0ffddc58d6a5c1f891910dc68fad86dd.ppt
- Количество слайдов: 34
Business Logic Attacks – Bots and BATs Eldad Chai Web Research Team Leader Imperva OWASP EU 09 Poland eldad@imperva. com Copyright © The OWASP Foundation Permission is granted to copy, distribute and/or modify this document under the terms of the OWASP License. The OWASP Foundation http: //www. owasp. org
Agenda <Business Logic Attacks (BATs) – The Whats and Whys <Classes of BATs <BATs and Bots <Mitigating BATs <Summary <Q&A OWASP App. Sec. EU 09 Poland 2
Business Logic Attacks (BATs) – The Whats and Whys OWASP App. Sec. EU 09 Poland 3
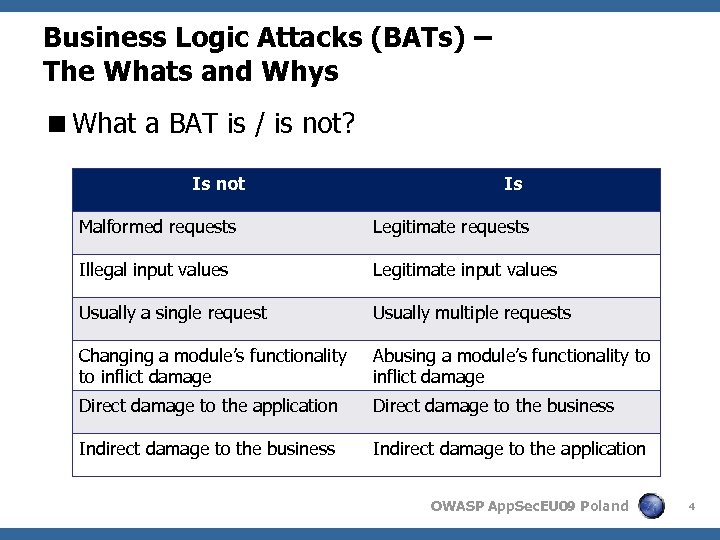
Business Logic Attacks (BATs) – The Whats and Whys <What a BAT is / is not? Is not Is Malformed requests Legitimate requests Illegal input values Legitimate input values Usually a single request Usually multiple requests Changing a module’s functionality to inflict damage Abusing a module’s functionality to inflict damage Direct damage to the application Direct damage to the business Indirect damage to the application OWASP App. Sec. EU 09 Poland 4
Business Logic Attacks (BATs) – The Whats and Whys <Why BATs? 4 Technical types of attacks are gaining more awareness 4 Better coding practices and tools at the development phase 4 In some cases an entire class of vulnerabilities was eliminated out of the box 4 Better assessment tools for detecting vulnerabilities 4 Better tools for detecting and blocking attacks OWASP App. Sec. EU 09 Poland 5
Business Logic Attacks (BATs) – The Whats and Whys <So… why BATs? 4 Require less understanding of the underlying technology 4 More targets / opportunities out there 4 Larger gain 4 Can be “amplified” through automation OWASP App. Sec. EU 09 Poland 6
Business Logic Attacks (BATs) – The Whats and Whys <What damage can BATs do? 4 Financial damage 4 Damage to reputation 4 Do. S, EDo. S/FDo. S 4 Qo. S degradation 4 Data leakage OWASP App. Sec. EU 09 Poland 7
Classes of BATs <Classifying flaws 4 Numerous examples of business logic flaws 4 Both the business logic and its implementation might have flaws <Classifying attacks 4 The attack techniques are not so diverse 4 Mainly because automation is usually required 4 Automation techniques have much in common OWASP App. Sec. EU 09 Poland 8
