042bbe7a94c0789e36584fb03b72e06b.ppt
- Количество слайдов: 28

BIG-IP Access Policy Manager Web Access Management
2 F 5 Delivers Access and Auth. Services • Security and identity is an integral part of an F 5 ADC – Integrate Web access control services – Innovative and scalable web security – Drive user and group identity into the network with policybased control to applications
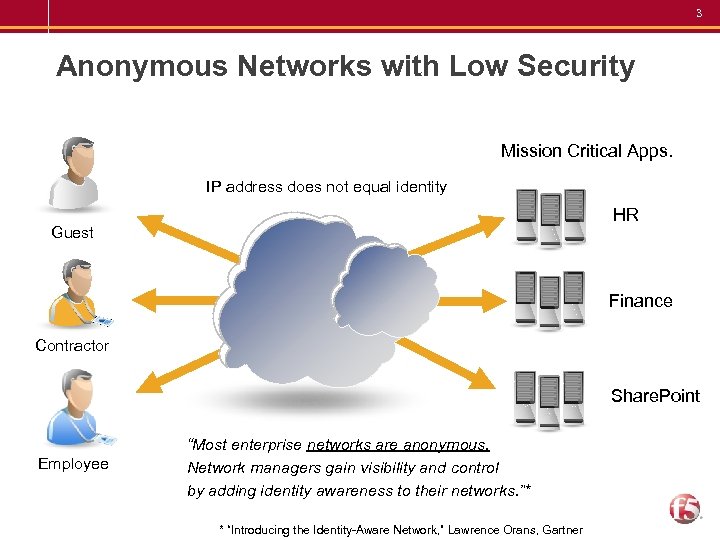
3 Anonymous Networks with Low Security Mission Critical Apps. IP address does not equal identity HR Guest Finance Contractor Share. Point Employee “Most enterprise networks are anonymous. Network managers gain visibility and control by adding identity awareness to their networks. ”* * “Introducing the Identity-Aware Network, ” Lawrence Orans, Gartner
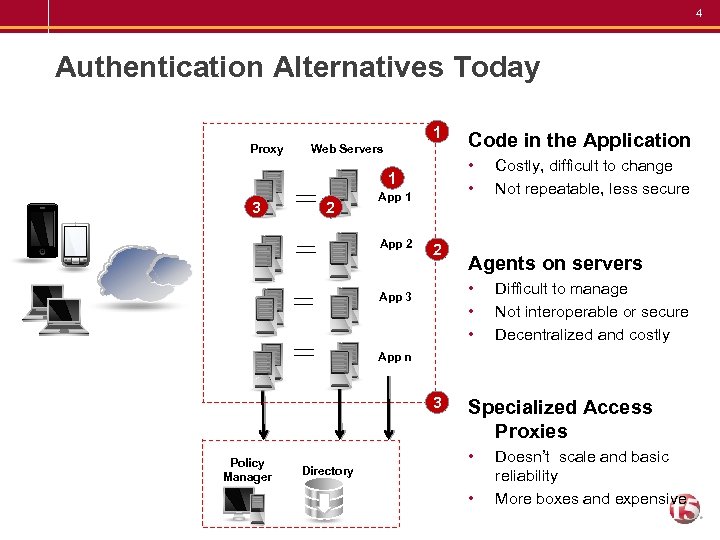
4 Authentication Alternatives Today 1 Proxy Web Servers • • 1 3 2 App 1 App 2 Code in the Application 2 Agents on servers • • • App 3 Costly, difficult to change Not repeatable, less secure Difficult to manage Not interoperable or secure Decentralized and costly App n 3 Policy Manager Directory Specialized Access Proxies • • Doesn’t scale and basic reliability More boxes and expensive
