ef351e8914972cb9e92904eb141b2b17.ppt
- Количество слайдов: 15
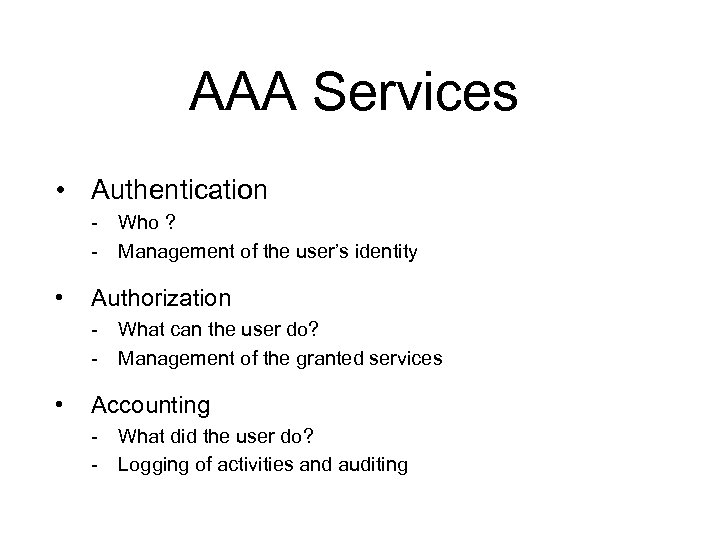 AAA Services • Authentication - Who ? - Management of the user’s identity • Authorization - What can the user do? - Management of the granted services • Accounting - What did the user do? - Logging of activities and auditing
AAA Services • Authentication - Who ? - Management of the user’s identity • Authorization - What can the user do? - Management of the granted services • Accounting - What did the user do? - Logging of activities and auditing
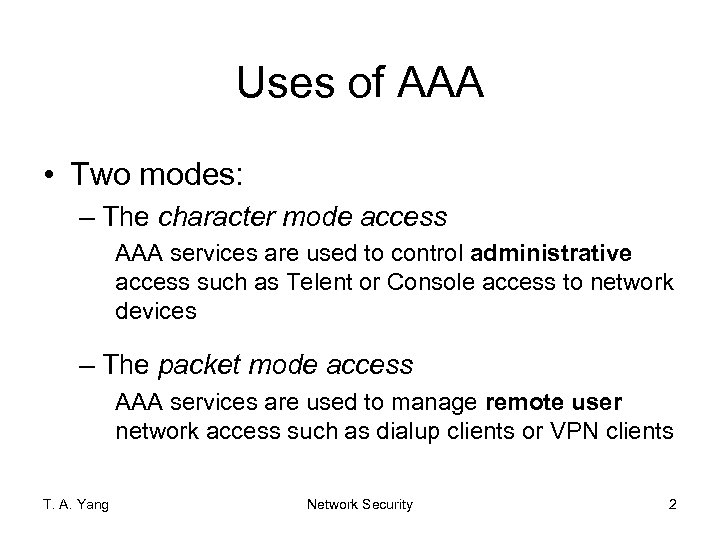 Uses of AAA • Two modes: – The character mode access AAA services are used to control administrative access such as Telent or Console access to network devices – The packet mode access AAA services are used to manage remote user network access such as dialup clients or VPN clients T. A. Yang Network Security 2
Uses of AAA • Two modes: – The character mode access AAA services are used to control administrative access such as Telent or Console access to network devices – The packet mode access AAA services are used to manage remote user network access such as dialup clients or VPN clients T. A. Yang Network Security 2
 c. f. , Alternative methods to AAA • Examples: – Password-based authentication – Challenge-response authentication • Incomplete access management – Limited to authentication only T. A. Yang Network Security 3
c. f. , Alternative methods to AAA • Examples: – Password-based authentication – Challenge-response authentication • Incomplete access management – Limited to authentication only T. A. Yang Network Security 3
