3e9057e06c820ef272d969656a15a553.ppt
- Количество слайдов: 78
Biometrics & Identity Addressing the concerns of privacy through technology Presentation to BCS/12 th April 2005 © 2005 The Generics Group AG
Biometrics & Privacy l Generics group research activities in biometrics and security l Overview of biometrics and basic model of how they work l Conventional and cryptographic modes of operation l Biometric key generation technology 2 © 2005 The Generics Group AG
Scientific Generics - Background l Cambridge based technology consultancy, research and development organisation with regional offices in US, Germany, Scandinavia and Hong Kong l Involved in the incubation of over 50 start off companies in fields ranging from: l l l Compact fuel cells Optical telecommunications Transmission of data over sound (e. g. between TV and mobile phone) Sensor devices Tracking and location technologies l Mainstay of business revenues come from fees for services consultancy activities relating to the interaction of technology with business value l Company retains a commitment to investment in commercially focused technology research activities 3 © 2005 The Generics Group AG
Background to biometrics research activities l Programme initiated in early 2001 with a view to deep integration of biometrics with private key management within a PKI with a view to realisation of the concept of I am my private key l First proof of principal demonstrator developed for iris in 2002 l Security research activities broadened in 2003 to include consideration address of full range of privacy concerns impacting on the use of biometrics within national identity cards l Second verification demonstrator developed in 2004 which verifiably reproduced 400 bit keys from third party iris test data l 2005 - current research activities focused on moving towards l l publication of test results that verify the technology creation of wider applications relating to other biometrics such as finger-print alpha product development of related security technologies incorporation as a commercial venture 4 © 2005 The Generics Group AG
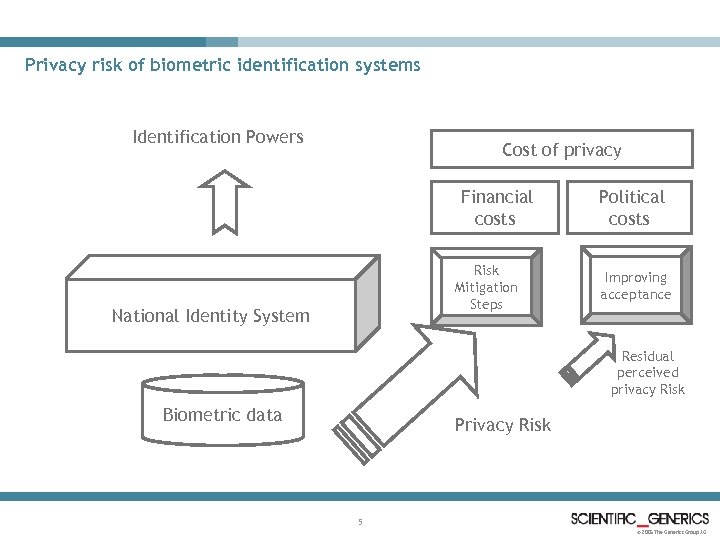
Privacy risk of biometric identification systems Identification Powers Cost of privacy Financial costs Risk Mitigation Steps National Identity System Political costs Improving acceptance Residual perceived privacy Risk Biometric data Privacy Risk 5 © 2005 The Generics Group AG
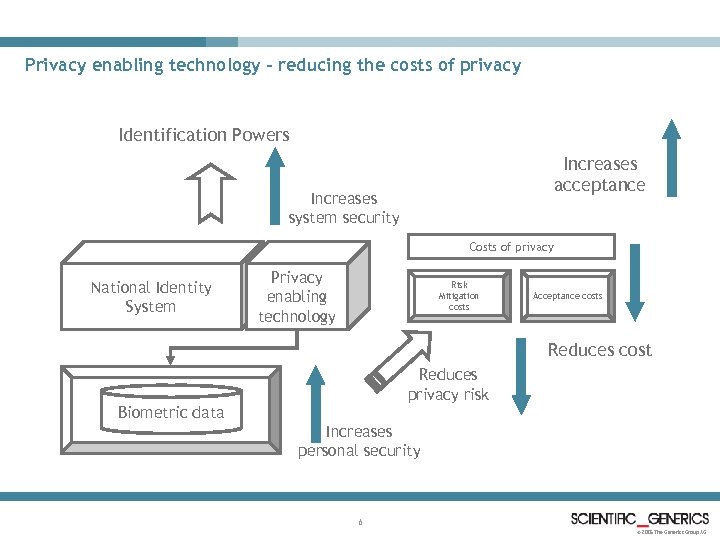
Privacy enabling technology - reducing the costs of privacy Identification Powers Increases acceptance Increases system security Costs of privacy National Identity System Privacy enabling technology Risk Mitigation costs Acceptance costs Reduces cost Reduces privacy risk Biometric data Increases personal security 6 © 2005 The Generics Group AG
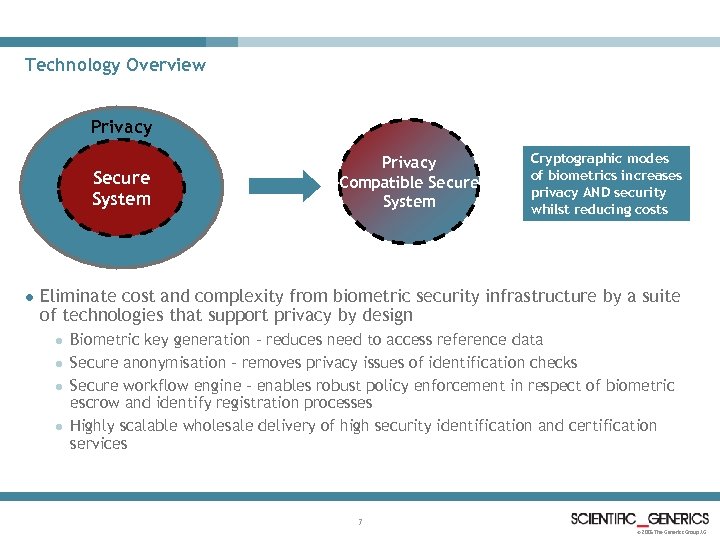
Technology Overview Privacy Secure System l Privacy Compatible Secure System Cryptographic modes of biometrics increases privacy AND security whilst reducing costs Eliminate cost and complexity from biometric security infrastructure by a suite of technologies that support privacy by design l l Biometric key generation - reduces need to access reference data Secure anonymisation - removes privacy issues of identification checks Secure workflow engine - enables robust policy enforcement in respect of biometric escrow and identify registration processes Highly scalable wholesale delivery of high security identification and certification services 7 © 2005 The Generics Group AG
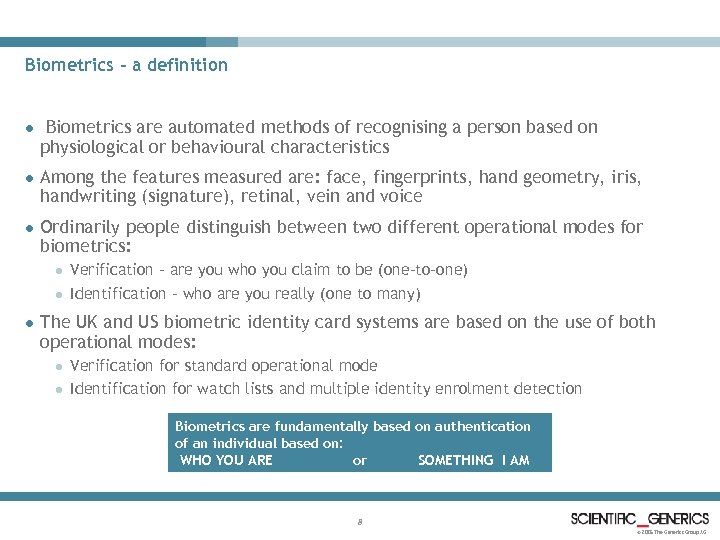
Biometrics - a definition l Biometrics are automated methods of recognising a person based on physiological or behavioural characteristics l Among the features measured are: face, fingerprints, hand geometry, iris, handwriting (signature), retinal, vein and voice l Ordinarily people distinguish between two different operational modes for biometrics: l l l Verification - are you who you claim to be (one-to-one) Identification - who are you really (one to many) The UK and US biometric identity card systems are based on the use of both operational modes: l l Verification for standard operational mode Identification for watch lists and multiple identity enrolment detection Biometrics are fundamentally based on authentication of an individual based on: WHO YOU ARE or SOMETHING I AM 8 © 2005 The Generics Group AG
Why are biometrics so compelling? l The human interface is the biggest security gap in most security systems l Authentication, rather than encryption is the major problem facing security l The aspiration of biometrics is automated recognition of identity based on the immutable properties of a person’s being The promise of direct proof of presence of the individual is the central premise of the appeal 9 © 2005 The Generics Group AG
