d7d4cbd2d464aacf82e79cd0463dffd3.ppt
- Количество слайдов: 33
 41 st World Telecommunication and Information Society Day IETE, 17 May 2009, New Delhi Protecting Children in cyberspace Karnika Seth Cyberlaw Expert & Partner, Seth Associates © Seth Associates, 2008 All Rights Reserved
41 st World Telecommunication and Information Society Day IETE, 17 May 2009, New Delhi Protecting Children in cyberspace Karnika Seth Cyberlaw Expert & Partner, Seth Associates © Seth Associates, 2008 All Rights Reserved
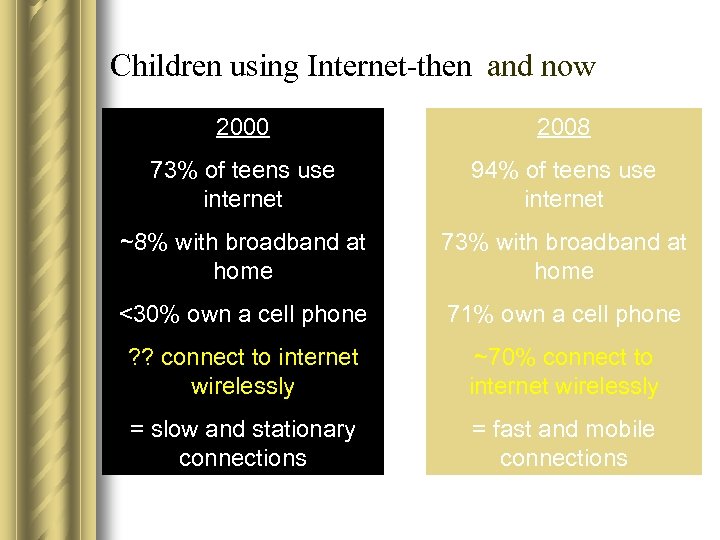 Children using Internet-then and now 2000 2008 73% of teens use internet 94% of teens use internet ~8% with broadband at home 73% with broadband at home <30% own a cell phone 71% own a cell phone ? ? connect to internet wirelessly ~70% connect to internet wirelessly = slow and stationary connections = fast and mobile connections
Children using Internet-then and now 2000 2008 73% of teens use internet 94% of teens use internet ~8% with broadband at home 73% with broadband at home <30% own a cell phone 71% own a cell phone ? ? connect to internet wirelessly ~70% connect to internet wirelessly = slow and stationary connections = fast and mobile connections
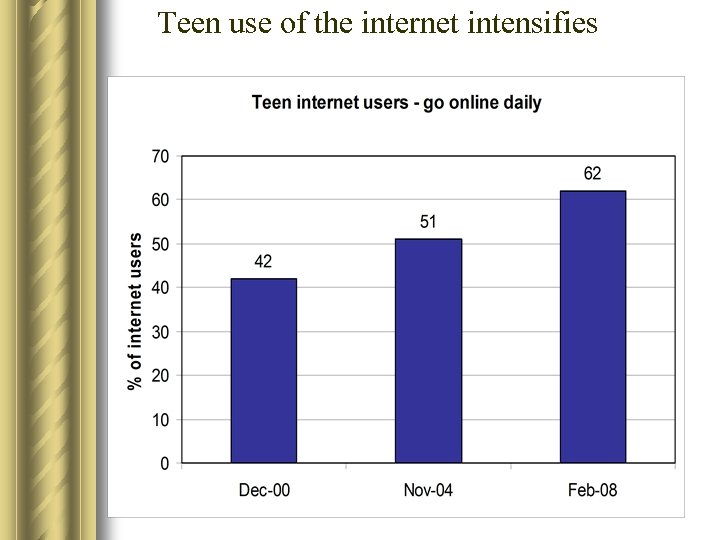 Teen use of the internet intensifies
Teen use of the internet intensifies
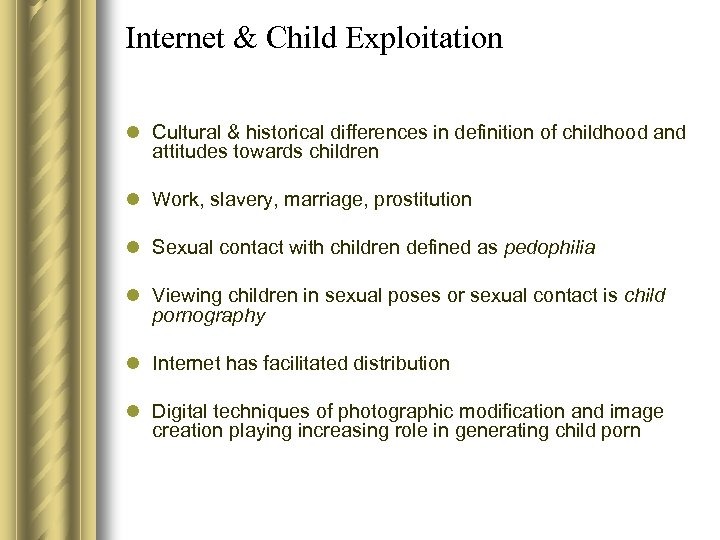 Internet & Child Exploitation l Cultural & historical differences in definition of childhood and attitudes towards children l Work, slavery, marriage, prostitution l Sexual contact with children defined as pedophilia l Viewing children in sexual poses or sexual contact is child pornography l Internet has facilitated distribution l Digital techniques of photographic modification and image creation playing increasing role in generating child porn
Internet & Child Exploitation l Cultural & historical differences in definition of childhood and attitudes towards children l Work, slavery, marriage, prostitution l Sexual contact with children defined as pedophilia l Viewing children in sexual poses or sexual contact is child pornography l Internet has facilitated distribution l Digital techniques of photographic modification and image creation playing increasing role in generating child porn