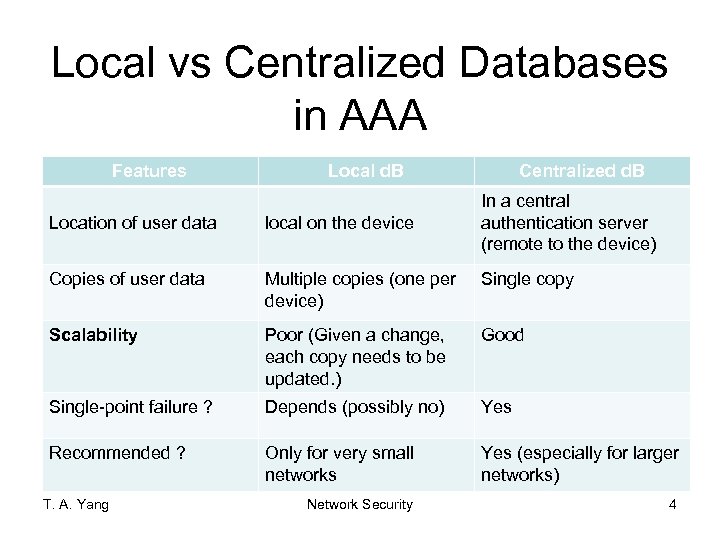 Local vs Centralized Databases in AAA Features Local d. B Centralized d. B In a central authentication server (remote to the device) Location of user data local on the device Copies of user data Multiple copies (one per device) Single copy Scalability Poor (Given a change, each copy needs to be updated. ) Good Single-point failure ? Depends (possibly no) Yes Recommended ? Only for very small networks Yes (especially for larger networks) Network Security 4 T. A. Yang
Local vs Centralized Databases in AAA Features Local d. B Centralized d. B In a central authentication server (remote to the device) Location of user data local on the device Copies of user data Multiple copies (one per device) Single copy Scalability Poor (Given a change, each copy needs to be updated. ) Good Single-point failure ? Depends (possibly no) Yes Recommended ? Only for very small networks Yes (especially for larger networks) Network Security 4 T. A. Yang
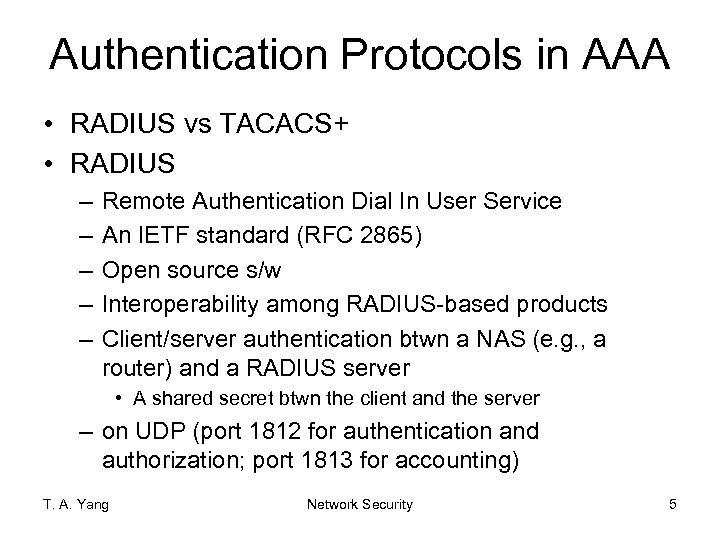 Authentication Protocols in AAA • RADIUS vs TACACS+ • RADIUS – – – Remote Authentication Dial In User Service An IETF standard (RFC 2865) Open source s/w Interoperability among RADIUS-based products Client/server authentication btwn a NAS (e. g. , a router) and a RADIUS server • A shared secret btwn the client and the server – on UDP (port 1812 for authentication and authorization; port 1813 for accounting) T. A. Yang Network Security 5
Authentication Protocols in AAA • RADIUS vs TACACS+ • RADIUS – – – Remote Authentication Dial In User Service An IETF standard (RFC 2865) Open source s/w Interoperability among RADIUS-based products Client/server authentication btwn a NAS (e. g. , a router) and a RADIUS server • A shared secret btwn the client and the server – on UDP (port 1812 for authentication and authorization; port 1813 for accounting) T. A. Yang Network Security 5