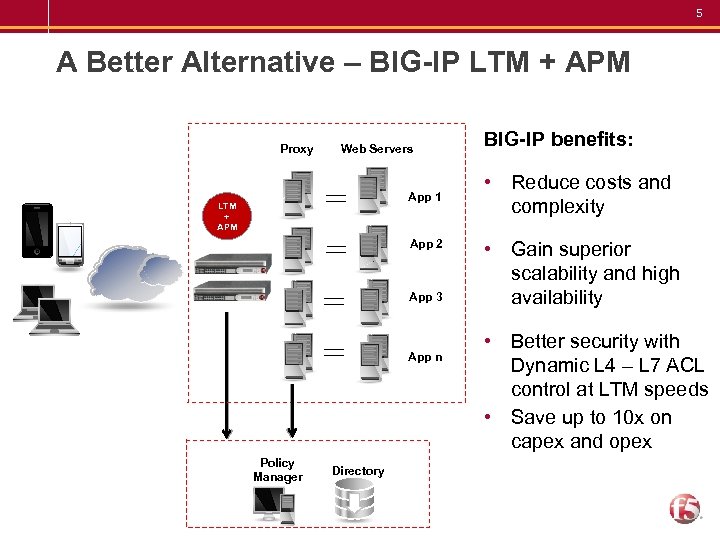
5 A Better Alternative – BIG-IP LTM + APM Proxy Web Servers App 1 LTM + APM App 2 App 3 App n Policy Manager Directory BIG-IP benefits: • Reduce costs and complexity • Gain superior scalability and high availability • Better security with Dynamic L 4 – L 7 ACL control at LTM speeds • Save up to 10 x on capex and opex
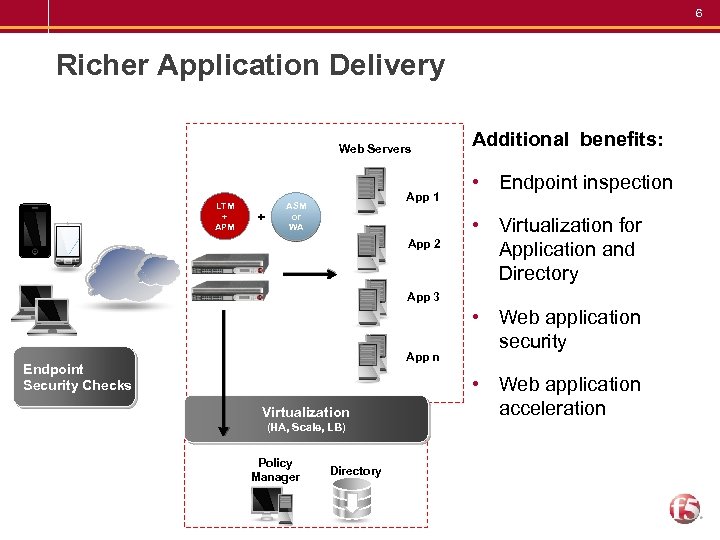
6 Richer Application Delivery Web Servers LTM + APM + App 1 ASM or WA App 2 Additional benefits: • Endpoint inspection • Virtualization for Application and Directory App 3 App n Endpoint Security Checks Virtualization (HA, Scale, LB) Policy Manager Directory • Web application security • Web application acceleration
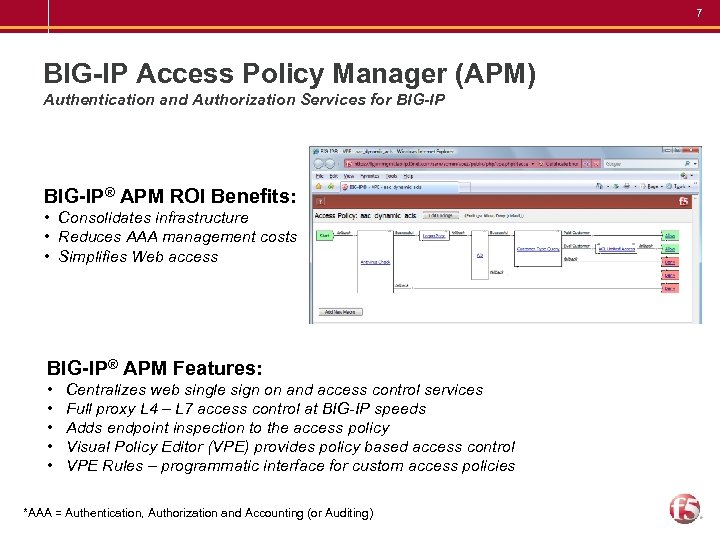
7 BIG-IP Access Policy Manager (APM) Authentication and Authorization Services for BIG-IP® APM ROI Benefits: • Consolidates infrastructure • Reduces AAA management costs • Simplifies Web access BIG-IP® APM Features: • Centralizes web single sign on and access control services • Full proxy L 4 – L 7 access control at BIG-IP speeds • Adds