06ffc5aa0d592231046713a069cdfb56.ppt
- Количество слайдов: 22
 AAA-ARCH 1 of 16 IRTF-RG Authentication Authorisation and Accounting ARCHitecture chairs: C. de Laat J. Vollbrecht
AAA-ARCH 1 of 16 IRTF-RG Authentication Authorisation and Accounting ARCHitecture chairs: C. de Laat J. Vollbrecht
 Applications • Applications – Network Access – Bandwidth Broker – Authorization of resources living in many administrative domains – Budget system – Library system – Computer based education system – E-Commerce – Micro-payments – Car Rental – Daily life 2 of 16
Applications • Applications – Network Access – Bandwidth Broker – Authorization of resources living in many administrative domains – Budget system – Library system – Computer based education system – E-Commerce – Micro-payments – Car Rental – Daily life 2 of 16
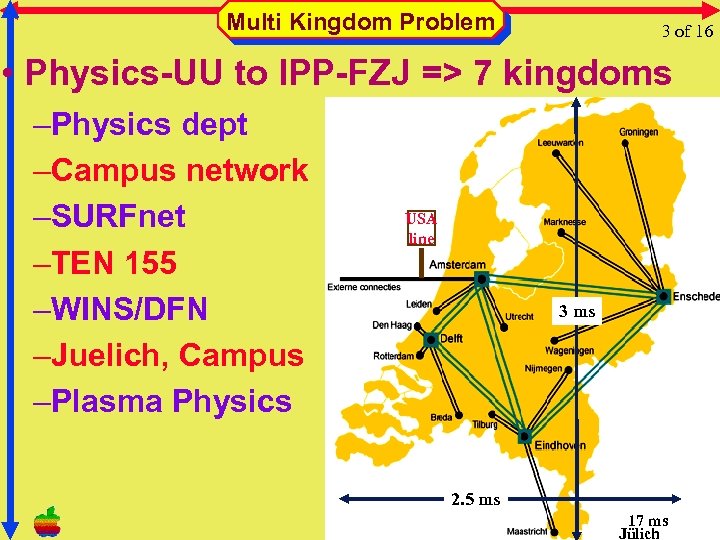 Multi Kingdom Problem 3 of 16 • Physics-UU to IPP-FZJ => 7 kingdoms –Physics dept –Campus network –SURFnet –TEN 155 –WINS/DFN –Juelich, Campus –Plasma Physics USA line 3 ms 2. 5 ms 17 ms Jülich
Multi Kingdom Problem 3 of 16 • Physics-UU to IPP-FZJ => 7 kingdoms –Physics dept –Campus network –SURFnet –TEN 155 –WINS/DFN –Juelich, Campus –Plasma Physics USA line 3 ms 2. 5 ms 17 ms Jülich
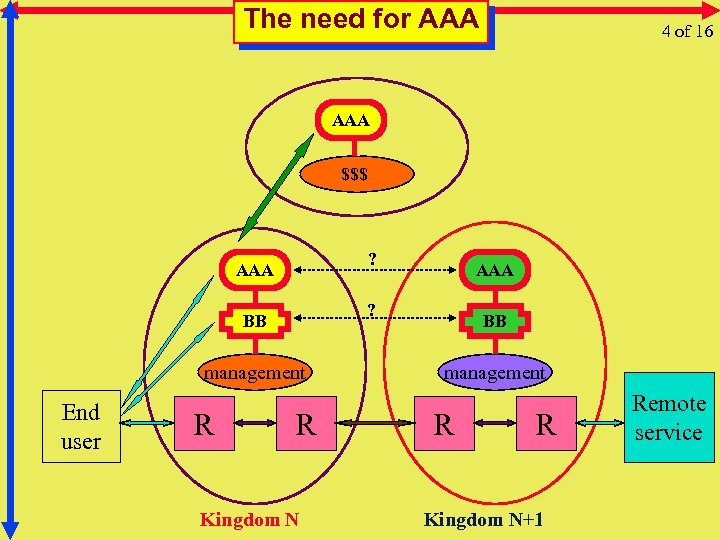 The need for AAA 4 of 16 AAA $$$ ? AAA ? BB management End user R AAA R Kingdom N BB management R R Kingdom N+1 Remote service
The need for AAA 4 of 16 AAA $$$ ? AAA ? BB management End user R AAA R Kingdom N BB management R R Kingdom N+1 Remote service
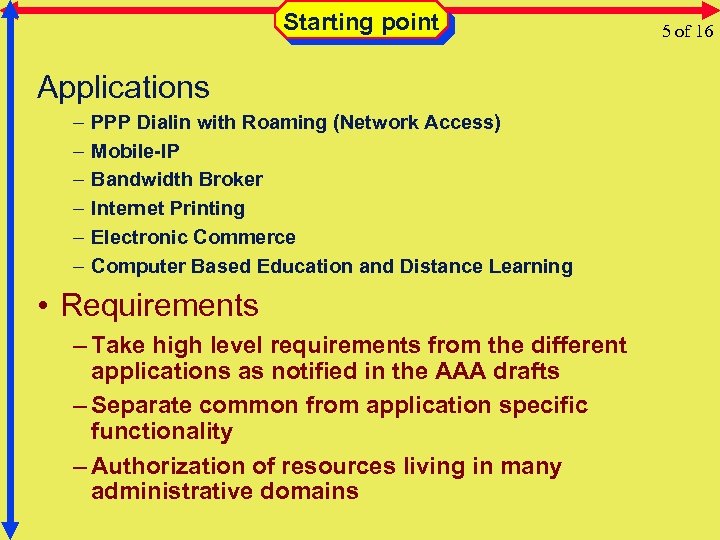 Starting point Applications – – – PPP Dialin with Roaming (Network Access) Mobile-IP Bandwidth Broker Internet Printing Electronic Commerce Computer Based Education and Distance Learning • Requirements – Take high level requirements from the different applications as notified in the AAA drafts – Separate common from application specific functionality – Authorization of resources living in many administrative domains 5 of 16
