71c6918f117da14cca36e3cb8d71f039.ppt
- Количество слайдов: 32
AT-9424 Product Overview Managed Gigabit Switch with Denial of Service (Do. S) Attack Protection
Allied Telesyn AT-9424 Gigabit Ethernet Switch for the Edge ¢ First security focused gigabit switch for the access edge – Detects and protects against 6 Do. S attack variants – Classifies and ACLs provide additional customizable security – Also offers a competitive base feature set outside of security • Available Now • 24 10/1000 ports and 2 SFPs or GBICs in 1 RU • Part Number: AT-9424 T/SP-10 & AT-9424 T/GB-10
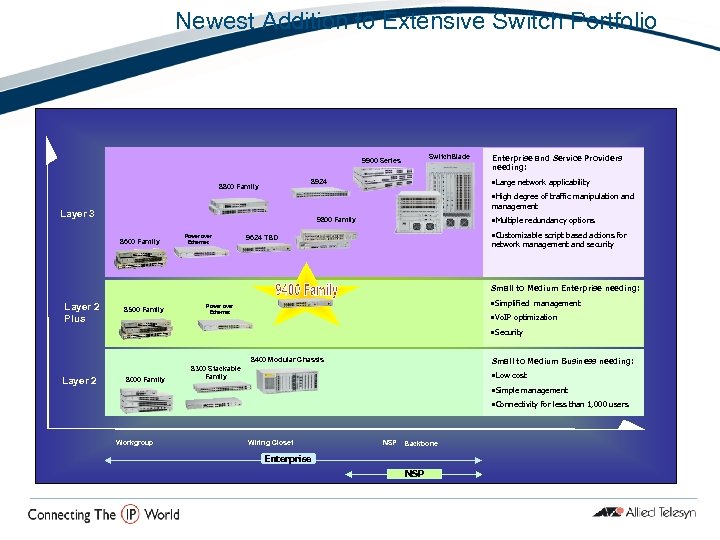
Newest Addition to Extensive Switch Portfolio Switch. Blade 9900 Series • Large network applicability 8924 8800 Family Enterprise and Service Providers needing: • High degree of traffic manipulation and management Layer 3 • Multiple redundancy options 9800 Family 8600 Family Power over Ethernet • Customizable script based actions for 9624 TBD network management and security Small to Medium Enterprise needing: Layer 2 Plus 8500 Family • Simplified management Power over Ethernet • Vo. IP optimization • Security 8400 Modular Chassis Layer 2 8000 Family Small to Medium Business needing: 8300 Stackable Family • Low cost • Simple management • Connectivity for less than 1, 000 users Workgroup Wiring Closet NSP Backbone Enterprise NSP
AT-9424 – Target Markets Traditional Enterprise LAN Education Institutions LAN Traditional Enterprise Service-provisioned Leased Offices or MTUs Traditional Enterprise LAN These organizations need gigabit and Do. S attack protection – Have users that bring laptops in and out of the network making the network susceptible to hosting Do. S attacks
