5fe8515294fe73cc42e698c27fb47e13.ppt
- Количество слайдов: 21
Biometrics Authentication Bruce Maggs
Biometric Identifiers • • Fingerprints, palm prints Palm veins Hand shape Facial image DNA Iris, retinal images Odor Etc. 2
Fingerprints https: //en. wikipedia. org/wiki/Fingerprint#/media/File: Fingerprints_taken_ by_William_James_Herschel_1859 -1860. jpg 3
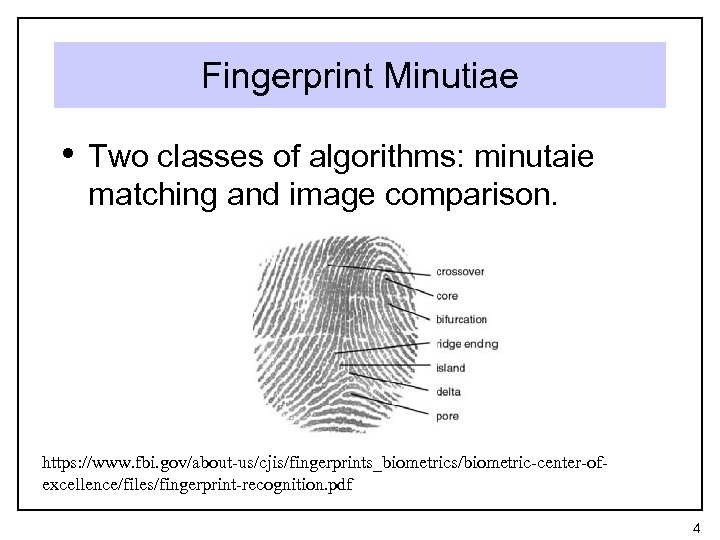
Fingerprint Minutiae • Two classes of algorithms: minutaie matching and image comparison. https: //www. fbi. gov/about-us/cjis/fingerprints_biometrics/biometric-center-ofexcellence/files/fingerprint-recognition. pdf 4
FBI Database • “Integrated Automated Fingerprint Identification System” • What is included in IAFIS: Not only fingerprints, but • • • corresponding criminal histories; mug shots; scars and tattoo photos; physical characteristics like height, weight, and hair and eye color; and aliases. https: //www. fbi. gov/about-us/cjis/fingerprints_biometrics/iafis Includes fingerprints for over 70 million criminals and 34 million other civilians. 27 minute processing time for criminal inquiry, 72 minutes for civil 5
Creating Fake Fingerprints • Relatively easy to do given access to a • real fingerprint. But in 2014 Jan Krissler demonstrated that he could create a fake fingerprint from a high-resolution photograph of Germany’s Federal Minister of Defense Ursula von der Leyen! http: //www. ibtimes. com/hacker-demonstrates-how-fake-fingerprint-sensors-using-regular -photographs-1769408 6
Retinal Scans • More difficult to collect than fingerprints. https: //en. wikipedia. org/wiki/Retina#/media/File: Fundus_photograph_of_normal_left_eye. jpg 7
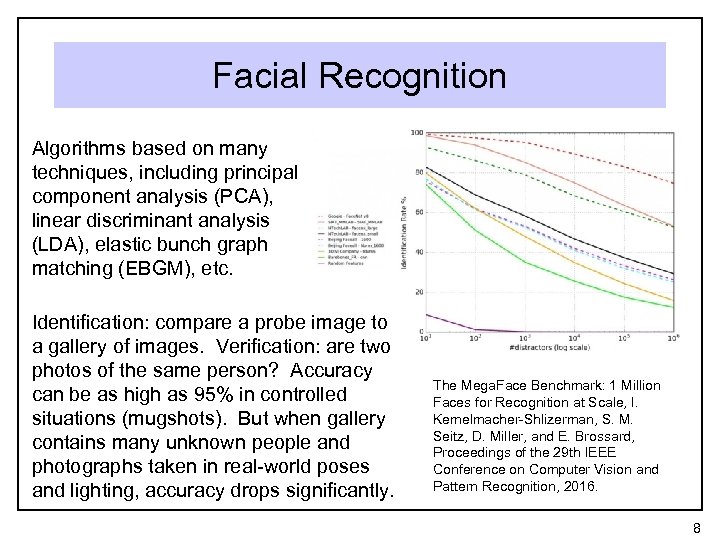