 Children on Internet could be victimized l l l l Cyber bullying Child pornography Child abuse Cognitive distortions Identity theft cases Cheating & fraud Lured into criminal activities Theft of personal information
Children on Internet could be victimized l l l l Cyber bullying Child pornography Child abuse Cognitive distortions Identity theft cases Cheating & fraud Lured into criminal activities Theft of personal information
 General concerns for children online l May inadvertently or intentionally access adult pornographic or violent material l Links or emails with innocent subjects that actually contain pornography l Children being approached or observed in chat rooms l Children’s identities, location or vulnerability being sourced from material available online l Social networking sites may introduce child pornography
General concerns for children online l May inadvertently or intentionally access adult pornographic or violent material l Links or emails with innocent subjects that actually contain pornography l Children being approached or observed in chat rooms l Children’s identities, location or vulnerability being sourced from material available online l Social networking sites may introduce child pornography
 Child pornography on Internet l Since 1999, the Interpol Standing Working Group on Offenses Against Minors has used the following definition: l Child pornography is the consequence of the exploitation or sexual abuse perpetrated against a child. It can be defined as any means of depicting or promoting sexual abuse of a child, including print and/or audio, centered on sex acts or the genital organs of children.
Child pornography on Internet l Since 1999, the Interpol Standing Working Group on Offenses Against Minors has used the following definition: l Child pornography is the consequence of the exploitation or sexual abuse perpetrated against a child. It can be defined as any means of depicting or promoting sexual abuse of a child, including print and/or audio, centered on sex acts or the genital organs of children.
