a9e705dd75c741ec16228fadc7d7bfee.ppt
- Количество слайдов: 46
 2 nd International Scientific Conference Security and Protection of Information Austrian e-Government and Citizen Card Initiatives Herbert Leitold Brno, 29. April 2003 Secure Information Technology Center – Austria (A-SIT) 3/19/2018 1/45
2 nd International Scientific Conference Security and Protection of Information Austrian e-Government and Citizen Card Initiatives Herbert Leitold Brno, 29. April 2003 Secure Information Technology Center – Austria (A-SIT) 3/19/2018 1/45
 About myself Working for A-SIT Confirmation body under Austrian Signature Law Notified body w. r. t. EU Electronic Signature Directive 1999/93/EC Advises public authorities in ICT security aspects Activities include Technology assessment activities Brno, 29. April 2003 Standardization Electronic signatures, biometrics, IT security tools, … EESSI: Common Criteria Protection Profiles that support the EU Electronic Signature Directive White Book “Austrian Citizen Card” 3/19/2018 2/45
About myself Working for A-SIT Confirmation body under Austrian Signature Law Notified body w. r. t. EU Electronic Signature Directive 1999/93/EC Advises public authorities in ICT security aspects Activities include Technology assessment activities Brno, 29. April 2003 Standardization Electronic signatures, biometrics, IT security tools, … EESSI: Common Criteria Protection Profiles that support the EU Electronic Signature Directive White Book “Austrian Citizen Card” 3/19/2018 2/45
 2 nd International Scientific Conference Security and Protection of Information Brno, 29. April 2003 Table of Contents @ 3/19/2018 Introduction e-Government in Europe Austrian e-Government basics Unique identification Electronic signatures & e-Gov. European dimension Austrian citizen card concept Identification/Confidentiality levels 3/45 Conclusions
2 nd International Scientific Conference Security and Protection of Information Brno, 29. April 2003 Table of Contents @ 3/19/2018 Introduction e-Government in Europe Austrian e-Government basics Unique identification Electronic signatures & e-Gov. European dimension Austrian citizen card concept Identification/Confidentiality levels 3/45 Conclusions
 Internet penetration in the EU Brno, 29. April 2003 50 % Source: Europ. Commission (e. Europe benchmarking 2002) 3/19/2018 4/45
Internet penetration in the EU Brno, 29. April 2003 50 % Source: Europ. Commission (e. Europe benchmarking 2002) 3/19/2018 4/45
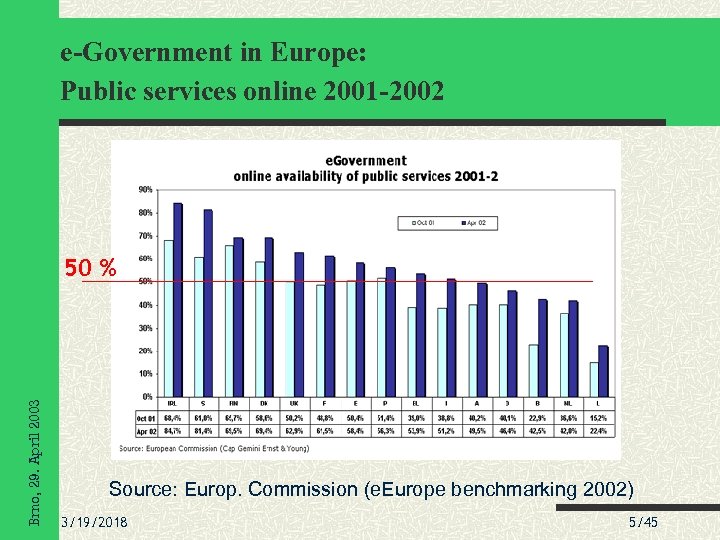 e-Government in Europe: Public services online 2001 -2002 Brno, 29. April 2003 50 % Source: Europ. Commission (e. Europe benchmarking 2002) 3/19/2018 5/45
e-Government in Europe: Public services online 2001 -2002 Brno, 29. April 2003 50 % Source: Europ. Commission (e. Europe benchmarking 2002) 3/19/2018 5/45
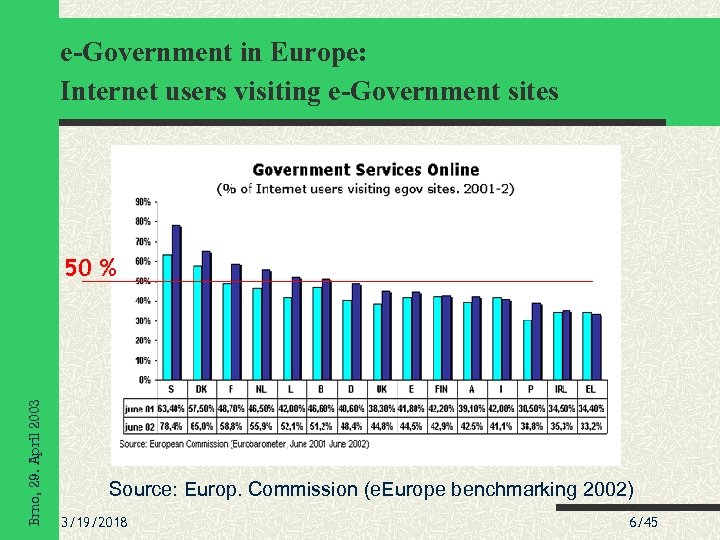 e-Government in Europe: Internet users visiting e-Government sites Brno, 29. April 2003 50 % Source: Europ. Commission (e. Europe benchmarking 2002) 3/19/2018 6/45
e-Government in Europe: Internet users visiting e-Government sites Brno, 29. April 2003 50 % Source: Europ. Commission (e. Europe benchmarking 2002) 3/19/2018 6/45
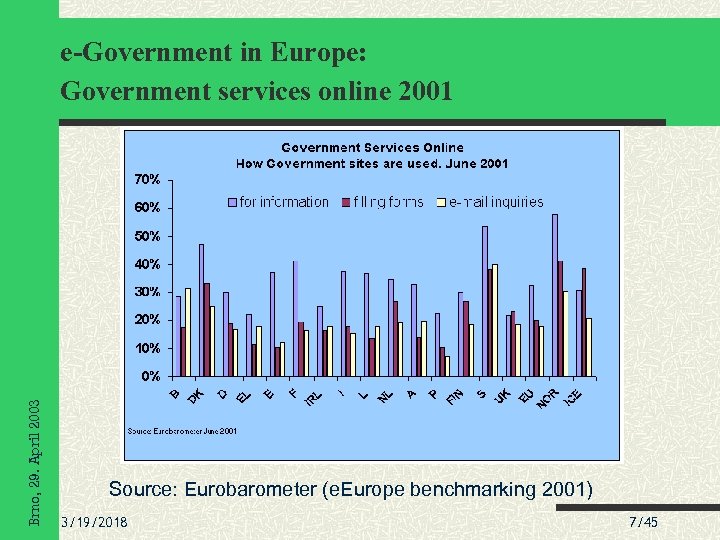 Brno, 29. April 2003 e-Government in Europe: Government services online 2001 Source: Eurobarometer (e. Europe benchmarking 2001) 3/19/2018 7/45