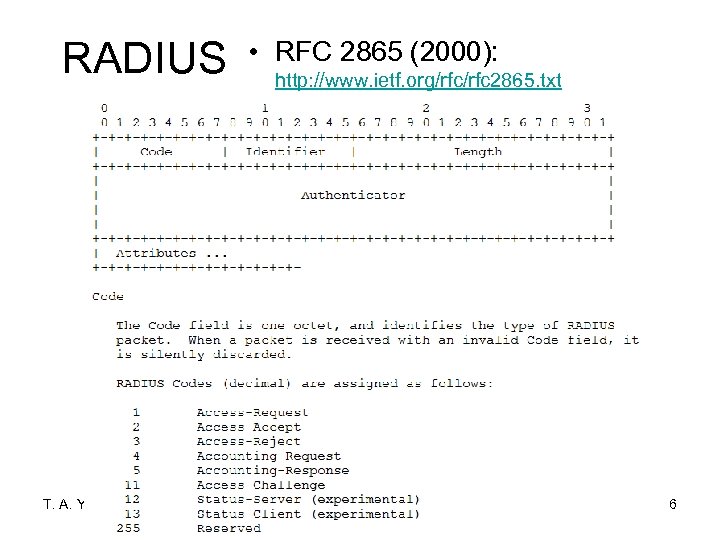 RADIUS T. A. Yang • RFC 2865 (2000): http: //www. ietf. org/rfc 2865. txt Network Security 6
RADIUS T. A. Yang • RFC 2865 (2000): http: //www. ietf. org/rfc 2865. txt Network Security 6
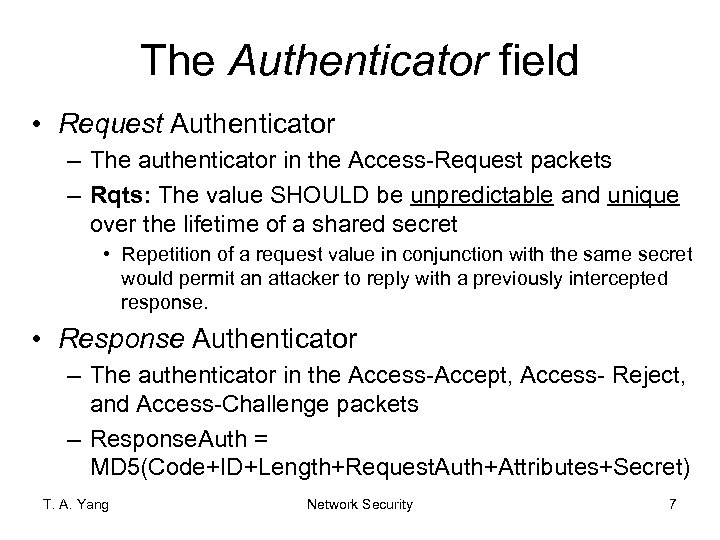 The Authenticator field • Request Authenticator – The authenticator in the Access-Request packets – Rqts: The value SHOULD be unpredictable and unique over the lifetime of a shared secret • Repetition of a request value in conjunction with the same secret would permit an attacker to reply with a previously intercepted response. • Response Authenticator – The authenticator in the Access-Accept, Access- Reject, and Access-Challenge packets – Response. Auth = MD 5(Code+ID+Length+Request. Auth+Attributes+Secret) T. A. Yang Network Security 7
The Authenticator field • Request Authenticator – The authenticator in the Access-Request packets – Rqts: The value SHOULD be unpredictable and unique over the lifetime of a shared secret • Repetition of a request value in conjunction with the same secret would permit an attacker to reply with a previously intercepted response. • Response Authenticator – The authenticator in the Access-Accept, Access- Reject, and Access-Challenge packets – Response. Auth = MD 5(Code+ID+Length+Request. Auth+Attributes+Secret) T. A. Yang Network Security 7
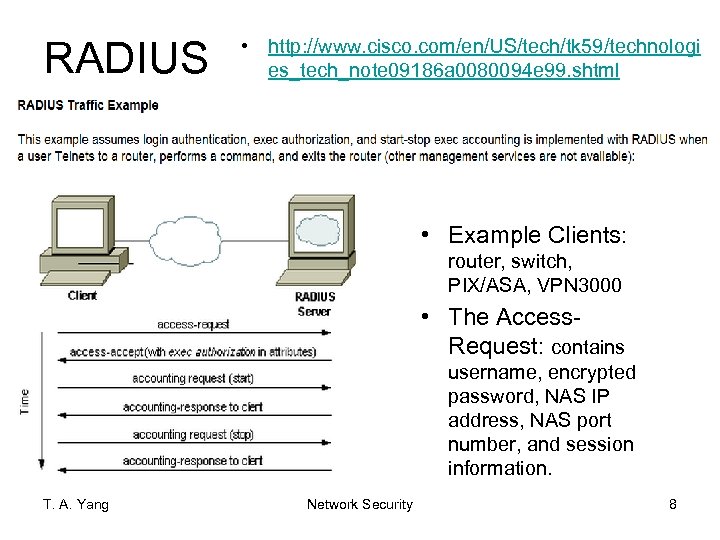 RADIUS • http: //www. cisco. com/en/US/tech/tk 59/technologi es_tech_note 09186 a 0080094 e 99. shtml • Example Clients: router, switch, PIX/ASA, VPN 3000 • The Access. Request: contains username, encrypted password, NAS IP address, NAS port number, and session information. T. A. Yang Network Security 8