Starting point Applications – – – PPP Dialin with Roaming (Network Access) Mobile-IP Bandwidth Broker Internet Printing Electronic Commerce Computer Based Education and Distance Learning • Requirements – Take high level requirements from the different applications as notified in the AAA drafts – Separate common from application specific functionality – Authorization of resources living in many administrative domains 5 of 16
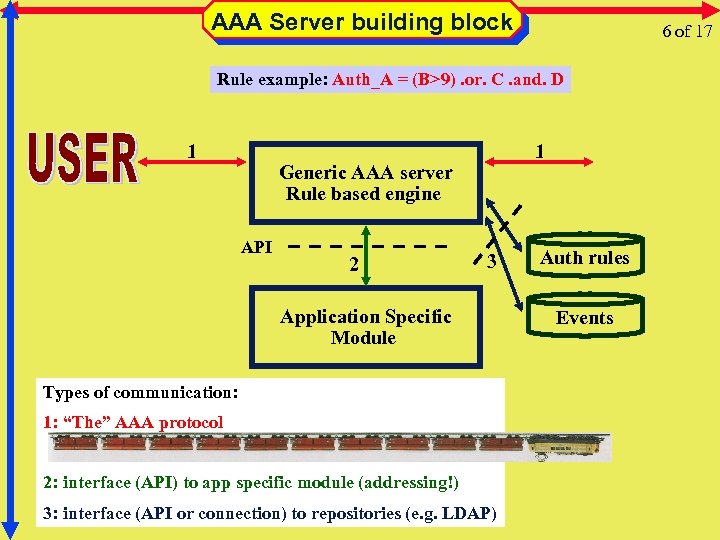 AAA Server building block 6 of 17 Rule example: Auth_A = (B>9). or. C. and. D 1 1 Generic AAA server Rule based engine API 2 3 Application Specific Module Types of communication: 1: “The” AAA protocol 2: interface (API) to app specific module (addressing!) 3: interface (API or connection) to repositories (e. g. LDAP) Auth rules Events
AAA Server building block 6 of 17 Rule example: Auth_A = (B>9). or. C. and. D 1 1 Generic AAA server Rule based engine API 2 3 Application Specific Module Types of communication: 1: “The” AAA protocol 2: interface (API) to app specific module (addressing!) 3: interface (API or connection) to repositories (e. g. LDAP) Auth rules Events
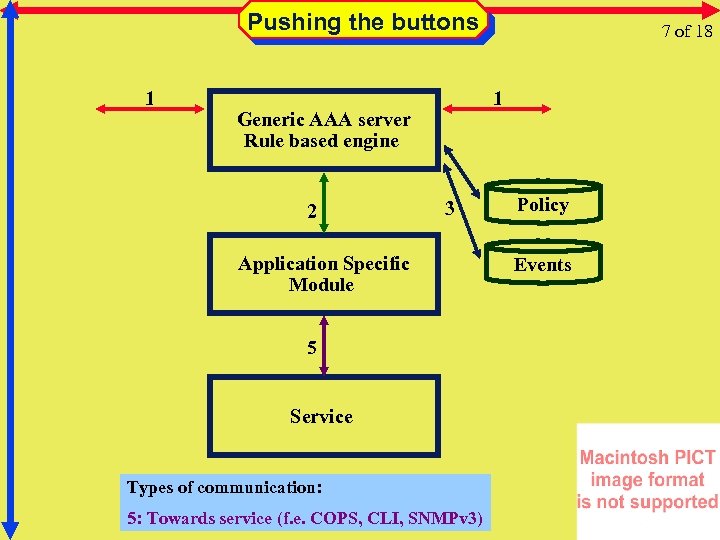 Pushing the buttons 1 1 Generic AAA server Rule based engine 2 7 of 18 3 Application Specific Module 5 Service Types of communication: 5: Towards service (f. e. COPS, CLI, SNMPv 3) Policy Events
Pushing the buttons 1 1 Generic AAA server Rule based engine 2 7 of 18 3 Application Specific Module 5 Service Types of communication: 5: Towards service (f. e. COPS, CLI, SNMPv 3) Policy Events
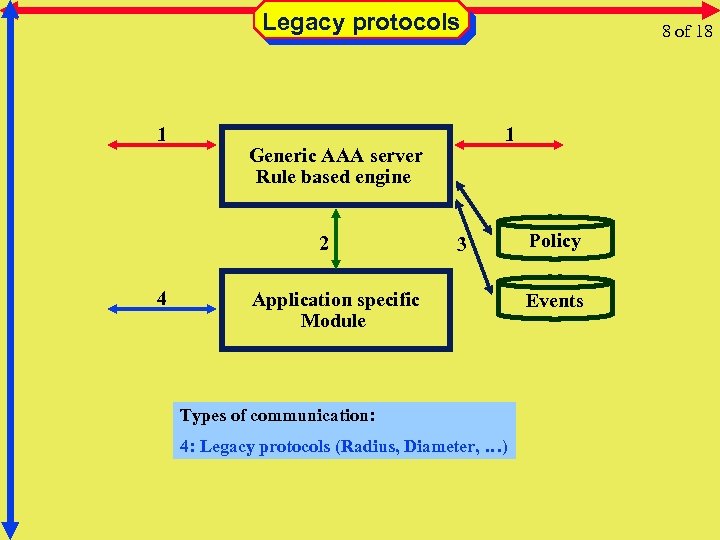 Legacy protocols 1 4 1 Generic AAA server Rule based engine 2 8 of 18 3 Application specific Module Types of communication: 4: Legacy protocols (Radius, Diameter, …) Policy Events
Legacy protocols 1 4 1 Generic AAA server Rule based engine 2 8 of 18 3 Application specific Module Types of communication: 4: Legacy protocols (Radius, Diameter, …) Policy Events
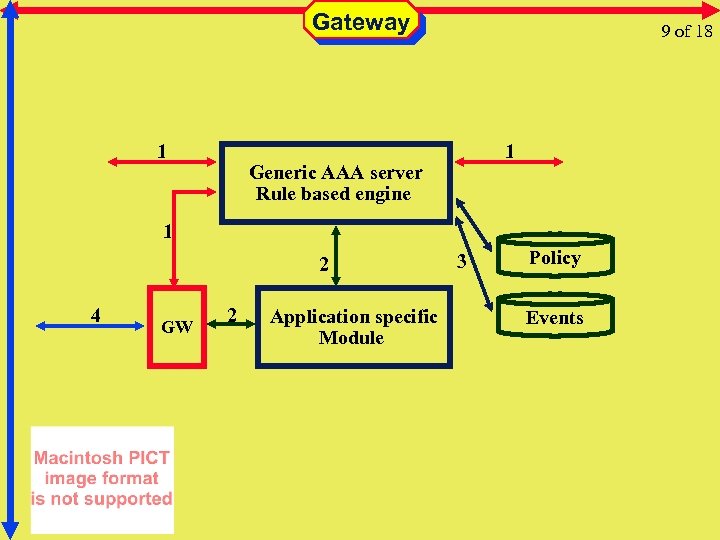 Gateway 1 9 of 18 1 Generic AAA server Rule based engine 1 2 4 GW 2 Application specific Module 3 Policy Events
Gateway 1 9 of 18 1 Generic AAA server Rule based engine 1 2 4 GW 2 Application specific Module 3 Policy Events
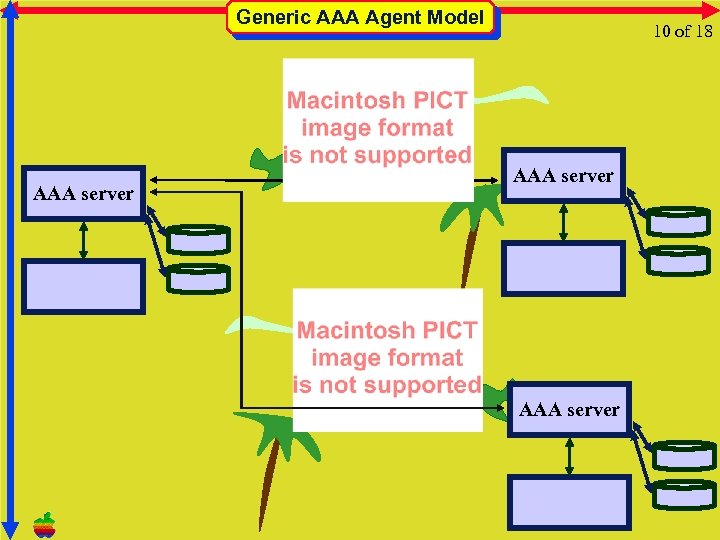 Generic AAA Agent Model AAA server 10 of 18 AAA server
