7f814ee04bbdb768ea326aa7d56c49e3.ppt
- Количество слайдов: 68
 2009 NIMS International Workshop on Mathematical Cryptology Economics of Provable Security and Probable Security Kanta Matsuura (The University of Tokyo) This work is partly supported by NEDO (New Energy and Industrial Technology Development Organization) of Japan.
2009 NIMS International Workshop on Mathematical Cryptology Economics of Provable Security and Probable Security Kanta Matsuura (The University of Tokyo) This work is partly supported by NEDO (New Energy and Industrial Technology Development Organization) of Japan.
 Abstract (1/4) n How much should we invest into information security? Can provablysecure primitives provide differences in the real world, despite the risk of implementation blunders? Can we transfer risks associated with distributed nature of security infrastructures? 2
Abstract (1/4) n How much should we invest into information security? Can provablysecure primitives provide differences in the real world, despite the risk of implementation blunders? Can we transfer risks associated with distributed nature of security infrastructures? 2
 Abstract (2/4) n Answers to these questions, or implications helpful in exploring them, may have impacts on mitigating the deployment problems of cutting-edge cryptography and information-security technologies. 3
Abstract (2/4) n Answers to these questions, or implications helpful in exploring them, may have impacts on mitigating the deployment problems of cutting-edge cryptography and information-security technologies. 3
 Abstract (3/4) n Now we have at least a decade of history in the economics of information security, this talk shows some mathematical models that provide such helpful implications. The models include an optimal investment model based on cost-benefit analysis, a two-dimensional space of information-security productivity, and a token model with option-pricing theories. 4
Abstract (3/4) n Now we have at least a decade of history in the economics of information security, this talk shows some mathematical models that provide such helpful implications. The models include an optimal investment model based on cost-benefit analysis, a two-dimensional space of information-security productivity, and a token model with option-pricing theories. 4
 Abstract (4/4) n Although the implications do not discourage engineers who investigate provable security and probable but higher security, cautions will be suggested regarding information sharing. 5
Abstract (4/4) n Although the implications do not discourage engineers who investigate provable security and probable but higher security, cautions will be suggested regarding information sharing. 5
 Agenda Economics of provable security 1. n Elementary calculus n n n Economics of probable security 2. Stochastic calculus Security efforts and their impacts Investment models Productivity space and Optimal investment Sensitivity analysis and implications n n Risks resulting from the distributed nature of information-security infrastructure Exploitation of financial derivatives for risk transfer, risk assessment, and more 6
Agenda Economics of provable security 1. n Elementary calculus n n n Economics of probable security 2. Stochastic calculus Security efforts and their impacts Investment models Productivity space and Optimal investment Sensitivity analysis and implications n n Risks resulting from the distributed nature of information-security infrastructure Exploitation of financial derivatives for risk transfer, risk assessment, and more 6
 1. Economics of Provable Security 7
1. Economics of Provable Security 7
 Security efforts and their impacts n Some countermeasures are provided so that attacks will fail. = Vulnerability reduction n Others are provided so that attacks will not occur. = Threat reduction (Research is rather sparse. ) n How the reductions influence the optimal investment strategies and relevant implications? 8
Security efforts and their impacts n Some countermeasures are provided so that attacks will fail. = Vulnerability reduction n Others are provided so that attacks will not occur. = Threat reduction (Research is rather sparse. ) n How the reductions influence the optimal investment strategies and relevant implications? 8
 Investment models n Taxonomies (e. g. , Rue et al. @WEIS 07) n Macro-economic input/output models, More traditional econometric techniques, Methods derived from financial markets, Case studies of firms, Heuristic models, Risk management & insurance framework, Game theoretic models, Accounting models. “A model is supposed to reveal the essence of what is going on: your model should be reduced to just those pieces that are required to make it work. ” (Varian 1997) “Clearer insights are provided by models that are less rather than more complex. ” (Gordon and Loeb 2002) 9
Investment models n Taxonomies (e. g. , Rue et al. @WEIS 07) n Macro-economic input/output models, More traditional econometric techniques, Methods derived from financial markets, Case studies of firms, Heuristic models, Risk management & insurance framework, Game theoretic models, Accounting models. “A model is supposed to reveal the essence of what is going on: your model should be reduced to just those pieces that are required to make it work. ” (Varian 1997) “Clearer insights are provided by models that are less rather than more complex. ” (Gordon and Loeb 2002) 9