RADIUS • http: //www. cisco. com/en/US/tech/tk 59/technologi es_tech_note 09186 a 0080094 e 99. shtml • Example Clients: router, switch, PIX/ASA, VPN 3000 • The Access. Request: contains username, encrypted password, NAS IP address, NAS port number, and session information. T. A. Yang Network Security 8
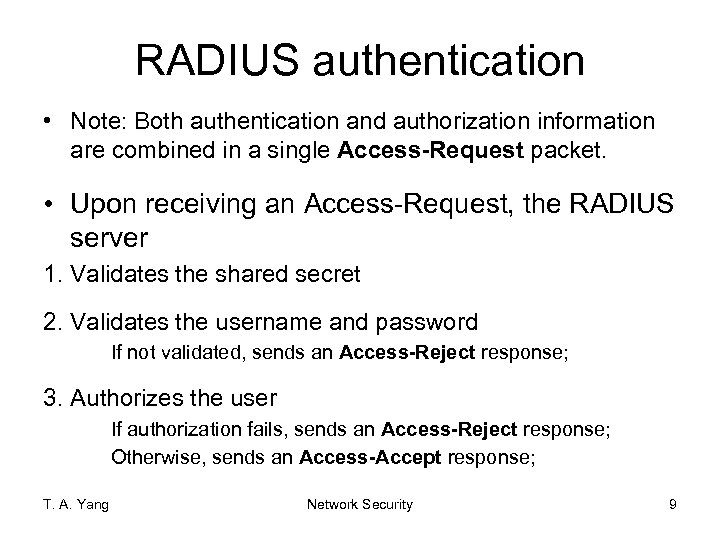 RADIUS authentication • Note: Both authentication and authorization information are combined in a single Access-Request packet. • Upon receiving an Access-Request, the RADIUS server 1. Validates the shared secret 2. Validates the username and password If not validated, sends an Access-Reject response; 3. Authorizes the user If authorization fails, sends an Access-Reject response; Otherwise, sends an Access-Accept response; T. A. Yang Network Security 9
RADIUS authentication • Note: Both authentication and authorization information are combined in a single Access-Request packet. • Upon receiving an Access-Request, the RADIUS server 1. Validates the shared secret 2. Validates the username and password If not validated, sends an Access-Reject response; 3. Authorizes the user If authorization fails, sends an Access-Reject response; Otherwise, sends an Access-Accept response; T. A. Yang Network Security 9
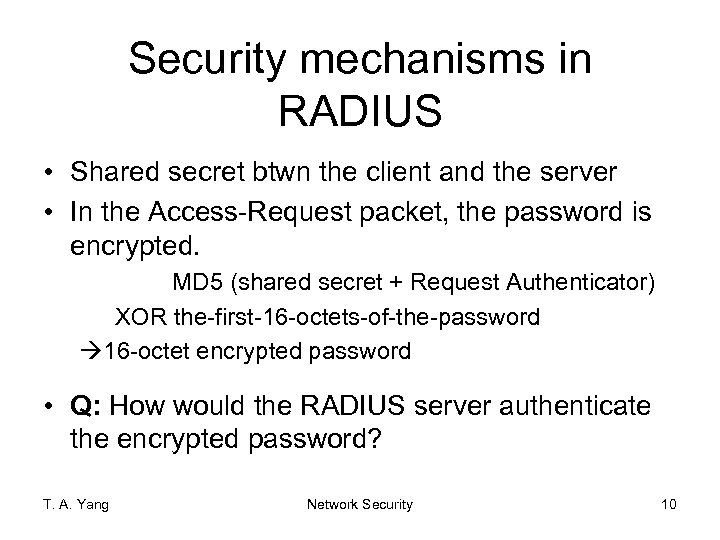 Security mechanisms in RADIUS • Shared secret btwn the client and the server • In the Access-Request packet, the password is encrypted. MD 5 (shared secret + Request Authenticator) XOR the-first-16 -octets-of-the-password à 16 -octet encrypted password • Q: How would the RADIUS server authenticate the encrypted password? T. A. Yang Network Security 10