endpoint inspection to the access policy • Visual Policy Editor (VPE) provides policy based access control • VPE Rules – programmatic interface for custom access policies *AAA = Authentication, Authorization and Accounting (or Auditing)
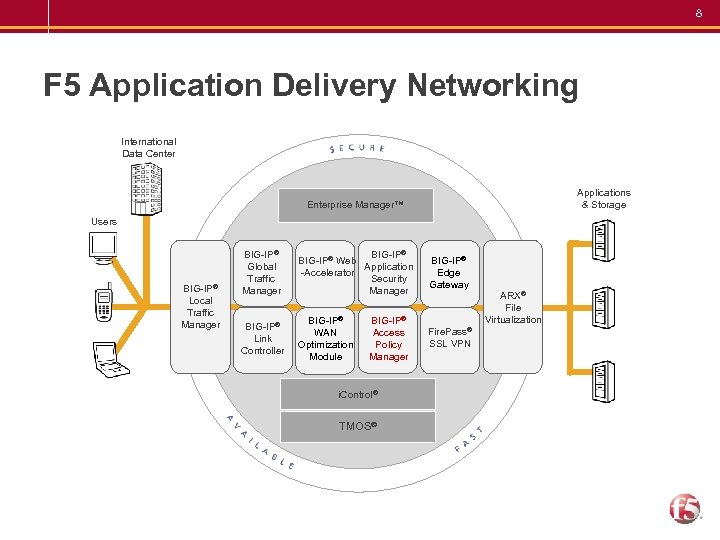
8 F 5 Application Delivery Networking International Data Center Applications & Storage Enterprise Manager™ Users BIG-IP® Local Traffic Manager BIG-IP® Global Traffic Manager BIG-IP® Web Application -Accelerator Security Manager BIG-IP® Edge Gateway BIG-IP® Link Controller BIG-IP® WAN Optimization Module Fire. Pass® SSL VPN BIG-IP® Access Policy Manager i. Control® TMOS® ARX® File Virtualization
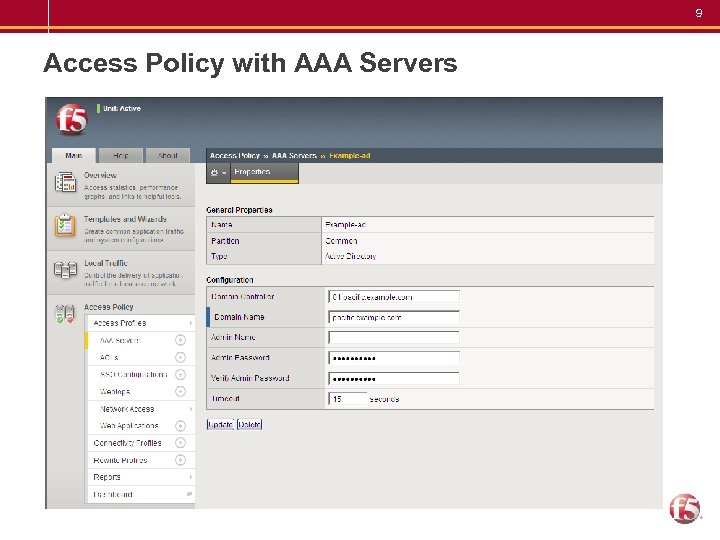
9 Access Policy with AAA Servers – Fully integrated to TMOS • CMP enabled • UI/CLI (bigip. conf) • Enterprise Manager – All HTTP based LTM features can be combined with Access Policy • i. Rules (events/cmds) • Session DB • SSL offloading – Compatible with add-ons (ASM/PSM)
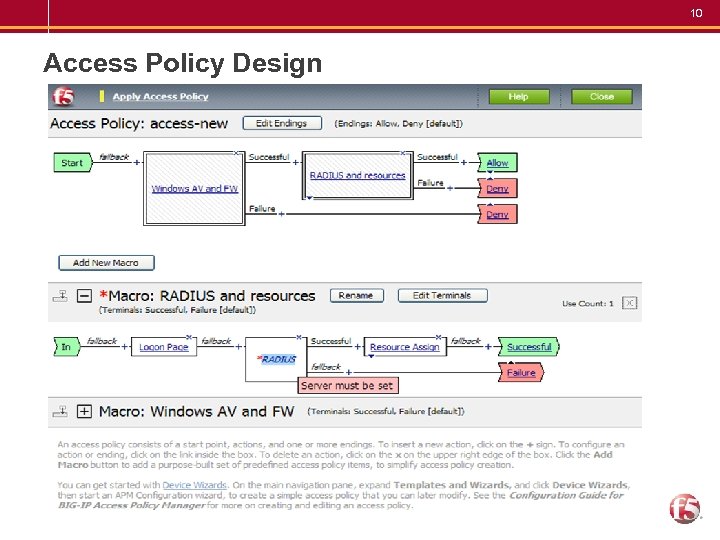