 The Gordon-Loeb model n Basic theory (Gordon and Loeb 2002) n n Empirical supports n n n Investigation considering Return-on-Investment in a one-period economic model. The optimal investment strategy of focusing on mid-range vulnerabilities (Tanaka et al. 2005). A class of security function (Liu et al. 2007). Extensive formulation n A model for information sharing and free-rider problem (Gordon et al. 2003). 10
The Gordon-Loeb model n Basic theory (Gordon and Loeb 2002) n n Empirical supports n n n Investigation considering Return-on-Investment in a one-period economic model. The optimal investment strategy of focusing on mid-range vulnerabilities (Tanaka et al. 2005). A class of security function (Liu et al. 2007). Extensive formulation n A model for information sharing and free-rider problem (Gordon et al. 2003). 10
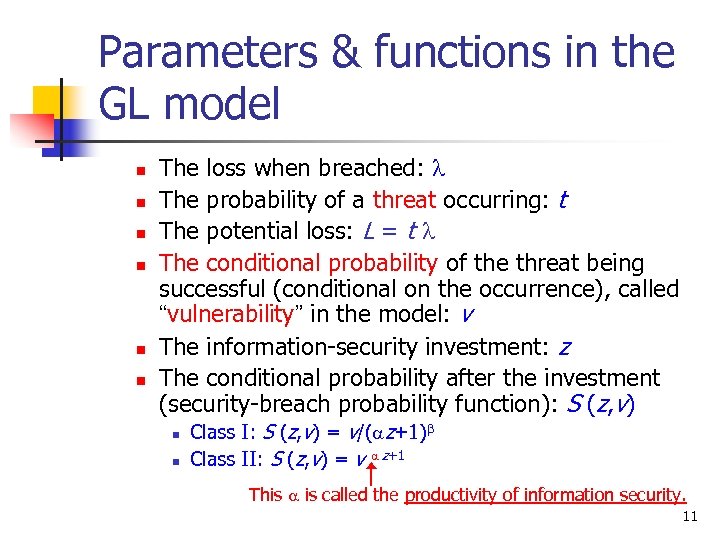 Parameters & functions in the GL model n n n The loss when breached: l The probability of a threat occurring: t The potential loss: L = t l The conditional probability of the threat being successful (conditional on the occurrence), called “vulnerability” in the model: v The information-security investment: z The conditional probability after the investment (security-breach probability function): S (z, v) n n Class I: S (z, v) = v/(az+1)b Class II: S (z, v) = v a z+1 This a is called the productivity of information security. 11
Parameters & functions in the GL model n n n The loss when breached: l The probability of a threat occurring: t The potential loss: L = t l The conditional probability of the threat being successful (conditional on the occurrence), called “vulnerability” in the model: v The information-security investment: z The conditional probability after the investment (security-breach probability function): S (z, v) n n Class I: S (z, v) = v/(az+1)b Class II: S (z, v) = v a z+1 This a is called the productivity of information security. 11
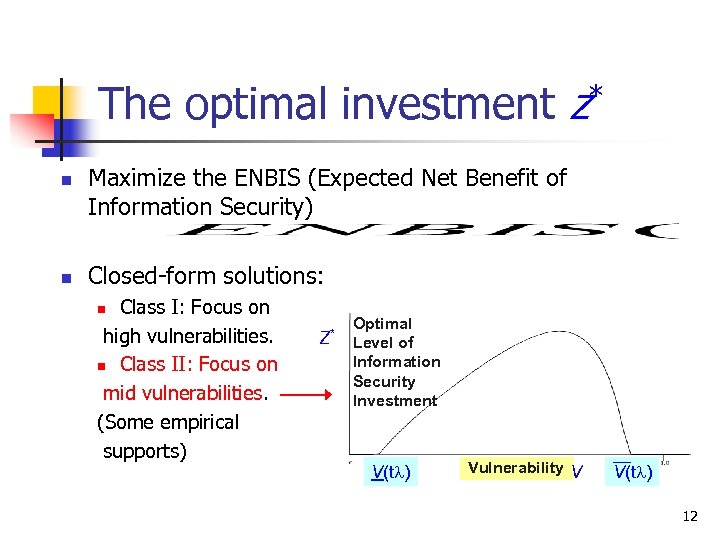 The optimal investment z* n n Maximize the ENBIS (Expected Net Benefit of Information Security) Closed-form solutions: Class I: Focus on high vulnerabilities. n Class II: Focus on mid vulnerabilities. (Some empirical supports) n Z* Optimal Level of Information Security Investment V(tl) Vulnerability V V(tl) 12
The optimal investment z* n n Maximize the ENBIS (Expected Net Benefit of Information Security) Closed-form solutions: Class I: Focus on high vulnerabilities. n Class II: Focus on mid vulnerabilities. (Some empirical supports) n Z* Optimal Level of Information Security Investment V(tl) Vulnerability V V(tl) 12
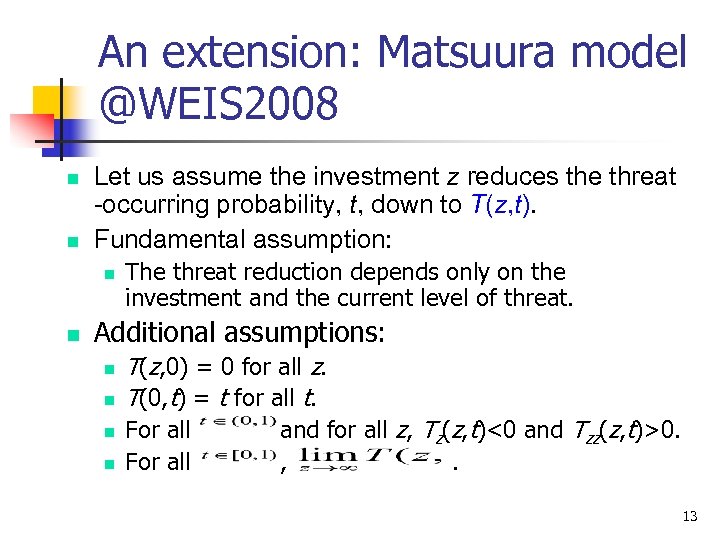 An extension: Matsuura model @WEIS 2008 n n Let us assume the investment z reduces the threat -occurring probability, t, down to T(z, t). Fundamental assumption: n n The threat reduction depends only on the investment and the current level of threat. Additional assumptions: n n T(z, 0) = 0 for all z. T(0, t) = t for all t. For all and for all z, Tz(z, t)<0 and Tzz(z, t)>0. , . 13
An extension: Matsuura model @WEIS 2008 n n Let us assume the investment z reduces the threat -occurring probability, t, down to T(z, t). Fundamental assumption: n n The threat reduction depends only on the investment and the current level of threat. Additional assumptions: n n T(z, 0) = 0 for all z. T(0, t) = t for all t. For all and for all z, Tz(z, t)<0 and Tzz(z, t)>0. , . 13
 The optimal investment z* under the risk-neutrality assumption n Determined by =B =C n Note: If the marginal benefit at z=0 is less than or equal to the marginal cost of such investment, z* equals zero. 14
The optimal investment z* under the risk-neutrality assumption n Determined by =B =C n Note: If the marginal benefit at z=0 is less than or equal to the marginal cost of such investment, z* equals zero. 14
 Risk neutrality n If someone is risk-neutral, it means that they are indifferent to investments that have the same expected value, even though the investments may have varying amounts of risk. 15
Risk neutrality n If someone is risk-neutral, it means that they are indifferent to investments that have the same expected value, even though the investments may have varying amounts of risk. 15
 Example n A risk-neutral decision-maker would be indifferent to Investment #1 that generates either a net return of $200, 000 or a net loss of $100, 000 each with probability of 0. 5, and Investment #2 that generates a net return of either $40, 000 or $60, 000 each with probability of 0. 5, as both investments have an expected net return of $50, 000. 16
Example n A risk-neutral decision-maker would be indifferent to Investment #1 that generates either a net return of $200, 000 or a net loss of $100, 000 each with probability of 0. 5, and Investment #2 that generates a net return of either $40, 000 or $60, 000 each with probability of 0. 5, as both investments have an expected net return of $50, 000. 16
 A note for the example n Notice that Investment #1 has more risk (i. e. , larger standard deviation around the expected value) than investment #2, and yet the two investments are being considered equal. 17
