8c58081f008b3144bd6f2492bfb5c1d5.ppt
- Количество слайдов: 37
33 AE IBM i System Logging for Compliance & SIEM Integration Patrick Townsend 724 Columbia Street NW, Suite 400 | Olympia, WA 98501 | 360. 359. 4400 | www. townsendsecurity. com
What is the big deal about system log collection and monitoring? National Institute of Standards & Technology (NIST) System Administration, Networking, and Security (SANS) Open Web Application Security Project (OWASP) Information Security Continuous Monitoring (ISCM) President’s Directive on Cyber Security DHS Continuous Diagnostics and Mitigation (CDM)
CIS Critical Security Control #6 Maintenance, Monitoring, and Analysis of Audit Logs 6. 6 Deploy a SIEM (Security Information and Event Management) or log analytic tools for log aggregation and consolidation from multiple machines and for log correlation and analysis. Using the SIEM tool, system administrators and security personnel should devise profiles of common events from given systems so that they can tune detection to focus on unusual activity, avoid false positives, more rapidly identify anomalies, and prevent overwhelming analysts with insignificant alerts.
Compliance Regulations Require System Logging § New regulations mandate that critical system actions are (securely) logged § It is not enough to assert you’ve done the right thing, you have to prove it § Government and industry regulations recognize the need for independent, verifiable, logs. § PCI requires logging of Administrative actions § GLBA / FFIEC requires logs of actions that could affect financial reporting or fraud § HIPAA requires logs of access to PHI
PCI Sections 10 and 11 Require Logging Requirement 10: Track and monitor all access to network resources and cardholder data § 10. 1 Establish a process for linking all access to system components (especially access done with administrative privileges such as root) to each individual user. § 10. 2 Implement automated audit trails for all system components to reconstruct the following events: § 10. 3 Record at least the following audit trail entries for all system components for each event: § 10. 4 Using time-synchronization technology, synchronize all critical system clocks and times § 10. 5 Secure audit trails so they cannot be altered. § 10. 6 Review logs for all system components at least daily. § 10. 7 Retain audit trail history for at least one year, with a minimum of three months immediately available for analysis.
GLBA / FFIEC Data Security LOG TRANSMISSION, NORMALIZATION, STORAGE, AND PROTECTION § Network and host activities typically are recorded on the host and sent across the network to a central logging facility. § The logging facility may process the logging data into a common format. That process is called normalization. Normalized data frequently enables timely and effective log analysis.
HIPAA / HITECH Act 3. LOG-IN MONITORING (A) - § 164. 308(a)(5)(ii)© § …the covered entity must implement: “Procedures for monitoring log-in attempts and reporting discrepancies. ” 4. Access controls - § 164. 312(b) § (b) Standard: Audit controls. Implement hardware, software, and/or procedural mechanisms that record and examine activity in information systems that contain or use electronic protected health information.
Why we do log collection and monitoring Active Monitoring – Catch the cybercriminals early Forensics – I’ve had a breach, how do I fix that?
Active Monitoring Stop a Data Breach Before it Happens. § 1, 093 breaches in 2016 § 40% increase over 2015, an all time high § Billions records lost since 2005 § Less than 1% of the breaches were discovered through log analysis § 69% of these breaches were detectible via log evidence Take Away: If you are monitoring your logs, you can detect a breach and stop it before data is lost.
