4c684cbbc09ecc28384e3839612da0c7.ppt
- Количество слайдов: 26
 22 – Integrity, Firewalls 8: Network Security 8 -1
22 – Integrity, Firewalls 8: Network Security 8 -1
 Chapter 8 Network Security A note on the use of these ppt slides: We’re making these slides freely available to all (faculty, students, readers). They’re in Power. Point form so you can add, modify, and delete slides (including this one) and slide content to suit your needs. They obviously represent a lot of work on our part. In return for use, we only ask the following: q If you use these slides (e. g. , in a class) in substantially unaltered form, that you mention their source (after all, we’d like people to use our book!) q If you post any slides in substantially unaltered form on a www site, that you note that they are adapted from (or perhaps identical to) our slides, and note our copyright of this material. Thanks and enjoy! JFK/KWR All material copyright 1996 -2004 J. F Kurose and K. W. Ross, All Rights Reserved Computer Networking: A Top Down Approach Featuring the Internet, 3 rd edition. Jim Kurose, Keith Ross Addison-Wesley, July 2004. 8: Network Security 8 -2
Chapter 8 Network Security A note on the use of these ppt slides: We’re making these slides freely available to all (faculty, students, readers). They’re in Power. Point form so you can add, modify, and delete slides (including this one) and slide content to suit your needs. They obviously represent a lot of work on our part. In return for use, we only ask the following: q If you use these slides (e. g. , in a class) in substantially unaltered form, that you mention their source (after all, we’d like people to use our book!) q If you post any slides in substantially unaltered form on a www site, that you note that they are adapted from (or perhaps identical to) our slides, and note our copyright of this material. Thanks and enjoy! JFK/KWR All material copyright 1996 -2004 J. F Kurose and K. W. Ross, All Rights Reserved Computer Networking: A Top Down Approach Featuring the Internet, 3 rd edition. Jim Kurose, Keith Ross Addison-Wesley, July 2004. 8: Network Security 8 -2
 Digital Signatures Cryptographic technique analogous to handwritten signatures. r sender (Bob) digitally signs document, establishing he is document owner/creator. r verifiable: recipient (Alice) can prove to someone that Bob, and no one else (including Alice), must have signed document 8: Network Security 8 -3
Digital Signatures Cryptographic technique analogous to handwritten signatures. r sender (Bob) digitally signs document, establishing he is document owner/creator. r verifiable: recipient (Alice) can prove to someone that Bob, and no one else (including Alice), must have signed document 8: Network Security 8 -3
