5bb056b6fa7ce1e455f785853538c3a3.ppt
- Количество слайдов: 39

Bluetooth Seminar Università degli Studi di Milano May 25, 2004

Seminar Agenda • Accenture Presentation 15’ • Bluetooth Technology and Market overview 30’ • Bluetooth at work: Micropayments concepts 30’ • Questions & Answers 15’ 2

Seminar Agenda • Accenture Presentation 15’ • Bluetooth Technology and Market overview 30’ • Bluetooth at work: u. Commerce concepts 30’ • Questions & Answers 15’ 3
Who is “Bluetooth”? • Harald Blaatand “Bluetooth” II • King of Denmark 940 -981 • Ericsson erected this Runic stone in hometown of Jelling – Harald is holding a mobile phone and notebook – Harald united Denmark and Norway – Harald brought Christianity to the Danes 4
What is Bluetooth? • Bluetooth is not a company • Wireless RF standard • Radio System – Hardware – Software – Interoperability requirements • Commitment from over 2, 100 companies • Operates in 2. 45 GHz unlicensed frequency 5

Who is promoting Bluetooth? The Bluetooth SIG (Special Interest Group) 9 Promoters 182 Associates 2100+ Adopters IEEE 802. 15 WPAN = Bluetooth 6
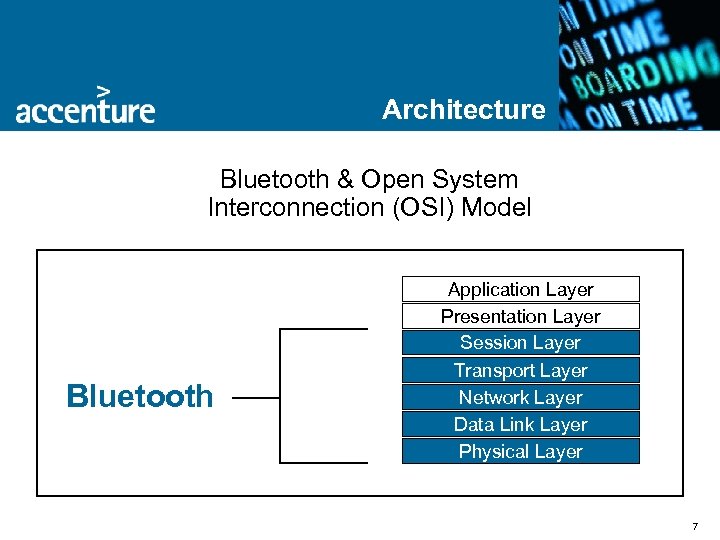
Architecture Bluetooth & Open System Interconnection (OSI) Model Bluetooth Application Layer Presentation Layer Session Layer Transport Layer Network Layer Data Link Layer Physical Layer 7
Core Capabilities Bandwidth • 721 kbs realized maximum data transfer • Simultaneous voice and data transmission • Support up to 7 connected devices • Piconets and Scatternets Power • ‘Client devices’ - 2. 5 m. W @ 10 meters Interference • FHSS on 1600 Channels Security • PIN and 128 bit key 8
Interference • Bluetooth supports Frequency Hopping Spread Spectrum (FHSS) • 1600 channel hops/sec on 79 channels • Avoids interference better than 802. 11 b that supports Direct Sequence Spread Spectrum (DSSS) 9