Forensics How did it happen, how do I clean it up? § What servers are infected? § How many are infected? § Where did it start? § How does the malware actually work? § How do I clean it up? If you do not have logs you can’t answer these questions and you are almost certain to become re-infected with malware
System Log Collection and Monitoring Core Principles § Centralize log collection from ALL servers, devices and PCs § Real time collection § Event correlation for pattern recognition § Real time monitoring and alerting § Historical archives forensics § Query and reporting services
The State of Logging on the IBM i § The state of logging on most IBM i’s is not good - There is a ton(!) of valuable information stored on your IBM i - The IBM i logs are in proprietary format - IBM i security logs are often an enclave inside the IT organization - No standardized syslog communications facility § The essence of good security is externalizing the logs § There is a requirement to remove the risk of tampering § Compliance regulations recognize the need to watch all users – including the most powerful users
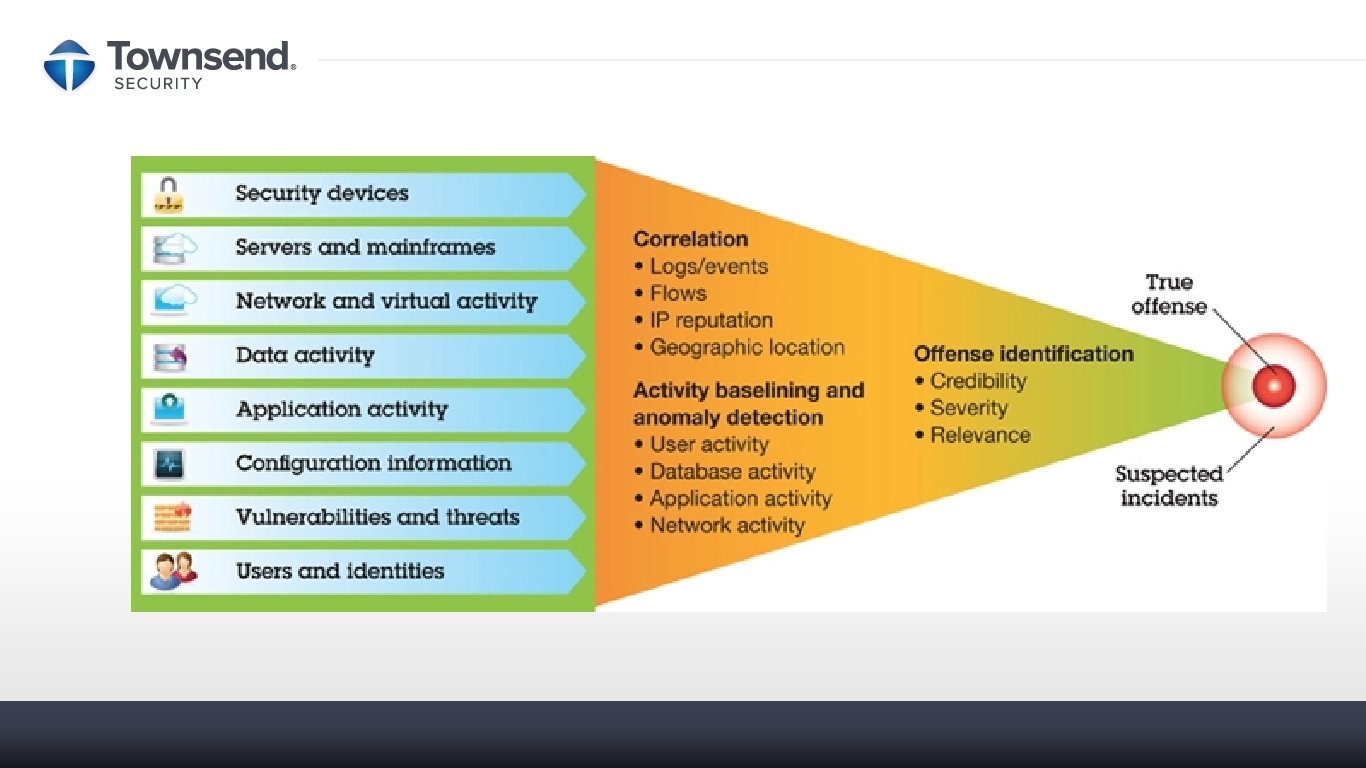
How to collect and monitor system logs? The high volume of events from the IBM i and all other devices, servers, and PCs makes human monitoring IMPOSSIBLE. Organizations of all sizes turn to Security Information and Event Management (SIEM) solutions to solve the problem. Smart SIEM software can handle the log collection and monitoring much better than us humans.
An example: A large global bank headquartered in the UK deploys 30+ IBM i servers and on average for each IBM i server: • Generates 25+ million entries in QAUDJRN every day • Generates 5 million QHST records every day • Generates multiple QHST files every day This was just the IBM i infrastructure and does not reflect the many other platforms deployed across the Enterprise.