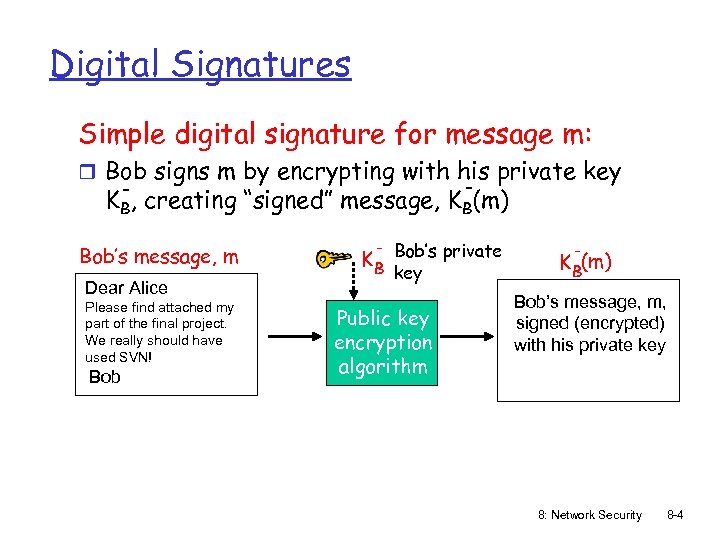 Digital Signatures Simple digital signature for message m: r Bob signs m by encrypting with his private key - KB, creating “signed” message, KB(m) Bob’s message, m Dear Alice Please find attached my part of the final project. We really should have used SVN! Bob K B Bob’s private key Public key encryption algorithm K B(m) Bob’s message, m, signed (encrypted) with his private key 8: Network Security 8 -4
Digital Signatures Simple digital signature for message m: r Bob signs m by encrypting with his private key - KB, creating “signed” message, KB(m) Bob’s message, m Dear Alice Please find attached my part of the final project. We really should have used SVN! Bob K B Bob’s private key Public key encryption algorithm K B(m) Bob’s message, m, signed (encrypted) with his private key 8: Network Security 8 -4
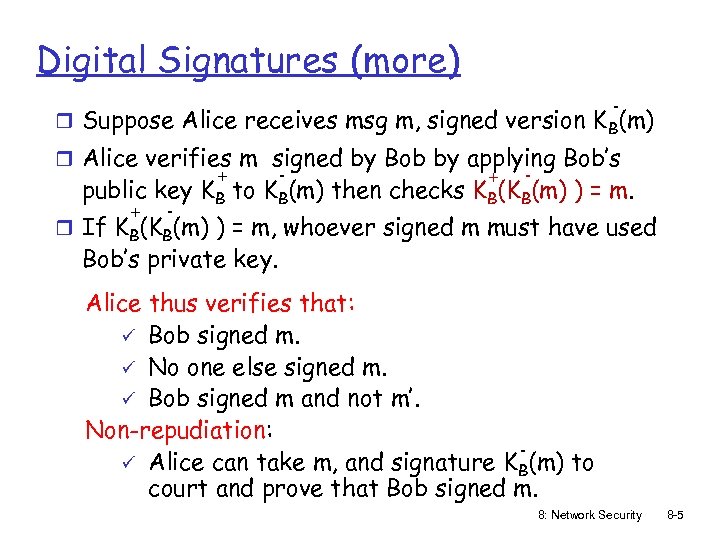 Digital Signatures (more) - r Suppose Alice receives msg m, signed version K B(m) r Alice verifies m signed by Bob by applying Bob’s + - public key KB to KB(m) then checks KB(KB(m) ) = m. + - r If KB(KB(m) ) = m, whoever signed m must have used Bob’s private key. Alice thus verifies that: ü Bob signed m. ü No one else signed m. ü Bob signed m and not m’. Non-repudiation: ü Alice can take m, and signature KB(m) to court and prove that Bob signed m. 8: Network Security 8 -5
Digital Signatures (more) - r Suppose Alice receives msg m, signed version K B(m) r Alice verifies m signed by Bob by applying Bob’s + - public key KB to KB(m) then checks KB(KB(m) ) = m. + - r If KB(KB(m) ) = m, whoever signed m must have used Bob’s private key. Alice thus verifies that: ü Bob signed m. ü No one else signed m. ü Bob signed m and not m’. Non-repudiation: ü Alice can take m, and signature KB(m) to court and prove that Bob signed m. 8: Network Security 8 -5
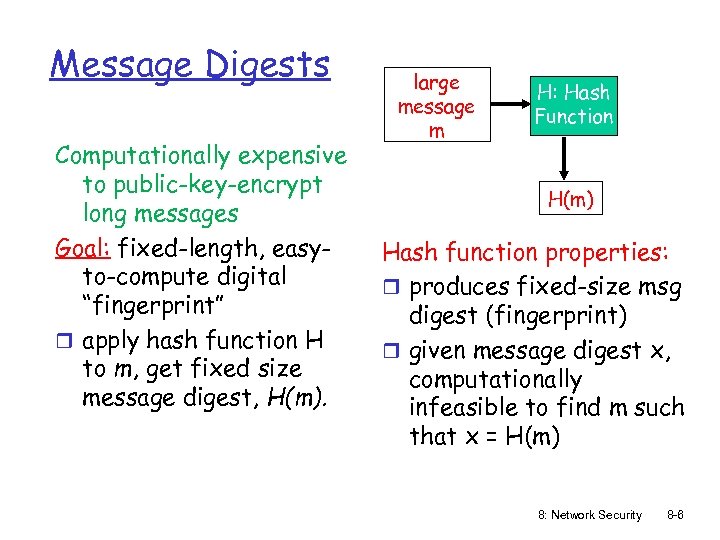 Message Digests Computationally expensive to public-key-encrypt long messages Goal: fixed-length, easyto-compute digital “fingerprint” r apply hash function H to m, get fixed size message digest, H(m). large message m H: Hash Function H(m) Hash function properties: r produces fixed-size msg digest (fingerprint) r given message digest x, computationally infeasible to find m such that x = H(m) 8: Network Security 8 -6
Message Digests Computationally expensive to public-key-encrypt long messages Goal: fixed-length, easyto-compute digital “fingerprint” r apply hash function H to m, get fixed size message digest, H(m). large message m H: Hash Function H(m) Hash function properties: r produces fixed-size msg digest (fingerprint) r given message digest x, computationally infeasible to find m such that x = H(m) 8: Network Security 8 -6