A note for the example n Notice that Investment #1 has more risk (i. e. , larger standard deviation around the expected value) than investment #2, and yet the two investments are being considered equal. 17
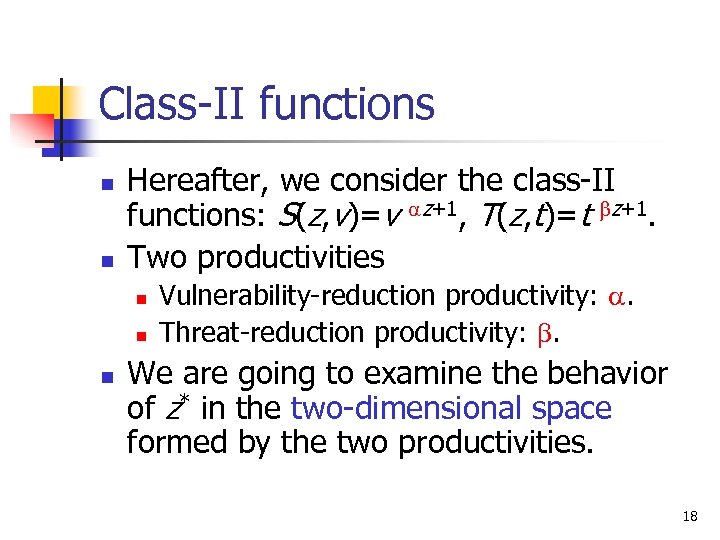 Class-II functions n n Hereafter, we consider the class-II functions: S(z, v)=v az+1, T(z, t)=t bz+1. Two productivities n n n Vulnerability-reduction productivity: a. Threat-reduction productivity: b. We are going to examine the behavior of z* in the two-dimensional space formed by the two productivities. 18
Class-II functions n n Hereafter, we consider the class-II functions: S(z, v)=v az+1, T(z, t)=t bz+1. Two productivities n n n Vulnerability-reduction productivity: a. Threat-reduction productivity: b. We are going to examine the behavior of z* in the two-dimensional space formed by the two productivities. 18
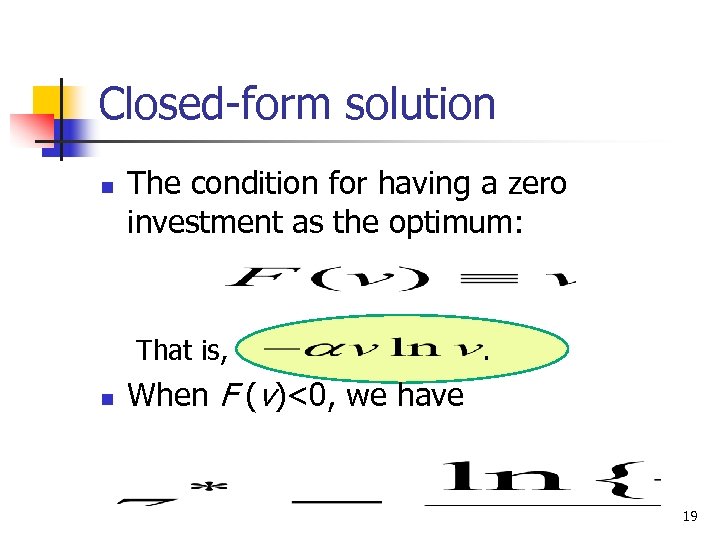 Closed-form solution n The condition for having a zero investment as the optimum: That is, n . When F (v)<0, we have 19
Closed-form solution n The condition for having a zero investment as the optimum: That is, n . When F (v)<0, we have 19
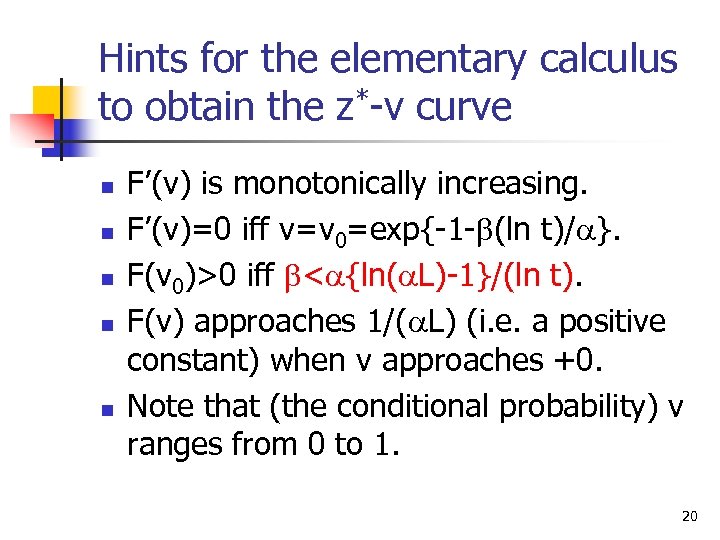 Hints for the elementary calculus to obtain the z*-v curve n n n F’(v) is monotonically increasing. F’(v)=0 iff v=v 0=exp{-1 -b(ln t)/a}. F(v 0)>0 iff b
Hints for the elementary calculus to obtain the z*-v curve n n n F’(v) is monotonically increasing. F’(v)=0 iff v=v 0=exp{-1 -b(ln t)/a}. F(v 0)>0 iff b
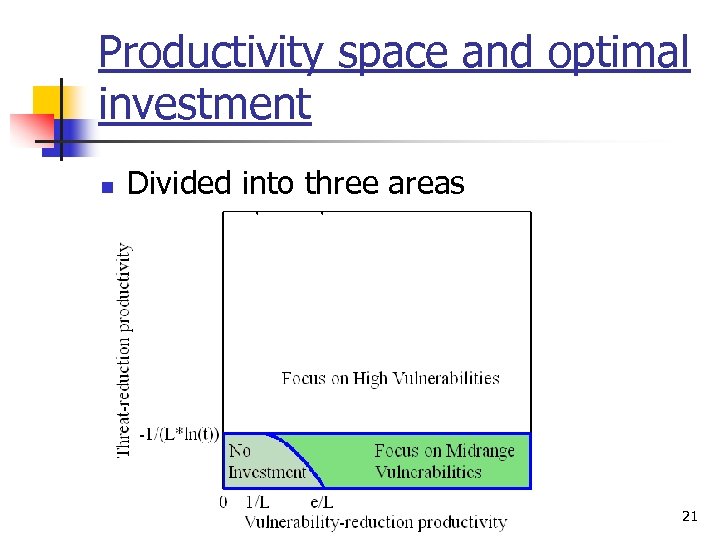 Productivity space and optimal investment n Divided into three areas 21
Productivity space and optimal investment n Divided into three areas 21
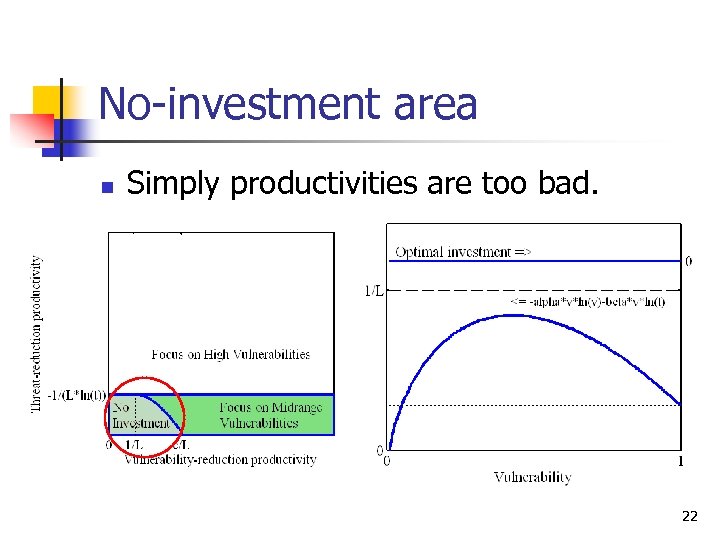 No-investment area n Simply productivities are too bad. 22
No-investment area n Simply productivities are too bad. 22
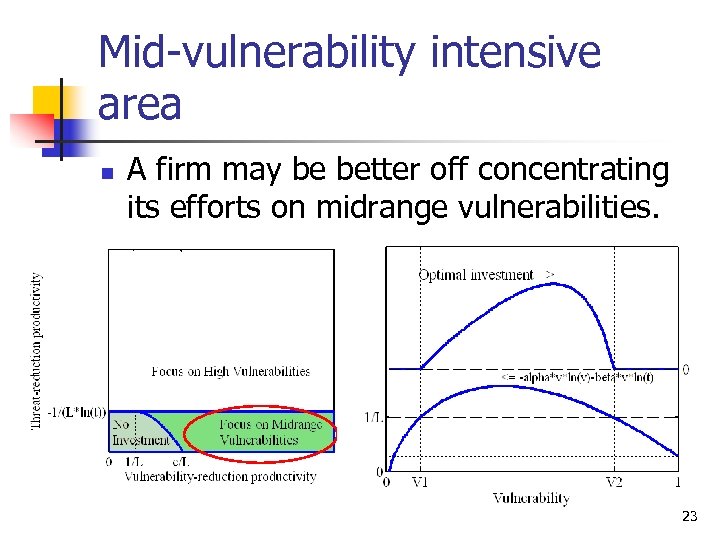 Mid-vulnerability intensive area n A firm may be better off concentrating its efforts on midrange vulnerabilities. 23
Mid-vulnerability intensive area n A firm may be better off concentrating its efforts on midrange vulnerabilities. 23
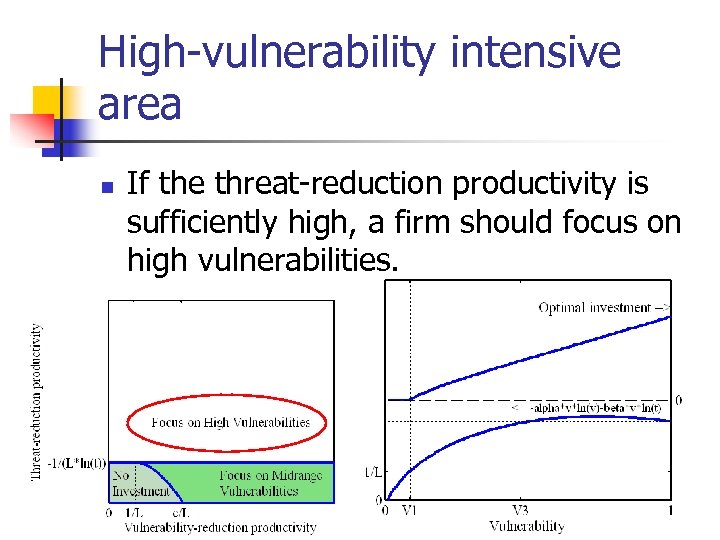 High-vulnerability intensive area n If the threat-reduction productivity is sufficiently high, a firm should focus on high vulnerabilities. 24
High-vulnerability intensive area n If the threat-reduction productivity is sufficiently high, a firm should focus on high vulnerabilities. 24
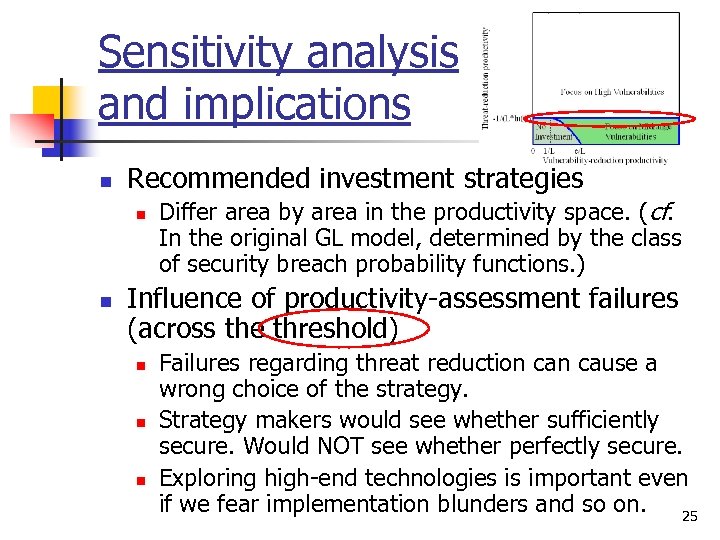 Sensitivity analysis and implications n Recommended investment strategies n n Differ area by area in the productivity space. (cf. In the original GL model, determined by the class of security breach probability functions. ) Influence of productivity-assessment failures (across the threshold) n n n Failures regarding threat reduction cause a wrong choice of the strategy. Strategy makers would see whether sufficiently secure. Would NOT see whether perfectly secure. Exploring high-end technologies is important even if we fear implementation blunders and so on. 25
Sensitivity analysis and implications n Recommended investment strategies n n Differ area by area in the productivity space. (cf. In the original GL model, determined by the class of security breach probability functions. ) Influence of productivity-assessment failures (across the threshold) n n n Failures regarding threat reduction cause a wrong choice of the strategy. Strategy makers would see whether sufficiently secure. Would NOT see whether perfectly secure. Exploring high-end technologies is important even if we fear implementation blunders and so on. 25
 Upper limit of the optimal investment n n n The optimum is always less than or equal to 36. 79% (i. e. , 1/e) of the loss that would be expected in the absence of any security investment (i. e. , vtl). Let x be – 1/{v. Lln(vatb)} (which is positive since v and t are conditional probabilities). Then z*/v. L=-x(ln x) takes its maximum value 1/e when x=1/e. 26
Upper limit of the optimal investment n n n The optimum is always less than or equal to 36. 79% (i. e. , 1/e) of the loss that would be expected in the absence of any security investment (i. e. , vtl). Let x be – 1/{v. Lln(vatb)} (which is positive since v and t are conditional probabilities). Then z*/v. L=-x(ln x) takes its maximum value 1/e when x=1/e. 26
 Sensitivity analysis n Influence of innovation n How the optimum z* would change in response to productivity improvements? If z* will be reduced, then vendors may have a negative incentive to realize the innovation. By the same elementary calculus, we have 27
Sensitivity analysis n Influence of innovation n How the optimum z* would change in response to productivity improvements? If z* will be reduced, then vendors may have a negative incentive to realize the innovation. By the same elementary calculus, we have 27
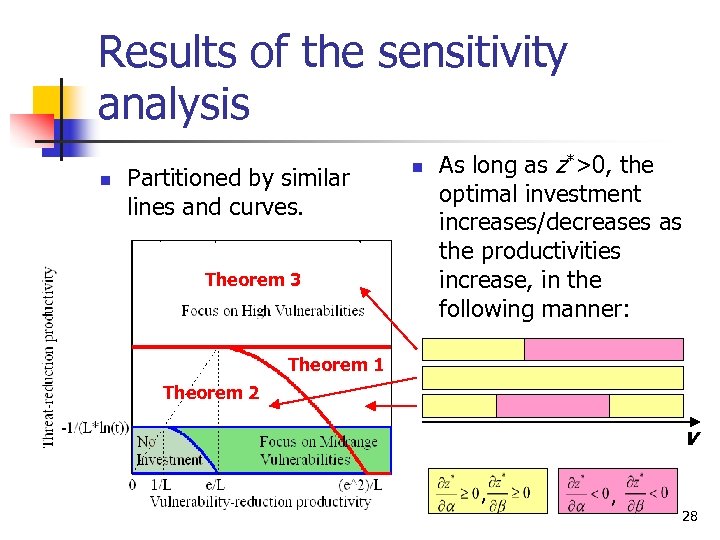 Results of the sensitivity analysis n Partitioned by similar lines and curves. Theorem 3 n As long as z*>0, the optimal investment increases/decreases as the productivities increase, in the following manner: Theorem 1 Theorem 2 v , , 28
