2ba7bb02faf3c833b270ca92da0d975d.ppt
- Количество слайдов: 48
A-to-Z of Public Key Infrastructure (PKI) Alberto Pace An adaptation from Rafal Lukawiecki presentation SEC 390 at Tech’Ed 2003 rafal@projectbotticelli. co. uk
2 Objectives Explain the basics of PKI without concentrating on any particular product Introduce commonly used terminology Point out those aspects of PKI that require careful planning and implementation Outline some social issues associated with PKI
3 Agenda A Briefest Summary of Cryptography Fundamentals of PKI Recommendations on PKI Deployment
4 PKI “Public Key Infrastructure provides the components and services that enable practical deployment and operation of a system that uses certificates. ” A. Nash, “PKI”, RSA Press PKI is a group of solutions for key distribution problems and other issues: Key generation Certificate generation, revocation, validation Managing trust I consider Web-of-Trust systems (e. g. PGP) as a perfectly alternative and compatible implementation of PKI
5 A Summary of Cryptography
6 Encryption Typically things sent over TCP/IP are not encrypted in any way. Anyone on the same network can listen in, grab the packets and read the contents This is a Bad Thing Would lower confidence in sending things like credit card numbers to ecommerce companies Confidential email Remote logins
7 What Does Cryptography Solve? Confidentiality ◄ Your data/service provides no useful information to unauthorised people Integrity ◄ If anyone tampers with your asset it will be immediately evident Authenticity ◄ We can verify that asset is attributable to its authors or caretakers Non-repudiation ◄ The author or owner or caretaker of asset cannot deny that they are associated with it
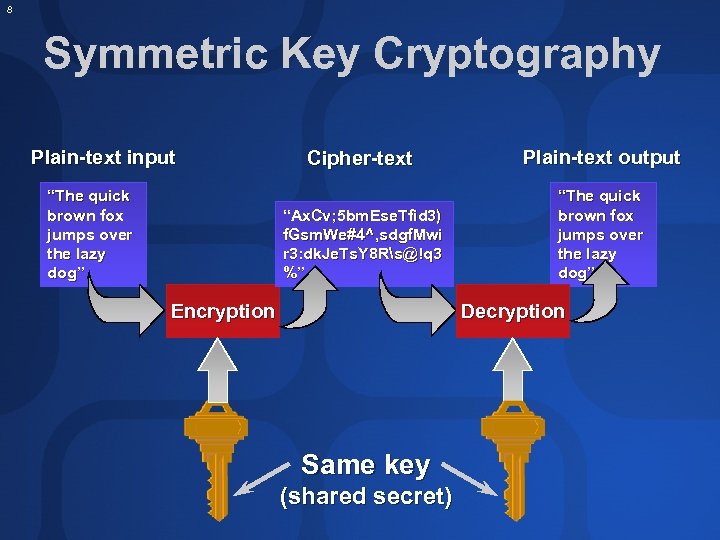
8 Symmetric Key Cryptography Plain-text input Plain-text output “Ax. Cv; 5 bm. Ese. Tfid 3) f. Gsm. We#4^, sdgf. Mwi r 3: dk. Je. Ts. Y 8 Rs@!q 3 %” “The quick brown fox jumps over the lazy dog” Cipher-text “The quick brown fox jumps over the lazy dog” Encryption Decryption Same key (shared secret)
9 Symmetric Encryption With a big organization you can physically distribute keys to users by some secure channel (courier, most likely) But this is vulnerable to compromise if your courier is compromised Bigger problem: how do you communicate with someone you’ve never met before from another organization?
