82939fb26267fe8fec91a19bf193bcb1.ppt
- Количество слайдов: 68
16: IP Extensions – VPN, Mobile IP, IP Multicast Last Modified: 3/18/2018 9: 03: 39 AM Adapted from Gordon Chaffee’s slides http: //bmrc. berkeley. edu/people/chaffee/advnet 98/ 4: Network Layer 4 a-1
Virtual Private Networks (VPN) 4: Network Layer 4 a-2
Virtual Private Networks r Definition m A VPN is a private network constructed within the public Internet r Goals m Connect private networks using shared public infrastructure r Examples m Connect two sites of a business m Allow people working at home to have full access to company network 4: Network Layer 4 a-3
How accomplished? r IP encapsulation and tunneling r Router at one end of tunnel places private IP packets into the data field of new IP packets (could be encrypted first for security) which are unicast to the other end of the tunnel 4: Network Layer 4 a-4
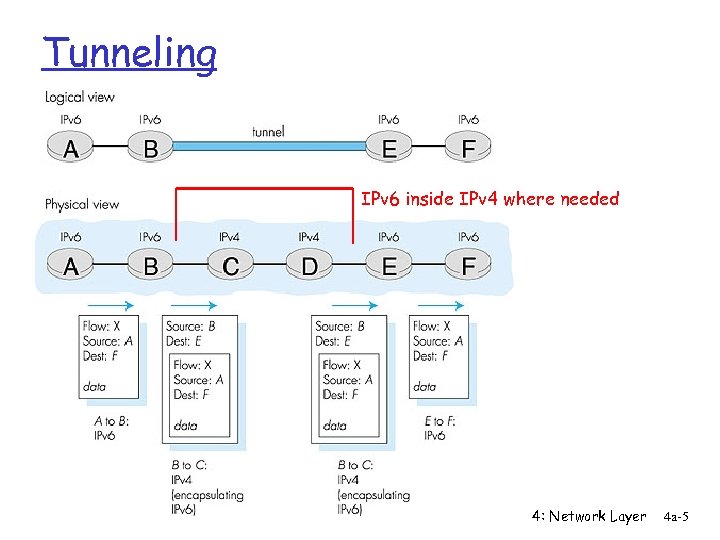
Tunneling IPv 6 inside IPv 4 where needed 4: Network Layer 4 a-5
Motivations r Economic m Using shared infrastructure lowers cost of networking m Less of a need for leased line connections r Communications privacy m Communications can be encrypted if required m Ensure that third parties cannot use virtual network r Virtualized equipment locations m Hosts on same network do not need to be co-located m Make one logical network out of separate physical networks r Support for private network features m Multicast, protocols like IPX or Appletalk, etc 4: Network Layer 4 a-6
Examples r Logical Network Creation r Virtual Dial-Up 4: Network Layer 4 a-7
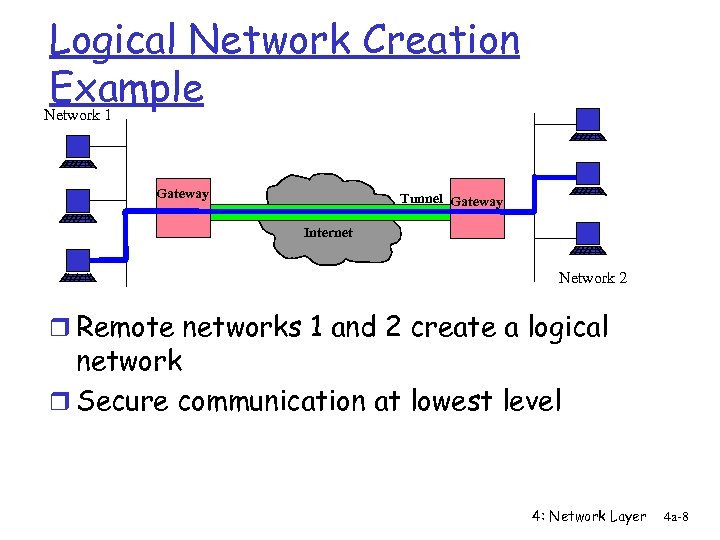
Logical Network Creation Example Network 1 Gateway Tunnel Gateway Internet Network 2 r Remote networks 1 and 2 create a logical network r Secure communication at lowest level 4: Network Layer 4 a-8
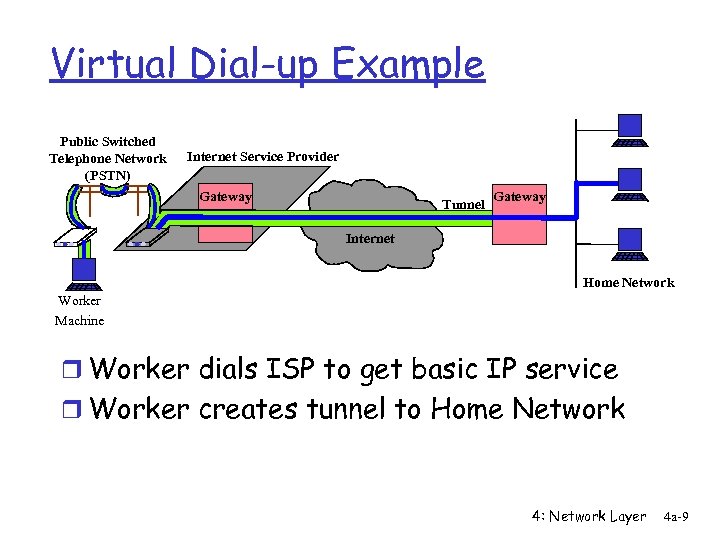
Virtual Dial-up Example Public Switched Telephone Network (PSTN) Internet Service Provider Gateway Tunnel Gateway Internet Home Network Worker Machine r Worker dials ISP to get basic IP service r Worker creates tunnel to Home Network 4: Network Layer 4 a-9
Mobile. IP 4: Network Layer 4 a-10
Mobile. IP r Goal: Allow machines to roam around and maintain IP connectivity r Problem: IP addresses => location m This is important for efficient routing r Solutions? m DHCP? • ok for relocation but not for ongoing connections m Dynamic DNS (mobile nodes update name to IP address mapping as they move around)? • ok for relocation but not for ongoing connections 4: Network Layer 4 a-11
Mobile IP r Allows computer to roam and be reachable r Basic architecture m Home agent (HA) on home network m Foreign agent (FA) at remote network location m Home and foreign agents tunnel traffic m Non-optimal data flow 4: Network Layer 4 a-12
Mobile. IP r Mobile nodes have a permanent home address and a default local router called the “home agent” r The router nearest a nodes current location is called the “foreign agent” m Register with foreign agent when connect to network m Located much like the DHCP server 4: Network Layer 4 a-13