¢ AT-9424 the Gig Switch of Choice for: Security Conscious Medium to Small organizations (50 -1000 users) – The 9424 is the only switch in its class with attack detection and suppression – 54% of respondents to the Network Computing Reader Survey plan to invest more in security than in anything else ¢ SMEs and SMBs moving towards Gig-to-the-desk – Cost effective and more secure ¢ SMEs seeking a simple server aggregation switch – Rich quality of service (Qo. S) capabilities ¢ SMEs who want to eliminate distribution tier bottlenecks – Wirespeed gigabit switching in a compact formfactor
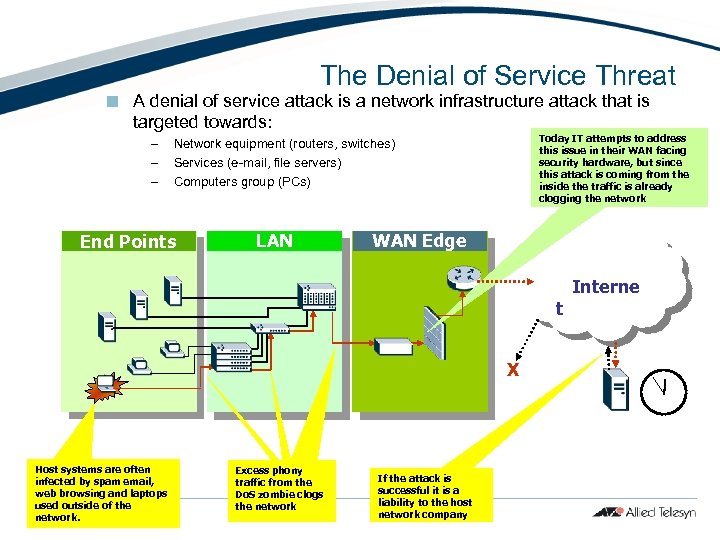
The Denial of Service Threat ¢ A denial of service attack is a network infrastructure attack that is targeted towards: – – – Today IT attempts to address this issue in their WAN facing security hardware, but since this attack is coming from the inside the traffic is already clogging the network Network equipment (routers, switches) Services (e-mail, file servers) Computers group (PCs) End Points LAN WAN Edge t X Host systems are often infected by spam email, web browsing and laptops used outside of the network. Excess phony traffic from the Do. S zombie clogs the network If the attack is successful it is a liability to the host network company Interne
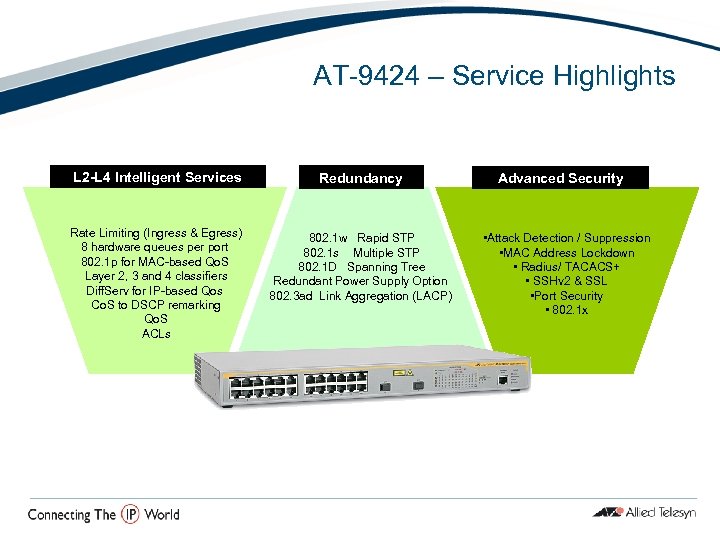
AT-9424 – Service Highlights L 2 -L 4 Intelligent Services Rate Limiting (Ingress & Egress) 8 hardware queues per port 802. 1 p for MAC-based Qo. S Layer 2, 3 and 4 classifiers Diff. Serv for IP-based Qos Co. S to DSCP remarking Qo. S ACLs Redundancy 802. 1 w Rapid STP 802. 1 s Multiple STP 802. 1 D Spanning Tree Redundant Power Supply Option 802. 3 ad Link Aggregation (LACP) Advanced Security • Attack Detection / Suppression • MAC Address Lockdown • Radius/ TACACS+ • SSHv 2 & SSL • Port Security • 802. 1 x