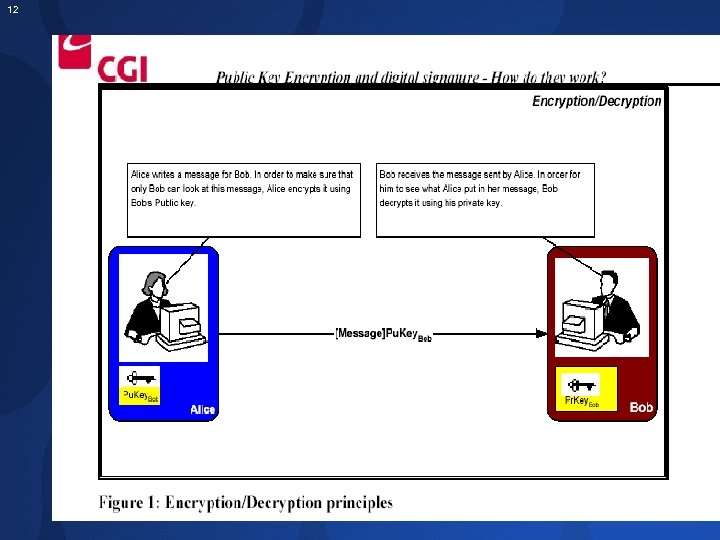
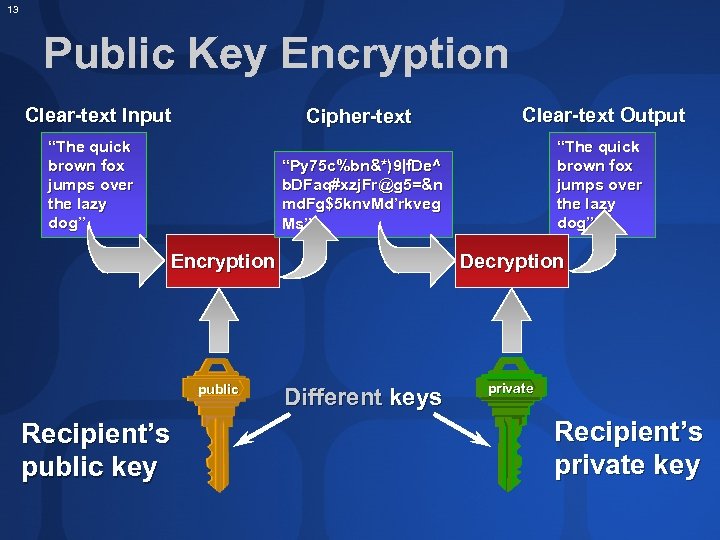
10 Asymmetric (Public Key) Encryption In this approach, there are two completely separate keys: one to encrypt the message, and one to decrypt it. This turns out to be very powerful, and is the basis for much of the crypto infrastructure on the net today It solves the key-distribution problem. How?
11 Public Key Crypto You publish, for all the world to see, your public key. If someone wants to send you email, they look up your public key. They encrypt the message using the public key and send it to you. You decrypt the message using your private key.
12
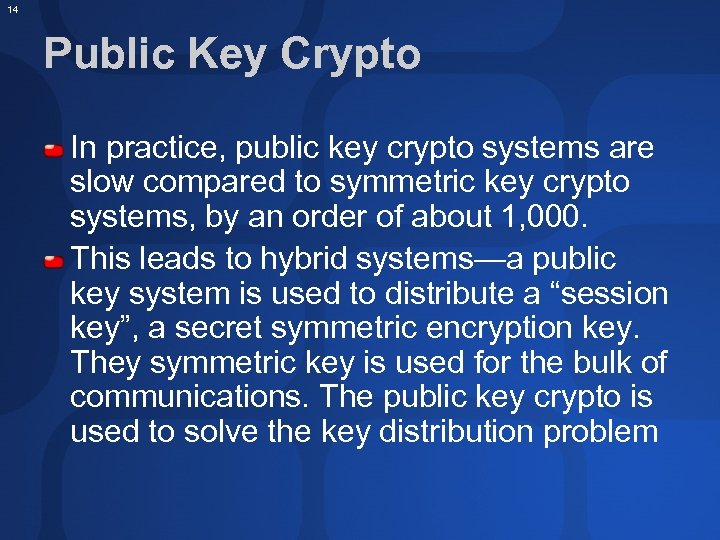
13 Public Key Encryption Clear-text Input Cipher-text “Py 75 c%bn&*)9|f. De^ b. DFaq#xzj. Fr@g 5=&n md. Fg$5 knv. Md’rkveg Ms” “The quick brown fox jumps over the lazy dog” Clear-text Output “The quick brown fox jumps over the lazy dog” Encryption public Recipient’s public key Decryption Different keys private Recipient’s private key
14 Public Key Crypto In practice, public key crypto systems are slow compared to symmetric key crypto systems, by an order of about 1, 000. This leads to hybrid systems—a public key system is used to distribute a “session key”, a secret symmetric encryption key. They symmetric key is used for the bulk of communications. The public key crypto is used to solve the key distribution problem
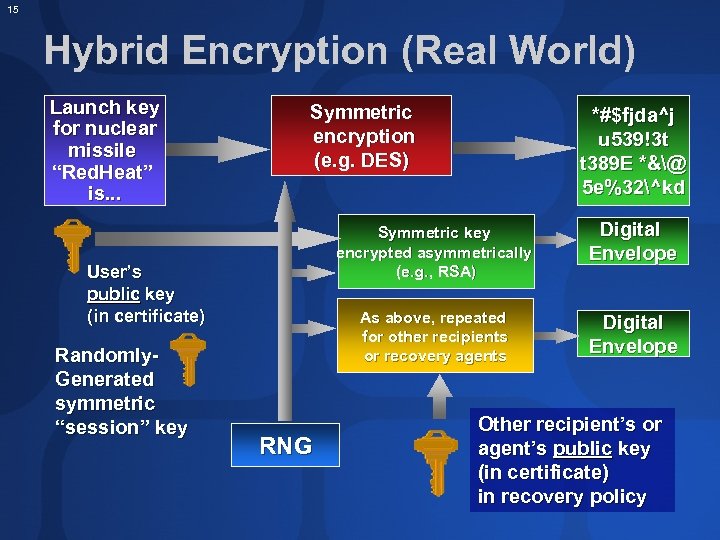
15 Hybrid Encryption (Real World) Launch key for nuclear missile “Red. Heat” is. . . Symmetric encryption (e. g. DES) Symmetric key encrypted asymmetrically (e. g. , RSA) RNG Digital Envelope As above, repeated for other recipients or recovery agents User’s public key (in certificate) Randomly. Generated symmetric “session” key *#$fjda^j u 539!3 t t 389 E *&@ 5 e%32^kd Digital Envelope Other recipient’s or agent’s public key (in certificate) in recovery policy