Why are biometrics so difficult? l High quality image capture of biometrics is difficult l High performance discrimination based on biometric data is challenging l Biometric capture processes can be challenging or upsetting to users l Biometrics are not the same as passwords l Protecting biometrics against spoofing is problematic l There are competing methods of authentication that are arguably lower cost, easier to use and do not invade privacy of the person - e. g. strong passwords, RSA Secure. Id tokens, smart-card protected secrets etc The cost benefit barriers for adoption should not be under-estimated of 10 © 2005 The Generics Group AG
The biometric conundrum l Biometrics are compelling to the market - otherwise any technology that is so difficult to use would otherwise have been dropped long ago. l Biometrics are problematic - otherwise anything so compelling would have been adopted on a much wider scale than has hitherto been the case Will biometrics become a niche technology relied on in times of political insecurity and for high value applications? OR Is the mass adoption of biometrics simply a question of time? 11 © 2005 The Generics Group AG
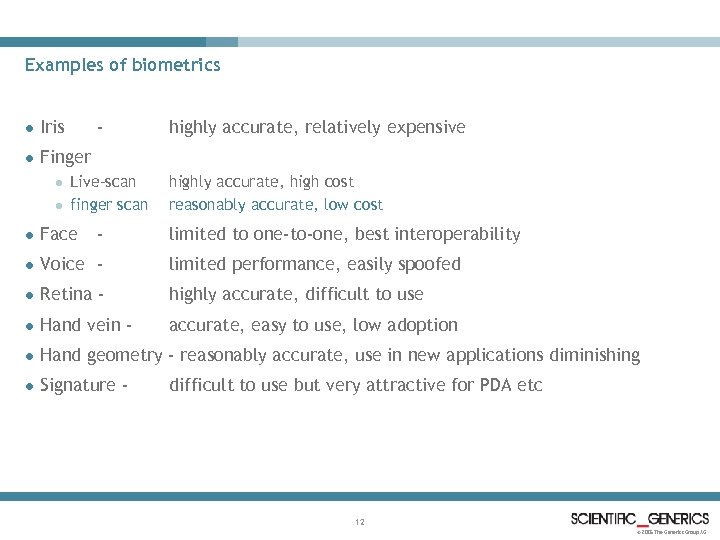
Examples of biometrics l Iris l Finger l l Live-scan finger scan - highly accurate, relatively expensive highly accurate, high cost reasonably accurate, low cost l Face limited to one-to-one, best interoperability l Voice - limited performance, easily spoofed l Retina - highly accurate, difficult to use l Hand vein - accurate, easy to use, low adoption l Hand geometry - reasonably accurate, use in new applications diminishing l Signature - difficult to use but very attractive for PDA etc 12 © 2005 The Generics Group AG
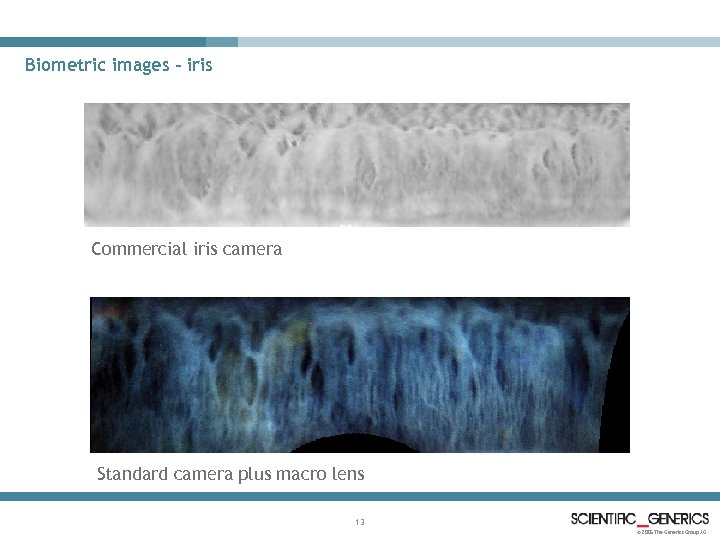
Biometric images - iris Commercial iris camera Standard camera plus macro lens 13 © 2005 The Generics Group AG
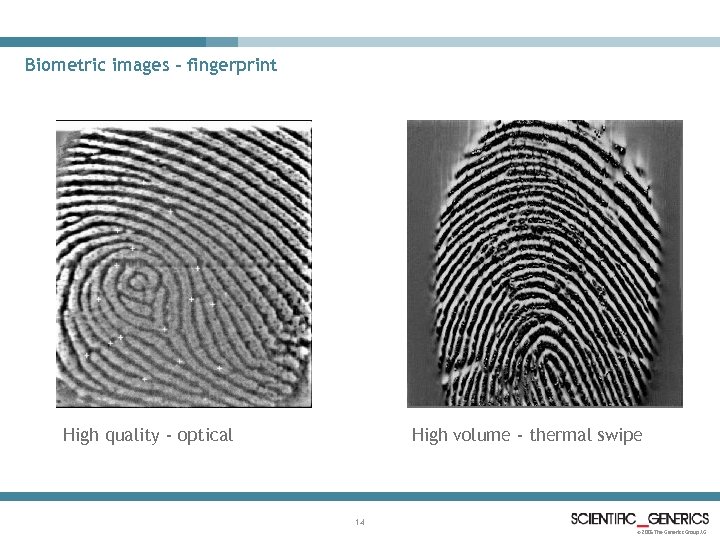
Biometric images - fingerprint High volume - thermal swipe High quality - optical 14 © 2005 The Generics Group AG
Limitations of biometrics l Performance l Cost l Security l Societal l Systems integration issues 15 © 2005 The Generics Group AG
Performance - alphabet soup l FMR - false match rate (or false accept) l FNMR - false non match rate (or false reject) l FTE - failure to enrol l Equal error rate - FMR=FNMR l ATV - ability to verify FTE * FNMR l SFMR - system false match rate l SFNMR - system false non match rate 16 © 2005 The Generics Group AG
Cost l Typical costs for high quality sensor devices (iris, finger, retina) is of the order of several thousand to several tens of thousands of dollars. l There is however also an emerging low-cost commodity tier of biometric devices that will enable most biometrics, with the possible exception of retina, to operate at price points of less than $100. l However the nature of applications compensates in that those applications which have the requirement of high throughput and high quality devices the cost tolerance for devices also tends to be higher. l For one-to-many applications such as border-control a small number of high cost devices can be used to support enrolment whilst a larger number of lower quality devices may be exploited to support verification. 17 © 2005 The Generics Group AG
Security l Security of authentication as measured by the SFMR l Biometric templates are a symmetric verification measure l Biometrics can be spoofed, if image data is stolen or captured by stealth l Mitigation of above with liveness checks l One to many matching requires central database storage. Data protection issues mandate that this is held in secure storage with high integrity, auditability and accountability of process l Security of the biometric image process environment to protect against interception l New sensor devices include use of capture specific generated nonce embedded into a trusted device as part of the defence against replay attacks 18 © 2005 The Generics Group AG
Societal factors l Public enthusiasm for national enrolment programmes! l l Who needs access to one to many matching and at what point? l l Or what? Actually most market research indicates reasonable compliance. One to many matching is required to trap multiple identity registration. There is NO other legitimate reason other than covert surveillance. Postulated conclusions l l l Required at enrolment only. Match database should be fully anonymised. ALL other checks should be one to one Highly secure mechanisms for biometric escrow, and subsequent escalation need to be in place and under the control of a trusted intermediary authority Trusted authority acts to uphold the institution of Government - but is not constituted by officers of the government. 19 © 2005 The Generics Group AG