Security Key elements to Bluetooth security framework • • Frequency hopping – helps prevent a third party from “listening in” on a communication between two devices (1600 hops/sec over 79 frequencies) Security entities – – – • Unique device identifier – 48 bit address Private authentication key (128 bit) 128 -bit random number (frequently changing) Private encryption key – 8 -128 bit PIN Link Key (128 bit) • Used for authentication • Parameter for deriving encryption key Each packet uses a different encryption key pair – If one packet is cracked, a new packet 625 ms later • • Due to national restrictions, keys may be shorter than 128 bits Additional application-level security can be implemented 10

What should the mobile device do at the beach? Expectations and Reality Initial Hype • World Peace • Huge markets overnight Today’s Reality • Many players • Interoperability issues • Poor quality 11
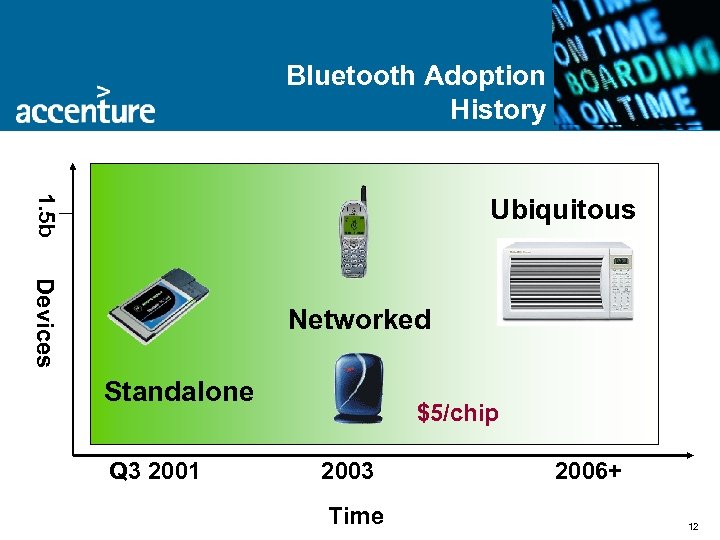
Bluetooth Adoption History 1. 5 b Ubiquitous Devices Networked Standalone Q 3 2001 $5/chip 2003 Time 2006+ 12
Common Issues • • Sometimes, it just doesn’t work Low bandwidth for some applications Interoperability Crowded RF Spectrum 13
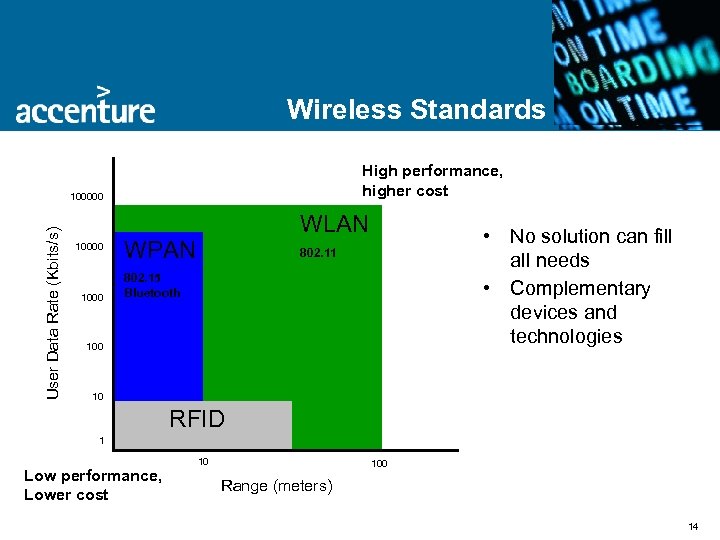
Wireless Standards High performance, higher cost User Data Rate (Kbits/s) 100000 1000 WLAN WPAN • No solution can fill all needs • Complementary devices and technologies 802. 11 802. 15 Bluetooth 100 10 RFID 1 Low performance, Lower cost 10 100 Range (meters) 14
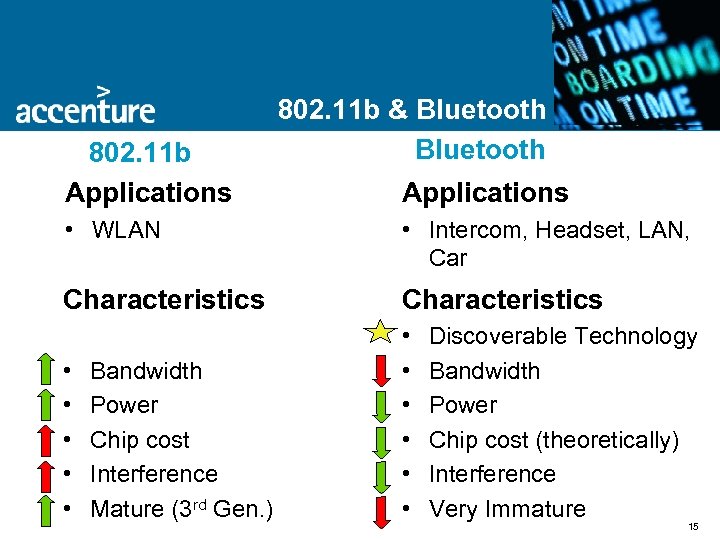
What should the mobile device do at the beach? 802. 11 b Applications 802. 11 b & Bluetooth Applications • WLAN • Intercom, Headset, LAN, Car Characteristics • • • Bandwidth Power Chip cost Interference Mature (3 rd Gen. ) Discoverable Technology Bandwidth Power Chip cost (theoretically) Interference Very Immature 15