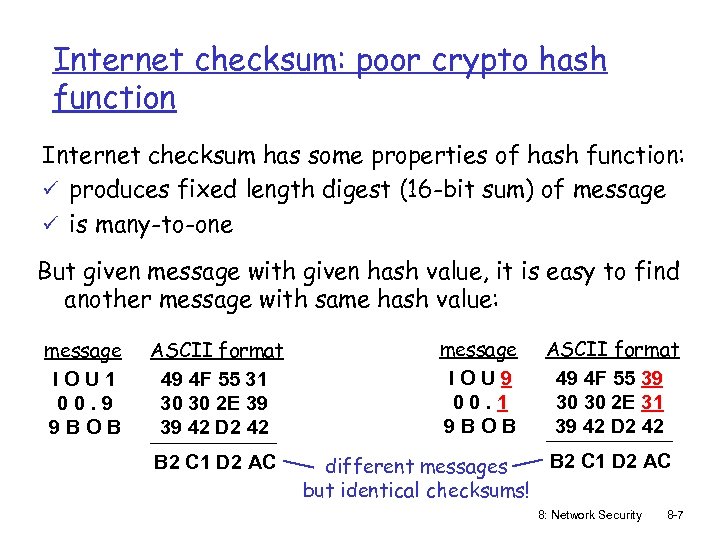 Internet checksum: poor crypto hash function Internet checksum has some properties of hash function: ü produces fixed length digest (16 -bit sum) of message ü is many-to-one But given message with given hash value, it is easy to find another message with same hash value: message IOU 1 00. 9 9 BOB ASCII format 49 4 F 55 31 30 30 2 E 39 39 42 D 2 42 B 2 C 1 D 2 AC message IOU 9 00. 1 9 BOB ASCII format 49 4 F 55 39 30 30 2 E 31 39 42 D 2 42 B 2 C 1 D 2 AC different messages but identical checksums! 8: Network Security 8 -7
Internet checksum: poor crypto hash function Internet checksum has some properties of hash function: ü produces fixed length digest (16 -bit sum) of message ü is many-to-one But given message with given hash value, it is easy to find another message with same hash value: message IOU 1 00. 9 9 BOB ASCII format 49 4 F 55 31 30 30 2 E 39 39 42 D 2 42 B 2 C 1 D 2 AC message IOU 9 00. 1 9 BOB ASCII format 49 4 F 55 39 30 30 2 E 31 39 42 D 2 42 B 2 C 1 D 2 AC different messages but identical checksums! 8: Network Security 8 -7
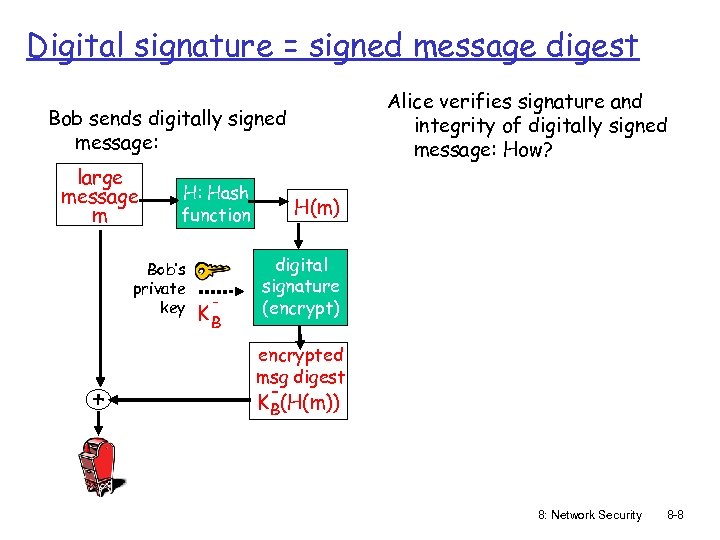 Digital signature = signed message digest Alice verifies signature and integrity of digitally signed message: How? Bob sends digitally signed message: large message m H: Hash function Bob’s private key + - KB H(m) digital signature (encrypt) encrypted msg digest KB(H(m)) 8: Network Security 8 -8
Digital signature = signed message digest Alice verifies signature and integrity of digitally signed message: How? Bob sends digitally signed message: large message m H: Hash function Bob’s private key + - KB H(m) digital signature (encrypt) encrypted msg digest KB(H(m)) 8: Network Security 8 -8
 Hash Function Algorithms r MD 5 hash function widely used (RFC 1321) m computes 128 -bit message digest in 4 -step process. m given an arbitrary 128 -bit string x, appears difficult to construct msg m whose MD 5 hash is equal to x. r SHA-1 (Secure Hash Algorithm) is also used. m US standard [NIST, FIPS PUB 180 -1] m 160 -bit message digest 8: Network Security 8 -9
Hash Function Algorithms r MD 5 hash function widely used (RFC 1321) m computes 128 -bit message digest in 4 -step process. m given an arbitrary 128 -bit string x, appears difficult to construct msg m whose MD 5 hash is equal to x. r SHA-1 (Secure Hash Algorithm) is also used. m US standard [NIST, FIPS PUB 180 -1] m 160 -bit message digest 8: Network Security 8 -9
 Trusted Intermediaries Symmetric key problem: Public key problem: r How do two entities r When Alice obtains establish shared secret key over network? Solution: r trusted key distribution center (KDC) acting as intermediary between entities Bob’s public key (from web site, e-mail, diskette), how does she know it is Bob’s public key, not Trudy’s? Solution: r trusted certification authority (CA) 8: Network Security 8 -10