Systems integration l Bio. API is the emerging standard l This is a framework approach supporting plug-in provider applications l Given the diversity of biometrics and the encoding regimes used this framework is highly abstract and has a light touch. l Framework is primarily focused on template based methods. l Cryptographic modes operate on a password substitution model and do not require the complexity of a framework since the integration problem is much cleaner 20 © 2005 The Generics Group AG
Other standards l ICAO l l all biometrics to be stored in full image format to support multi-vendor operability face to be stored in unencrypted format other biometrics, iris or face, to be stored using encryption protocols to be determined by n-lateral agreements for n-lateral read US led definition of ad-hoc standards - ultimately these will be moderated by the domestic mandates for privacy 21 © 2005 The Generics Group AG
Biometric modes l Conventional biometrics l l l Template matching One to one Vs one to many Local storage Vs central storage Data protection Encrypted storage/universal access Cryptographic modes l l l Repeatable number generation - biometric keys Digitally signed identity certificate Entitlement certificate Private key mode Password substitution 22 © 2005 The Generics Group AG
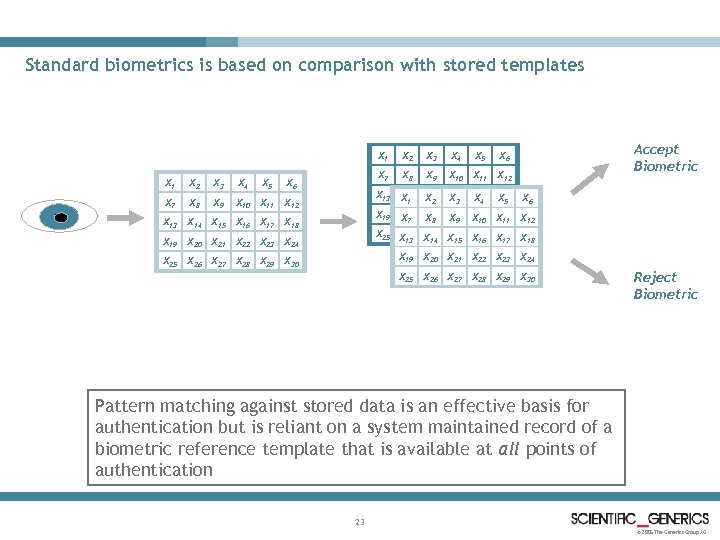
Standard biometrics is based on comparison with stored templates X 1 X 2 X 3 X 4 X 5 X 7 X 8 X 9 X 10 X 11 X 12 X 3 X 4 X 7 X 6 X 2 X 5 X 8 X 9 Accept Biometric X 6 X 10 X 11 X 12 X 13 X 14 X 15 X 16 X 17 X 18 X 1 X 2 X 3 X 4 X 5 X 6 X 19 X 20 X 21 X 22 X 23 X 24 X X 7 X 8 X 9 X 10 X 11 12 X 13 X 14 X 15 X 16 X 17 X 18 X 19 X 20 X 21 X 22 X 23 X 24 X 25 X 26 X 27 X 28 X 29 X 30 X X X 13 14 15 16 17 18 X 25 X 26 X 27 X 28 X 29 X 30 X 19 X 20 X 21 X 22 X 23 X 24 X 25 X 26 X 27 X 28 X 29 X 30 Reject Biometric Pattern matching against stored data is an effective basis for authentication but is reliant on a system maintained record of a biometric reference template that is available at all points of authentication 23 © 2005 The Generics Group AG
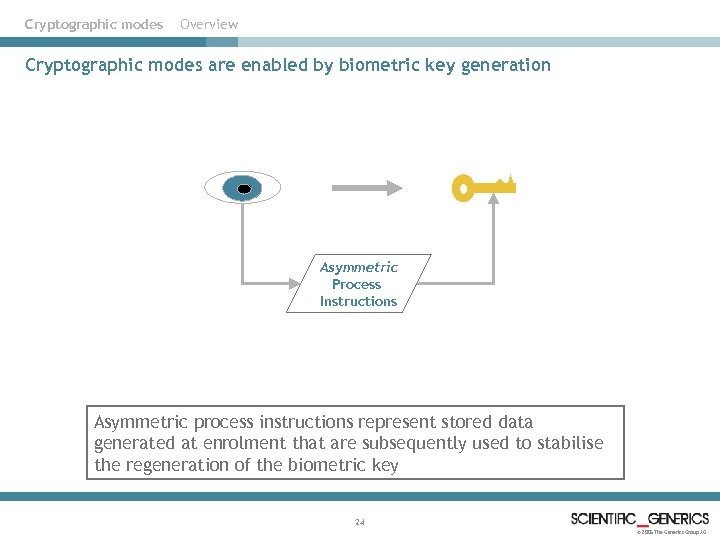
Cryptographic modes Overview Cryptographic modes are enabled by biometric key generation Asymmetric Process Instructions Asymmetric process instructions represent stored data generated at enrolment that are subsequently used to stabilise the regeneration of the biometric key 24 © 2005 The Generics Group AG
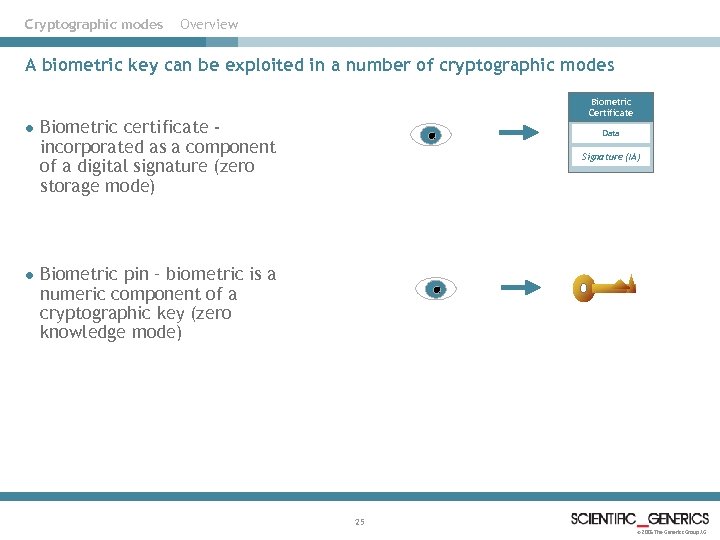
Cryptographic modes Overview A biometric key can be exploited in a number of cryptographic modes l l Biometric Certificate Biometric certificate incorporated as a component of a digital signature (zero storage mode) Data Signature (IA) Biometric pin – biometric is a numeric component of a cryptographic key (zero knowledge mode) 25 © 2005 The Generics Group AG
Biometric certificates – zero storage mode l Biometric number is a stable integer value and can therefore be used as a component of signing data for a digital signature l The signing data can include other data attributes that can be bound to a biometric under the security jurisdiction of the private key that is used to generate the signature l The combination of digital signature and associated data is referred to as a biometric certificate since it contains a certified assertion of the binding between a biometric identity and related information l The security of the resultant document is based entirely on a single principal PKI key pair – i. e. protection of the private key used at issuance and trusted distribution of the public key that is used at verification l The biometric data does not contain any security sensitive data. It can be stored openly in plain-text format and does not require secure storage. This is a major driver of cost reduction as well as privacy. 26 © 2005 The Generics Group AG
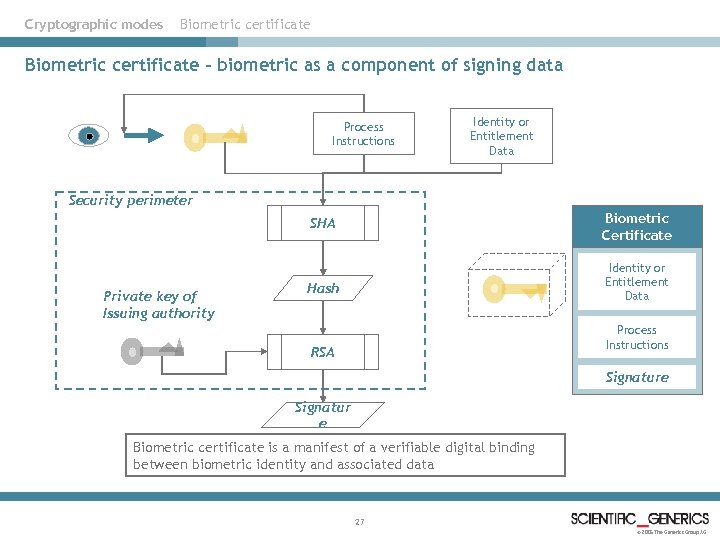
Cryptographic modes Biometric certificate – biometric as a component of signing data Process Instructions Identity or Entitlement Data Security perimeter Biometric Certificate SHA Private key of Issuing authority Identity or Entitlement Data Hash Process Instructions RSA Signature Signatur e Biometric certificate is a manifest of a verifiable digital binding between biometric identity and associated data 27 © 2005 The Generics Group AG
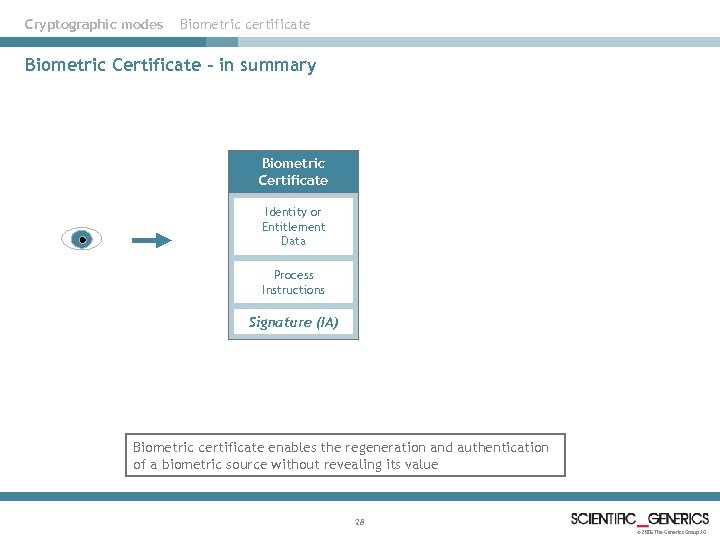
Cryptographic modes Biometric certificate Biometric Certificate – in summary Biometric Certificate Identity or Entitlement Data Process Instructions Signature (IA) Biometric certificate enables the regeneration and authentication of a biometric source without revealing its value 28 © 2005 The Generics Group AG