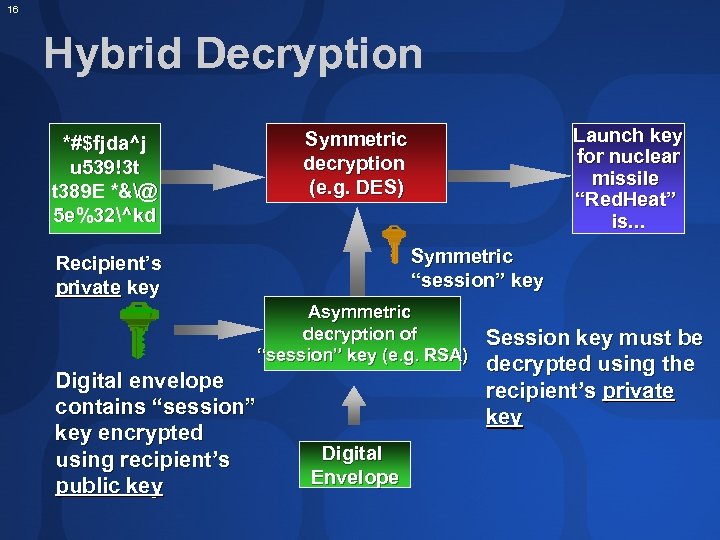
16 Hybrid Decryption *#$fjda^j u 539!3 t t 389 E *&@ 5 e%32^kd Launch key for nuclear missile “Red. Heat” is. . . Symmetric decryption (e. g. DES) Symmetric “session” key Recipient’s private key Asymmetric decryption of “session” key (e. g. RSA) Digital envelope contains “session” key encrypted using recipient’s public key Digital Envelope Session key must be decrypted using the recipient’s private key
17 Public Key Distribution Problem We just solved the problem of symmetric key distribution by using public/private keys But… Scott creates a keypair (private/public) and quickly tells the world that the public key he published belongs to Bill People send confidential stuff to Bill does not have the private key to read them… Scott reads Bill’s messages
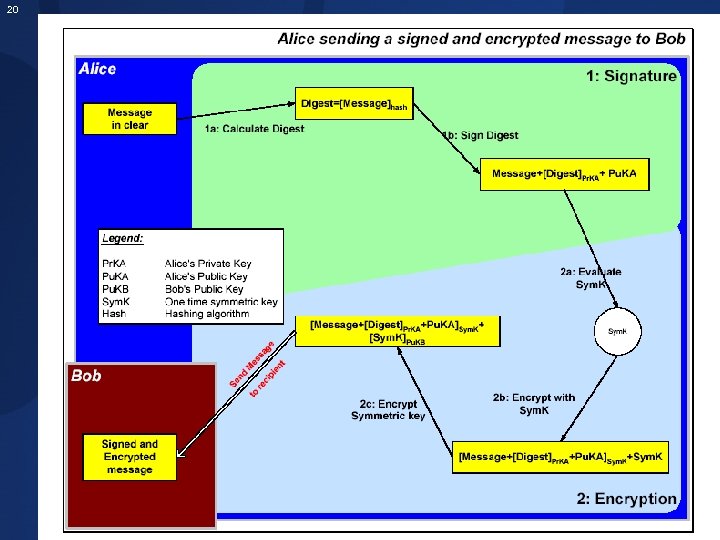
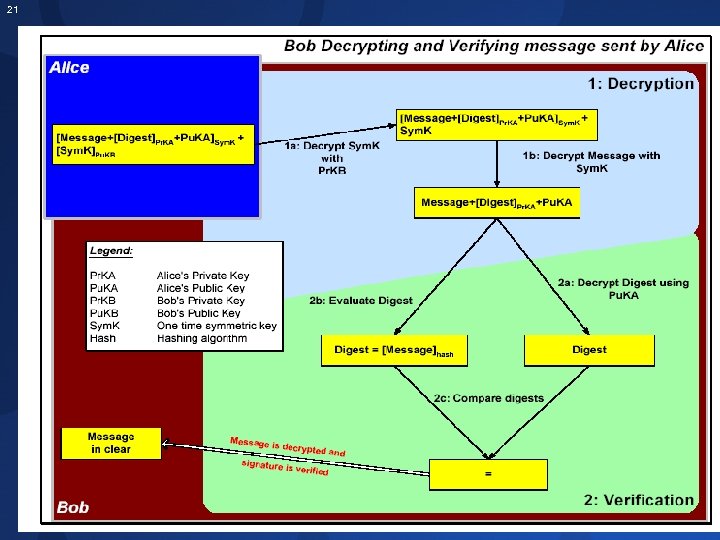
18 Digital Signature and Verification Digital signature is a mechanism by which a message is authenticated i. e. proving that a message is effectively coming from a given sender, much like a signature on a paper document. For instance, suppose that Alice wants to digitally sign a message to Bob. To do so, she uses her private-key to encrypt the message; she then sends the message along with her public-key (typically, the public key is attached to the signed message). Since Alice’s public-key is the only key that can decrypt that message, a successful decryption constitutes a Digital Signature Verification, meaning that there is no doubt that it is Alice’s private key that encrypted the message.
