608e9c627b177af0ee222bfd028d08c8.ppt
- Количество слайдов: 18
Application of Attribute Certificates in S/MIME 47 th IETF Conference Adelaide, March 2000 Greg Colla & Michael Zolotarev Baltimore Technologies IETF 47, Mar 2000, Adelaide
Attribute Certificates & S/MIME Overview • S/MIME and PK Certificates • S/MIME Problems • Secure mail requirements • Possible solutions • E-mail Attribute Certificates • Practical Implementation • Issues IETF 47, Mar 2000, Adelaide
Attribute Certificates & S/MIME Certificate Usage alice@foo. com cn=Alice subj. Alt. Name=alice@foo. com Verification – check signer’s e-mail address against sender’s address Encryption – obtaining “encryptee’s” public key certificate IETF 47, Mar 2000, Adelaide
Attribute Certificates & S/MIME Problems • Multiple e-mail addresses – User has multiple e-mail addresses • Maintenance of e-mail addresses – Change company name (and Internet domain) • Security Proxy – a proxy signs and decrypts on behalf of many users • Privacy/Spam alice@foo. com alice@dev. foo. com alice@bar. com IETF 47, Mar 2000, Adelaide
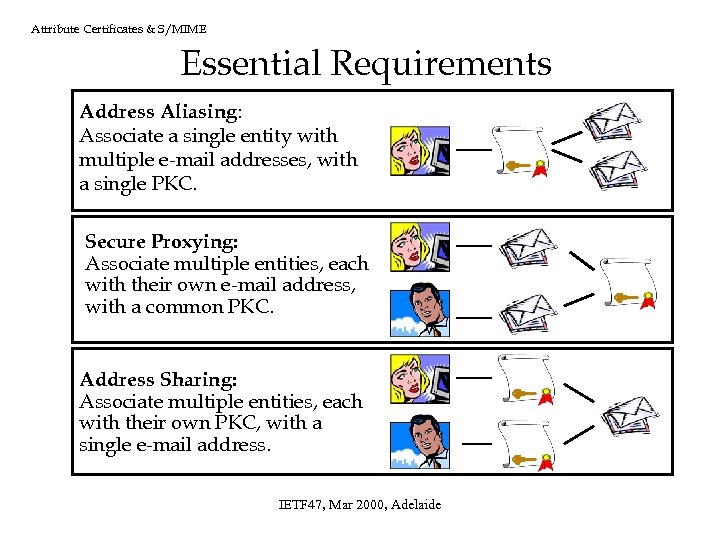
Attribute Certificates & S/MIME Essential Requirements Address Aliasing: Associate a single entity with multiple e-mail addresses, with a single PKC. Secure Proxying: Associate multiple entities, each with their own e-mail address, with a common PKC. Address Sharing: Associate multiple entities, each with their own PKC, with a single e-mail address. IETF 47, Mar 2000, Adelaide