Cryptographic modes Biometric certificates - applications l Public identity certificate – e. g. ID card l Anonymous Entitlement certificate – e. g. benefits entitlement card l Anonymous identity certificate l Biometric extension to public key certificate 29 © 2005 The Generics Group AG
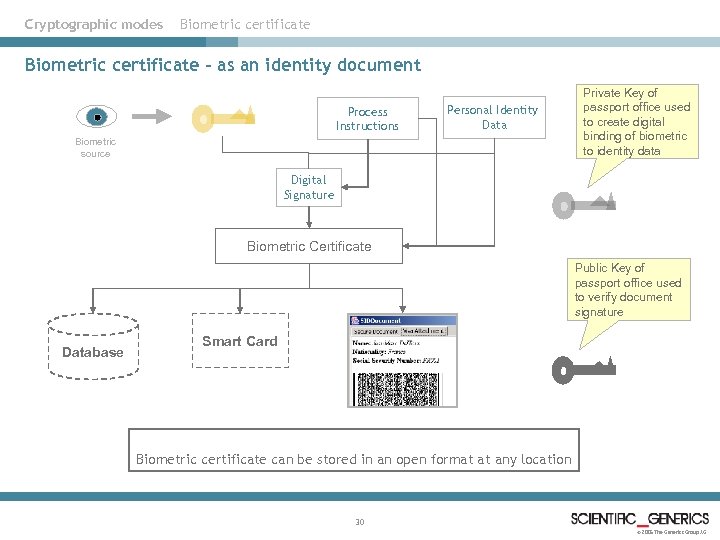
Cryptographic modes Biometric certificate – as an identity document Process Instructions Personal Identity Data Biometric source Private Key of passport office used to create digital binding of biometric to identity data Digital Signature Biometric Certificate Public Key of passport office used to verify document signature Database Smart Card Biometric certificate can be stored in an open format at any location 30 © 2005 The Generics Group AG
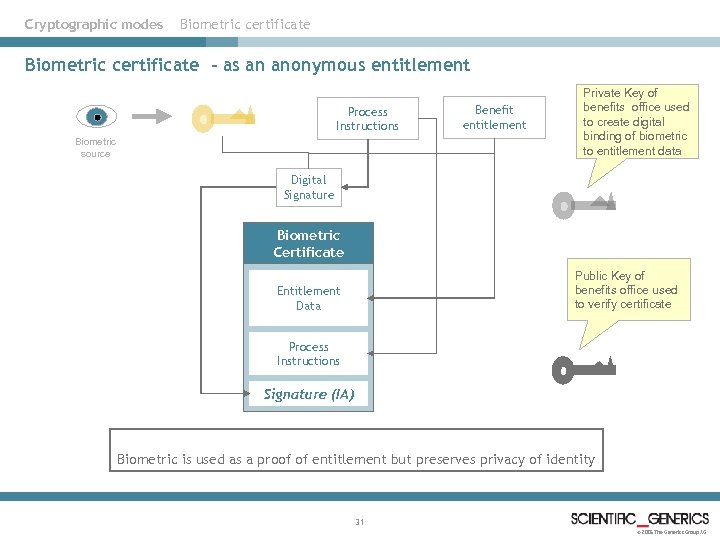
Cryptographic modes Biometric certificate - as an anonymous entitlement Process Instructions Biometric source Benefit entitlement Private Key of benefits office used to create digital binding of biometric to entitlement data Digital Signature Biometric Certificate Public Key of benefits office used to verify certificate Entitlement Data Process Instructions Signature (IA) Biometric is used as a proof of entitlement but preserves privacy of identity 31 © 2005 The Generics Group AG
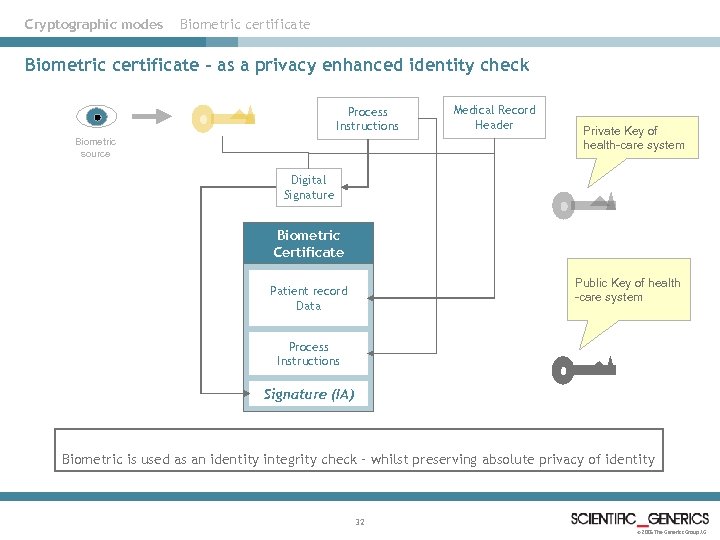
Cryptographic modes Biometric certificate – as a privacy enhanced identity check Process Instructions Biometric source Medical Record Header Private Key of health-care system Digital Signature Biometric Certificate Public Key of health -care system Patient record Data Process Instructions Signature (IA) Biometric is used as an identity integrity check – whilst preserving absolute privacy of identity 32 © 2005 The Generics Group AG
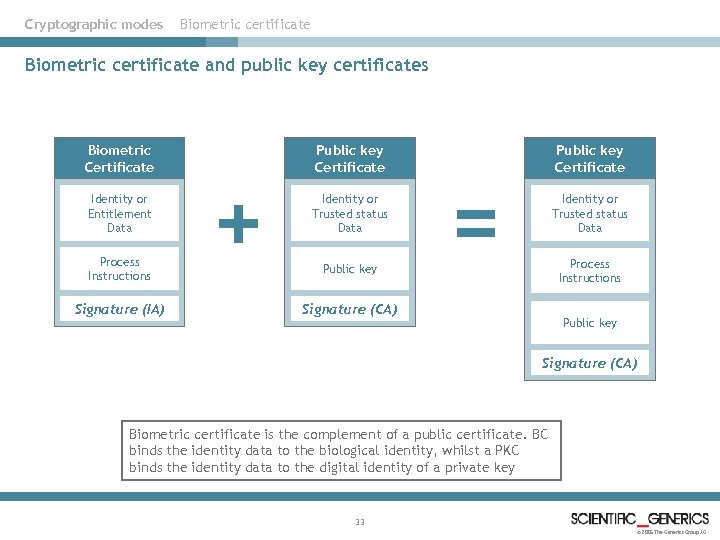
Cryptographic modes Biometric certificate and public key certificates Biometric Certificate Identity or Entitlement Data Process Instructions Signature (IA) + Public key Certificate Identity or Trusted status Data Public key Certificate = Identity or Trusted status Data Process Instructions Signature (CA) Public key Signature (CA) Biometric certificate is the complement of a public certificate. BC binds the identity data to the biological identity, whilst a PKC binds the identity data to the digital identity of a private key 33 © 2005 The Generics Group AG
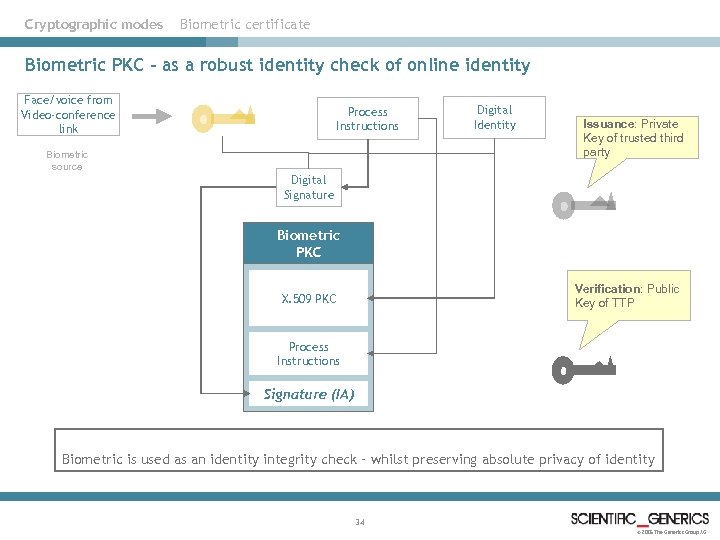
Cryptographic modes Biometric certificate Biometric PKC – as a robust identity check of online identity Face/voice from Video-conference link Process Instructions Biometric source Digital Identity Issuance: Private Key of trusted third party Digital Signature Biometric PKC Verification: Public Key of TTP X. 509 PKC Process Instructions Signature (IA) Biometric is used as an identity integrity check – whilst preserving absolute privacy of identity 34 © 2005 The Generics Group AG
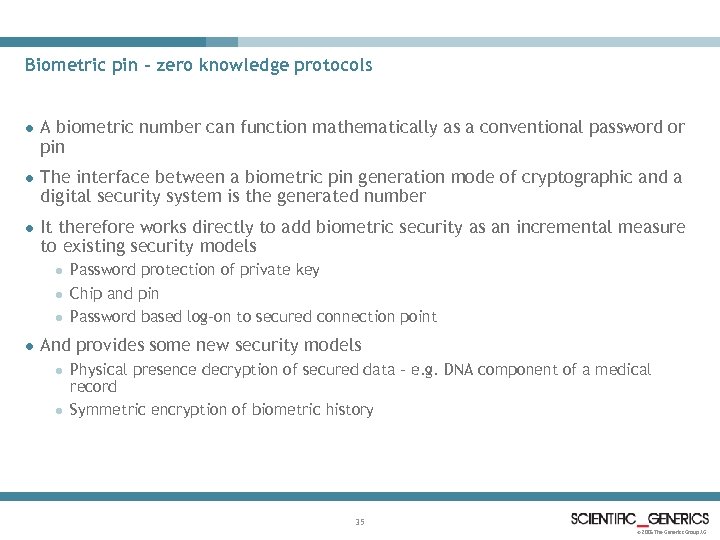
Biometric pin – zero knowledge protocols l A biometric number can function mathematically as a conventional password or pin l The interface between a biometric pin generation mode of cryptographic and a digital security system is the generated number l It therefore works directly to add biometric security as an incremental measure to existing security models l l Password protection of private key Chip and pin Password based log-on to secured connection point And provides some new security models l l Physical presence decryption of secured data – e. g. DNA component of a medical record Symmetric encryption of biometric history 35 © 2005 The Generics Group AG
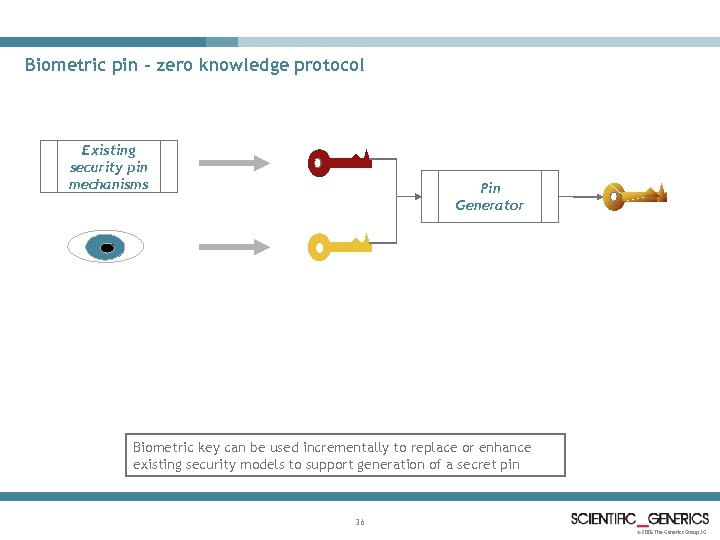
Biometric pin – zero knowledge protocol Existing security pin mechanisms Pin Generator Biometric key can be used incrementally to replace or enhance existing security models to support generation of a secret pin 36 © 2005 The Generics Group AG
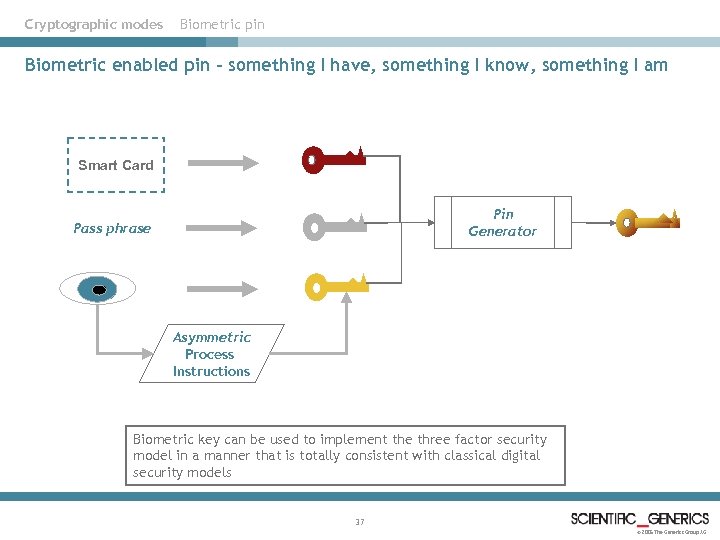
Cryptographic modes Biometric pin Biometric enabled pin – something I have, something I know, something I am Smart Card Pin Generator Pass phrase Asymmetric Process Instructions Biometric key can be used to implement the three factor security model in a manner that is totally consistent with classical digital security models 37 © 2005 The Generics Group AG
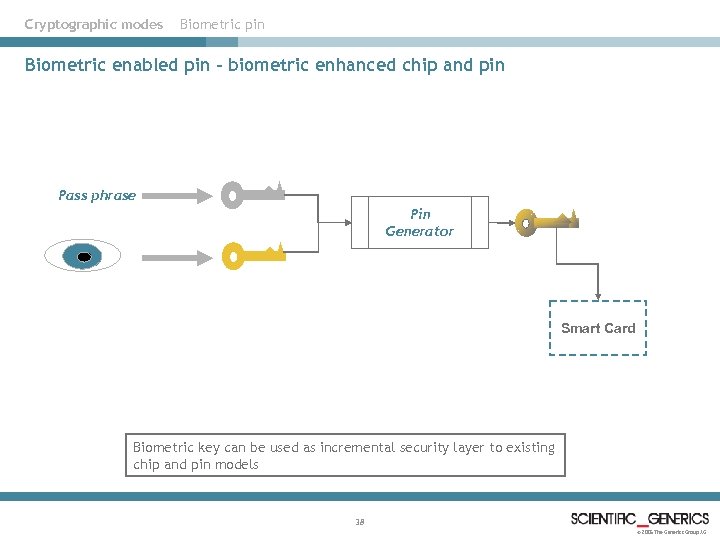
Cryptographic modes Biometric pin Biometric enabled pin – biometric enhanced chip and pin Pass phrase Pin Generator Smart Card Biometric key can be used as incremental security layer to existing chip and pin models 38 © 2005 The Generics Group AG
Biometric pin – in summary Biometric key that is used as a component of a generated PIN allows biometrics to be used as a replacement or enhancement to any existing password enabled application 39 © 2005 The Generics Group AG
