cc937a09a5a3cf8472eebf6b57f69c61.ppt
- Количество слайдов: 20
ACM/IEEE NSys. S 2017 BUET, Dhaka, Bangladesh “A Security-Aware Near Field Communication Architecture” 5– 8 January 2017
ACM/IEEE NSys. S 2017 BUET, Dhaka, Bangladesh “A Security-Aware Near Field Communication Architecture” Author, Presenter: Dr. Abu Asaduzzaman, Associate Professor Director of CAPPLab and Advisor of the IEEE Student Branch at Wichita State Department of Electrical Engineering and Computer Science (EECS) Wichita State University (WSU), USA 5– 8 January 2017
“A Security-Aware Near Field Communication Architecture” Outline ■ Introduction to NFC Technology Ø Short-range wireless communication, many applications - Io. T Ø Suffers due to different types of network attacks ■ Background and Motivation Ø Easy/efficient to use, convenient, growing; Secure Element (SE) is unable to provide security for all NFC applications ■ Proposed NFC Architecture with Secure Protocol Ø Novel secure protocol along with the NFC chip Ø Modified NFC Data Exchange Format (NDEF) and Alert Mechanism ■ Experimental Results, Conclusions ■ Q/A, Discussion QUESTIONS? Any time, please! ■ Contact Information Dr. Zaman 3
“A Security-Aware Near Field Communication Architecture” Authors ■ Abu Asaduzzaman, Associate Professor § EECS Department, Wichita State University, USA ■ Shanta Mazumder, MS Student § EECS Department, Wichita State University, USA ■ Sergio Selinas, Assistant Professor § EECS Department, Wichita State University, USA ■ Muhammad F. Mridha, Assistant Professor § CSE Department, University of Asia Pacific, Bangladesh Dr. Zaman 4
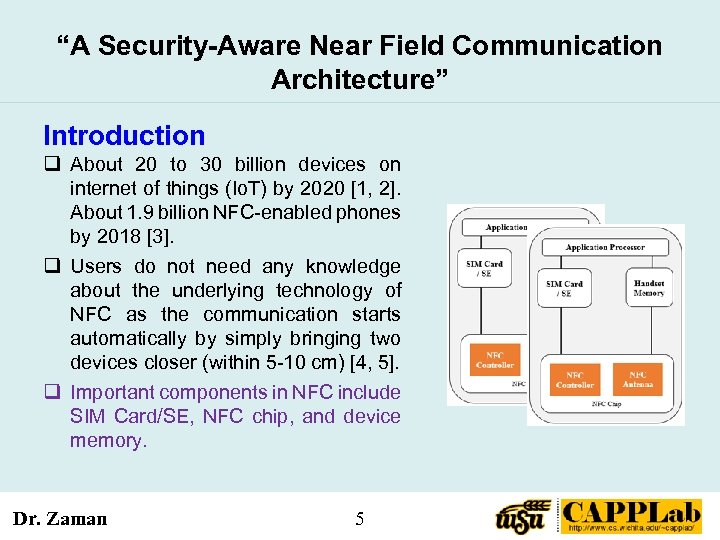