Brno, 29. April 2003 e-Government in Europe: Government services online 2001 Source: Eurobarometer (e. Europe benchmarking 2001) 3/19/2018 7/45
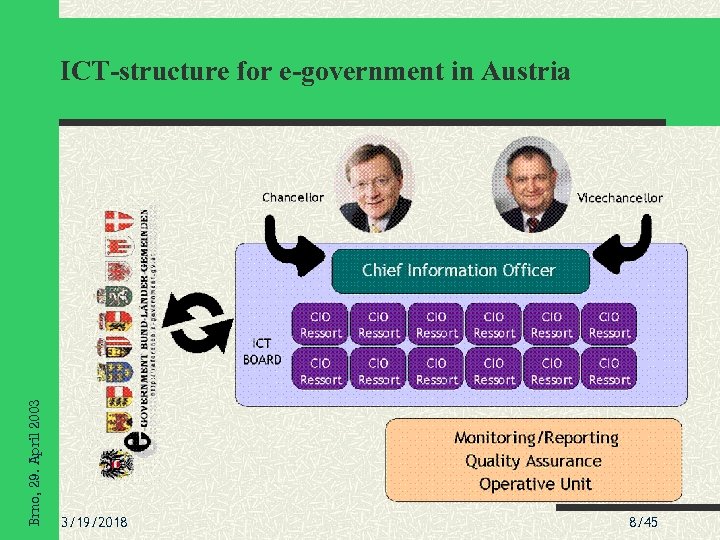 Brno, 29. April 2003 ICT-structure for e-government in Austria 3/19/2018 8/45
Brno, 29. April 2003 ICT-structure for e-government in Austria 3/19/2018 8/45
 The starting points. . . Austrian cabinet council decision (Nov. 2000) … to employ chip-card technology to improve citizen’s access to public services … to supplement the planned health insurance card with electronic signature Brno, 29. April 2003 “White book” citizen card (June 2001) defines general requirements and strategic decisions from an authority’s perspective 3/19/2018 9/45
The starting points. . . Austrian cabinet council decision (Nov. 2000) … to employ chip-card technology to improve citizen’s access to public services … to supplement the planned health insurance card with electronic signature Brno, 29. April 2003 “White book” citizen card (June 2001) defines general requirements and strategic decisions from an authority’s perspective 3/19/2018 9/45
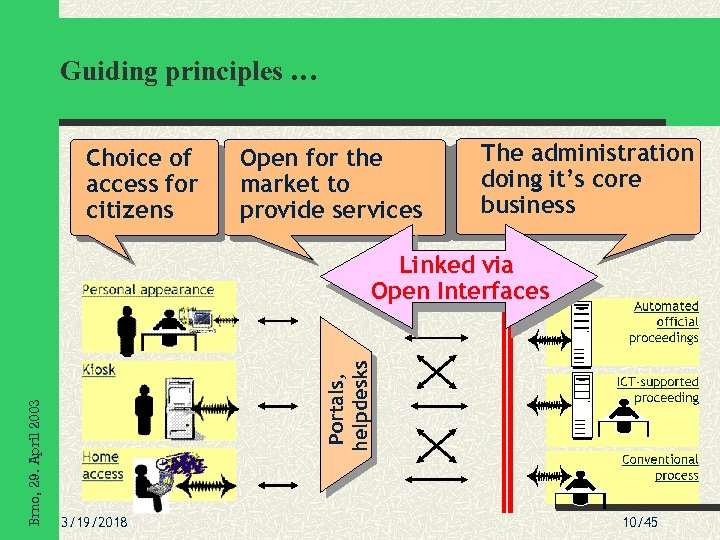 Guiding principles … Choice of access for citizens Open for the market to provide services The administration doing it’s core business Portals, helpdesks Brno, 29. April 2003 Linked via Open Interfaces 3/19/2018 10/45
Guiding principles … Choice of access for citizens Open for the market to provide services The administration doing it’s core business Portals, helpdesks Brno, 29. April 2003 Linked via Open Interfaces 3/19/2018 10/45
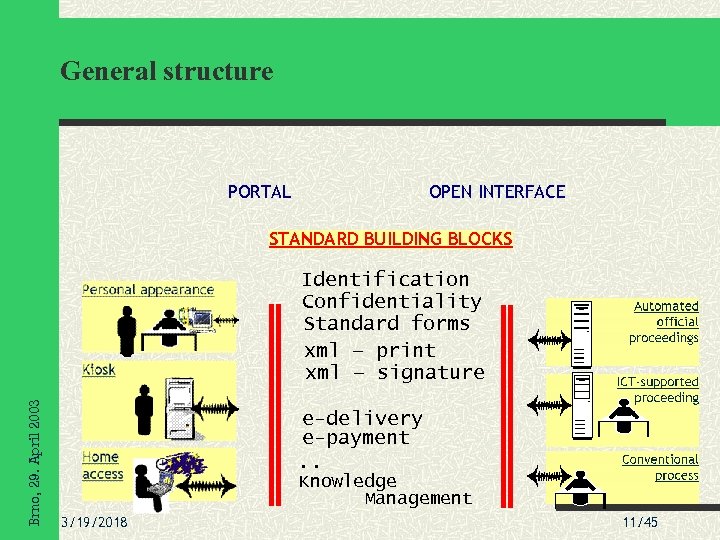 General structure PORTAL OPEN INTERFACE STANDARD BUILDING BLOCKS Brno, 29. April 2003 Identification Confidentiality Standard forms xml – print xml – signature e-delivery e-payment . . Knowledge Management 3/19/2018 11/45
General structure PORTAL OPEN INTERFACE STANDARD BUILDING BLOCKS Brno, 29. April 2003 Identification Confidentiality Standard forms xml – print xml – signature e-delivery e-payment . . Knowledge Management 3/19/2018 11/45
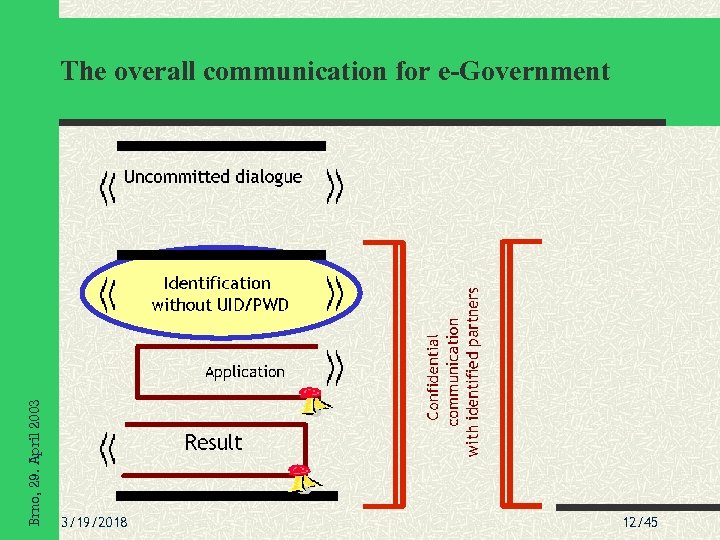 Brno, 29. April 2003 The overall communication for e-Government 3/19/2018 12/45
Brno, 29. April 2003 The overall communication for e-Government 3/19/2018 12/45
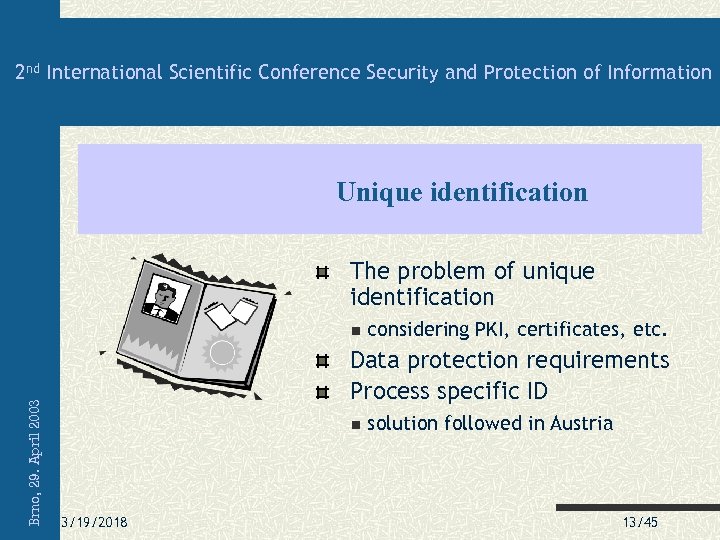 2 nd International Scientific Conference Security and Protection of Information Unique identification The problem of unique identification Brno, 29. April 2003 considering PKI, certificates, etc. Data protection requirements Process specific ID 3/19/2018 solution followed in Austria 13/45
2 nd International Scientific Conference Security and Protection of Information Unique identification The problem of unique identification Brno, 29. April 2003 considering PKI, certificates, etc. Data protection requirements Process specific ID 3/19/2018 solution followed in Austria 13/45
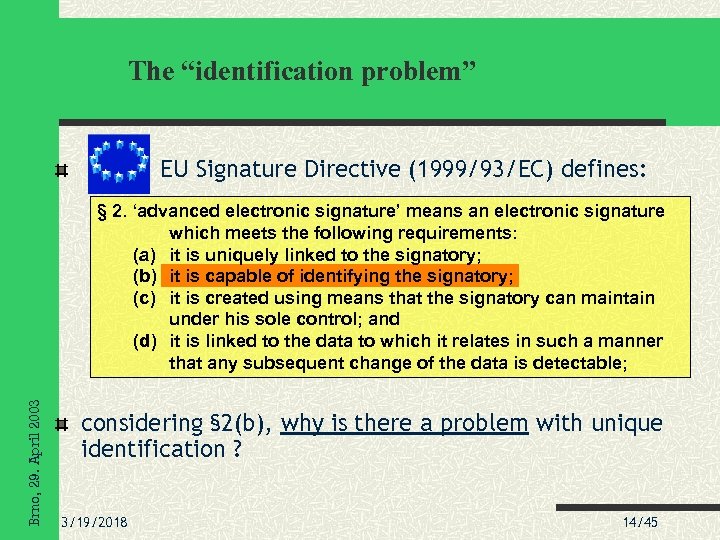 The “identification problem” EU Signature Directive (1999/93/EC) defines: Brno, 29. April 2003 § 2. ‘advanced electronic signature’ means an electronic signature which meets the following requirements: (a) it is uniquely linked to the signatory; (b) it is capable of identifying the signatory; (c) it is created using means that the signatory can maintain under his sole control; and (d) it is linked to the data to which it relates in such a manner that any subsequent change of the data is detectable; considering § 2(b), why is there a problem with unique identification ? 3/19/2018 14/45