Abuse of Functionality – Brute Force <Multiple invocations of transactions with random or semi-random data <Usually includes repeating a request to a certain module with the intention of guessing valid values OWASP App. Sec. EU 09 Poland 9
Abuse of Functionality – Brute Force <Solution requirements 4 Detection § Identify failed transactions § Measure the rate of failed transactions in real time § Define acceptable thresholds for the rate of failed transactions in varying contexts: IP, session, user, systemwide, etc. 4 Mitigation § Anti-automation – Validate human interaction – Forced delays § Reduce the effective rate of attacks to the point that they become futile OWASP App. Sec. EU 09 Poland 10
Abuse of Functionality – Repetition Attacks <Multiple invocations of requests with valid data <Include repeating requests to a certain module with the intention of invoking a large number of business transactions OWASP App. Sec. EU 09 Poland 11
Abuse of Functionality – Repetition Attacks <Solution requirements 4 Detection § Identify successful transactions § Measure the rate of successful transactions in real time § Define acceptable thresholds for the rate of successful transactions in varying contexts: IP, session, user, systemwide, etc. 4 Mitigation § Anti-automation – Validate human interaction – Forced delays § Reduce the effective rate of attacks to the point that they become futile OWASP App. Sec. EU 09 Poland 12
Abuse of Functionality – Locking Business Resources OWASP App. Sec. EU 09 Poland 13
Abuse of Functionality – Locking Business Resources <Lock resources by doing nothing <Invoke business transactions that (temporarily) consume / hold business resources <Prevent the transactions from completing <Resources are kept locked and pending, virtually unavailable to others OWASP App. Sec. EU 09 Poland 14
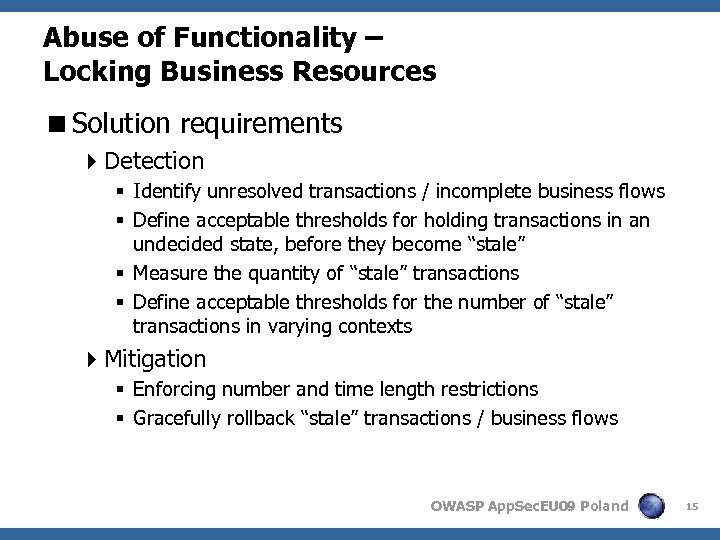
Abuse of Functionality – Locking Business Resources <Solution requirements 4 Detection § Identify unresolved transactions / incomplete business flows § Define acceptable thresholds for holding transactions in an undecided state, before they become “stale” § Measure the quantity of “stale” transactions § Define acceptable thresholds for the number of “stale” transactions in varying contexts 4 Mitigation § Enforcing number and time length restrictions § Gracefully rollback “stale” transactions / business flows OWASP App. Sec. EU 09 Poland 15