Forwarding Packets r Home agent impersonates the mobile host by changing the mapping from IP address to hardware address (“proxy ARP”) r Sends any packets destined for mobile host on to the foreign agent with IP encapsulation r Foreign agent strips off and does a special translation of the mobile nodes IP address to its current hardware address 4: Network Layer 4 a-14
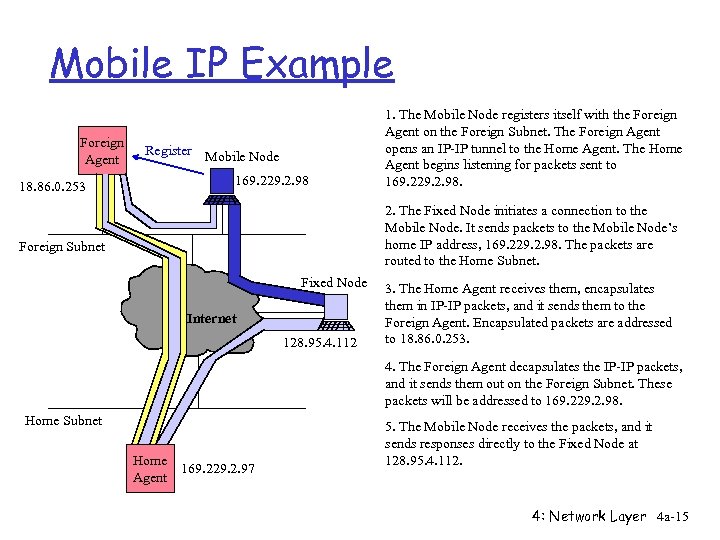
Mobile IP Example Foreign Agent Register Mobile Node 169. 229. 2. 98 18. 86. 0. 253 1. The Mobile Node registers itself with the Foreign Agent on the Foreign Subnet. The Foreign Agent opens an IP-IP tunnel to the Home Agent. The Home Agent begins listening for packets sent to 169. 229. 2. 98. 2. The Fixed Node initiates a connection to the Mobile Node. It sends packets to the Mobile Node’s home IP address, 169. 229. 2. 98. The packets are routed to the Home Subnet. Foreign Subnet Fixed Node Internet 128. 95. 4. 112 3. The Home Agent receives them, encapsulates them in IP-IP packets, and it sends them to the Foreign Agent. Encapsulated packets are addressed to 18. 86. 0. 253. 4. The Foreign Agent decapsulates the IP-IP packets, and it sends them out on the Foreign Subnet. These packets will be addressed to 169. 229. 2. 98. Home Subnet Home Agent 169. 229. 2. 97 5. The Mobile Node receives the packets, and it sends responses directly to the Fixed Node at 128. 95. 4. 112. 4: Network Layer 4 a-15
Avoiding the Foreign Agent r Mobile host can also obtain a new IP address on the remote network and inform the home agent r The home agent can then resend the packet to the new IP address 4: Network Layer 4 a-16
Optimizations r What if two remote hosts are temporarily close together r If they want to send traffic to each other, why should it have to go all the way to their home agents and back again r Optimizations exist to allow the sending node to learn and cache the current location of a recipient to avoid this problem 4: Network Layer 4 a-17
IP Multicast 4: Network Layer 4 a-18
What is multicast? r 1 to N communication r Bandwidth-conserving technology that reduces traffic by simultaneously delivering a single stream of information to multiple recipients r Examples of Multicast m Network hardware efficiently supports multicast transport • Example: Ethernet allows one packet to be received by many hosts m Many different protocols and service models • Examples: IETF IP Multicast, ATM Multipoint 4: Network Layer 4 a-19
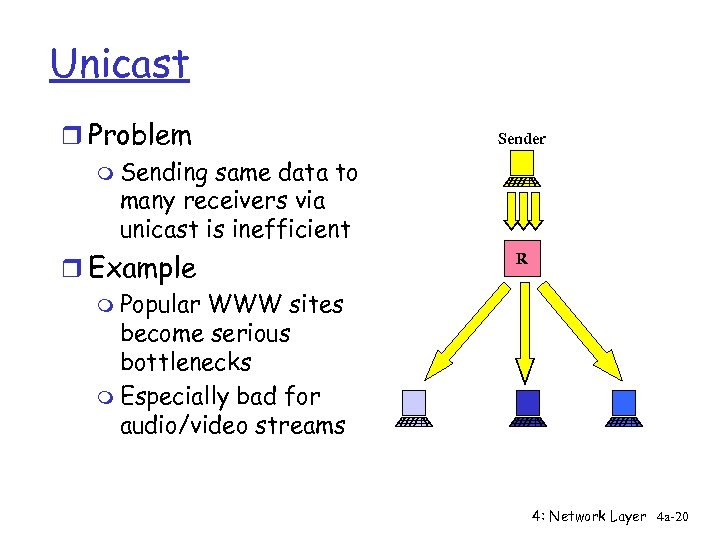
Unicast r Problem m Sending same data to many receivers via unicast is inefficient r Example m Popular WWW sites become serious bottlenecks m Especially bad for audio/video streams Sender R 4: Network Layer 4 a-20
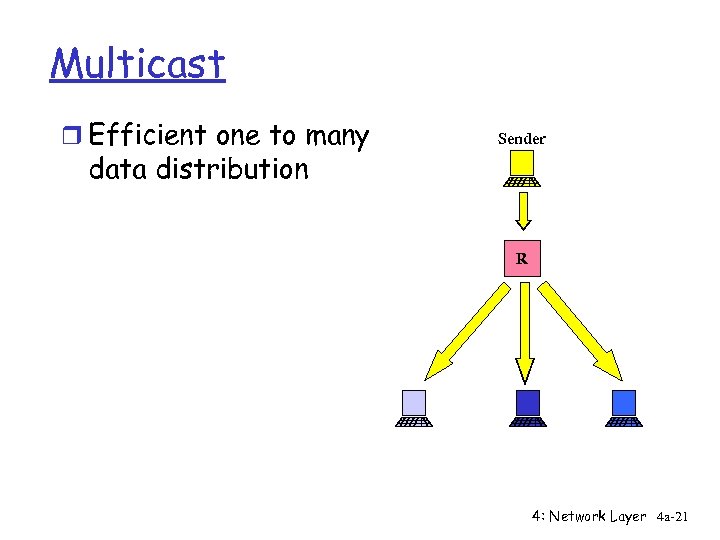
Multicast r Efficient one to many data distribution Sender R 4: Network Layer 4 a-21