The “identification problem” EU Signature Directive (1999/93/EC) defines: Brno, 29. April 2003 § 2. ‘advanced electronic signature’ means an electronic signature which meets the following requirements: (a) it is uniquely linked to the signatory; (b) it is capable of identifying the signatory; (c) it is created using means that the signatory can maintain under his sole control; and (d) it is linked to the data to which it relates in such a manner that any subsequent change of the data is detectable; considering § 2(b), why is there a problem with unique identification ? 3/19/2018 14/45
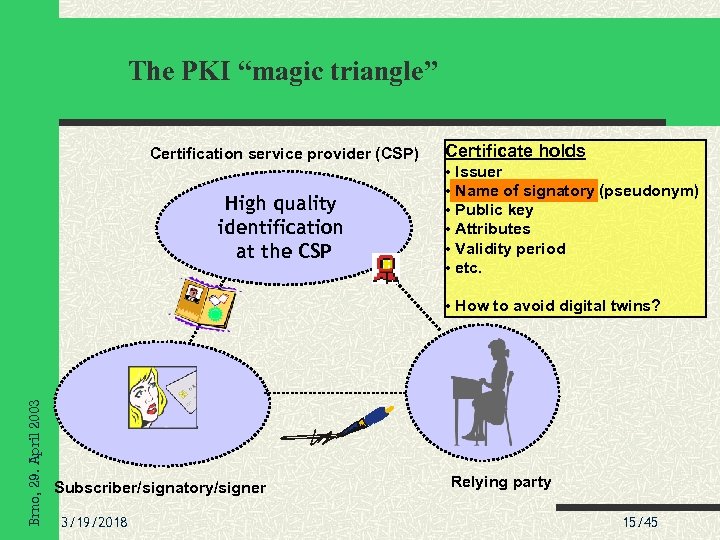 The PKI “magic triangle” Certification service provider (CSP) High quality identification at the CSP Certificate holds • Issuer • Name of signatory (pseudonym) • Public key • Attributes • Validity period • etc. Brno, 29. April 2003 • How to avoid digital twins? Subscriber/signatory/signer 3/19/2018 Relying party 15/45
The PKI “magic triangle” Certification service provider (CSP) High quality identification at the CSP Certificate holds • Issuer • Name of signatory (pseudonym) • Public key • Attributes • Validity period • etc. Brno, 29. April 2003 • How to avoid digital twins? Subscriber/signatory/signer 3/19/2018 Relying party 15/45
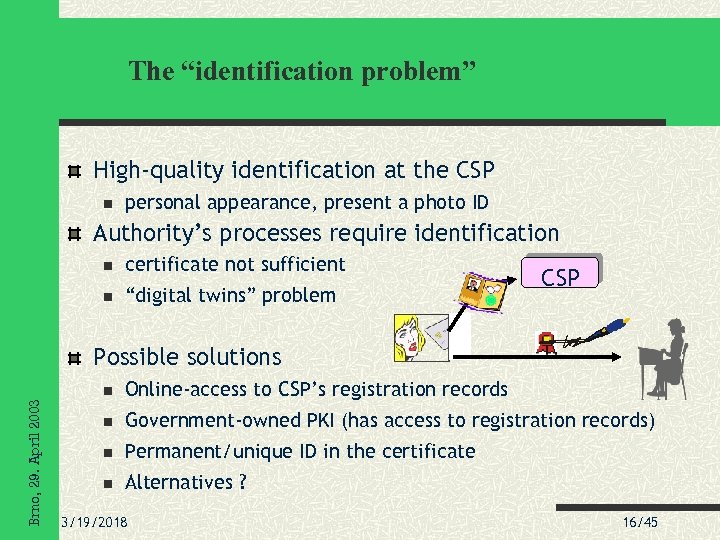 The “identification problem” High-quality identification at the CSP personal appearance, present a photo ID Authority’s processes require identification certificate not sufficient “digital twins” problem CSP Possible solutions Brno, 29. April 2003 Online-access to CSP’s registration records Government-owned PKI (has access to registration records) Permanent/unique ID in the certificate Alternatives ? 3/19/2018 16/45
The “identification problem” High-quality identification at the CSP personal appearance, present a photo ID Authority’s processes require identification certificate not sufficient “digital twins” problem CSP Possible solutions Brno, 29. April 2003 Online-access to CSP’s registration records Government-owned PKI (has access to registration records) Permanent/unique ID in the certificate Alternatives ? 3/19/2018 16/45
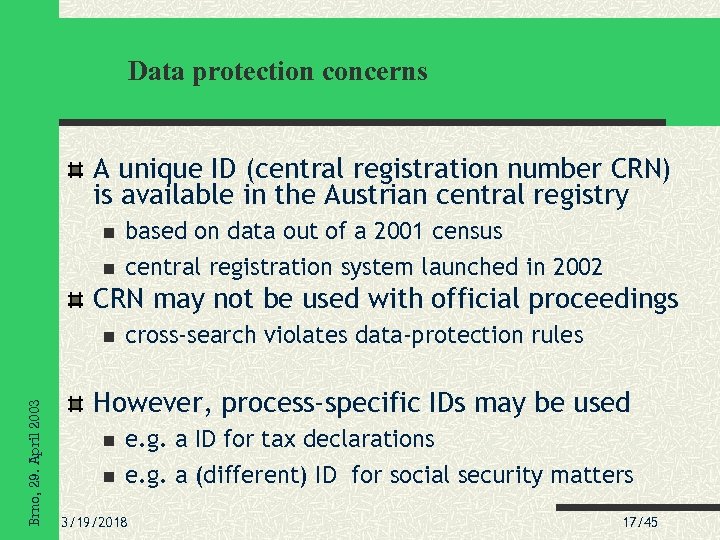 Data protection concerns A unique ID (central registration number CRN) is available in the Austrian central registry based on data out of a 2001 census central registration system launched in 2002 CRN may not be used with official proceedings Brno, 29. April 2003 cross-search violates data-protection rules However, process-specific IDs may be used e. g. a ID for tax declarations e. g. a (different) ID for social security matters 3/19/2018 17/45
Data protection concerns A unique ID (central registration number CRN) is available in the Austrian central registry based on data out of a 2001 census central registration system launched in 2002 CRN may not be used with official proceedings Brno, 29. April 2003 cross-search violates data-protection rules However, process-specific IDs may be used e. g. a ID for tax declarations e. g. a (different) ID for social security matters 3/19/2018 17/45
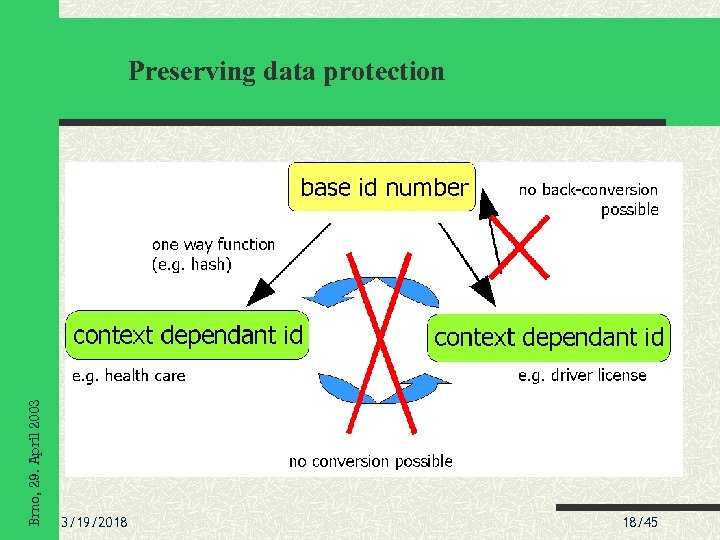 Brno, 29. April 2003 Preserving data protection 3/19/2018 18/45
Brno, 29. April 2003 Preserving data protection 3/19/2018 18/45
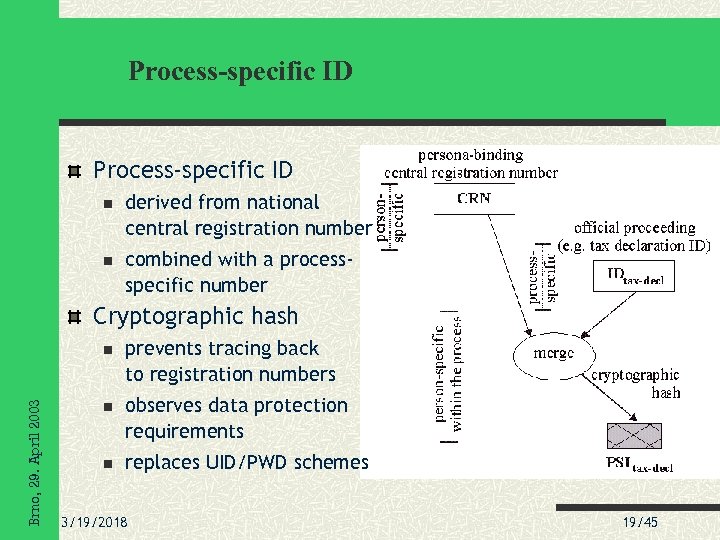 Process-specific ID derived from national central registration number combined with a processspecific number Cryptographic hash Brno, 29. April 2003 prevents tracing back to registration numbers observes data protection requirements replaces UID/PWD schemes 3/19/2018 19/45