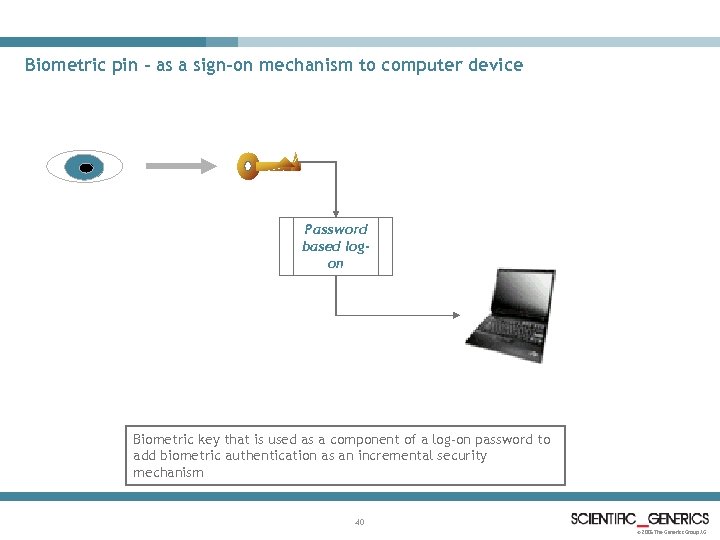
Biometric pin – as a sign-on mechanism to computer device Password based logon Biometric key that is used as a component of a log-on password to add biometric authentication as an incremental security mechanism 40 © 2005 The Generics Group AG
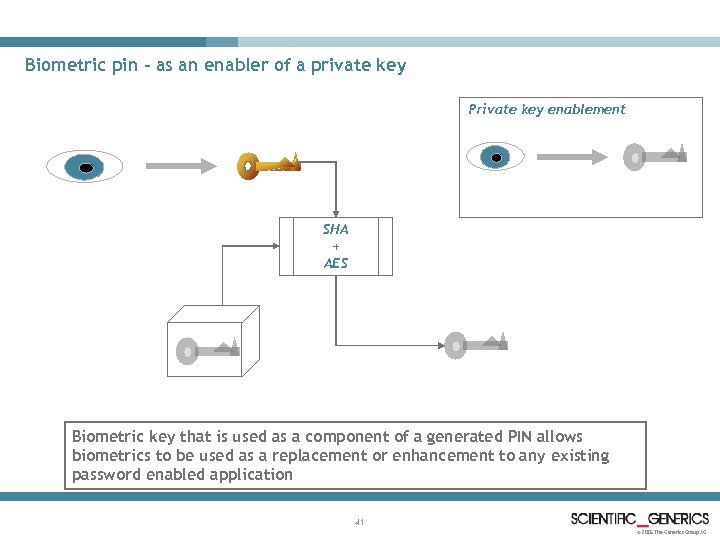
Biometric pin – as an enabler of a private key Private key enablement SHA + AES Biometric key that is used as a component of a generated PIN allows biometrics to be used as a replacement or enhancement to any existing password enabled application 41 © 2005 The Generics Group AG
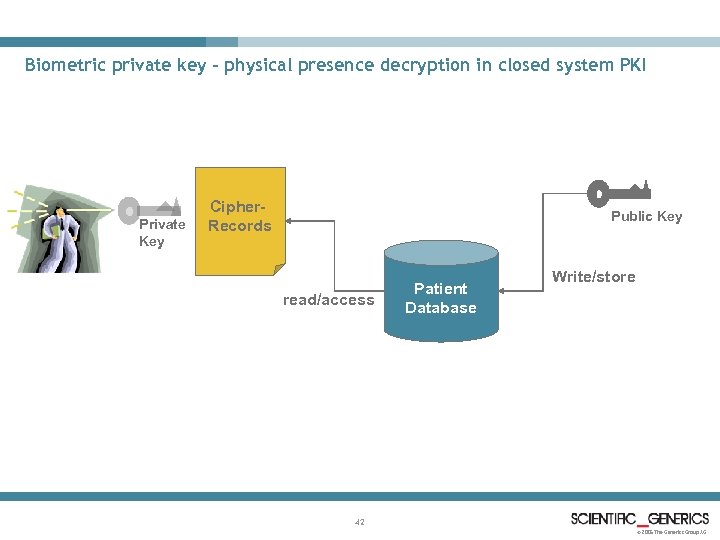
Biometric private key – physical presence decryption in closed system PKI Private Key Cipher. Records Public Key read/access Patient Database Write/store 42 © 2005 The Generics Group AG
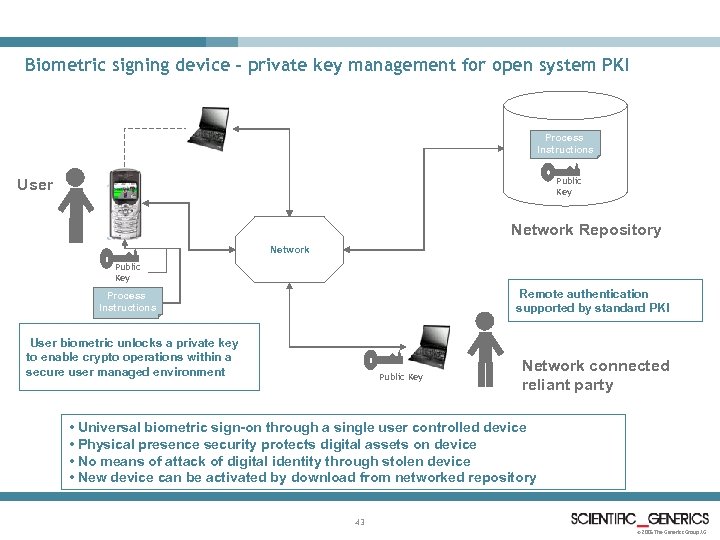
Biometric signing device – private key management for open system PKI Process Instructions Public Key User Network Repository Network Public Key Remote authentication supported by standard PKI Process Instructions User biometric unlocks a private key to enable crypto operations within a secure user managed environment Public Key Network connected reliant party • Universal biometric sign-on through a single user controlled device • Physical presence security protects digital assets on device • No means of attack of digital identity through stolen device • New device can be activated by download from networked repository 43 © 2005 The Generics Group AG
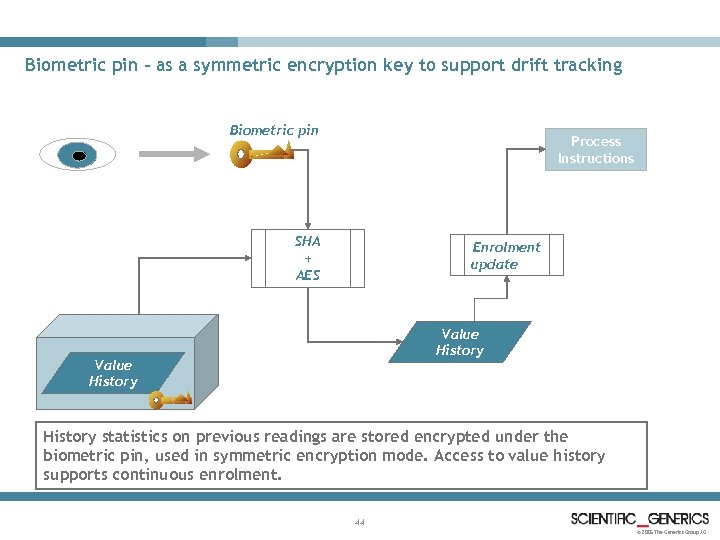
Biometric pin – as a symmetric encryption key to support drift tracking Biometric pin Process Instructions SHA + AES Enrolment update Value History statistics on previous readings are stored encrypted under the biometric pin, used in symmetric encryption mode. Access to value history supports continuous enrolment. 44 © 2005 The Generics Group AG
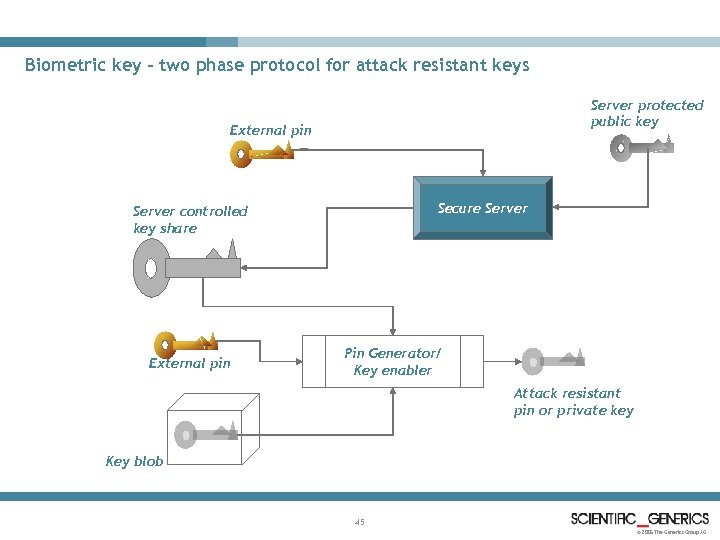
Biometric key – two phase protocol for attack resistant keys Server protected public key External pin Secure Server controlled key share External pin Pin Generator/ Key enabler Attack resistant pin or private key Key blob 45 © 2005 The Generics Group AG
Technology overview for biometric key generation 46 © 2005 The Generics Group AG
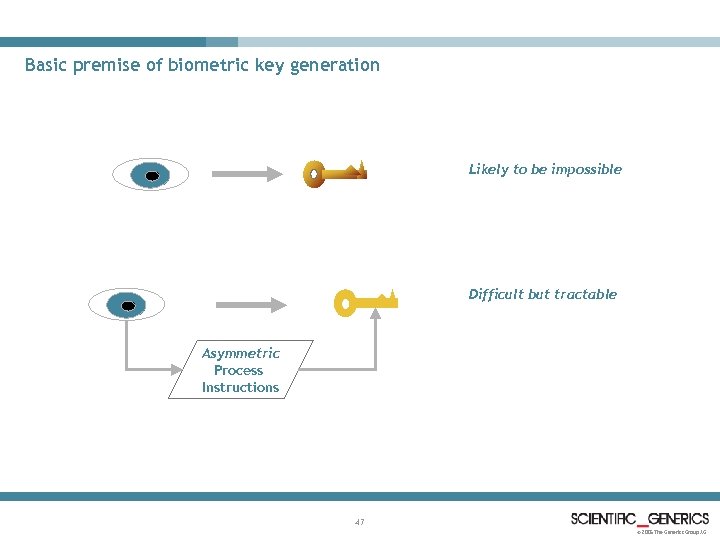
Basic premise of biometric key generation Likely to be impossible Difficult but tractable Asymmetric Process Instructions 47 © 2005 The Generics Group AG
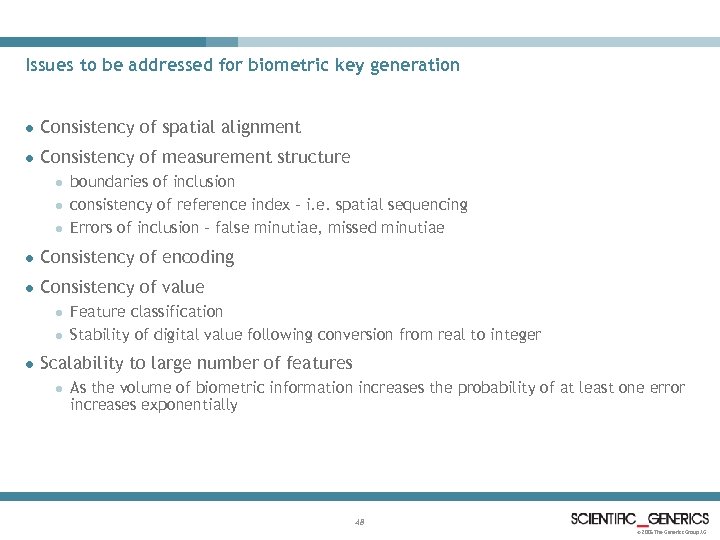
Issues to be addressed for biometric key generation l Consistency of spatial alignment l Consistency of measurement structure l l l boundaries of inclusion consistency of reference index – i. e. spatial sequencing Errors of inclusion – false minutiae, missed minutiae l Consistency of encoding l Consistency of value l l l Feature classification Stability of digital value following conversion from real to integer Scalability to large number of features l As the volume of biometric information increases the probability of at least one error increases exponentially 48 © 2005 The Generics Group AG
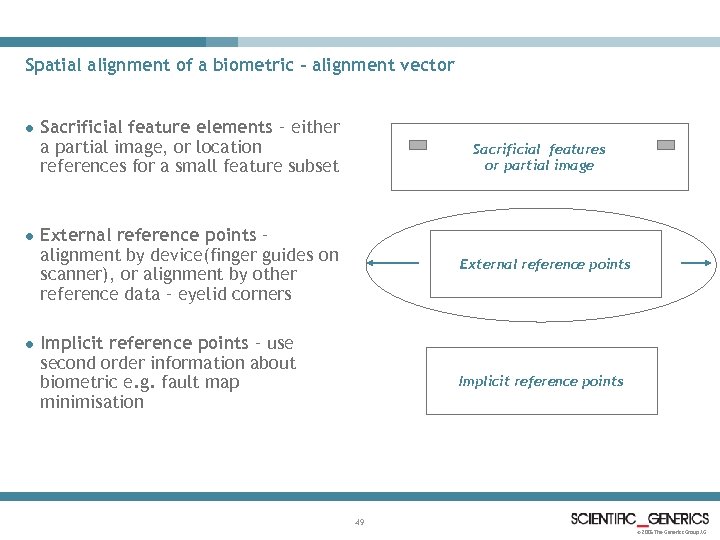
Spatial alignment of a biometric – alignment vector l l l Sacrificial feature elements – either a partial image, or location references for a small feature subset Sacrificial features or partial image External reference points – alignment by device(finger guides on scanner), or alignment by other reference data – eyelid corners External reference points Implicit reference points – use second order information about biometric e. g. fault map minimisation Implicit reference points 49 © 2005 The Generics Group AG
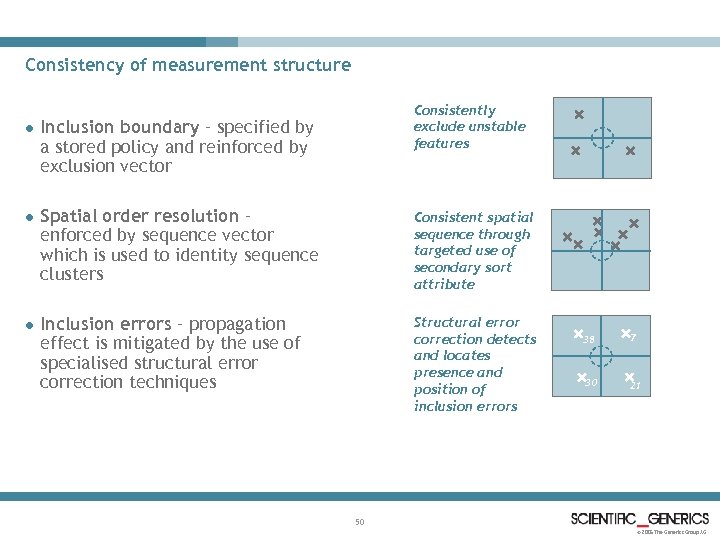
Consistency of measurement structure Consistently exclude unstable features l Inclusion boundary – specified by a stored policy and reinforced by exclusion vector l Spatial order resolution – enforced by sequence vector which is used to identity sequence clusters Consistent spatial sequence through targeted use of secondary sort attribute l Inclusion errors – propagation effect is mitigated by the use of specialised structural error correction techniques Structural error correction detects and locates presence and position of inclusion errors 38 7 30 21 50 © 2005 The Generics Group AG
Configuration of encoders l Selection of encoders – e. g. selection of wavelet function and secondary properties such as scale, orientation l Spatial variation of encoders – different elements of the biometrics may be configured separately so as to maximise information extracted l Typical examples for iris: l l Grid resolution of biometric surface Selection of encoder, texture, intensity gradient, normalised intensity l Configuration is dynamically optimised at enrolment and once optimised is remembered in the form of stored configuration parameters l Configuration instructions provide the formal basis of interaction between generic enrolment processes and plug-in encoders l Optimisation models will typically explore the configuration space of the enabled encoders 51 © 2005 The Generics Group AG