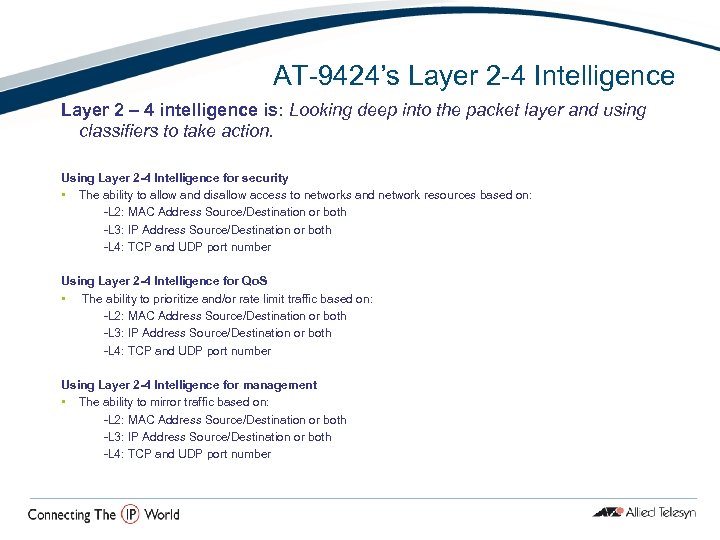
AT-9424’s Layer 2 -4 Intelligence Layer 2 – 4 intelligence is: Looking deep into the packet layer and using classifiers to take action. Using Layer 2 -4 Intelligence for security • The ability to allow and disallow access to networks and network resources based on: -L 2: MAC Address Source/Destination or both -L 3: IP Address Source/Destination or both -L 4: TCP and UDP port number Using Layer 2 -4 Intelligence for Qo. S • The ability to prioritize and/or rate limit traffic based on: -L 2: MAC Address Source/Destination or both -L 3: IP Address Source/Destination or both -L 4: TCP and UDP port number Using Layer 2 -4 Intelligence for management • The ability to mirror traffic based on: -L 2: MAC Address Source/Destination or both -L 3: IP Address Source/Destination or both -L 4: TCP and UDP port number
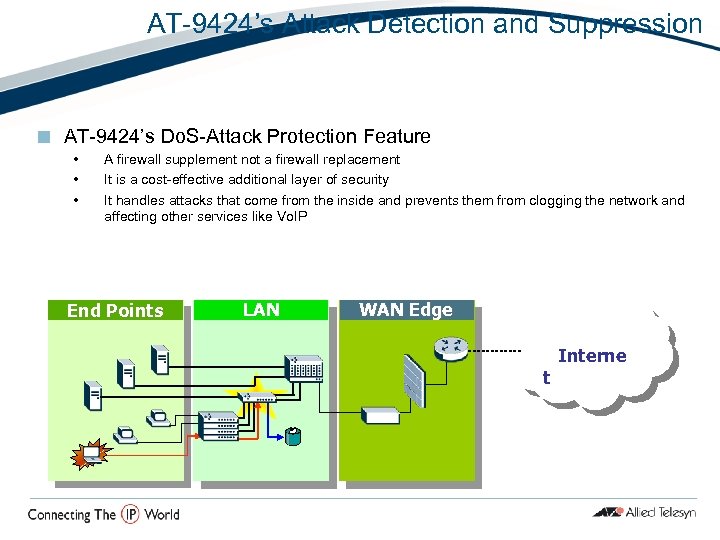
AT-9424’s Attack Detection and Suppression ¢ AT-9424’s Do. S-Attack Protection Feature • • • A firewall supplement not a firewall replacement It is a cost-effective additional layer of security It handles attacks that come from the inside and prevents them from clogging the network and affecting other services like Vo. IP End Points LAN WAN Edge t Interne
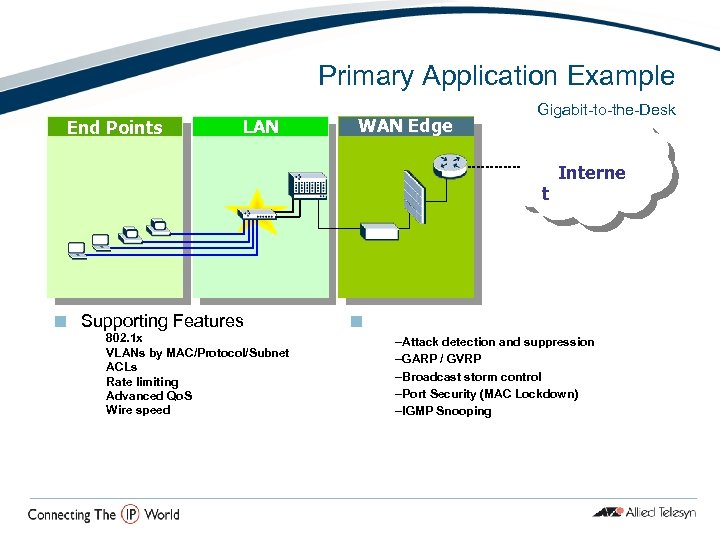
Primary Application Example End Points LAN WAN Edge Gigabit-to-the-Desk t ¢ Supporting Features – 802. 1 x –VLANs by MAC/Protocol/Subnet –ACLs –Rate limiting –Advanced Qo. S –Wire speed ¢ Interne s –Attack detection and suppression –GARP / GVRP –Broadcast storm control –Port Security (MAC Lockdown) –IGMP Snooping