Trusted Intermediaries Symmetric key problem: Public key problem: r How do two entities r When Alice obtains establish shared secret key over network? Solution: r trusted key distribution center (KDC) acting as intermediary between entities Bob’s public key (from web site, e-mail, diskette), how does she know it is Bob’s public key, not Trudy’s? Solution: r trusted certification authority (CA) 8: Network Security 8 -10
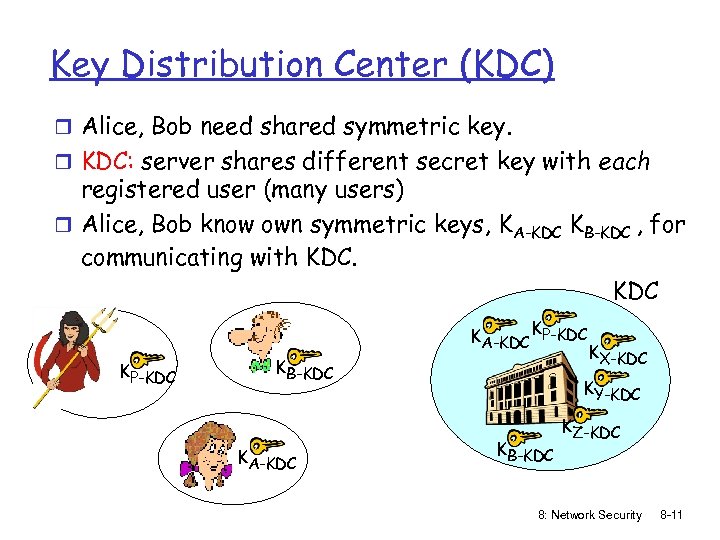 Key Distribution Center (KDC) r Alice, Bob need shared symmetric key. r KDC: server shares different secret key with each registered user (many users) r Alice, Bob know own symmetric keys, KA-KDC KB-KDC , for communicating with KDC KA-KDC KP-KDC KB-KDC KA-KDC KX-KDC KY-KDC KB-KDC KZ-KDC 8: Network Security 8 -11
Key Distribution Center (KDC) r Alice, Bob need shared symmetric key. r KDC: server shares different secret key with each registered user (many users) r Alice, Bob know own symmetric keys, KA-KDC KB-KDC , for communicating with KDC KA-KDC KP-KDC KB-KDC KA-KDC KX-KDC KY-KDC KB-KDC KZ-KDC 8: Network Security 8 -11
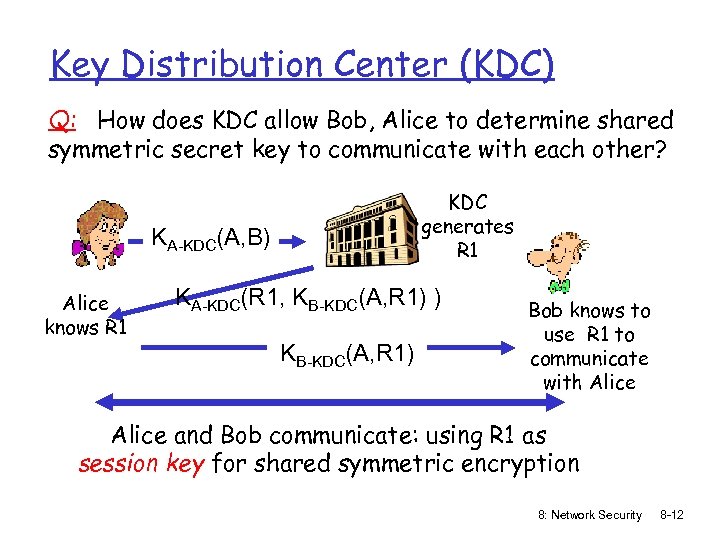 Key Distribution Center (KDC) Q: How does KDC allow Bob, Alice to determine shared symmetric secret key to communicate with each other? KDC generates R 1 KA-KDC(A, B) Alice knows R 1 KA-KDC(R 1, KB-KDC(A, R 1) ) KB-KDC(A, R 1) Bob knows to use R 1 to communicate with Alice and Bob communicate: using R 1 as session key for shared symmetric encryption 8: Network Security 8 -12
Key Distribution Center (KDC) Q: How does KDC allow Bob, Alice to determine shared symmetric secret key to communicate with each other? KDC generates R 1 KA-KDC(A, B) Alice knows R 1 KA-KDC(R 1, KB-KDC(A, R 1) ) KB-KDC(A, R 1) Bob knows to use R 1 to communicate with Alice and Bob communicate: using R 1 as session key for shared symmetric encryption 8: Network Security 8 -12
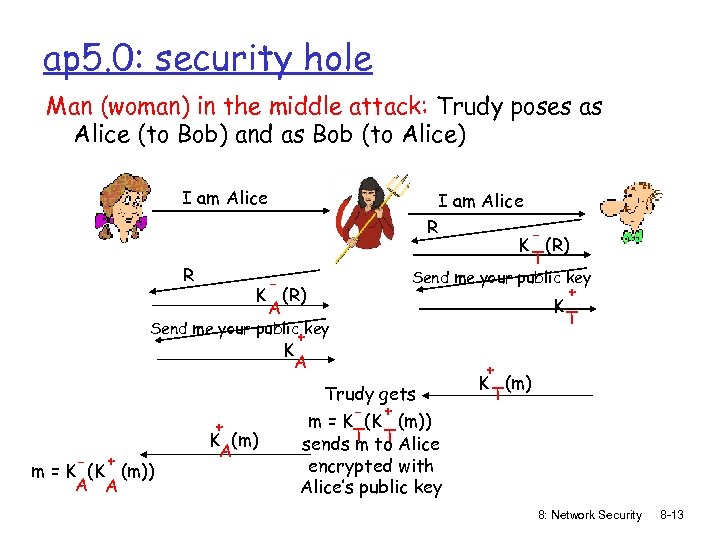 ap 5. 0: security hole Man (woman) in the middle attack: Trudy poses as Alice (to Bob) and as Bob (to Alice) I am Alice R K (R) T K (R) A Send me your public key + K T Send me your public key + K A - + m = K (K (m)) A A + K (m) A Trudy gets - + m = K (K (m)) sends T to Alice m T + K (m) T encrypted with Alice’s public key 8: Network Security 8 -13
ap 5. 0: security hole Man (woman) in the middle attack: Trudy poses as Alice (to Bob) and as Bob (to Alice) I am Alice R K (R) T K (R) A Send me your public key + K T Send me your public key + K A - + m = K (K (m)) A A + K (m) A Trudy gets - + m = K (K (m)) sends T to Alice m T + K (m) T encrypted with Alice’s public key 8: Network Security 8 -13