IP Multicast Introduction r Efficient one to many data distribution m Tree style data distribution m Packets traverse network links only once r Location independent addressing m IP address per multicast group r Receiver oriented service model m Applications can join and leave multicast groups m Senders do not know who is listening m Similar to television model m Contrasts with telephone network, ATM 4: Network Layer 4 a-22
IP Multicast r Service m All senders send at the same time to the same group m Receivers subscribe to any group m Routers find receivers r Unreliable delivery r Reserved IP addresses m 224. 0. 0. 0 to 239. 255 reserved for multicast m Static addresses for popular services (e. g. Session Announcement Protocol) 4: Network Layer 4 a-23
Internet Group Management Protocol (IGMP) r Protocol for managing group membership m IP hosts report multicast group memberships to neighboring routers m Messages in IGMPv 2 (RFC 2236) • Membership Query (from routers) • Membership Report (from hosts) • Leave Group (from hosts) r Announce-Listen protocol with Suppression m Hosts respond only if no other hosts has responded r Soft State protocol 4: Network Layer 4 a-24
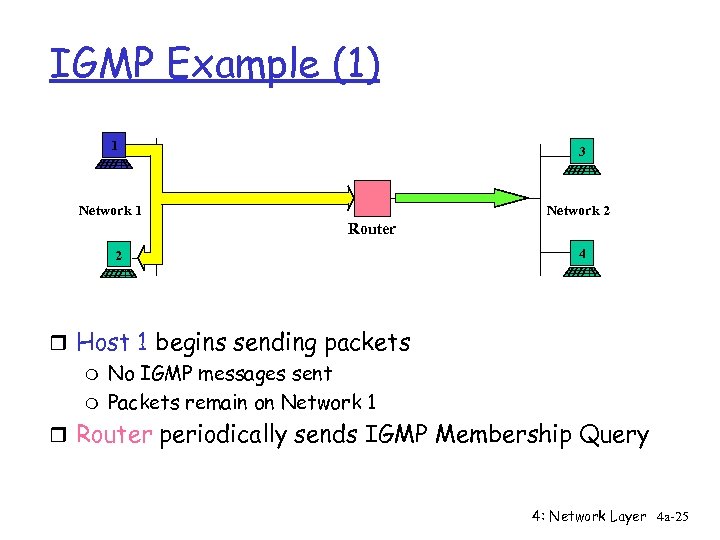
IGMP Example (1) 1 3 Network 1 Network 2 Router 2 4 r Host 1 begins sending packets m No IGMP messages sent m Packets remain on Network 1 r Router periodically sends IGMP Membership Query 4: Network Layer 4 a-25
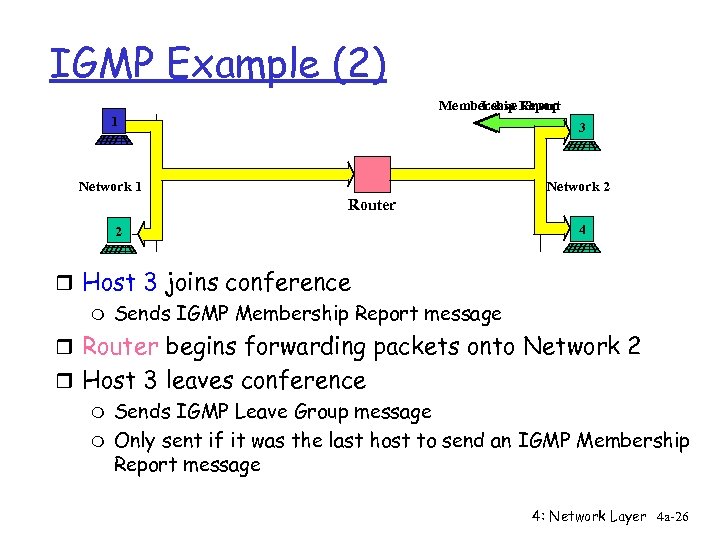
IGMP Example (2) Membership Report Leave Group 1 3 Network 1 Network 2 Router 2 4 r Host 3 joins conference m Sends IGMP Membership Report message r Router begins forwarding packets onto Network 2 r Host 3 leaves conference m Sends IGMP Leave Group message m Only sent if it was the last host to send an IGMP Membership Report message 4: Network Layer 4 a-26
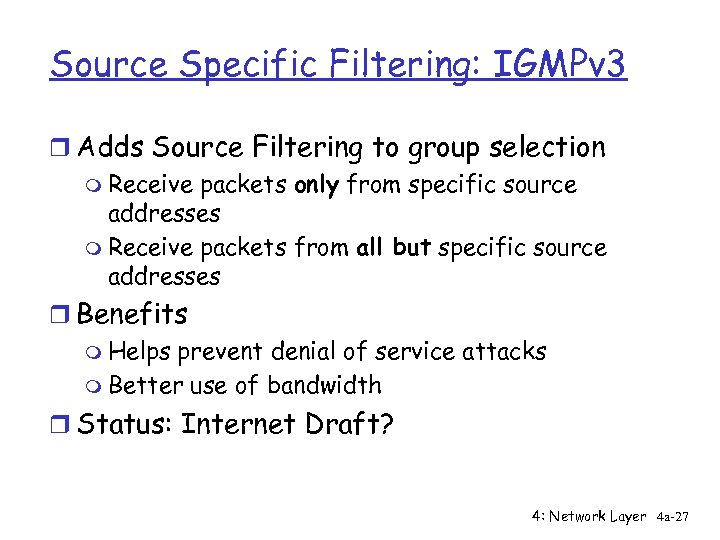
Source Specific Filtering: IGMPv 3 r Adds Source Filtering to group selection m Receive packets only from specific source addresses m Receive packets from all but specific source addresses r Benefits m Helps prevent denial of service attacks m Better use of bandwidth r Status: Internet Draft? 4: Network Layer 4 a-27
Multicast Routing Discussion r What is the problem? m Need to find all receivers in a multicast group m Need to create spanning tree of receivers r Design goals m Minimize unwanted traffic m Minimize router state m Scalability m Reliability 4: Network Layer 4 a-28
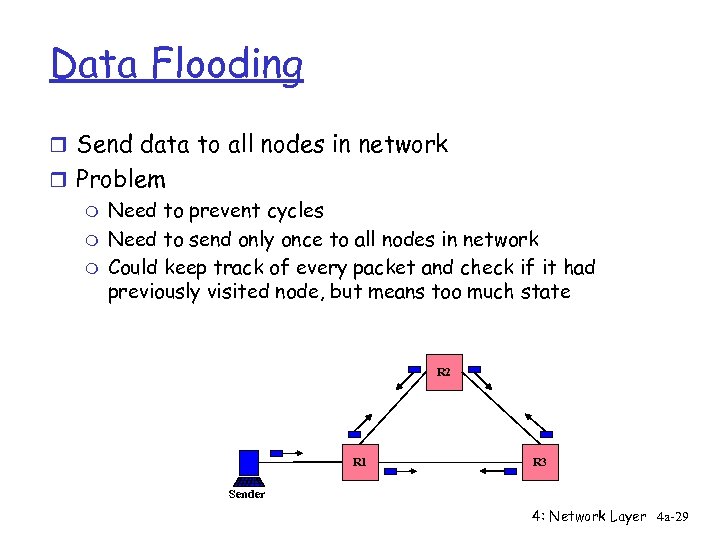
Data Flooding r Send data to all nodes in network r Problem m Need to prevent cycles m Need to send only once to all nodes in network m Could keep track of every packet and check if it had previously visited node, but means too much state R 2 R 1 R 3 Sender 4: Network Layer 4 a-29
Reverse Path Forwarding (RPF) r Simple technique for building trees r Send out all interfaces except the one with the shortest path to the sender r In unicast routing, routers send to the destination via the shortest path r In multicast routing, routers send away from the shortest path to the sender 4: Network Layer 4 a-30
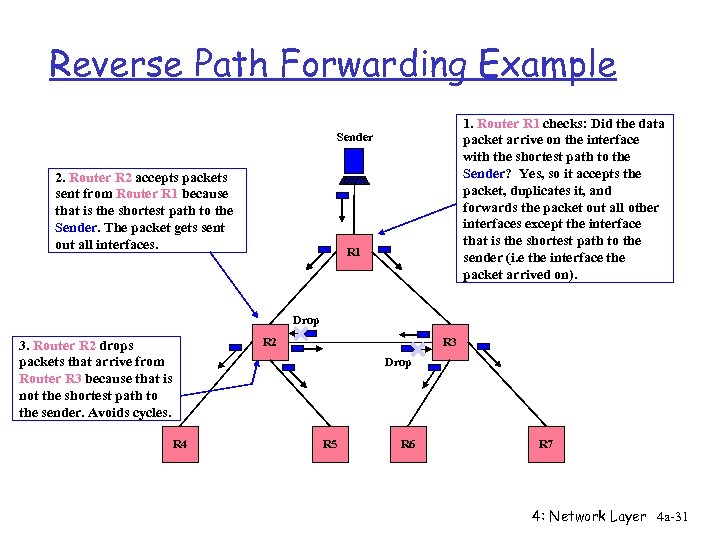