RFID vs. Bluetooth RFID is gaining acceptance as a quick, convenient payment option, mostly in fast service industries (gas stations, fast food restaurants). • • • Bluetooth can be positioned in similar industries to serve multiple back office payment systems. More payment options are available with Bluetooth and the user is not constrained to ‘one device, one payment system’. Bluetooth devices can easily be updated to add retailers that were not originally associated to the user. Sign up for service via RFID requires the mailing of the RFID hardware needed before the quick mobile payment method is available for usage. Bluetooth sign up and initialization would be more efficient because the user’s mobile device would act as a unique identifier. Both options assume you carry the RFID or mobile device at the Point of Sale. Bluetooth could facilitate the use of online payment systems, such as, Qpass or Paypal, and therefore not add another back office system. RFID uses a payment method connected to the proprietary RFID reader system. RFID has a short transmission range and requires more proprietary hardware readers to cover the service area. Bluetooth has a larger range, 10 meters (100 meters with power boost), to easily cover required service areas. However, this may cause other usability issues for Bluetooth. RFIDs require more equipment than necessary to conduct a transaction and are only useful at participating vendors. Each Bluetooth device has the potential to be used as a payment/identification vehicle. 16
3 G & Bluetooth Lowering the Price of Admission to High Band. Width Services • Traditional Carriers • New Competitors Defining Characteristics • Licensed vs. Unlicensed RF Bands • Location Based Services vs. Proximity Based Services 17

Global Impact Market Sentiment • Europe and Asia Ahead • US Lags 18