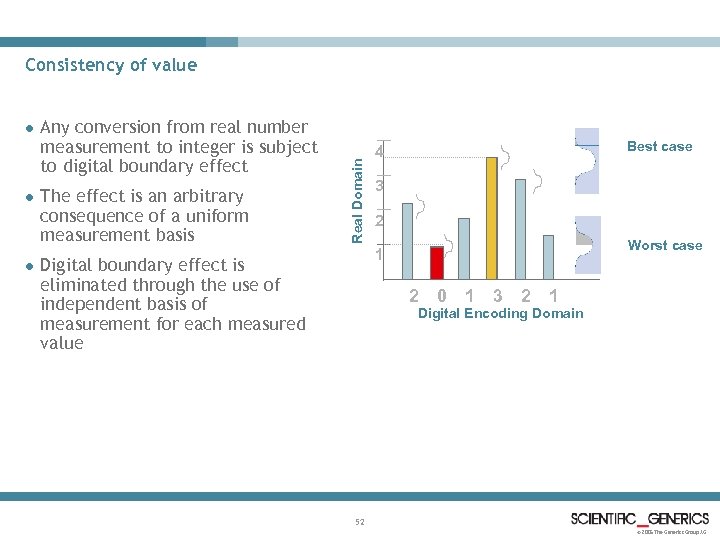
l l l Any conversion from real number measurement to integer is subject to digital boundary effect The effect is an arbitrary consequence of a uniform measurement basis Real Domain Consistency of value Best case 4 3 2 Worst case 1 Digital boundary effect is eliminated through the use of independent basis of measurement for each measured value 2 0 1 3 2 1 Digital Encoding Domain 52 © 2005 The Generics Group AG
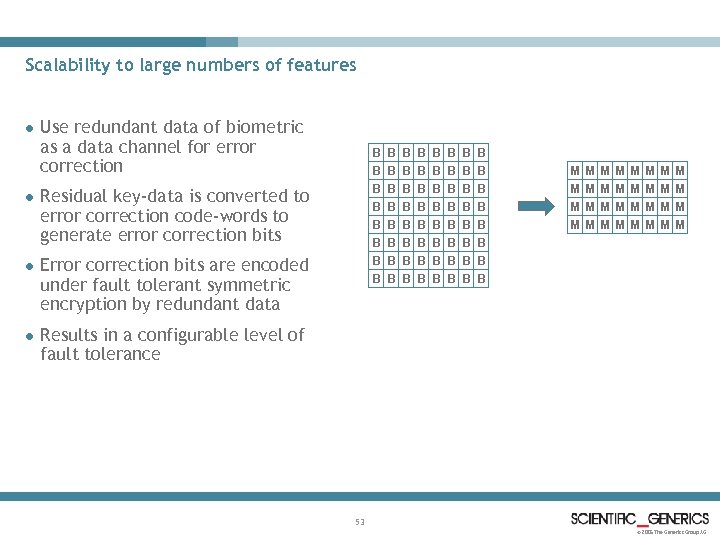
Scalability to large numbers of features l l Use redundant data of biometric as a data channel for error correction B B B B Residual key-data is converted to error correction code-words to generate error correction bits l Error correction bits are encoded under fault tolerant symmetric encryption by redundant data l B B B B B B B B B B B B B M M M M M M M M B B B Results in a configurable level of fault tolerance 53 © 2005 The Generics Group AG
Value stabilisation in detail l Exploration of the digital boundary effect reveals it to be an arbitrary property of an unnecessarily constrained measurement basis l The key to addressing the digital boundary effect is in adaptive customisation of the measurement axis on a per-feature basis l This supports minimisation of element faults that arise from digital boundary noise l The limitations on effectiveness of the technique derive from statistical analysis of offset patterns in data-encoding schemes where over-sampling has been applied. l In this situation the property of asymmetry is compromised because analysis of the offsets provides better than random predictability of where edge transitions occur 54 © 2005 The Generics Group AG
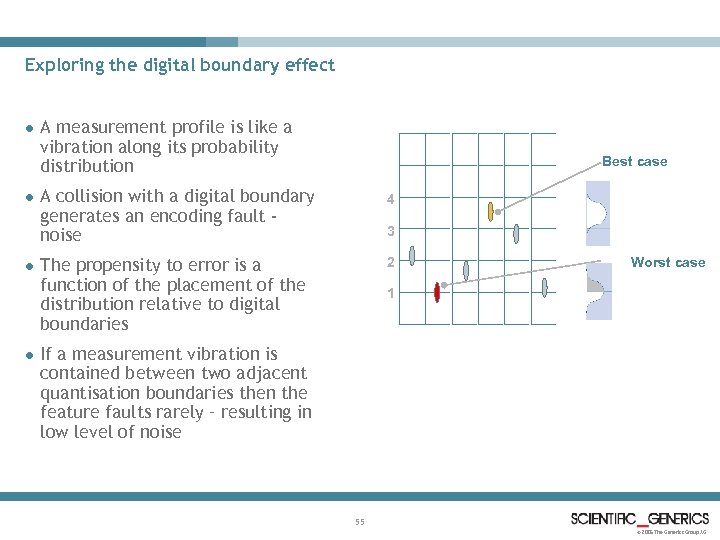
Exploring the digital boundary effect l l A measurement profile is like a vibration along its probability distribution Best case A collision with a digital boundary generates an encoding fault noise 4 The propensity to error is a function of the placement of the distribution relative to digital boundaries 2 3 Worst case 1 If a measurement vibration is contained between two adjacent quantisation boundaries then the feature faults rarely – resulting in low level of noise 55 © 2005 The Generics Group AG
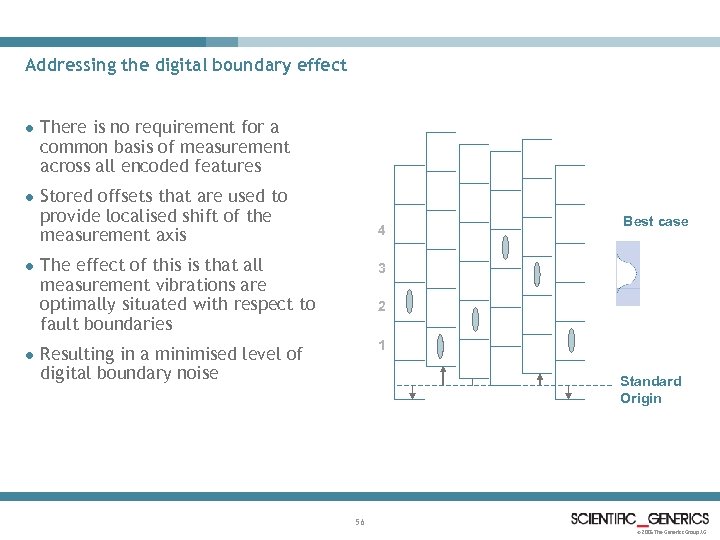
Addressing the digital boundary effect l There is no requirement for a common basis of measurement across all encoded features l Stored offsets that are used to provide localised shift of the measurement axis l l 4 The effect of this is that all measurement vibrations are optimally situated with respect to fault boundaries 3 Resulting in a minimised level of digital boundary noise Best case 1 2 Standard Origin 56 © 2005 The Generics Group AG
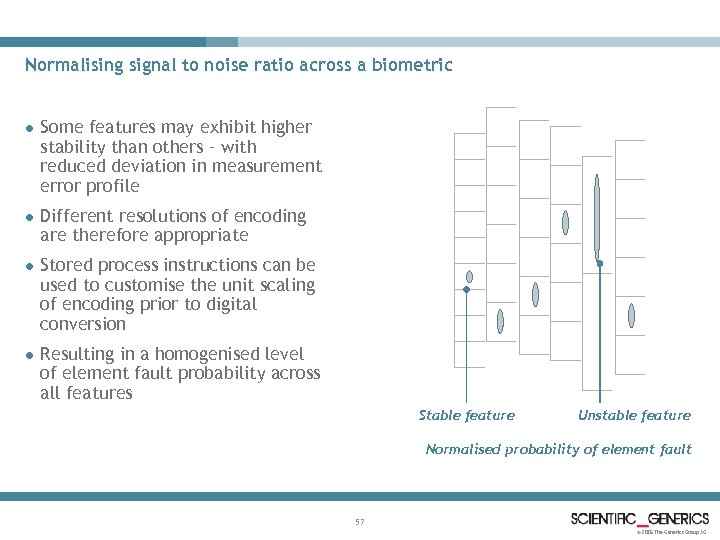
Normalising signal to noise ratio across a biometric l Some features may exhibit higher stability than others – with reduced deviation in measurement error profile l Different resolutions of encoding are therefore appropriate l Stored process instructions can be used to customise the unit scaling of encoding prior to digital conversion l Resulting in a homogenised level of element fault probability across all features Stable feature Unstable feature Normalised probability of element fault 57 © 2005 The Generics Group AG
Error correction – in detail 58 © 2005 The Generics Group AG
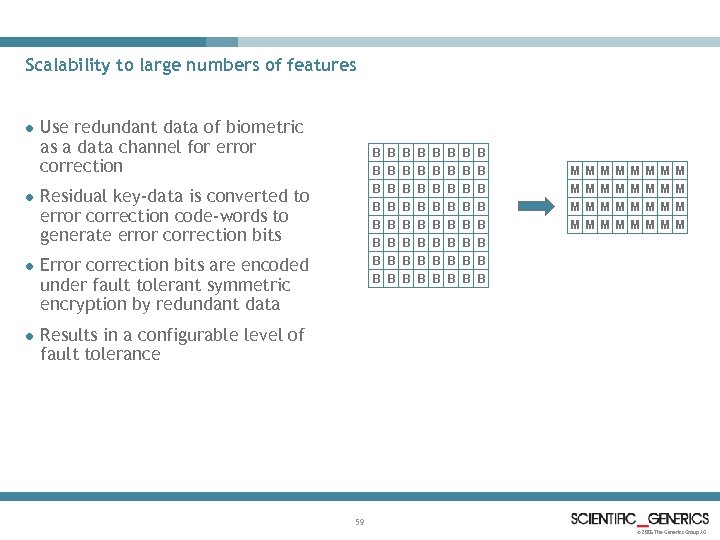
Scalability to large numbers of features l l Use redundant data of biometric as a data channel for error correction B B B B Residual key-data is converted to error correction code-words to generate error correction bits l Error correction bits are encoded under fault tolerant symmetric encryption by redundant data l B B B B B B B B B B B B B M M M M M M M M B B B Results in a configurable level of fault tolerance 59 © 2005 The Generics Group AG
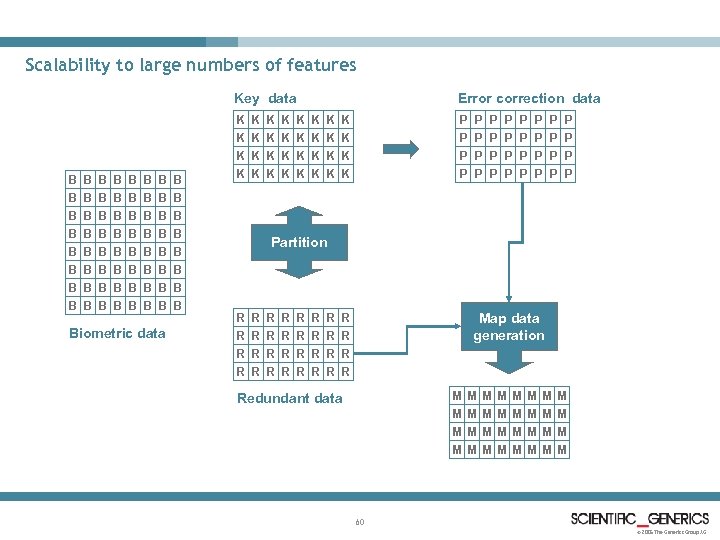
Scalability to large numbers of features Key data K K K K B B B B B B B B B B B B B B B B Biometric data Error correction data P P P P K K K K K K P P P P P P Partition R R R R R R R Map data generation R R M M Redundant data M M M M M M M 60 © 2005 The Generics Group AG
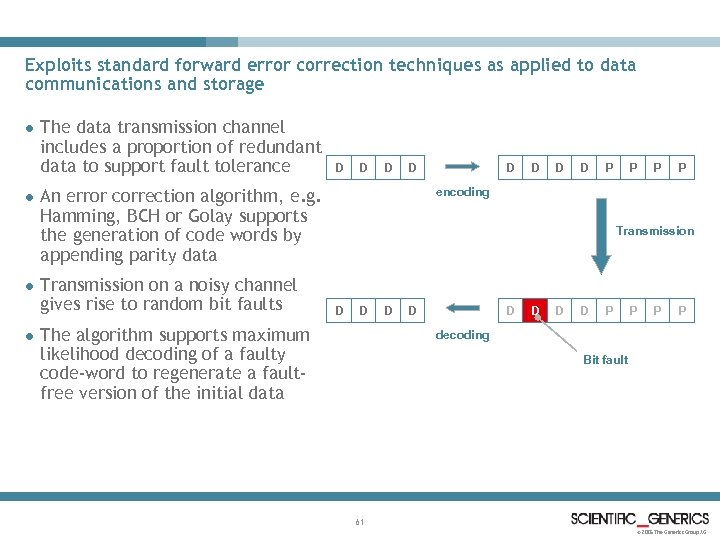