10 Access Policy Design • Industry-leading advanced Visual Policy Editor (VPE) – Flexible – Easy to understand, visual representation of policy – VPE Rules (TCL-based) for advanced functions – Trigger TMM i. Rules events • Usability features – Macros – Visual cues to aid configuration
11 Dynamic ACL Control • Cost effective alternative for policy based access control • Before: Expensive and complicated control of resources • After: Layer 7 ACLs with access profiles – Provide advanced authentication and access control for web based applications
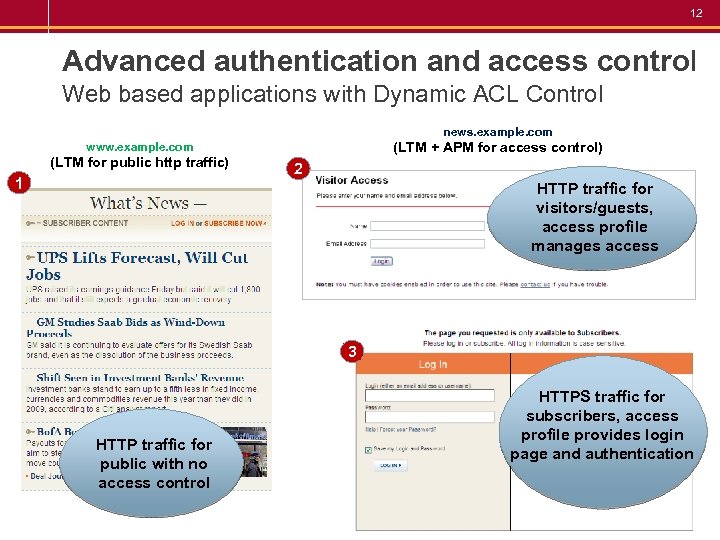
12 Advanced authentication and access control Web based applications with Dynamic ACL Control news. example. com (LTM + APM for access control) www. example. com (LTM for public http traffic) 1 2 HTTP traffic for visitors/guests, access profile manages access 3 HTTP traffic for public with no access control HTTPS traffic for subscribers, access profile provides login page and authentication
13 Customized User Interface • Updated End-User Interface with Full Customization – Stylesheet (CSS) based customization eliminates the need to customize each page individually – Form location (left, center, right) – Font style/sizes – Header and footer
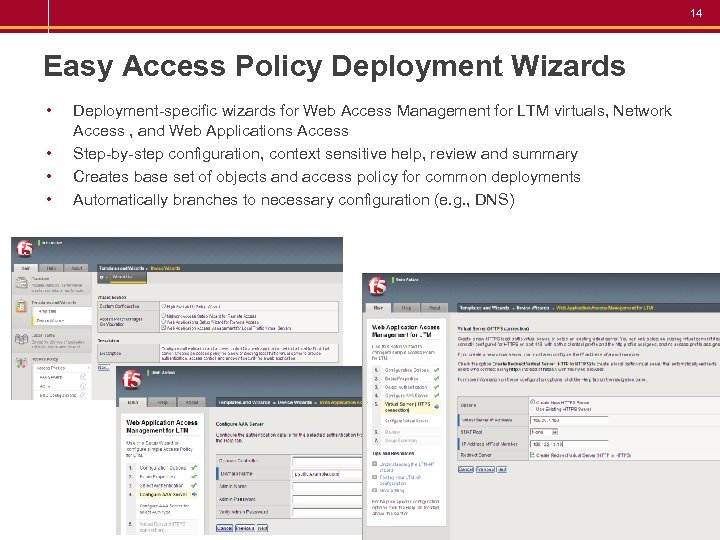