Industries In the News • Hospitality • Starwood, Holiday Inn, Venetian Resort, Classwave, Registry Magic • Airlines • SAS, Sabre, Bluetags • Retail • Strio, Classwave • Automobile • Nokian Tyres, Clarion, AMI-C, Zucotto • Communication • O 2, BT, AT&T Wireless, Vodafone, Orange, Taiwan Cellular and Telefonica del Sur (Chile). 19
Seminar Agenda • Accenture Presentation 15’ • Bluetooth Technology and Market overview 30’ • Bluetooth at work: u. Commerce concepts 30’ • Questions & Answers 15’ 20
Introduction Video • Launch the Video of the Mobile Service Link Prototype 21
What is “u. Commerce”? Extending e. Commerce beyond the static terminal of the PC to anytime, anyplace, anywhere 22
What does “U” mean? • Untethered – Not constrained by hardwires of traditional computing • Ubiquitous – Taking place where a person wants • Unbounded – Not limited to traditional definition of commerce 23
Bluetooth + u. Commerce • Originally created as a cable replacement system by Ericsson • Capable of much more • Allows commerce and applications to be placed in once inaccessible places • Enables the u. Commerce vision of anytime, anyplace, anywhere through proximity based computing 24
Internet Micropayments to the Real World • Imagine you can pay for beverages from vending machines, taxi fares or even supermarket shopping using your mobile phone • Imagine, as well, that the vending machine products and prices all appear automatically on your mobile’s display, so that all you have to do is type in your secret PIN code to authenticate the transaction. All products in the future could be customised to “hijack” your mobile phone as their interface to offer you services as you walk within range • All purchases and payments remain simple and secure and, more importantly, you don’t need to carry loose change around any longer. You don’t need to collect separate bills either, since your payment provider will send you a detailed bill at the end of the month 25