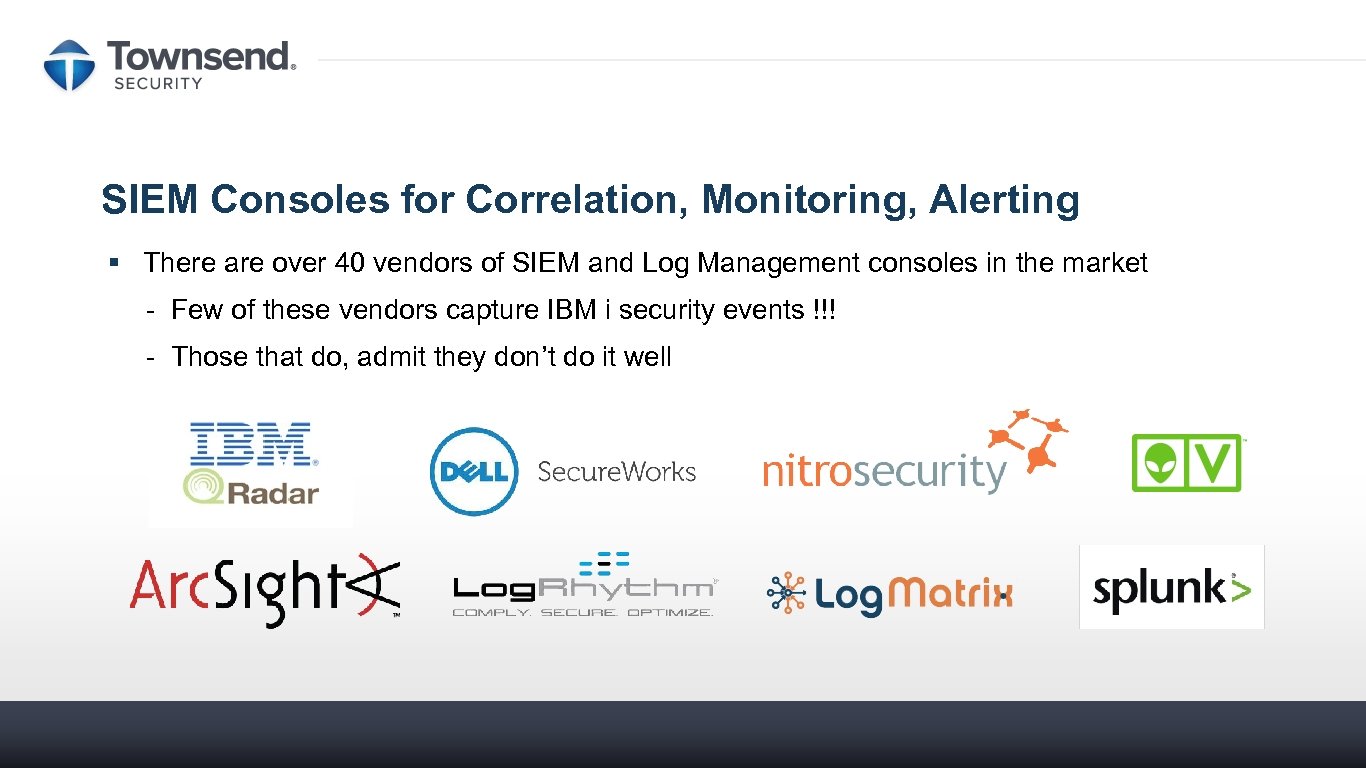
SIEM Consoles for Correlation, Monitoring, Alerting § There are over 40 vendors of SIEM and Log Management consoles in the market - Few of these vendors capture IBM i security events !!! - Those that do, admit they don’t do it well
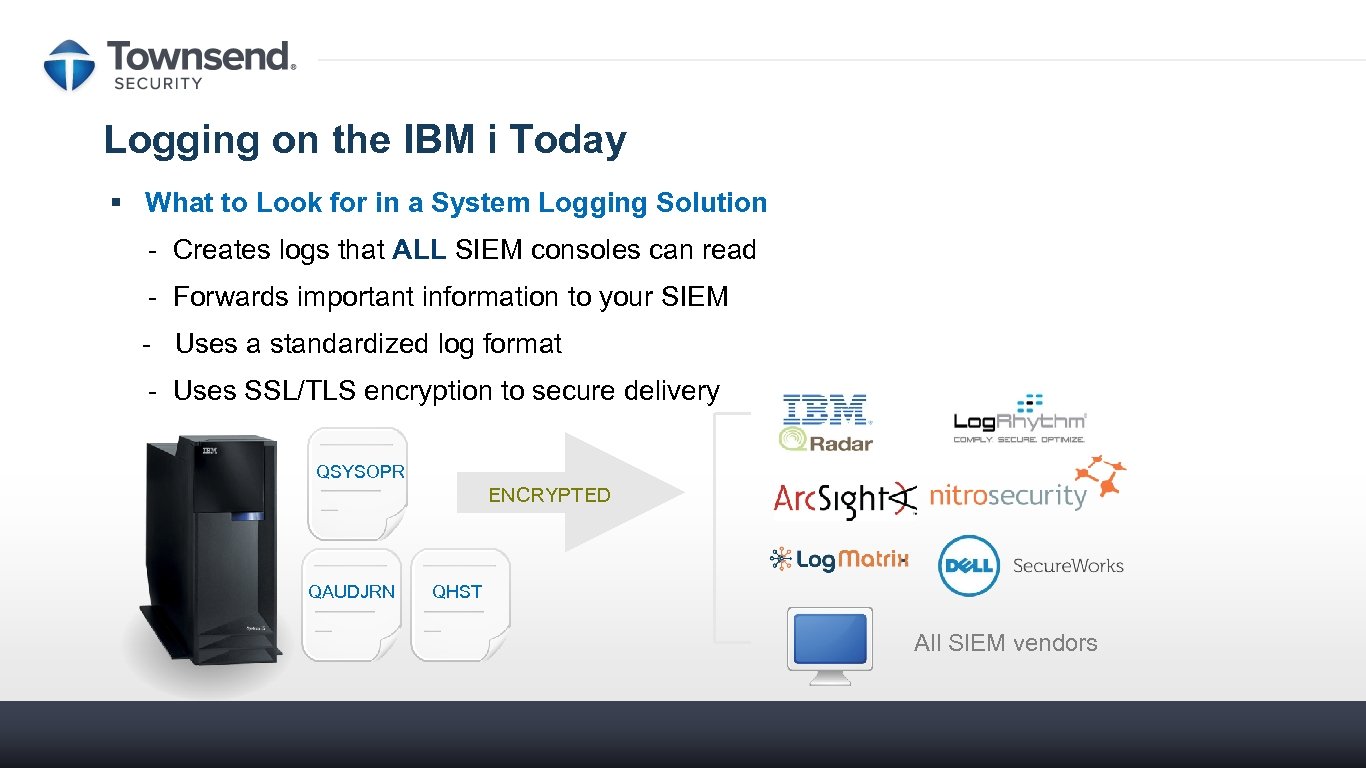
Logging on the IBM i Today § What to Look for in a System Logging Solution - Creates logs that ALL SIEM consoles can read - Forwards important information to your SIEM - Uses a standardized log format - Uses SSL/TLS encryption to secure delivery QSYSOPR ENCRYPTED QAUDJRN QHST All SIEM vendors
IBM i Log Sources and Collection There are many and disparate sources of logging information: § IBM Security Audit Journal QAUDJRN § System history message file QHST § System operator message queue (QSYSOPR, QSYSMSG) § IBM exit points (SQL, Telnet, FTP, RCMD, and many more) § Linux/Unix style logs (Apache, Open. SSH, Websphere, Perl, PHP, etc. ) § DB 2 row and column access § User and ISV applications
IBM Adds New Journal Entry Types with OS release IBM creates over 80 journal entry types in the Security Audit Journal (QAUDJRN) § With ‘sub-types’ the number swells to over 800 record formats. § ISV’s are adding their own journal entry types all the time.