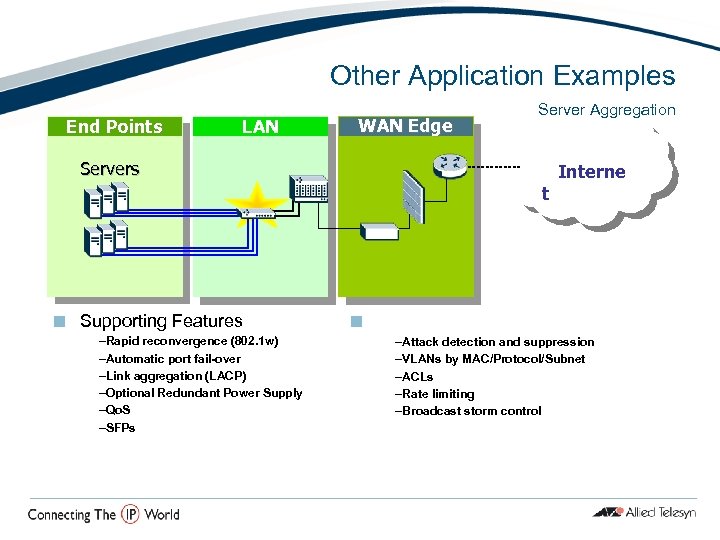
Other Application Examples End Points LAN WAN Edge Server Aggregation Servers t ¢ Supporting Features –Rapid reconvergence (802. 1 w) –Automatic port fail-over –Link aggregation (LACP) –Optional Redundant Power Supply –Qo. S –SFPs ¢ Interne s –Attack detection and suppression –VLANs by MAC/Protocol/Subnet –ACLs –Rate limiting –Broadcast storm control
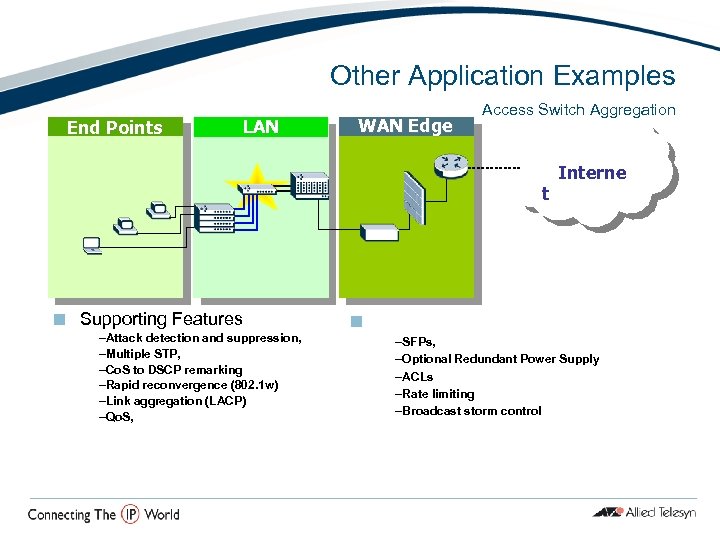
Other Application Examples End Points LAN WAN Edge Access Switch Aggregation t ¢ Supporting Features –Attack detection and suppression, –Multiple STP, –Co. S to DSCP remarking –Rapid reconvergence (802. 1 w) –Link aggregation (LACP) –Qo. S, ¢ Interne s –SFPs, –Optional Redundant Power Supply –ACLs –Rate limiting –Broadcast storm control
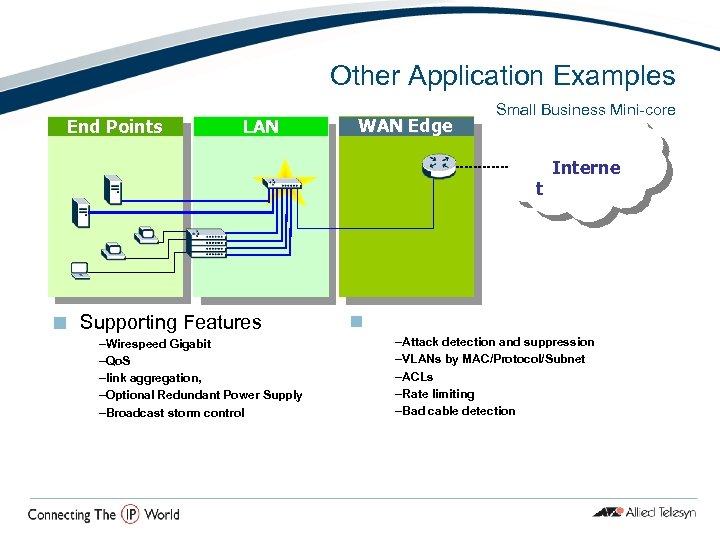
Other Application Examples End Points LAN WAN Edge Small Business Mini-core t ¢ Supporting Features –Wirespeed Gigabit –Qo. S –link aggregation, –Optional Redundant Power Supply –Broadcast storm control ¢ Interne s –Attack detection and suppression –VLANs by MAC/Protocol/Subnet –ACLs –Rate limiting –Bad cable detection

Most Compelling L 2 -4 Gigabit Switch AT-9424 ¢ Everything you expect and more… – Attack detection and suppression – Advanced Qo. S capabilities – L 2 -4 intelligence for custom security, management and Qo. S control
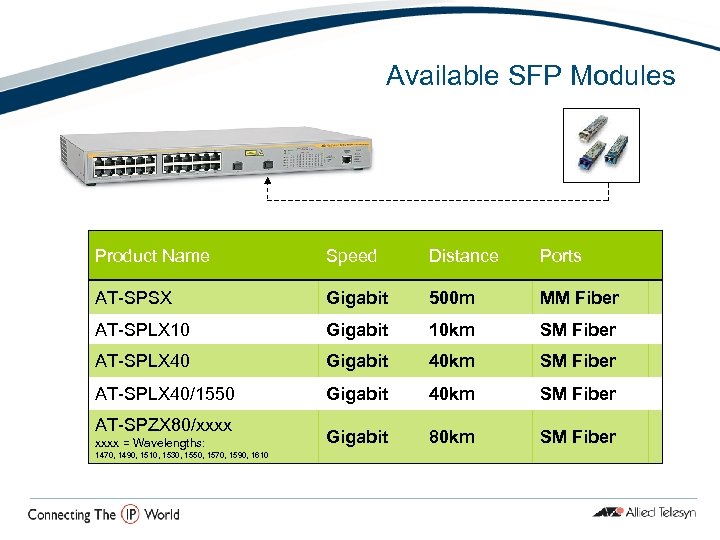
Available SFP Modules Product Name Speed Distance Ports AT-SPSX Gigabit 500 m MM Fiber AT-SPLX 10 Gigabit 10 km SM Fiber AT-SPLX 40 Gigabit 40 km SM Fiber AT-SPLX 40/1550 Gigabit 40 km SM Fiber Gigabit 80 km SM Fiber AT-SPZX 80/xxxx = Wavelengths: 1470, 1490, 1510, 1530, 1550, 1570, 1590, 1610