Internet Micropayments to the Real World • The following two slides describe two variations of an architecture that could enable this concept using today’s existing and emerging technologies: • the first variant is based on SMS over GSM and is currently restricted to European implementations • the second variant makes use of the Internet as a globally available communications medium. • Let’s see how Internet micropayments can be ported to the real world. . . 26
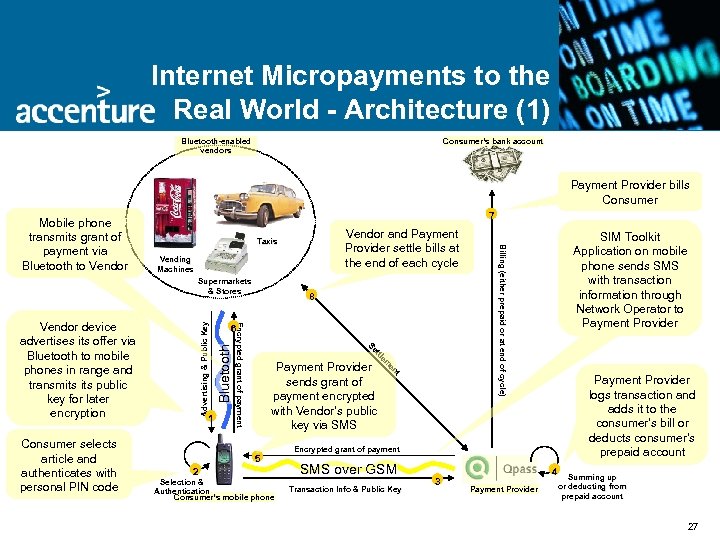
Internet Micropayments to the Real World - Architecture (1) Bluetooth-enabled vendors Consumer’s bank account Payment Provider bills Consumer 7 Vending Machines Supermarkets & Stores Bluetooth Advertising & Public Key 6 t en e em e tttl Se Se 1 8 Encrypted grant of payment Vendor device advertises its offer via Bluetooth to mobile phones in range and transmits public key for later encryption Consumer selects article and authenticates with personal PIN code Vendor and Payment Provider settle bills at the end of each cycle Taxis Payment Provider sends grant of payment encrypted with Vendor’s public key via SMS 5 2 Selection & Authentication Consumer’s mobile phone SIM Toolkit Application on mobile phone sends SMS with transaction information through Network Operator to Payment Provider Billing (either prepaid or at end of cycle) Mobile phone transmits grant of payment via Bluetooth to Vendor Payment Provider logs transaction and adds it to the consumer’s bill or deducts consumer’s prepaid account Encrypted grant of payment SMS over GSM Transaction Info & Public Key 3 4 Payment Provider Summing up or deducting from prepaid account 27
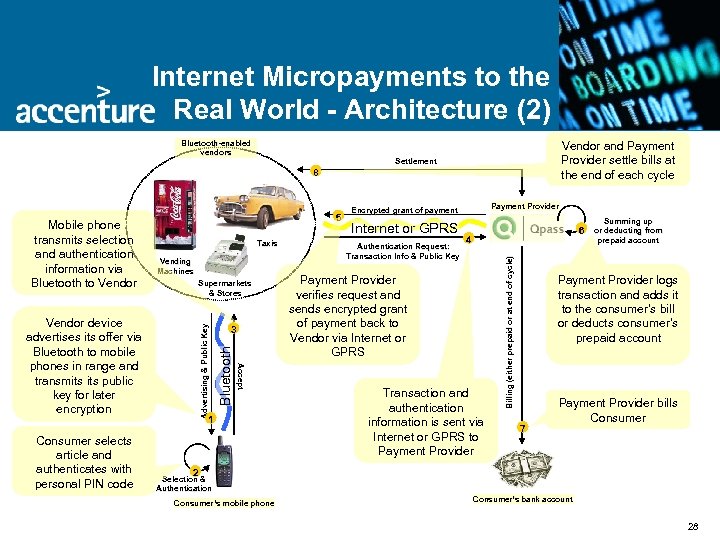