19 Hashing For Digital signature, another technique used is called hashing. Hashing produces a message digest that is a small and unique representation (a bit like a sophisticated checksum) of the complete message. Hashing algorithms are a one-way encryption, i. e. it is impossible to derive the message from the digest. The main reasons for producing a message digest are: 1. The message integrity being sent is preserved; any message alteration will immediately be detected; 2. The digital signature will be applied to the digest, which is usually considerably smaller than the message itself; 3. Hashing algorithms are much faster than any encryption algorithm (asymmetric or symmetric).
20
21

22 Fundamentals of PKI
23 Is PKI relevant? Who uses all of that stuff? Web’s HTTP and other protocols (SSL) VPN (PPTP, IPSec, L 2 TP…) Email (S/MIME, PGP, Exchange KMS) Files (W 2 K EFS, PGP and many others) Web Services (WS-Security) Good ID Smartcards (Certificates and Challenge/Response) Executables (. NET Assemblies, Drivers, Authenticode) …
24 Eureka! We need PKI to solve that problem And a few others…
25 . 2. What is a Certificate A certificate is a piece of information that proves the identity of a public-key’s owner. Like a passport, a certificate provides recognized proof of a person’s (or entity) identity. Certificates are signed and delivered securely by a trusted third party entity called a Certificate Authority (CA). As long as Bob and Alice trust this third party, the CA, they can be assured that the keys belong to the persons they claim to be.