Facial Recognition Algorithms based on many techniques, including principal component analysis (PCA), linear discriminant analysis (LDA), elastic bunch graph matching (EBGM), etc. Identification: compare a probe image to a gallery of images. Verification: are two photos of the same person? Accuracy can be as high as 95% in controlled situations (mugshots). But when gallery contains many unknown people and photographs taken in real-world poses and lighting, accuracy drops significantly. The Mega. Face Benchmark: 1 Million Faces for Recognition at Scale, I. Kemelmacher-Shlizerman, S. M. Seitz, D. Miller, and E. Brossard, Proceedings of the 29 th IEEE Conference on Computer Vision and Pattern Recognition, 2016. 8
DNA • 99. 9% of DNA is identical in every • • • human! Tests focus on loci where differences are likely to occur. Original DNA is not compared directly: first, copies are made using Polymerase Chain Reaction (PCR) FBI estimates probability of a coincidental match at 1 in 108 trillion, but other estimates are much lower. https: //sasha 949. files. wordpres s. com/2010/05/3642508132_3 f 7 c 649 f 62_o. jpg http: //www. nij. gov/topics/forensics/evidence/dna/basics/pages/analyzing. aspx 9
Voice-Based Authentication http: //www. paymentscardsandmobile. com/barclays-roll-voice-biometrics-12 m-customers/ • Compare a speaker’s voice with known • • • characteristics of the voice, usually with the cooperation of the speaker. Non-invasive biometric capture (microphones) Barclay’s uses with high-end banking clients Protocol must protect against replay attack 10
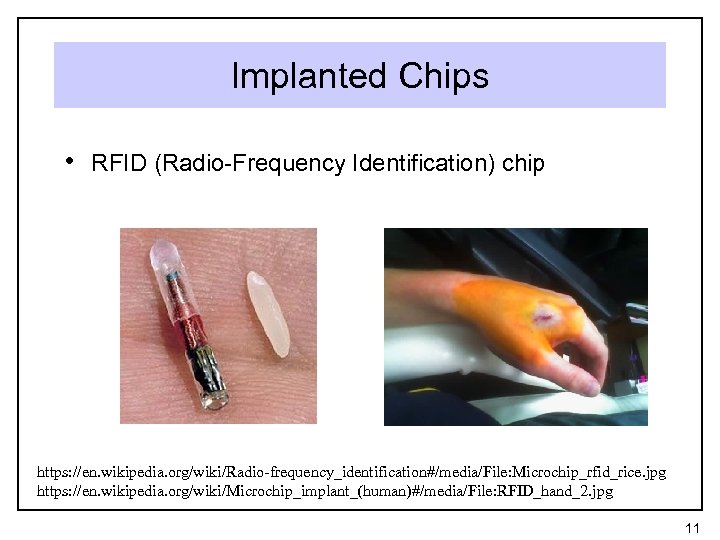
Implanted Chips • RFID (Radio-Frequency Identification) chip https: //en. wikipedia. org/wiki/Radio-frequency_identification#/media/File: Microchip_rfid_rice. jpg https: //en. wikipedia. org/wiki/Microchip_implant_(human)#/media/File: RFID_hand_2. jpg 11