“A Security-Aware Near Field Communication Architecture” Introduction q About 20 to 30 billion devices on internet of things (Io. T) by 2020 [1, 2]. About 1. 9 billion NFC-enabled phones by 2018 [3]. q Users do not need any knowledge about the underlying technology of NFC as the communication starts automatically by simply bringing two devices closer (within 5 -10 cm) [4, 5]. q Important components in NFC include SIM Card/SE, NFC chip, and device memory. Dr. Zaman 5
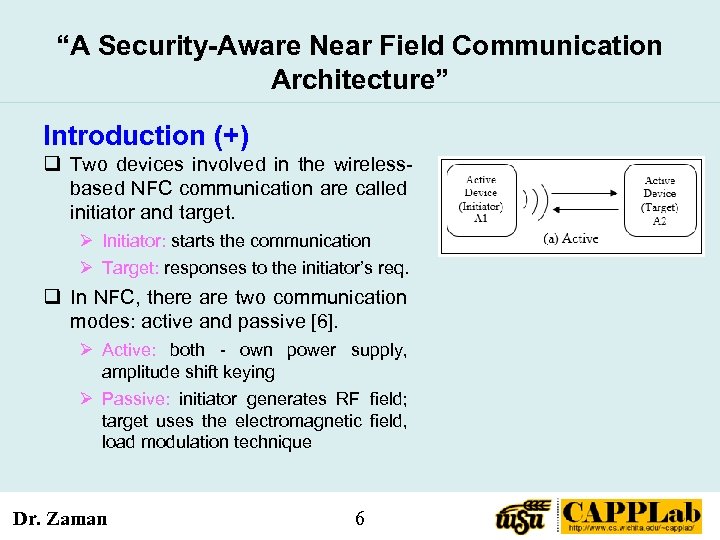
“A Security-Aware Near Field Communication Architecture” Introduction (+) q Two devices involved in the wirelessbased NFC communication are called initiator and target. Ø Initiator: starts the communication Ø Target: responses to the initiator’s req. q In NFC, there are two communication modes: active and passive [6]. Ø Active: both - own power supply, amplitude shift keying Ø Passive: initiator generates RF field; target uses the electromagnetic field, load modulation technique Dr. Zaman 6
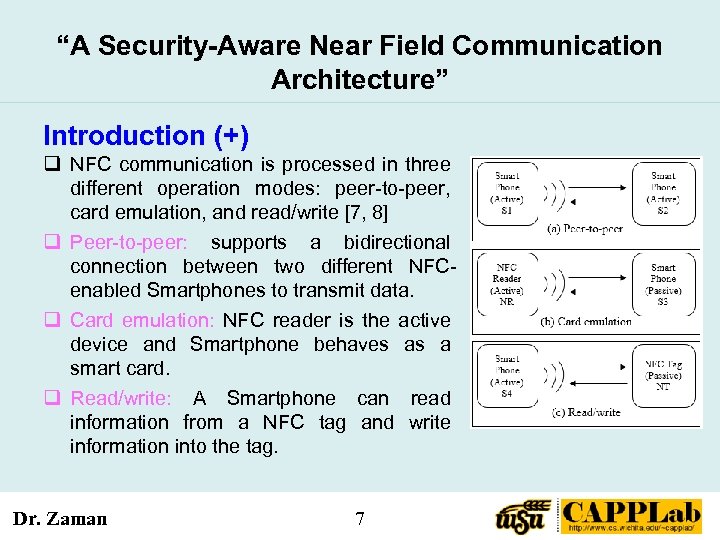
“A Security-Aware Near Field Communication Architecture” Introduction (+) q NFC communication is processed in three different operation modes: peer-to-peer, card emulation, and read/write [7, 8] q Peer-to-peer: supports a bidirectional connection between two different NFCenabled Smartphones to transmit data. q Card emulation: NFC reader is the active device and Smartphone behaves as a smart card. q Read/write: A Smartphone can read information from a NFC tag and write information into the tag. Dr. Zaman 7
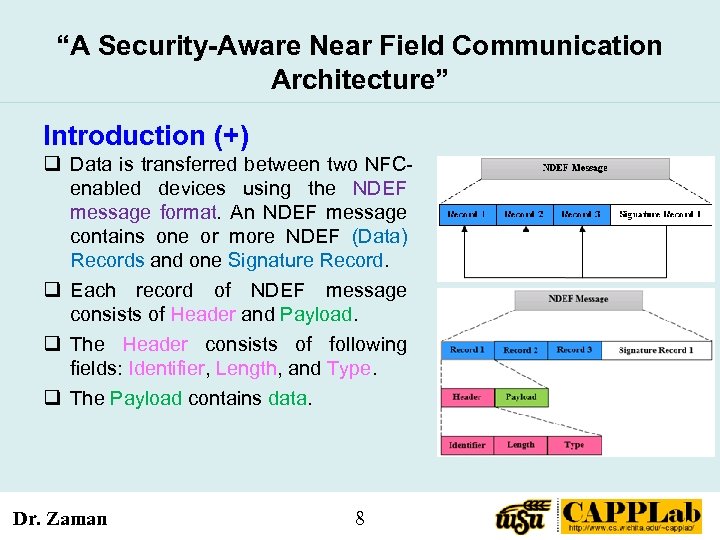
“A Security-Aware Near Field Communication Architecture” Introduction (+) q Data is transferred between two NFCenabled devices using the NDEF message format. An NDEF message contains one or more NDEF (Data) Records and one Signature Record. q Each record of NDEF message consists of Header and Payload. q The Header consists of following fields: Identifier, Length, and Type. q The Payload contains data. Dr. Zaman 8