 Unique problems arising from child pornography on the internet l l l l l Lack of borders/mobility Differences in international law Anonymity Accessibility Quantity Satiation and subsequent increasing thresholds for content Normalise deviant sexual interest Desire to replicate scenarios viewed on the internet Commercial trading Peer-to-peer networks – Huge digital collections – Encrypted files
Unique problems arising from child pornography on the internet l l l l l Lack of borders/mobility Differences in international law Anonymity Accessibility Quantity Satiation and subsequent increasing thresholds for content Normalise deviant sexual interest Desire to replicate scenarios viewed on the internet Commercial trading Peer-to-peer networks – Huge digital collections – Encrypted files
 Test of obscenity l Obscenity is difficult to define- Miller Test in U. S – – – Average person Contemporary community standards Prurient interest Patently offensive depiction of sex acts Lacking in serious value l All of these elements are subjective and debatable l Position in Indial Ajay Goswami v UOI[1] , the Supreme court considered the issue of obscenity on internet and held that restriction on freedom of speech on ground of curtailing obscenity amounts to reasonable restriction under Article 19(2) of the Constitution. The court observed that the test of community mores and standards has become obsolete in the internet age. l [1] 2007(1) SCC 143 see also Maqbool Fida Hussain v Raj Kumar Pandey 2008(6) ( Delhi) 533 -publishing obscene information on internet amounts to an offence
Test of obscenity l Obscenity is difficult to define- Miller Test in U. S – – – Average person Contemporary community standards Prurient interest Patently offensive depiction of sex acts Lacking in serious value l All of these elements are subjective and debatable l Position in Indial Ajay Goswami v UOI[1] , the Supreme court considered the issue of obscenity on internet and held that restriction on freedom of speech on ground of curtailing obscenity amounts to reasonable restriction under Article 19(2) of the Constitution. The court observed that the test of community mores and standards has become obsolete in the internet age. l [1] 2007(1) SCC 143 see also Maqbool Fida Hussain v Raj Kumar Pandey 2008(6) ( Delhi) 533 -publishing obscene information on internet amounts to an offence
 Types of child pornography offences l l View + collect child pornography View, collect + distribute child pornography View, collect and distribute child pornography + commit contact offences l View, collect and distribute child pornography, commit contact offences + produce child pornography
Types of child pornography offences l l View + collect child pornography View, collect + distribute child pornography View, collect and distribute child pornography + commit contact offences l View, collect and distribute child pornography, commit contact offences + produce child pornography
 Cyber Predators Statistics l “…A child goes missing every 40 seconds in the U. S, over 2, 100 per day” (OJJDP) l In 2005, 662, 196 children were reported lost, runaway, or kidnapped (ncmec) l 2/3 of all missing children reports were for youths aged 15 -17 (ncmec) l 2/5 missing children ages 15 -17 are abducted due to Internet activity (ICAC)
Cyber Predators Statistics l “…A child goes missing every 40 seconds in the U. S, over 2, 100 per day” (OJJDP) l In 2005, 662, 196 children were reported lost, runaway, or kidnapped (ncmec) l 2/3 of all missing children reports were for youths aged 15 -17 (ncmec) l 2/5 missing children ages 15 -17 are abducted due to Internet activity (ICAC)
 Cyber porn convictionsl In a California case, police posed as a thirteen-year-old girl and apprehended thirty-four-year-old Patrick Naughton, an executive vice-president of Infoseek Corporation, for attempting to have sex with a "child. “ l On September 24, 1999, Michael David Rostoker was arrested in San Jose, California for "traveling to engage in sex with a minor and enticing someone under 18 into sexual activity. “ l Air force Bal Bharati School case , Delhi; class(XII) student created pornographic site as revenge against his classmates (girls) and posted pornographic images of his classmates and lady teachers in internet. He was then suspended by school and arrested by Police under IPC and IT Act; though Juvenile Court allowed his bail thereafter.
Cyber porn convictionsl In a California case, police posed as a thirteen-year-old girl and apprehended thirty-four-year-old Patrick Naughton, an executive vice-president of Infoseek Corporation, for attempting to have sex with a "child. “ l On September 24, 1999, Michael David Rostoker was arrested in San Jose, California for "traveling to engage in sex with a minor and enticing someone under 18 into sexual activity. “ l Air force Bal Bharati School case , Delhi; class(XII) student created pornographic site as revenge against his classmates (girls) and posted pornographic images of his classmates and lady teachers in internet. He was then suspended by school and arrested by Police under IPC and IT Act; though Juvenile Court allowed his bail thereafter.