Exploits standard forward error correction techniques as applied to data communications and storage l l The data transmission channel includes a proportion of redundant data to support fault tolerance D D D P P encoding An error correction algorithm, e. g. Hamming, BCH or Golay supports the generation of code words by appending parity data Transmission on a noisy channel gives rise to random bit faults D D Transmission D D The algorithm supports maximum likelihood decoding of a faulty code-word to regenerate a faultfree version of the initial data D D D P P decoding Bit fault 61 © 2005 The Generics Group AG
Enrolment steps for error correction l Partition the biometric data into key-data (k-data) and redundant data (r-data) l Decompose the key-data into error correction code words according to the configured algorithm l Apply the configured algorithm to generate the required error correction parity data for each code-word l Recover all of the generated parity data as an array of binary data (p-data) l Apply binary mapping function to store the P-data, transformed under R-data to generate the mapping data M-data l Place the M-data within the storage unit for stored process instructions 62 © 2005 The Generics Group AG
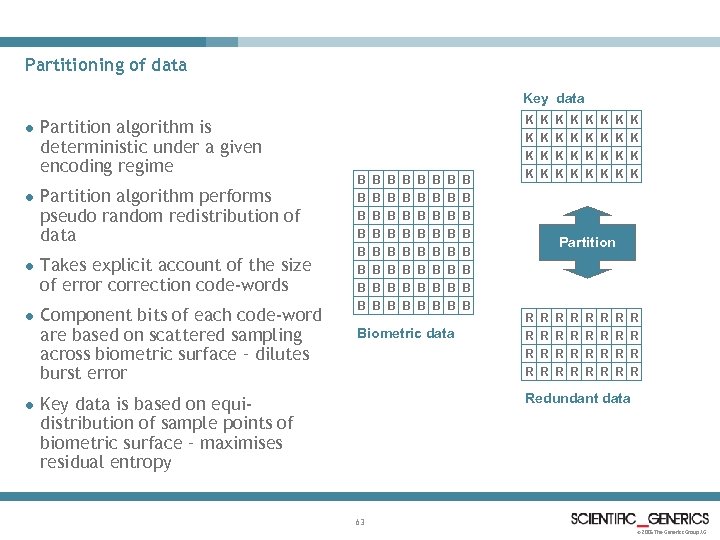
Partitioning of data Key data l l Partition algorithm is deterministic under a given encoding regime Partition algorithm performs pseudo random redistribution of data l Takes explicit account of the size of error correction code-words l Component bits of each code-word are based on scattered sampling across biometric surface – dilutes burst error l K K K K B B B B B B B B B B B B B B B B Biometric data K K K K K K Partition R R R R R R R R Redundant data Key data is based on equidistribution of sample points of biometric surface – maximises residual entropy 63 © 2005 The Generics Group AG
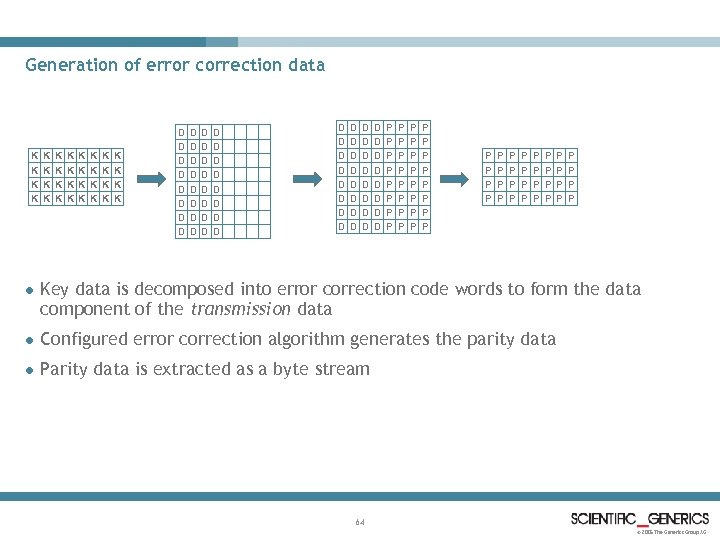
Generation of error correction data K K K K K K K K D D D D D D D D D D D D D D D D P P P P P P P P P P P P P P P P l Key data is decomposed into error correction code words to form the data component of the transmission data l Configured error correction algorithm generates the parity data l Parity data is extracted as a byte stream 64 © 2005 The Generics Group AG
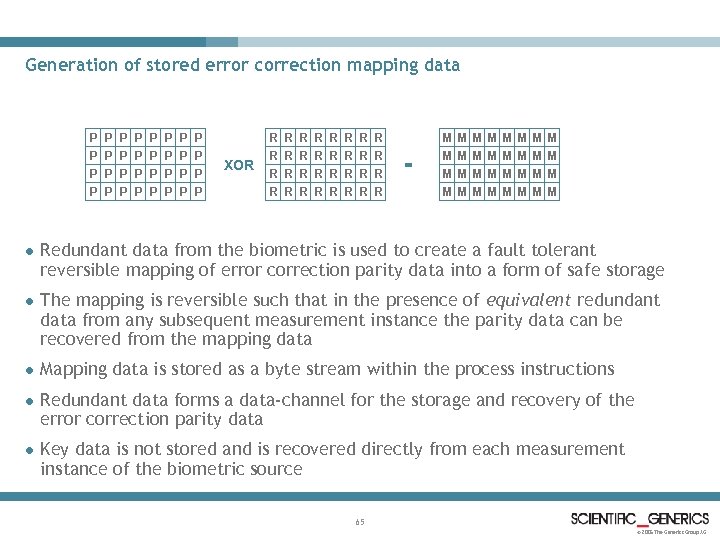
Generation of stored error correction mapping data P P P P P P P P XOR R R R R R R R R = M M M M M M M M l Redundant data from the biometric is used to create a fault tolerant reversible mapping of error correction parity data into a form of safe storage l The mapping is reversible such that in the presence of equivalent redundant data from any subsequent measurement instance the parity data can be recovered from the mapping data l Mapping data is stored as a byte stream within the process instructions l Redundant data forms a data-channel for the storage and recovery of the error correction parity data l Key data is not stored and is recovered directly from each measurement instance of the biometric source 65 © 2005 The Generics Group AG
Application of stored mapping data to apply error correction to biometric key l Partition the biometric into K-Data and R-Data using the same algorithm as applied in enrolment l Read M-Data from the process instructions l Recover P-Data by applying the inverse mapping of M-Data under R-Data l Decompose K-data into error correction code words as at enrolment l Populate the parity data of each code word from the recovered P-Data l Apply the error correction algorithm for each code word l Recover K-data as the error corrected data component of each code word 66 © 2005 The Generics Group AG
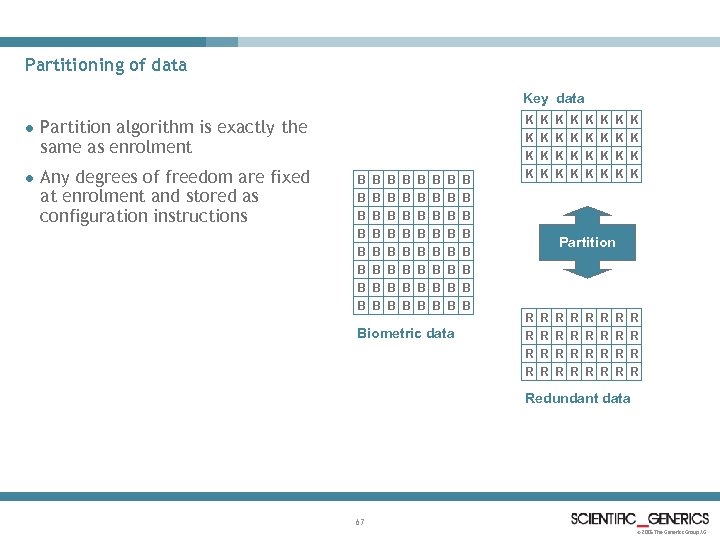
Partitioning of data Key data l l Any degrees of freedom are fixed at enrolment and stored as configuration instructions K K K K Partition algorithm is exactly the same as enrolment B B B B B B B B B B B B B B B B Biometric data K K K K K K Partition R R R R R R R R Redundant data 67 © 2005 The Generics Group AG
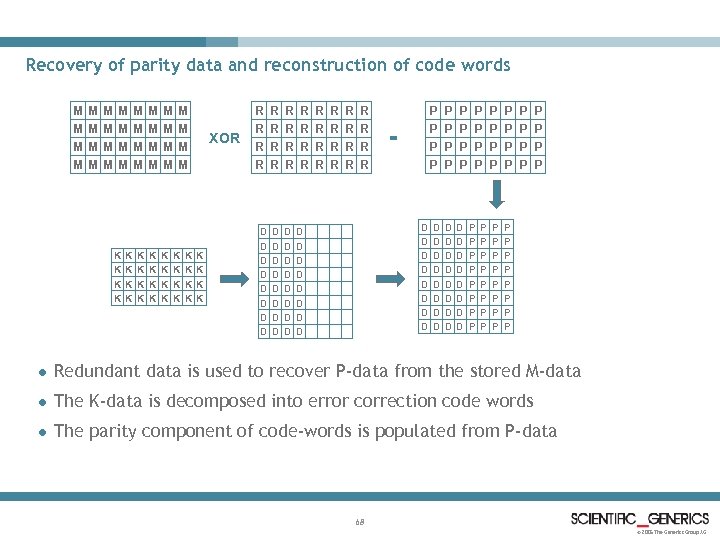
Recovery of parity data and reconstruction of code words M M M M XOR M M M M K K K K K K K K R R R R R R R R D D D D D D P P P P = P P P P D D D D D D D D D D P P P P P P P P l Redundant data is used to recover P-data from the stored M-data l The K-data is decomposed into error correction code words l The parity component of code-words is populated from P-data 68 © 2005 The Generics Group AG
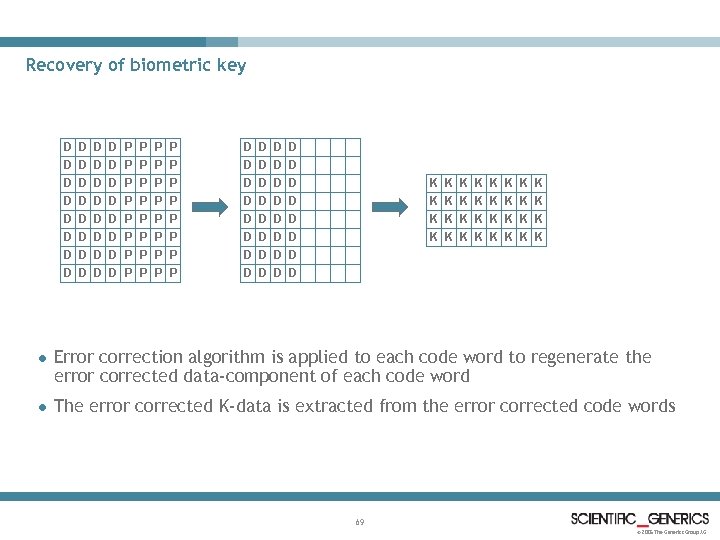
Recovery of biometric key D D D D P P P P D D D D P P P P D D D D D D D D K K K K K K K K l Error correction algorithm is applied to each code word to regenerate the error corrected data-component of each code word l The error corrected K-data is extracted from the error corrected code words 69 © 2005 The Generics Group AG
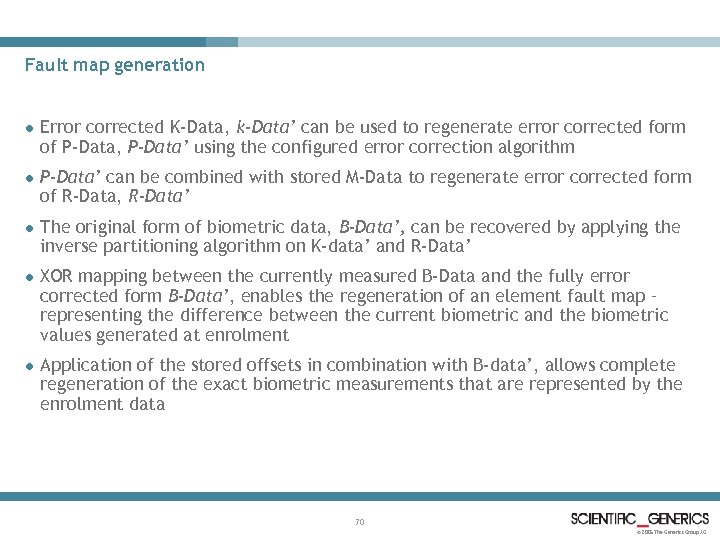