Reverse Path Forwarding Example 1. Router R 1 checks: Did the data packet arrive on the interface with the shortest path to the Sender? Yes, so it accepts the packet, duplicates it, and forwards the packet out all other interfaces except the interface that is the shortest path to the sender (i. e the interface the packet arrived on). Sender 2. Router R 2 accepts packets sent from Router R 1 because that is the shortest path to the Sender. The packet gets sent out all interfaces. R 1 Drop R 2 3. Router R 2 drops packets that arrive from Router R 3 because that is not the shortest path to the sender. Avoids cycles. R 3 Drop R 4 R 5 R 6 R 7 4: Network Layer 4 a-31
Multicast Tunneling r Problem m Not all routers are multicast capable m Want to connect domains with non-multicast routers between them r Solution m Encapsulate multicast packets in unicast packet m Tunnel multicast traffic across non-multicast routers m We will see more examples of tunneling later 4: Network Layer 4 a-32
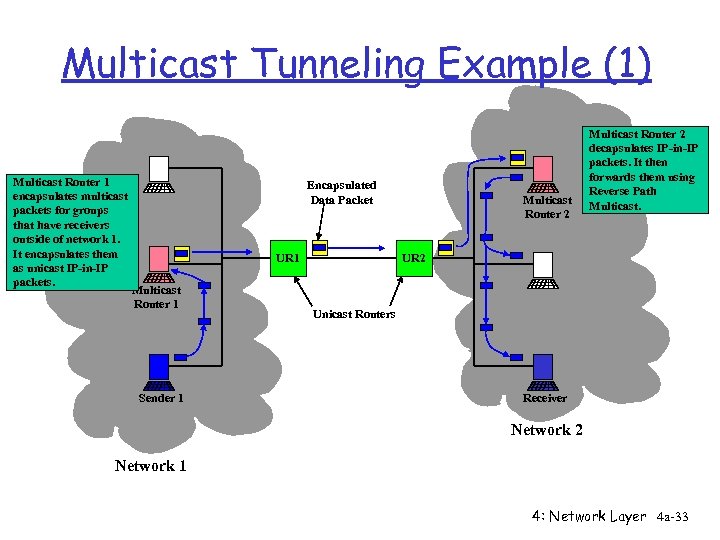
Multicast Tunneling Example (1) Multicast Router 1 encapsulates multicast packets for groups that have receivers outside of network 1. It encapsulates them as unicast IP-in-IP packets. Encapsulated Data Packet UR 1 Multicast Router 1 Sender 1 Multicast Router 2 decapsulates IP-in-IP packets. It then forwards them using Reverse Path Multicast. UR 2 Unicast Routers Receiver Network 2 Network 1 4: Network Layer 4 a-33
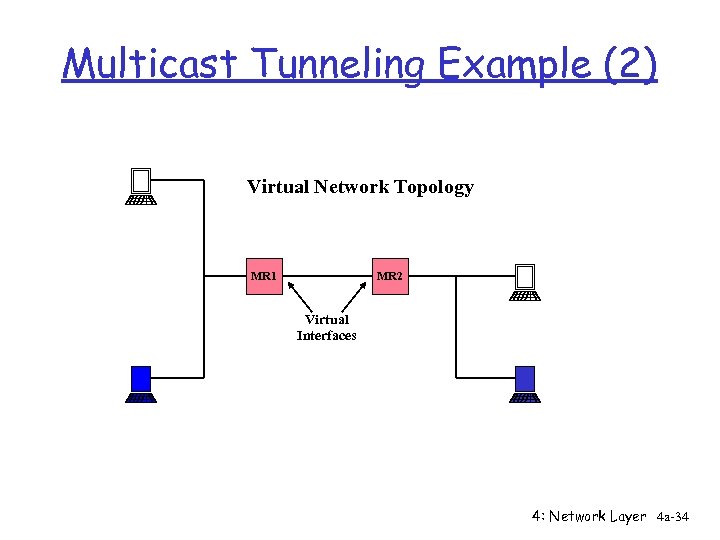
Multicast Tunneling Example (2) Virtual Network Topology MR 1 MR 2 Virtual Interfaces 4: Network Layer 4 a-34
Roadmap r Finished with the network layer and IP specifics r Next on to the link layer r If two hosts are on the same network how do they send data directly to one another 4: Network Layer 4 a-35
Outtakes 4: Network Layer 4 a-36
Protocol Independent Multicast (PIM) r Uses unicast routing table for topology r Dense mode (PIM-DM) m For groups with many receivers in local/global region m Like DVMRP, a flood and prune algorithm r Sparse mode (PIM-SM) m For groups with few widely distributed receivers m Builds shared tree per group, but may construct source rooted tree for efficiency m Explicit join 4: Network Layer 4 a-37
MBone r MBONE m Multicast capable virtual network, subset of Internet m Native multicast regions connection with tunnels r In 1992, the MBone was created to further the development of IP multicast m m Experimental, global multicast network Served as a testbed for multicast applications development • vat -- audio tool • vic -- video tool • wb -- shared whiteboard 4: Network Layer 4 a-38
Data Distribution Choices r Source rooted trees m State in routers for each sender m Forms shortest path tree from each sender to receivers m Minimal delays from sources to destinations r Shared trees m All senders use the same distribution tree m State in routers only for wanted groups m No per sender state (until IGMPv 3) m Greater latency for data distribution 4: Network Layer 4 a-39