Process-specific ID derived from national central registration number combined with a processspecific number Cryptographic hash Brno, 29. April 2003 prevents tracing back to registration numbers observes data protection requirements replaces UID/PWD schemes 3/19/2018 19/45
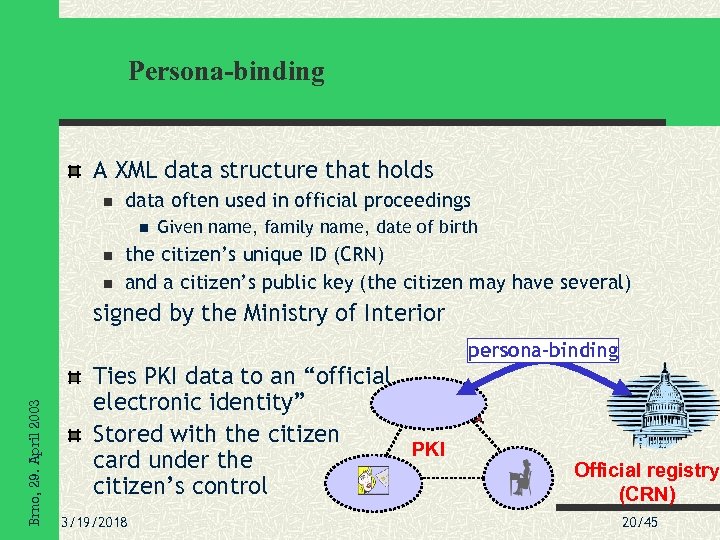 Persona-binding A XML data structure that holds data often used in official proceedings Given name, family name, date of birth the citizen’s unique ID (CRN) and a citizen’s public key (the citizen may have several) Brno, 29. April 2003 signed by the Ministry of Interior Ties PKI data to an “official electronic identity” Stored with the citizen PKI card under the citizen’s control 3/19/2018 persona-binding Official registry (CRN) 20/45
Persona-binding A XML data structure that holds data often used in official proceedings Given name, family name, date of birth the citizen’s unique ID (CRN) and a citizen’s public key (the citizen may have several) Brno, 29. April 2003 signed by the Ministry of Interior Ties PKI data to an “official electronic identity” Stored with the citizen PKI card under the citizen’s control 3/19/2018 persona-binding Official registry (CRN) 20/45
 2 nd International Scientific Conference Security and Protection of Information Electronic signatures and e-Government EU signature directive Directive 1999/93/EC Requirements for SSCDs Brno, 29. April 2003 the European dimension Evaluation of components Austrian signature law 3/19/2018 Relation to the EU directive 21/45
2 nd International Scientific Conference Security and Protection of Information Electronic signatures and e-Government EU signature directive Directive 1999/93/EC Requirements for SSCDs Brno, 29. April 2003 the European dimension Evaluation of components Austrian signature law 3/19/2018 Relation to the EU directive 21/45
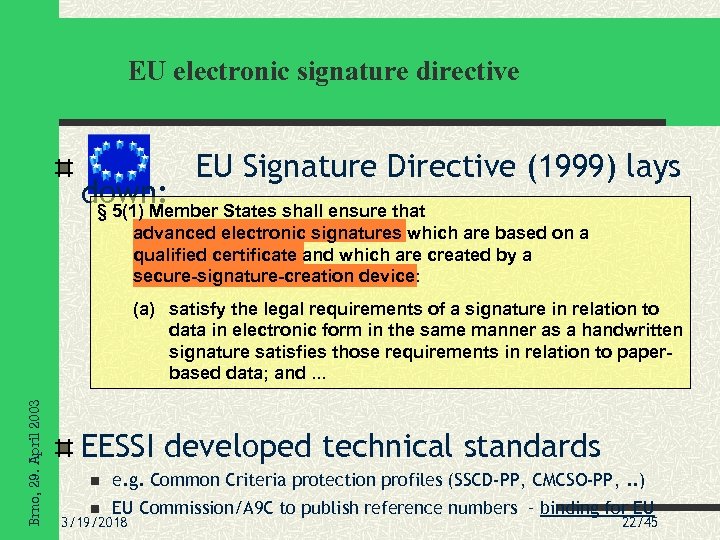 EU electronic signature directive EU Signature Directive (1999) lays down: § 5(1) Member States shall ensure that advanced electronic signatures which are based on a qualified certificate and which are created by a secure-signature-creation device: Brno, 29. April 2003 (a) satisfy the legal requirements of a signature in relation to data in electronic form in the same manner as a handwritten signature satisfies those requirements in relation to paperbased data; and. . . EESSI developed technical standards e. g. Common Criteria protection profiles (SSCD-PP, CMCSO-PP, . . ) EU Commission/A 9 C to publish reference numbers – binding for EU 3/19/2018 22/45
EU electronic signature directive EU Signature Directive (1999) lays down: § 5(1) Member States shall ensure that advanced electronic signatures which are based on a qualified certificate and which are created by a secure-signature-creation device: Brno, 29. April 2003 (a) satisfy the legal requirements of a signature in relation to data in electronic form in the same manner as a handwritten signature satisfies those requirements in relation to paperbased data; and. . . EESSI developed technical standards e. g. Common Criteria protection profiles (SSCD-PP, CMCSO-PP, . . ) EU Commission/A 9 C to publish reference numbers – binding for EU 3/19/2018 22/45