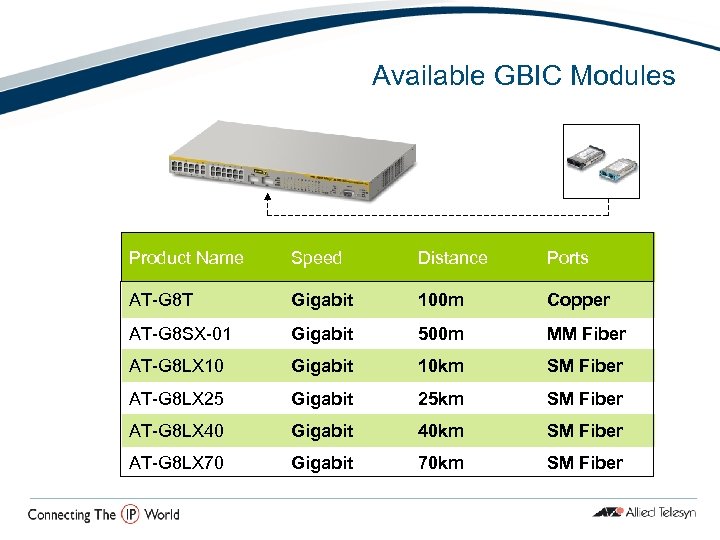
Available GBIC Modules Product Name Speed Distance Ports AT-G 8 T Gigabit 100 m Copper AT-G 8 SX-01 Gigabit 500 m MM Fiber AT-G 8 LX 10 Gigabit 10 km SM Fiber AT-G 8 LX 25 Gigabit 25 km SM Fiber AT-G 8 LX 40 Gigabit 40 km SM Fiber AT-G 8 LX 70 Gigabit 70 km SM Fiber
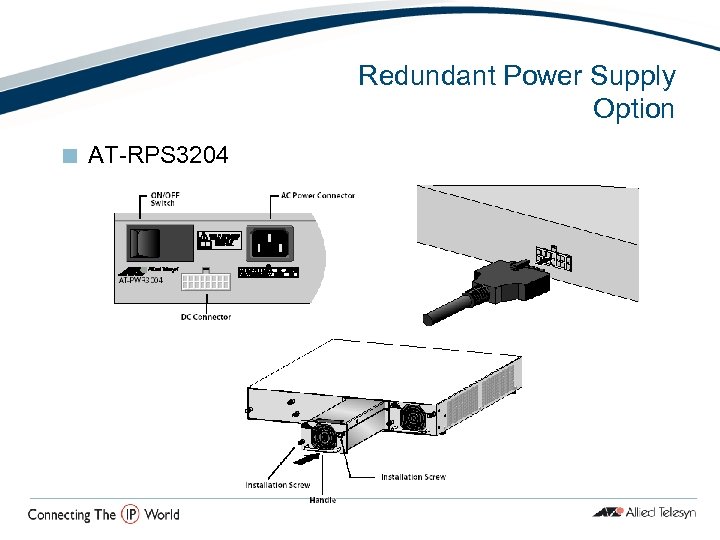
Redundant Power Supply Option ¢ AT-RPS 3204
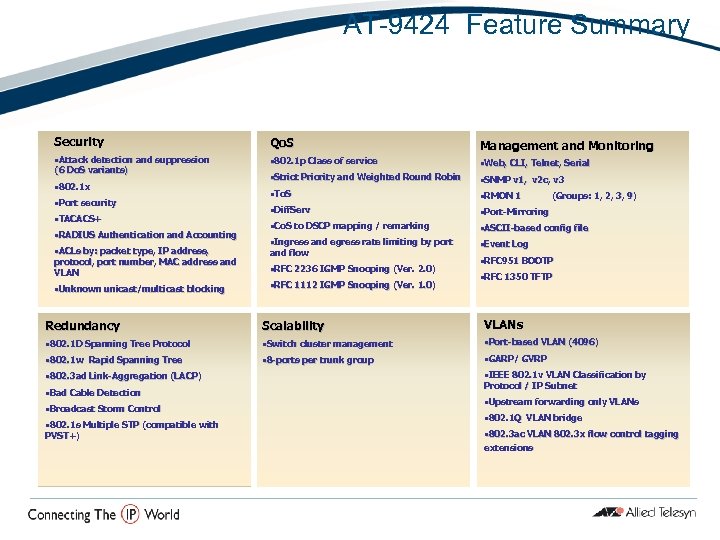
AT-9424 Feature Summary Security Qo. S Management and Monitoring • Attack detection and suppression • 802. 1 p Class of service • Web, CLI, Telnet, Serial • Strict Priority and Weighted Round Robin • SNMP v 1, v 2 c, v 3 • To. S • RMON 1 • Diff. Serv • Port-Mirroring • Co. S to DSCP mapping / remarking • ASCII-based config file • Ingress and egress rate limiting by port • Event Log (6 Do. S variants) • 802. 1 x • Port security • TACACS+ • RADIUS Authentication and Accounting • ACLs by: packet type, IP address, protocol, port number, MAC address and VLAN • Unknown unicast/multicast blocking unicast/multicast and flow • RFC 2236 IGMP Snooping (Ver. 2. 0) (Ver. • RFC 1112 IGMP Snooping (Ver. 1. 0) (Ver. (Groups: 1, 2, 3, 9) • RFC 951 BOOTP • RFC 1350 TFTP Redundancy Scalability VLANs • 802. 1 D Spanning Tree Protocol • Switch cluster management • Port-based VLAN (4096) • 802. 1 w Rapid Spanning Tree • 8 -ports per trunk group • GARP/ GVRP • 802. 3 ad Link-Aggregation (LACP) • Bad Cable Detection • Broadcast Storm Control • 802. 1 s Multiple STP (compatible with PVST+) • IEEE 802. 1 v VLAN Classification by Protocol / IP Subnet • Upstream forwarding only VLANs • 802. 1 Q VLAN bridge • 802. 3 ac VLAN 802. 3 x flow control tagging extensions