The Three standard formats for log information § Syslog format (RFC-3164 and RFC-5424) § Common Event Format (CEF) – from Arc. Sight § Log Event Extended Format (LEEF) – from IBM QRadar
![SYSLOG (raw) Dec 16 01: 21: 08 debian kernel: [ 9. 832215] lp: driver SYSLOG (raw) Dec 16 01: 21: 08 debian kernel: [ 9. 832215] lp: driver](https://present5.com/presentation/8c58081f008b3144bd6f2492bfb5c1d5/image-21.jpg)
SYSLOG (raw) Dec 16 01: 21: 08 debian kernel: [ 9. 832215] lp: driver loaded but no devices found mingus sshd[2260]: Failed password for illegal user from 219. 117. 251. 250 port 44741 ssh 2
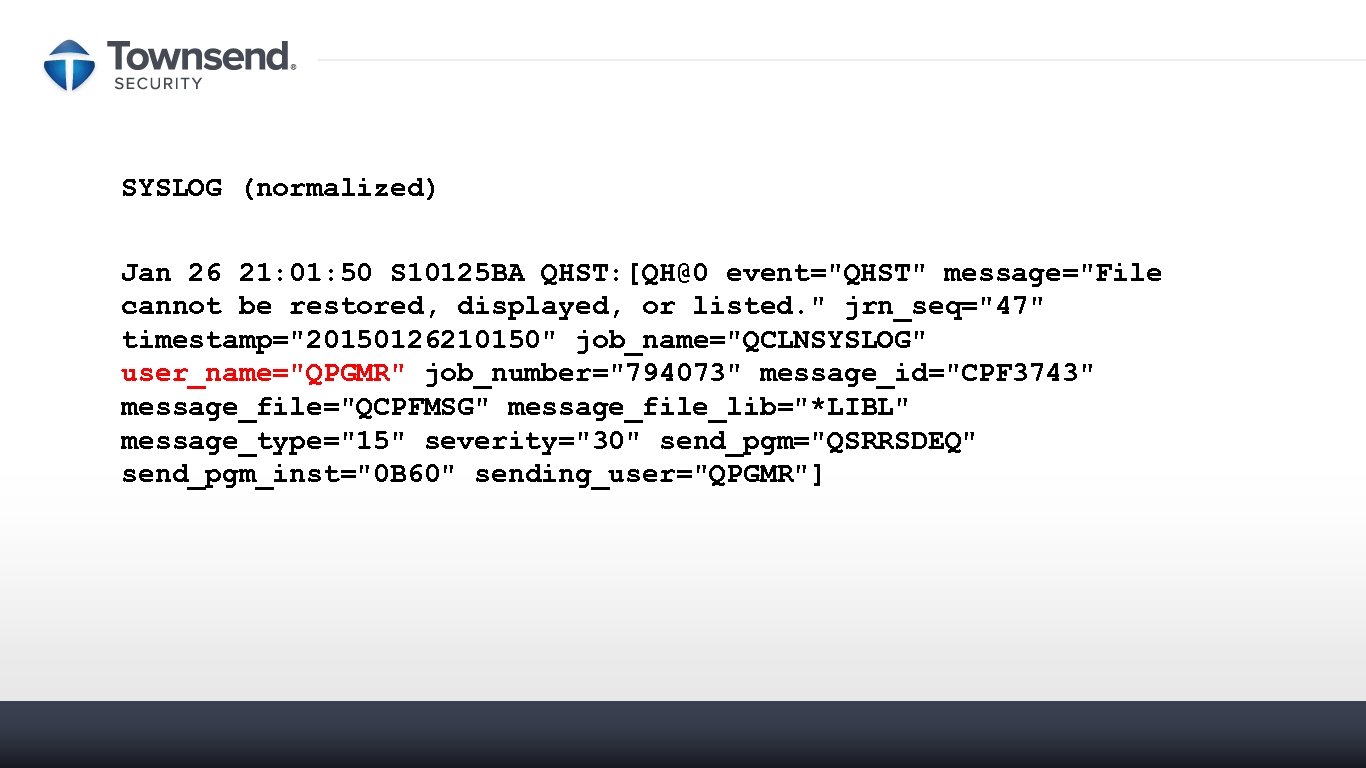
SYSLOG (normalized) Jan 26 21: 01: 50 S 10125 BA QHST: [QH@0 event="QHST" message="File cannot be restored, displayed, or listed. " jrn_seq="47" timestamp="20150126210150" job_name="QCLNSYSLOG" user_name="QPGMR" job_number="794073" message_id="CPF 3743" message_file="QCPFMSG" message_file_lib="*LIBL" message_type="15" severity="30" send_pgm="QSRRSDEQ" send_pgm_inst="0 B 60" sending_user="QPGMR"]
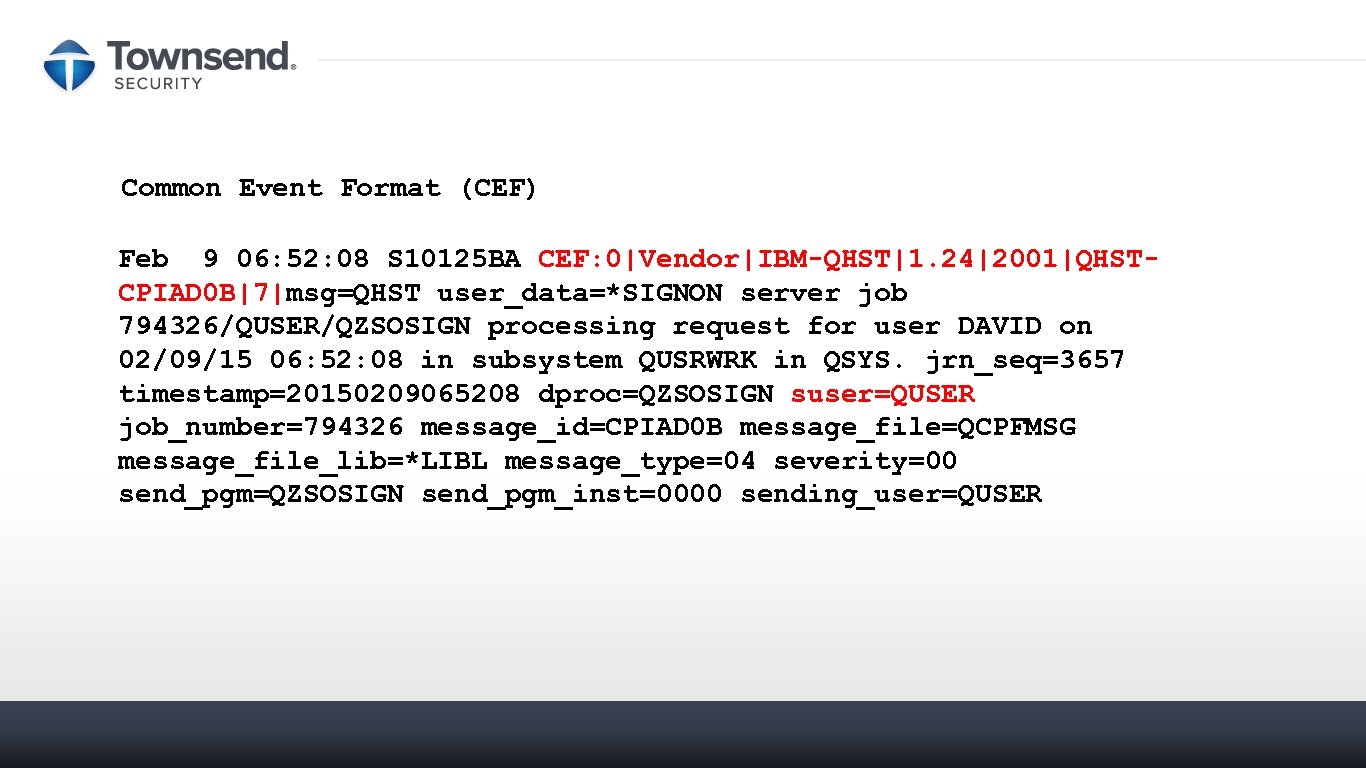