Security mechanisms in RADIUS • Shared secret btwn the client and the server • In the Access-Request packet, the password is encrypted. MD 5 (shared secret + Request Authenticator) XOR the-first-16 -octets-of-the-password à 16 -octet encrypted password • Q: How would the RADIUS server authenticate the encrypted password? T. A. Yang Network Security 10
 TACACS+ • TACACS: Terminal Access Controller Access Control System • A Cisco proprietary client/server authentication protocol • A shared secret btwn the client & the server • Can encrypt the entire body of the packet (as indicated by the flags field) • On TCP T. A. Yang Network Security 11
TACACS+ • TACACS: Terminal Access Controller Access Control System • A Cisco proprietary client/server authentication protocol • A shared secret btwn the client & the server • Can encrypt the entire body of the packet (as indicated by the flags field) • On TCP T. A. Yang Network Security 11
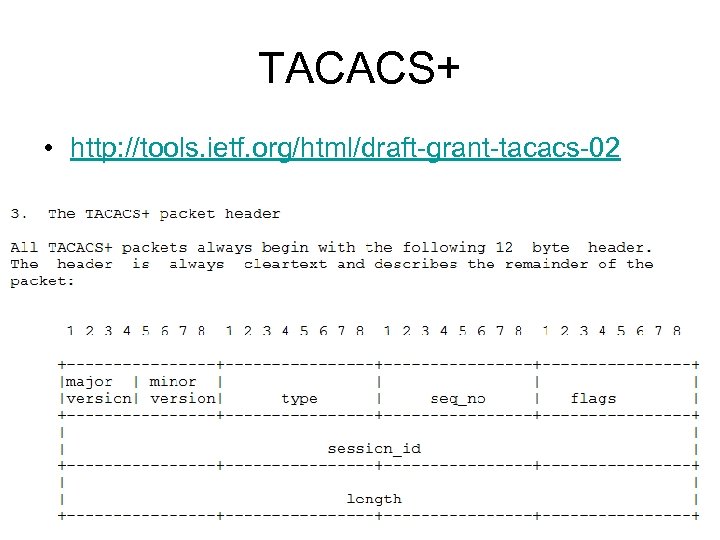 TACACS+ • http: //tools. ietf. org/html/draft-grant-tacacs-02 T. A. Yang Network Security 12
TACACS+ • http: //tools. ietf. org/html/draft-grant-tacacs-02 T. A. Yang Network Security 12
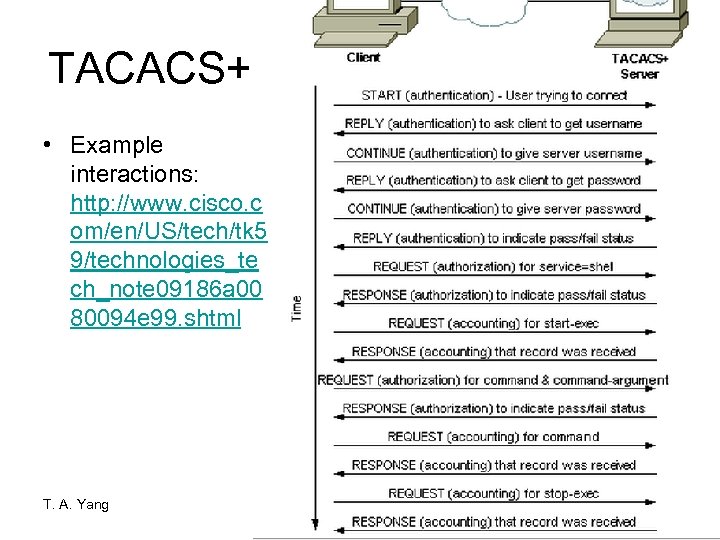 TACACS+ • Example interactions: http: //www. cisco. c om/en/US/tech/tk 5 9/technologies_te ch_note 09186 a 00 80094 e 99. shtml T. A. Yang Network Security 13
TACACS+ • Example interactions: http: //www. cisco. c om/en/US/tech/tk 5 9/technologies_te ch_note 09186 a 00 80094 e 99. shtml T. A. Yang Network Security 13