Results of the sensitivity analysis n Partitioned by similar lines and curves. Theorem 3 n As long as z*>0, the optimal investment increases/decreases as the productivities increase, in the following manner: Theorem 1 Theorem 2 v , , 28
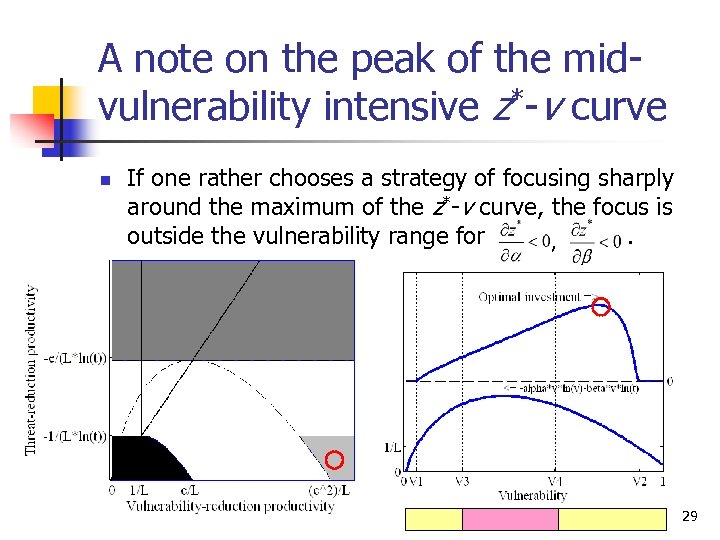 A note on the peak of the midvulnerability intensive z*-v curve n If one rather chooses a strategy of focusing sharply around the maximum of the z*-v curve, the focus is outside the vulnerability range for. , 29
A note on the peak of the midvulnerability intensive z*-v curve n If one rather chooses a strategy of focusing sharply around the maximum of the z*-v curve, the focus is outside the vulnerability range for. , 29
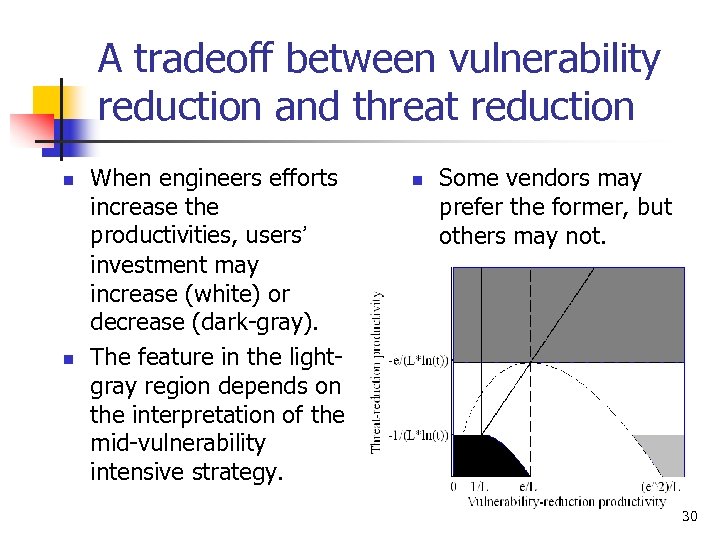 A tradeoff between vulnerability reduction and threat reduction n n When engineers efforts increase the productivities, users’ investment may increase (white) or decrease (dark-gray). The feature in the lightgray region depends on the interpretation of the mid-vulnerability intensive strategy. n Some vendors may prefer the former, but others may not. 30
A tradeoff between vulnerability reduction and threat reduction n n When engineers efforts increase the productivities, users’ investment may increase (white) or decrease (dark-gray). The feature in the lightgray region depends on the interpretation of the mid-vulnerability intensive strategy. n Some vendors may prefer the former, but others may not. 30
 Be careful about externality n watchdog Three possibilities: One’s efforts for threat reduction may have n n n No impact on threats to others. (Presented today) A positive impact on (i. e. , increase) threats to others (e. g. , attackers change their targets). A negative impact on (i. e. , decrease) threats to others (e. g. , attackers are totally discouraged). 31
Be careful about externality n watchdog Three possibilities: One’s efforts for threat reduction may have n n n No impact on threats to others. (Presented today) A positive impact on (i. e. , increase) threats to others (e. g. , attackers change their targets). A negative impact on (i. e. , decrease) threats to others (e. g. , attackers are totally discouraged). 31
 2. Economics of Probable Security 32
2. Economics of Probable Security 32
 An example: E-commerce n Protocols require frequent (and feasible but heavy) verifications. Verify, verify, . . . n Why? n n Digital certificates. Avoid copyright violation. Need freshness. Trust management. Real-time, distributed & trusted directories are too difficult. Probably OK. . . 33
An example: E-commerce n Protocols require frequent (and feasible but heavy) verifications. Verify, verify, . . . n Why? n n Digital certificates. Avoid copyright violation. Need freshness. Trust management. Real-time, distributed & trusted directories are too difficult. Probably OK. . . 33
 Associated risks n n The verification may output NG. It may output OK. Who knows in advance? Suppose a digital ticket signed by an issuer. When I buy it, I verified the signature and the result was OK. However, when I attempt to use it at a virtual theater, the verification may output NG. Or I may even face a congestion that keeps me from connection with theater, or TTP needed for verification. 34
Associated risks n n The verification may output NG. It may output OK. Who knows in advance? Suppose a digital ticket signed by an issuer. When I buy it, I verified the signature and the result was OK. However, when I attempt to use it at a virtual theater, the verification may output NG. Or I may even face a congestion that keeps me from connection with theater, or TTP needed for verification. 34
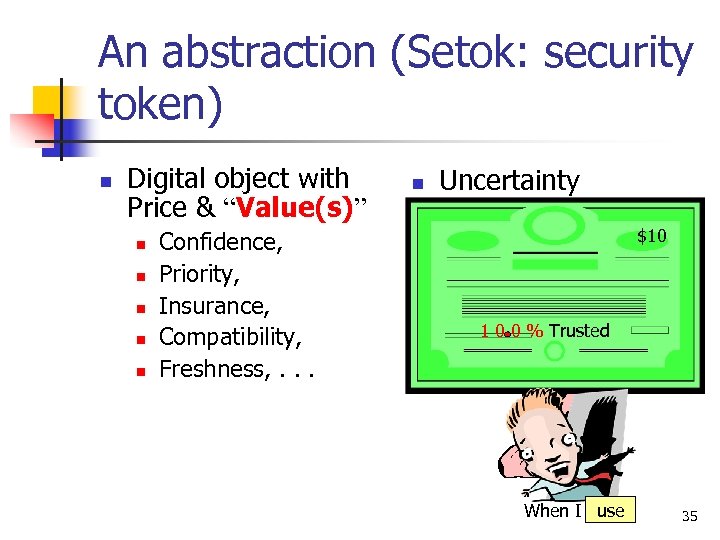 An abstraction (Setok: security token) n Digital object with Price & “Value(s)” n n n Confidence, Priority, Insurance, Compatibility, Freshness, . . . n Uncertainty $10 1 0 0 % Trusted When I buy , use 35
An abstraction (Setok: security token) n Digital object with Price & “Value(s)” n n n Confidence, Priority, Insurance, Compatibility, Freshness, . . . n Uncertainty $10 1 0 0 % Trusted When I buy , use 35
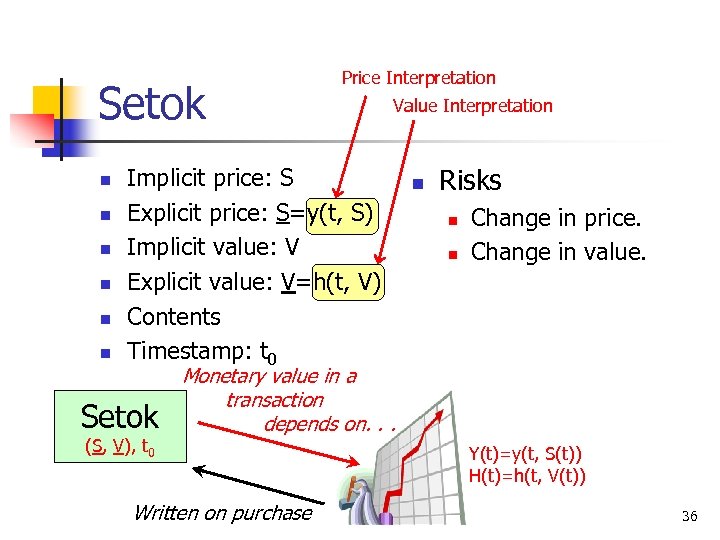 Setok n n n Price Interpretation Implicit price: S Explicit price: S=y(t, S) Implicit value: V Explicit value: V=h(t, V) Contents Timestamp: t 0 Setok (S, V), t 0 Value Interpretation n Risks n n Change in price. Change in value. Monetary value in a transaction depends on. . . Written on purchase Y(t)=y(t, S(t)) H(t)=h(t, V(t)) 36
Setok n n n Price Interpretation Implicit price: S Explicit price: S=y(t, S) Implicit value: V Explicit value: V=h(t, V) Contents Timestamp: t 0 Setok (S, V), t 0 Value Interpretation n Risks n n Change in price. Change in value. Monetary value in a transaction depends on. . . Written on purchase Y(t)=y(t, S(t)) H(t)=h(t, V(t)) 36
 The stochastic processes n n The implicit price, S, represents the market price of the setok. S is a stochastic process. The implicit value, V, is composed of a set of stochastic processes. Each process Vi represents an indicator (e. g. a firm’s transaction volume, a financial rating, revocation frequency, etc. ) that influences values associated with the setok. 37