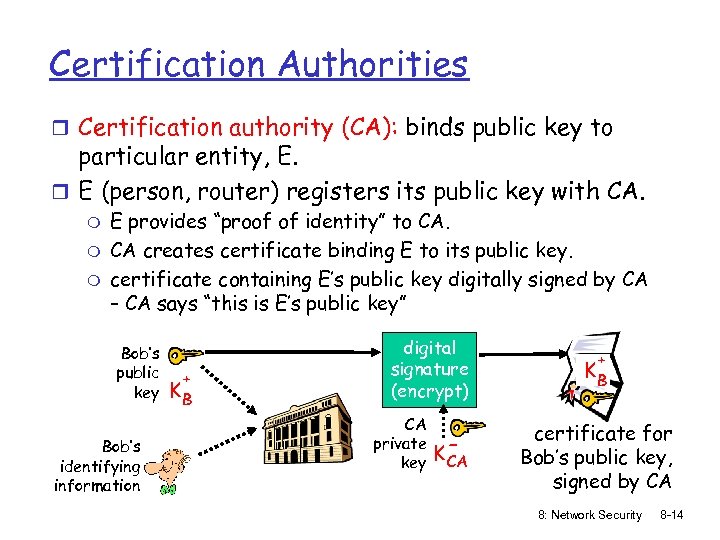 Certification Authorities r Certification authority (CA): binds public key to particular entity, E. r E (person, router) registers its public key with CA. m m m E provides “proof of identity” to CA. CA creates certificate binding E to its public key. certificate containing E’s public key digitally signed by CA – CA says “this is E’s public key” Bob’s public key Bob’s identifying information + KB digital signature (encrypt) CA private key K- CA + KB certificate for Bob’s public key, signed by CA 8: Network Security 8 -14
Certification Authorities r Certification authority (CA): binds public key to particular entity, E. r E (person, router) registers its public key with CA. m m m E provides “proof of identity” to CA. CA creates certificate binding E to its public key. certificate containing E’s public key digitally signed by CA – CA says “this is E’s public key” Bob’s public key Bob’s identifying information + KB digital signature (encrypt) CA private key K- CA + KB certificate for Bob’s public key, signed by CA 8: Network Security 8 -14
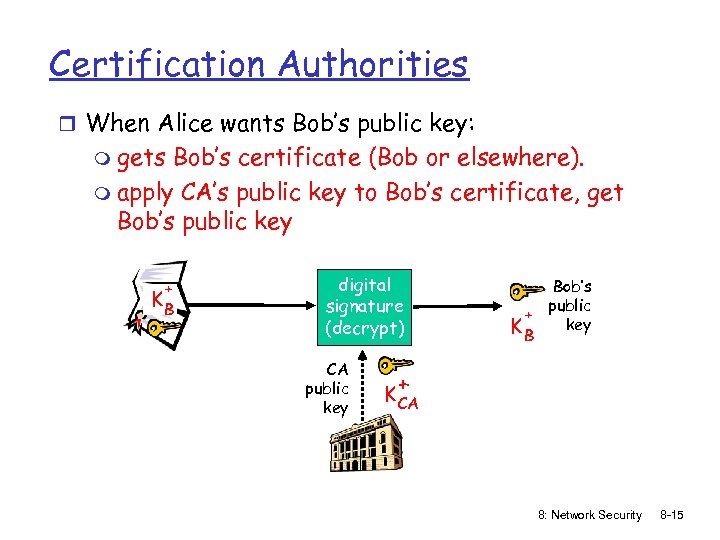 Certification Authorities r When Alice wants Bob’s public key: m gets Bob’s certificate (Bob or elsewhere). m apply CA’s public key to Bob’s certificate, get Bob’s public key + KB digital signature (decrypt) CA public key Bob’s public + key KB + K CA 8: Network Security 8 -15
Certification Authorities r When Alice wants Bob’s public key: m gets Bob’s certificate (Bob or elsewhere). m apply CA’s public key to Bob’s certificate, get Bob’s public key + KB digital signature (decrypt) CA public key Bob’s public + key KB + K CA 8: Network Security 8 -15
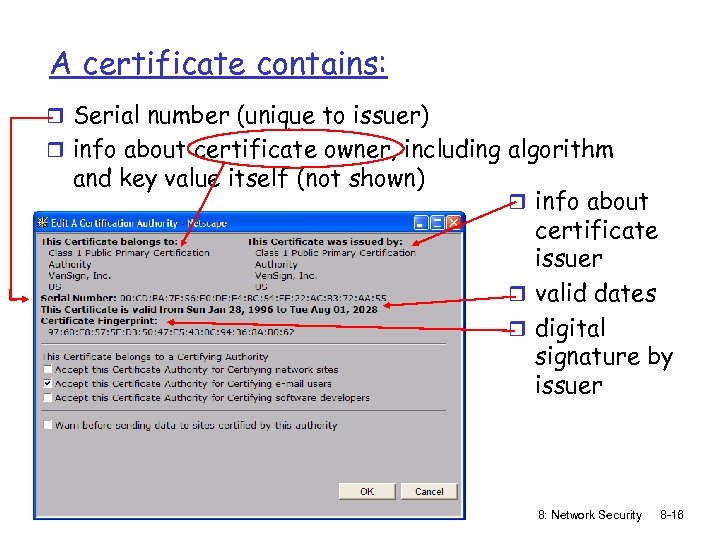 A certificate contains: r Serial number (unique to issuer) r info about certificate owner, including algorithm and key value itself (not shown) r info about certificate issuer r valid dates r digital signature by issuer 8: Network Security 8 -16
A certificate contains: r Serial number (unique to issuer) r info about certificate owner, including algorithm and key value itself (not shown) r info about certificate issuer r valid dates r digital signature by issuer 8: Network Security 8 -16
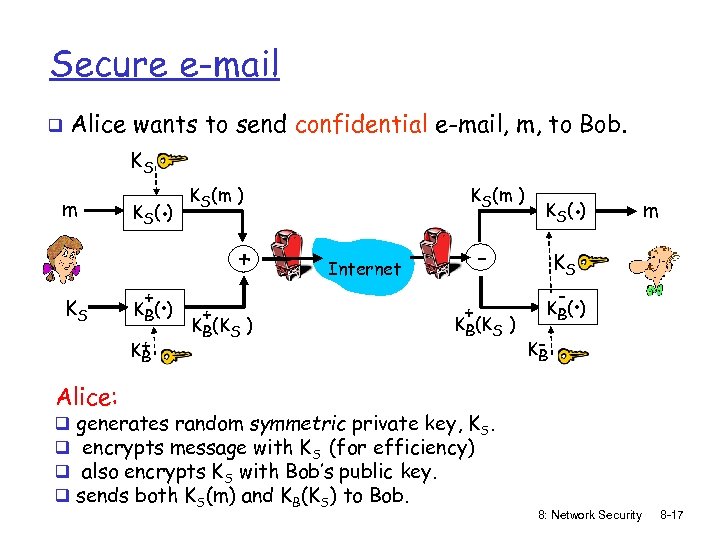 Secure e-mail q Alice wants to send confidential e-mail, m, to Bob. KS m KS K (. ) S + . K B( ) K+ B KS(m ) + + KB(KS ) . K S( ) - Internet + KB(KS ) m KS - . K B( ) KB Alice: q q generates random symmetric private key, KS. encrypts message with KS (for efficiency) also encrypts KS with Bob’s public key. sends both KS(m) and KB(KS) to Bob. 8: Network Security 8 -17