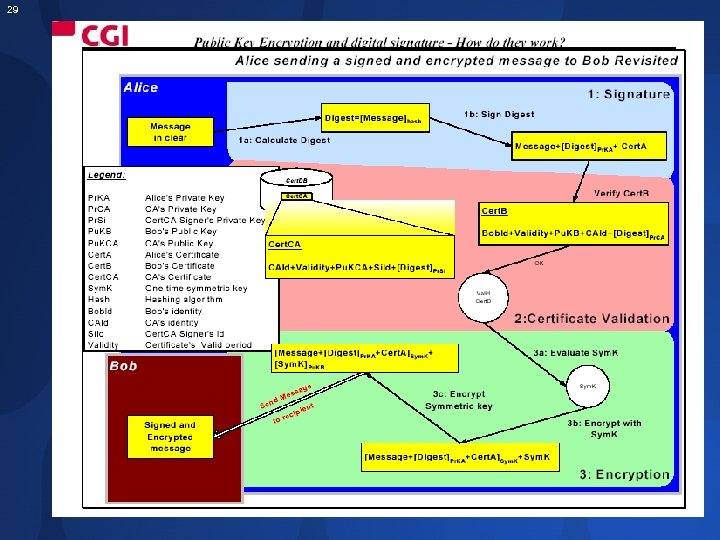
26 . A certificate contains among other things: 1) The CA’s identity 2) The owner’s identity 3) The owner’s public-key 4) The certificate expiry date 5) The CA’s signature of that certificate 6) Other information that is beyond the scope of this article. With a certificate instead of a public-key, a recipient can now verify a few things about the issuer to make sure that the certificate is valid and belongs to the person claiming its ownership:
27 Certificates The simplest certificate just contains: Information about the entity that is being certified to own a public key That public key And all of this is Digitally signed by someone trusted (like your friend or a CA)

28 X. 509 Certificate Authority Digital Signature of All Components Together: Serial Number Issuer X. 500 Distinguished Name Validity Period Subject X. 500 Distinguished Name OU=Project Botticelli… Subject Public Key Information The Key or Info About It Key/Certificate Usage Extensions
29
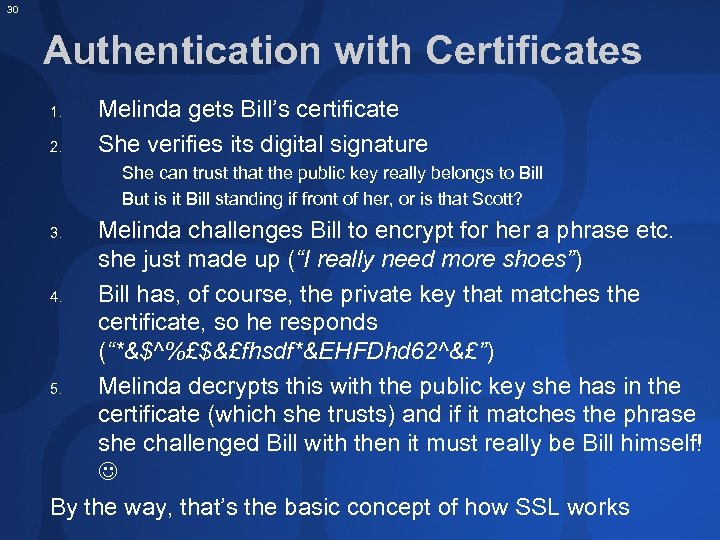
30 Authentication with Certificates 1. 2. Melinda gets Bill’s certificate She verifies its digital signature She can trust that the public key really belongs to Bill But is it Bill standing if front of her, or is that Scott? Melinda challenges Bill to encrypt for her a phrase etc. she just made up (“I really need more shoes”) 4. Bill has, of course, the private key that matches the certificate, so he responds (“*&$^%£$&£fhsdf*&EHFDhd 62^&£”) 5. Melinda decrypts this with the public key she has in the certificate (which she trusts) and if it matches the phrase she challenged Bill with then it must really be Bill himself! By the way, that’s the basic concept of how SSL works 3.
31 What’s in the Store? Certificates are “safe” No need to protect them too much, as they are digitally signed Store anywhere, a file or a “dumb” memory-only smartcard Private keys that match the public key are extremely vulnerable (key assets) You must protect them well Store in “Protected Storage” on your OS or a “smart” smartcard that will have crypto functionality on board
32 Key and certificate management is the set of operations required to create and maintain keys and certificates. The following is the list of the major points being addressed in a managed PKI: 1. Key and certificate creation: How to generate key pairs? How to issue certificates to the users? A PKI must offer software support for key pair generation as well as certificate requests. In addition, procedures must be put in place to verify the user identity prior to allowing him to request a certificate. Certificates are widely accessible because they are used for either encryption or signature verification. Private-keys require some reasonable level of protection because they are used either for decryption or for digital signature. A strong password mechanism must be part of the features of an effective PKI.