The stochastic processes n n The implicit price, S, represents the market price of the setok. S is a stochastic process. The implicit value, V, is composed of a set of stochastic processes. Each process Vi represents an indicator (e. g. a firm’s transaction volume, a financial rating, revocation frequency, etc. ) that influences values associated with the setok. 37
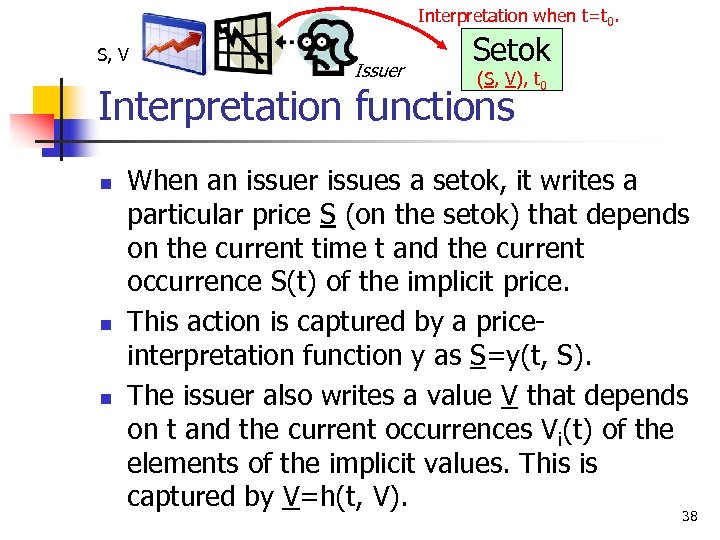 Interpretation when t=t 0. S, V Issuer Setok (S, V), t 0 Interpretation functions n n n When an issuer issues a setok, it writes a particular price S (on the setok) that depends on the current time t and the current occurrence S(t) of the implicit price. This action is captured by a priceinterpretation function y as S=y(t, S). The issuer also writes a value V that depends on t and the current occurrences Vi(t) of the elements of the implicit values. This is captured by V=h(t, V). 38
Interpretation when t=t 0. S, V Issuer Setok (S, V), t 0 Interpretation functions n n n When an issuer issues a setok, it writes a particular price S (on the setok) that depends on the current time t and the current occurrence S(t) of the implicit price. This action is captured by a priceinterpretation function y as S=y(t, S). The issuer also writes a value V that depends on t and the current occurrences Vi(t) of the elements of the implicit values. This is captured by V=h(t, V). 38
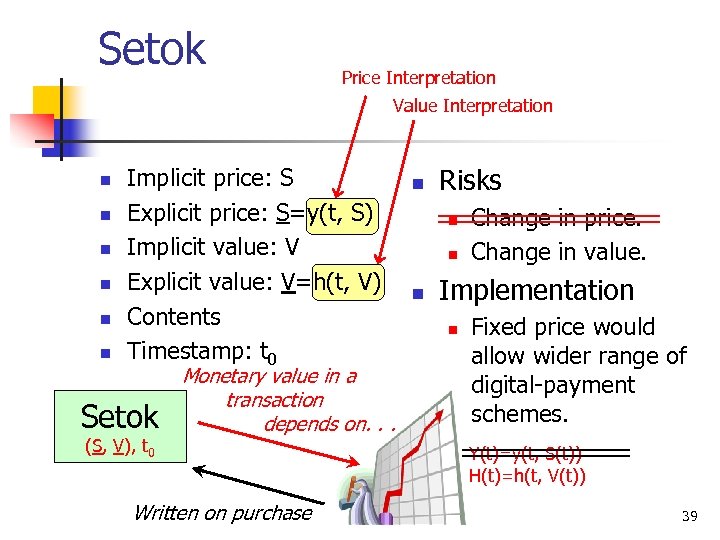 Setok Price Interpretation Value Interpretation n n n Implicit price: S Explicit price: S=y(t, S) Implicit value: V Explicit value: V=h(t, V) Contents Timestamp: t 0 Setok (S, V), t 0 Monetary value in a transaction depends on. . . Written on purchase n Risks n n n Change in price. Change in value. Implementation n Fixed price would allow wider range of digital-payment schemes. Y(t)=y(t, S(t)) H(t)=h(t, V(t)) 39
Setok Price Interpretation Value Interpretation n n n Implicit price: S Explicit price: S=y(t, S) Implicit value: V Explicit value: V=h(t, V) Contents Timestamp: t 0 Setok (S, V), t 0 Monetary value in a transaction depends on. . . Written on purchase n Risks n n n Change in price. Change in value. Implementation n Fixed price would allow wider range of digital-payment schemes. Y(t)=y(t, S(t)) H(t)=h(t, V(t)) 39
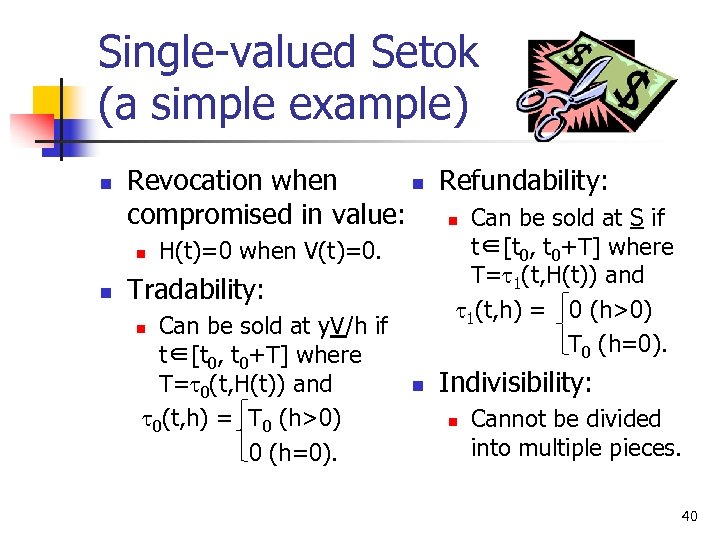 Single-valued Setok (a simple example) n Revocation when n Refundability: compromised in value: n Can be sold at S if n n t∈[t 0, t 0+T] where T=t 1(t, H(t)) and t 1(t, h) = 0 (h>0) T 0 (h=0). H(t)=0 when V(t)=0. Tradability: Can be sold at y. V/h if t∈[t 0, t 0+T] where T=t 0(t, H(t)) and t 0(t, h) = T 0 (h>0) 0 (h=0). n n Indivisibility: n Cannot be divided into multiple pieces. 40
Single-valued Setok (a simple example) n Revocation when n Refundability: compromised in value: n Can be sold at S if n n t∈[t 0, t 0+T] where T=t 1(t, H(t)) and t 1(t, h) = 0 (h>0) T 0 (h=0). H(t)=0 when V(t)=0. Tradability: Can be sold at y. V/h if t∈[t 0, t 0+T] where T=t 0(t, H(t)) and t 0(t, h) = T 0 (h>0) 0 (h=0). n n Indivisibility: n Cannot be divided into multiple pieces. 40
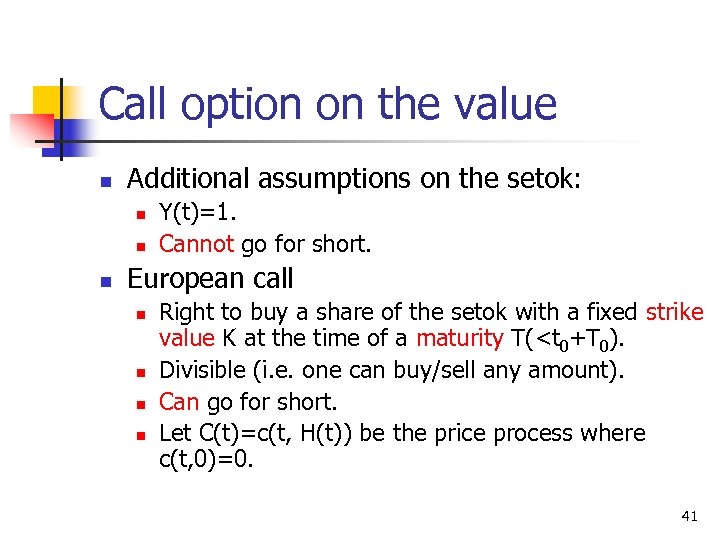 Call option on the value n Additional assumptions on the setok: n n n Y(t)=1. Cannot go for short. European call n n Right to buy a share of the setok with a fixed strike value K at the time of a maturity T(
Call option on the value n Additional assumptions on the setok: n n n Y(t)=1. Cannot go for short. European call n n Right to buy a share of the setok with a fixed strike value K at the time of a maturity T(
 Market assumptions n n n There are no transaction costs of trading both in time and in money; any transaction can be completed immediately, free of charge. The market is completely liquid, i. e. it is always possible to buy/sell unlimited quantities. The selling price is equal to the buying price. The market is free of arbitrage. There is a riskless asset with the short rate r (intuitively, the interest rate of the bank account). 42
Market assumptions n n n There are no transaction costs of trading both in time and in money; any transaction can be completed immediately, free of charge. The market is completely liquid, i. e. it is always possible to buy/sell unlimited quantities. The selling price is equal to the buying price. The market is free of arbitrage. There is a riskless asset with the short rate r (intuitively, the interest rate of the bank account). 42
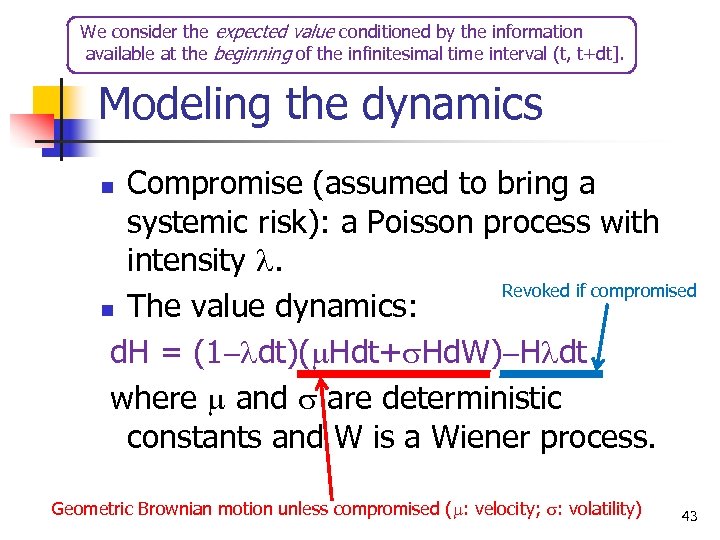 We consider the expected value conditioned by the information available at the beginning of the infinitesimal time interval (t, t+dt]. Modeling the dynamics Compromise (assumed to bring a systemic risk): a Poisson process with intensity l. Revoked if compromised n The value dynamics: d. H = (1 -ldt)(m. Hdt+s. Hd. W)-Hldt where m and s are deterministic constants and W is a Wiener process. n Geometric Brownian motion unless compromised (m: velocity; s: volatility) 43
We consider the expected value conditioned by the information available at the beginning of the infinitesimal time interval (t, t+dt]. Modeling the dynamics Compromise (assumed to bring a systemic risk): a Poisson process with intensity l. Revoked if compromised n The value dynamics: d. H = (1 -ldt)(m. Hdt+s. Hd. W)-Hldt where m and s are deterministic constants and W is a Wiener process. n Geometric Brownian motion unless compromised (m: velocity; s: volatility) 43