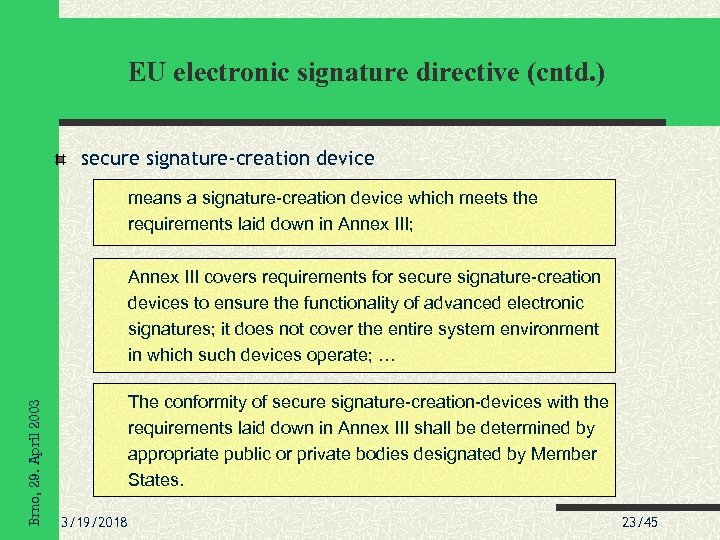 EU electronic signature directive (cntd. ) secure signature-creation device means a signature-creation device which meets the requirements laid down in Annex III; Brno, 29. April 2003 Annex III covers requirements for secure signature-creation devices to ensure the functionality of advanced electronic signatures; it does not cover the entire system environment in which such devices operate; … The conformity of secure signature-creation-devices with the requirements laid down in Annex III shall be determined by appropriate public or private bodies designated by Member States. 3/19/2018 23/45
EU electronic signature directive (cntd. ) secure signature-creation device means a signature-creation device which meets the requirements laid down in Annex III; Brno, 29. April 2003 Annex III covers requirements for secure signature-creation devices to ensure the functionality of advanced electronic signatures; it does not cover the entire system environment in which such devices operate; … The conformity of secure signature-creation-devices with the requirements laid down in Annex III shall be determined by appropriate public or private bodies designated by Member States. 3/19/2018 23/45
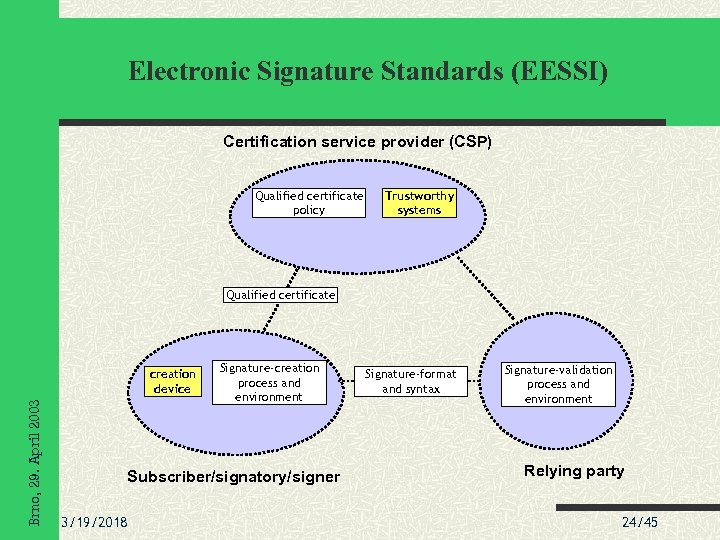 Electronic Signature Standards (EESSI) Certification service provider (CSP) Qualified certificate policy Trustworthy systems Qualified certificate Brno, 29. April 2003 creation device Signature-creation process and environment Subscriber/signatory/signer 3/19/2018 Signature-format and syntax Signature-validation process and environment Relying party 24/45
Electronic Signature Standards (EESSI) Certification service provider (CSP) Qualified certificate policy Trustworthy systems Qualified certificate Brno, 29. April 2003 creation device Signature-creation process and environment Subscriber/signatory/signer 3/19/2018 Signature-format and syntax Signature-validation process and environment Relying party 24/45
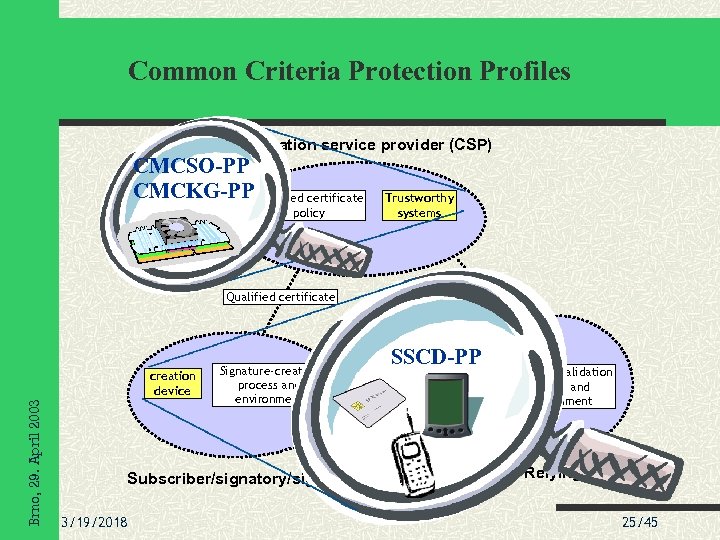 Common Criteria Protection Profiles Certification service provider (CSP) CMCSO-PP CMCKG-PP Qualified certificate policy Trustworthy systems Qualified certificate Brno, 29. April 2003 creation device Signature-creation process and environment Subscriber/signatory/signer 3/19/2018 SSCD-PP Signature-format and syntax Signature-validation process and environment Relying party 25/45
Common Criteria Protection Profiles Certification service provider (CSP) CMCSO-PP CMCKG-PP Qualified certificate policy Trustworthy systems Qualified certificate Brno, 29. April 2003 creation device Signature-creation process and environment Subscriber/signatory/signer 3/19/2018 SSCD-PP Signature-format and syntax Signature-validation process and environment Relying party 25/45
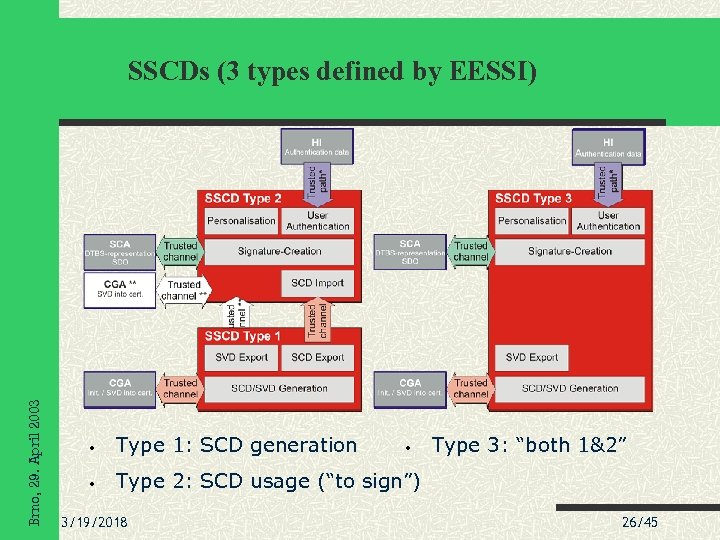 Brno, 29. April 2003 SSCDs (3 types defined by EESSI) • Type 1: SCD generation • Type 3: “both 1&2” Type 2: SCD usage (“to sign”) 3/19/2018 • 26/45
Brno, 29. April 2003 SSCDs (3 types defined by EESSI) • Type 1: SCD generation • Type 3: “both 1&2” Type 2: SCD usage (“to sign”) 3/19/2018 • 26/45
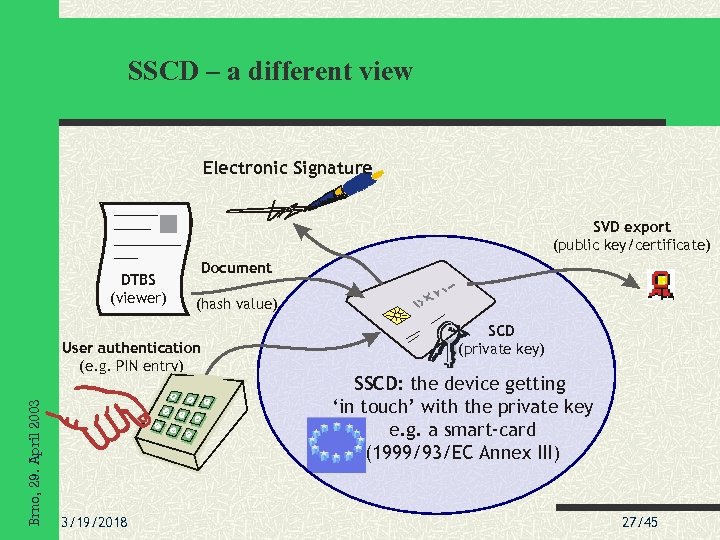 SSCD – a different view Electronic Signature SVD export (public key/certificate) DTBS (viewer) Document (hash value) Brno, 29. April 2003 User authentication (e. g. PIN entry) 3/19/2018 SCD (private key) SSCD: the device getting ‘in touch’ with the private key e. g. a smart-card (1999/93/EC Annex III) 27/45
