ccb2e7534dcfb759befe26483b992de4.ppt
- Количество слайдов: 15
A Framework for Distributed OCSP without Responders Certificate Young-Ho Park (pyhoya@mail 1. pknu. ac. kr) Kyung-Hyune Rhee (khrhee@pknu. ac. kr) Pukyong National University WISA 2004 Lab. of Information security & Internet Applications, PKNU
Public Key Certificate ¢ Public Key Infrastructure(PKI) ¯ The main architecture for security services over the Internet ¢ Public Key Certificate ¯ Bind a public key to the owner’s identity information ¯ Digitally signed and certified by a trusted certificate authority(CA) ¢ Certificates Revocation ¯ Compromising of the key or abuse of the owner ¯ Certificates Revocation List (CRL) ¯ Online Certificate Status Protocol (OCSP) Lab. of Information security & Internet Applications, PKNU 2
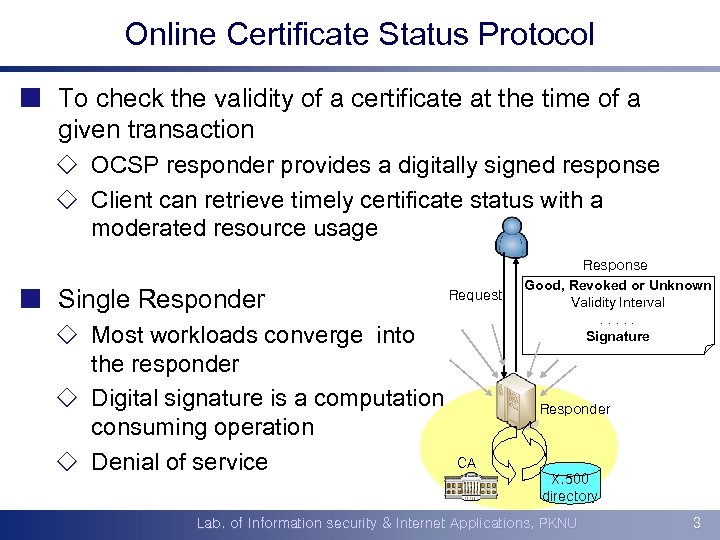
Online Certificate Status Protocol ¢ To check the validity of a certificate at the time of a given transaction ¯ OCSP responder provides a digitally signed response ¯ Client can retrieve timely certificate status with a moderated resource usage ¢ Single Responder ¯ Most workloads converge into the responder ¯ Digital signature is a computation consuming operation ¯ Denial of service Request Response Good, Revoked or Unknown Validity Interval. . . Signature Responder CA X. 500 directory Lab. of Information security & Internet Applications, PKNU 3
Distributed OCSP ¢ Composed of multiple OCSP responders ¯ Sharing and balancing the workload of OCSP response ¯ Client can choose one responder ¢ Certificate of responder is required to verify the signature in response of both OCSP and D-OCSP ¢ In D-OCSP ¯ Using the same private signing key for every responder ¾ Easy key management but high risk for key exposure ¯ Using different private key ¾ Increasing the complexity of key management Lab. of Information security & Internet Applications, PKNU 4