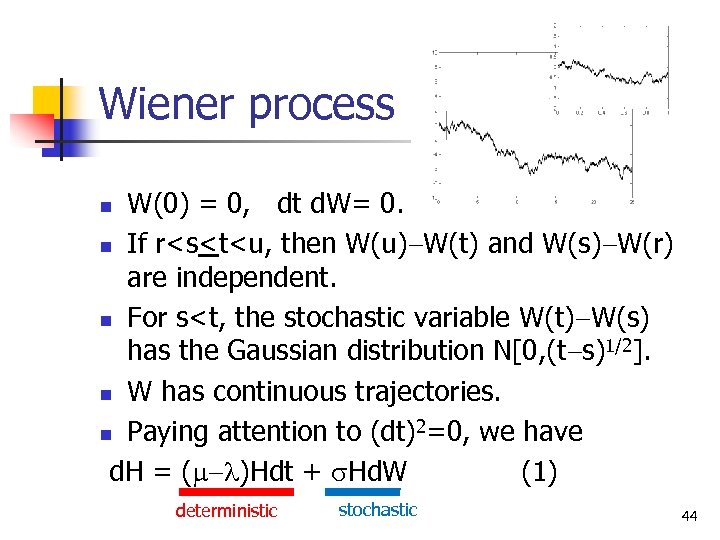 Wiener process W(0) = 0, dt d. W= 0. n If r
Wiener process W(0) = 0, dt d. W= 0. n If r
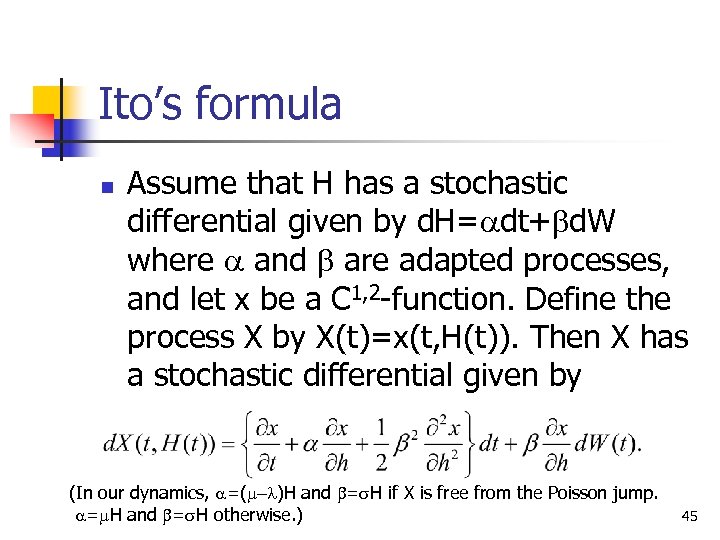 Ito’s formula n Assume that H has a stochastic differential given by d. H=adt+bd. W where a and b are adapted processes, and let x be a C 1, 2 -function. Define the process X by X(t)=x(t, H(t)). Then X has a stochastic differential given by (In our dynamics, a=(m-l)H and b=s. H if X is free from the Poisson jump. a=m. H and b=s. H otherwise. ) 45
Ito’s formula n Assume that H has a stochastic differential given by d. H=adt+bd. W where a and b are adapted processes, and let x be a C 1, 2 -function. Define the process X by X(t)=x(t, H(t)). Then X has a stochastic differential given by (In our dynamics, a=(m-l)H and b=s. H if X is free from the Poisson jump. a=m. H and b=s. H otherwise. ) 45
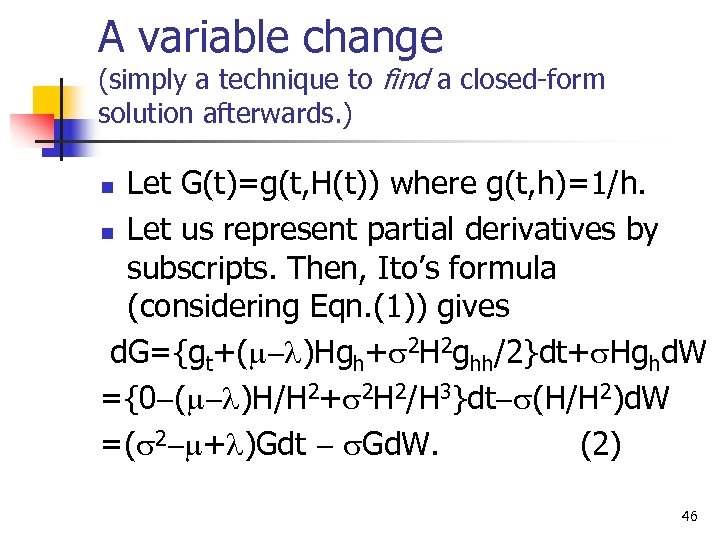 A variable change (simply a technique to find a closed-form solution afterwards. ) Let G(t)=g(t, H(t)) where g(t, h)=1/h. n Let us represent partial derivatives by subscripts. Then, Ito’s formula (considering Eqn. (1)) gives d. G={gt+(m-l)Hgh+s 2 H 2 ghh/2}dt+s. Hghd. W ={0 -(m-l)H/H 2+s 2 H 2/H 3}dt-s(H/H 2)d. W =(s 2 -m+l)Gdt - s. Gd. W. (2) n 46
A variable change (simply a technique to find a closed-form solution afterwards. ) Let G(t)=g(t, H(t)) where g(t, h)=1/h. n Let us represent partial derivatives by subscripts. Then, Ito’s formula (considering Eqn. (1)) gives d. G={gt+(m-l)Hgh+s 2 H 2 ghh/2}dt+s. Hghd. W ={0 -(m-l)H/H 2+s 2 H 2/H 3}dt-s(H/H 2)d. W =(s 2 -m+l)Gdt - s. Gd. W. (2) n 46
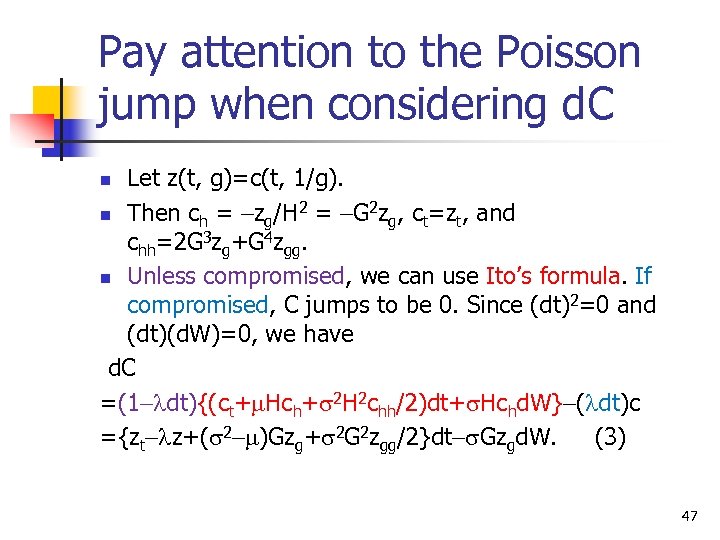 Pay attention to the Poisson jump when considering d. C Let z(t, g)=c(t, 1/g). n Then ch = -zg/H 2 = -G 2 zg, ct=zt, and chh=2 G 3 zg+G 4 zgg. n Unless compromised, we can use Ito’s formula. If compromised, C jumps to be 0. Since (dt)2=0 and (dt)(d. W)=0, we have d. C =(1 -ldt){(ct+m. Hch+s 2 H 2 chh/2)dt+s. Hchd. W}-(ldt)c ={zt-lz+(s 2 -m)Gzg+s 2 G 2 zgg/2}dt-s. Gzgd. W. (3) n 47
Pay attention to the Poisson jump when considering d. C Let z(t, g)=c(t, 1/g). n Then ch = -zg/H 2 = -G 2 zg, ct=zt, and chh=2 G 3 zg+G 4 zgg. n Unless compromised, we can use Ito’s formula. If compromised, C jumps to be 0. Since (dt)2=0 and (dt)(d. W)=0, we have d. C =(1 -ldt){(ct+m. Hch+s 2 H 2 chh/2)dt+s. Hchd. W}-(ldt)c ={zt-lz+(s 2 -m)Gzg+s 2 G 2 zgg/2}dt-s. Gzgd. W. (3) n 47
 Let us consider a riskless portfolio n n n Composed of one share of the setok and M options. Let F be the monetary value (in terms of the initial investment at the beginning of the infinitesimal time interval (t, t+dt]) of this portfolio. F = 1 + MC. M 1 48
Let us consider a riskless portfolio n n n Composed of one share of the setok and M options. Let F be the monetary value (in terms of the initial investment at the beginning of the infinitesimal time interval (t, t+dt]) of this portfolio. F = 1 + MC. M 1 48
 We want to see d. F. n n Remark: We should write the expected gain conditioned by the information available at the beginning of the infinitesimal time interval (t, t+dt]. Regarding the term that considers the M options (i. e. Md. C), we can use Eqn. (3). 49
We want to see d. F. n n Remark: We should write the expected gain conditioned by the information available at the beginning of the infinitesimal time interval (t, t+dt]. Regarding the term that considers the M options (i. e. Md. C), we can use Eqn. (3). 49
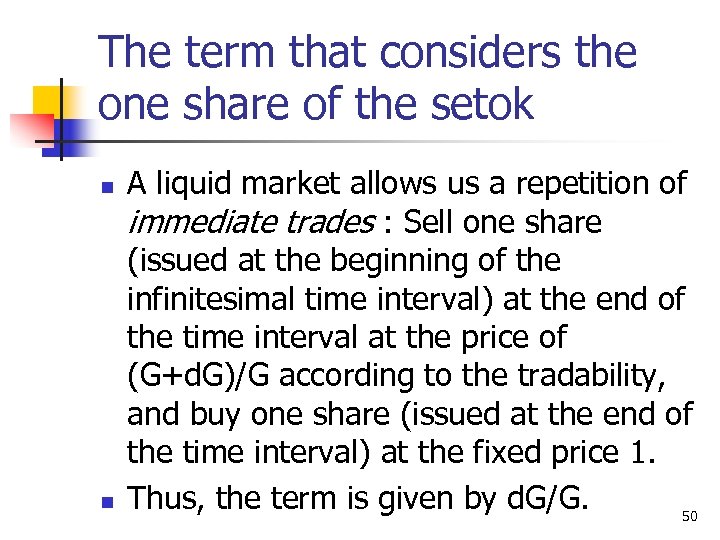 The term that considers the one share of the setok n n A liquid market allows us a repetition of immediate trades : Sell one share (issued at the beginning of the infinitesimal time interval) at the end of the time interval at the price of (G+d. G)/G according to the tradability, and buy one share (issued at the end of the time interval) at the fixed price 1. Thus, the term is given by d. G/G. 50
The term that considers the one share of the setok n n A liquid market allows us a repetition of immediate trades : Sell one share (issued at the beginning of the infinitesimal time interval) at the end of the time interval at the price of (G+d. G)/G according to the tradability, and buy one share (issued at the end of the time interval) at the fixed price 1. Thus, the term is given by d. G/G. 50
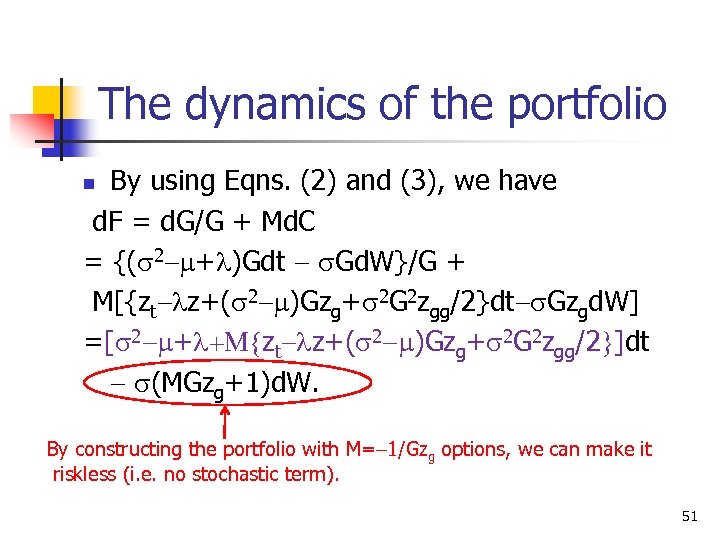 The dynamics of the portfolio By using Eqns. (2) and (3), we have d. F = d. G/G + Md. C = {(s 2 -m+l)Gdt - s. Gd. W}/G + M[{zt-lz+(s 2 -m)Gzg+s 2 G 2 zgg/2}dt-s. Gzgd. W] =[s 2 -m+l+M{zt-lz+(s 2 -m)Gzg+s 2 G 2 zgg/2}]dt - s(MGzg+1)d. W. n By constructing the portfolio with M=-1/Gzg options, we can make it riskless (i. e. no stochastic term). 51
The dynamics of the portfolio By using Eqns. (2) and (3), we have d. F = d. G/G + Md. C = {(s 2 -m+l)Gdt - s. Gd. W}/G + M[{zt-lz+(s 2 -m)Gzg+s 2 G 2 zgg/2}dt-s. Gzgd. W] =[s 2 -m+l+M{zt-lz+(s 2 -m)Gzg+s 2 G 2 zgg/2}]dt - s(MGzg+1)d. W. n By constructing the portfolio with M=-1/Gzg options, we can make it riskless (i. e. no stochastic term). 51