33 2. Private-key protection: How will the user protect his private-key against misuse by other malicious users? Certificates are widely accessible because they are used for either encryption or signature verification. Private-keys require some reasonable level of protection because they are used either for decryption or for digital signature. A strong password mechanism must be part of the features of an effective PKI. 3. Certificate revocation: How to handle the situation where a user’s private-key has been compromised? Similarly, how to handle the situation where an employee leaves the company? How to know whether or not a certificate has been revoked? A PKI must provide a means by which a certificate can be revoked. Once revoked, this certificate must be included in a revocation list that is available to all users. A mechanism must be provided to verify that revocation list and refuse to use a revoked certificate.
34 4. Key backup and recovery: What happens to encrypted files when a user loses his privatekey? Without key backup, all messages and files that have been encrypted with his public-key can no longer be decrypted and are lost forever. A PKI must offer private-key backup and a private-key recovery mechanism such that the user can get back his private-key to be able to get access to his files 11. 5. Key and certificate update: What happens when a certificate reaches or is near its expiry date? Keys and certificates have a finite lifetime. A PKI must offer a mechanism to at least update the expiry date for that certificate. Good practice though is to update the user’s keys and certificates. The key and certificate update can be automatic in which case the end user gets notified that his keys have been updated, or can require that the user performs an action during or before his keys and certificates expire;
35 Certificate Revocation Keys get compromised, as a fact of life You or your CA issue a certificate revocation certificate Must be signed by CA, of course And you do everything you can to let the world know that you issued it This is not easy Certificate Revocation Lists (CRL) are used They require that the process of cert validation actively checks the CRL and keep it up-to-date There are some scalability issues Many people disable this function That is why short expiration policies are important
36 Storing Certificates and Keys Certificates need to be stored so that interested users can obtain them Keys need to be stored for data recovery purposes This weakens the system, but is a necessity This is a function of most certificate servers such as certificate services in Windows 2003 Server Those servers are also responsible for issuing, revoking, signing etc. of certs
37 Developers: Which API? CAPI (Crypto API, Cryptographic API) is the underlying API provided by the operating system Mature Not too easy to use Good functionality . NET Framework System. Security. Cryptography Newer, but wraps some CAPI functions Extremely easy to use Not all needed functionality is present
38 . NET Framework API Comprehensive cryptographic library Easy, unified, stream-based architecture System. Security. Cryptography Open & extensible model (for new algorithms) Some implementations just CAPI wrappers, some completely managed by. NET Configuration classes for control Streaming model for block algorithms Supporting CBC (Cipher Block Chaining)
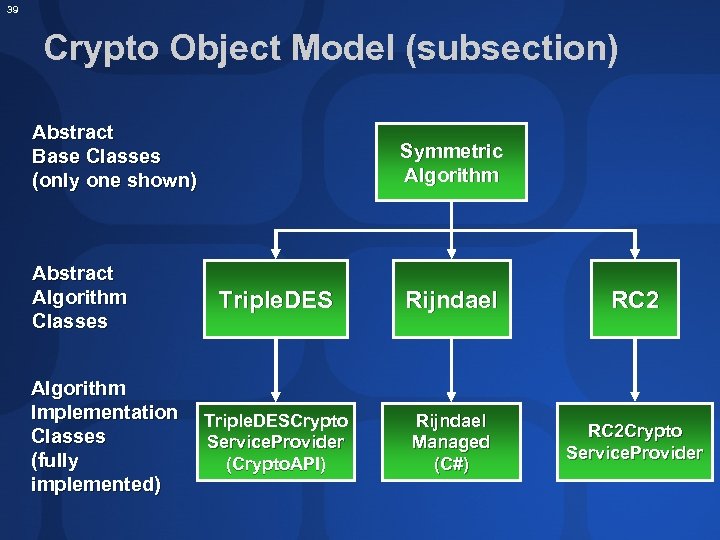