Secure e-mail q Alice wants to send confidential e-mail, m, to Bob. KS m KS K (. ) S + . K B( ) K+ B KS(m ) + + KB(KS ) . K S( ) - Internet + KB(KS ) m KS - . K B( ) KB Alice: q q generates random symmetric private key, KS. encrypts message with KS (for efficiency) also encrypts KS with Bob’s public key. sends both KS(m) and KB(KS) to Bob. 8: Network Security 8 -17
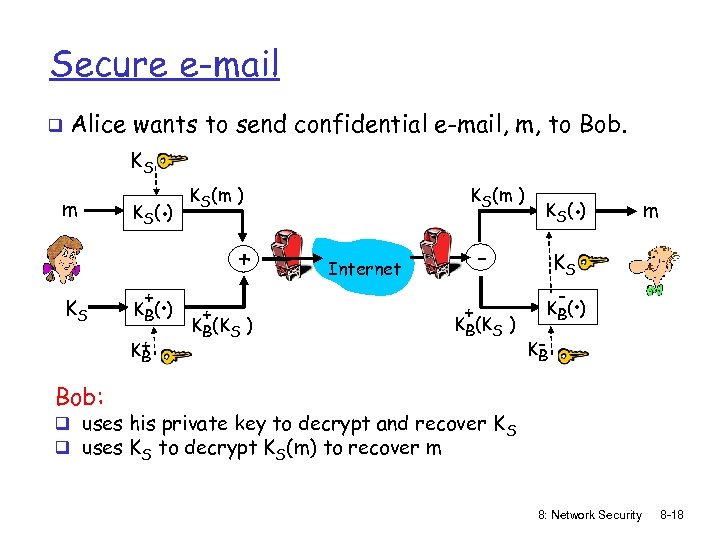 Secure e-mail q Alice wants to send confidential e-mail, m, to Bob. KS m KS K (. ) S + . K B( ) K+ B KS(m ) + + KB(KS ) . K S( ) - Internet + KB(KS ) m KS - . K B( ) KB Bob: q uses his private key to decrypt and recover K S q uses KS to decrypt KS(m) to recover m 8: Network Security 8 -18
Secure e-mail q Alice wants to send confidential e-mail, m, to Bob. KS m KS K (. ) S + . K B( ) K+ B KS(m ) + + KB(KS ) . K S( ) - Internet + KB(KS ) m KS - . K B( ) KB Bob: q uses his private key to decrypt and recover K S q uses KS to decrypt KS(m) to recover m 8: Network Security 8 -18
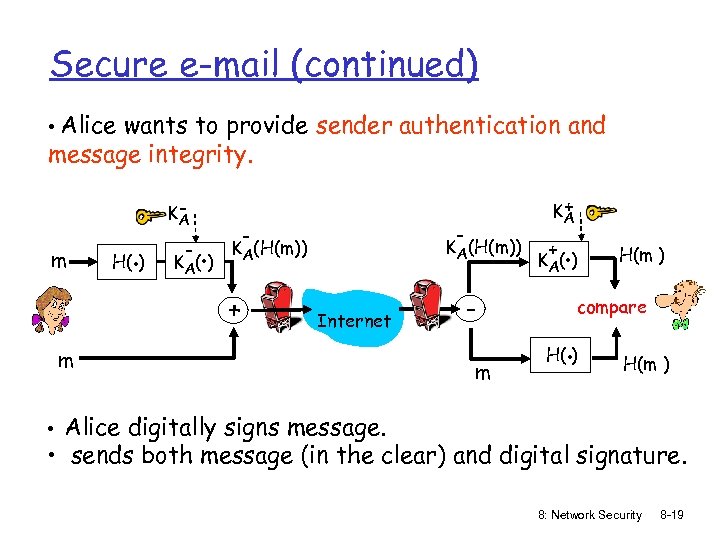 Secure e-mail (continued) • Alice wants to provide sender authentication and message integrity. m H(. ) KA - . K A( ) - - KA(H(m)) + + KA Internet m m + . K A( ) H(m ) compare . H( ) H(m ) • Alice digitally signs message. • sends both message (in the clear) and digital signature. 8: Network Security 8 -19
Secure e-mail (continued) • Alice wants to provide sender authentication and message integrity. m H(. ) KA - . K A( ) - - KA(H(m)) + + KA Internet m m + . K A( ) H(m ) compare . H( ) H(m ) • Alice digitally signs message. • sends both message (in the clear) and digital signature. 8: Network Security 8 -19
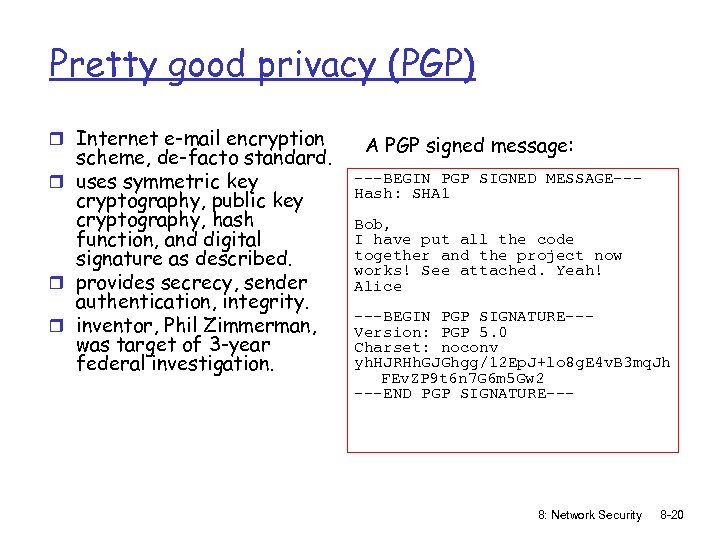 Pretty good privacy (PGP) r Internet e-mail encryption scheme, de-facto standard. r uses symmetric key cryptography, public key cryptography, hash function, and digital signature as described. r provides secrecy, sender authentication, integrity. r inventor, Phil Zimmerman, was target of 3 -year federal investigation. A PGP signed message: ---BEGIN PGP SIGNED MESSAGE--Hash: SHA 1 Bob, I have put all the code together and the project now works! See attached. Yeah! Alice ---BEGIN PGP SIGNATURE--Version: PGP 5. 0 Charset: noconv yh. HJRHh. GJGhgg/12 Ep. J+lo 8 g. E 4 v. B 3 mq. Jh FEv. ZP 9 t 6 n 7 G 6 m 5 Gw 2 ---END PGP SIGNATURE--- 8: Network Security 8 -20
Pretty good privacy (PGP) r Internet e-mail encryption scheme, de-facto standard. r uses symmetric key cryptography, public key cryptography, hash function, and digital signature as described. r provides secrecy, sender authentication, integrity. r inventor, Phil Zimmerman, was target of 3 -year federal investigation. A PGP signed message: ---BEGIN PGP SIGNED MESSAGE--Hash: SHA 1 Bob, I have put all the code together and the project now works! See attached. Yeah! Alice ---BEGIN PGP SIGNATURE--Version: PGP 5. 0 Charset: noconv yh. HJRHh. GJGhgg/12 Ep. J+lo 8 g. E 4 v. B 3 mq. Jh FEv. ZP 9 t 6 n 7 G 6 m 5 Gw 2 ---END PGP SIGNATURE--- 8: Network Security 8 -20