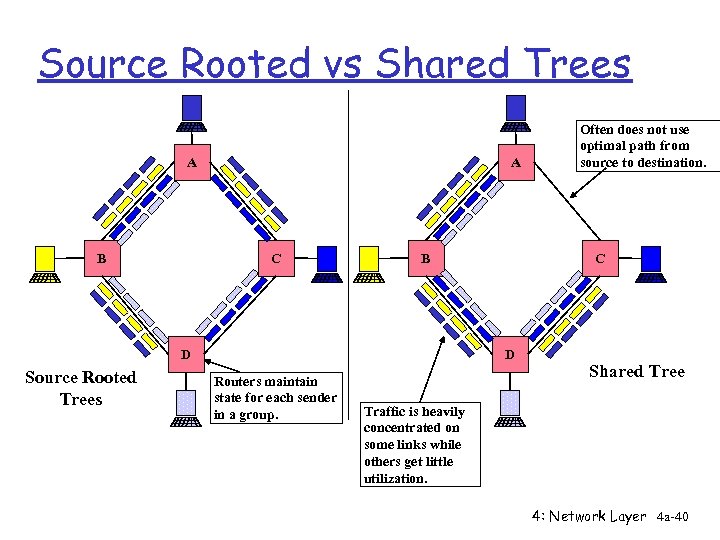
Source Rooted vs Shared Trees A B A C B D Source Rooted Trees C D Routers maintain state for each sender in a group. Often does not use optimal path from source to destination. Shared Tree Traffic is heavily concentrated on some links while others get little utilization. 4: Network Layer 4 a-40
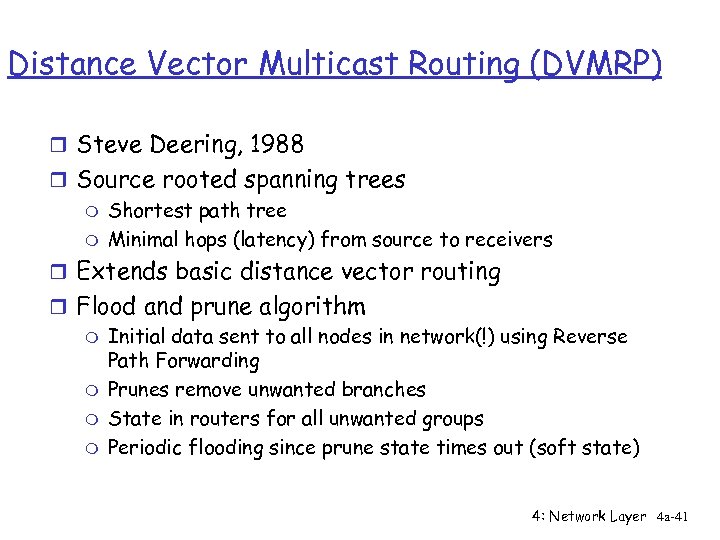
Distance Vector Multicast Routing (DVMRP) r Steve Deering, 1988 r Source rooted spanning trees m Shortest path tree m Minimal hops (latency) from source to receivers r Extends basic distance vector routing r Flood and prune algorithm m Initial data sent to all nodes in network(!) using Reverse Path Forwarding m Prunes remove unwanted branches m State in routers for all unwanted groups m Periodic flooding since prune state times out (soft state) 4: Network Layer 4 a-41
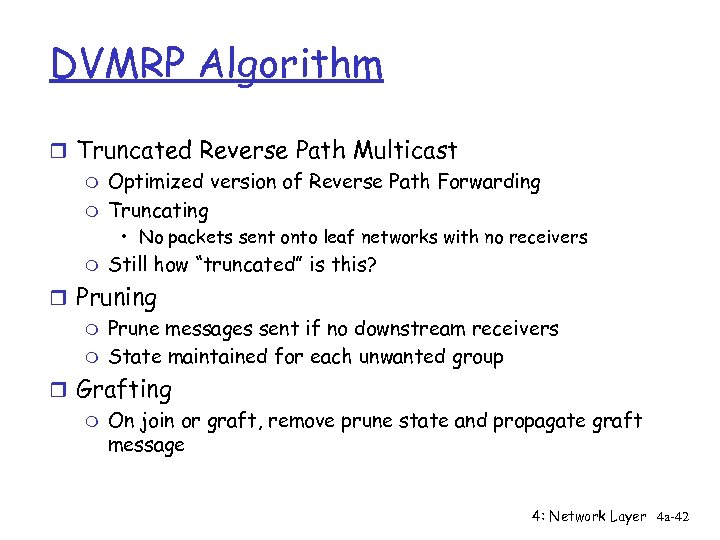
DVMRP Algorithm r Truncated Reverse Path Multicast m Optimized version of Reverse Path Forwarding m Truncating • No packets sent onto leaf networks with no receivers m Still how “truncated” is this? r Pruning m Prune messages sent if no downstream receivers m State maintained for each unwanted group r Grafting m On join or graft, remove prune state and propagate graft message 4: Network Layer 4 a-42
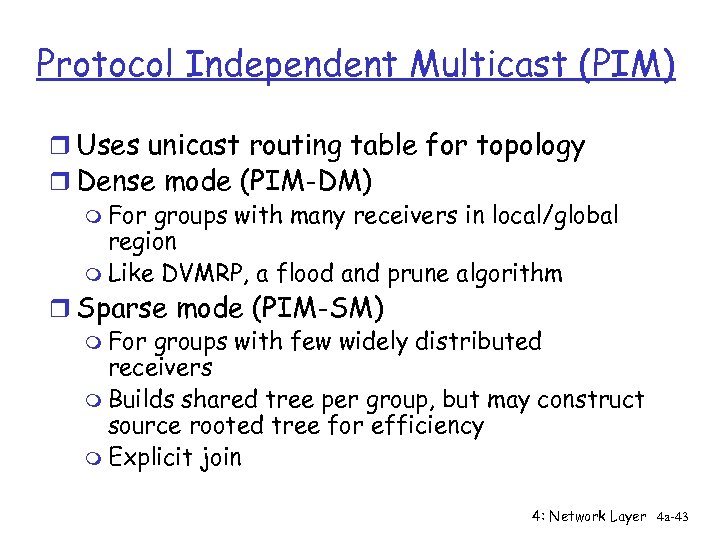
Protocol Independent Multicast (PIM) r Uses unicast routing table for topology r Dense mode (PIM-DM) m For groups with many receivers in local/global region m Like DVMRP, a flood and prune algorithm r Sparse mode (PIM-SM) m For groups with few widely distributed receivers m Builds shared tree per group, but may construct source rooted tree for efficiency m Explicit join 4: Network Layer 4 a-43
IP Multicast in the Real World 4: Network Layer 4 a-44
Commercial Motivation r Problem m Traffic on Internet is growing about 100% per year m Router technology is getting better at 70% per year m Routers that are fast enough are very expensive r ISPs need to find ways to reduce traffic r Multicast could be used to… m WWW: Distribute data from popular sites to caches throughout Internet m Send video/audio streams multicast m Software distribution 4: Network Layer 4 a-45
ISP Concerns r Multicast causes high network utilization m One source can produce high total network load m Experimental multicast applications are relatively high bandwidth: audio and video m Flow control non-existent in many multicast apps r Multicast breaks telco/ISP pricing model m Currently, both sender and receiver pay for bandwidth m Multicast allows sender to buy less bandwidth while reaching same number of receivers m Load on ISP network not proportional to source data rate 4: Network Layer 4 a-46
Economics of Multicast r One packet sent to multiple receivers r Sender + Benefits by reducing network load compared to unicast + Lower cost of network connectivity r Network service provider - One packet sent can cause load greater than unicast packet load + Reduces overall traffic that flows over network r Receiver = Same number of packets received as unicast 4: Network Layer 4 a-47