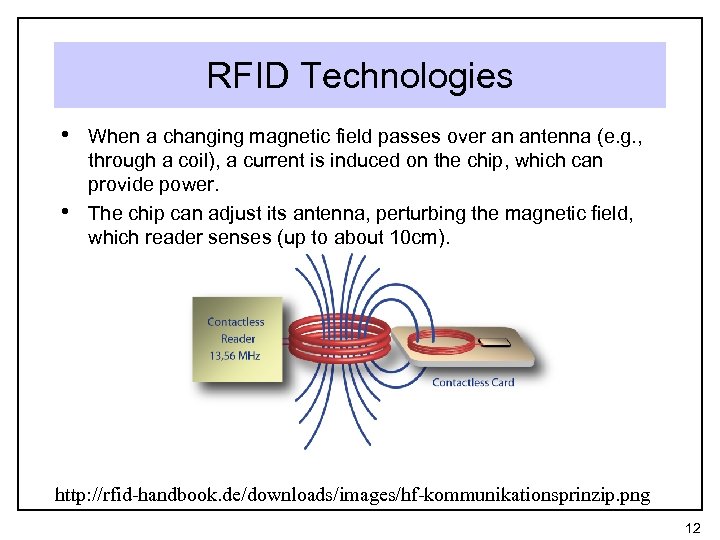
RFID Technologies • When a changing magnetic field passes over an antenna (e. g. , • through a coil), a current is induced on the chip, which can provide power. The chip can adjust its antenna, perturbing the magnetic field, which reader senses (up to about 10 cm). http: //rfid-handbook. de/downloads/images/hf-kommunikationsprinzip. png 12
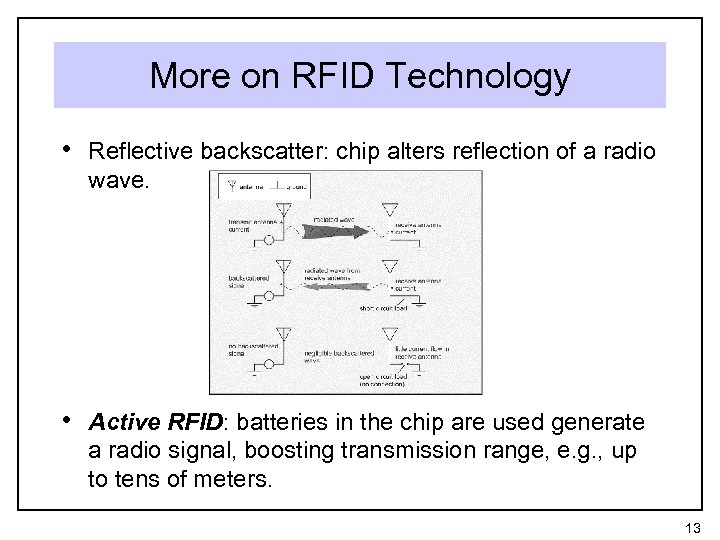
More on RFID Technology • Reflective backscatter: chip alters reflection of a radio wave. • Active RFID: batteries in the chip are used generate a radio signal, boosting transmission range, e. g. , up to tens of meters. 13
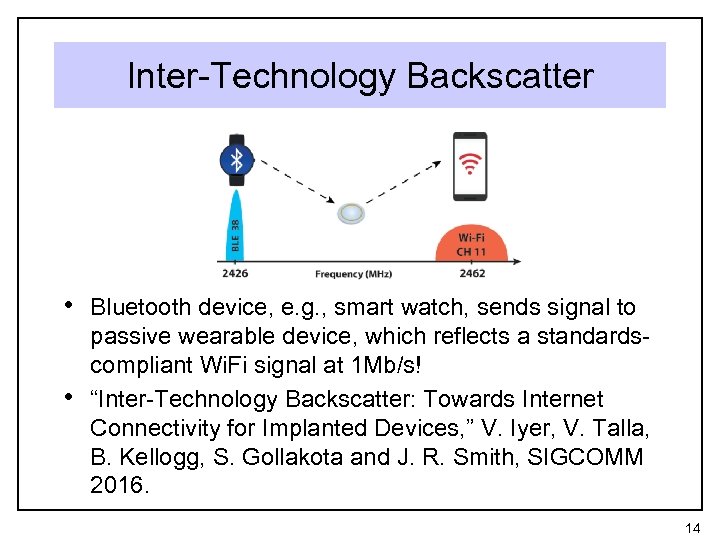
Inter-Technology Backscatter • Bluetooth device, e. g. , smart watch, sends signal to • passive wearable device, which reflects a standardscompliant Wi. Fi signal at 1 Mb/s! “Inter-Technology Backscatter: Towards Internet Connectivity for Implanted Devices, ” V. Iyer, V. Talla, B. Kellogg, S. Gollakota and J. R. Smith, SIGCOMM 2016. 14
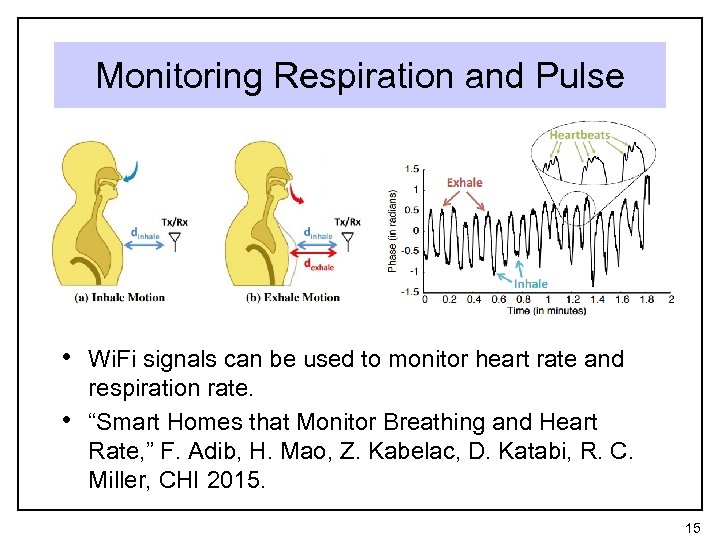
Monitoring Respiration and Pulse • Wi. Fi signals can be used to monitor heart rate and • respiration rate. “Smart Homes that Monitor Breathing and Heart Rate, ” F. Adib, H. Mao, Z. Kabelac, D. Katabi, R. C. Miller, CHI 2015. 15
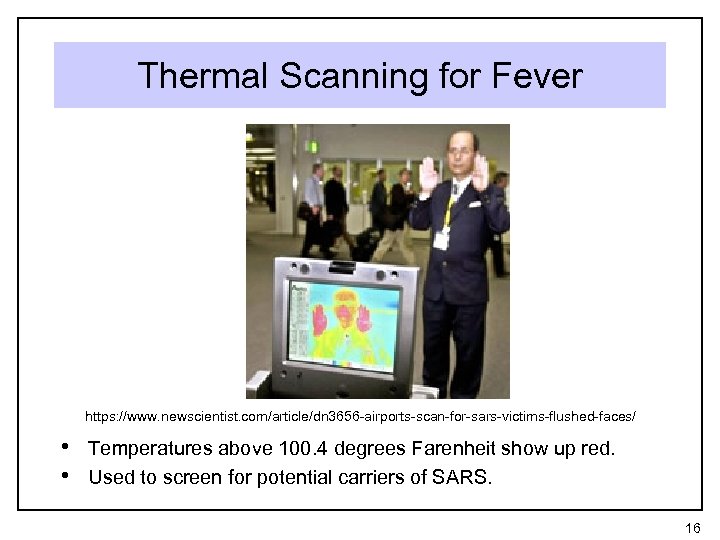
Thermal Scanning for Fever https: //www. newscientist. com/article/dn 3656 -airports-scan-for-sars-victims-flushed-faces/ • Temperatures above 100. 4 degrees Farenheit show up red. • Used to screen for potential carriers of SARS. 16
Turing Test A test of a computer’s ability to behave in a way that is indistinguishable from a human being. Turing proposed natural language conversations. 17