39 Crypto Object Model (subsection) Abstract Base Classes (only one shown) Abstract Algorithm Classes Algorithm Implementation Classes (fully implemented) Symmetric Algorithm Triple. DES Rijndael RC 2 Triple. DESCrypto Service. Provider (Crypto. API) Rijndael Managed (C#) RC 2 Crypto Service. Provider

40 Recommendations on PKI Deployment
41 CA Services If you decide against web-of-trust, you need to make an important decision: Use a well known CA Your certs will be universally recognised but you are dependent on the trustworthiness of the CA Establish your own CA No one except your explicitly nominated partners or clients will recognise your certs but you are in full control In addition, you may want to outsource CA services altogether
42 Identity Management Process Consider using Windows Server 2003 as it integrates active directory managament of users with PKI provisioning Microsoft is investing heavily in identity management across directory boundaries Between Active Directories Between heterogenous systems
43 Social Problem Real-life certificates are well understood What do you trust more: a passport or a driving license? Digital certificates are a long way from public understanding Is Verisign Class 1 better or worse than Class 5? What about BT Class 2 versus Thawte Class 3? Easier if you just deploy internal PKI Use real-life names, like “passport”, “company id” etc. if possible
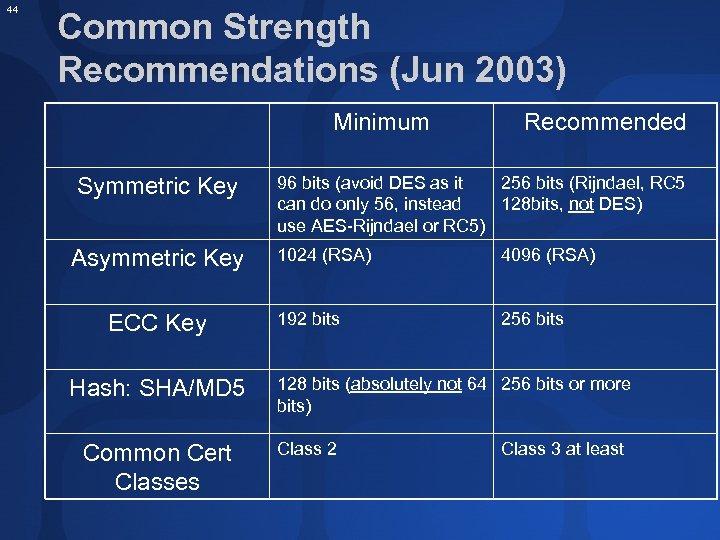
44 Common Strength Recommendations (Jun 2003) Minimum Symmetric Key Asymmetric Key ECC Key Hash: SHA/MD 5 Common Cert Classes Recommended 96 bits (avoid DES as it 256 bits (Rijndael, RC 5 can do only 56, instead 128 bits, not DES) use AES-Rijndael or RC 5) 1024 (RSA) 4096 (RSA) 192 bits 256 bits 128 bits (absolutely not 64 256 bits or more bits) Class 2 Class 3 at least
45 Word About Smartcards Most smartcards are “dumb”, i. e. they are only a memory chip This is OK for a certificate store, but not recommended for storing a private key used in a challenge test (verifying identity) Anyway, they are still better than leaving keys on a floppy disk Cryptographically-enabled smartcards are more expensive but they give much more security Private key is secure and used as needed Additional protection (password, biometrics) is possible Hardware implements some algorithms Self-destruct is possible
46 Certificate Revocations It is a good idea to prepare one in advance if possible! Keep it really safe Particularly important in web-of-trust systems in case you lose access to your private key Please, please enable checking and updating of CRL (revocation list) on all of your systems Apply numerous security patches – this was a particularly “patchy” area recently
47 Summary Asymmetric encryption solved the extremely difficult problem of key symmetric key exchange It created a smaller, easier to solve problem of asymmetric key management… Which is solved with PKI Bringing additional benefits, such as trust and identity management
48 Resources and Reading Visit www. microsoft. com/security Review session slides on crypto & security For more detail, read: PKI, A. Nash et al. , RSA Press, ISBN 0 -07 -213123 -3 Applied Cryptography, B. Schneier, John Wiley & Sons, ISBN 0 -471 -12845 -7 Foundations of Cryptography, O. Goldereich, www. eccc. uni-trier. de/eccc-local/ ECCC-Books/oded_book_readme. html Handbook of Applied Cryptography, A. J. Menezes, CRC Press, ISBN 0 -8493 -8523 -7 Cryptography in C and C++, M. Welschenbach, Apress, ISBN 1 -893115 -95 -X (includes code samples CD)
2ba7bb02faf3c833b270ca92da0d975d.ppt