Generic AAA Agent Model AAA server 10 of 18 AAA server
 Macs. Bug 6. 5. 4 a 6, Copyright Apple Computer, Inc. 1981 -98 Next section NMI (user entered Macs. Bug on purpose) 11 of 19 Just kidding • We will now examine the generic AAA problem from the perspective of a layered protocol model 17 -Jun-1999 11: 51: 26 PM (since boot = 28 minutes) Current application is “Microsoft Power. Point” Machine = 312 (Power. Book. G 3 Series), System $0860, sysu = $01008000 ROM version $077 D, $41 F 6, $0002 (ROMBase $FFC 00000) VM is on; paging is currently safe NIL^ = $FFC 10000 Stack space used = -8018882 Address FFC 0693 A is in the ROM at _Put. Icon+0378 C 68020 Registers D 0 = 0000 A 0 = FEE 00000 USP = 0 B 25 F 3 D 8 D 1 = 0000003 C A 1 = 0028 B 9 A 4 MSP = 0000 D 2 = 008 D 49 B 0 A 2 = 00019570 ISP = 0 BA 055 E 4 D 3 = 0 B 25 FAF 0 A 3 = 0000 VBR = 0016 D 494 D 4 = 746 FFF 00 A 4 = 0 B 25 F 754 CACR = 00000001 SFC = 0 D 5 = 0000 FFFE A 5 = 0 B 9 F 3790 CAAR = 0000 DFC = 0 D 6 = 6 C 204301 A 6 = 0 B 25 F 42 C PC = FFC 0693 A D 7 = 00010000 A 7 = 0 BA 055 E 4 SR = Smxnzv. C Int = 0 • This contribution is mostly done by George Gross Calling chain using A 6/R 1 links Back chain ISA Caller 0 B 25 F 8 FF PPC 002 FD 83 C Em. To. Nat. End. Move. Params+00014 0 B 25 F 880 PPC 1 B 5 C 67 F 8 0 B 25 F 848 PPC 1 B 5 C 68 A 8 0 B 25 F 7 D 8 PPC 1 B 249 B 30 0 B 25 F 780 PPC 1 B 2905 DC 0 B 25 F 710 PPC 1 B 28 F 3 FC 0 B 25 F 6 A 0 PPC 1 AE 7 BE 98 Afx. Wait. Next. Event+00050
Macs. Bug 6. 5. 4 a 6, Copyright Apple Computer, Inc. 1981 -98 Next section NMI (user entered Macs. Bug on purpose) 11 of 19 Just kidding • We will now examine the generic AAA problem from the perspective of a layered protocol model 17 -Jun-1999 11: 51: 26 PM (since boot = 28 minutes) Current application is “Microsoft Power. Point” Machine = 312 (Power. Book. G 3 Series), System $0860, sysu = $01008000 ROM version $077 D, $41 F 6, $0002 (ROMBase $FFC 00000) VM is on; paging is currently safe NIL^ = $FFC 10000 Stack space used = -8018882 Address FFC 0693 A is in the ROM at _Put. Icon+0378 C 68020 Registers D 0 = 0000 A 0 = FEE 00000 USP = 0 B 25 F 3 D 8 D 1 = 0000003 C A 1 = 0028 B 9 A 4 MSP = 0000 D 2 = 008 