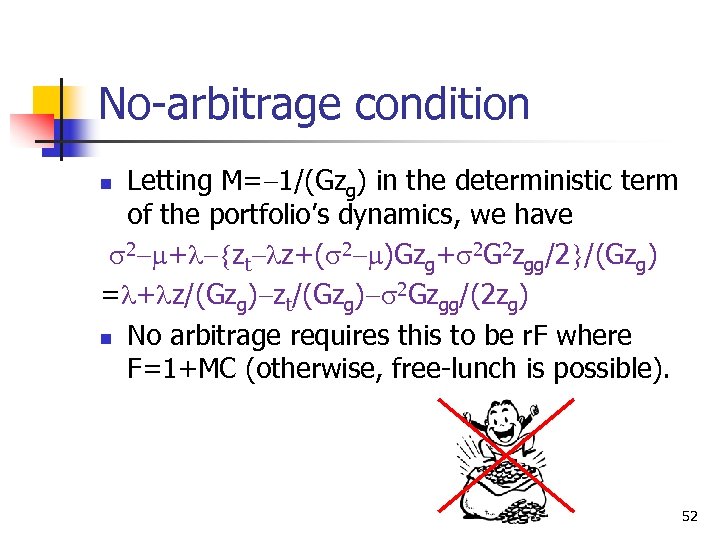 No-arbitrage condition Letting M=-1/(Gzg) in the deterministic term of the portfolio’s dynamics, we have s 2 -m+l-{zt-lz+(s 2 -m)Gzg+s 2 G 2 zgg/2}/(Gzg) =l+lz/(Gzg)-zt/(Gzg)-s 2 Gzgg/(2 zg) n No arbitrage requires this to be r. F where F=1+MC (otherwise, free-lunch is possible). n 52
No-arbitrage condition Letting M=-1/(Gzg) in the deterministic term of the portfolio’s dynamics, we have s 2 -m+l-{zt-lz+(s 2 -m)Gzg+s 2 G 2 zgg/2}/(Gzg) =l+lz/(Gzg)-zt/(Gzg)-s 2 Gzgg/(2 zg) n No arbitrage requires this to be r. F where F=1+MC (otherwise, free-lunch is possible). n 52
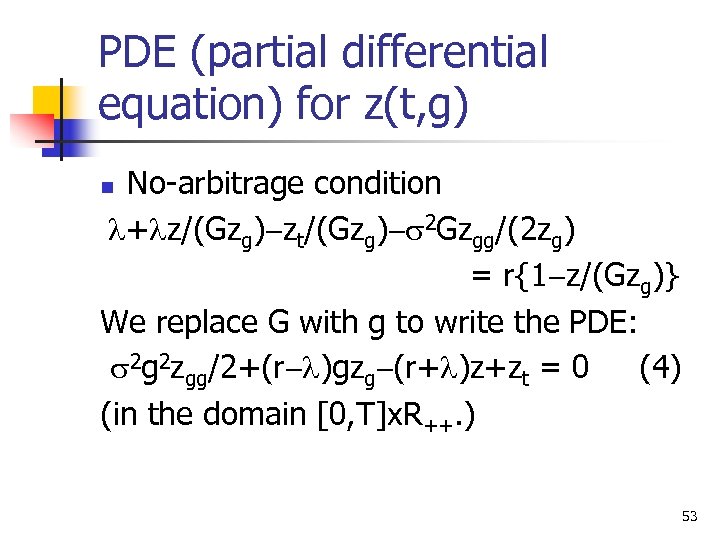 PDE (partial differential equation) for z(t, g) No-arbitrage condition l+lz/(Gzg)-zt/(Gzg)-s 2 Gzgg/(2 zg) = r{1 -z/(Gzg)} We replace G with g to write the PDE: s 2 g 2 zgg/2+(r-l)gzg-(r+l)z+zt = 0 (4) (in the domain [0, T]x. R++. ) n 53
PDE (partial differential equation) for z(t, g) No-arbitrage condition l+lz/(Gzg)-zt/(Gzg)-s 2 Gzgg/(2 zg) = r{1 -z/(Gzg)} We replace G with g to write the PDE: s 2 g 2 zgg/2+(r-l)gzg-(r+l)z+zt = 0 (4) (in the domain [0, T]x. R++. ) n 53
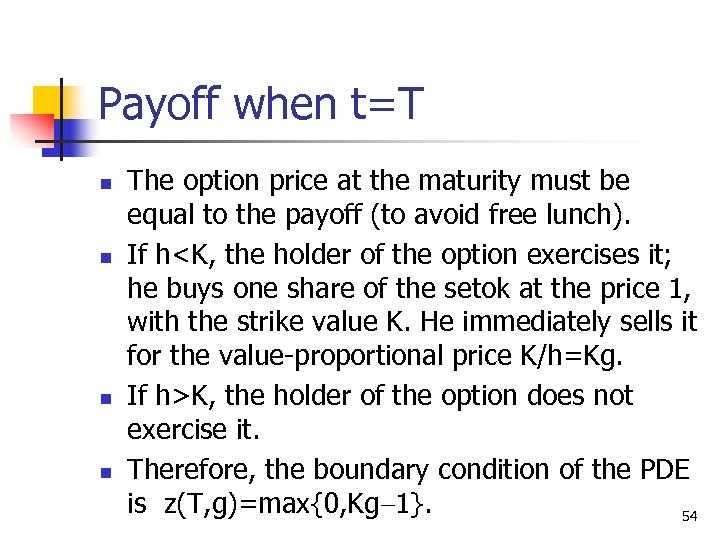 Payoff when t=T n n The option price at the maturity must be equal to the payoff (to avoid free lunch). If h
Payoff when t=T n n The option price at the maturity must be equal to the payoff (to avoid free lunch). If h
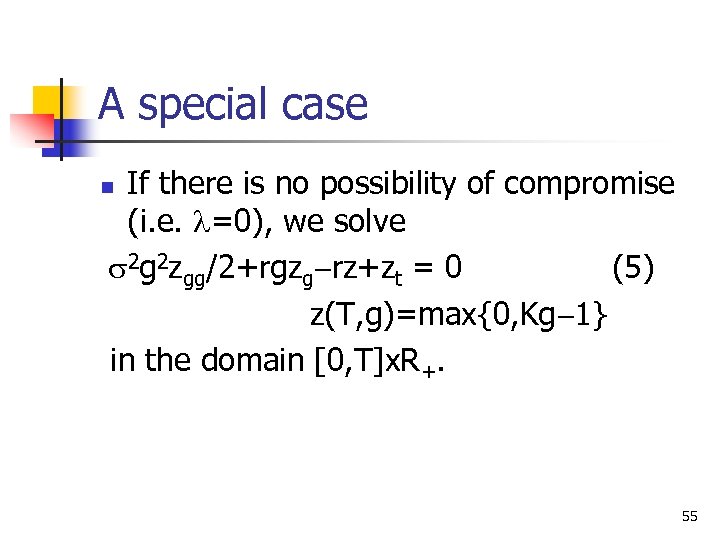 A special case If there is no possibility of compromise (i. e. l=0), we solve s 2 g 2 zgg/2+rgzg-rz+zt = 0 (5) z(T, g)=max{0, Kg-1} in the domain [0, T]x. R+. n 55
A special case If there is no possibility of compromise (i. e. l=0), we solve s 2 g 2 zgg/2+rgzg-rz+zt = 0 (5) z(T, g)=max{0, Kg-1} in the domain [0, T]x. R+. n 55
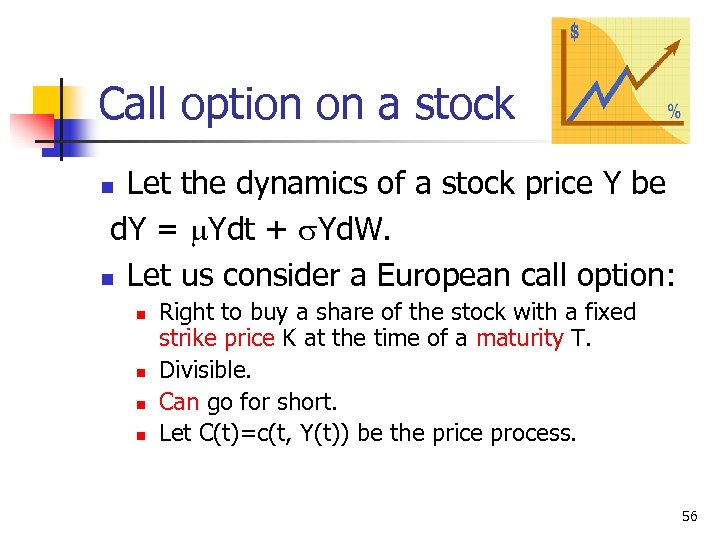 Call option on a stock Let the dynamics of a stock price Y be d. Y = m. Ydt + s. Yd. W. n Let us consider a European call option: n n n Right to buy a share of the stock with a fixed strike price K at the time of a maturity T. Divisible. Can go for short. Let C(t)=c(t, Y(t)) be the price process. 56
Call option on a stock Let the dynamics of a stock price Y be d. Y = m. Ydt + s. Yd. W. n Let us consider a European call option: n n n Right to buy a share of the stock with a fixed strike price K at the time of a maturity T. Divisible. Can go for short. Let C(t)=c(t, Y(t)) be the price process. 56
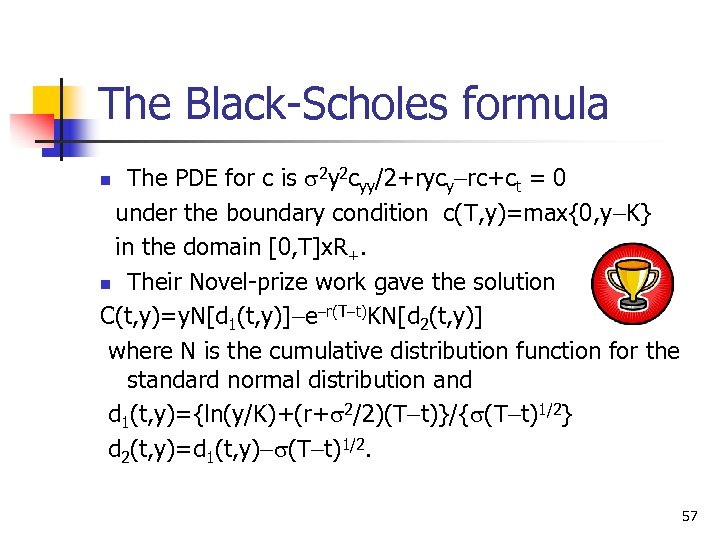 The Black-Scholes formula The PDE for c is s 2 y 2 cyy/2+rycy-rc+ct = 0 under the boundary condition c(T, y)=max{0, y-K} in the domain [0, T]x. R+. n Their Novel-prize work gave the solution C(t, y)=y. N[d 1(t, y)]-e-r(T-t)KN[d 2(t, y)] where N is the cumulative distribution function for the standard normal distribution and d 1(t, y)={ln(y/K)+(r+s 2/2)(T-t)}/{s(T-t)1/2} d 2(t, y)=d 1(t, y)-s(T-t)1/2. n 57
The Black-Scholes formula The PDE for c is s 2 y 2 cyy/2+rycy-rc+ct = 0 under the boundary condition c(T, y)=max{0, y-K} in the domain [0, T]x. R+. n Their Novel-prize work gave the solution C(t, y)=y. N[d 1(t, y)]-e-r(T-t)KN[d 2(t, y)] where N is the cumulative distribution function for the standard normal distribution and d 1(t, y)={ln(y/K)+(r+s 2/2)(T-t)}/{s(T-t)1/2} d 2(t, y)=d 1(t, y)-s(T-t)1/2. n 57
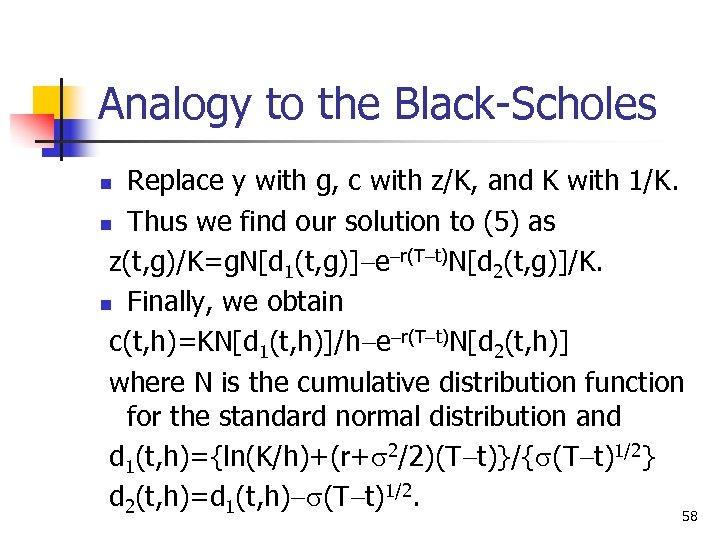 Analogy to the Black-Scholes Replace y with g, c with z/K, and K with 1/K. n Thus we find our solution to (5) as z(t, g)/K=g. N[d 1(t, g)]-e-r(T-t)N[d 2(t, g)]/K. n Finally, we obtain c(t, h)=KN[d 1(t, h)]/h-e-r(T-t)N[d 2(t, h)] where N is the cumulative distribution function for the standard normal distribution and d 1(t, h)={ln(K/h)+(r+s 2/2)(T-t)}/{s(T-t)1/2} d 2(t, h)=d 1(t, h)-s(T-t)1/2. n 58
Analogy to the Black-Scholes Replace y with g, c with z/K, and K with 1/K. n Thus we find our solution to (5) as z(t, g)/K=g. N[d 1(t, g)]-e-r(T-t)N[d 2(t, g)]/K. n Finally, we obtain c(t, h)=KN[d 1(t, h)]/h-e-r(T-t)N[d 2(t, h)] where N is the cumulative distribution function for the standard normal distribution and d 1(t, h)={ln(K/h)+(r+s 2/2)(T-t)}/{s(T-t)1/2} d 2(t, h)=d 1(t, h)-s(T-t)1/2. n 58
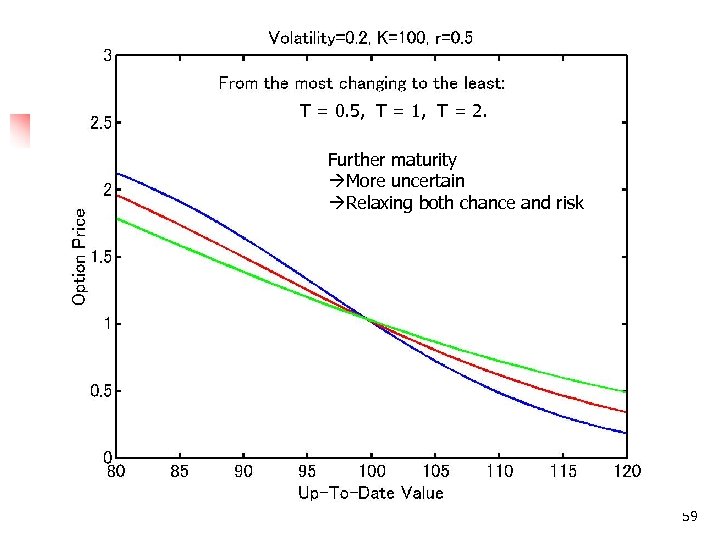 T = 0. 5, T = 1, T = 2. Further maturity More uncertain Relaxing both chance and risk 59
T = 0. 5, T = 1, T = 2. Further maturity More uncertain Relaxing both chance and risk 59
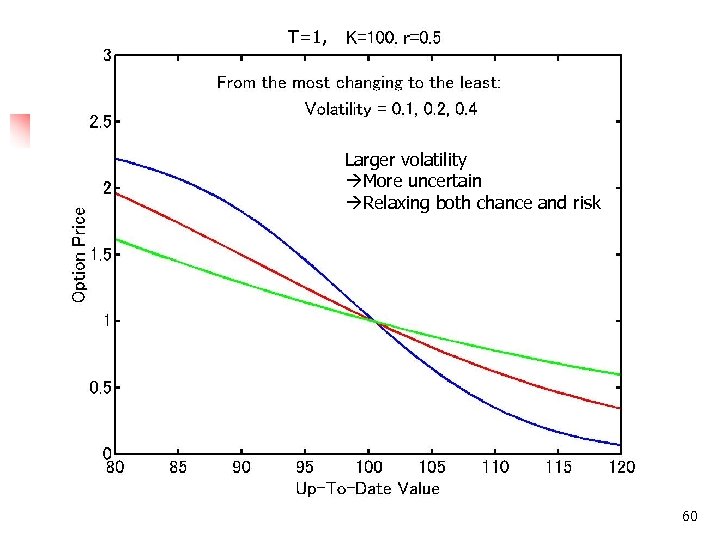 T=1, Larger volatility More uncertain Relaxing both chance and risk 60
T=1, Larger volatility More uncertain Relaxing both chance and risk 60
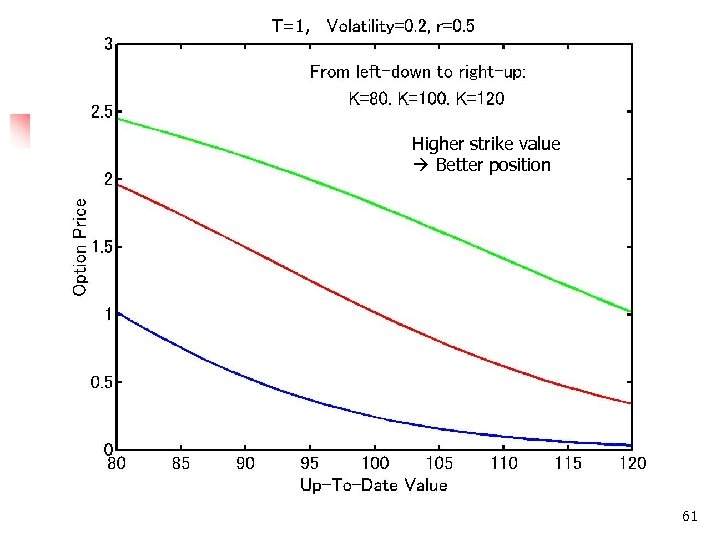 T=1, Higher strike value Better position 61
T=1, Higher strike value Better position 61
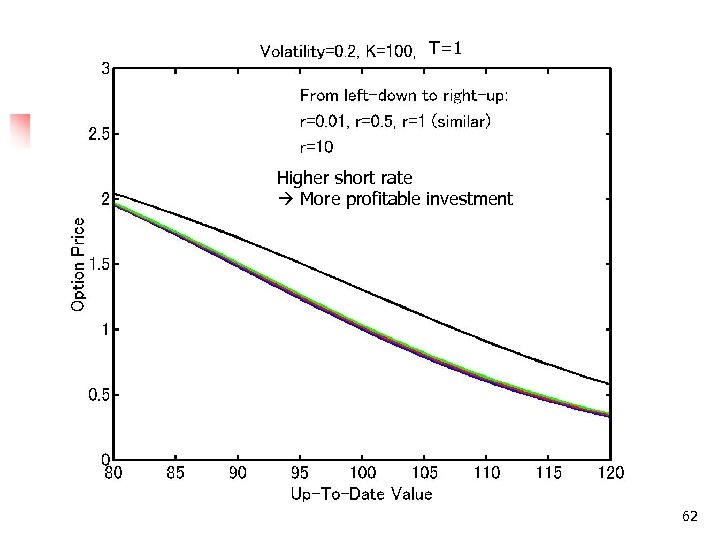 T=1 Higher short rate More profitable investment 62
T=1 Higher short rate More profitable investment 62
 Application n Sudden ruin of values n n How often? Systemic risk Could be implied by the option price n Security minister Let’s measure the market evaluation of the risk. 63
Application n Sudden ruin of values n n How often? Systemic risk Could be implied by the option price n Security minister Let’s measure the market evaluation of the risk. 63
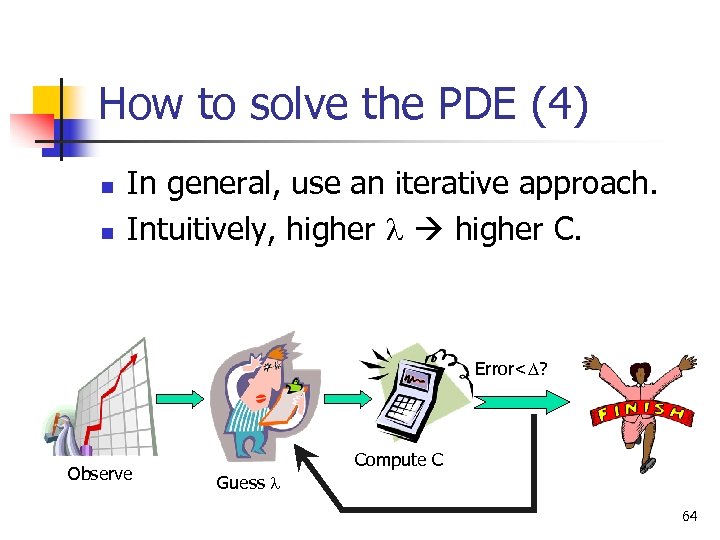 How to solve the PDE (4) n n In general, use an iterative approach. Intuitively, higher l higher C. Error
How to solve the PDE (4) n n In general, use an iterative approach. Intuitively, higher l higher C. Error
