. LEAP會先強迫連線處於未授權模式,並只讓 802. 1 x的資料通過,其 它像DHCP(Dynamic Host Configuration Protocol)、HTTP( Hypertext Transfer Protocol)、FTP(File Transfer Protocol)、 SMTP(Simple Message Transfer Protocol)以及POP 3(Post Office Protocol 3)等通訊協定都將遭到限制 3. 4. 當客戶端傳送EAP-Start封包時,即開始了EAP認證程序 5. 客戶端所回傳之EAP-Response封包與身分辨識資訊,將由部署於企 業分公司的無線網路基地台,透過WAN將認證要求傳送回總公司的認 證伺服器中,例如ACS、Access Control Server或是RADIUS 6. 最後無線網路基地會根據認證伺服器的授權結果來開放或拒絕客戶端 的通訊連結 20020212001 基地台接著會傳送EAP-Request Identity身分需求封包給客戶端,並 要求客戶端提供身分辨識的資訊 © 2001, Cisco Systems, Inc. All rights reserved. 52
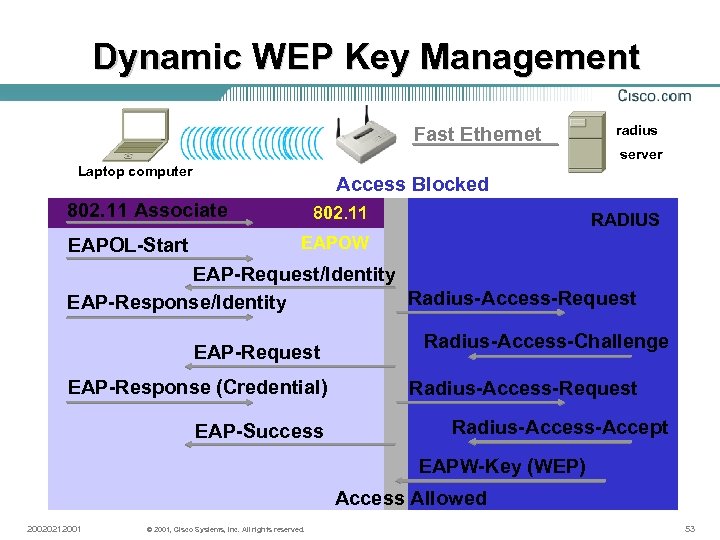
Dynamic WEP Key Management Fast Ethernet radius server Laptop computer Access Blocked 802. 11 Associate EAPOL-Start 802. 11 RADIUS EAPOW EAP-Request/Identity Radius-Access-Request EAP-Response/Identity EAP-Request EAP-Response (Credential) EAP-Success Radius-Access-Challenge Radius-Access-Request Radius-Access-Accept EAPW-Key (WEP) Access Allowed 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 53
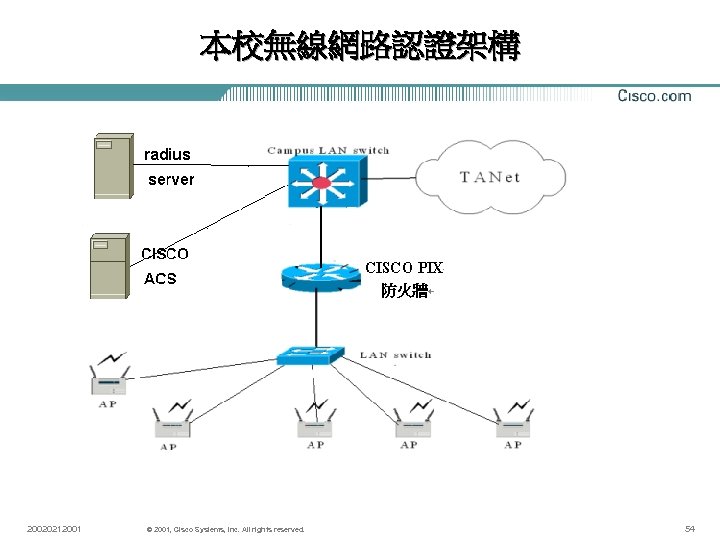
本校無線網路認證架構 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 54
Questions and Thank You 資訊網路中心 朱朝昑 20020212001 © 2001, Cisco Systems, Inc. All rights reserved. 55
f9d28def6d6a710ee47987f3ff00ae86.ppt