Internet Micropayments to the Real World - Architecture (2) Bluetooth-enabled vendors Vendor and Payment Provider settle bills at the end of each cycle Settlement 8 Vending Machines Supermarkets & Stores Consumer selects article and authenticates with personal PIN code Advertising & Public Key 3 Accept Vendor device advertises its offer via Bluetooth to mobile phones in range and transmits public key for later encryption 1 Payment Provider Encrypted grant of payment Internet or GPRS Authentication Request: Transaction Info & Public Key 6 4 Payment Provider verifies request and sends encrypted grant of payment back to Vendor via Internet or GPRS Transaction and authentication information is sent via Internet or GPRS to Payment Provider Billing (either prepaid or at end of cycle) Taxis Bluetooth Mobile phone transmits selection and authentication information via Bluetooth to Vendor 5 Summing up or deducting from prepaid account Payment Provider logs transaction and adds it to the consumer’s bill or deducts consumer’s prepaid account 7 Payment Provider bills Consumer 2 Selection & Authentication Consumer’s mobile phone Consumer’s bank account 28
Real World Service Portal • Imagine you can virtually meet up with a ‘new-friend’ who lives a long way away, using the Coke machine around the corner. • You select a beverage from your mobile phone's menu and type in your secret PIN code to authenticate the purchase. Subsequently, your phone prompts you to enter the name of your friend. Within seconds the vending machine connects you to a vending machine on the other side of the world where your friend is also enjoying a drink and you can both talk for free, enjoying the refreshment of your cold drinks. All you have to do is stay within 100 metres of the vending machine. • Let’s see how a real world point of sale can turn your mobile phone into a service portal. . . 29
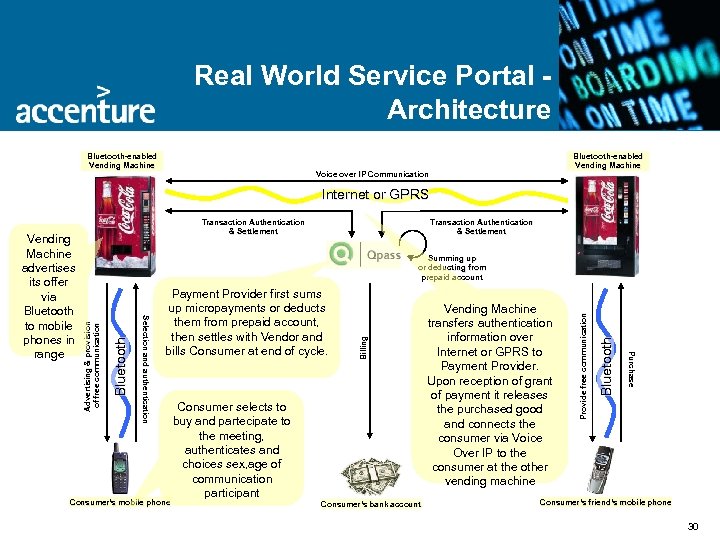