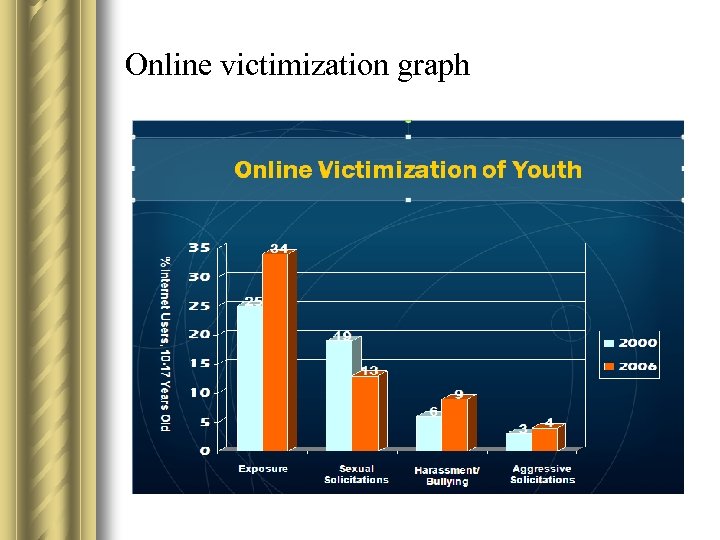 Online victimization graph
Online victimization graph
 Role of Law enforcement-India l Cybercrime cells established to deal with cyber offences in India l IT Act, 2000 amended to include special provisions on child pornography. The newly passed Information Technology Bill is set to make it illegal to not only create and transmit child pornography in any electronic form, but even to browse it. The punishment for a first offence of publishing creating, exchanging, downloading or browsing any electronic depiction of children in "obscene or indecent or sexually explicit manner" can attract five years in jail and a fine of Rs 10 lakh.
Role of Law enforcement-India l Cybercrime cells established to deal with cyber offences in India l IT Act, 2000 amended to include special provisions on child pornography. The newly passed Information Technology Bill is set to make it illegal to not only create and transmit child pornography in any electronic form, but even to browse it. The punishment for a first offence of publishing creating, exchanging, downloading or browsing any electronic depiction of children in "obscene or indecent or sexually explicit manner" can attract five years in jail and a fine of Rs 10 lakh.
 Position in India l Section 67 of the existing IT Act deals with "publishing obscene information in electronic form". It is a generally worded section that does not specifically define "pornography" or make it an offence, and does not mention "child pornography" at all l Section 293 IPC - distribution of obscene books to young persons below 20 yrs-punishable with two years of imprisonment-It also states that it is a cognizable offence and the Magistrate is empowered to try any such offence
Position in India l Section 67 of the existing IT Act deals with "publishing obscene information in electronic form". It is a generally worded section that does not specifically define "pornography" or make it an offence, and does not mention "child pornography" at all l Section 293 IPC - distribution of obscene books to young persons below 20 yrs-punishable with two years of imprisonment-It also states that it is a cognizable offence and the Magistrate is empowered to try any such offence
 Position in USA l After the U. S. Supreme Court struck down the CDA’s provisions governing obscene materials, Congress passed the Children’s Online Protection Act (COPA), codified at 47 U. S. C. § 231 (http: //www. law. cornell. edu/uscode/47/231. html), in an effort to satisfy the First Amendment requirements affirmed in Reno v. ACLU.
Position in USA l After the U. S. Supreme Court struck down the CDA’s provisions governing obscene materials, Congress passed the Children’s Online Protection Act (COPA), codified at 47 U. S. C. § 231 (http: //www. law. cornell. edu/uscode/47/231. html), in an effort to satisfy the First Amendment requirements affirmed in Reno v. ACLU.