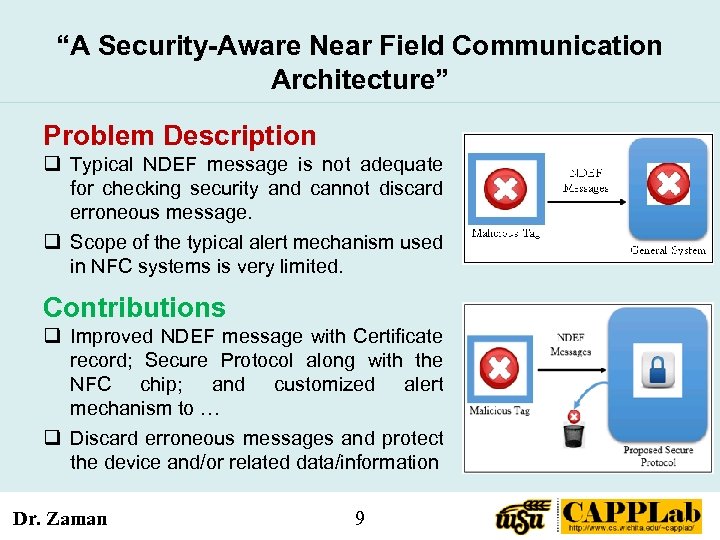
“A Security-Aware Near Field Communication Architecture” Problem Description q Typical NDEF message is not adequate for checking security and cannot discard erroneous message. q Scope of the typical alert mechanism used in NFC systems is very limited. Contributions q Improved NDEF message with Certificate record; Secure Protocol along with the NFC chip; and customized alert mechanism to … q Discard erroneous messages and protect the device and/or related data/information Dr. Zaman 9
“A Security-Aware Near Field Communication Architecture” Outline ■ Introduction to NFC Technology Ø Short-range wireless communication, many applications - Io. T Ø Suffers due to different types of network attacks ■ Background and Motivation Ø Easy/efficient to use, convenient, growing; Secure Element (SE) is unable to provide security for all NFC applications ■ Proposed NFC Architecture with Secure Protocol Ø Novel secure protocol along with the NFC chip Ø Modified NFC Data Exchange Format (NDEF) and Alert Mechanism ■ Experimental Results, Conclusions ■ Q/A, Discussion QUESTIONS? Any time, please! ■ Contact Information Dr. Zaman 10
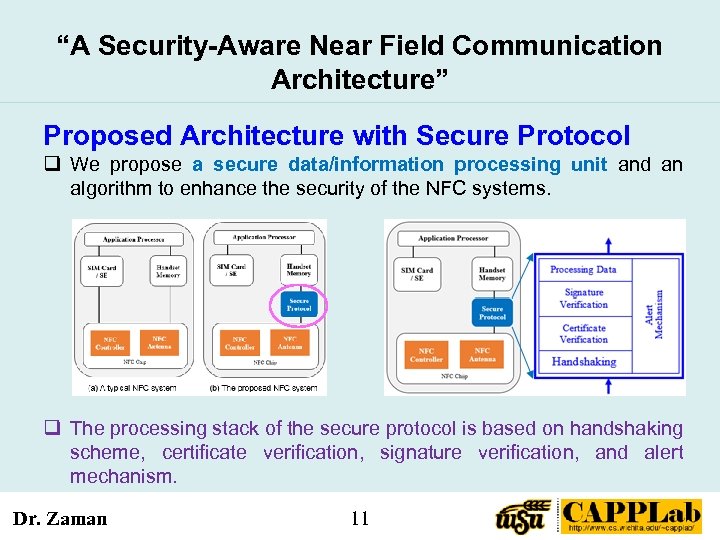
“A Security-Aware Near Field Communication Architecture” Proposed Architecture with Secure Protocol q We propose a secure data/information processing unit and an algorithm to enhance the security of the NFC systems. q The processing stack of the secure protocol is based on handshaking scheme, certificate verification, signature verification, and alert mechanism. Dr. Zaman 11
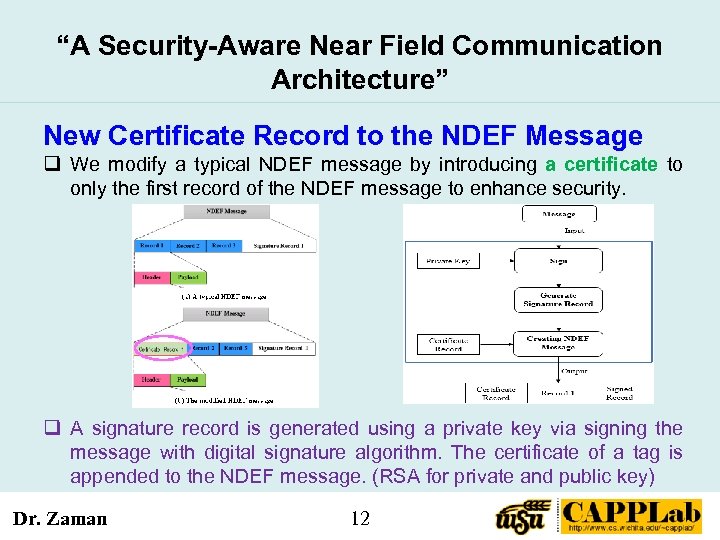