Application Flow Bypass <Bypass or circumvent the intended flow of an application <This includes invoking transactions out of their intended order OWASP App. Sec. EU 09 Poland 16
Application Flow Bypass <Solution requirements 4 Detection § Identify a set of transactions that form a logical flow § Define an acceptable order of transactions in a flow 4 Mitigation § Gracefully rollback transactions / business flows that do not comply with the flow definition OWASP App. Sec. EU 09 Poland 17
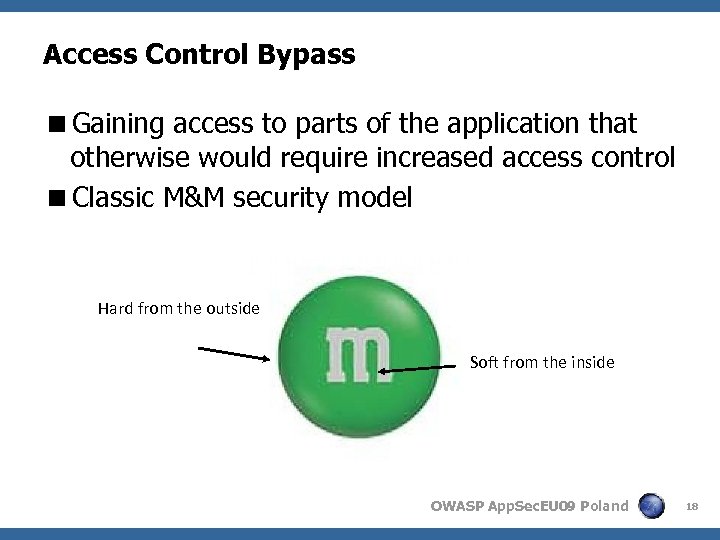
Access Control Bypass <Gaining access to parts of the application that otherwise would require increased access control <Classic M&M security model Hard from the outside Soft from the inside OWASP App. Sec. EU 09 Poland 18
Access Control Bypass <Solution requirements 4 Detection § Identify application users and their roles § Associate roles with privileged transactions § Identify access to privileged transactions by an unprivileged user 4 Mitigation § Deny access from unprivileged users OWASP App. Sec. EU 09 Poland 19
Web Leeching <Leeching on business resources 4 Contact forms (email spam) 4 Sharing interfaces (comment spam) 4 Redirect modules (phishing scams) 4 Hotlinking (bandwidth leeching) 4 Resource scraping (business data leeching) OWASP App. Sec. EU 09 Poland 20
Web Leeching <Solution requirements 4 Detection § Identify textual abuse patterns (e. g. , comment spam, email spam) § Identify abusive sources (e. g. , by Referer, by IP) § Identify intensive automated access 4 Mitigation § Block abusive access § Anti-automation § Throttle down automated access OWASP App. Sec. EU 09 Poland 21
BATs and Bots <Automation’s part of total attacks is growing 4 Spam bots 4 Email harvesters 4 RFI bots 4 SQLi bots 4… <Automation is getting more sophisticated 4 Deployment techniques 4 Attack automation techniques OWASP App. Sec. EU 09 Poland 22
BATs and Bots <Online business transactions usually have a small effect on the business <An attacker needs to invoke multiple transactions in order to have a significant effect <Some examples of automated BATs: 4 Brute force 4 Repetition attacks 4 Do. S (EDo. S/FDo. S) 4 Comment spam 4… OWASP App. Sec. EU 09 Poland 23