Multicast Problems r Multicast is immature m Immature protocols and applications m Tools are poor, difficult to use, debugging is difficult m Routing protocols leave many issues unresolved • Interoperability of flood and prune/explicit join • Routing instability r Multicast development has focused on academic problems, not business concerns m m Multicast breaks telco/ISP traffic charging and management models Routing did not address policy • PIM, DVMRP, CBT do not address ISP policy concerns • BGMP addresses some ISP concerns, but it is still under development 4: Network Layer 4 a-48
Current ISP Multicast Solution r Restrict senders of multicast data r Charge senders to distribute multicast traffic m Static agreements r Do not forward multicast traffic m Some ISP’s offer multicast service to customers (e. g. UUNET UUCast) m ISP beginning to discuss peer agreements 4: Network Layer 4 a-49
Distance Vector Multicast Routing (DVMRP) r Steve Deering, 1988 r Source rooted spanning trees m Shortest path tree m Minimal hops (latency) from source to receivers r Extends basic distance vector routing r Flood and prune algorithm m Initial data sent to all nodes in network(!) using Reverse Path Forwarding m Prunes remove unwanted branches m State in routers for all unwanted groups m Periodic flooding since prune state times out (soft state) 4: Network Layer 4 a-50
DVMRP Algorithm r Truncated Reverse Path Multicast m Optimized version of Reverse Path Forwarding m Truncating • No packets sent onto leaf networks with no receivers m Still how “truncated” is this? r Pruning m Prune messages sent if no downstream receivers m State maintained for each unwanted group r Grafting m On join or graft, remove prune state and propagate graft message 4: Network Layer 4 a-51
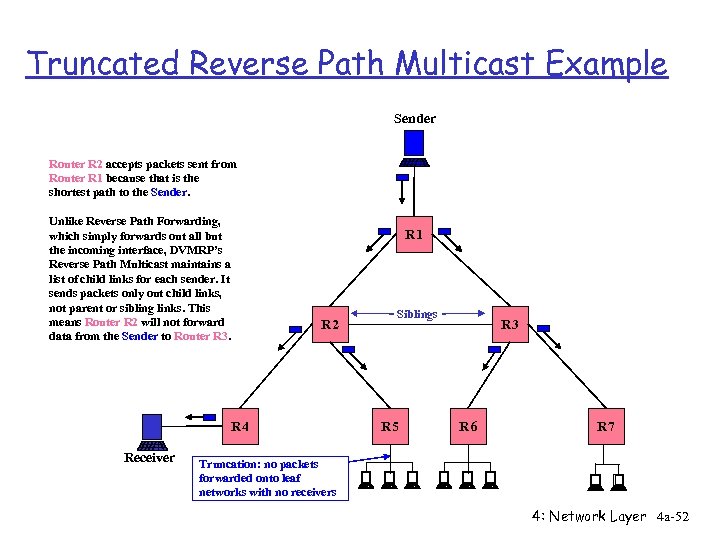
Truncated Reverse Path Multicast Example Sender Router R 2 accepts packets sent from Router R 1 because that is the shortest path to the Sender. Unlike Reverse Path Forwarding, which simply forwards out all but the incoming interface, DVMRP’s Reverse Path Multicast maintains a list of child links for each sender. It sends packets only out child links, not parent or sibling links. This means Router R 2 will not forward data from the Sender to Router R 3. R 1 R 2 R 4 Receiver Siblings R 5 R 3 R 6 R 7 Truncation: no packets forwarded onto leaf networks with no receivers 4: Network Layer 4 a-52
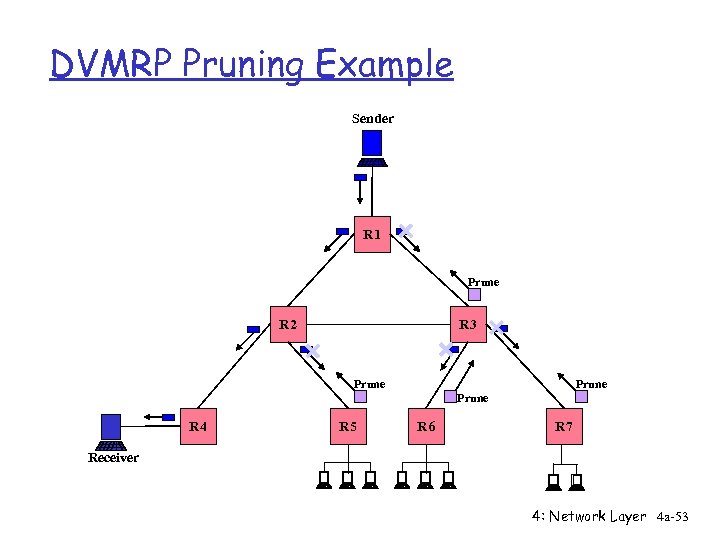
DVMRP Pruning Example Sender R 1 Prune R 2 R 3 Prune R 4 R 5 R 6 R 7 Receiver 4: Network Layer 4 a-53
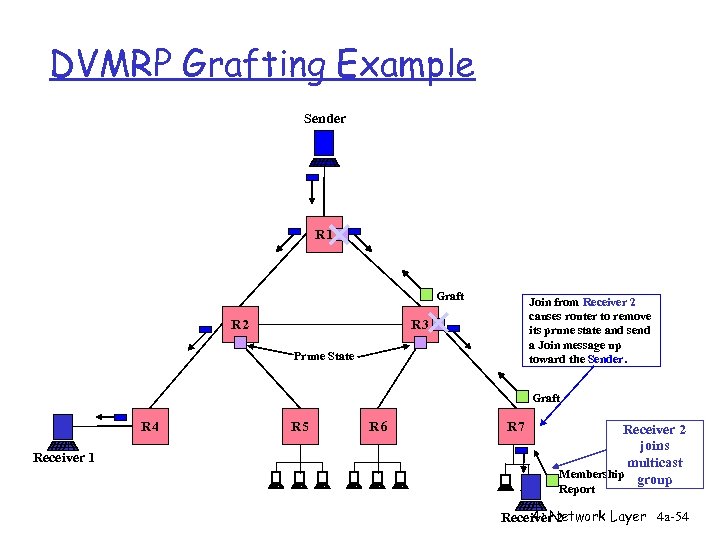
DVMRP Grafting Example Sender R 1 Graft R 2 Join from Receiver 2 causes router to remove its prune state and send a Join message up toward the Sender. R 3 Prune State Graft R 4 Receiver 1 R 5 R 6 R 7 Receiver 2 joins multicast Membership group Report 4: Network Layer 4 a-54 Receiver 2
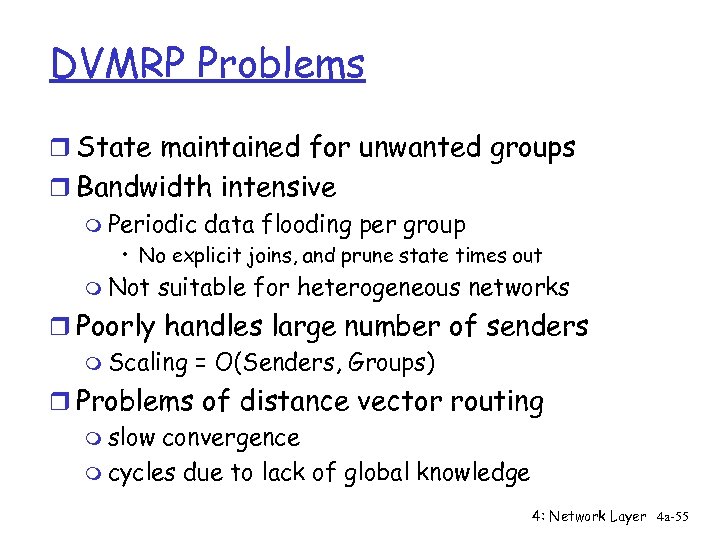