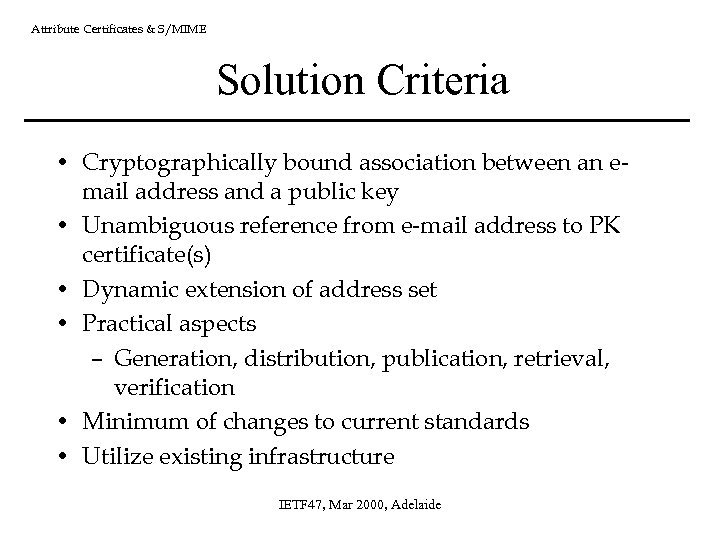
Attribute Certificates & S/MIME Solution Criteria • Cryptographically bound association between an email address and a public key • Unambiguous reference from e-mail address to PK certificate(s) • Dynamic extension of address set • Practical aspects – Generation, distribution, publication, retrieval, verification • Minimum of changes to current standards • Utilize existing infrastructure IETF 47, Mar 2000, Adelaide
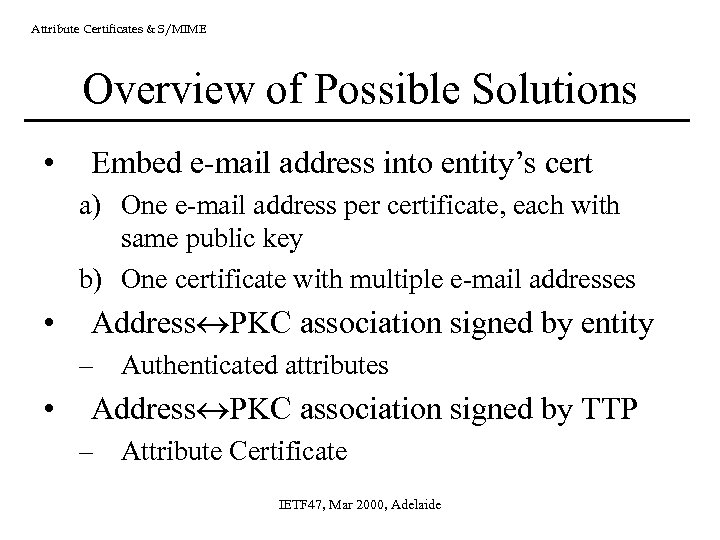
Attribute Certificates & S/MIME Overview of Possible Solutions • Embed e-mail address into entity’s cert a) One e-mail address per certificate, each with same public key b) One certificate with multiple e-mail addresses • Address PKC association signed by entity – Authenticated attributes • Address PKC association signed by TTP – Attribute Certificate IETF 47, Mar 2000, Adelaide
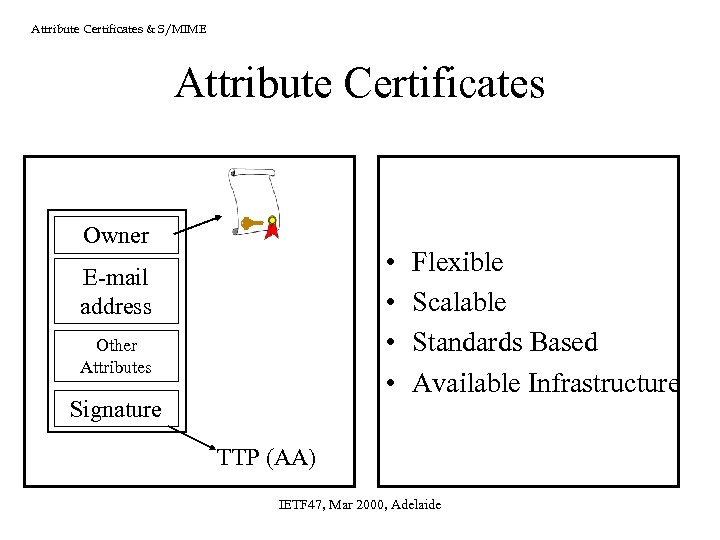
Attribute Certificates & S/MIME Attribute Certificates Owner • • E-mail address Other Attributes Signature Flexible Scalable Standards Based Available Infrastructure TTP (AA) IETF 47, Mar 2000, Adelaide
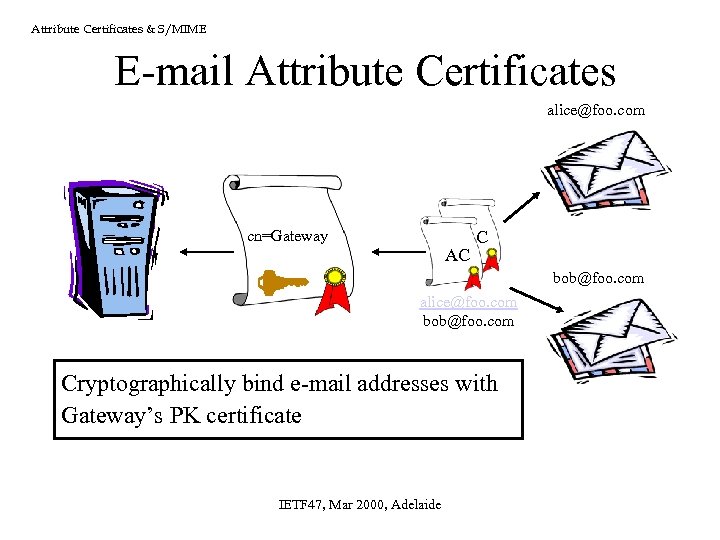