Real World Service Portal Architecture Bluetooth-enabled Vending Machine Voice over IP Communication Internet or GPRS Transaction Authentication & Settlement Consumer’s mobile phone Consumer’s bank account Bluetooth Vending Machine transfers authentication information over Internet or GPRS to Payment Provider. Upon reception of grant of payment it releases the purchased good and connects the consumer via Voice Over IP to the consumer at the other vending machine Provide free communication Consumer selects to buy and partecipate to the meeting, authenticates and choices sex, age of communication participant Billing Bluetooth Payment Provider first sums up micropayments or deducts them from prepaid account, then settles with Vendor and bills Consumer at end of cycle. Purchase Advertising & provision of free communication Summing up or deducting from prepaid account Selection and authentication Vending Machine advertises its offer via Bluetooth to mobile phones in range Transaction Authentication & Settlement Consumer’s friend’s mobile phone 30
Seminar Agenda • Accenture Presentation 15’ • Bluetooth Technology and Market overview 30’ • Bluetooth at work: u. Commerce concepts 30’ • Questions & Answers 15’ 31
Seminar Agenda • Back-up slides 32
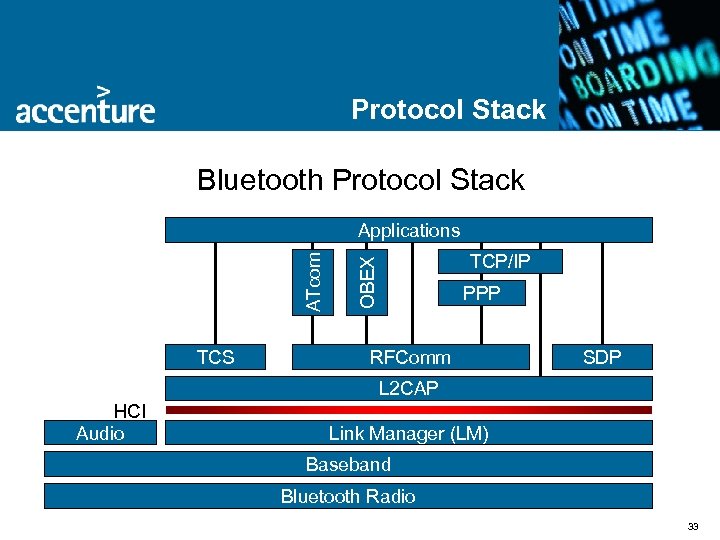
Protocol Stack Bluetooth Protocol Stack TCS TCP/IP OBEX ATcom Applications PPP RFComm SDP L 2 CAP HCI Audio Link Manager (LM) Baseband Bluetooth Radio 33
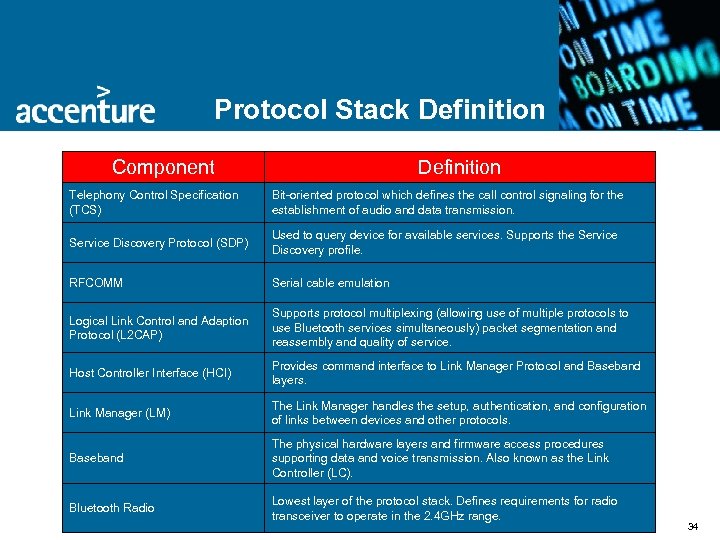
Protocol Stack Definition Component Definition Telephony Control Specification (TCS) Bit-oriented protocol which defines the call control signaling for the establishment of audio and data transmission. Service Discovery Protocol (SDP) Used to query device for available services. Supports the Service Discovery profile. RFCOMM Serial cable emulation Logical Link Control and Adaption Protocol (L 2 CAP) Supports protocol multiplexing (allowing use of multiple protocols