SSCD – a different view Electronic Signature SVD export (public key/certificate) DTBS (viewer) Document (hash value) Brno, 29. April 2003 User authentication (e. g. PIN entry) 3/19/2018 SCD (private key) SSCD: the device getting ‘in touch’ with the private key e. g. a smart-card (1999/93/EC Annex III) 27/45
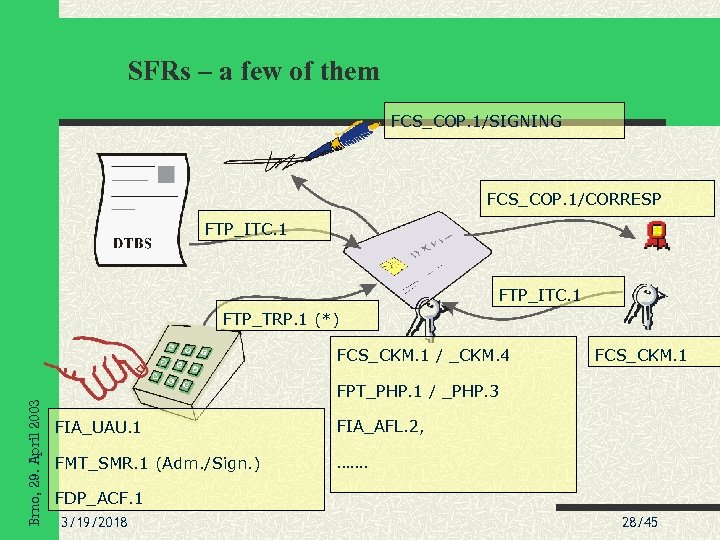 SFRs – a few of them FCS_COP. 1/SIGNING FCS_COP. 1/CORRESP FTP_ITC. 1 FTP_TRP. 1 (*) Brno, 29. April 2003 FCS_CKM. 1 / _CKM. 4 FCS_CKM. 1 FPT_PHP. 1 / _PHP. 3 FIA_UAU. 1 FIA_AFL. 2, FMT_SMR. 1 (Adm. /Sign. ) ……. FDP_ACF. 1 3/19/2018 28/45
SFRs – a few of them FCS_COP. 1/SIGNING FCS_COP. 1/CORRESP FTP_ITC. 1 FTP_TRP. 1 (*) Brno, 29. April 2003 FCS_CKM. 1 / _CKM. 4 FCS_CKM. 1 FPT_PHP. 1 / _PHP. 3 FIA_UAU. 1 FIA_AFL. 2, FMT_SMR. 1 (Adm. /Sign. ) ……. FDP_ACF. 1 3/19/2018 28/45
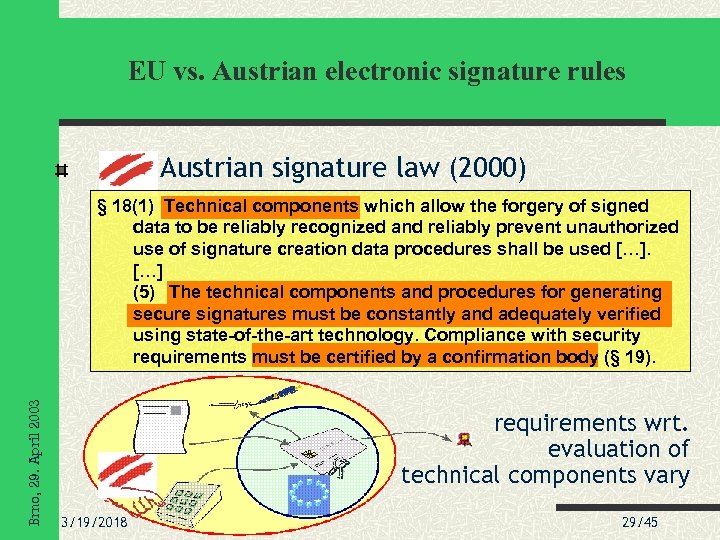 EU vs. Austrian electronic signature rules Austrian signature law (2000) Brno, 29. April 2003 § 18(1) Technical components which allow the forgery of signed data to be reliably recognized and reliably prevent unauthorized use of signature creation data procedures shall be used […] (5) The technical components and procedures for generating secure signatures must be constantly and adequately verified using state-of-the-art technology. Compliance with security requirements must be certified by a confirmation body (§ 19). requirements wrt. evaluation of technical components vary 3/19/2018 29/45
EU vs. Austrian electronic signature rules Austrian signature law (2000) Brno, 29. April 2003 § 18(1) Technical components which allow the forgery of signed data to be reliably recognized and reliably prevent unauthorized use of signature creation data procedures shall be used […] (5) The technical components and procedures for generating secure signatures must be constantly and adequately verified using state-of-the-art technology. Compliance with security requirements must be certified by a confirmation body (§ 19). requirements wrt. evaluation of technical components vary 3/19/2018 29/45
 2 nd International Scientific Conference Security and Protection of Information Austrian Citizen Card Brno, 29. April 2003 a single specific smart-card? requirements of the citizen card logical view to the card security layer / security capsule How the model is used 3/19/2018 30/45
2 nd International Scientific Conference Security and Protection of Information Austrian Citizen Card Brno, 29. April 2003 a single specific smart-card? requirements of the citizen card logical view to the card security layer / security capsule How the model is used 3/19/2018 30/45
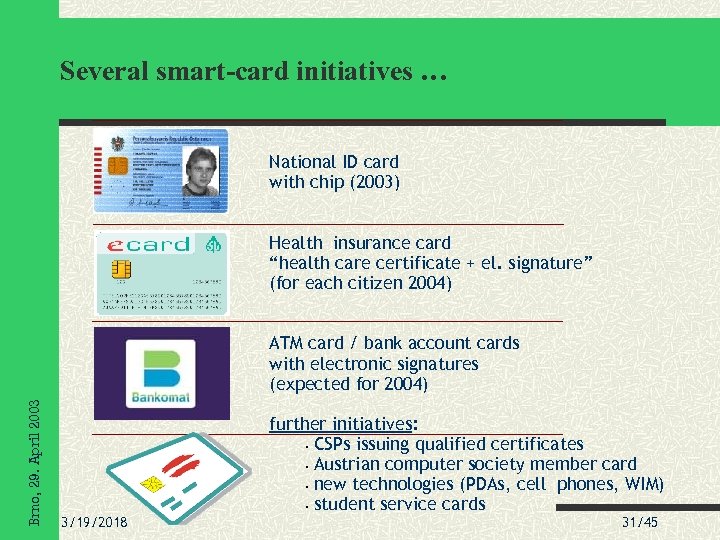 Several smart-card initiatives … National ID card with chip (2003) Health insurance card “health care certificate + el. signature” (for each citizen 2004) Brno, 29. April 2003 ATM card / bank account cards with electronic signatures (expected for 2004) 3/19/2018 further initiatives: • CSPs issuing qualified certificates • Austrian computer society member card • new technologies (PDAs, cell phones, WIM) • student service cards 31/45
Several smart-card initiatives … National ID card with chip (2003) Health insurance card “health care certificate + el. signature” (for each citizen 2004) Brno, 29. April 2003 ATM card / bank account cards with electronic signatures (expected for 2004) 3/19/2018 further initiatives: • CSPs issuing qualified certificates • Austrian computer society member card • new technologies (PDAs, cell phones, WIM) • student service cards 31/45