![KIS-D-OCSP (1) ¢ [S. Koga and K. Sakurai, PKC 2004] ¢ One solution for KIS-D-OCSP (1) ¢ [S. Koga and K. Sakurai, PKC 2004] ¢ One solution for](https://present5.com/presentation/ccb2e7534dcfb759befe26483b992de4/image-5.jpg)
KIS-D-OCSP (1) ¢ [S. Koga and K. Sakurai, PKC 2004] ¢ One solution for efficient certificate management of multiple responders ¯ Key insulated signature(KIS) scheme and hash chain ¯ Different private key for every responders but the same public key for signature verification ¾ Only one certificate is required for multiple responders ¾ Private key exposure of one responder does not effect other responders ¯ Hash chain is used for checking the validity of a responder at the given time period Lab. of Information security & Internet Applications, PKNU 5
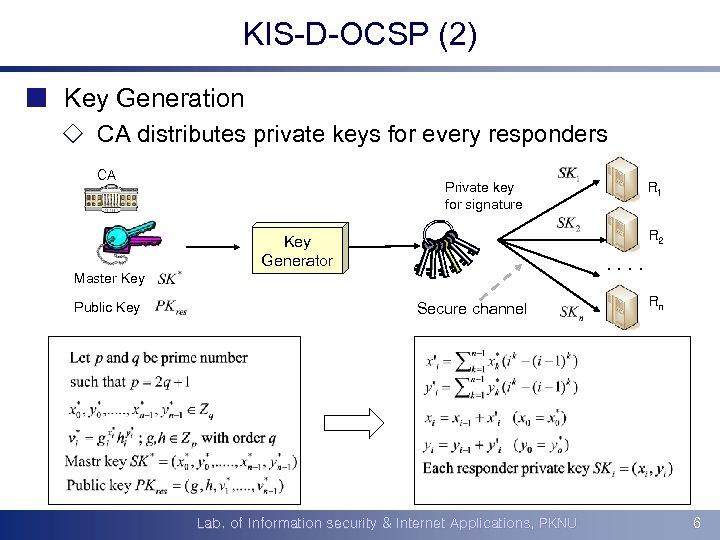
KIS-D-OCSP (2) ¢ Key Generation ¯ CA distributes private keys for every responders CA Private key for signature R 2 Key Generator . . Master Key Public Key R 1 Secure channel Lab. of Information security & Internet Applications, PKNU Rn 6
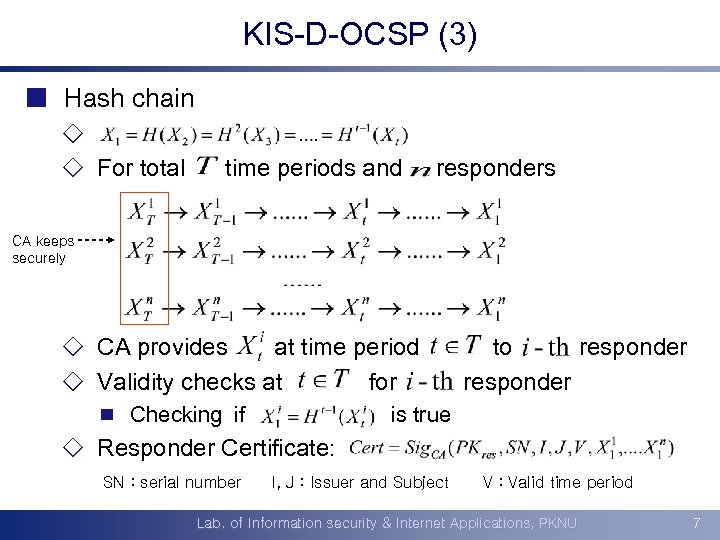
KIS-D-OCSP (3) ¢ Hash chain ¯ ¯ For total time periods and responders CA keeps securely ¯ CA provides at time period ¯ Validity checks at for ¾ Checking if to responder is true ¯ Responder Certificate: SN : serial number I, J : Issuer and Subject V : Valid time period Lab. of Information security & Internet Applications, PKNU 7
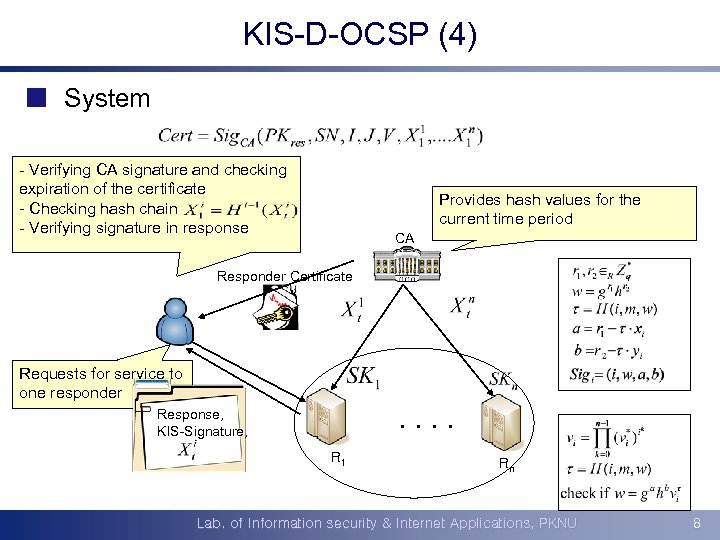