14 Easy Access Policy Deployment Wizards • • Deployment-specific wizards for Web Access Management for LTM virtuals, Network Access , and Web Applications Access Step-by-step configuration, context sensitive help, review and summary Creates base set of objects and access policy for common deployments Automatically branches to necessary configuration (e. g. , DNS)
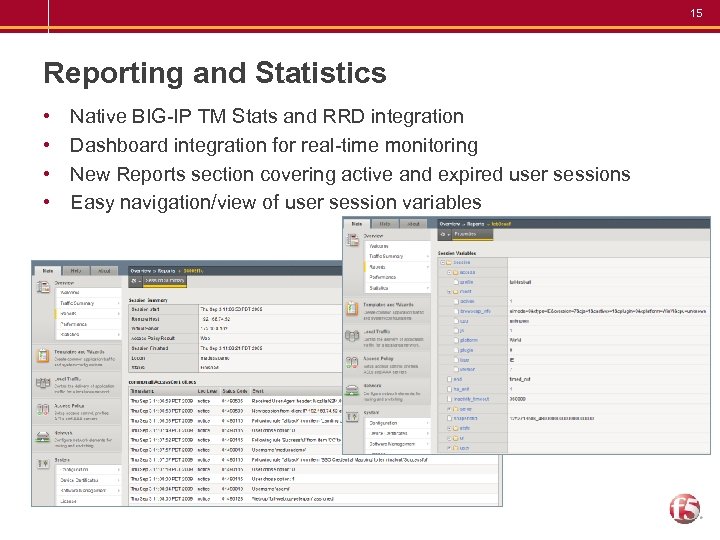
15 Reporting and Statistics • • Native BIG-IP TM Stats and RRD integration Dashboard integration for real-time monitoring New Reports section covering active and expired user sessions Easy navigation/view of user session variables
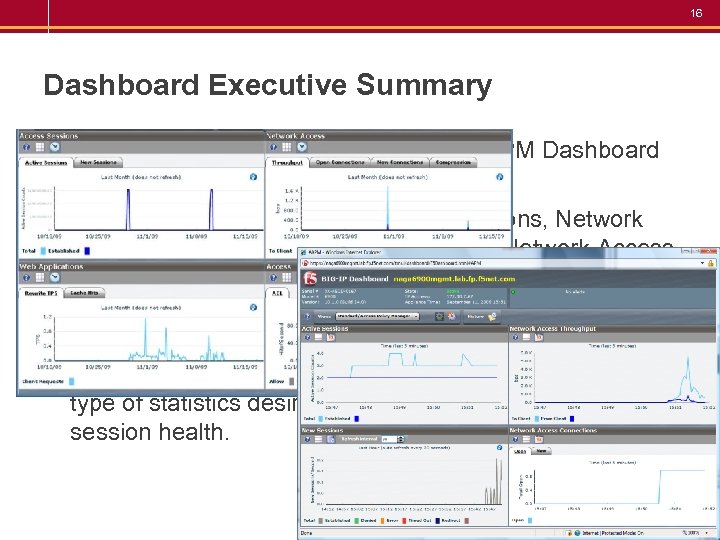
16 Dashboard Executive Summary • Administrators quickly view the BIG-IP APM Dashboard • Real-time understanding of access health • View the default template of Active Sessions, Network Access Throughput, New Sessions, and Network Access Connections • Optionally, administrators create customized views using the Dashboard Windows Chooser • Drag and drop selections onto the window pane with the type of statistics desired for fast comprehension of session health.