Common Event Format (CEF) Feb 9 06: 52: 08 S 10125 BA CEF: 0|Vendor|IBM-QHST|1. 24|2001|QHSTCPIAD 0 B|7|msg=QHST user_data=*SIGNON server job 794326/QUSER/QZSOSIGN processing request for user DAVID on 02/09/15 06: 52: 08 in subsystem QUSRWRK in QSYS. jrn_seq=3657 timestamp=20150209065208 dproc=QZSOSIGN suser=QUSER job_number=794326 message_id=CPIAD 0 B message_file=QCPFMSG message_file_lib=*LIBL message_type=04 severity=00 send_pgm=QZSOSIGN send_pgm_inst=0000 sending_user=QUSER
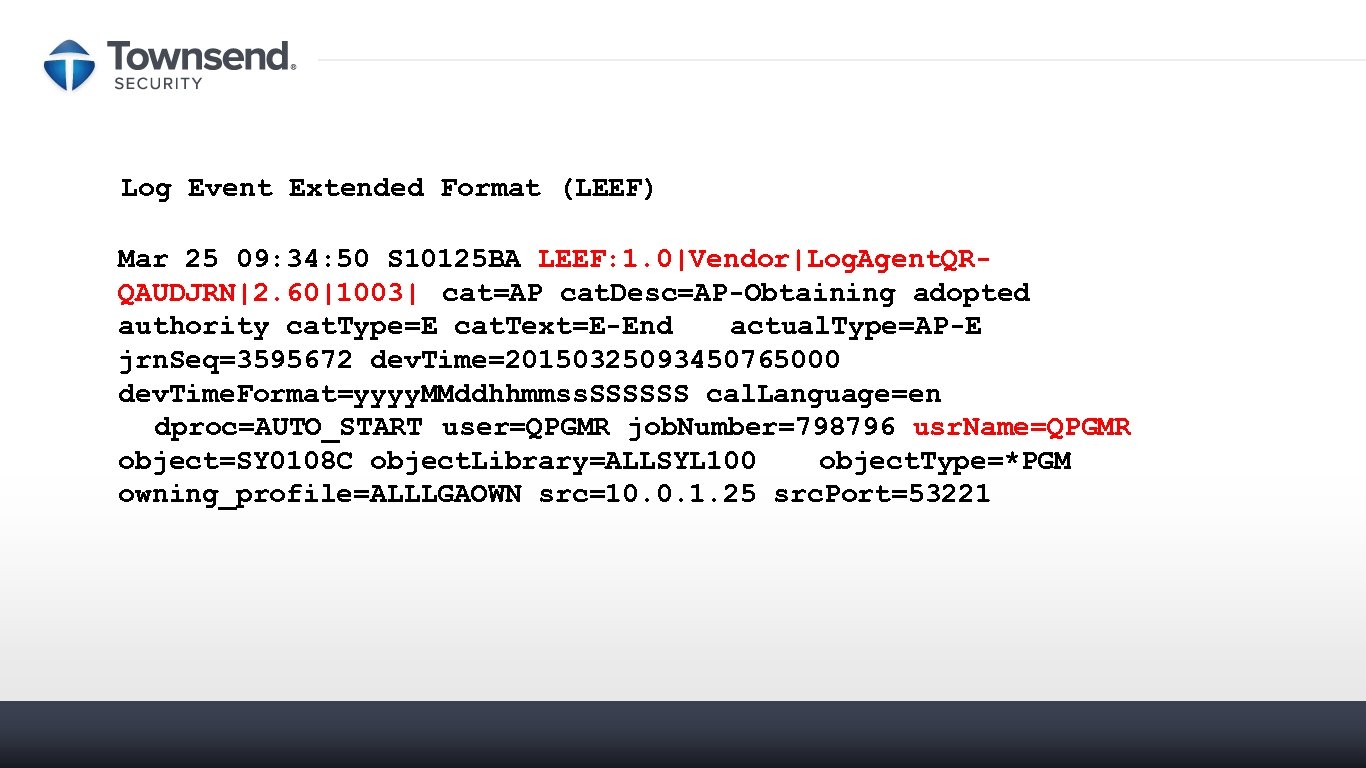
Log Event Extended Format (LEEF) Mar 25 09: 34: 50 S 10125 BA LEEF: 1. 0|Vendor|Log. Agent. QRQAUDJRN|2. 60|1003| cat=AP cat. Desc=AP-Obtaining adopted authority cat. Type=E cat. Text=E-End actual. Type=AP-E jrn. Seq=3595672 dev. Time=20150325093450765000 dev. Time. Format=yyyy. MMddhhmmss. SSSSSS cal. Language=en dproc=AUTO_START user=QPGMR job. Number=798796 usr. Name=QPGMR object=SY 0108 C object. Library=ALLSYL 100 object. Type=*PGM owning_profile=ALLLGAOWN src=10. 0. 1. 25 src. Port=53221
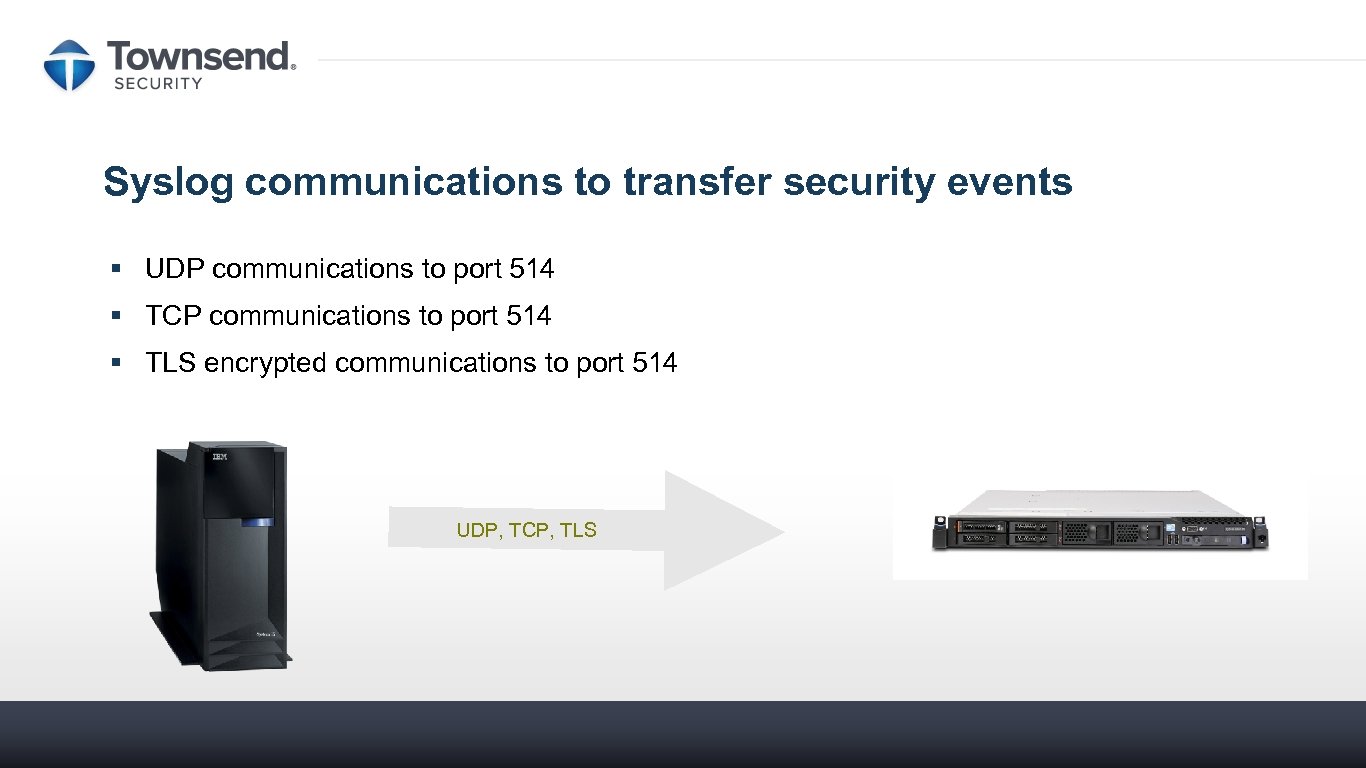
Syslog communications to transfer security events § UDP communications to port 514 § TCP communications to port 514 § TLS encrypted communications to port 514 UDP, TCP, TLS