to use Bluetooth services simultaneously) packet segmentation and reassembly and quality of service. Host Controller Interface (HCI) Provides command interface to Link Manager Protocol and Baseband layers. Link Manager (LM) The Link Manager handles the setup, authentication, and configuration of links between devices and other protocols. Baseband The physical hardware layers and firmware access procedures supporting data and voice transmission. Also known as the Link Controller (LC). Bluetooth Radio Lowest layer of the protocol stack. Defines requirements for radio transceiver to operate in the 2. 4 GHz range. 34
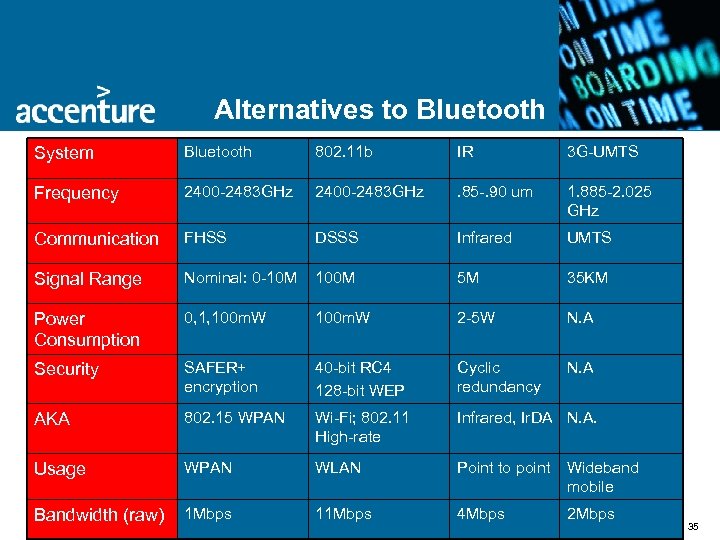
Alternatives to Bluetooth System Bluetooth 802. 11 b IR 3 G-UMTS Frequency 2400 -2483 GHz . 85 -. 90 um 1. 885 -2. 025 GHz Communication FHSS DSSS Infrared UMTS Signal Range Nominal: 0 -10 M 100 M 5 M 35 KM Power Consumption 0, 1, 100 m. W 2 -5 W N. A Security SAFER+ encryption 40 -bit RC 4 128 -bit WEP Cyclic redundancy N. A AKA 802. 15 WPAN Wi-Fi; 802. 11 High-rate Infrared, Ir. DA N. A. Usage WPAN WLAN Point to point Wideband mobile Bandwidth (raw) 1 Mbps 11 Mbps 4 Mbps 2 Mbps 35
Ad-hoc networking Piconet • 1 master, up to 7 active slaves • Up to 255 inactive slaves • All devices in a piconet hop on same pattern Scatternet • Scatternet = 2 or more connected piconets • Master or slave device can be connection • Piconets in scatternet are not sync-ed to same hopping pattern 36
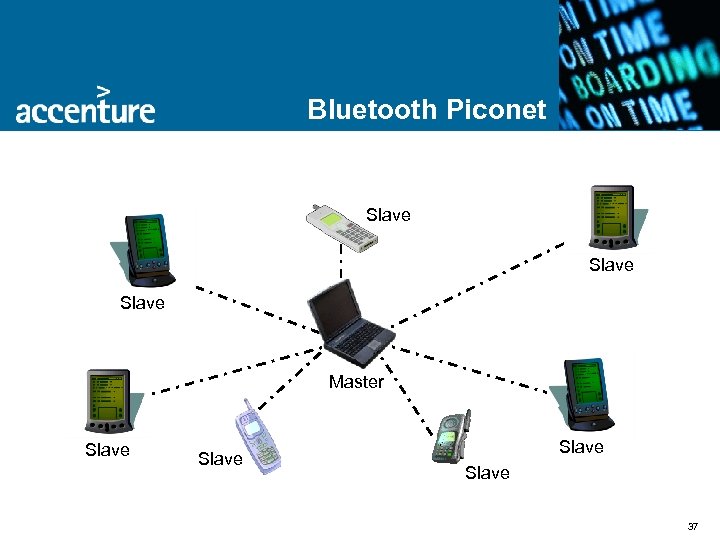
Bluetooth Piconet Slave Master Slave 37
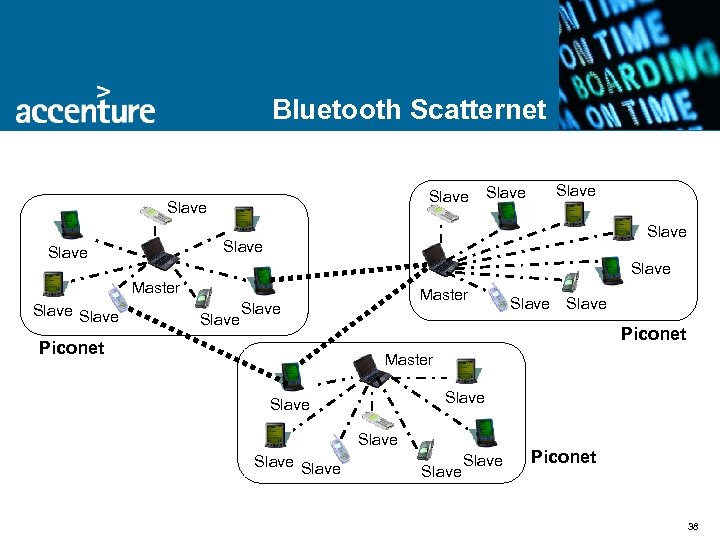
Bluetooth Scatternet Slave Slave Slave Master Slave Piconet Master Slave Slave Piconet 38
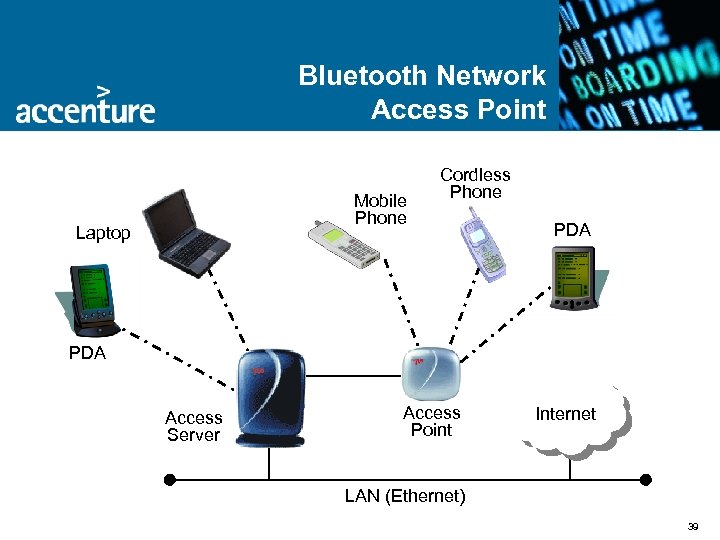
Bluetooth Network Access Point Mobile Phone Laptop Cordless Phone PDA Access Server Access Point Internet LAN (Ethernet) 39
5bb056b6fa7ce1e455f785853538c3a3.ppt