D 49 B 0 A 2 = 00019570 ISP = 0 BA 055 E 4 D 3 = 0 B 25 FAF 0 A 3 = 0000 VBR = 0016 D 494 D 4 = 746 FFF 00 A 4 = 0 B 25 F 754 CACR = 00000001 SFC = 0 D 5 = 0000 FFFE A 5 = 0 B 9 F 3790 CAAR = 0000 DFC = 0 D 6 = 6 C 204301 A 6 = 0 B 25 F 42 C PC = FFC 0693 A D 7 = 00010000 A 7 = 0 BA 055 E 4 SR = Smxnzv. C Int = 0 • This contribution is mostly done by George Gross Calling chain using A 6/R 1 links Back chain ISA Caller 0 B 25 F 8 FF PPC 002 FD 83 C Em. To. Nat. End. Move. Params+00014 0 B 25 F 880 PPC 1 B 5 C 67 F 8 0 B 25 F 848 PPC 1 B 5 C 68 A 8 0 B 25 F 7 D 8 PPC 1 B 249 B 30 0 B 25 F 780 PPC 1 B 2905 DC 0 B 25 F 710 PPC 1 B 28 F 3 FC 0 B 25 F 6 A 0 PPC 1 AE 7 BE 98 Afx. Wait. Next. Event+00050
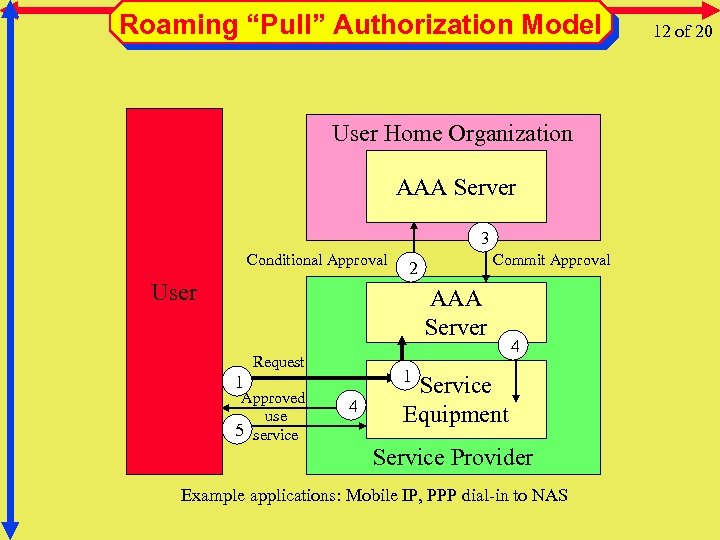 Roaming “Pull” Authorization Model User Home Organization AAA Server 3 Conditional Approval Commit Approval 2 User AAA Server Request 1 1 Approved use 5 service 4 4 Service Equipment Service Provider Example applications: Mobile IP, PPP dial-in to NAS 12 of 20
Roaming “Pull” Authorization Model User Home Organization AAA Server 3 Conditional Approval Commit Approval 2 User AAA Server Request 1 1 Approved use 5 service 4 4 Service Equipment Service Provider Example applications: Mobile IP, PPP dial-in to NAS 12 of 20
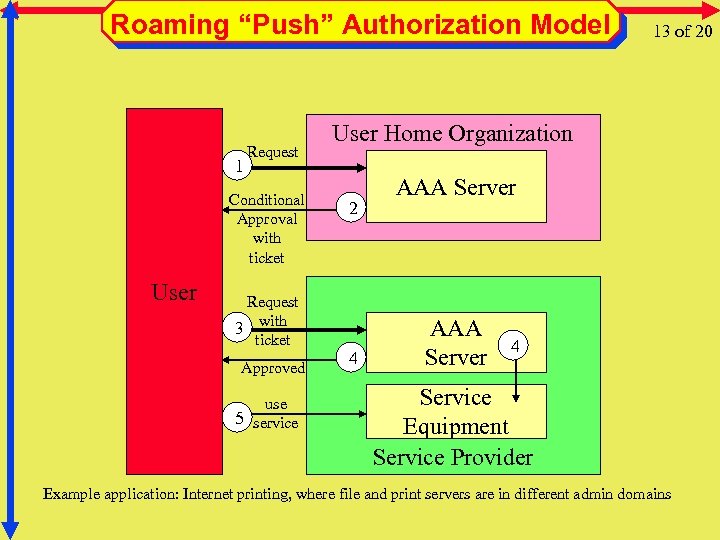 Roaming “Push” Authorization Model 1 Request Conditional Approval with ticket User Request 3 with ticket Approved use 5 service 13 of 20 User Home Organization 2 4 AAA Server 4 Service Equipment Service Provider Example application: Internet printing, where file and print servers are in different admin domains
Roaming “Push” Authorization Model 1 Request Conditional Approval with ticket User Request 3 with ticket Approved use 5 service 13 of 20 User Home Organization 2 4 AAA Server 4 Service Equipment Service Provider Example application: Internet printing, where file and print servers are in different admin domains
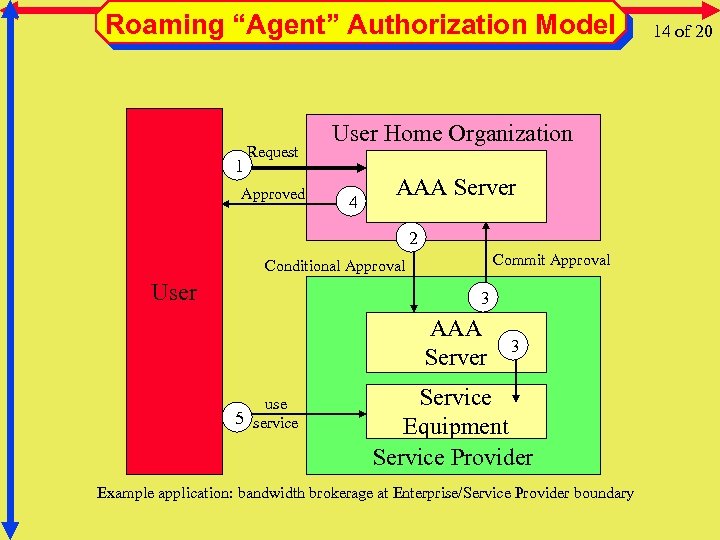 Roaming “Agent” Authorization Model 1 Request Approved User Home Organization 4 AAA Server 2 Commit Approval Conditional Approval User 3 AAA Server use 5 service 3 Service Equipment Service Provider Example application: bandwidth brokerage at Enterprise/Service Provider boundary 14 of 20