17 F 5 and Oracle Announcement • F 5 and Oracle Announce Plans to Unify Access Management for Web Applications • Solution will combine F 5’s BIG-IP system with Oracle Access Manager • Enhance single sign-on (SSO) capabilities and simplify access control • Available in 1 H 2010 calendar year – http: //www. f 5. com/news-press-events/press/20091006. html
18 APM – v 10. 1 Features • Authentication and Authorization Services – SSO/Credential Caching: HTTP Basic, HTTP NTLMv 1/v 2, Cookie, Form, and HTTP Header – Dynamic per-session layer 4 - 7 (HTTP) ACLs – Native RSA Secur. ID – RADIUS accounting – Authentication server redundancy
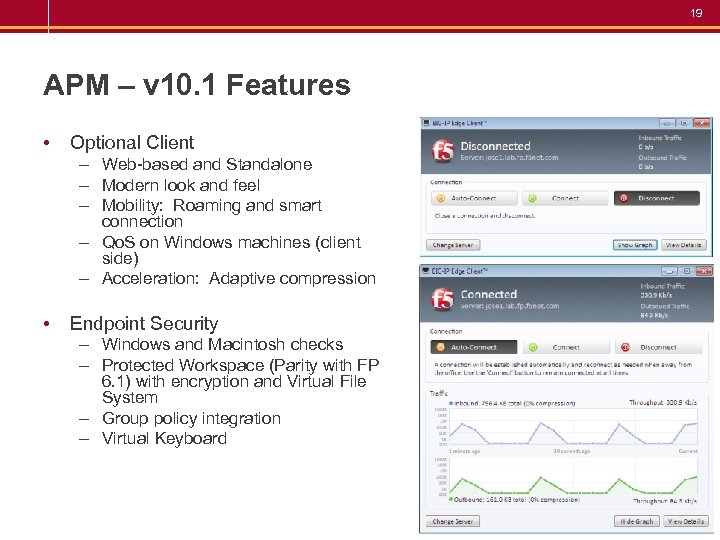
19 APM – v 10. 1 Features • Optional Client – Web-based and Standalone – Modern look and feel – Mobility: Roaming and smart connection – Qo. S on Windows machines (client side) – Acceleration: Adaptive compression • Endpoint Security – Windows and Macintosh checks – Protected Workspace (Parity with FP 6. 1) with encryption and Virtual File System – Group policy integration – Virtual Keyboard
20 APM – v 10. 1 Features • Miscellaneous – – Set-up wizards Dashboards Policy import/export Splunk for F 5 logging and reporting – Win 7 Support POWERED
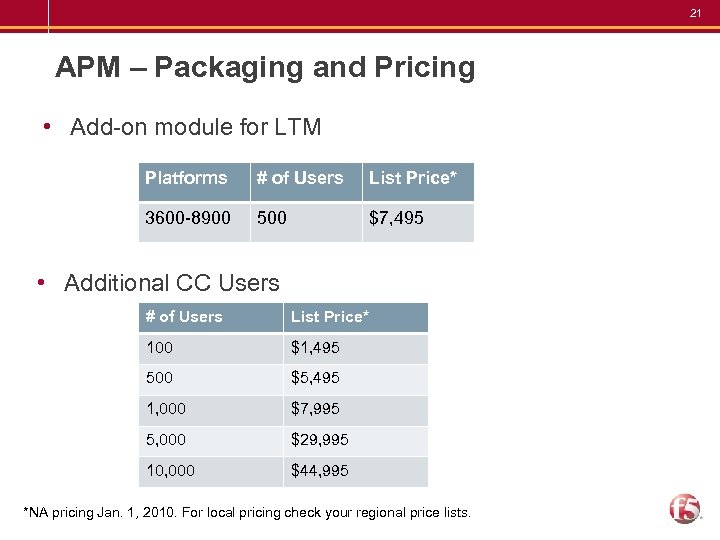
21 APM – Packaging and Pricing • Add-on module for LTM Platforms # of Users List Price* 3600 -8900 500 $7, 495 • Additional CC Users # of Users List Price* 100 $1, 495 500 $5, 495 1, 000 $7, 995 5, 000 $29, 995 10, 000 $44, 995 *NA pricing Jan. 1, 2010. For local pricing check your regional price lists.
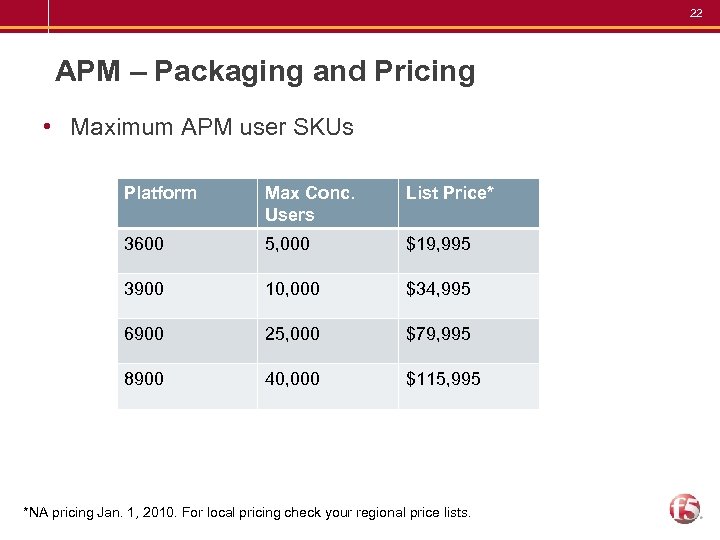
22 APM – Packaging and Pricing • Maximum APM user SKUs Platform Max Conc. Users List Price* 3600 5, 000 $19, 995 3900 10, 000 $34, 995 6900 25, 000 $79, 995 8900 40, 000 $115, 995 *NA pricing Jan. 1, 2010. For local pricing check your regional price lists.