Mitigating BATs <First thing’s first: How do you know that you are susceptible to BATs? 4 Use OWASP testing guide for business logic testing 4 Use assessment services <Purely automated scans usually don’t detect business logic flaws 4 Cannot differentiate between a positive and a negative business effect 4 Have a major disadvantage in assessing production environments OWASP App. Sec. EU 09 Poland 24
Mitigating BATs < Validate human interaction 4 CAPTCHA § Generic § Affects user experience § Blocks legitimate bots 4 Second level authentication § Authentication based on personal data § Validates specific user § Requires additional data 4 Integrated § Requires prior knowledge of all validation points § Hard to validate based on user behavior 4 External § Can be generic § Might require changing application responses § Easy to validate suspicious sessions only OWASP App. Sec. EU 09 Poland 25
Mitigating BATs <Rolling back transactions 4 Integrated § Requires handling within several application modules § Requires prior knowledge and definition of the protected flows and rollback sequences § Implementation complexity is highly dependant on application architecture 4 External § Can be generic § Easily integrated into existing detection and mitigation framework § Might require additional session data § Needs to be carefully designed and implemented OWASP App. Sec. EU 09 Poland 26
Mitigating BATs <Real time measurements 4 Integrated § Requires prior knowledge of what is to be measured § Added complexity to the application § Might be more accurate when conditions cannot be detected by external tools 4 External § Generic § Easily integrated into existing detection and mitigation framework § Not everything can be measured externally OWASP App. Sec. EU 09 Poland 27
Mitigating BATs <Force delays 4 Integrated § Require handling within several application modules § In case of an attack, the application might be overhelmed § Not really a “classic” internal feature 4 External § Can be generic § Easily integrated into existing detection and mitigation framework § Might be too crude OWASP App. Sec. EU 09 Poland 28
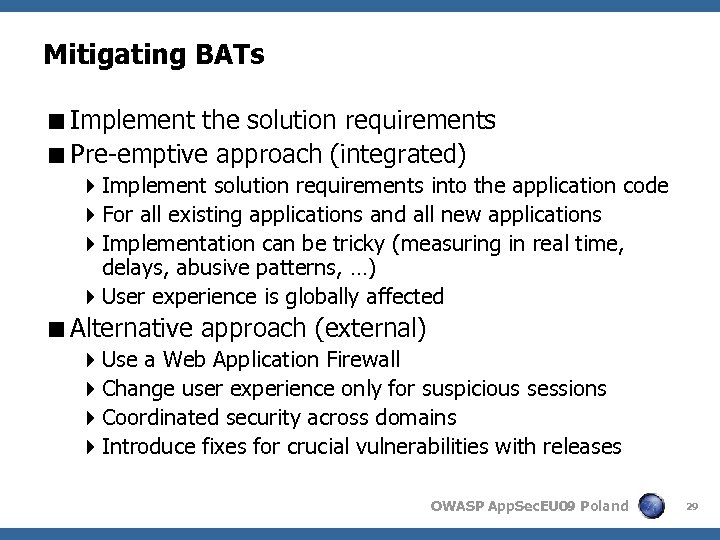