KIS-D-OCSP (4) ¢ System - Verifying CA signature and checking expiration of the certificate - Checking hash chain - Verifying signature in response Provides hash distributes private Generates andvalues for the current every responders keys fortime period CA Responder Certificate Requests for service to one responder Response, KIS-Signature, . . R 1 Rn Lab. of Information security & Internet Applications, PKNU 8
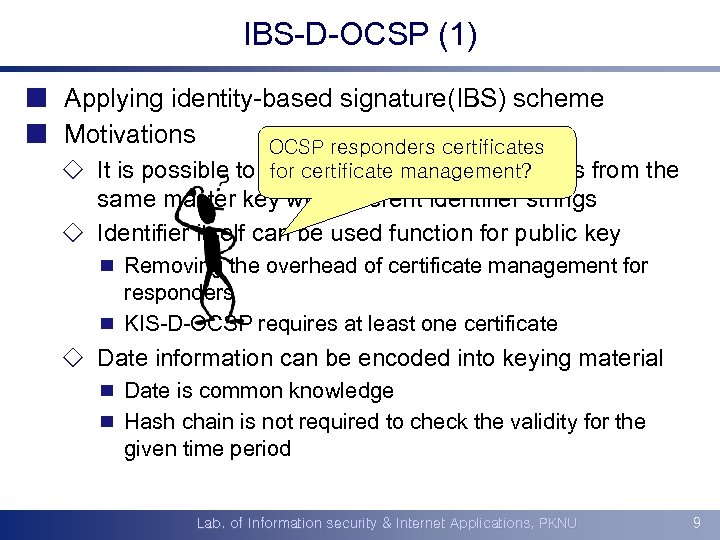
IBS-D-OCSP (1) ¢ Applying identity-based signature(IBS) scheme ¢ Motivations OCSP responders certificates for certificate management? ¯ It is possible to generate different private keys from the same master key with different identifier strings ¯ Identifier itself can be used function for public key ¾ Removing the overhead of certificate management for responders ¾ KIS-D-OCSP requires at least one certificate ¯ Date information can be encoded into keying material ¾ Date is common knowledge ¾ Hash chain is not required to check the validity for the given time period Lab. of Information security & Internet Applications, PKNU 9
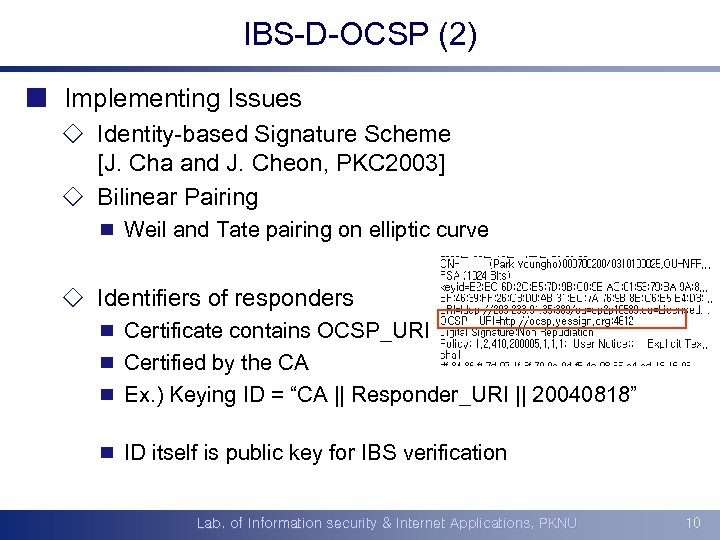
IBS-D-OCSP (2) ¢ Implementing Issues ¯ Identity-based Signature Scheme [J. Cha and J. Cheon, PKC 2003] ¯ Bilinear Pairing ¾ Weil and Tate pairing on elliptic curve ¯ Identifiers of responders ¾ Certificate contains OCSP_URI ¾ Certified by the CA ¾ Ex. ) Keying ID = “CA || Responder_URI || 20040818” ¾ ID itself is public key for IBS verification Lab. of Information security & Internet Applications, PKNU 10
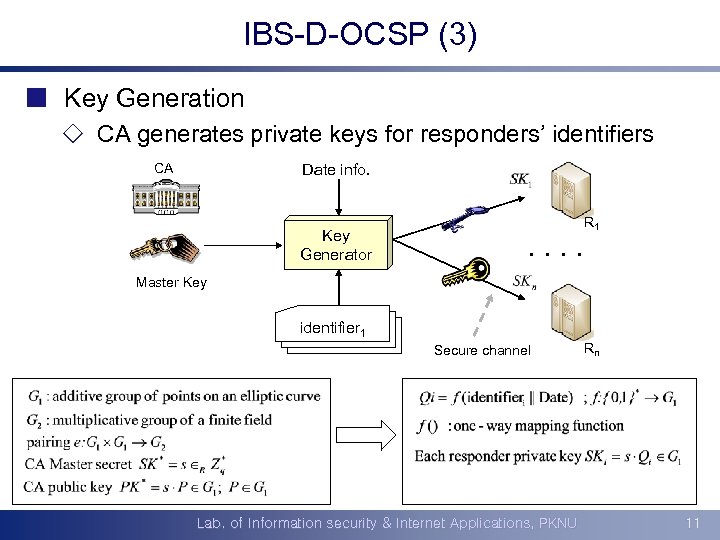
IBS-D-OCSP (3) ¢ Key Generation ¯ CA generates private keys for responders’ identifiers CA Date info. Key Generator R 1 . . Master Key identifier 1 Secure channel Lab. of Information security & Internet Applications, PKNU Rn 11
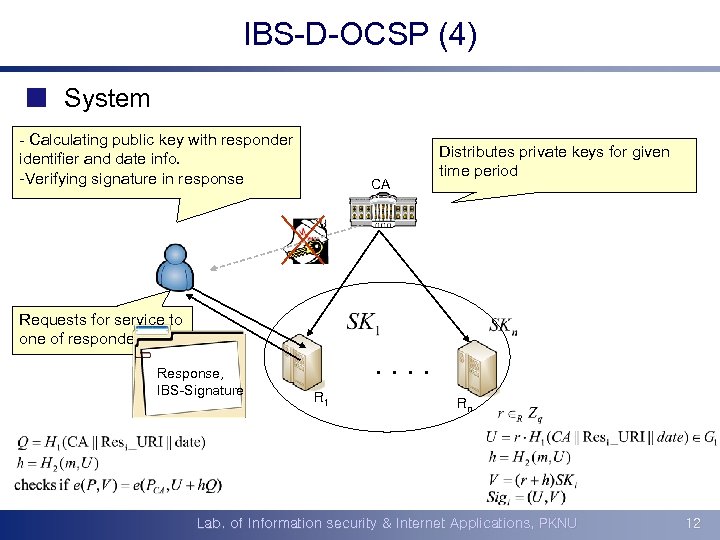