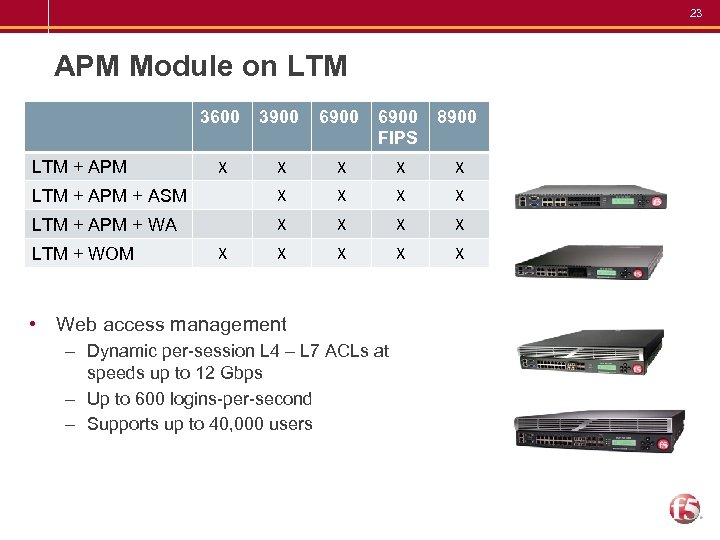
23 APM Module on LTM 3600 3900 6900 FIPS 8900 X X X LTM + APM + ASM X X LTM + APM + WA X X X X LTM + APM LTM + WOM X • Web access management – Dynamic per-session L 4 – L 7 ACLs at speeds up to 12 Gbps – Up to 600 logins-per-second – Supports up to 40, 000 users
24 What is the value of F 5 access? Access value proposition • Integrates with existing enterprise infrastructure and applications • Authentication and access to networks, applications and portals • Comprehensive end-point security for corporate compliance • Powerful, easy to use management interface • Scalability, Performance and Reliability • Better security driving identity into the network Reduce costs of managing AAA with integrated authentication Only ADC that effectively provides Web Access Management capabilities

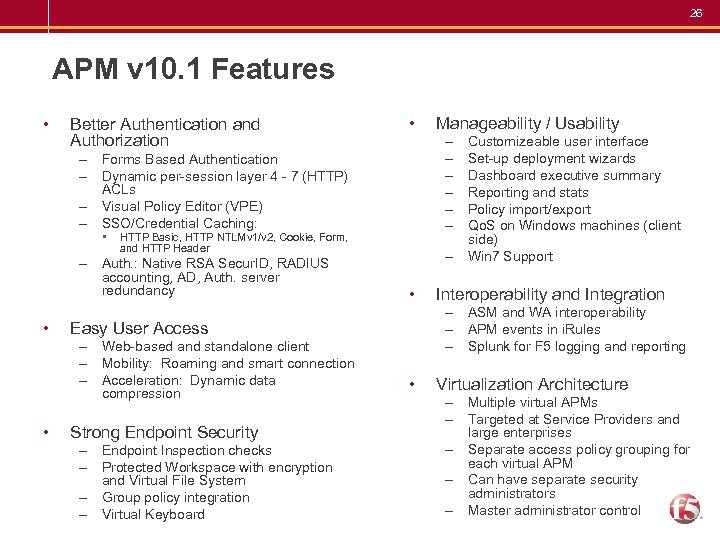
26 APM v 10. 1 Features • Better Authentication and Authorization • – – – – Forms Based Authentication – Dynamic per-session layer 4 - 7 (HTTP) ACLs – Visual Policy Editor (VPE) – SSO/Credential Caching: • HTTP Basic, HTTP NTLMv 1/v 2, Cookie, Form, and HTTP Header – Auth. : Native RSA Secur. ID, RADIUS accounting, AD, Auth. server redundancy • • – • Strong Endpoint Security – Endpoint Inspection checks – Protected Workspace with encryption and Virtual File System – Group policy integration – Virtual Keyboard Customizeable user interface Set-up deployment wizards Dashboard executive summary Reporting and stats Policy