Thank You

Competitive Positioning AT-9424
Competitive Landscape ¢ ¢ ¢ 3 com Super. Stack 3 Switch 3824 3 com Super. Stack 3 Switch 3870 Cisco Catalyst 2970 G-24 TS HP Pro. Curve Switch 2824 Foundry Edge. Iron 24 GS (FES 2402 CF) Enterasys Matrix C 1 G 124 -24
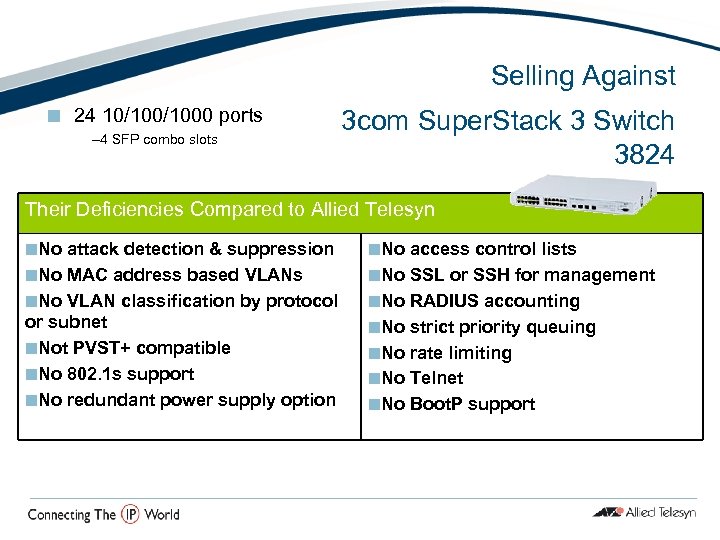
Selling Against ¢ 24 10/1000 ports – 4 SFP combo slots 3 com Super. Stack 3 Switch 3824 Their Deficiencies Compared to Allied Telesyn ¢No attack detection & suppression ¢No MAC address based VLANs ¢No VLAN classification by protocol or subnet ¢Not PVST+ compatible ¢No 802. 1 s support ¢No redundant power supply option ¢No access control lists ¢No SSL or SSH for management ¢No RADIUS accounting ¢No strict priority queuing ¢No rate limiting ¢No Telnet ¢No Boot. P support
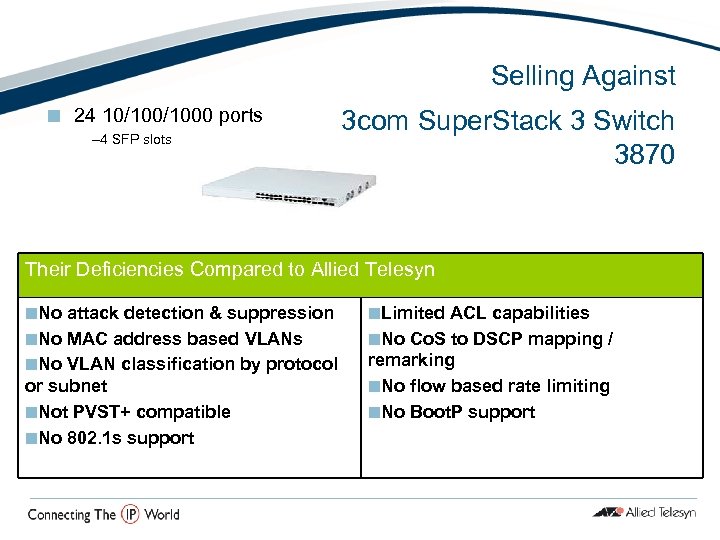
Selling Against ¢ 24 10/1000 ports – 4 SFP slots 3 com Super. Stack 3 Switch 3870 Their Deficiencies Compared to Allied Telesyn ¢No attack detection & suppression ¢No MAC address based VLANs ¢No VLAN classification by protocol or subnet ¢Not PVST+ compatible ¢No 802. 1 s support ¢Limited ACL capabilities ¢No Co. S to DSCP mapping / remarking ¢No flow based rate limiting ¢No Boot. P support
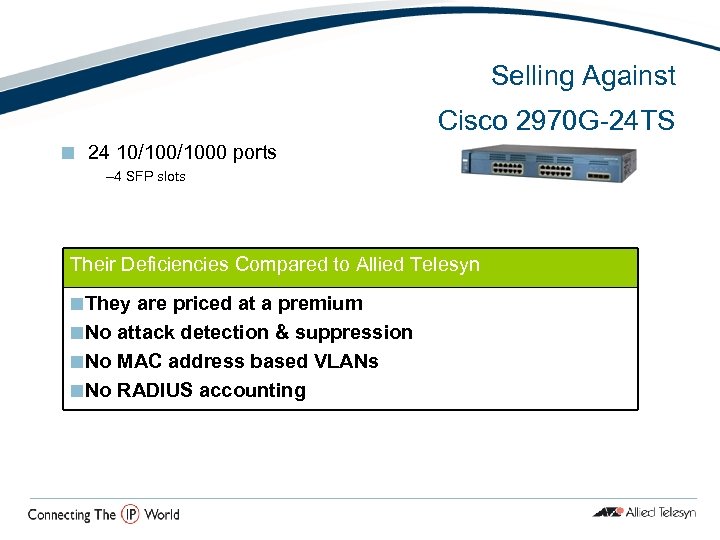
Selling Against Cisco 2970 G-24 TS ¢ 24 10/1000 ports – 4 SFP slots Their Deficiencies Compared to Allied Telesyn ¢They are priced at a premium ¢No attack detection & suppression ¢No MAC address based VLANs ¢No RADIUS accounting
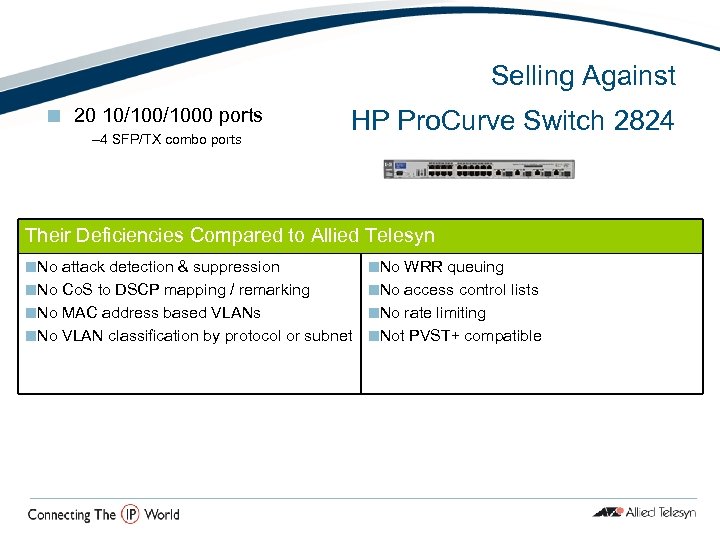