“Reverse” Turing Test or “CAPTCHA” • A test that can distinguish a human from a computer. • CAPTCHA: Completely Automated Public Turing test to tell Computers and Humans Apart 18
“Captchas” http: //www. captcha. net/ Easy to generate, difficult for a computer to solve. U. S. Patent 6195698: Method for selectively restricting access to computer systems. Mark D. Lillibridge, Martin Abadi, Krishna Bharat, Andrei Z. Broder. Filed April 13, 1998, published February 27, 2001. von Ahn, Luis; Blum, Manuel; Hopper, Nicholas J. ; Langford, John (May 2003). CAPTCHA: Using Hard AI Problems for Security. EUROCRYPT 2003: International Conference on the Theory and Applications of Cryptographic Techniques 19
Polygraph / Lie Detector • Measures physiological responses to questions, such as heart rate, blood pressure, perspiration http: //abcnewspapers. com/2012/07/07/new-business-detects-between-truth-and-lies/ 20
Scientific Validity? • “CONCLUSION: Polygraph testing yields an unacceptable choice for DOE employee security screening between too many loyal employees falsely judged deceptive and too many major security threats left undetected. Its accuracy in distinguishing actual or potential security violators from innocent test takers is insufficient to justify reliance on its use in employee security screening in federal agencies. ” Ø The Polygraph and Lie Detection, Committee to Review the Scientific Evidence on the Polygraph. Division of Behavioral and Social Sciences and Education. Washington, DC: The National Academies Press. 2003 • Not admissible in court. • But accuracy is better than chance when focused on • specific incidents. Subject’s belief in validity may lead to truthfulness. 21
5fe8515294fe73cc42e698c27fb47e13.ppt