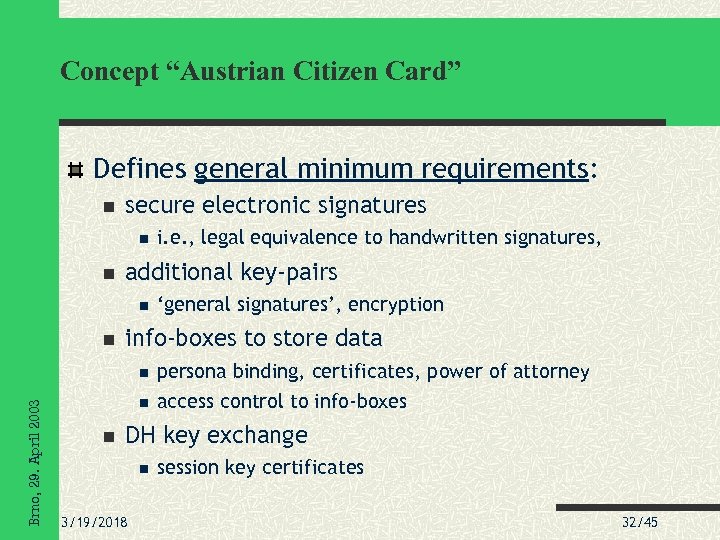 Concept “Austrian Citizen Card” Defines general minimum requirements: secure electronic signatures additional key-pairs i. e. , legal equivalence to handwritten signatures, ‘general signatures’, encryption info-boxes to store data Brno, 29. April 2003 persona binding, certificates, power of attorney access control to info-boxes DH key exchange 3/19/2018 session key certificates 32/45
Concept “Austrian Citizen Card” Defines general minimum requirements: secure electronic signatures additional key-pairs i. e. , legal equivalence to handwritten signatures, ‘general signatures’, encryption info-boxes to store data Brno, 29. April 2003 persona binding, certificates, power of attorney access control to info-boxes DH key exchange 3/19/2018 session key certificates 32/45
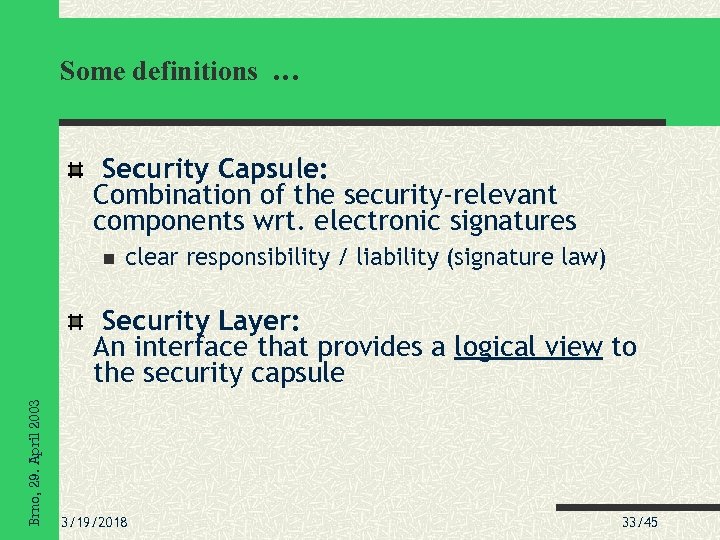 Some definitions … Security Capsule: Combination of the security-relevant components wrt. electronic signatures clear responsibility / liability (signature law) Brno, 29. April 2003 Security Layer: An interface that provides a logical view to the security capsule 3/19/2018 33/45
Some definitions … Security Capsule: Combination of the security-relevant components wrt. electronic signatures clear responsibility / liability (signature law) Brno, 29. April 2003 Security Layer: An interface that provides a logical view to the security capsule 3/19/2018 33/45
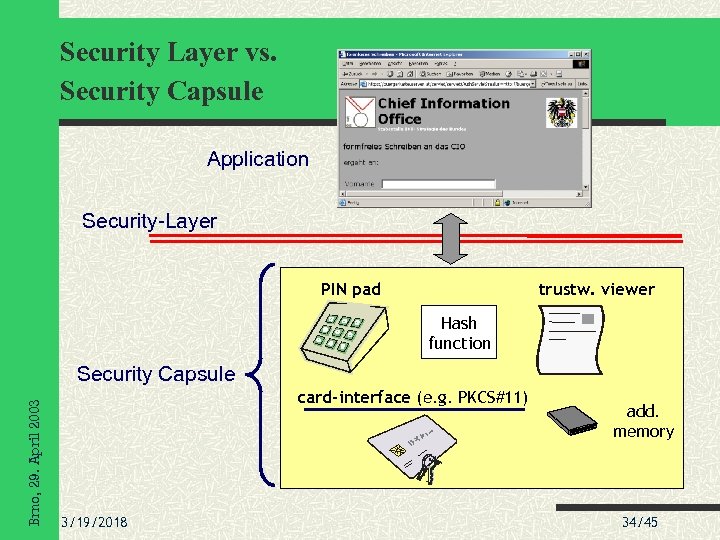 Security Layer vs. Security Capsule Application Security-Layer PIN pad trustw. viewer Hash function Brno, 29. April 2003 Security Capsule card-interface (e. g. PKCS#11) 3/19/2018 add. memory 34/45
Security Layer vs. Security Capsule Application Security-Layer PIN pad trustw. viewer Hash function Brno, 29. April 2003 Security Capsule card-interface (e. g. PKCS#11) 3/19/2018 add. memory 34/45
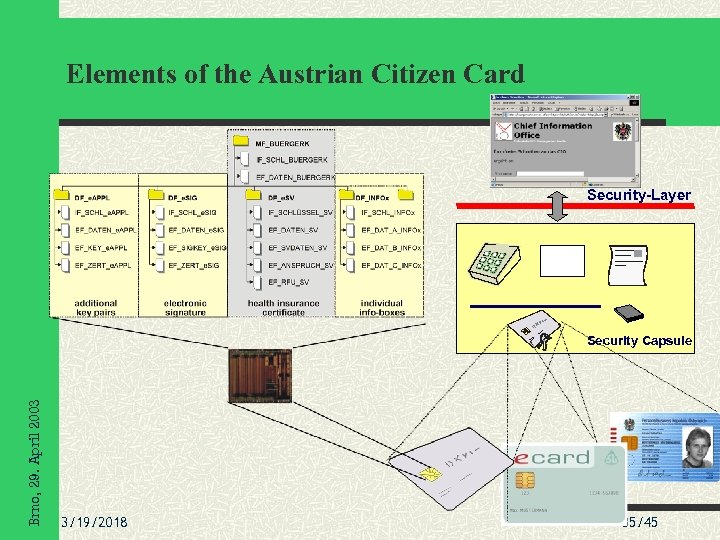 Elements of the Austrian Citizen Card Security-Layer Brno, 29. April 2003 Security Capsule 3/19/2018 35/45
Elements of the Austrian Citizen Card Security-Layer Brno, 29. April 2003 Security Capsule 3/19/2018 35/45
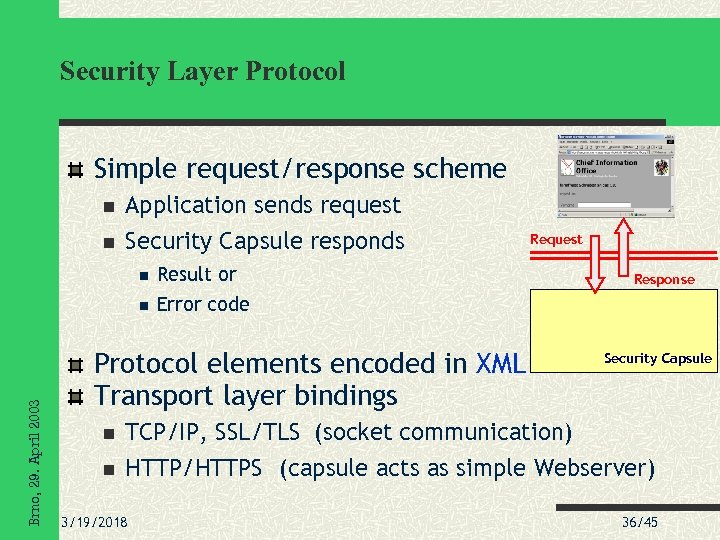 Security Layer Protocol Simple request/response scheme Application sends request Security Capsule responds Result or Brno, 29. April 2003 Request Error code Protocol elements encoded in XML Transport layer bindings Response Security Capsule TCP/IP, SSL/TLS (socket communication) HTTP/HTTPS (capsule acts as simple Webserver) 3/19/2018 36/45
Security Layer Protocol Simple request/response scheme Application sends request Security Capsule responds Result or Brno, 29. April 2003 Request Error code Protocol elements encoded in XML Transport layer bindings Response Security Capsule TCP/IP, SSL/TLS (socket communication) HTTP/HTTPS (capsule acts as simple Webserver) 3/19/2018 36/45
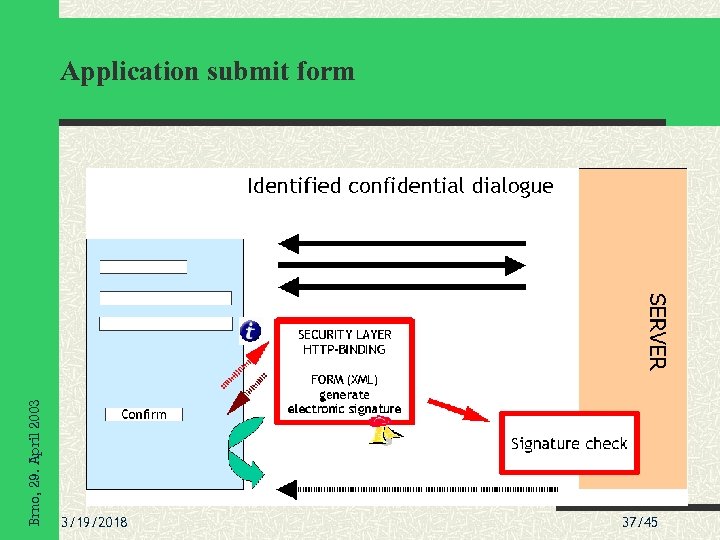 Brno, 29. April 2003 Application submit form 3/19/2018 37/45
Brno, 29. April 2003 Application submit form 3/19/2018 37/45
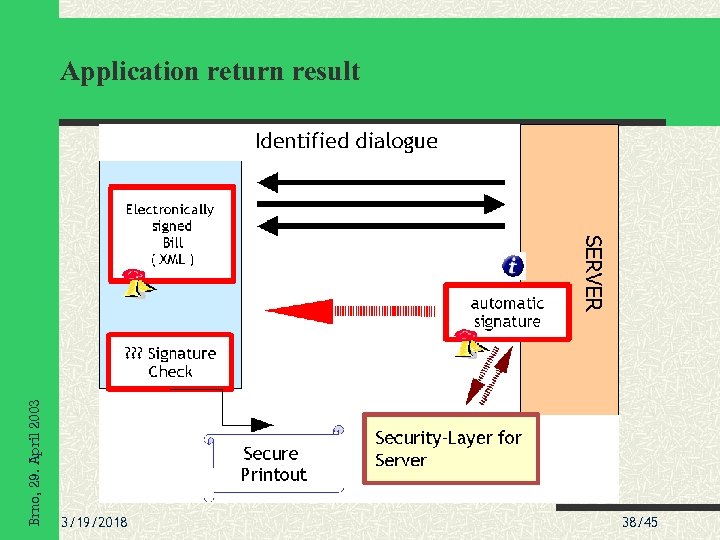 Brno, 29. April 2003 Application return result 3/19/2018 38/45
Brno, 29. April 2003 Application return result 3/19/2018 38/45
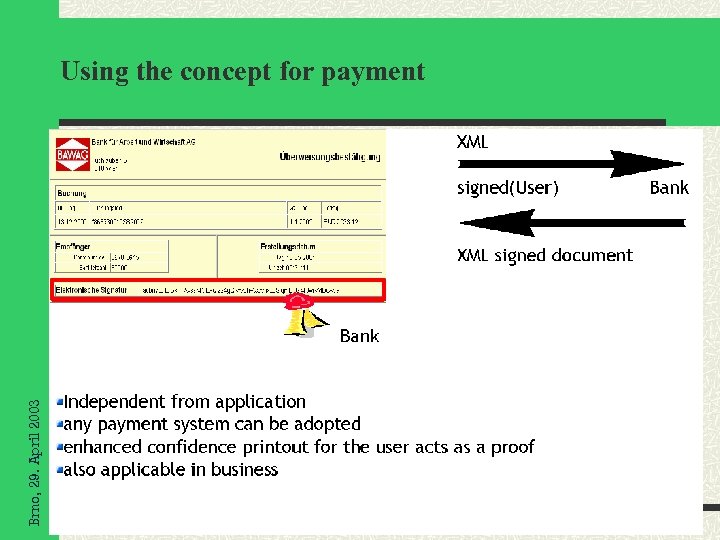 Brno, 29. April 2003 Using the concept for payment 3/19/2018 39/45
Brno, 29. April 2003 Using the concept for payment 3/19/2018 39/45