“A Security-Aware Near Field Communication Architecture” New Certificate Record to the NDEF Message q We modify a typical NDEF message by introducing a certificate to only the first record of the NDEF message to enhance security. q A signature record is generated using a private key via signing the message with digital signature algorithm. The certificate of a tag is appended to the NDEF message. (RSA for private and public key) Dr. Zaman 12
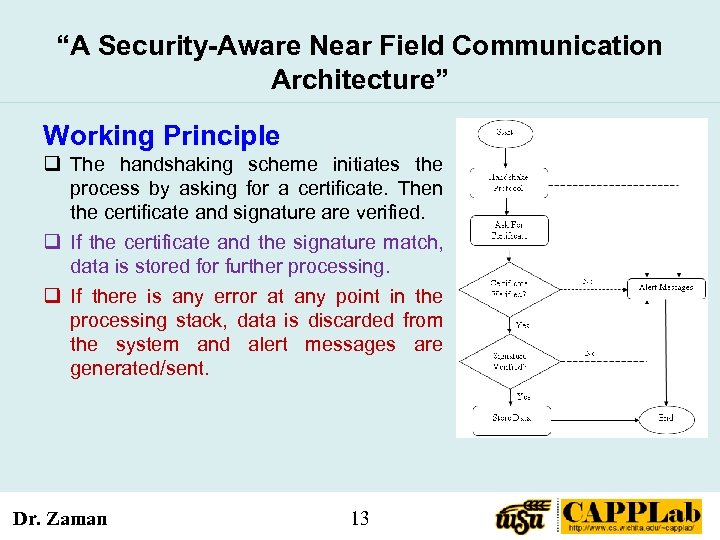
“A Security-Aware Near Field Communication Architecture” Working Principle q The handshaking scheme initiates the process by asking for a certificate. Then the certificate and signature are verified. q If the certificate and the signature match, data is stored for further processing. q If there is any error at any point in the processing stack, data is discarded from the system and alert messages are generated/sent. Dr. Zaman 13
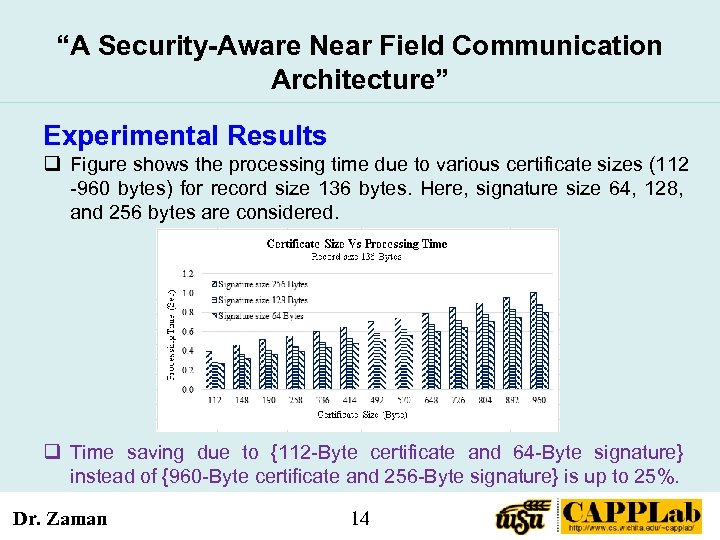
“A Security-Aware Near Field Communication Architecture” Experimental Results q Figure shows the processing time due to various certificate sizes (112 -960 bytes) for record size 136 bytes. Here, signature size 64, 128, and 256 bytes are considered. q Time saving due to {112 -Byte certificate and 64 -Byte signature} instead of {960 -Byte certificate and 256 -Byte signature} is up to 25%. Dr. Zaman 14
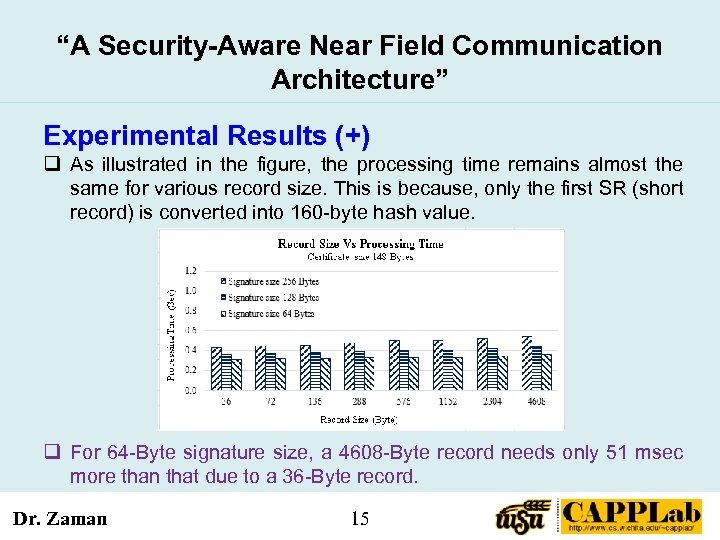
“A Security-Aware Near Field Communication Architecture” Experimental Results (+) q As illustrated in the figure, the processing time remains almost the same for various record size. This is because, only the first SR (short record) is converted into 160 -byte hash value. q For 64 -Byte signature size, a 4608 -Byte record needs only 51 msec more than that due to a 36 -Byte record. Dr. Zaman 15
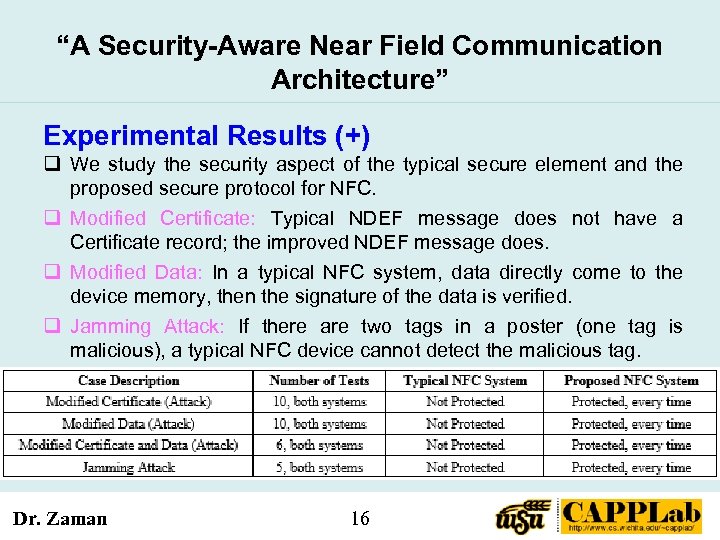