Mitigating BATs <Implement the solution requirements <Pre-emptive approach (integrated) 4 Implement solution requirements into the application code 4 For all existing applications and all new applications 4 Implementation can be tricky (measuring in real time, delays, abusive patterns, …) 4 User experience is globally affected <Alternative approach (external) 4 Use a Web Application Firewall 4 Change user experience only for suspicious sessions 4 Coordinated security across domains 4 Introduce fixes for crucial vulnerabilities with releases OWASP App. Sec. EU 09 Poland 29
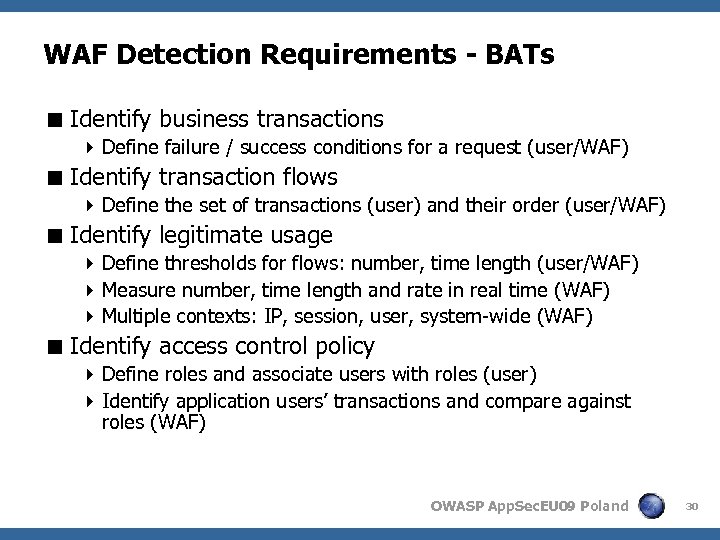
WAF Detection Requirements - BATs < Identify business transactions 4 Define failure / success conditions for a request (user/WAF) < Identify transaction flows 4 Define the set of transactions (user) and their order (user/WAF) < Identify legitimate usage 4 Define thresholds for flows: number, time length (user/WAF) 4 Measure number, time length and rate in real time (WAF) 4 Multiple contexts: IP, session, user, system-wide (WAF) < Identify access control policy 4 Define roles and associate users with roles (user) 4 Identify application users’ transactions and compare against roles (WAF) OWASP App. Sec. EU 09 Poland 30
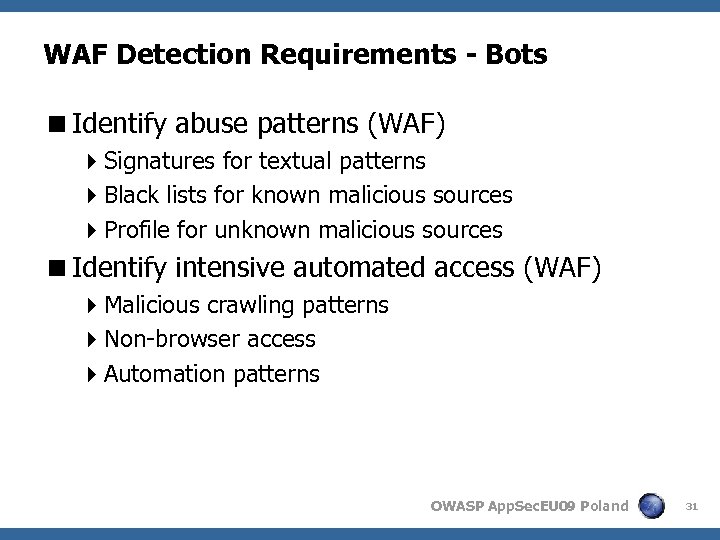
WAF Detection Requirements - Bots <Identify abuse patterns (WAF) 4 Signatures for textual patterns 4 Black lists for known malicious sources 4 Profile for unknown malicious sources <Identify intensive automated access (WAF) 4 Malicious crawling patterns 4 Non-browser access 4 Automation patterns OWASP App. Sec. EU 09 Poland 31
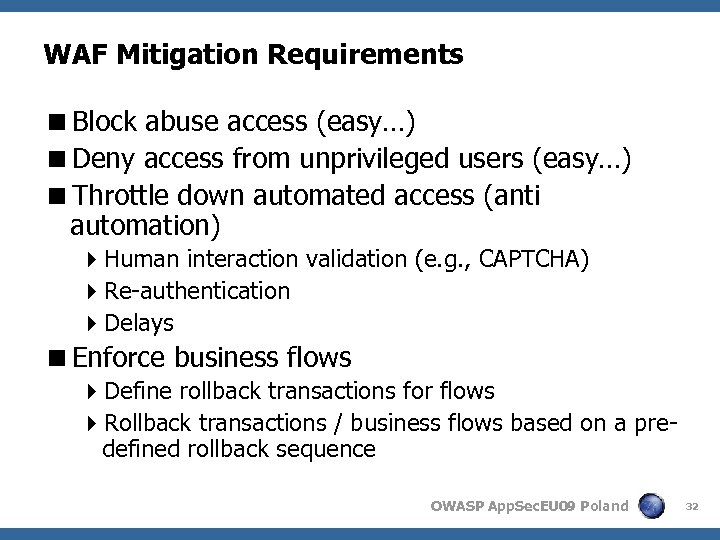
WAF Mitigation Requirements <Block abuse access (easy…) <Deny access from unprivileged users (easy…) <Throttle down automated access (anti automation) 4 Human interaction validation (e. g. , CAPTCHA) 4 Re-authentication 4 Delays <Enforce business flows 4 Define rollback transactions for flows 4 Rollback transactions / business flows based on a predefined rollback sequence OWASP App. Sec. EU 09 Poland 32
Summary <The risk of business logic attacks is increasing <Business logic attacks abuse the web application’s functionalities <Most classes of attacks require automation <Detecting and mitigating BATs requires a new set of tools <These tools can be implemented internally or externally <WAFs can detect and mitigate BATs and Bots OWASP App. Sec. EU 09 Poland 33
Thanks! Q&A OWASP App. Sec. EU 09 Poland 34
0ffddc58d6a5c1f891910dc68fad86dd.ppt