Roaming “Agent” Authorization Model 1 Request Approved User Home Organization 4 AAA Server 2 Commit Approval Conditional Approval User 3 AAA Server use 5 service 3 Service Equipment Service Provider Example application: bandwidth brokerage at Enterprise/Service Provider boundary 14 of 20
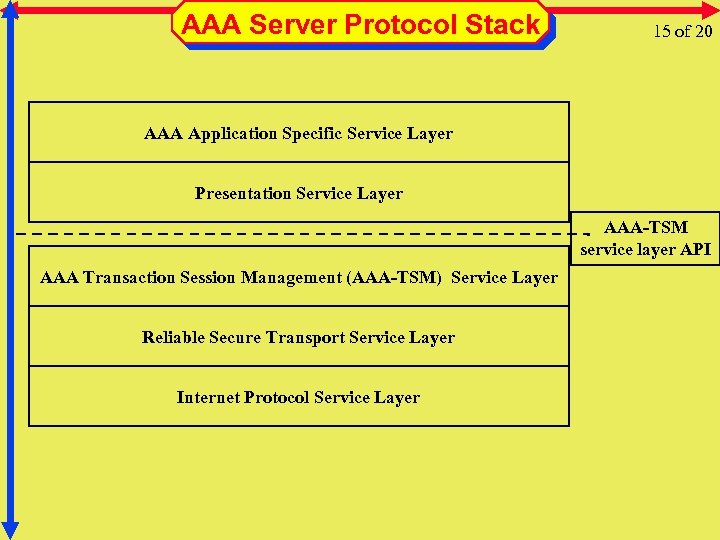 AAA Server Protocol Stack 15 of 20 AAA Application Specific Service Layer Presentation Service Layer AAA-TSM service layer API AAA Transaction Session Management (AAA-TSM) Service Layer Reliable Secure Transport Service Layer Internet Protocol Service Layer
AAA Server Protocol Stack 15 of 20 AAA Application Specific Service Layer Presentation Service Layer AAA-TSM service layer API AAA Transaction Session Management (AAA-TSM) Service Layer Reliable Secure Transport Service Layer Internet Protocol Service Layer
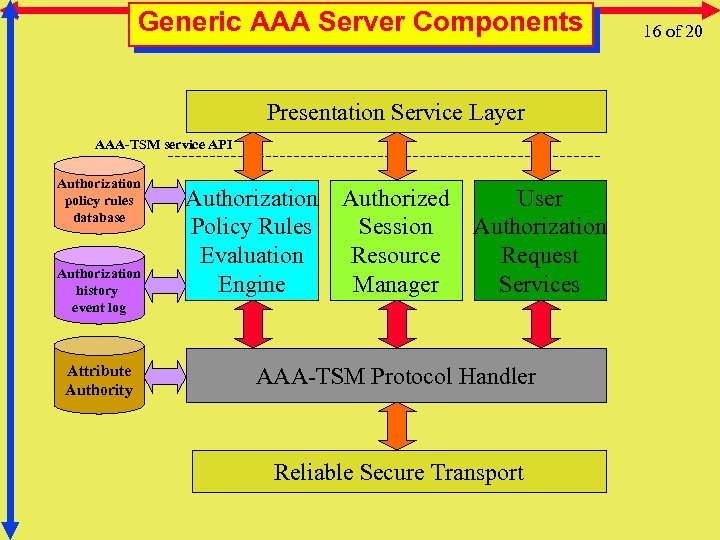 Generic AAA Server Components Presentation Service Layer AAA-TSM service API Authorization policy rules database Authorization history event log Attribute Authority Authorization Authorized User Policy Rules Session Authorization Evaluation Resource Request Engine Manager Services AAA-TSM Protocol Handler Reliable Secure Transport 16 of 20
Generic AAA Server Components Presentation Service Layer AAA-TSM service API Authorization policy rules database Authorization history event log Attribute Authority Authorization Authorized User Policy Rules Session Authorization Evaluation Resource Request Engine Manager Services AAA-TSM Protocol Handler Reliable Secure Transport 16 of 20
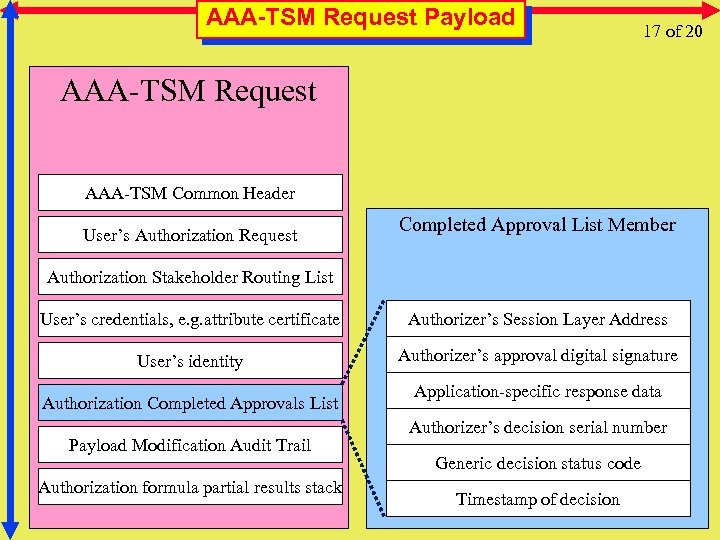 AAA-TSM Request Payload 17 of 20 AAA-TSM Request AAA-TSM Common Header User’s Authorization Request Completed Approval List Member Authorization Stakeholder Routing List User’s credentials, e. g. attribute certificate Authorizer’s Session Layer Address User’s identity Authorizer’s approval digital signature Authorization Completed Approvals List Payload Modification Audit Trail Authorization formula partial results stack Application-specific response data Authorizer’s decision serial number Generic decision status code Timestamp of decision