 Position in USA l Unlike pornographic images of adults, the First Amendment does not protect the possession or distribution of child pornography. Content that depicts children engaged in sexual conduct is "a category of material outside the protection of the First Amendment. " New York v. Ferber, 458 U. S. 747 1982
Position in USA l Unlike pornographic images of adults, the First Amendment does not protect the possession or distribution of child pornography. Content that depicts children engaged in sexual conduct is "a category of material outside the protection of the First Amendment. " New York v. Ferber, 458 U. S. 747 1982
 Net. Alert in Australia l Australia’s internet safety advisory body l Established in 1999 to provide independent advice and education on internet safety and managing access to online content l For tips and advice on internet safety for parents, teachers, children and others visit the website l www. netalert. net. au l 1800 880 176 l Australian Communications and Media Authority (ACMA, formerly ABA) l Australian Federal Police Online Child Sex Exploitation Team
Net. Alert in Australia l Australia’s internet safety advisory body l Established in 1999 to provide independent advice and education on internet safety and managing access to online content l For tips and advice on internet safety for parents, teachers, children and others visit the website l www. netalert. net. au l 1800 880 176 l Australian Communications and Media Authority (ACMA, formerly ABA) l Australian Federal Police Online Child Sex Exploitation Team
 Germany –new law against child porn
Germany –new law against child porn
 Online safety of children l Vigilance groups reporting child pornographers l Technical softwares to protect children on internet l Place computer in activity centre of house l Block children’s access to specific sites - only partly effective l Set time limits and suitable sites l Closely supervise internet use l Educate yourself of latest sites that children visit
Online safety of children l Vigilance groups reporting child pornographers l Technical softwares to protect children on internet l Place computer in activity centre of house l Block children’s access to specific sites - only partly effective l Set time limits and suitable sites l Closely supervise internet use l Educate yourself of latest sites that children visit
 High risk indicators l More technical knowledge than parents l Teens who feel they are not listened to l Do not feel like they are getting enough attention l Do not communicate about who or what they are doing online l Deleting computer’s Internet history l Minimize screen or switch to another screen quickly when someone comes in the room l Unexplained phone calls l Unexplained absences l Unexpected gifts
High risk indicators l More technical knowledge than parents l Teens who feel they are not listened to l Do not feel like they are getting enough attention l Do not communicate about who or what they are doing online l Deleting computer’s Internet history l Minimize screen or switch to another screen quickly when someone comes in the room l Unexplained phone calls l Unexplained absences l Unexpected gifts
 The ten commandments of child protection in cyberspace 1. Rules from “real” life apply: courtesy, kindness, modesty, dignity, respect for the law and for others, etc. 2. Don’t talk to strangers 3. Keep your private information private 4. Never agree to meet an online friend without your parents 5. There are no guarantees that what you say or post on the Internet is private