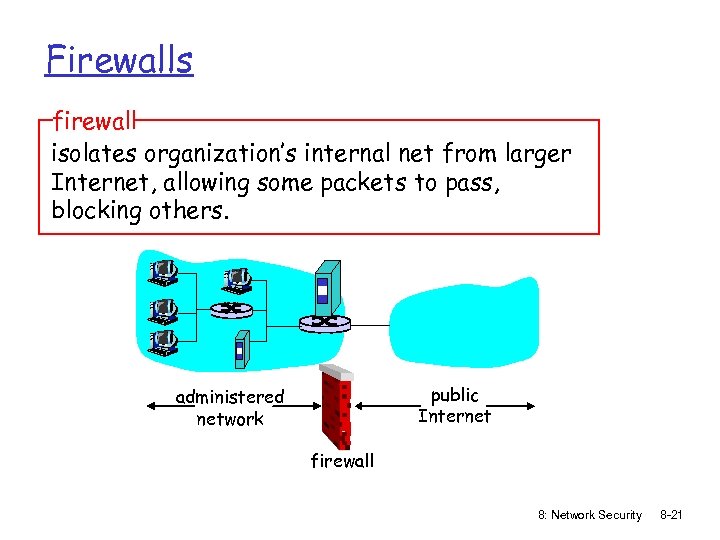 Firewalls firewall isolates organization’s internal net from larger Internet, allowing some packets to pass, blocking others. public Internet administered network firewall 8: Network Security 8 -21
Firewalls firewall isolates organization’s internal net from larger Internet, allowing some packets to pass, blocking others. public Internet administered network firewall 8: Network Security 8 -21
 Firewalls: Why prevent denial of service attacks: m SYN flooding: attacker establishes many bogus TCP connections, no resources left for “real” connections. prevent illegal modification/access of internal data. m e. g. , attacker replaces CIA’s homepage with something else allow only authorized access to inside network (set of authenticated users/hosts) two types of firewalls: m application-level m packet-filtering 8: Network Security 8 -22
Firewalls: Why prevent denial of service attacks: m SYN flooding: attacker establishes many bogus TCP connections, no resources left for “real” connections. prevent illegal modification/access of internal data. m e. g. , attacker replaces CIA’s homepage with something else allow only authorized access to inside network (set of authenticated users/hosts) two types of firewalls: m application-level m packet-filtering 8: Network Security 8 -22
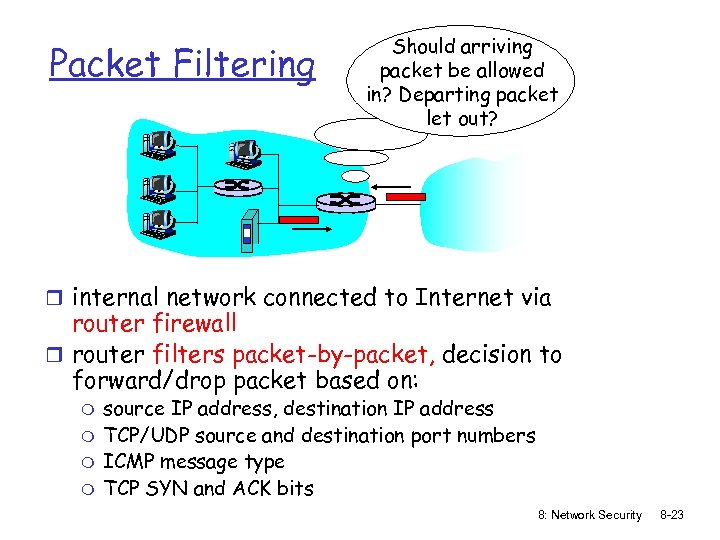 Packet Filtering Should arriving packet be allowed in? Departing packet let out? r internal network connected to Internet via router firewall r router filters packet-by-packet, decision to forward/drop packet based on: m m source IP address, destination IP address TCP/UDP source and destination port numbers ICMP message type TCP SYN and ACK bits 8: Network Security 8 -23
Packet Filtering Should arriving packet be allowed in? Departing packet let out? r internal network connected to Internet via router firewall r router filters packet-by-packet, decision to forward/drop packet based on: m m source IP address, destination IP address TCP/UDP source and destination port numbers ICMP message type TCP SYN and ACK bits 8: Network Security 8 -23
 Packet Filtering r Example 1: block incoming and outgoing datagrams with IP protocol field = 17 and with either source or dest port = 23. m All incoming and outgoing UDP flows and telnet connections are blocked. r Example 2: Block inbound TCP segments with ACK=0. m Prevents external clients from making TCP connections with internal clients, but allows internal clients to connect to outside. 8: Network Security 8 -24