 2 nd International Scientific Conference Security and Protection of Information Identification / Confidentiality levels sleve. DWoi/DIicif. Stdialnre. T rol n tila ce e ieethw y. Piru. Un in ner oc yt ta t g c f di R p . Brno, 29. April 2003 e-Government processes have different requirements 3/19/2018 40/45
2 nd International Scientific Conference Security and Protection of Information Identification / Confidentiality levels sleve. DWoi/DIicif. Stdialnre. T rol n tila ce e ieethw y. Piru. Un in ner oc yt ta t g c f di R p . Brno, 29. April 2003 e-Government processes have different requirements 3/19/2018 40/45
 Security Level I no specific requirements Browser Server SSL/TLS Brno, 29. April 2003 Based on “conventional” SSL/TLS 3/19/2018 41/45
Security Level I no specific requirements Browser Server SSL/TLS Brno, 29. April 2003 Based on “conventional” SSL/TLS 3/19/2018 41/45
 Security Level II usual G 2 C services Browser Server SSL/TLS 1 Brno, 29. April 2003 2 Authentic. Block: • time • URL • ID 3/19/2018 SCT: • time • URL 3 active component 42/45
Security Level II usual G 2 C services Browser Server SSL/TLS 1 Brno, 29. April 2003 2 Authentic. Block: • time • URL • ID 3/19/2018 SCT: • time • URL 3 active component 42/45
 Security Level III specific confidentiality requirements Browser Server Brno, 29. April 2003 SSL/TLS bind the SSL/TLS certificates to citizen card 3/19/2018 active component 43/45
Security Level III specific confidentiality requirements Browser Server Brno, 29. April 2003 SSL/TLS bind the SSL/TLS certificates to citizen card 3/19/2018 active component 43/45
 Current State Security Layer Demonstrator implemented in JAVA Used by developers “golden device” for developing security capsules to test e-Government applications in early stages Some e-Government applications Brno, 29. April 2003 Applications to social insurance (operational) Registration of a business in Vienna (operational) Petitions to federal ministries (end 2002) Penal records (Q 1 2003) Tax declarations online (Q 1 2003) 3/19/2018 44/45
Current State Security Layer Demonstrator implemented in JAVA Used by developers “golden device” for developing security capsules to test e-Government applications in early stages Some e-Government applications Brno, 29. April 2003 Applications to social insurance (operational) Registration of a business in Vienna (operational) Petitions to federal ministries (end 2002) Penal records (Q 1 2003) Tax declarations online (Q 1 2003) 3/19/2018 44/45
 2 nd International Scientific Conference Security and Protection of Information Brno, 29. April 2003 Conclusions Security capsule / layer provide a technology-neutral interface to the Austrian citizen card e-Austria v Electronic signatures are a central element Concept is the basis of Austrian e-Government initiatives 3/19/2018 45/45
2 nd International Scientific Conference Security and Protection of Information Brno, 29. April 2003 Conclusions Security capsule / layer provide a technology-neutral interface to the Austrian citizen card e-Austria v Electronic signatures are a central element Concept is the basis of Austrian e-Government initiatives 3/19/2018 45/45
 2 nd International Scientific Conference Security and Protection of Information Brno, 29. April 2003 Thank you for your attention ! Herbert. Leitold@a-sit. at 3/19/2018 46/45
2 nd International Scientific Conference Security and Protection of Information Brno, 29. April 2003 Thank you for your attention ! Herbert. Leitold@a-sit. at 3/19/2018 46/45


