ab4546042a871a92a5eacbd3c58bff75.ppt
- Количество слайдов: 34

ACCORD -TSHM Accord. Reliabilityin an unreliableworld. Moscow, 2009
Why does this happen — you are using various information security products, yet the information still leaks out ?
In order toprovide security, and not simply protect, it is necessary to understand what exactly is the OBJECT OF PROTECTION.
The objects of information protection are defined by the things that the intruders ’ activities may be aimed at:
The goals of the information protection are definedin accordance with the objects:
The goals of the information protection are solvedby using the unauthorized access controlproduct Accord-TSHM and the information protection systems, which are based on it.
The computer protection from an unauthorized access is reached by providing the operating system trusted startup mode, which guarantees that:
Accord-TSHM: Trusted startup hardware module Provides a trusted startup of the operating system, irrespective of its type, for an authenticated user.
What is secure boot? The operating system boot is performed only after a successful completion of the following procedures:

Accord-TSHM— protection from an unauthorized access

Accord-TSHM— protection from an unauthorized access
An unauthorized access control product Accord-TSHM consists of the hardware and software tools :
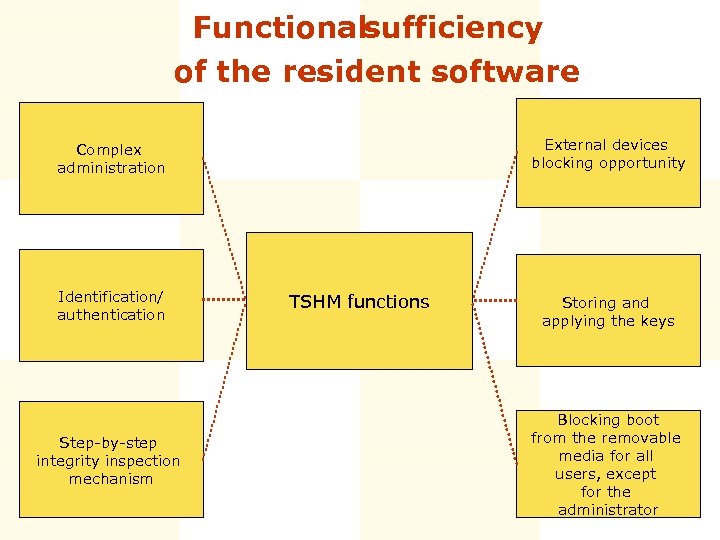
Functionalsufficiency of the resident software External devices blocking opportunity Complex administration Identification/ authentication Step-by-step integrity inspection mechanism TSHM functions Storing and applying the keys Blocking boot from the removable media for all users, except for the administrator
The main versions of Accord-TSHM include the controllers:

Accord-TSHM Accord-5 MX controller-based

Accord-TSHM Accord-5. 5 controller-based

Accord-TSHM Accord-5. 5 controller-based

Accord-TSHM Accord-5. 5 controller-based
Accord-TSHM may also include the controllers:

Accord-TSHM Accord-4. 5 controller-based

Accord-TSHM Accord 5 МХ mini-PCI controller-based
Individual packaging in accordance with the customer’s requirement, Accord-TSHMand Accord-TSHM-based systems may use various identifiers:
All of the Accord-TSHM modifications
All of the Accord-TSHM modifications
All of the Accord-TSHM modifications
System administration:
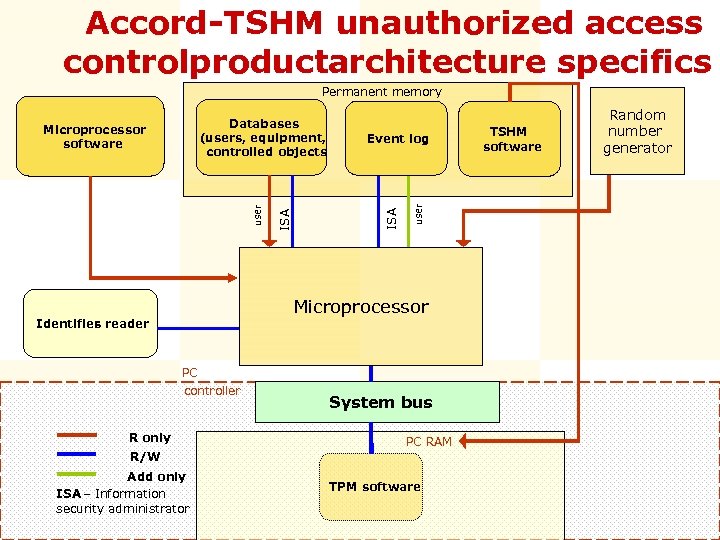
Accord-TSHM unauthorized access controlproductarchitecture specifics Permanent memory user Event log ISA user Microprocessor software ISA Databases (users, equipment, controlled objects Microprocessor Identifier reader s PC controller R only System bus PC RAM R/W Add only ISA – Information security administrator TPM software TSHM software Random number generator
Reliabilityin an unreliableworld: The Accord-TSHM architecture provides:
Delimitation of the data access rights is provided by the hardware/software complexes, based on Accord-TSHM and special software
Information protection management based on theprotected network data exchange is provided by the Accord -RAU subsystem, which joins the automated workplace of the information security administrator (AWP ISA) and the user terminals, equipped with the Accord-AMDZ-based hardware/software complexes.
Cryptographic algorithm s for the information technolog protection ies and data transfer in a protected form have been realized in the Accord -5. 5 controller, which may be used for data encryption, signing its electronic digital signature and protecting the information technologies with the help of the authentication protection codes (APC).
Certificate s The protection level, provided by Accord-TSHM and the Accord-TSHM-based systems, is approved by 20 conformance certificate issued s, by:
Reinforc ing the protective properties of the unauthorized access control products тм of the ACCORD family may be reached using the following as a by hardware identifier: A personal cryptographic data security tool – SHIPKA

ACCORD -TSHM Accord. Reliabilityin an unreliableworld. Moscow, 2009
ab4546042a871a92a5eacbd3c58bff75.ppt