Attribute Certificates & S/MIME E-mail Attribute Certificates alice@foo. com cn=Gateway AC AC bob@foo. com alice@foo. com bob@foo. com Cryptographically bind e-mail addresses with Gateway’s PK certificate IETF 47, Mar 2000, Adelaide
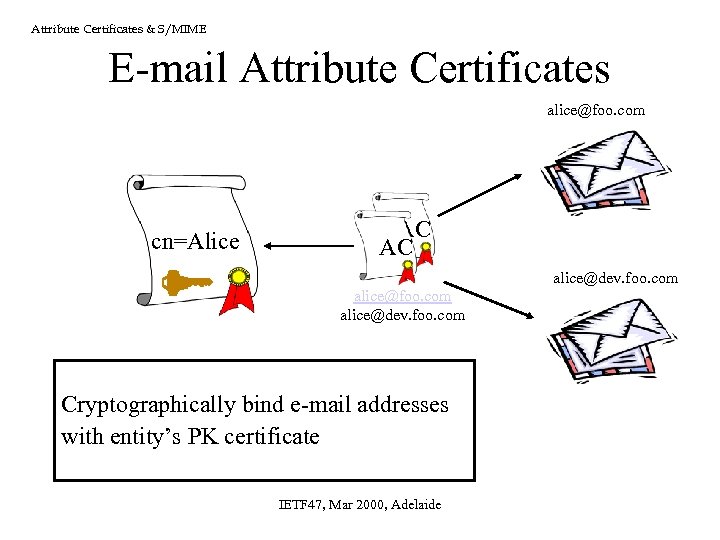
Attribute Certificates & S/MIME E-mail Attribute Certificates alice@foo. com cn=Alice AC AC alice@dev. foo. com Cryptographically bind e-mail addresses with entity’s PK certificate IETF 47, Mar 2000, Adelaide
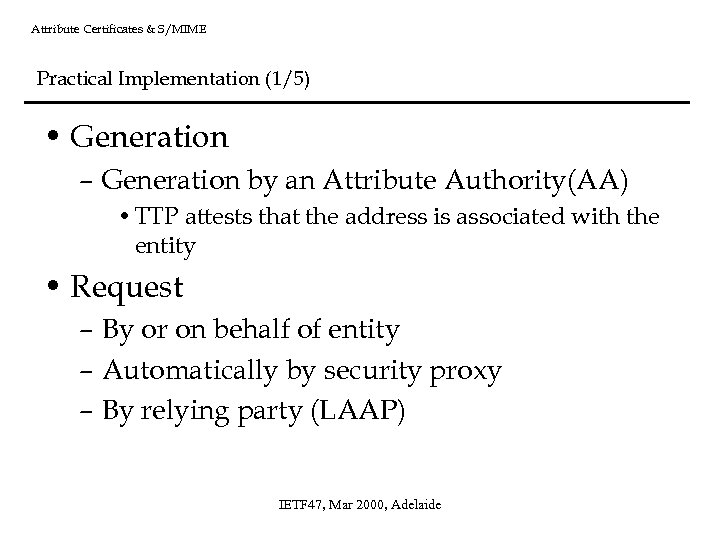
Attribute Certificates & S/MIME Practical Implementation (1/5) • Generation – Generation by an Attribute Authority(AA) • TTP attests that the address is associated with the entity • Request – By or on behalf of entity – Automatically by security proxy – By relying party (LAAP) IETF 47, Mar 2000, Adelaide
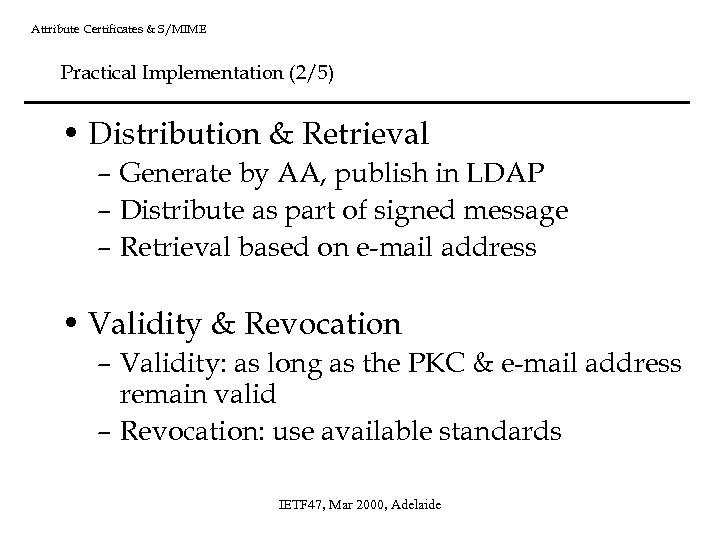
Attribute Certificates & S/MIME Practical Implementation (2/5) • Distribution & Retrieval – Generate by AA, publish in LDAP – Distribute as part of signed message – Retrieval based on e-mail address • Validity & Revocation – Validity: as long as the PKC & e-mail address remain valid – Revocation: use available standards IETF 47, Mar 2000, Adelaide
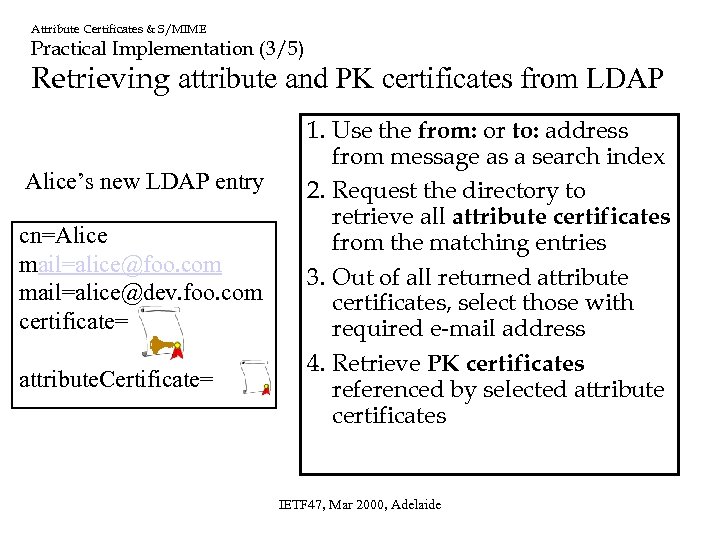