IBS-D-OCSP (4) ¢ System - Calculating public key with responder identifier and date info. -Verifying signature in response CA Distributes private keys for given time period Requests for service to one of responders Response, IBS-Signature . . R 1 Rn Lab. of Information security & Internet Applications, PKNU 12
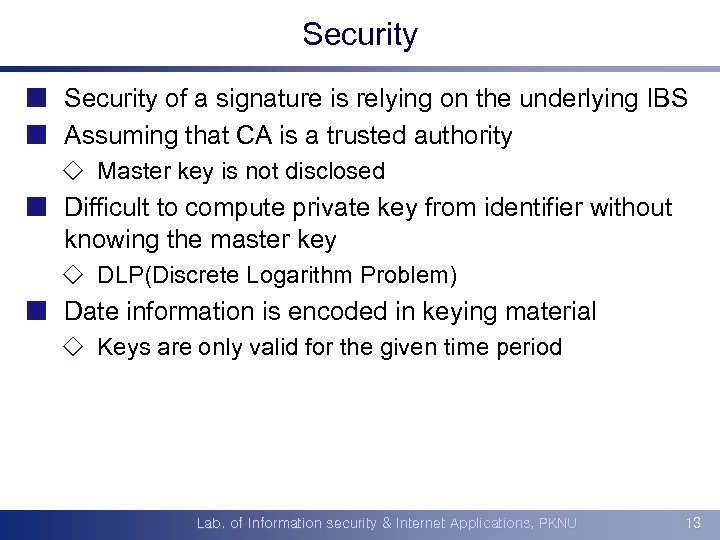
Security ¢ Security of a signature is relying on the underlying IBS ¢ Assuming that CA is a trusted authority ¯ Master key is not disclosed ¢ Difficult to compute private key from identifier without knowing the master key ¯ DLP(Discrete Logarithm Problem) ¢ Date information is encoded in keying material ¯ Keys are only valid for the given time period Lab. of Information security & Internet Applications, PKNU 13

Efficiency ¢ n n K I Compare KIS-D-OCSP & S D Master public key size is proportional to O the number of responders C S At least one certificate for responders P I B IBS-D-OCSP S D n Master public key size is constant to O the number of responders C n No certificate. S responders for P n CA stores hash values securely n CA stores no hash values n Return : {response, signature, hash} n Return : {response, signature} n 2 signature verifications + ( t-I ) hashing n 1 signature verification n Hash chains to check timely validity n Encoding date info. into keying material n Update hash values every time period n Refresh private keys every time period Lab. of Information security & Internet Applications, PKNU 14

Conclusion ¢ Public key certificate is essential for secure Internet ¯ Certificate validity checking is required ¯ OCSP is one solution ¢ Proposed an efficient D-OCSP framework ¯ IBS-D-OCSP ¯ Remove responders certificate ¾ Don’t require additional certificate management ¯ Any other efficient IBS schemes can be applied to the system Lab. of Information security & Internet Applications, PKNU 15
ccb2e7534dcfb759befe26483b992de4.ppt