Packet Filtering r Example 1: block incoming and outgoing datagrams with IP protocol field = 17 and with either source or dest port = 23. m All incoming and outgoing UDP flows and telnet connections are blocked. r Example 2: Block inbound TCP segments with ACK=0. m Prevents external clients from making TCP connections with internal clients, but allows internal clients to connect to outside. 8: Network Security 8 -24
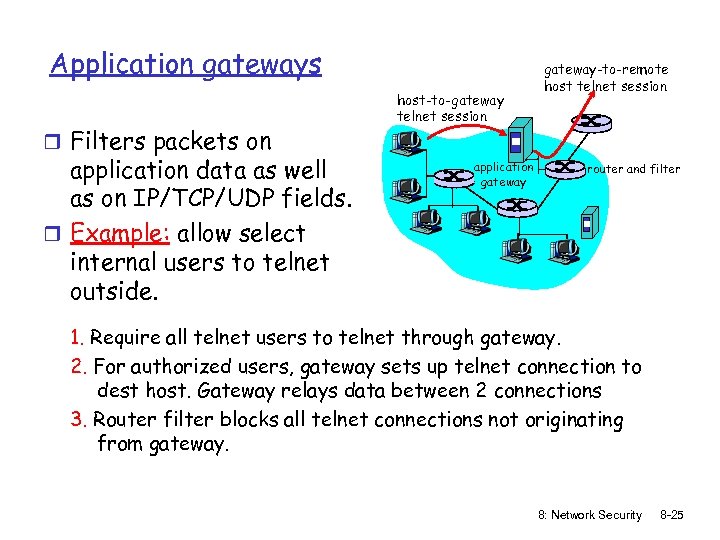 Application gateways r Filters packets on application data as well as on IP/TCP/UDP fields. r Example: allow select internal users to telnet outside. host-to-gateway telnet session application gateway-to-remote host telnet session router and filter 1. Require all telnet users to telnet through gateway. 2. For authorized users, gateway sets up telnet connection to dest host. Gateway relays data between 2 connections 3. Router filter blocks all telnet connections not originating from gateway. 8: Network Security 8 -25
Application gateways r Filters packets on application data as well as on IP/TCP/UDP fields. r Example: allow select internal users to telnet outside. host-to-gateway telnet session application gateway-to-remote host telnet session router and filter 1. Require all telnet users to telnet through gateway. 2. For authorized users, gateway sets up telnet connection to dest host. Gateway relays data between 2 connections 3. Router filter blocks all telnet connections not originating from gateway. 8: Network Security 8 -25
 Limitations of firewalls and gateways r IP spoofing: router can’t know if data “really” comes from claimed source r if multiple app’s. need special treatment, each has own app. gateway. r client software must know how to contact gateway. m e. g. , must set IP address of proxy in Web browser r filters often use all or nothing policy for UDP. r tradeoff: degree of communication with outside world, level of security r many highly protected sites still suffer from attacks. http: //darkreading. com/security/intrusionprevention/show. Article. jhtml? article. ID=217300227 8: Network Security 8 -26
Limitations of firewalls and gateways r IP spoofing: router can’t know if data “really” comes from claimed source r if multiple app’s. need special treatment, each has own app. gateway. r client software must know how to contact gateway. m e. g. , must set IP address of proxy in Web browser r filters often use all or nothing policy for UDP. r tradeoff: degree of communication with outside world, level of security r many highly protected sites still suffer from attacks. http: //darkreading. com/security/intrusionprevention/show. Article. jhtml? article. ID=217300227 8: Network Security 8 -26