import/export Qo. S on Windows machines (client side) Win 7 Support Interoperability and Integration – ASM and WA interoperability – APM events in i. Rules – Splunk for F 5 logging and reporting Easy User Access – Web-based and standalone client – Mobility: Roaming and smart connection – Acceleration: Dynamic data compression Manageability / Usability • Virtualization Architecture – Multiple virtual APMs – Targeted at Service Providers and large enterprises – Separate access policy grouping for each virtual APM – Can have separate security administrators – Master administrator control
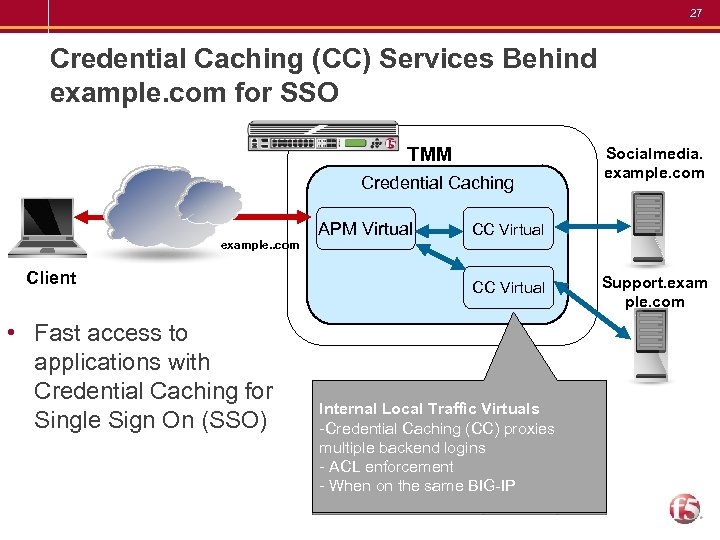
27 Credential Caching (CC) Services Behind example. com for SSO TMM Credential Caching example. . com Client • Fast access to applications with Credential Caching for Single Sign On (SSO) APM Virtual Socialmedia. example. com CC Virtual Internal Local Traffic Virtuals -Credential Caching (CC) proxies multiple backend logins - ACL enforcement - When on the same BIG-IP Support. exam ple. com
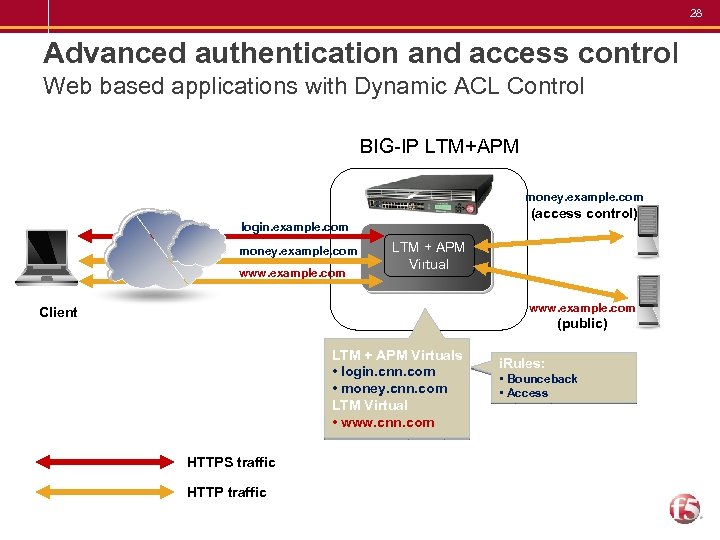
28 Advanced authentication and access control Web based applications with Dynamic ACL Control BIG-IP LTM+APM money. example. com (access control) login. example. com money. example. com www. example. com LTM + APM Virtual www. example. com Client (public) LTM + APM Virtuals • login. cnn. com • money. cnn. com LTM Virtual • www. cnn. com HTTPS traffic HTTP traffic i. Rules: • Bounceback • Access
042bbe7a94c0789e36584fb03b72e06b.ppt