DVMRP Problems r State maintained for unwanted groups r Bandwidth intensive m Periodic data flooding per group • No explicit joins, and prune state times out m Not suitable for heterogeneous networks r Poorly handles large number of senders m Scaling = O(Senders, Groups) r Problems of distance vector routing m slow convergence m cycles due to lack of global knowledge 4: Network Layer 4 a-55
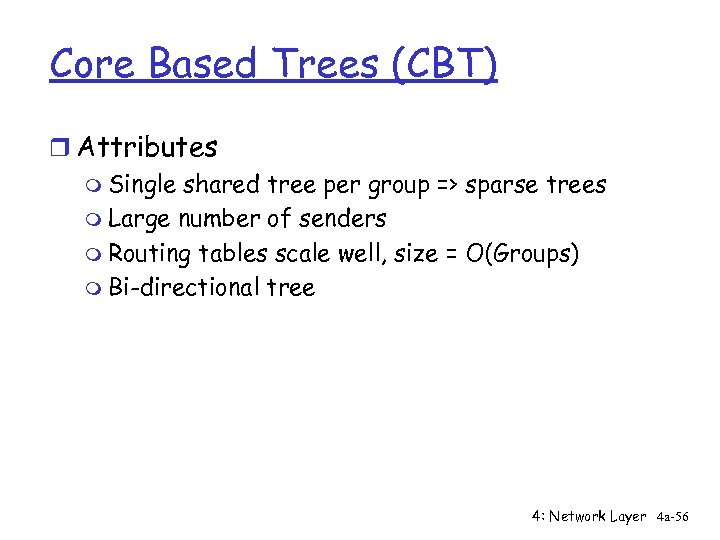
Core Based Trees (CBT) r Attributes m Single shared tree per group => sparse trees m Large number of senders m Routing tables scale well, size = O(Groups) m Bi-directional tree 4: Network Layer 4 a-56
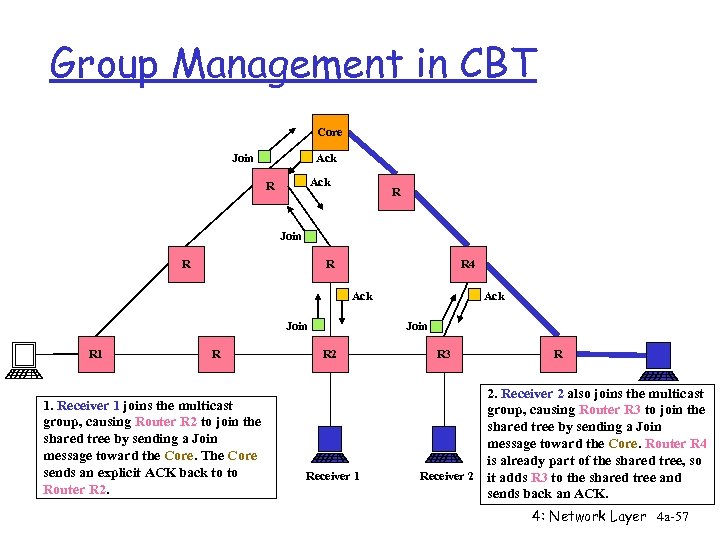
Group Management in CBT Core Join Ack R R Join R R R 4 Ack Join R 1. Receiver 1 joins the multicast group, causing Router R 2 to join the shared tree by sending a Join message toward the Core. The Core sends an explicit ACK back to to Router R 2. Ack Join R 2 Receiver 1 R 3 R 2. Receiver 2 also joins the multicast group, causing Router R 3 to join the shared tree by sending a Join message toward the Core. Router R 4 is already part of the shared tree, so Receiver 2 it adds R 3 to the shared tree and sends back an ACK. 4: Network Layer 4 a-57
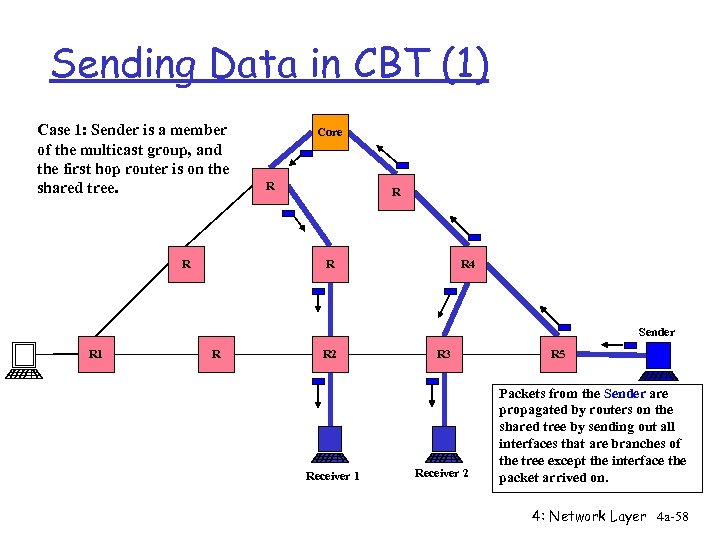
Sending Data in CBT (1) Case 1: Sender is a member of the multicast group, and the first hop router is on the shared tree. R Core R R 4 Sender R 1 R R 2 Receiver 1 R 3 Receiver 2 R 5 Packets from the Sender are propagated by routers on the shared tree by sending out all interfaces that are branches of the tree except the interface the packet arrived on. 4: Network Layer 4 a-58
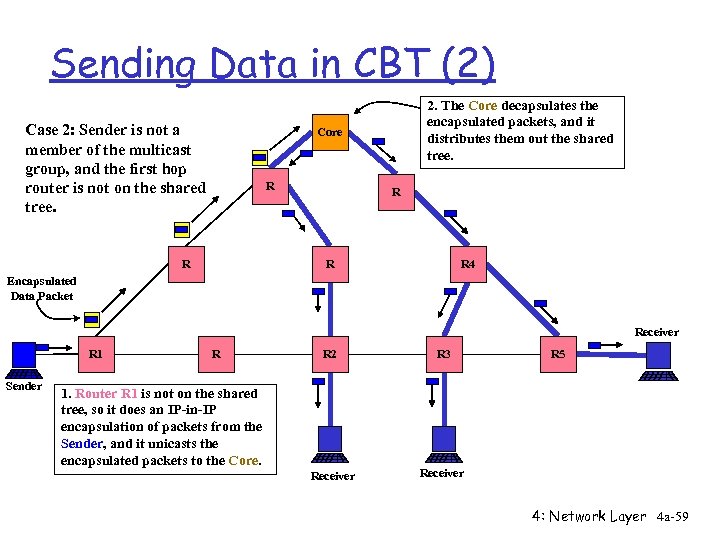
Sending Data in CBT (2) Case 2: Sender is not a member of the multicast group, and the first hop router is not on the shared tree. 2. The Core decapsulates the encapsulated packets, and it distributes them out the shared tree. Core R R R 4 Encapsulated Data Packet Receiver R 1 Sender R R 2 R 3 Receiver 1. Router R 1 is not on the shared tree, so it does an IP-in-IP encapsulation of packets from the Sender, and it unicasts the encapsulated packets to the Core. R 5 4: Network Layer 4 a-59
Protocol Independent Multicast (PIM) r Uses unicast routing table for topology r Dense mode (PIM-DM) m For groups with many receivers in local/global region m Like DVMRP, a flood and prune algorithm r Sparse mode (PIM-SM) m For groups with few widely distributed receivers m Builds shared tree per group, but may construct source rooted tree for efficiency m Explicit join 4: Network Layer 4 a-60
PIM Sparse Mode r Hybrid protocol that combines features of DVMRP and CBT r Suited to widely distributed, heterogeneous networks r Shared tree centered at Rendezvous Point (RP) r Shared tree introduces sources to receivers r Source specific trees for heavy traffic flows r Unidirectional distribution tree 4: Network Layer 4 a-61
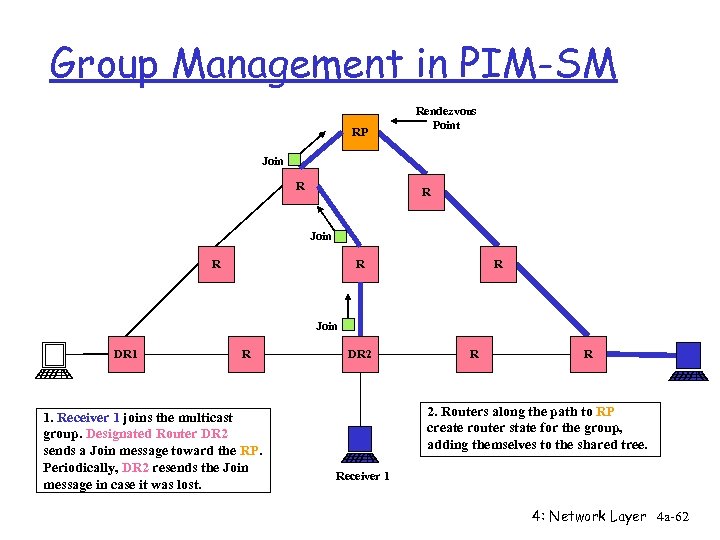