Selling Against ¢ 20 10/1000 ports – 4 SFP/TX combo ports HP Pro. Curve Switch 2824 Their Deficiencies Compared to Allied Telesyn ¢No attack detection & suppression ¢No WRR queuing ¢No Co. S to DSCP mapping / remarking ¢No access control lists ¢No MAC address based VLANs ¢No rate limiting ¢No VLAN classification by protocol or subnet ¢Not PVST+ compatible
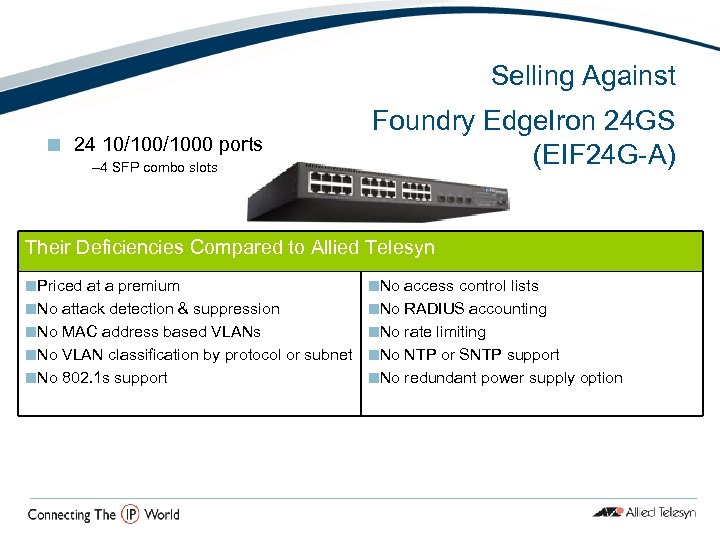
Selling Against Foundry Edge. Iron 24 GS (EIF 24 G-A) ¢ 24 10/1000 ports – 4 SFP combo slots Their Deficiencies Compared to Allied Telesyn ¢Priced at a premium ¢No access control lists ¢No attack detection & suppression ¢No RADIUS accounting ¢No MAC address based VLANs ¢No rate limiting ¢No VLAN classification by protocol or subnet ¢No NTP or SNTP support ¢No 802. 1 s support ¢No redundant power supply option
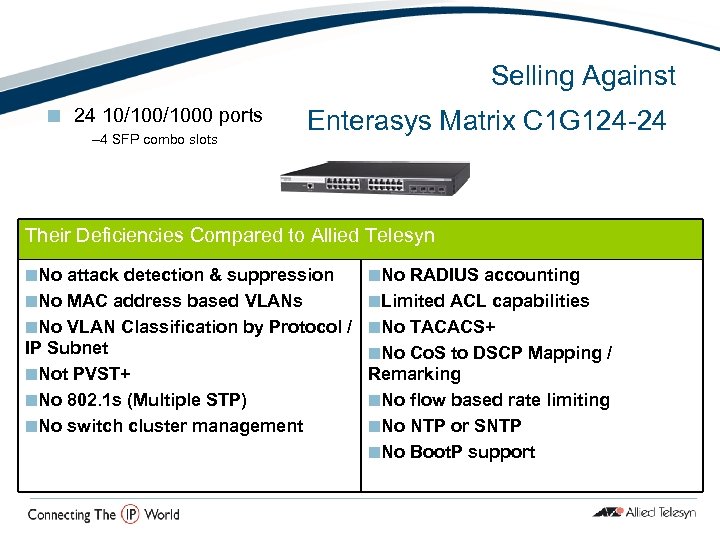
Selling Against ¢ 24 10/1000 ports – 4 SFP combo slots Enterasys Matrix C 1 G 124 -24 Their Deficiencies Compared to Allied Telesyn ¢No attack detection & suppression ¢No MAC address based VLANs ¢No VLAN Classification by Protocol / IP Subnet ¢Not PVST+ ¢No 802. 1 s (Multiple STP) ¢No switch cluster management ¢No RADIUS accounting ¢Limited ACL capabilities ¢No TACACS+ ¢No Co. S to DSCP Mapping / Remarking ¢No flow based rate limiting ¢No NTP or SNTP ¢No Boot. P support
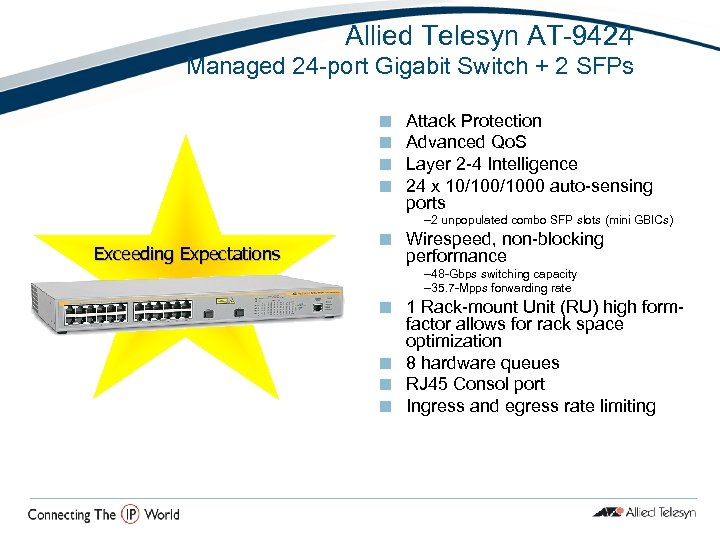
Allied Telesyn AT-9424 Managed 24 -port Gigabit Switch + 2 SFPs ¢ ¢ Attack Protection Advanced Qo. S Layer 2 -4 Intelligence 24 x 10/1000 auto-sensing ports – 2 unpopulated combo SFP slots (mini GBICs) Exceeding Expectations ¢ Wirespeed, non-blocking performance – 48 -Gbps switching capacity – 35. 7 -Mpps forwarding rate 1 Rack-mount Unit (RU) high formfactor allows for rack space optimization ¢ 8 hardware queues ¢ RJ 45 Consol port ¢ Ingress and egress rate limiting ¢