The ten commandments of child protection in cyberspace 1. Rules from “real” life apply: courtesy, kindness, modesty, dignity, respect for the law and for others, etc. 2. Don’t talk to strangers 3. Keep your private information private 4. Never agree to meet an online friend without your parents 5. There are no guarantees that what you say or post on the Internet is private
 The ten commandments of child protection in cyberspace 6. Information (including photos, videos, etc. ) posted on the Internet can last forever 7. Tell your parents if you encounter something uncomfortable 8. Don’t reply to unknown screen names on IM 9. Never open e-mail from strangers or click on any attachments 10. Find the “good” online – good friends, good Web sites, good games – and enjoy
The ten commandments of child protection in cyberspace 6. Information (including photos, videos, etc. ) posted on the Internet can last forever 7. Tell your parents if you encounter something uncomfortable 8. Don’t reply to unknown screen names on IM 9. Never open e-mail from strangers or click on any attachments 10. Find the “good” online – good friends, good Web sites, good games – and enjoy
 Precautions are better than cure. . l Discuss and agree upon precautions – – People may not be who they say they are online Encourage the use of pen names Remove address and contact details from emails Never respond to obscene or suggestive messages – Don’t send personal photos over the internet
Precautions are better than cure. . l Discuss and agree upon precautions – – People may not be who they say they are online Encourage the use of pen names Remove address and contact details from emails Never respond to obscene or suggestive messages – Don’t send personal photos over the internet
 Secure online connections l Install and keep up-to-date anti-virus, antispyware, and firewall – Microsoft Malicious Software Removal Tool http: //www. microsoft. com/downloads/details. aspx? Family. Id=AD 724 AE 0 -E 72 D-4 F 54 -9 AB 375 B 8 EB 148356&displaylang=en – CCleaner (Free) http: //www. ccleaner. com/download/ – Anti-Spyware – A-Squared (free) http: //download 5. emsisoft. com/a 2 Free. Setup. exe – AVG Free http: //free. grisoft. com/ l Use Commercial Web Filtering Software – Free - http: //www. k 9 webprotection. com/ – Net Nanny (2007 best) http: //www. netnanny. com/ l Check internet cache – @winspy (free) http: //www. acesoft. net/winspy l Spector Pro to track everything done on a PC http: //www. spectorsoft. com/products/Spector. Pro_Windows
Secure online connections l Install and keep up-to-date anti-virus, antispyware, and firewall – Microsoft Malicious Software Removal Tool http: //www. microsoft. com/downloads/details. aspx? Family. Id=AD 724 AE 0 -E 72 D-4 F 54 -9 AB 375 B 8 EB 148356&displaylang=en – CCleaner (Free) http: //www. ccleaner. com/download/ – Anti-Spyware – A-Squared (free) http: //download 5. emsisoft. com/a 2 Free. Setup. exe – AVG Free http: //free. grisoft. com/ l Use Commercial Web Filtering Software – Free - http: //www. k 9 webprotection. com/ – Net Nanny (2007 best) http: //www. netnanny. com/ l Check internet cache – @winspy (free) http: //www. acesoft. net/winspy l Spector Pro to track everything done on a PC http: //www. spectorsoft. com/products/Spector. Pro_Windows
 Useful softwares l Monitoring Software l Spectorsoft. com or 1 -888 -598 -2788 l Safety-net. info or 1 -800 -513 -1916 l Software 4 Parents. com or 1 -866 -345 -8371 l PCmagazine. com (search “parental monitoring”)
Useful softwares l Monitoring Software l Spectorsoft. com or 1 -888 -598 -2788 l Safety-net. info or 1 -800 -513 -1916 l Software 4 Parents. com or 1 -866 -345 -8371 l PCmagazine. com (search “parental monitoring”)