“A Security-Aware Near Field Communication Architecture” Experimental Results (+) q We study the security aspect of the typical secure element and the proposed secure protocol for NFC. q Modified Certificate: Typical NDEF message does not have a Certificate record; the improved NDEF message does. q Modified Data: In a typical NFC system, data directly come to the device memory, then the signature of the data is verified. q Jamming Attack: If there are two tags in a poster (one tag is malicious), a typical NFC device cannot detect the malicious tag. Dr. Zaman 16
“A Security-Aware Near Field Communication Architecture” Conclusions ■ In this work, a data processing unit for NFC systems is proposed to provide extra security. ■ Before storing data in the device memory, the proposed secure protocol checks the signature of the sender and newly introduced certificate of the NDEF message. If both (signature and certificate) are not verified, an alert message is generated and data is discarded. ■ According to the experimental results, the NFC technology helps save transfer time up to 24% and power up to 62% when compared those with Bluetooth technology. Dr. Zaman 17
“A Security-Aware Near Field Communication Architecture” Conclusions (+) ■ MATLAB simulation results show that the processing time increases linearly with the increase of the certificate size making the system scalable. Simulation results also show that the processing time remains almost the same for various record sizes. ■ Although the proposed system may require little extra time due to the addition of the secure protocol, it offers better security on various networking attacks. ■ The proposed secure processing technique for NFC systems can be extended to heighten the security of Io. T applications and NFC devices. Dr. Zaman 18
![“A Security-Aware Near Field Communication Architecture” References [1] K. Ok, V. Coskun, M. N. “A Security-Aware Near Field Communication Architecture” References [1] K. Ok, V. Coskun, M. N.](https://present5.com/presentation/cc937a09a5a3cf8472eebf6b57f69c61/image-19.jpg)