LAMP Style Logging on the IBM i LAMP (Linux, Apache, My. SQL, and PHP, Perl, or Python) logs are different than traditional IBM i logs § Logging is under application control, not system control. § LAMP logs are not generally forwarded from the IBM i because they are different.
File Integrity Monitoring (FIM) Monitor changes to application configuration files and sensitive data § Monitor changes to any sensitive data in any DB 2 file § Monitor system and application configuration changes § User and application white lists with security exceptions § High and Low limit notifications for numeric fields § Immediate transfer of security events to SIEM or Log Collection server
What to Look for in a FIM Solution Security and File Integrity Monitoring § A complete solution that can capture and forward all IBM i security events § Monitoring of field-level changes § Selectively monitor data access without changing applications or user accounts § Built for SIEM integration § Robust filtering capability to minimize network impact § Strong encryption between IBM i and SIEM console § Integration built on industry standard log formats
What About Performance? § High performance event collection from QAUDJRN, QSYSOPR, QHST § Thousands of events per second § Millions of events per day § Event filter options (event, user, etc. ) § Buffered and metered transmission § Simultaneous collection from multiple sources
Step 1: Don’t PANIC !!! What to do right now § Start collecting IBM i logs forensics § Install Syslog-NG (open source) on a Linux or Windows server § Install a QAUDJRN collector (buy one or cobble one together) § Start sending those logs! § Use FTP if you have to § Configure your firewall, switches and IDS/IPS to log to the server § Configure user PCs for logging § Configure web, application, and database servers for logging Congratulations !!! You’ve taken a big step forward !!!
Step 2: Evaluate and deploy a SIEM § Assess the value of your data assets § More valuable, more investment in SIEM § Assess your risk § Assess your appetite for loss § Cost / Benefit analysis comes into this § Review features § Some SIEMs better with complex networks § Some SIEMs better with business data § Some SIEMs handle high volumes of data better § Try before you buy !!!
SIEM affordability is improving § Alien. Vault OSSIM – open source § Microsoft OMS – requires adapters, Azure based § IBM Security QRadar on Soft. Layer § Splunk on Amazon Web Services (AWS) – this is new
Looking into the Crystal Ball § Artificial Intelligence (Cognitive Computing) will play a bigger role § SIEMs are getting upgrades (IBM leading the way) § Threat Intelligence will play a bigger role § IBM X-Force is one example § Alien. Vault Open Threat Exchange (OTX)
Looking into the Crystal Ball § Blockchain § Log source § Event immutability
Cyber Insurance – Why you need it (It’s not why you think) The right cyber insurance policy will come with access to a legal and forensics team that you can use in the event of a breach. The benefits include: • Pre-allocated legal and cyber forensics professionals • Legally enforced privacy • Lower cost for services
Summary § Logging is a now compliance mandate § Externalizing logs from the IBM i can be difficult § A system logging solution can easily capture and forward logs to your favorite SIEM console
Any Questions About System Logging for Security ? Contact Patrick Townsend patrick. townsend@townsendsecurity. com www. townsendsecurity. com 800. 357. 1019 www. townsendsecurity. com
8c58081f008b3144bd6f2492bfb5c1d5.ppt