Attribute Certificates & S/MIME Practical Implementation (3/5) Retrieving attribute and PK certificates from LDAP Alice’s new LDAP entry cn=Alice mail=alice@foo. com mail=alice@dev. foo. com certificate= attribute. Certificate= 1. Use the from: or to: address from message as a search index 2. Request the directory to retrieve all attribute certificates from the matching entries 3. Out of all returned attribute certificates, select those with required e-mail address 4. Retrieve PK certificates referenced by selected attribute certificates IETF 47, Mar 2000, Adelaide
Attribute Certificates & S/MIME Practical Implementation (4/5) Message Verification Walkthrough – Retrieve e-mail AC(s) using sender’s address as index – Retrieve PKC(s) referenced by AC(s) – Identify signing certificate – Validate. . . – Validate the message IETF 47, Mar 2000, Adelaide
Attribute Certificates & S/MIME Practical Implementation (5/5) Message Encryption Walkthrough – Retrieve e-mail AC(s) using recipient’s address as index – Validate. . . – Retrieve PKC(s) referenced by valid e-mail AC(s) – Validate. . . – Encrypt the message using valid encryption certificate(s) IETF 47, Mar 2000, Adelaide
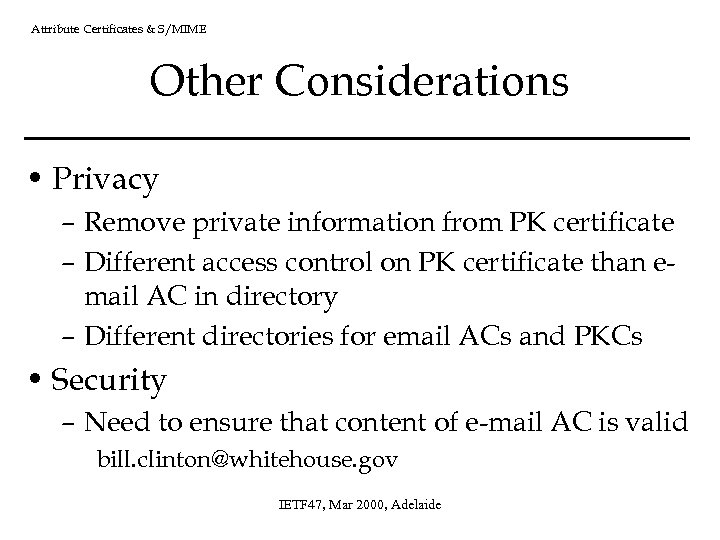
Attribute Certificates & S/MIME Other Considerations • Privacy – Remove private information from PK certificate – Different access control on PK certificate than email AC in directory – Different directories for email ACs and PKCs • Security – Need to ensure that content of e-mail AC is valid bill. clinton@whitehouse. gov IETF 47, Mar 2000, Adelaide