 Vigilance can help ! l Look at the online handout on how to check computer history files to find what has been surfed. Also check the settings and documents in My documents to see what is on their account. l Undelete files with Restoration or PC Inspector File recovery to find out what your child has deleted. Look for files in the recycle bin and ones that have been deleted.
Vigilance can help ! l Look at the online handout on how to check computer history files to find what has been surfed. Also check the settings and documents in My documents to see what is on their account. l Undelete files with Restoration or PC Inspector File recovery to find out what your child has deleted. Look for files in the recycle bin and ones that have been deleted.
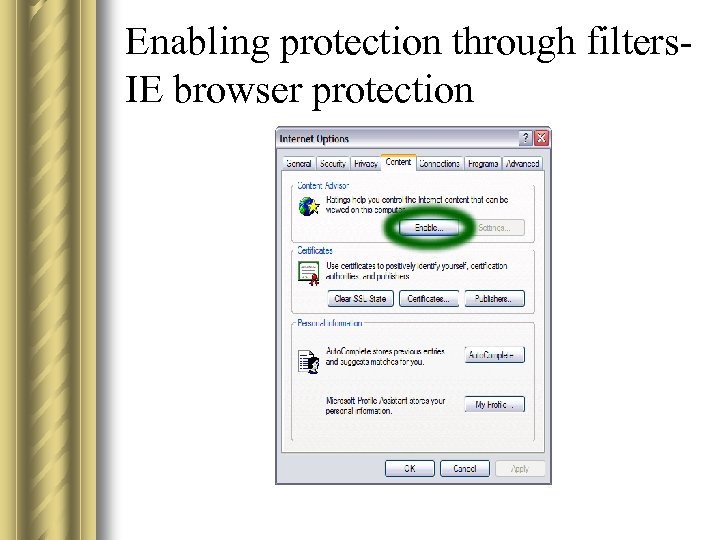 Enabling protection through filters. IE browser protection
Enabling protection through filters. IE browser protection
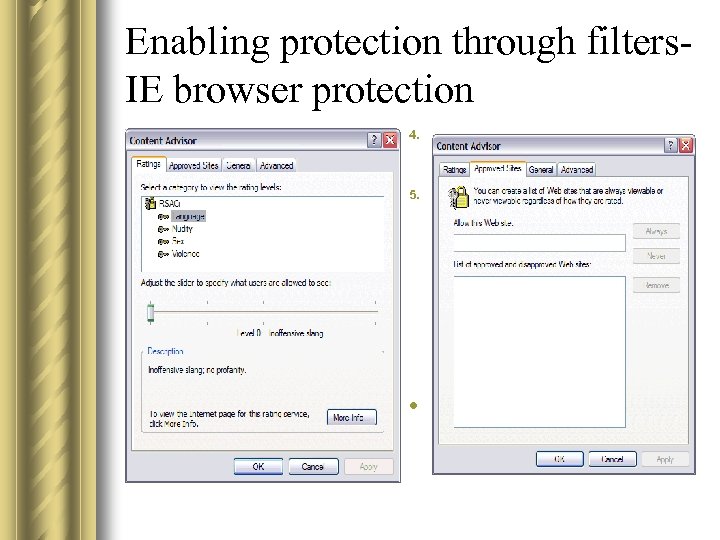 Enabling protection through filters. IE browser protection 4. 5. Select filter settings for the categories shown: Language, Nudity, Sex, Violence. The further right you push the slider, the more content is allowed. Click on the Approved Sites tab. Here you can type in any specific websites that you might want to be treated specially. You can come back and change this list later, perhaps after feedback from your family. 'Approved Sites' list 6. Navigate to the General tab, and click on Create Password. This will set you up as Administrator, and prevent other users from altering the Content Advisor settings. Change the Rating Settings to block types of content l es shown: Language, Nudity, Sex, Violence. The further right you push the slider, the more content is allowed. Change the Rating Settings to block types of content
Enabling protection through filters. IE browser protection 4. 5. Select filter settings for the categories shown: Language, Nudity, Sex, Violence. The further right you push the slider, the more content is allowed. Click on the Approved Sites tab. Here you can type in any specific websites that you might want to be treated specially. You can come back and change this list later, perhaps after feedback from your family. 'Approved Sites' list 6. Navigate to the General tab, and click on Create Password. This will set you up as Administrator, and prevent other users from altering the Content Advisor settings. Change the Rating Settings to block types of content l es shown: Language, Nudity, Sex, Violence. The further right you push the slider, the more content is allowed. Change the Rating Settings to block types of content
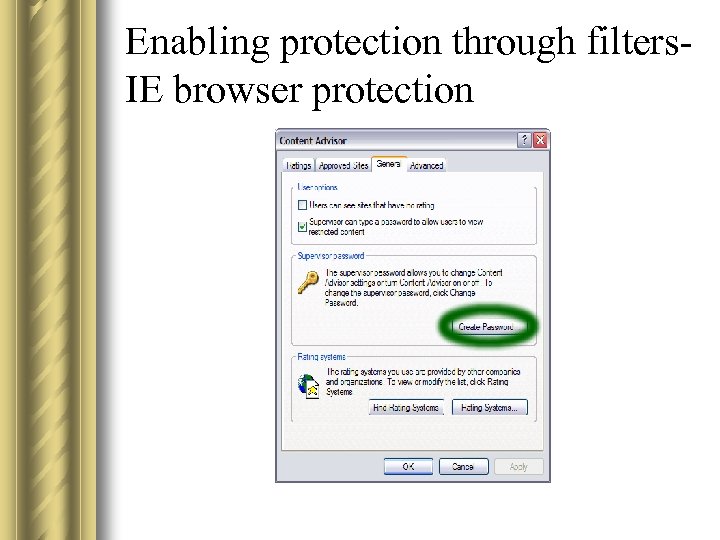 Enabling protection through filters. IE browser protection
Enabling protection through filters. IE browser protection
 Thank You! SETH ASSOCIATES ADVOCATES AND LEGAL CONSULTANTS New Delhi Law Office: C-1/16, Daryaganj, New Delhi-110002, India Tel: +91 (11) 65352272, +91 9868119137 Corporate Law Office: B-10, Sector 40, NOIDA-201301, N. C. R , India Tel: +91 (120) 4352846, +91 9810155766 Fax: +91 (120) 4331304 E-mail: mail@sethassociates. com © Seth Associates, 2009 All Rights Reserved
Thank You! SETH ASSOCIATES ADVOCATES AND LEGAL CONSULTANTS New Delhi Law Office: C-1/16, Daryaganj, New Delhi-110002, India Tel: +91 (11) 65352272, +91 9868119137 Corporate Law Office: B-10, Sector 40, NOIDA-201301, N. C. R , India Tel: +91 (120) 4352846, +91 9810155766 Fax: +91 (120) 4331304 E-mail: mail@sethassociates. com © Seth Associates, 2009 All Rights Reserved