AAA-TSM Request Payload 17 of 20 AAA-TSM Request AAA-TSM Common Header User’s Authorization Request Completed Approval List Member Authorization Stakeholder Routing List User’s credentials, e. g. attribute certificate Authorizer’s Session Layer Address User’s identity Authorizer’s approval digital signature Authorization Completed Approvals List Payload Modification Audit Trail Authorization formula partial results stack Application-specific response data Authorizer’s decision serial number Generic decision status code Timestamp of decision
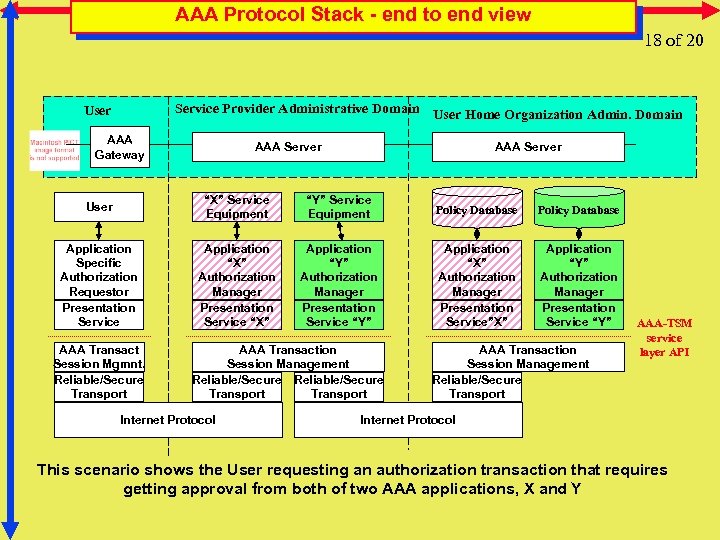 AAA Protocol Stack - end to end view 18 of 20 Service Provider Administrative Domain User Home Organization Admin. Domain User AAA Gateway AAA Server User “X” Service Equipment “Y” Service Equipment Policy Database Application Specific Authorization Requestor Presentation Service Application “X” Authorization Manager Presentation Service “X” Application “Y” Authorization Manager Presentation Service “Y” Application “X” Authorization Manager Presentation Service”X” Application “Y” Authorization Manager Presentation Service “Y” AAA Transact Session Mgmnt. Reliable/Secure Transport AAA Transaction Session Management Reliable/Secure Transport Internet Protocol AAA Transaction Session Management Reliable/Secure Transport AAA-TSM service layer API Internet Protocol This scenario shows the User requesting an authorization transaction that requires getting approval from both of two AAA applications, X and Y
AAA Protocol Stack - end to end view 18 of 20 Service Provider Administrative Domain User Home Organization Admin. Domain User AAA Gateway AAA Server User “X” Service Equipment “Y” Service Equipment Policy Database Application Specific Authorization Requestor Presentation Service Application “X” Authorization Manager Presentation Service “X” Application “Y” Authorization Manager Presentation Service “Y” Application “X” Authorization Manager Presentation Service”X” Application “Y” Authorization Manager Presentation Service “Y” AAA Transact Session Mgmnt. Reliable/Secure Transport AAA Transaction Session Management Reliable/Secure Transport Internet Protocol AAA Transaction Session Management Reliable/Secure Transport AAA-TSM service layer API Internet Protocol This scenario shows the User requesting an authorization transaction that requires getting approval from both of two AAA applications, X and Y