 TACACS+ vs RADIUS • Shared: – Client/server based – Authentication btwn a NAS and an authentication server – Shared secret • Differences ? T. A. Yang Network Security 14
TACACS+ vs RADIUS • Shared: – Client/server based – Authentication btwn a NAS and an authentication server – Shared secret • Differences ? T. A. Yang Network Security 14
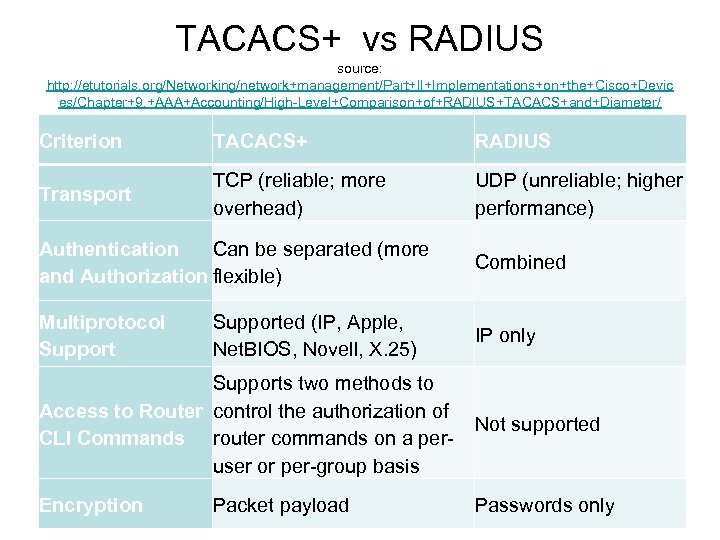 TACACS+ vs RADIUS source: http: //etutorials. org/Networking/network+management/Part+II+Implementations+on+the+Cisco+Devic es/Chapter+9. +AAA+Accounting/High-Level+Comparison+of+RADIUS+TACACS+and+Diameter/ Criterion TACACS+ RADIUS Transport TCP (reliable; more overhead) UDP (unreliable; higher performance) Authentication Can be separated (more and Authorization flexible) Combined Multiprotocol Support IP only Supported (IP, Apple, Net. BIOS, Novell, X. 25) Supports two methods to Access to Router control the authorization of CLI Commands router commands on a peruser or per-group basis Not supported T. A. Yang Encryption Passwords only Network Packet payload Security 15
TACACS+ vs RADIUS source: http: //etutorials. org/Networking/network+management/Part+II+Implementations+on+the+Cisco+Devic es/Chapter+9. +AAA+Accounting/High-Level+Comparison+of+RADIUS+TACACS+and+Diameter/ Criterion TACACS+ RADIUS Transport TCP (reliable; more overhead) UDP (unreliable; higher performance) Authentication Can be separated (more and Authorization flexible) Combined Multiprotocol Support IP only Supported (IP, Apple, Net. BIOS, Novell, X. 25) Supports two methods to Access to Router control the authorization of CLI Commands router commands on a peruser or per-group basis Not supported T. A. Yang Encryption Passwords only Network Packet payload Security 15