Group Management in PIM-SM RP Rendezvous Point Join R R R Join DR 1 R 1. Receiver 1 joins the multicast group. Designated Router DR 2 sends a Join message toward the RP. Periodically, DR 2 resends the Join message in case it was lost. DR 2 R R 2. Routers along the path to RP create router state for the group, adding themselves to the shared tree. Receiver 1 4: Network Layer 4 a-62
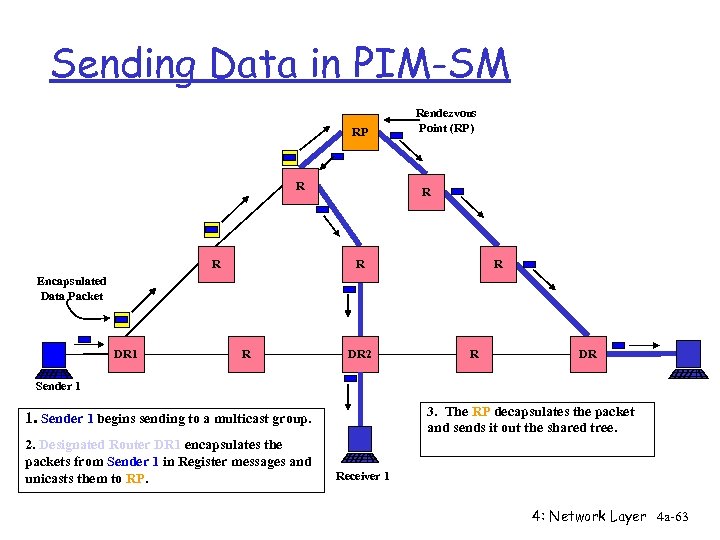
Sending Data in PIM-SM RP R R Rendezvous Point (RP) R R R Encapsulated Data Packet DR 1 R DR 2 R DR Sender 1 3. The RP decapsulates the packet and sends it out the shared tree. 1. Sender 1 begins sending to a multicast group. 2. Designated Router DR 1 encapsulates the packets from Sender 1 in Register messages and unicasts them to RP. Receiver 1 4: Network Layer 4 a-63
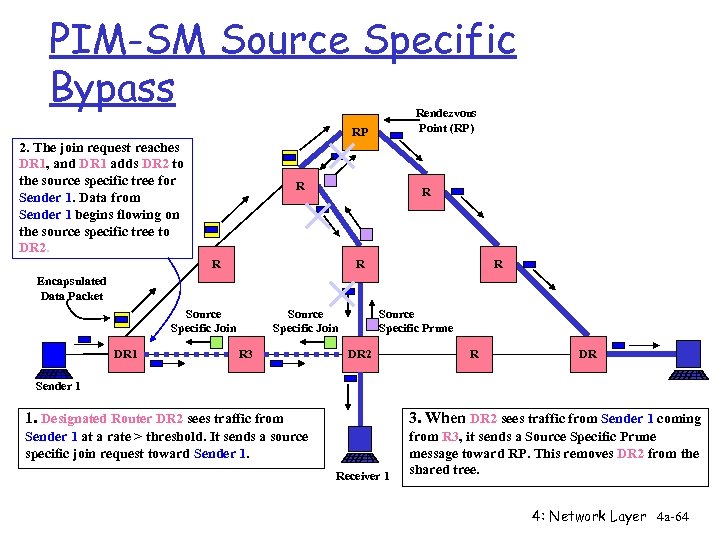
PIM-SM Source Specific Bypass Rendezvous Point (RP) RP 2. The join request reaches DR 1, and DR 1 adds DR 2 to the source specific tree for Sender 1. Data from Sender 1 begins flowing on the source specific tree to DR 2. R R R Encapsulated Data Packet Source Specific Join DR 1 Source Specific Join R 3 Source Specific Prune DR 2 R DR Sender 1 1. Designated Router DR 2 sees traffic from 3. When DR 2 sees traffic from Sender 1 coming Sender 1 at a rate > threshold. It sends a source specific join request toward Sender 1. from R 3, it sends a Source Specific Prune message toward RP. This removes DR 2 from the shared tree. Receiver 1 4: Network Layer 4 a-64
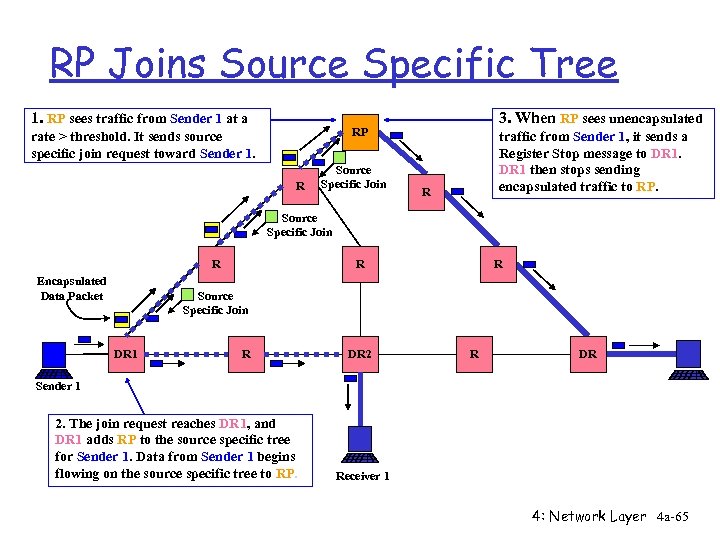
RP Joins Source Specific Tree 1. RP sees traffic from Sender 1 at a 3. When RP sees unencapsulated RP rate > threshold. It sends source specific join request toward Sender 1. R Source Specific Join traffic from Sender 1, it sends a Register Stop message to DR 1 then stops sending encapsulated traffic to RP. R Source Specific Join R Encapsulated Data Packet R R Source Specific Join DR 1 R DR 2 R DR Sender 1 2. The join request reaches DR 1, and DR 1 adds RP to the source specific tree for Sender 1. Data from Sender 1 begins flowing on the source specific tree to RP. Receiver 1 4: Network Layer 4 a-65
Problems with PIM r Global broadcasts of all Rendezvous Points r Sensitive to location of RP r No administrative control over multicast traffic; policy controls lacking r Conceived as inter-domain, but now considered intra-domain 4: Network Layer 4 a-66
Classification of Tree Building Choices r Flood network topology to all routers m Link state protocol m Multicast Extensions to OSPF (MOSPF) r Flood and prune m Distance Vector Multicast Routing Protocol (DVMRP) m Protocol Independent Multicast Dense Mode (PIM-DM) r Explicit join m Core Based Trees (CBT) m Protocol Independent Multicast Sparse Mode (PIM-SM) 4: Network Layer 4 a-67
Border Gateway Multicast Protocol (BGMP) r Administrative control of multicast traffic r Hierarchical multicast address allocation r Uses BGP for routing tables r No global broadcasts of anything r Bi-directional shared multicast routing tree 4: Network Layer 4 a-68
82939fb26267fe8fec91a19bf193bcb1.ppt