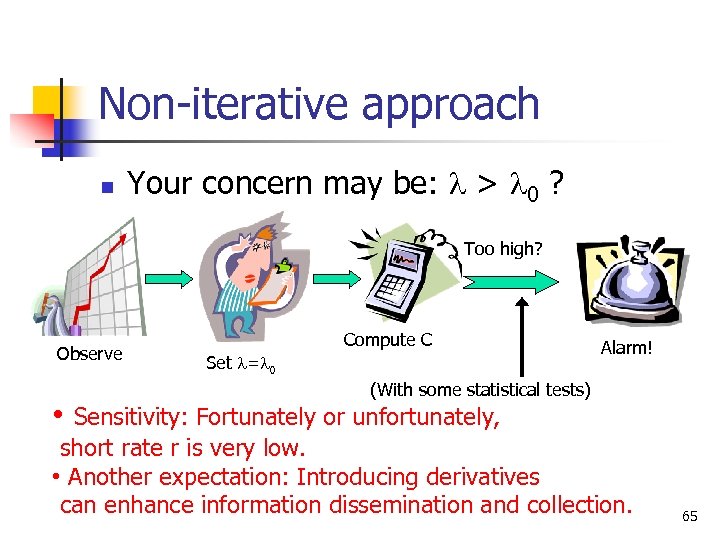 Non-iterative approach n Your concern may be: l > l 0 ? Too high? Observe • Compute C Set l=l 0 Alarm! (With some statistical tests) Sensitivity: Fortunately or unfortunately, short rate r is very low. • Another expectation: Introducing derivatives can enhance information dissemination and collection. 65
Non-iterative approach n Your concern may be: l > l 0 ? Too high? Observe • Compute C Set l=l 0 Alarm! (With some statistical tests) Sensitivity: Fortunately or unfortunately, short rate r is very low. • Another expectation: Introducing derivatives can enhance information dissemination and collection. 65
 References (1/3) n n R. Rue, S. L. Pfleeger, and D. Ortiz: A Framework for Classifying and Comparing Models of Cyber Security Investment to Support Policy and Decision-Making. Workshop on the Economics of Information Security 2007. H. Varian: How to build an economic model in your spare time. Part of a collection titled Passion and Craft: Economists at Work (M. Szenberg ed. ), University of Michigan Press, 1997. L. A. Gordon and M. P. Loeb: The Economics of Information Security Investment. ACM Transactions on Information and System Security (5: 4) pp. 438 -457, 2002. H. Tanaka, K. Matsuura, and O. Sudoh: Vulnerability and Information Security Investment: an Empirical Analysis of e. Local Government in Japan. Journal of Accounting and Public Policy (24: 1) pp. 37 -59, 2005. 66
References (1/3) n n R. Rue, S. L. Pfleeger, and D. Ortiz: A Framework for Classifying and Comparing Models of Cyber Security Investment to Support Policy and Decision-Making. Workshop on the Economics of Information Security 2007. H. Varian: How to build an economic model in your spare time. Part of a collection titled Passion and Craft: Economists at Work (M. Szenberg ed. ), University of Michigan Press, 1997. L. A. Gordon and M. P. Loeb: The Economics of Information Security Investment. ACM Transactions on Information and System Security (5: 4) pp. 438 -457, 2002. H. Tanaka, K. Matsuura, and O. Sudoh: Vulnerability and Information Security Investment: an Empirical Analysis of e. Local Government in Japan. Journal of Accounting and Public Policy (24: 1) pp. 37 -59, 2005. 66
 References (2/3) n n W. Liu, H. Tanaka, and K. Matsuura: Empirical-Analysis Methodology for Information-Security Investment and Its Application to a Reliable Survey of Japanese Firms. IPSJ Journal (48: 9) pp. 3204 -3218, 2007. L. A. Gordon, M. P. Loeb, and W. Lucyshyn: Sharing Information on Computer Systems Security: An Economic Analysis. Journal of Accounting & Public Policy (22: 6) pp. 461 -485, 2003. K. Matsuura: Productivity Space of Information Security in an Extension of the Gordon-Loeb's Investment Model. Workshop on the Economics of Information Security 2008. K. Matsuura: Productivity Space of Information Security in an Extension of the Gordon-Loeb's Investment Model. In Managing Information Risk and the Economics of Security (E. Johnson ed. ), Springer, pp. 99 -119, 2009. 67
References (2/3) n n W. Liu, H. Tanaka, and K. Matsuura: Empirical-Analysis Methodology for Information-Security Investment and Its Application to a Reliable Survey of Japanese Firms. IPSJ Journal (48: 9) pp. 3204 -3218, 2007. L. A. Gordon, M. P. Loeb, and W. Lucyshyn: Sharing Information on Computer Systems Security: An Economic Analysis. Journal of Accounting & Public Policy (22: 6) pp. 461 -485, 2003. K. Matsuura: Productivity Space of Information Security in an Extension of the Gordon-Loeb's Investment Model. Workshop on the Economics of Information Security 2008. K. Matsuura: Productivity Space of Information Security in an Extension of the Gordon-Loeb's Investment Model. In Managing Information Risk and the Economics of Security (E. Johnson ed. ), Springer, pp. 99 -119, 2009. 67
 References (3/3) n n K. Matsuura: Security Tokens and Their Derivatives. Technical Reports 29, Centre for Communications Systems Research, University of Cambridge, 2001. K. Matsuura: Digital Security Tokens and Their Derivatives. 7 th International Conference of the Society for Computational Economics, 2001. K. Matsuura: A Derivative of Digital Objects and Estimation of Default Risks in Electronic Commerce. Lecture Notes in Computer Science 2229, Springer, pp. 90 -94, 2001. K. Matsuura: Digital Security Tokens and Their Derivatives. Netnomics (5: 2) pp. 161 -179, 2003. (A note) My publication in 2008: 50% in cryptography, 27% in network security, 23% in economics of information security. 68
References (3/3) n n K. Matsuura: Security Tokens and Their Derivatives. Technical Reports 29, Centre for Communications Systems Research, University of Cambridge, 2001. K. Matsuura: Digital Security Tokens and Their Derivatives. 7 th International Conference of the Society for Computational Economics, 2001. K. Matsuura: A Derivative of Digital Objects and Estimation of Default Risks in Electronic Commerce. Lecture Notes in Computer Science 2229, Springer, pp. 90 -94, 2001. K. Matsuura: Digital Security Tokens and Their Derivatives. Netnomics (5: 2) pp. 161 -179, 2003. (A note) My publication in 2008: 50% in cryptography, 27% in network security, 23% in economics of information security. 68