 Architecture's Focus 19 a of 20 The architecture's focus is to support AAA services that: • can inter-operate across organizational boundaries • are extensible yet common across a wide variety of Internet services • enables a concept of an AAA transaction spanning many stakeholders • provides application independent session management mechanisms • contains strong security mechanisms that be tuned to local policies • is a scalable to the size of the global Internet
Architecture's Focus 19 a of 20 The architecture's focus is to support AAA services that: • can inter-operate across organizational boundaries • are extensible yet common across a wide variety of Internet services • enables a concept of an AAA transaction spanning many stakeholders • provides application independent session management mechanisms • contains strong security mechanisms that be tuned to local policies • is a scalable to the size of the global Internet
 RG-Goals-1 19 b of 20 Specific goals of the RG are: • develop generic AAA model by specifically including Authentication and Accounting • develop auditability framework specification that allows the AAA system functions to be checked in a multiorganization environment • develop a model that supports management of a "mesh" of interconnected AAA Servers • define distributed policy framework, coordinate with policy framework WG and others • develop an accounting model that allows authorization to define the type of accounting processing required for each session
RG-Goals-1 19 b of 20 Specific goals of the RG are: • develop generic AAA model by specifically including Authentication and Accounting • develop auditability framework specification that allows the AAA system functions to be checked in a multiorganization environment • develop a model that supports management of a "mesh" of interconnected AAA Servers • define distributed policy framework, coordinate with policy framework WG and others • develop an accounting model that allows authorization to define the type of accounting processing required for each session