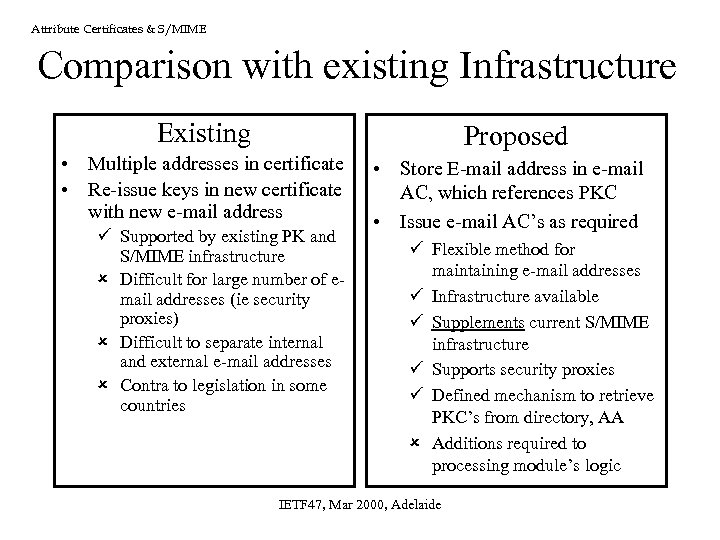
Attribute Certificates & S/MIME Comparison with existing Infrastructure Existing Proposed • Multiple addresses in certificate • Re-issue keys in new certificate with new e-mail address ü Supported by existing PK and S/MIME infrastructure û Difficult for large number of email addresses (ie security proxies) û Difficult to separate internal and external e-mail addresses û Contra to legislation in some countries • Store E-mail address in e-mail AC, which references PKC • Issue e-mail AC’s as required ü Flexible method for maintaining e-mail addresses ü Infrastructure available ü Supplements current S/MIME infrastructure ü Supports security proxies ü Defined mechanism to retrieve PKC’s from directory, AA û Additions required to processing module’s logic IETF 47, Mar 2000, Adelaide
Attribute Certificates & S/MIME Summary • Maintenance of e-mail addresses limits S/MIME usability • Attribute Certificates cryptographically bind e-mail addresses with PK certificates • E-mail Attribute Certificates provide a flexible solution for maintaining e-mail addresses • Supplements current infrastructure • Localized modifications required to S/MIME components to utilize E-mail ACs • E-mail ACs can be used to solve other S/MIME limitations IETF 47, Mar 2000, Adelaide
608e9c627b177af0ee222bfd028d08c8.ppt