Thank You
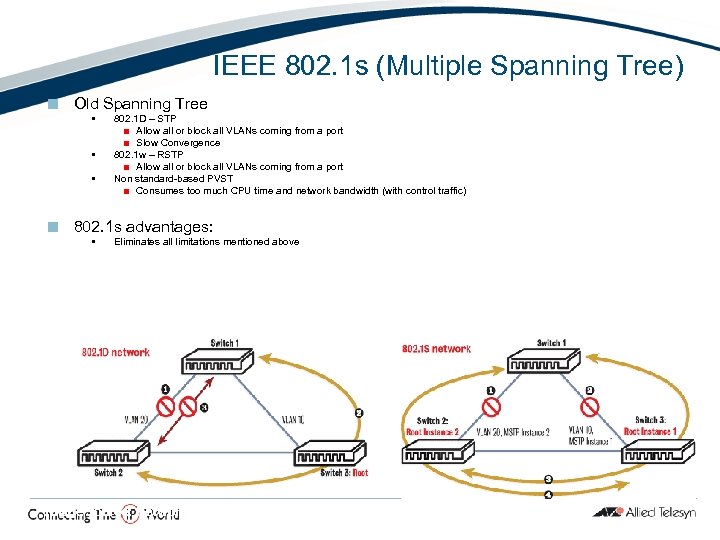
IEEE 802. 1 s (Multiple Spanning Tree) ¢ Old Spanning Tree • • • ¢ 802. 1 D – STP ¢ Allow all or block all VLANs coming from a port ¢ Slow Convergence 802. 1 w – RSTP ¢ Allow all or block all VLANs coming from a port Non standard-based PVST ¢ Consumes too much CPU time and network bandwidth (with control traffic) 802. 1 s advantages: • Eliminates all limitations mentioned above Image Source: Network. World. Fusion, ‘ 802. 1 s solves architecture issues’ 08/04/03
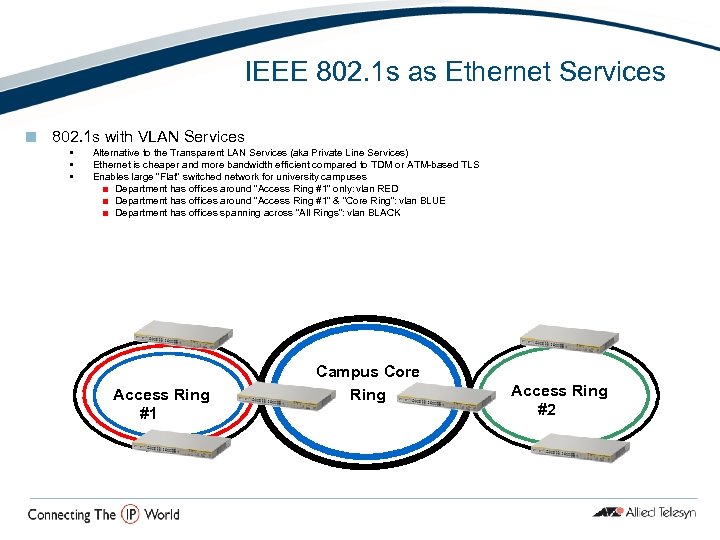
IEEE 802. 1 s as Ethernet Services ¢ 802. 1 s with VLAN Services • • • Alternative to the Transparent LAN Services (aka Private Line Services) Ethernet is cheaper and more bandwidth efficient compared to TDM or ATM-based TLS Enables large “Flat” switched network for university campuses ¢ Department has offices around “Access Ring #1” only: vlan RED ¢ Department has offices around “Access Ring #1” & “Core Ring”: vlan BLUE ¢ Department has offices spanning across “All Rings”: vlan BLACK Access Ring #1 Campus Core Ring Access Ring #2
IEEE 802. 1 x (Port-Based Network Access Control) ¢ Prevents unauthorized use of network resources, such as: Bandwidth and Servers ¢ “Multi-Supplicant” and “Authenticator” modes are supported to allow indirect and direct host attachments ¢ Verified with all popular 802. 1 x clients, such as: Win-XP, Aegis Meeting House ¢ 8500 offers “Tiered Security” with 802. 1 x authentication and Do. S-attack protecttion
71c6918f117da14cca36e3cb8d71f039.ppt