 RG-Goals-2 19 c of 20 Specific goals of the RG are: • implement a simulation model that allows experimentation with the proposed architectural models (also work on an emulation) • describe interdomain issues using generic model • work with AAA WG to align short term AAA protocol requirements with long term requirements as much as possible • complete the work in Q 3 - 2000 (ambitious)
RG-Goals-2 19 c of 20 Specific goals of the RG are: • implement a simulation model that allows experimentation with the proposed architectural models (also work on an emulation) • describe interdomain issues using generic model • work with AAA WG to align short term AAA protocol requirements with long term requirements as much as possible • complete the work in Q 3 - 2000 (ambitious)
 RG-info • Research Group Name: AAAARCH • Chair(s) – John Vollbrecht – Cees de Laat --- 20 of 20 jrv@merit. edu delaat@phys. uu. nl • Mailing list(s) – aaaarch@fokus. gmd. de – For subscription to the mailing list, send e-mail to majordomo@fokus. gmd. de with content of message subscribe aaaarch end – will be archived, retrieval with frames » http: //www. fokus. gmd. de/glone/research/aaaarch/ – in plain ascii: » http: //www. fokus. gmd. de/glone/research/mail-archive/aaaarch-current » ftp: //ftp. fokus. gmd. de/pub/glone/mail-archive/aaaarch-current • Web page – Http: //www. phys. uu. nl/~wwwfi/aaaarch
RG-info • Research Group Name: AAAARCH • Chair(s) – John Vollbrecht – Cees de Laat --- 20 of 20 jrv@merit. edu delaat@phys. uu. nl • Mailing list(s) – aaaarch@fokus. gmd. de – For subscription to the mailing list, send e-mail to majordomo@fokus. gmd. de with content of message subscribe aaaarch end – will be archived, retrieval with frames » http: //www. fokus. gmd. de/glone/research/aaaarch/ – in plain ascii: » http: //www. fokus. gmd. de/glone/research/mail-archive/aaaarch-current » ftp: //ftp. fokus. gmd. de/pub/glone/mail-archive/aaaarch-current • Web page – Http: //www. phys. uu. nl/~wwwfi/aaaarch