Fault map generation l Error corrected K-Data, k-Data’ can be used to regenerate error corrected form of P-Data, P-Data’ using the configured error correction algorithm l P-Data’ can be combined with stored M-Data to regenerate error corrected form of R-Data, R-Data’ l The original form of biometric data, B-Data’, can be recovered by applying the inverse partitioning algorithm on K-data’ and R-Data’ l XOR mapping between the currently measured B-Data and the fully error corrected form B-Data’, enables the regeneration of an element fault map – representing the difference between the current biometric and the biometric values generated at enrolment l Application of the stored offsets in combination with B-data’, allows complete regeneration of the exact biometric measurements that are represented by the enrolment data 70 © 2005 The Generics Group AG
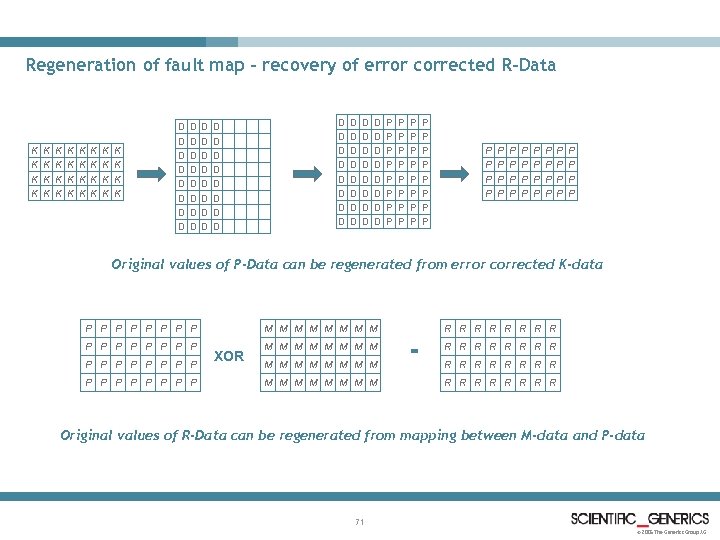
Regeneration of fault map – recovery of error corrected R-Data K K K K K K K K D D D D D D D D D D D D D D D D P P P P P P P P P P P P P P P P Original values of P-Data can be regenerated from error corrected K-data P P P P P P P P M M M M XOR M M M M R R R R = R R R R M M M M R R R R Original values of R-Data can be regenerated from mapping between M-data and P-data 71 © 2005 The Generics Group AG
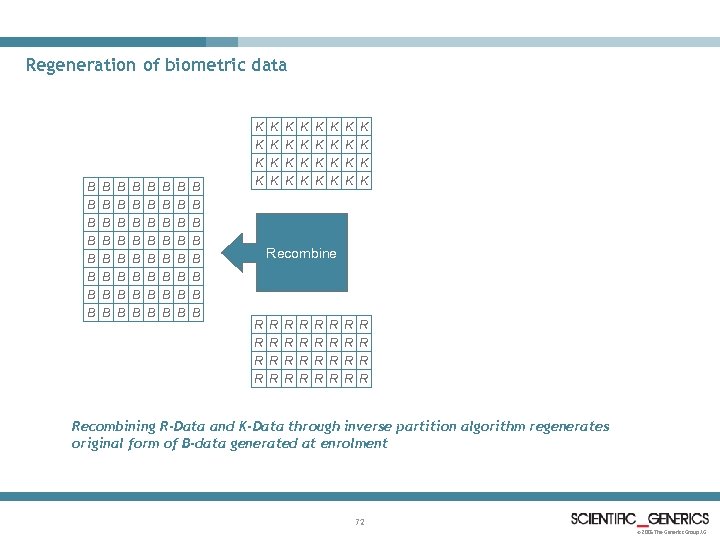
Regeneration of biometric data K K K K B B B B B B B B B B B B B B B B K K K K K K Recombine R R R R R R R R Recombining R-Data and K-Data through inverse partition algorithm regenerates original form of B-data generated at enrolment 72 © 2005 The Generics Group AG
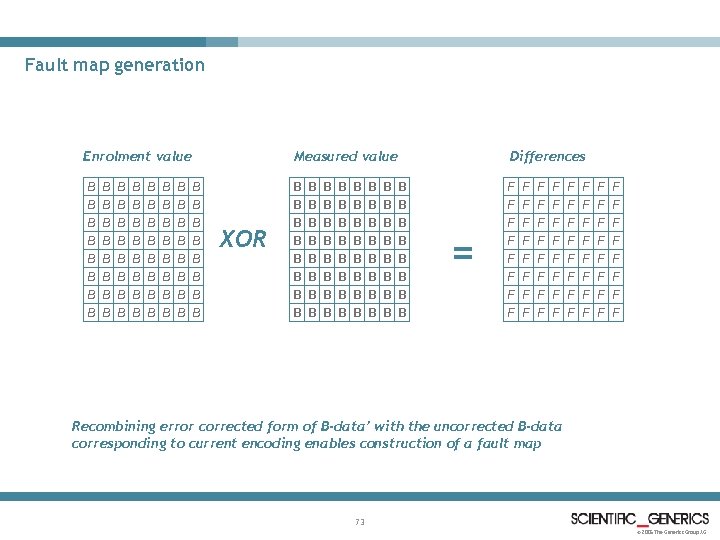
Fault map generation Enrolment value Measured value B B B B B B B B B B B B B B B B XOR Differences B B B B B B B B B B B B B B B B = F F F F F F F F F F F F F F F F Recombining error corrected form of B-data’ with the uncorrected B-data corresponding to current encoding enables construction of a fault map 73 © 2005 The Generics Group AG
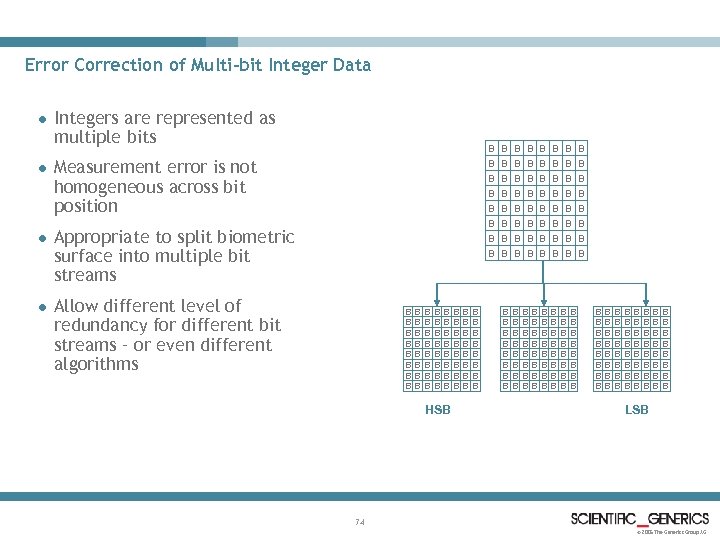
Error Correction of Multi-bit Integer Data l l Integers are represented as multiple bits B B B B Measurement error is not homogeneous across bit position B B B B B B B B B B Appropriate to split biometric surface into multiple bit streams B B B B Allow different level of redundancy for different bit streams – or even different algorithms B B B B B B B B B B HSB B B B B B B B B B B B B B B B B B B B B B B B B B B B B B B B B B B B B B B LSB 74 © 2005 The Generics Group AG
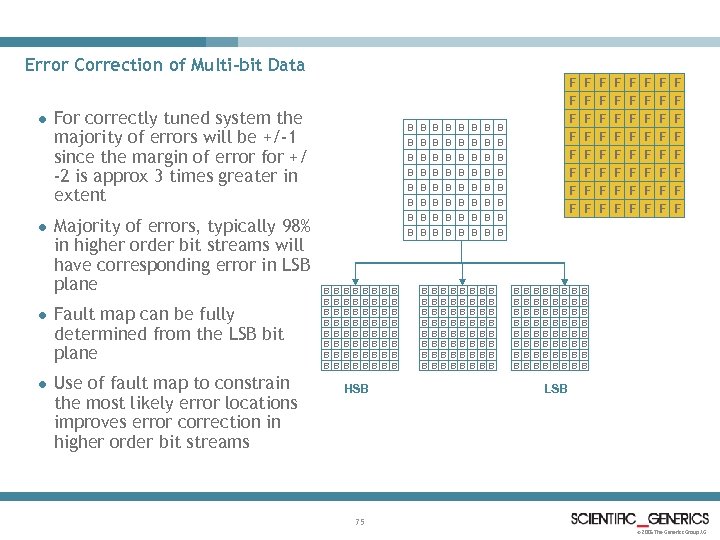
Error Correction of Multi-bit Data l l For correctly tuned system the majority of errors will be +/-1 since the margin of error for +/ -2 is approx 3 times greater in extent Majority of errors, typically 98% in higher order bit streams will have corresponding error in LSB plane l Fault map can be fully determined from the LSB bit plane l Use of fault map to constrain the most likely error locations improves error correction in higher order bit streams F F F F F F B B B B F F F F F F F F F B B B B B B B B B B F F B B B B B B B B B B B B HSB B B B B B B B B B B B B B B B B B B B B B B B B B B B B B B B B B B B B B B LSB 75 © 2005 The Generics Group AG
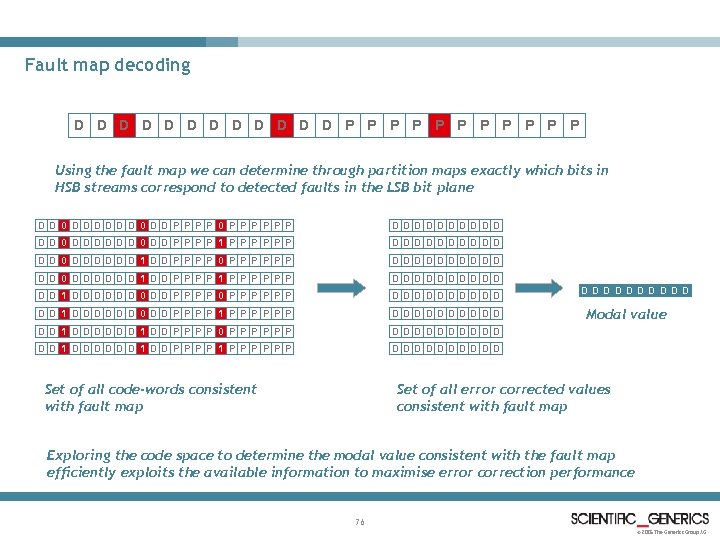
Fault map decoding D D D P P P Using the fault map we can determine through partition maps exactly which bits in HSB streams correspond to detected faults in the LSB bit plane DD 0 DDDDDD 0 DD P P 0 P P P DDD DD 0 DDDDDD 0 DD P P 1 P P P DDD DD 0 DDDDDD 1 DD P P 0 P P P DDD DD 0 DDDDDD 1 DD P P 1 P P P DDD DD 1 DDDDDD 0 DD P P 0 P P P DDD DD 1 DDDDDD 0 DD P P 1 P P P DDD DD 1 DDDDDD 1 DD P P 0 P P P DDD DD 1 DDDDDD 1 DD P P 1 P P P DDD D DD Set of all code-words consistent with fault map DDD D DD Modal value Set of all error corrected values consistent with fault map Exploring the code space to determine the modal value consistent with the fault map efficiently exploits the available information to maximise error correction performance 76 © 2005 The Generics Group AG
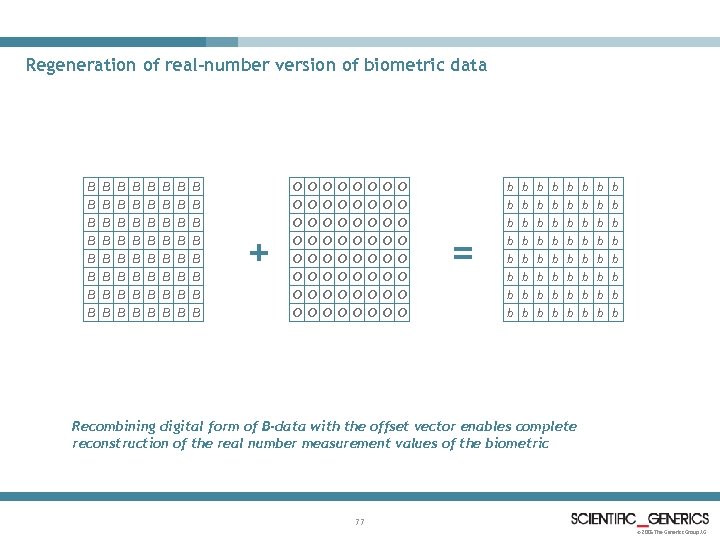
Regeneration of real-number version of biometric data B B B B B B B B B B B B B B B B + O O O O O O O O O O O O O O O O = b b b b b b b b b b b b b b b b Recombining digital form of B-data with the offset vector enables complete reconstruction of the real number measurement values of the biometric 77 © 2005 The Generics Group AG
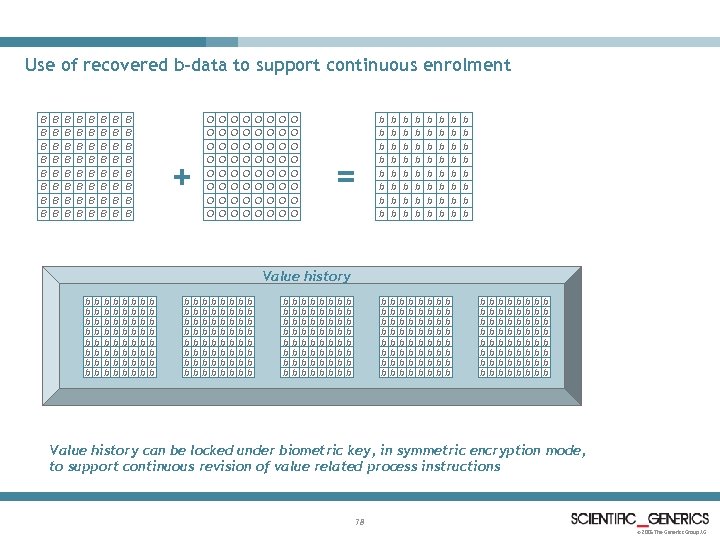
Use of recovered b-data to support continuous enrolment B B B B B B B B B B B B B B B B O O O O + O O O O O O O O O O O O O O b b b b = b b b b b b b b b b b b b b b b b b b b Value history b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b b Value history can be locked under biometric key, in symmetric encryption mode, to support continuous revision of value related process instructions 78 © 2005 The Generics Group AG
3e9057e06c820ef272d969656a15a553.ppt