“A Security-Aware Near Field Communication Architecture” References [1] K. Ok, V. Coskun, M. N. Aydin, and B. Ozdenizci, “Current benefits and future directions of NFC services, ” IEEE Int’l Conf. on Education and Management Tech. (ICEMT), pp. 334 -338, Nov. 2010. [2] K. Ok, M. N. Aydin, V. Coskun, and B. Ozdenizci, “Exploring underlying values of NFC applications, ” International Conference on Information and Financial Engineering IPEDR, Vol. 12, 2011. [3] R. Boden, “IDATE forecasts NFC phones and payments volumes, ” NFC World, 2014. http: //www. nfcworld. com/2014/07/15/330373/idate-forecasts-nfc-phones-payments-volumes/ [4] B. Ozdenizci, M. Alsadi, K. Ok, and V. Coskun, “Classification of NFC Applications in Diverse Service Domains, ” Int’l J. of Computer and Communication Engineering, Vol. 2, No. 5, pp. 614 -620, 2013. [5] N. A. Chattha, “NFC—Vulnerabilities and defense, ” IEEE Conference on Information Assurance and Cyber Security (CIACS), pp. 35 -38, June 2014. [6] M. Riyazuddin, “NFC: A review of the technology, applications and security, ” ABI Research, 2011. [7] P. S. Halgaonkar, S. Jain, and V. M. Wadhai, “NFC: A review of technology, tags, applications and security, ” IJRCCT, Vol. 2, No. 10, pp. 979 -987, 2013. [8] S. Burkard, “MS Thesis – Near field communication in smartphones, ” Computer Engineering Dept. of Telecommunication Systems, Berlin Institute of Technology, Germany, 2012. Dr. Zaman 19
ACM/IEEE NSys. S 2017 at BUET, Dhaka, Bangladesh “A Security-Aware Near Field Communication Architecture” QUESTIONS? Contact: Abu Asaduzzaman E-mail: abuasaduzzaman@ieee. org Phone: +1 -316 -978 -5261 CAPPLab: http: //www. cs. wichita. edu/~capplab/ Thank You!
cc937a09a5a3cf8472eebf6b57f69c61.ppt